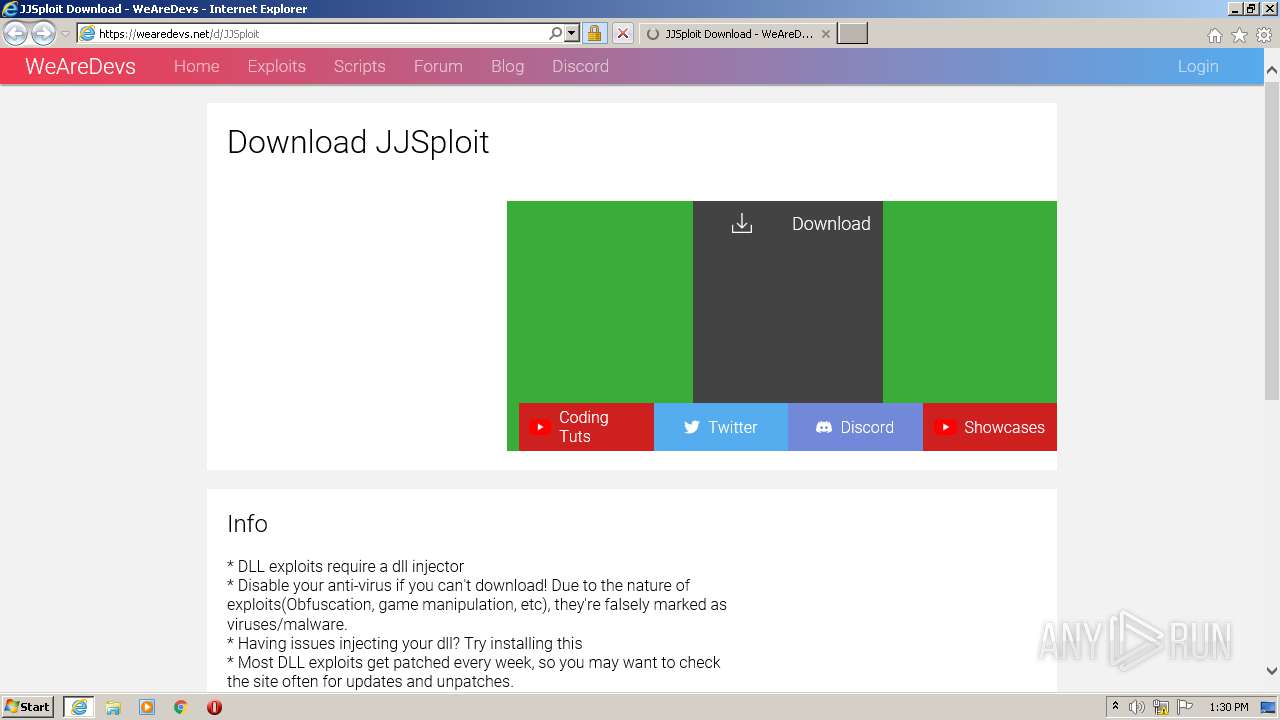
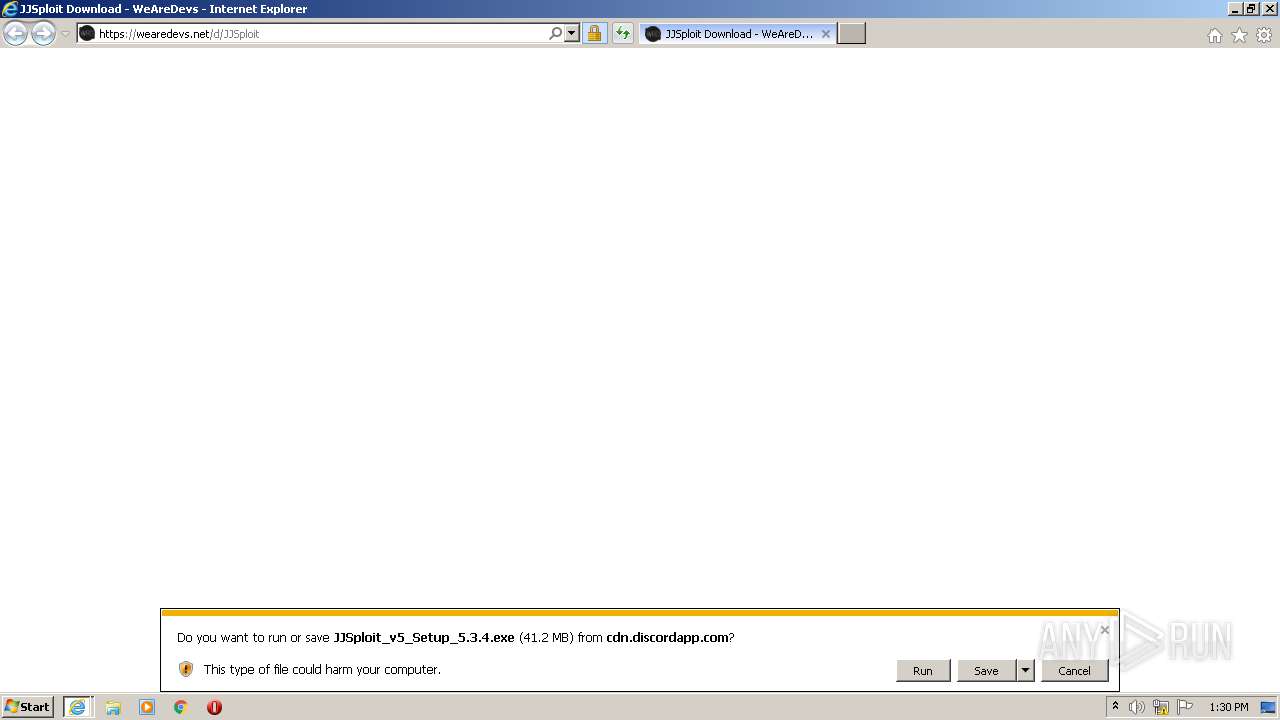
