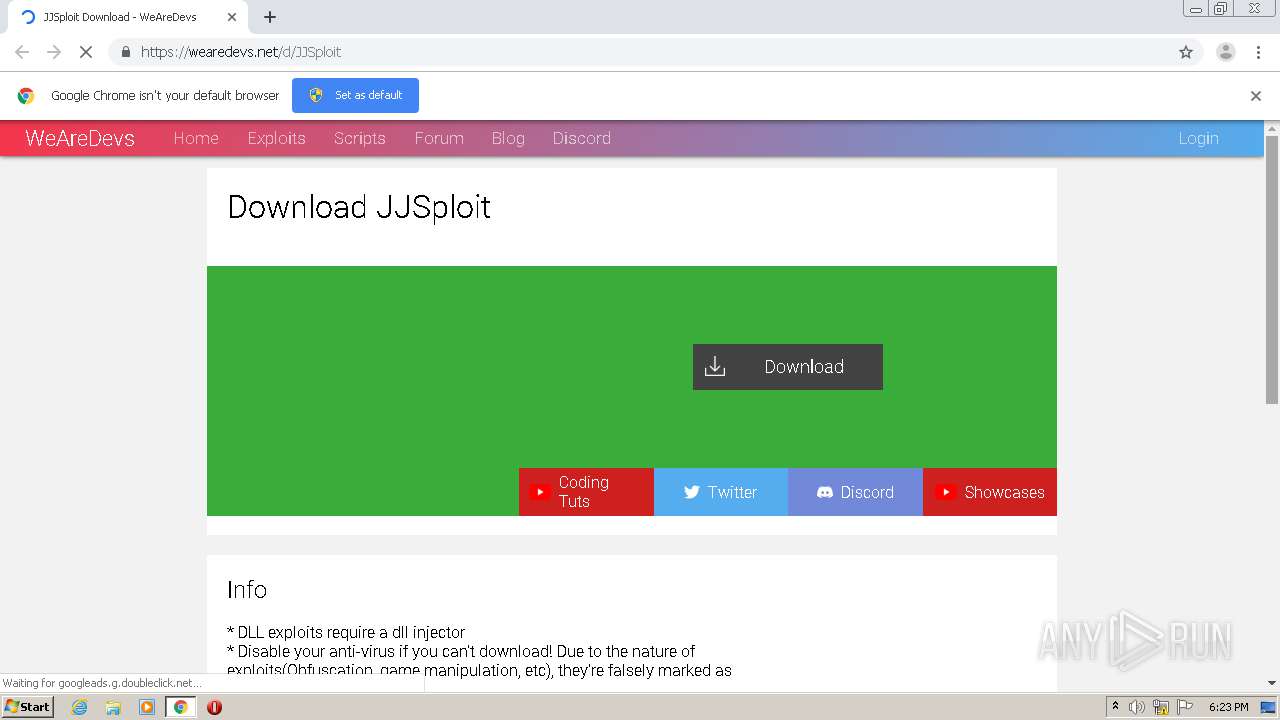
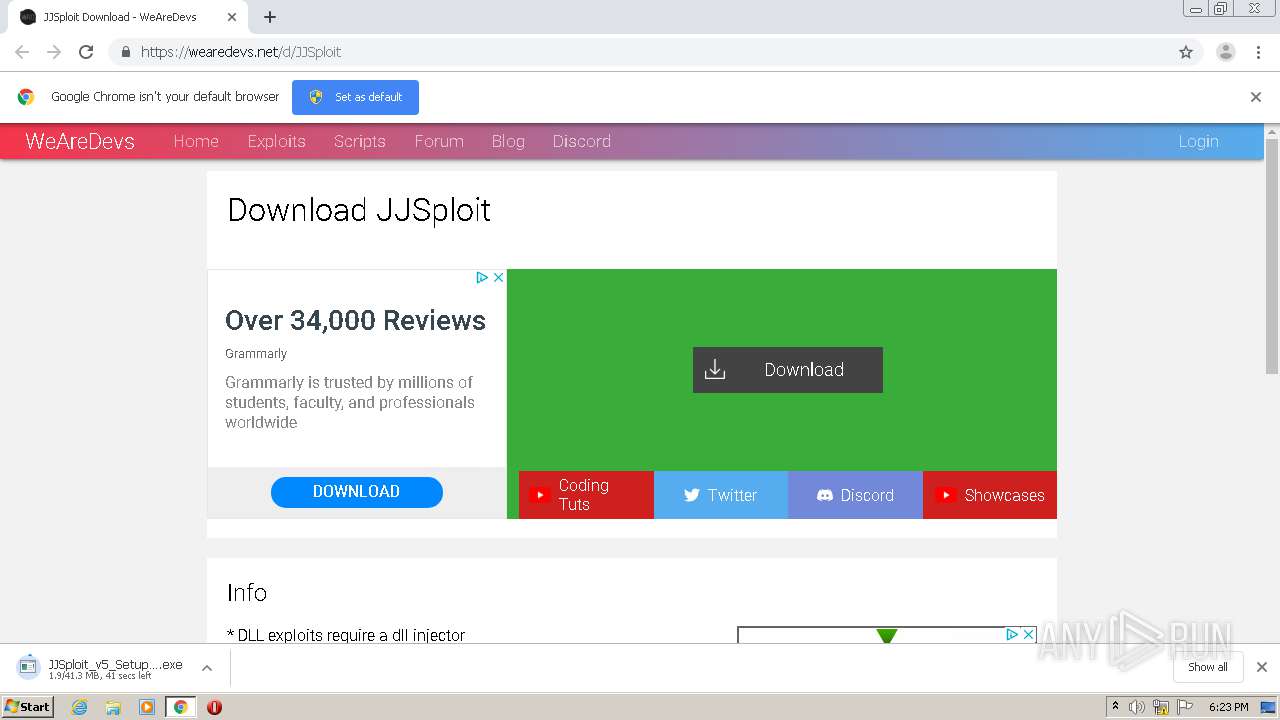
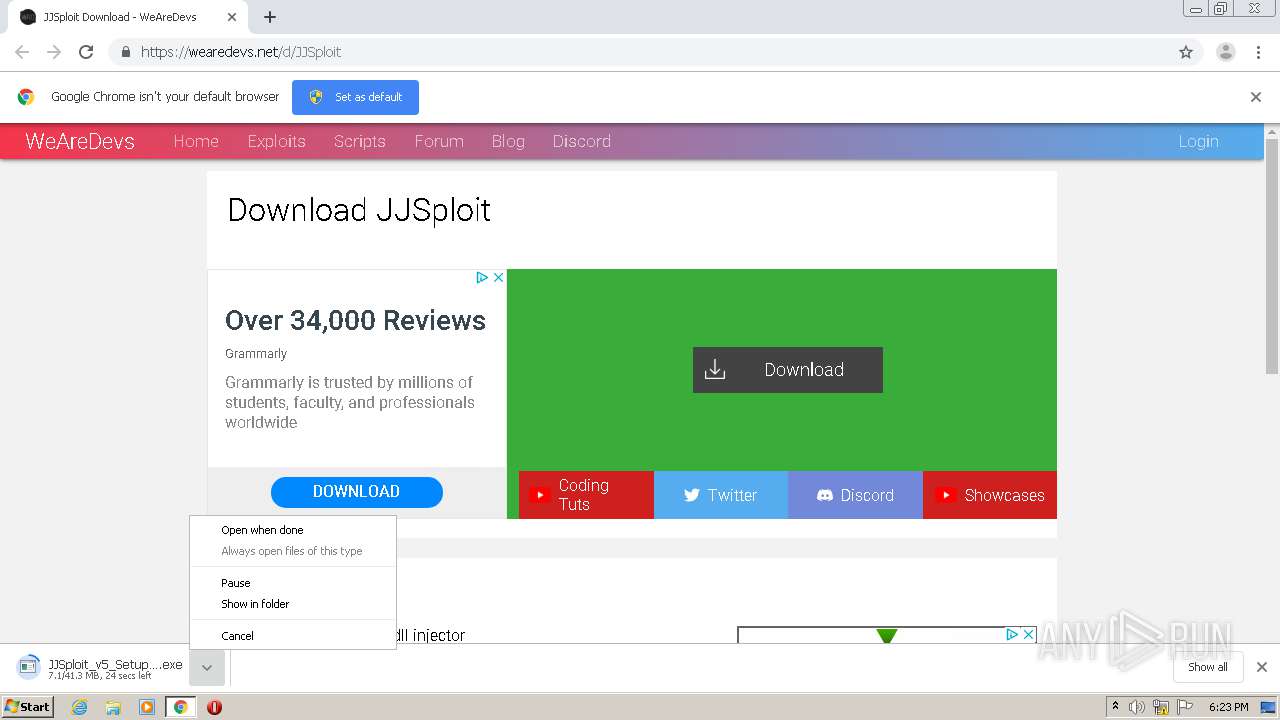
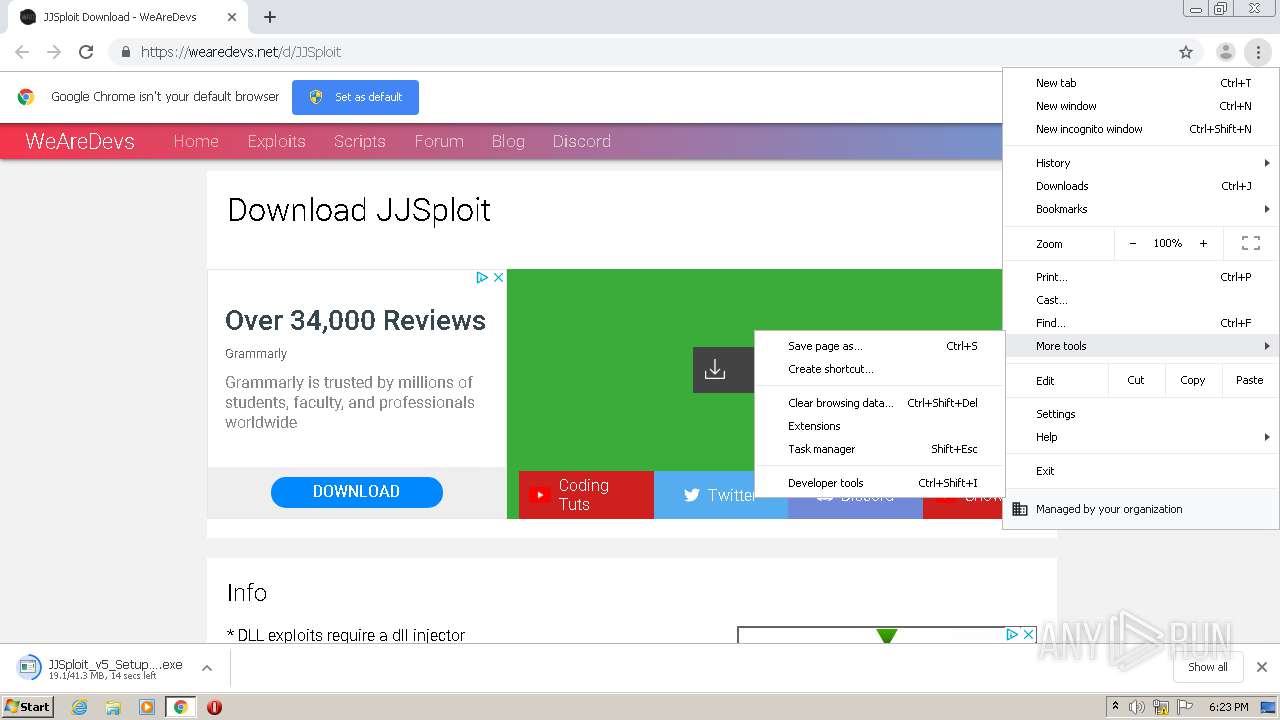
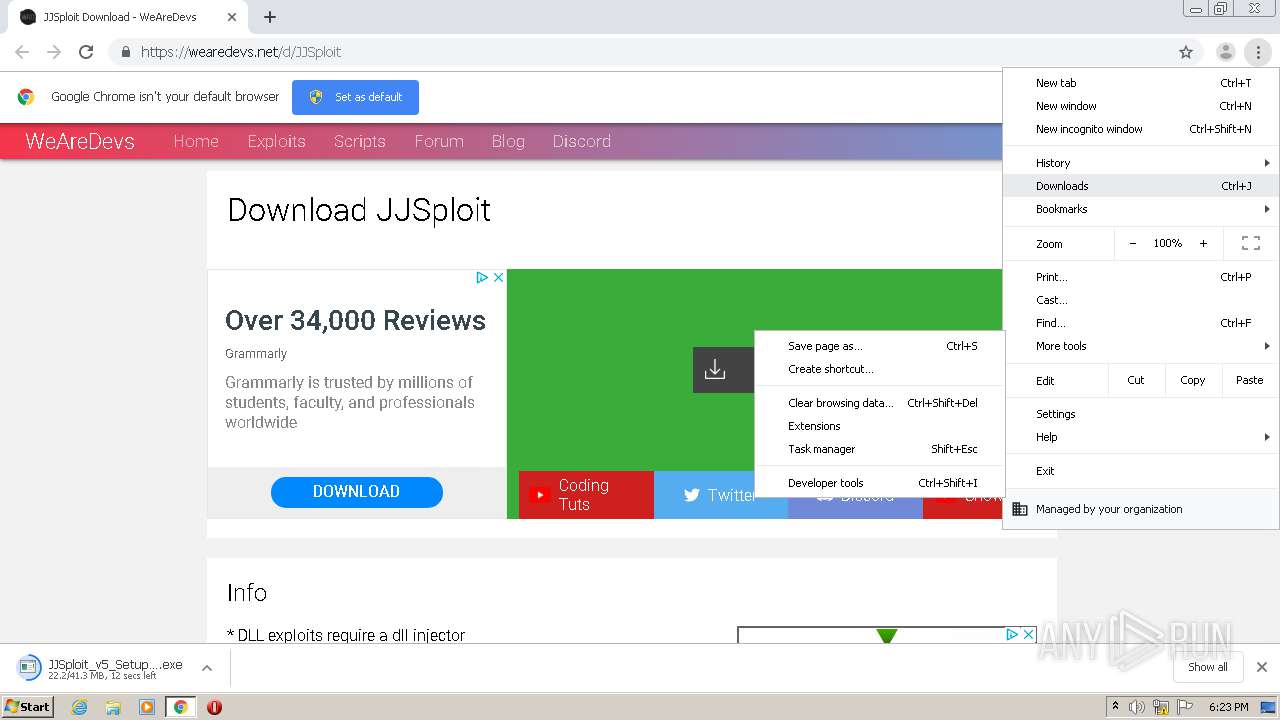
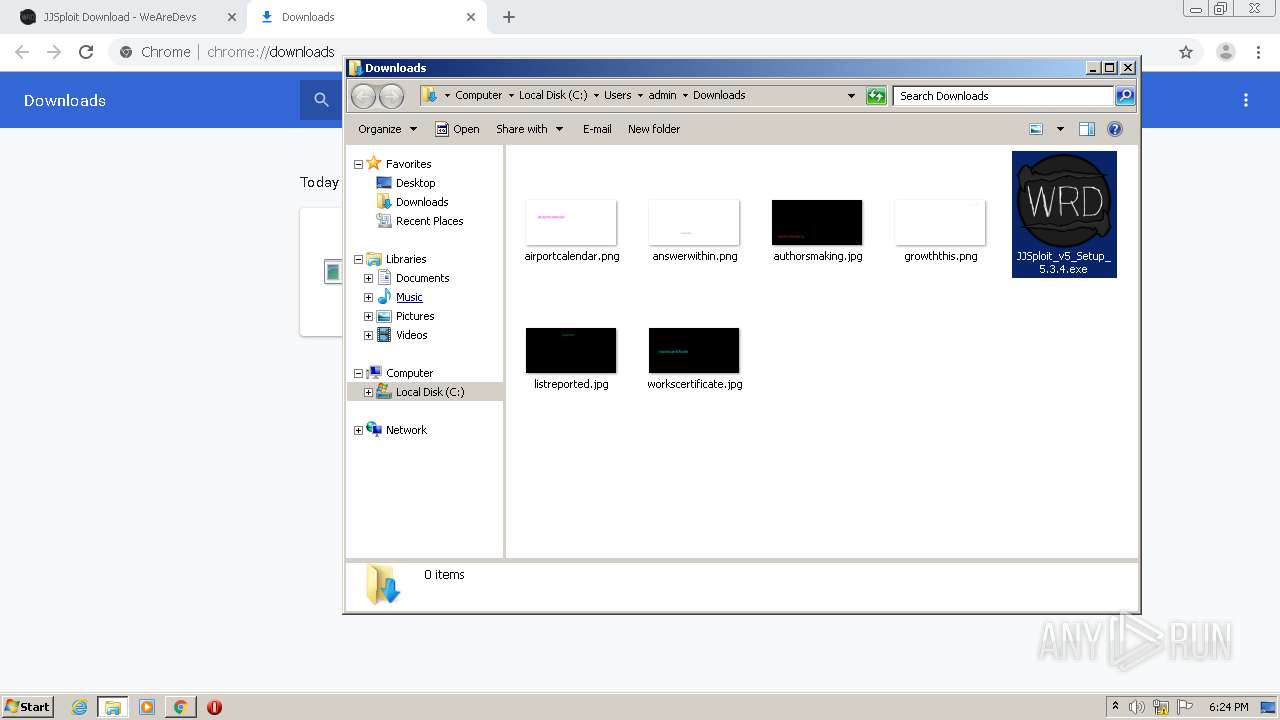
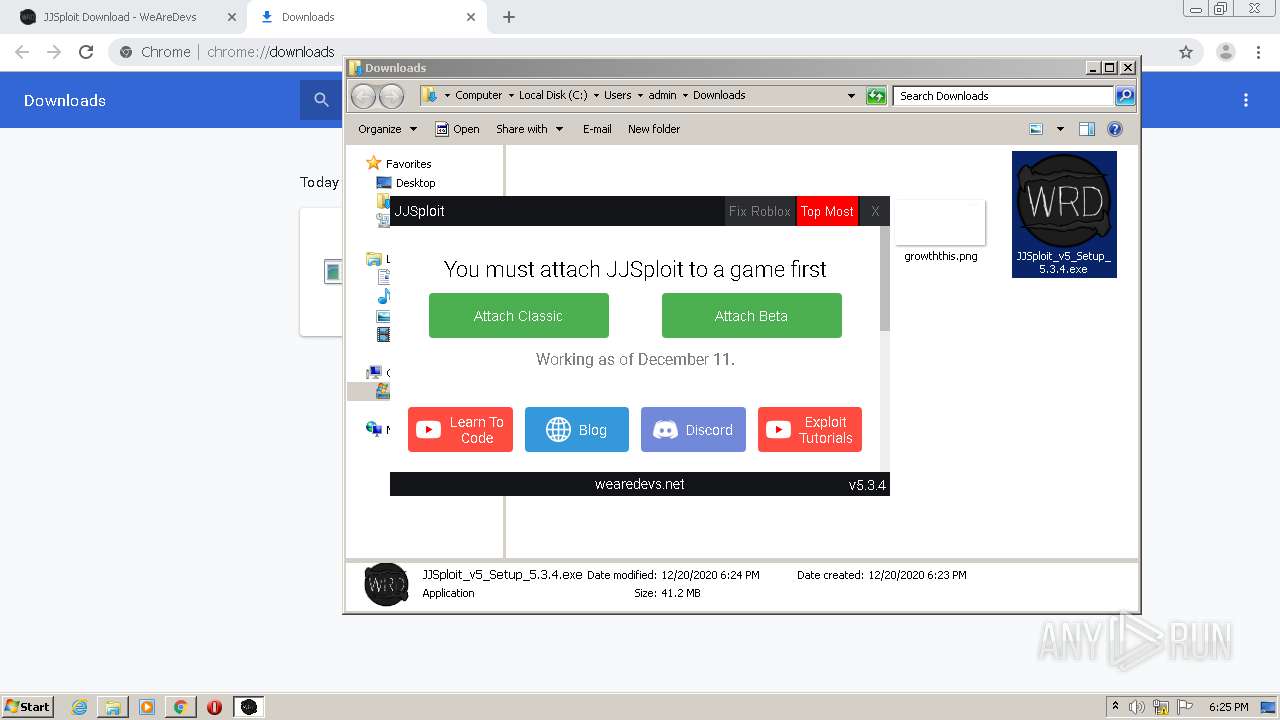
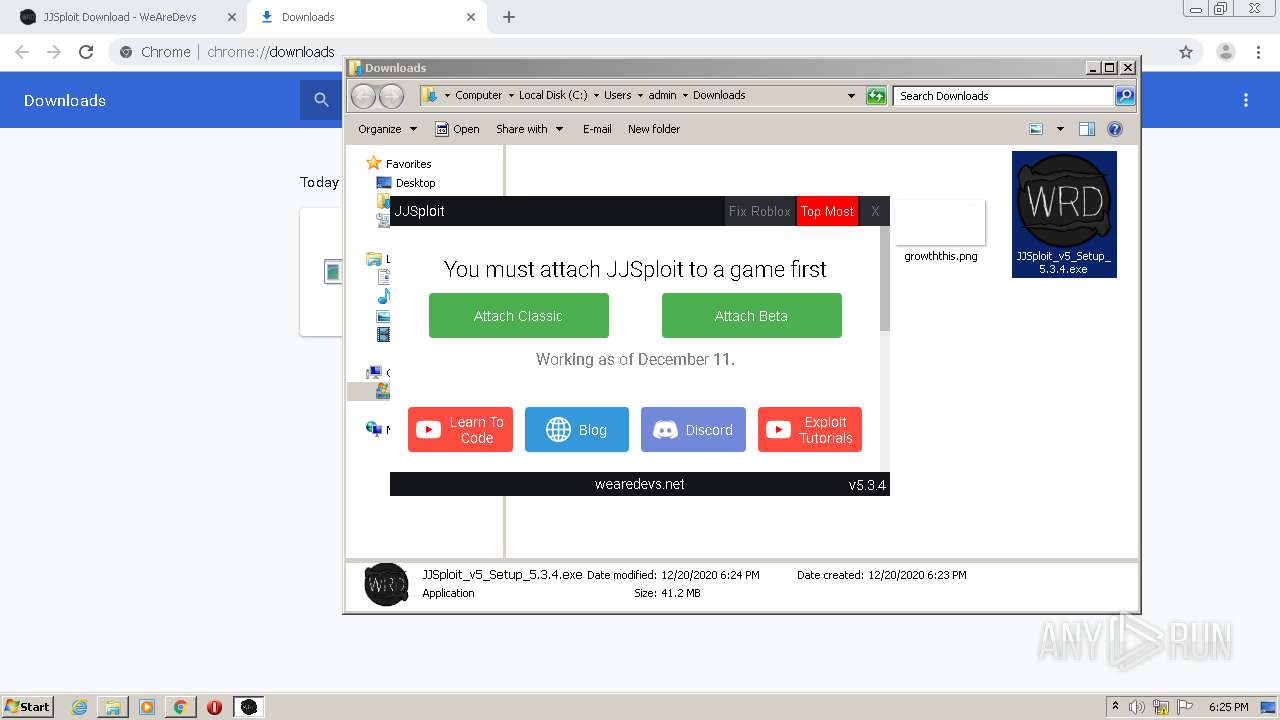
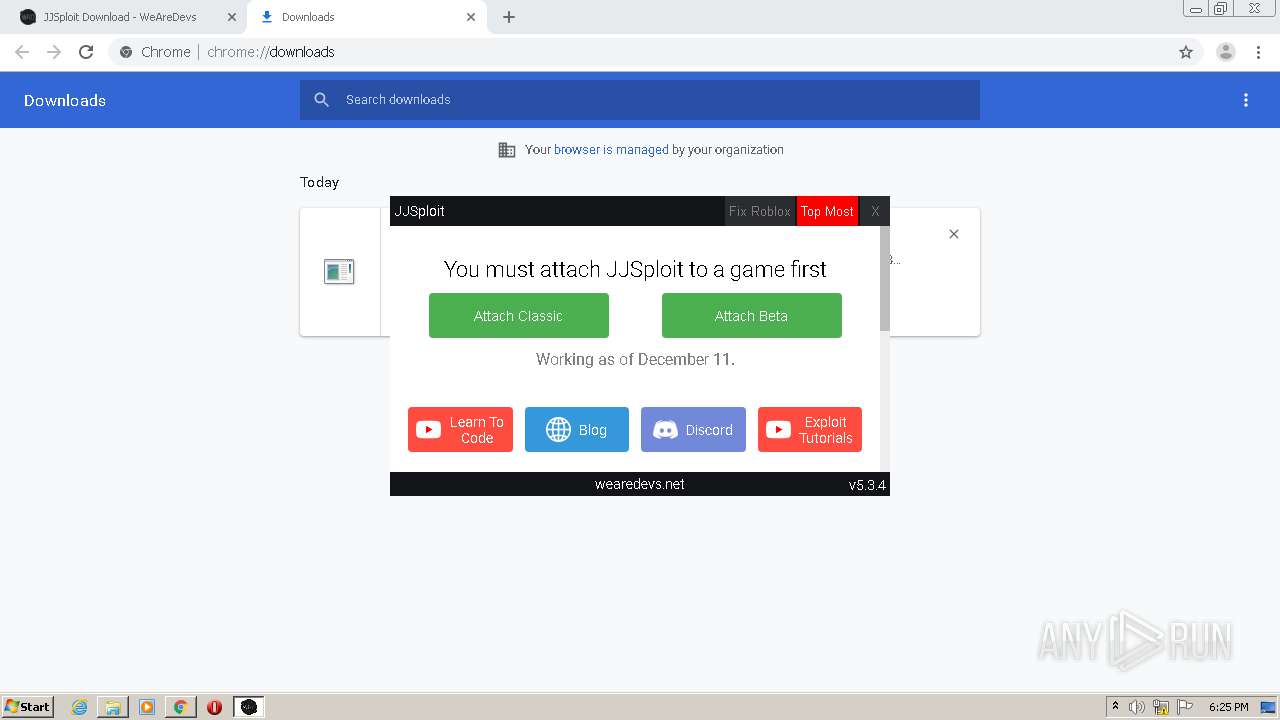
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/c753382f-e4a8-4f01-a938-5be0dd1ec876 |
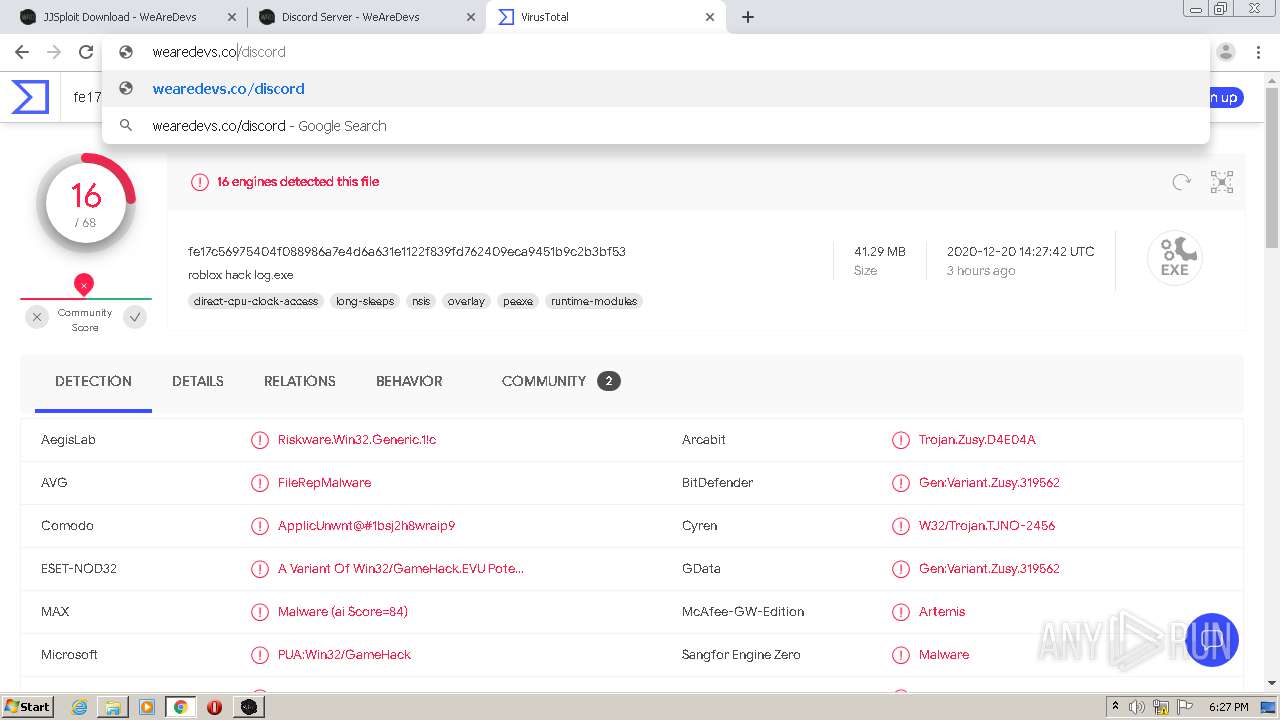
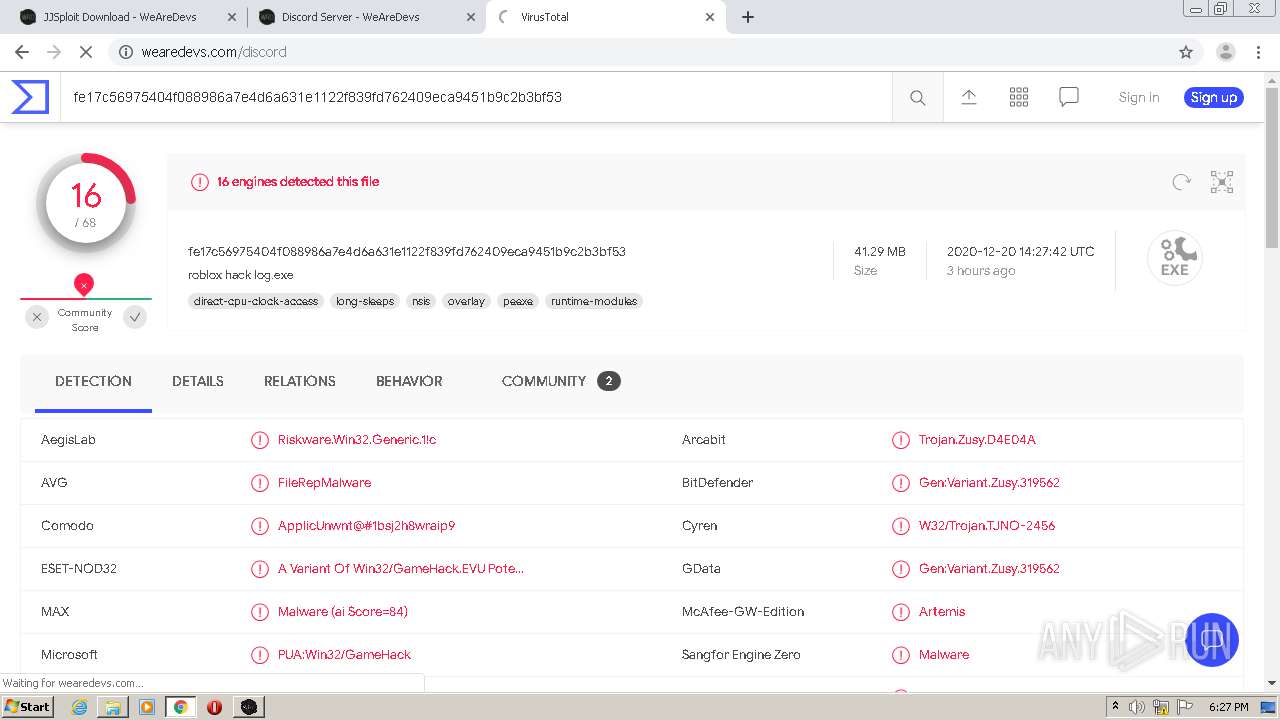
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2020, 18:23:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
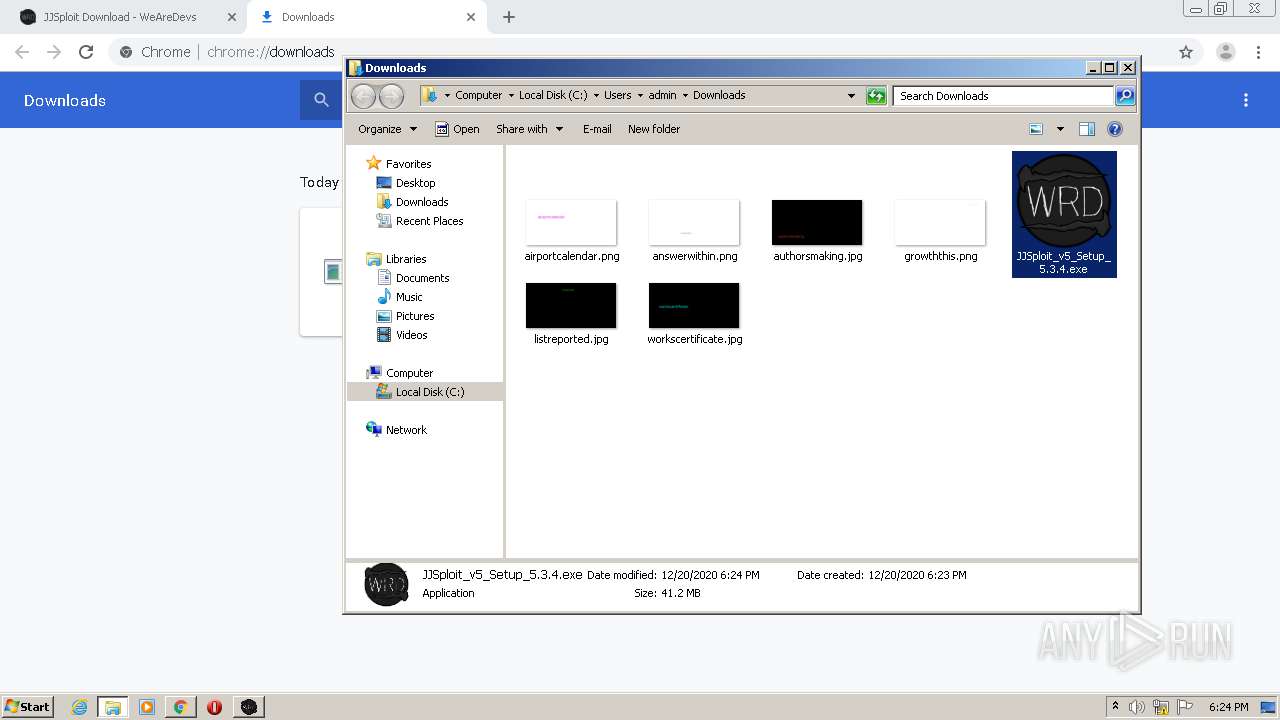
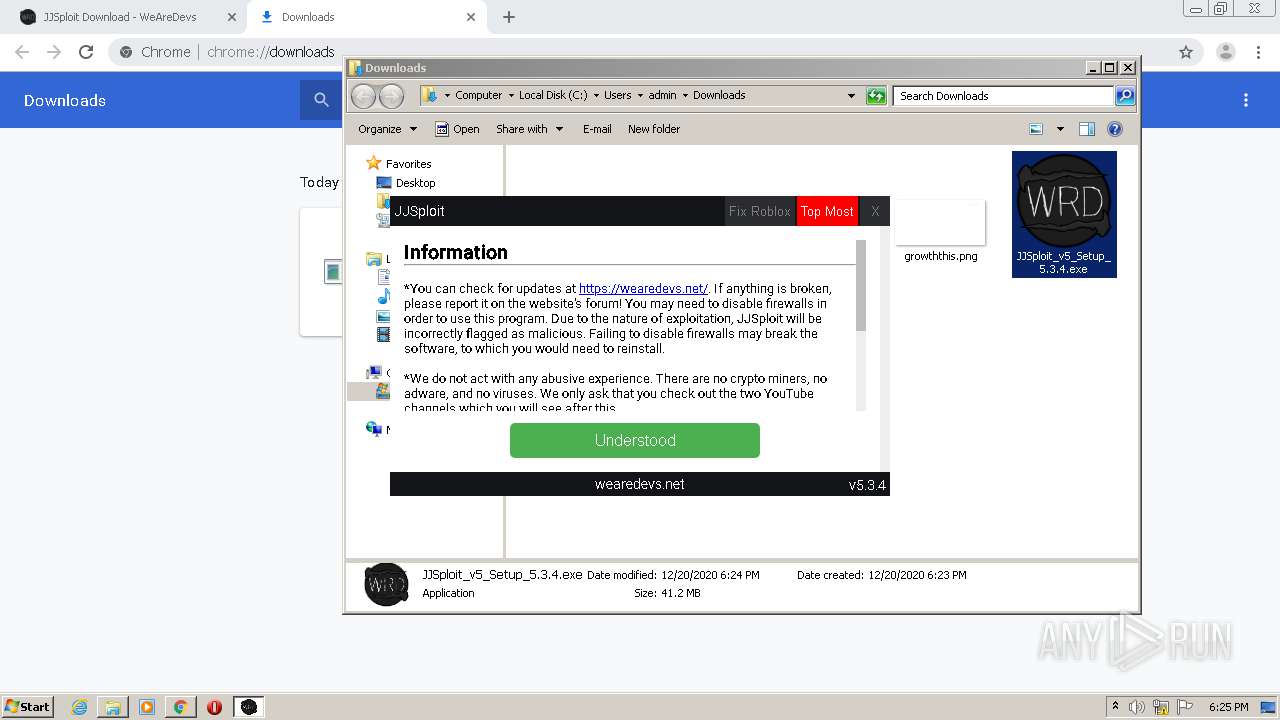
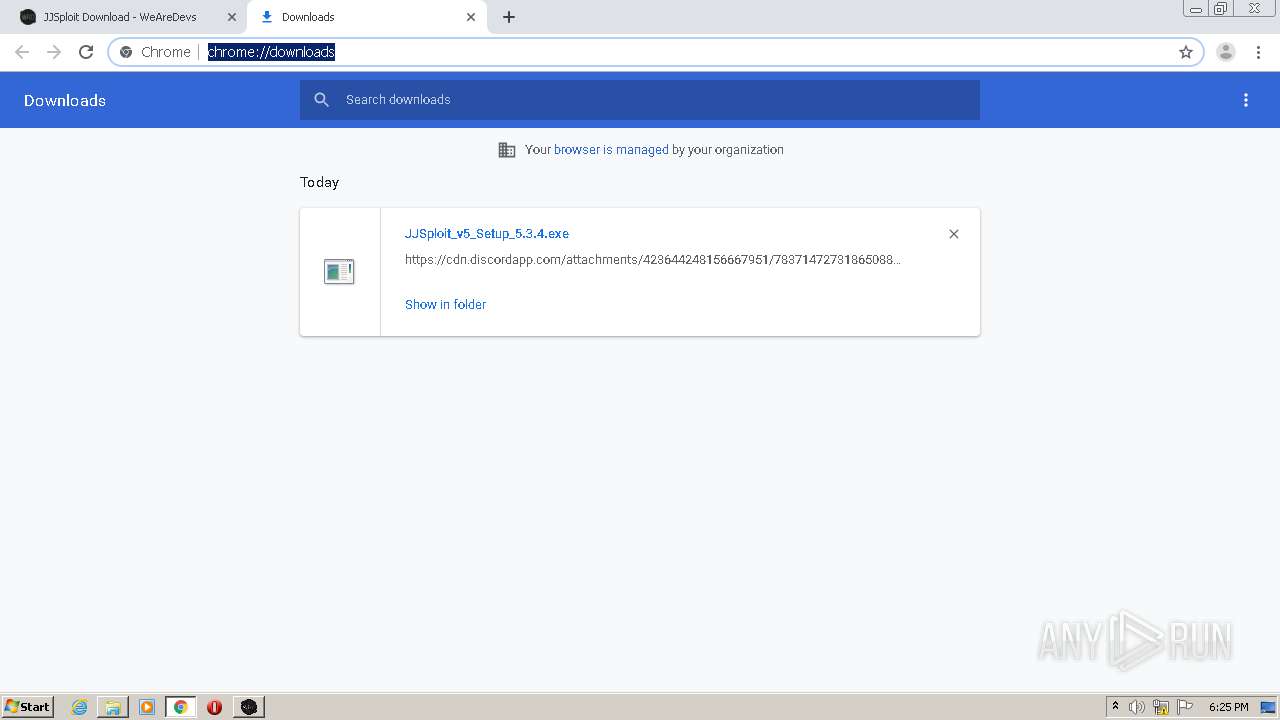
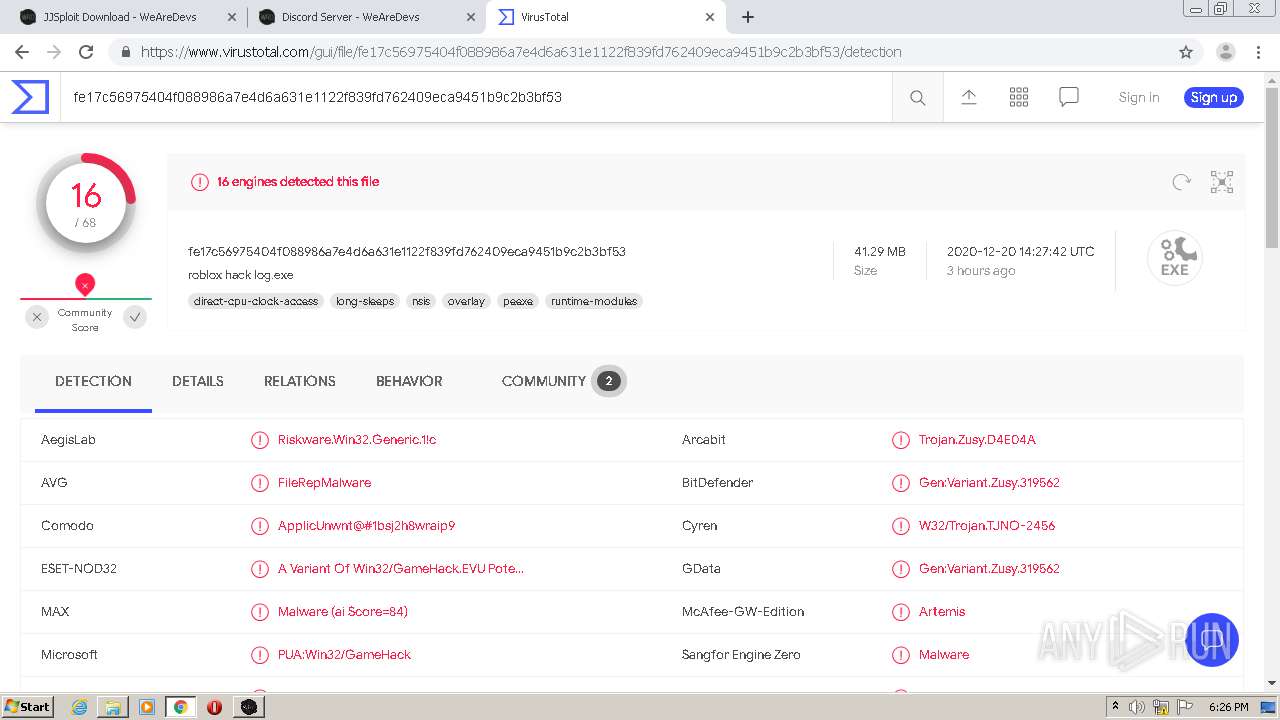