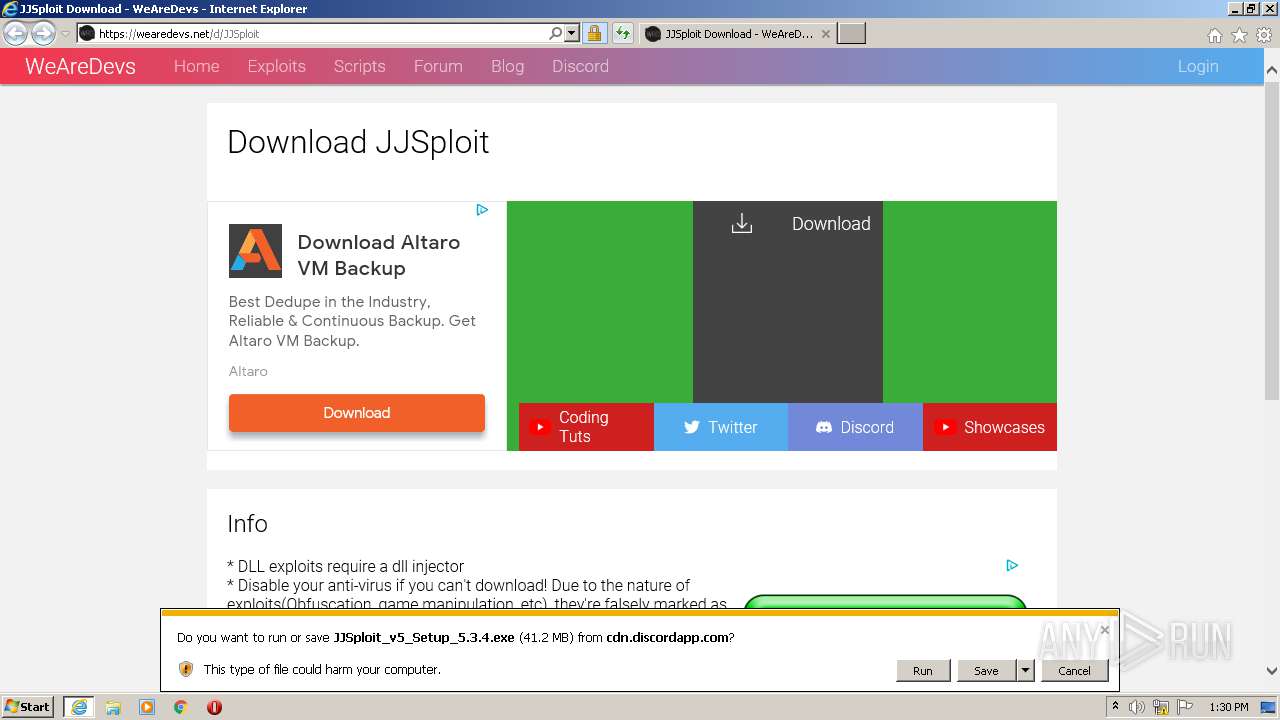
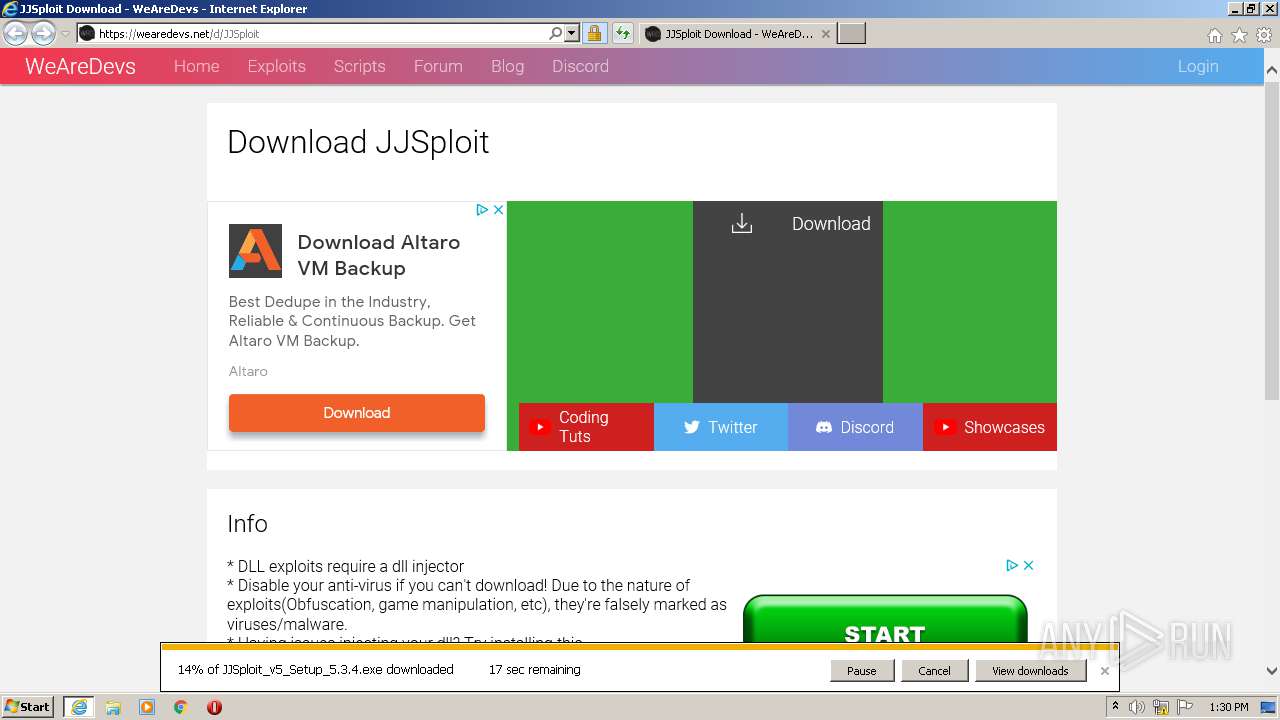
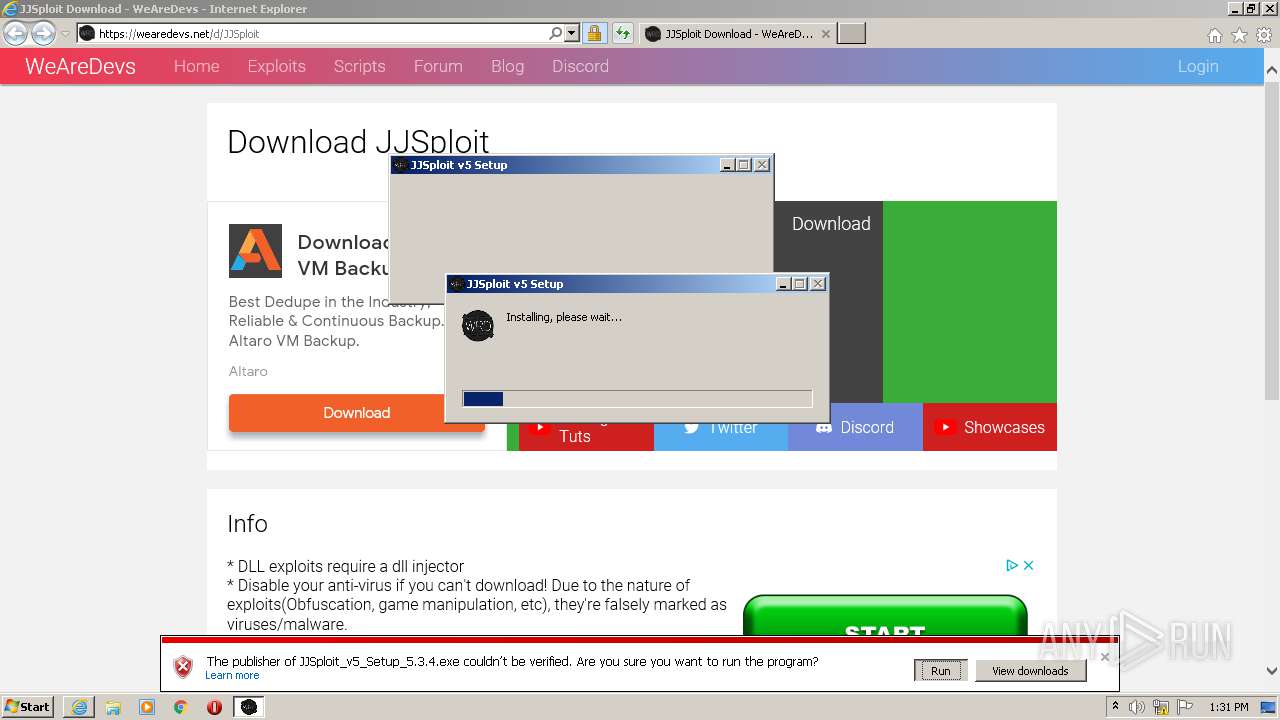
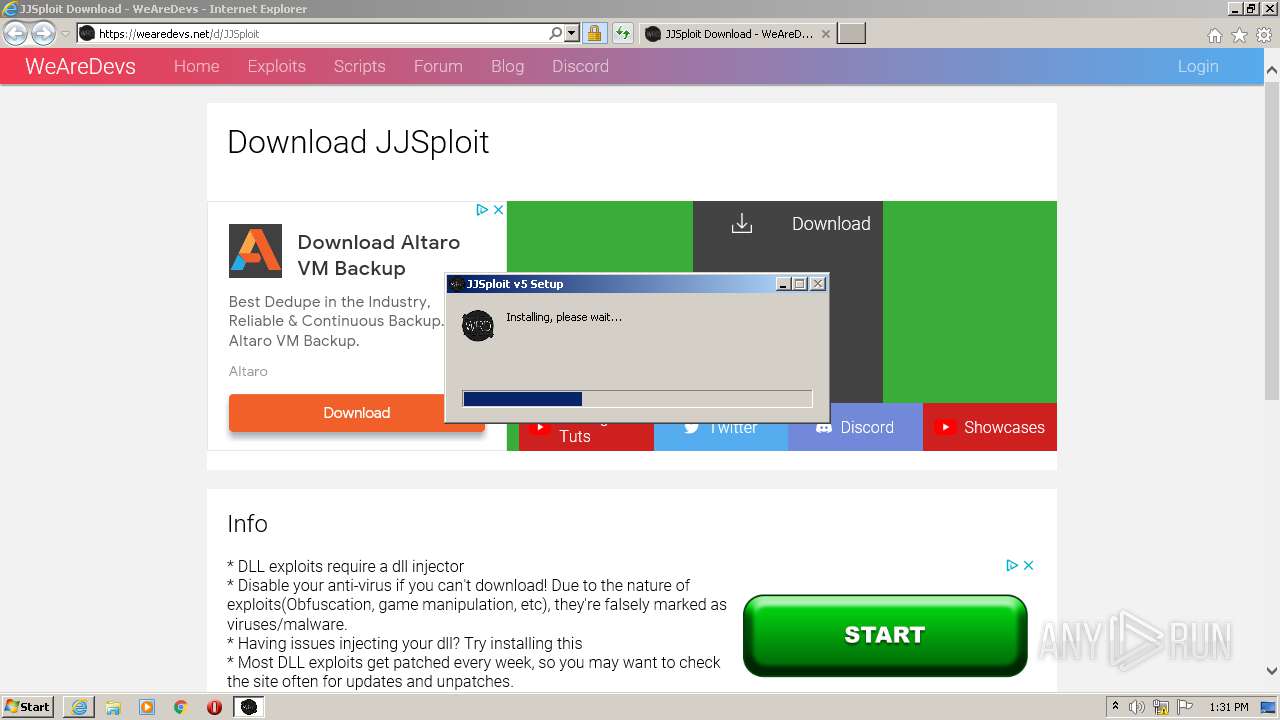