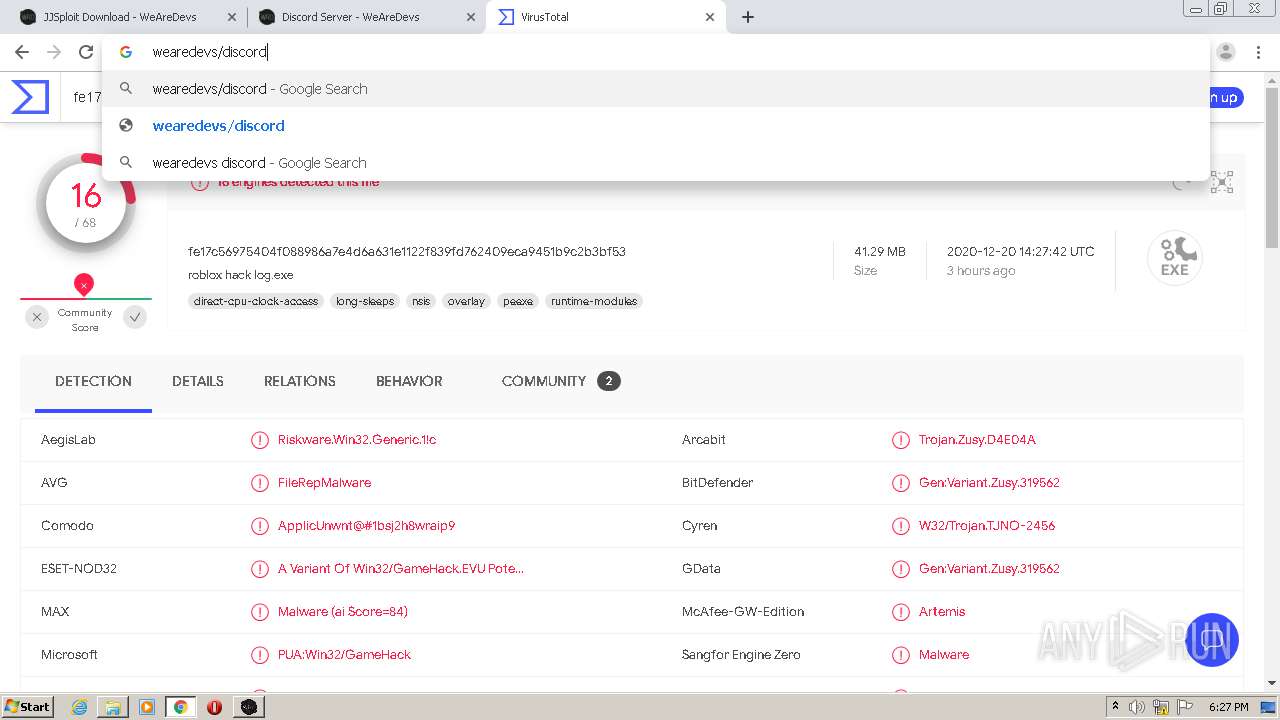
MALICIOUS
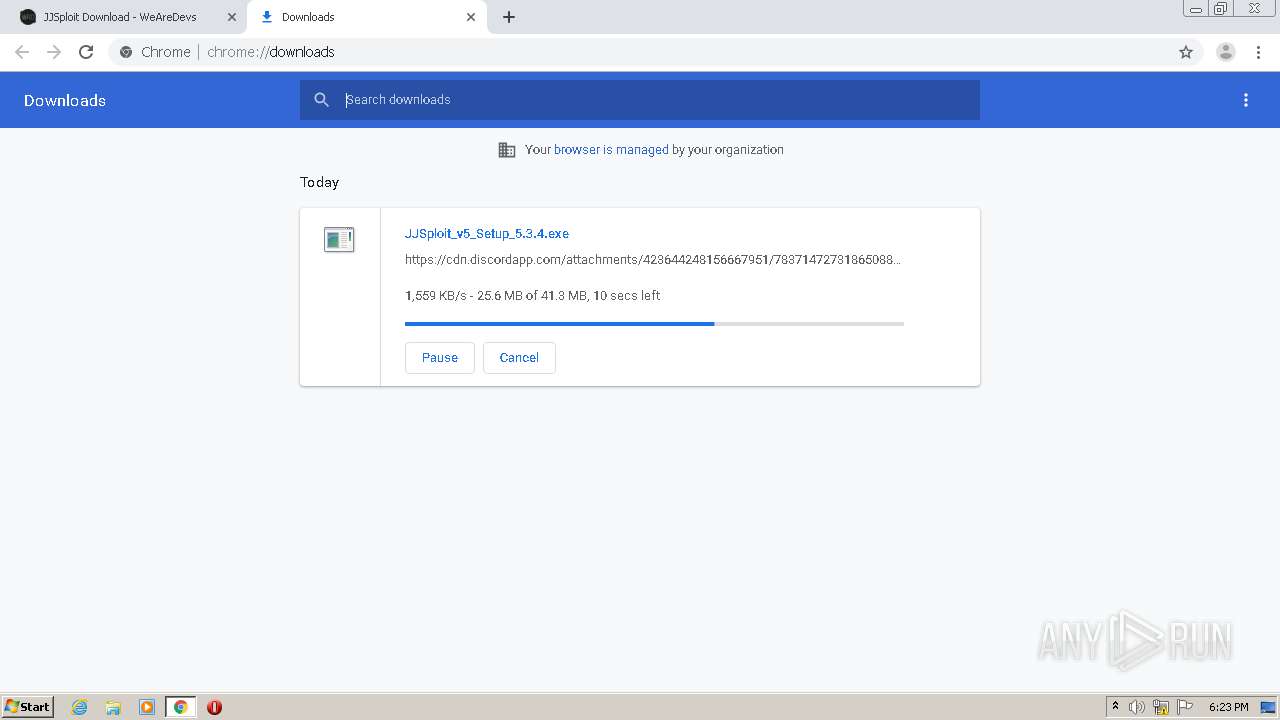
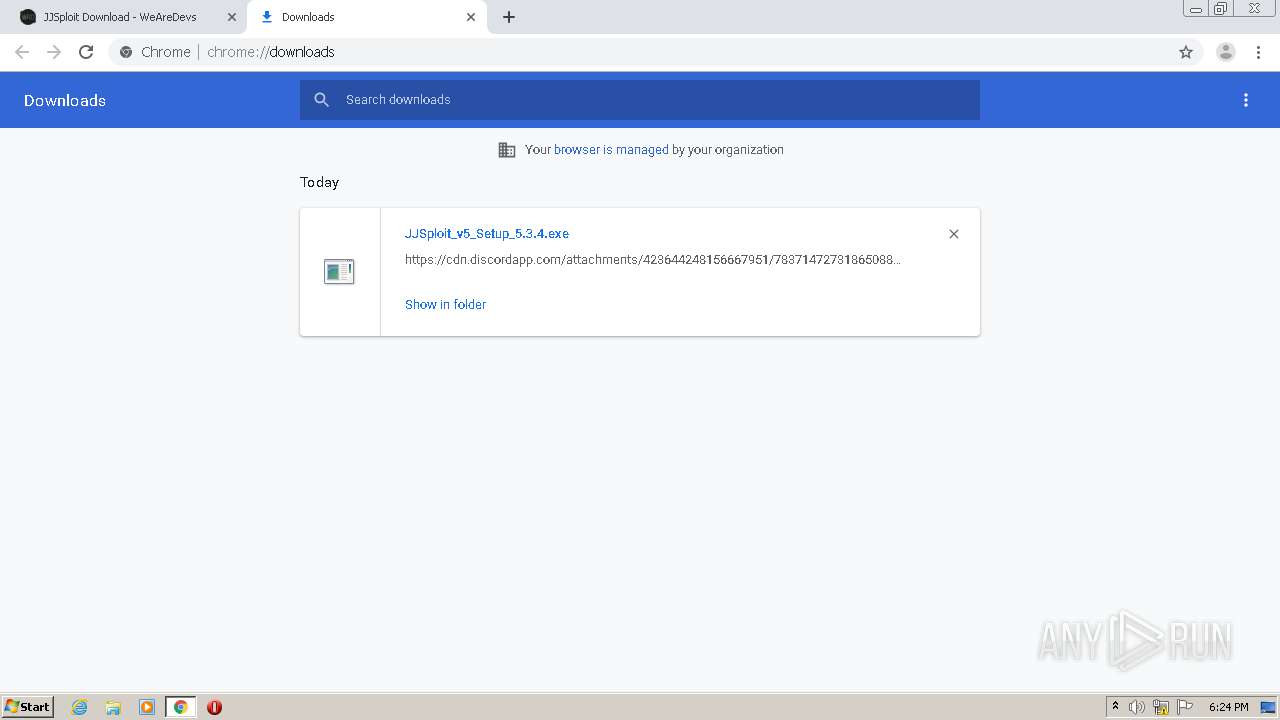
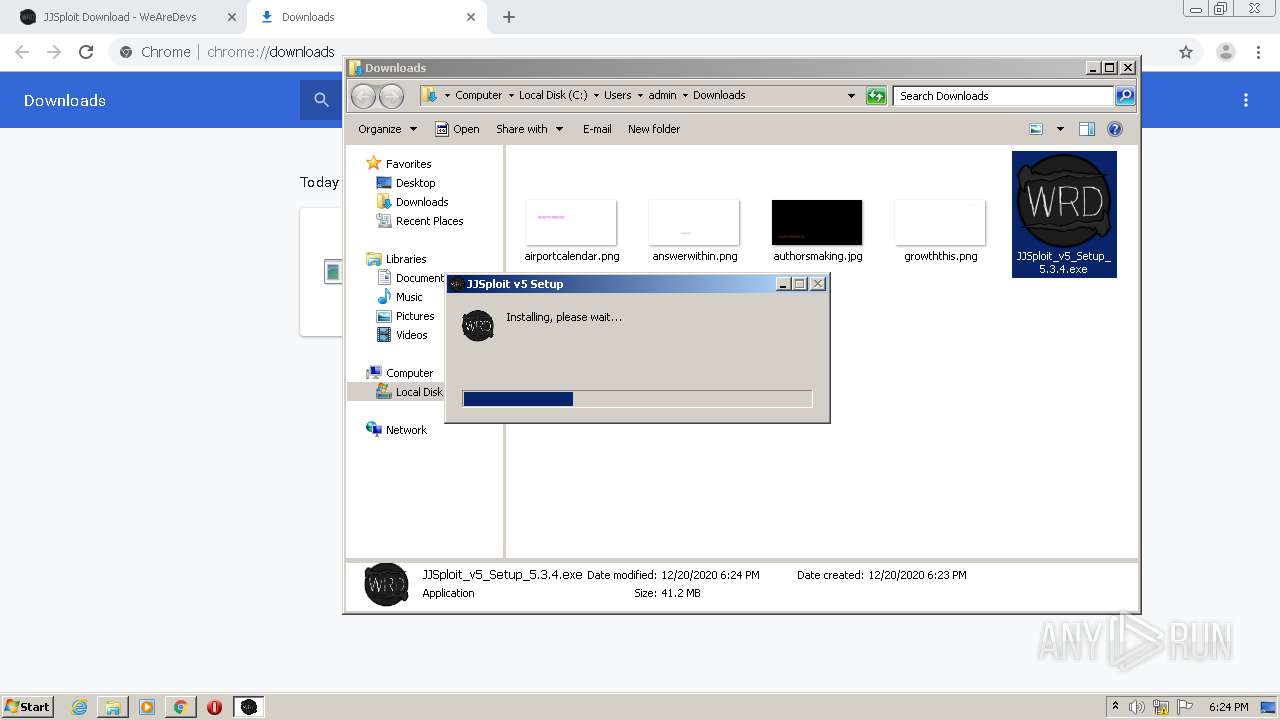
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
- JJSploit v5.exe (PID: 3404)
- JJSploit v5.exe (PID: 2852)
- JJSploit v5.exe (PID: 3372)
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
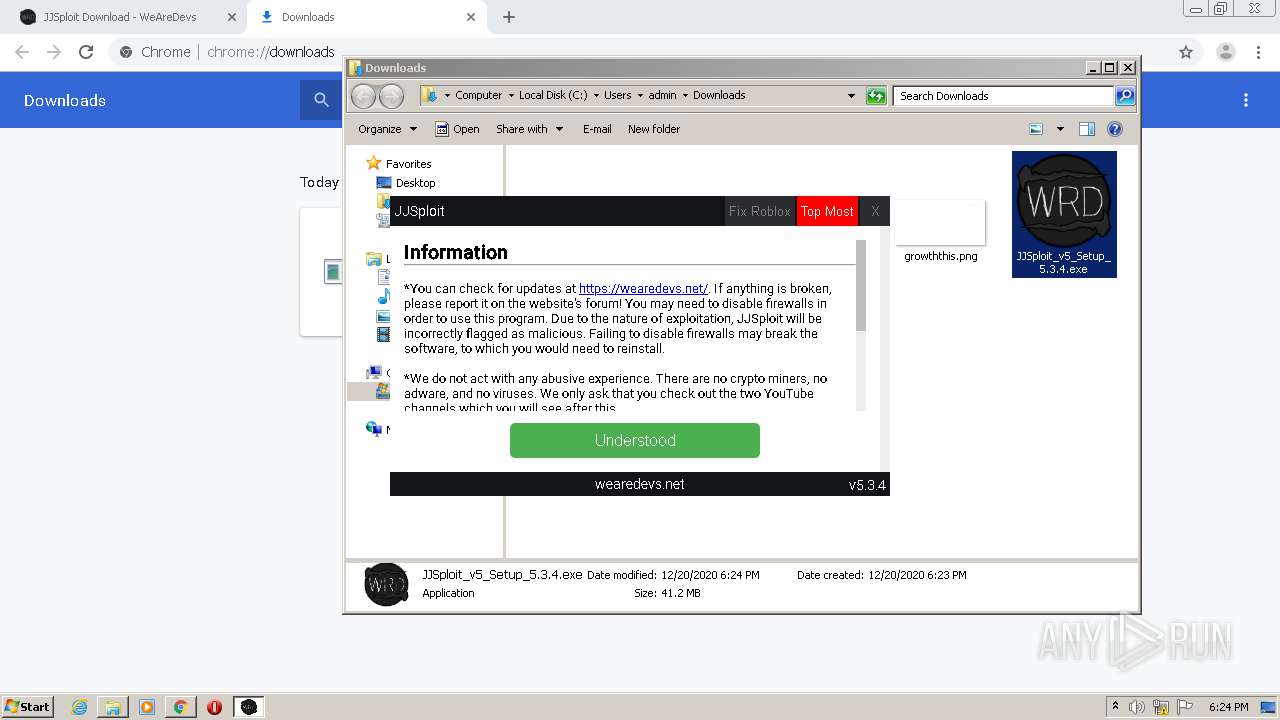
SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 2648)
- JJSploit v5.exe (PID: 3404)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
- JJSploit v5.exe (PID: 3404)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
- JJSploit v5.exe (PID: 3404)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
Executable content was dropped or overwritten
- JJSploit v5.exe (PID: 3404)
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