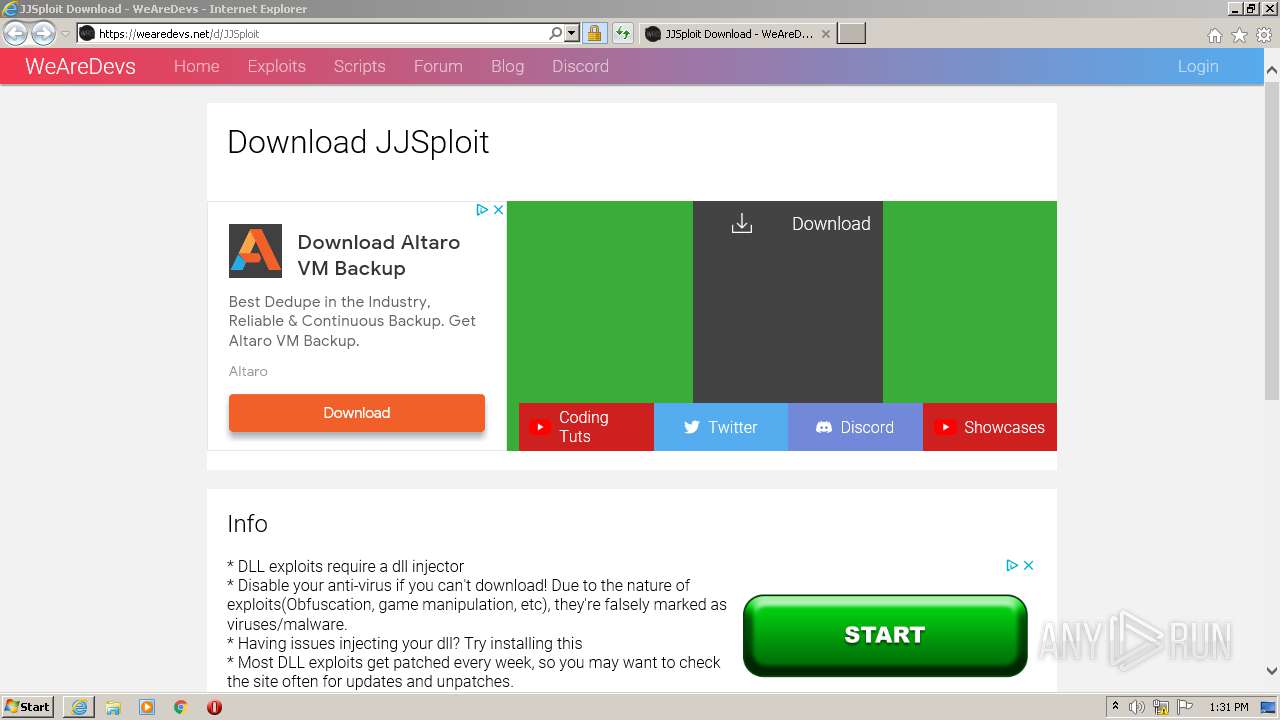
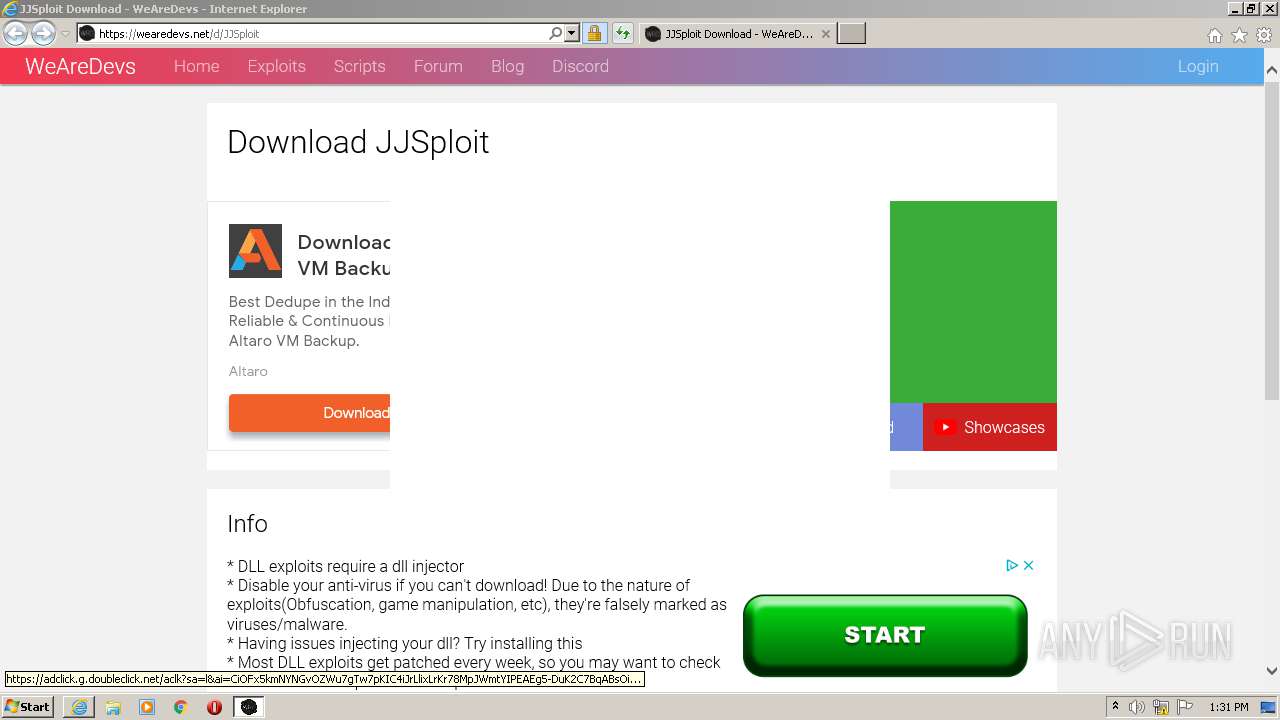
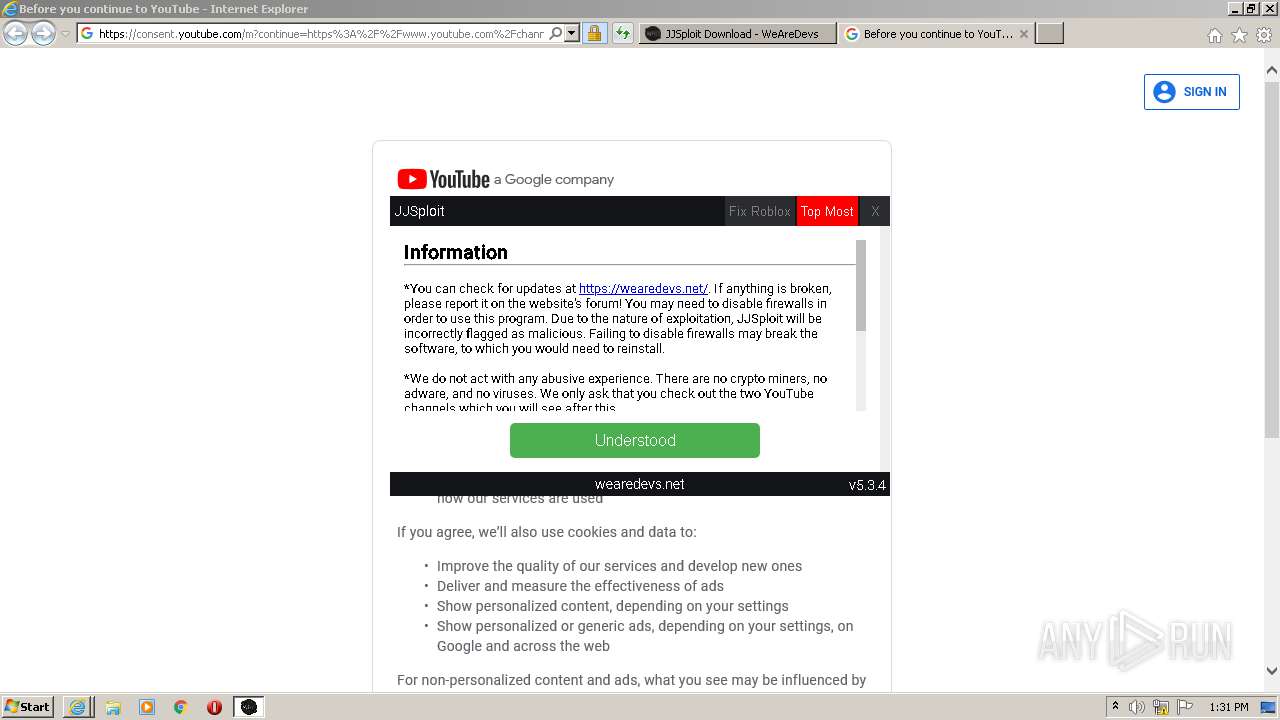
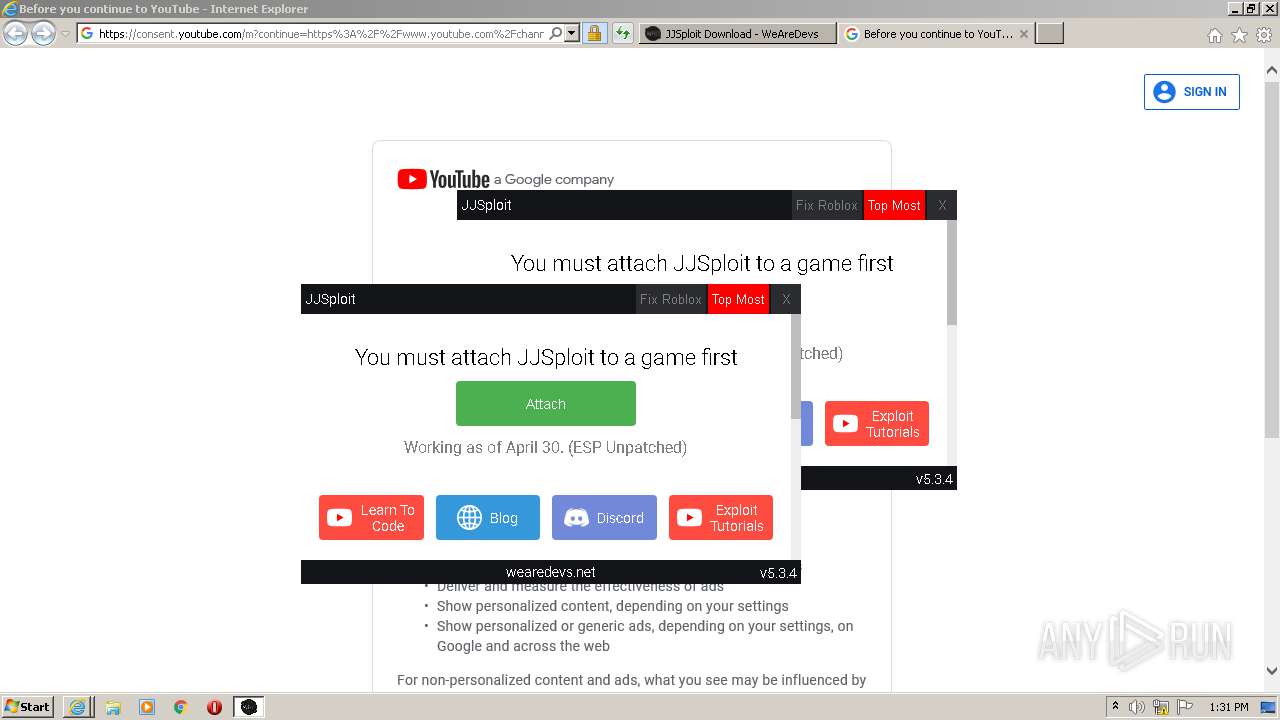