- chrome.exe (PID: 2648)
Application launched itself
- JJSploit v5.exe (PID: 3404)
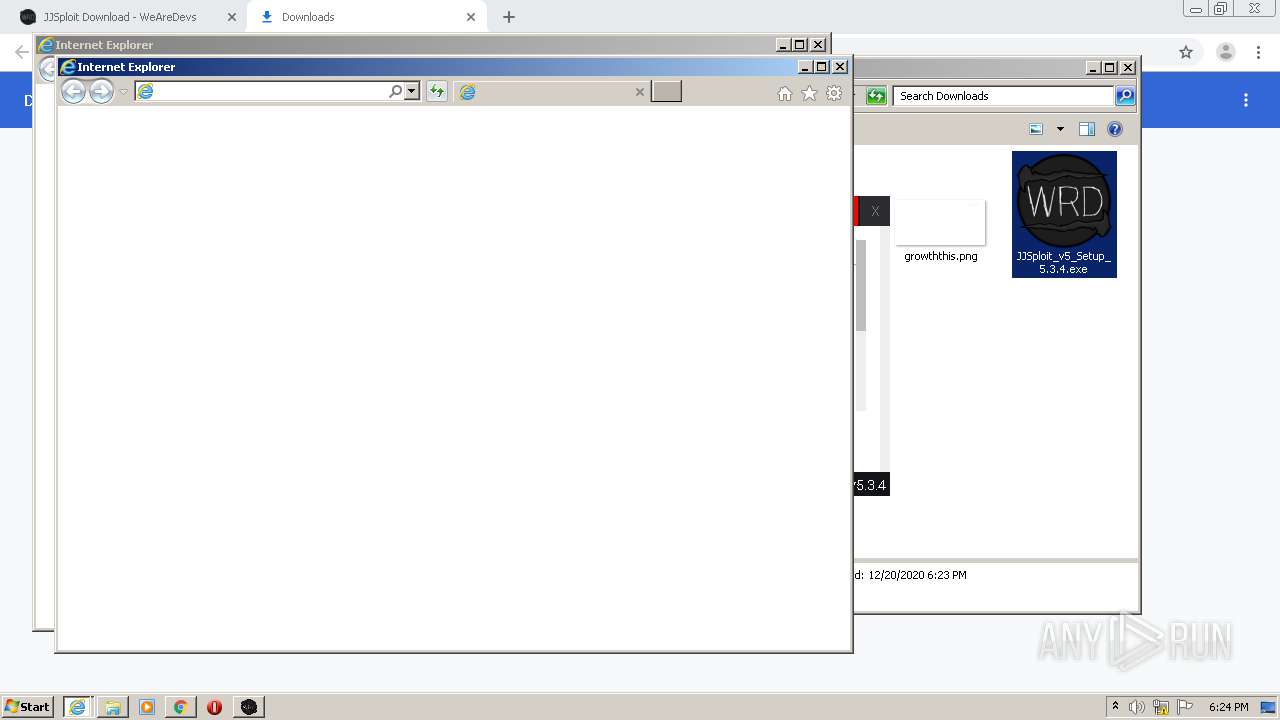
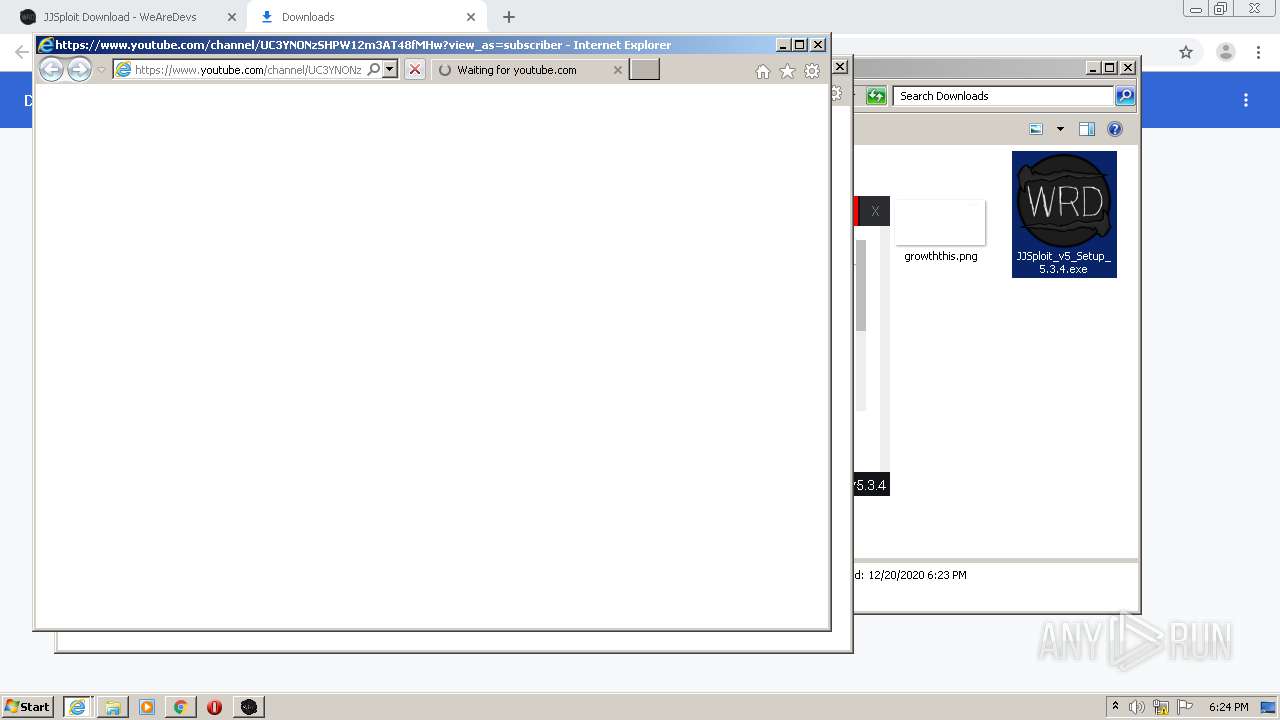
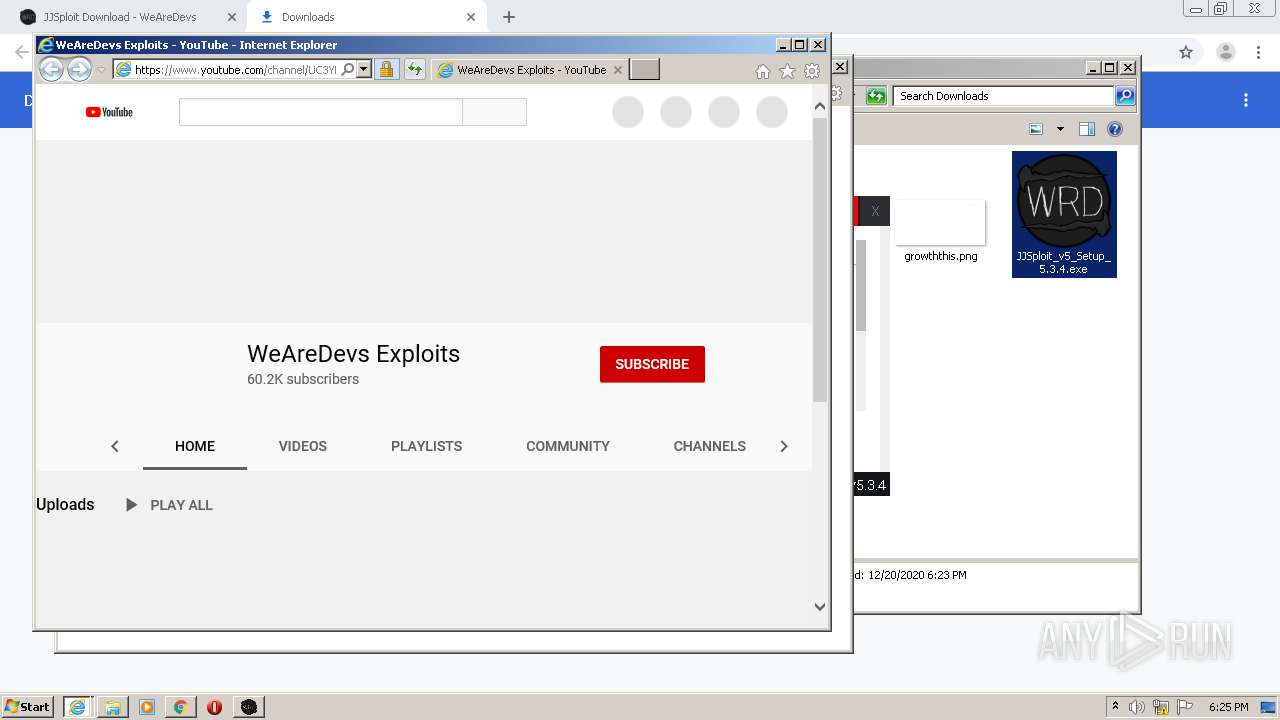
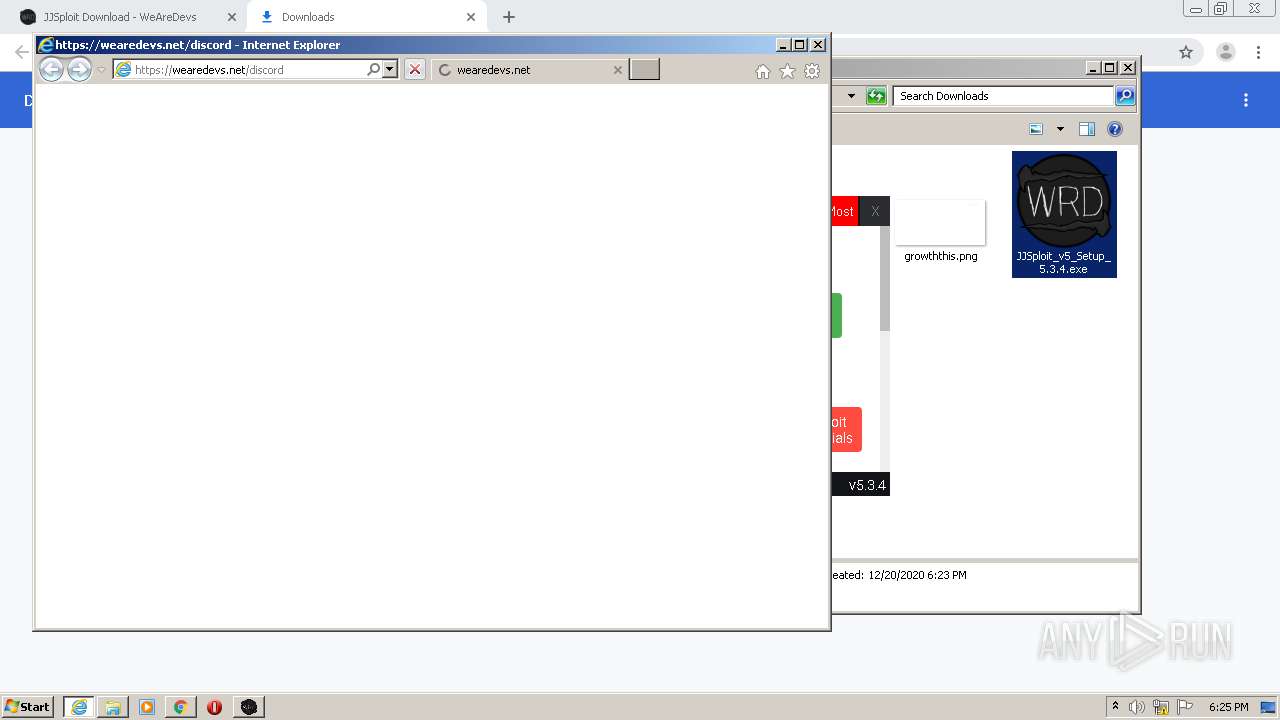
Starts Internet Explorer
- JJSploit v5.exe (PID: 3404)
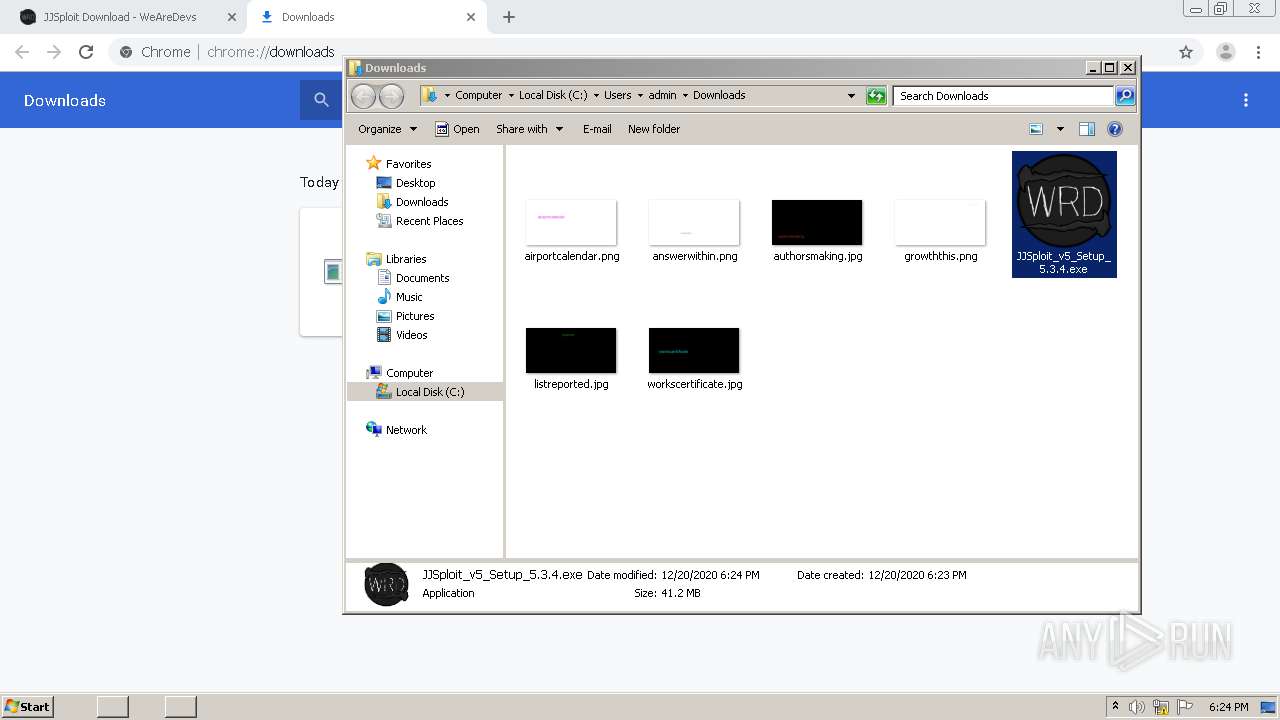
INFO
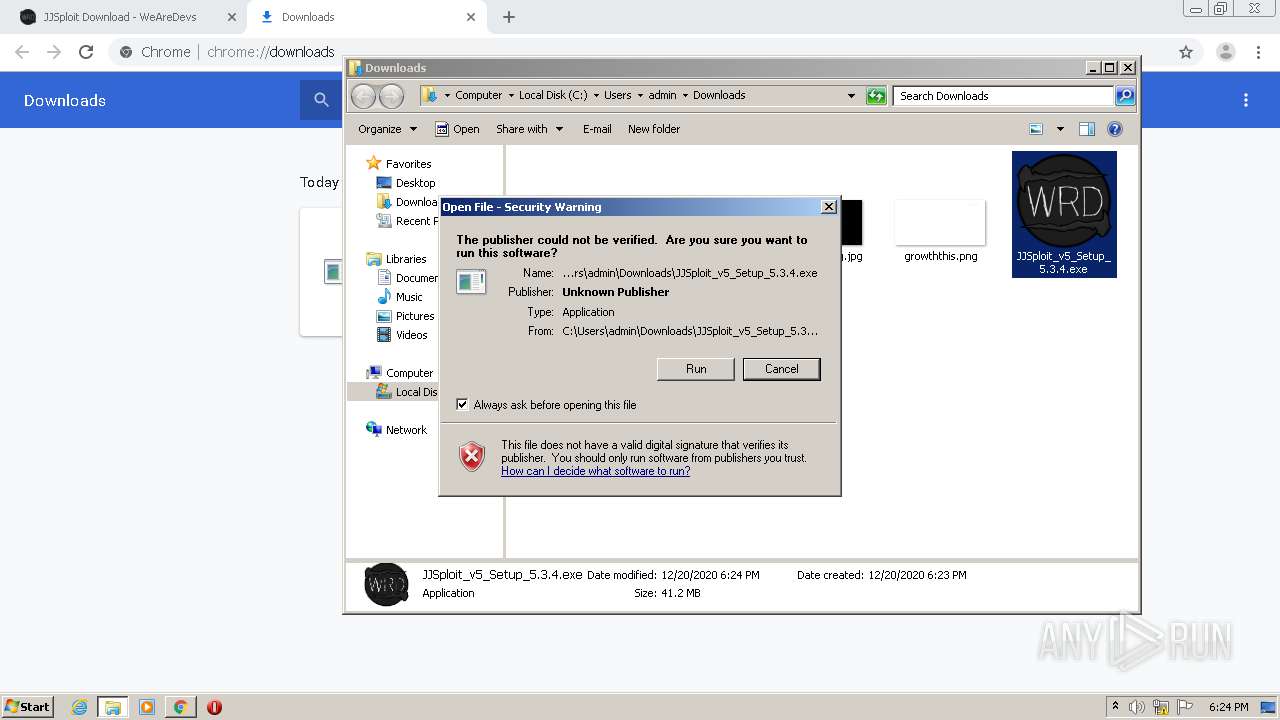
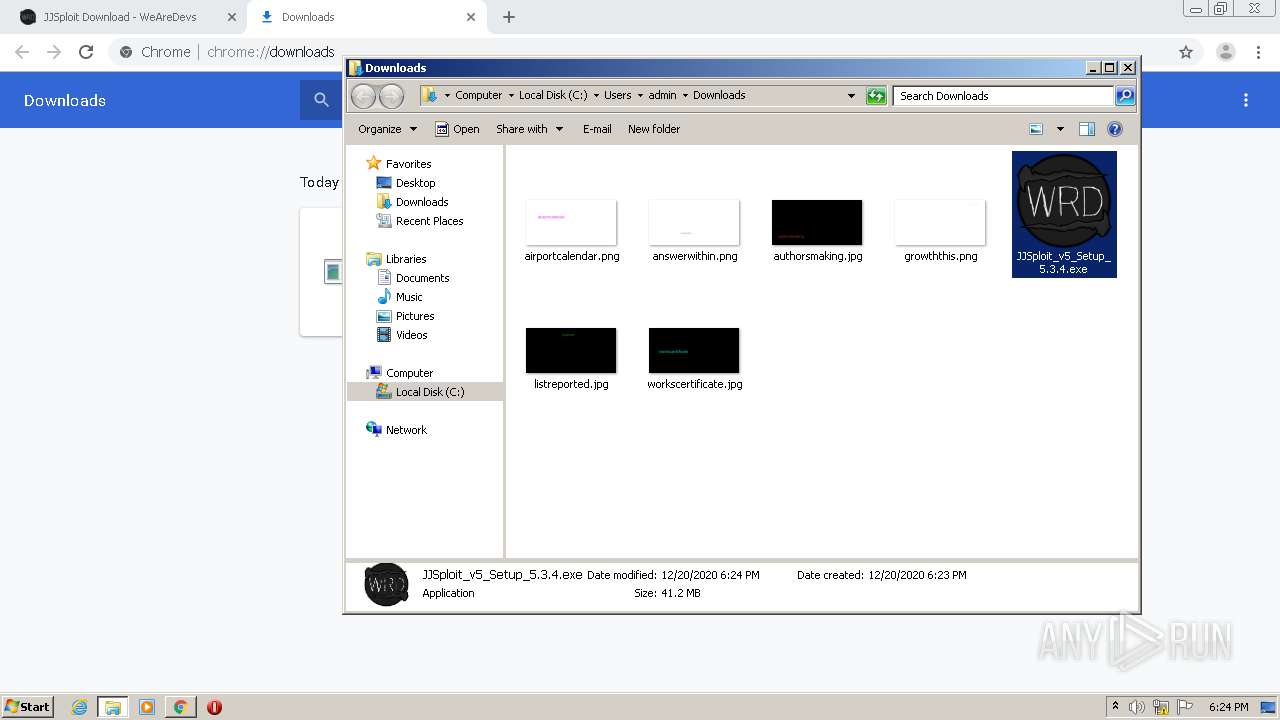
Manual execution by user
- JJSploit v5.exe (PID: 3404)
- JJSploit_v5_Setup_5.3.4.exe (PID: 3548)
Reads the hosts file
- JJSploit v5.exe (PID: 3404)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 2648)
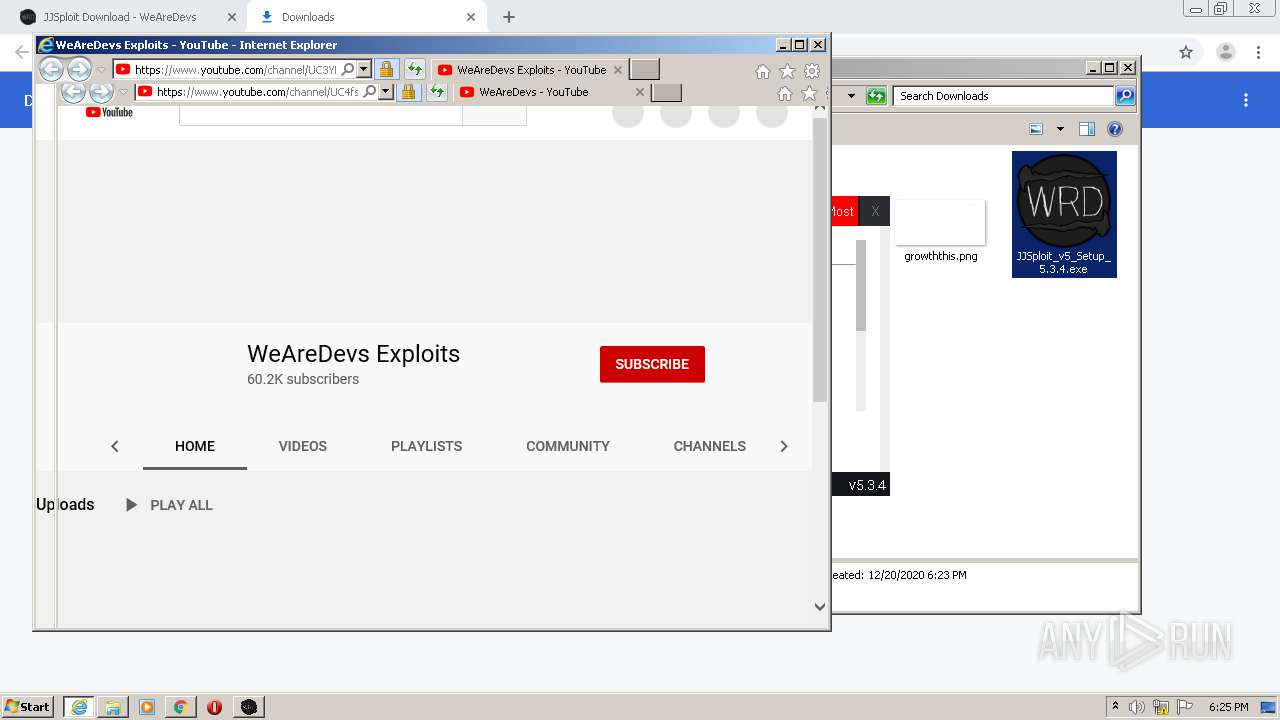
Application launched itself
- chrome.exe (PID: 2648)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 776)
- iexplore.exe (PID: 1120)
Changes internet zones settings