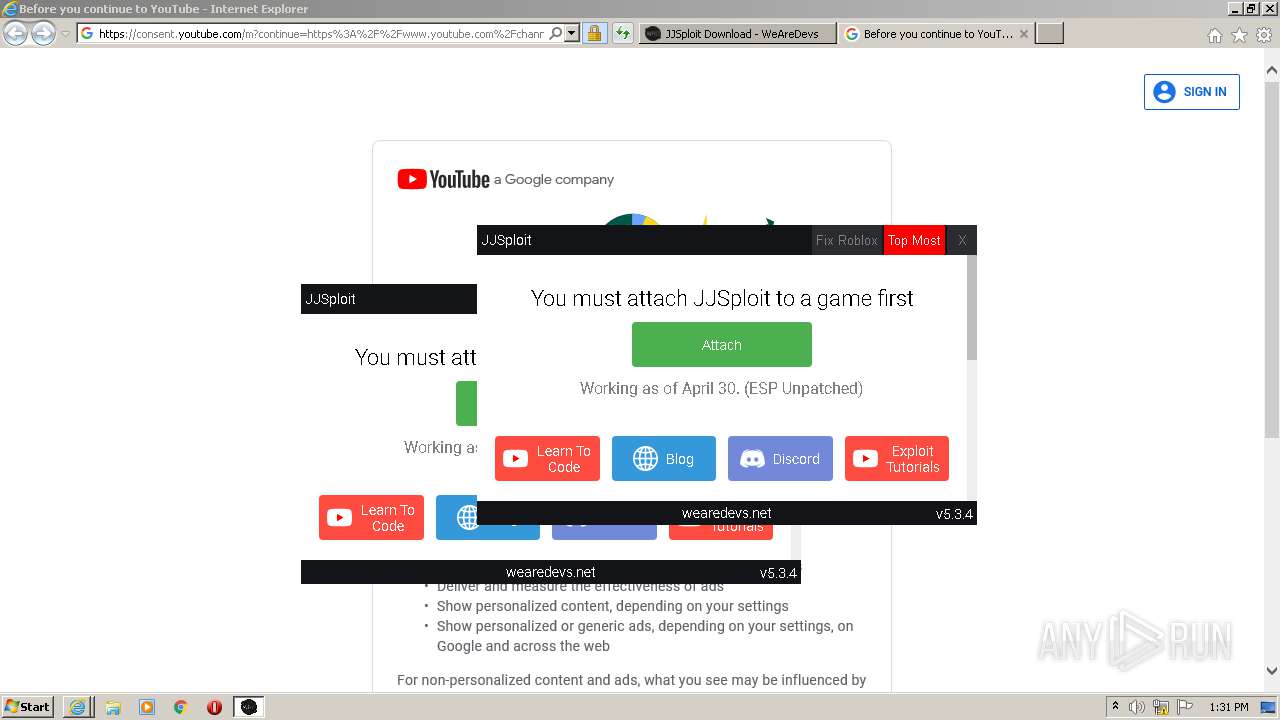
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/303688f5-55fd-443e-80ea-96cef4e59b15 |
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2021, 12:30:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
MALICIOUS