- iexplore.exe (PID: 776)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 1120)
Reads settings of System Certificates
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 776)
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 1120)
Creates files in the user directory
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 1120)
Reads internet explorer settings
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 4076)
Changes settings of System certificates
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 776)
- iexplore.exe (PID: 1120)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2996)
- iexplore.exe (PID: 776)
- iexplore.exe (PID: 1120)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
40
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10291186527166803120 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC3YNONzSHPW12m3AT48fMHw?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16081609806059319182 --mojo-platform-channel-handle=4192 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2138431458527633106 --mojo-platform-channel-handle=3832 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2592 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
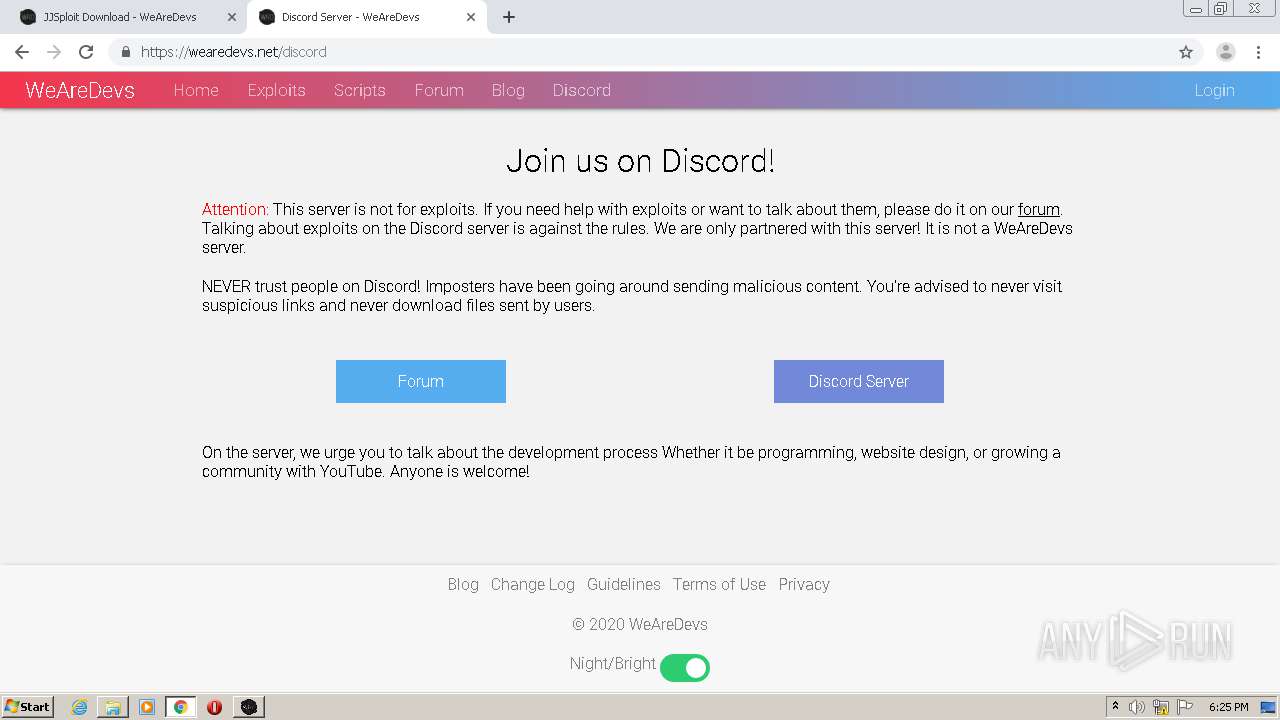
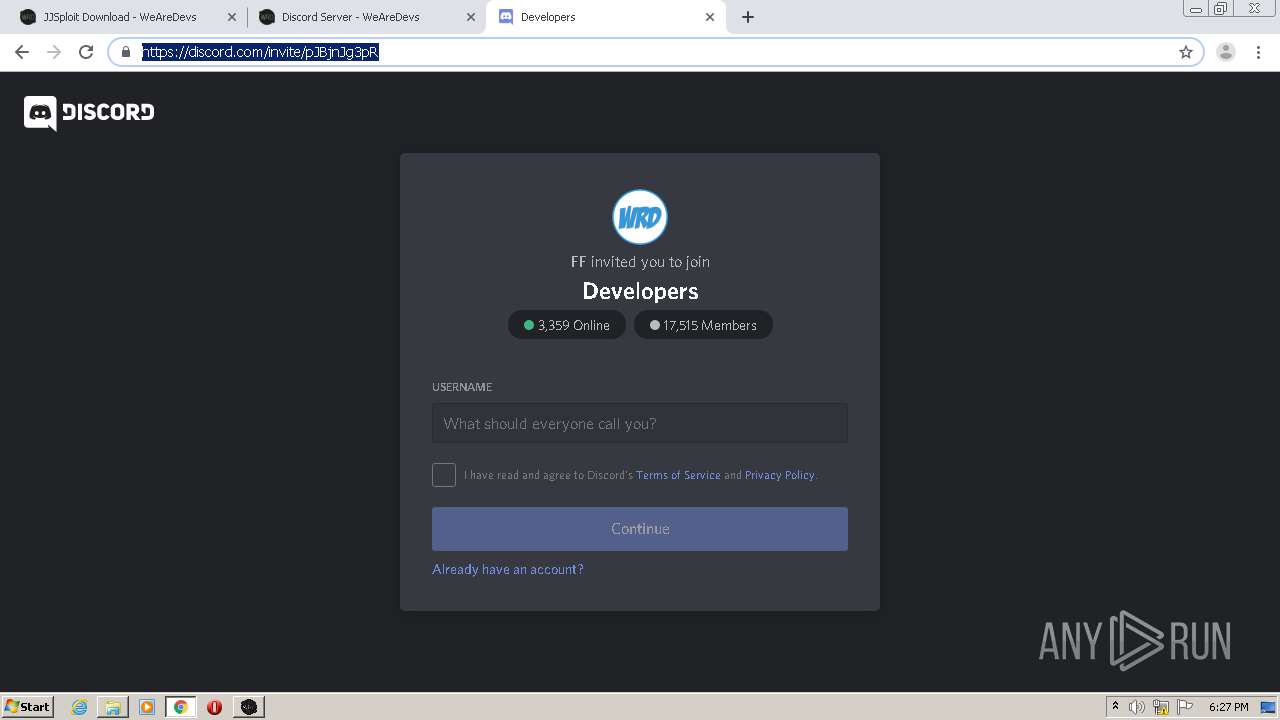
| 1120 | "C:\Program Files\Internet Explorer\iexplore.exe" https://wearedevs.net/discord | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16599501283100579128 --mojo-platform-channel-handle=4608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8531707950377453206 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8567720574778183381 --mojo-platform-channel-handle=4432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14353797170519788044,5115308045278217354,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18236661356094389504 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 874
Read events
4 341
Write events
519
Delete events
14
Modification events
| (PID) Process: | (1092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2648-13252962215708500 |
Value: 259 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2648) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
21
Suspicious files
170
Text files
174
Unknown types
107
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FDF96A8-A58.pma | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4a3dd3a9-37e7-407d-a425-b8d7afa30f9c.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1504fb.TMP | text | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF150549.TMP | text | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1506c0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
140
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCi%2BuKU1GfA0wUAAAAAfosl | US | der | 472 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCi%2BuKU1GfA0wUAAAAAfosl | US | der | 472 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYLJWXOOilPwUAAAAAfozF | US | der | 472 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYLJWXOOilPwUAAAAAfozF | US | der | 472 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEG5DGLjXkBZcAwAAAAC624o%3D | US | der | 471 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDcESu58tA7KQMAAAAAutv8 | US | der | 472 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYLJWXOOilPwUAAAAAfozF | US | der | 472 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDcESu58tA7KQMAAAAAutv8 | US | der | 472 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCi%2BuKU1GfA0wUAAAAAfosl | US | der | 472 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYLJWXOOilPwUAAAAAfozF | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1708 | chrome.exe | 172.217.5.237:443 | accounts.google.com | Google Inc. | US | unknown |
1708 | chrome.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
1708 | chrome.exe | 142.250.73.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.21.226:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.13.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.21.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
— | — | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
1708 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.22.34:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |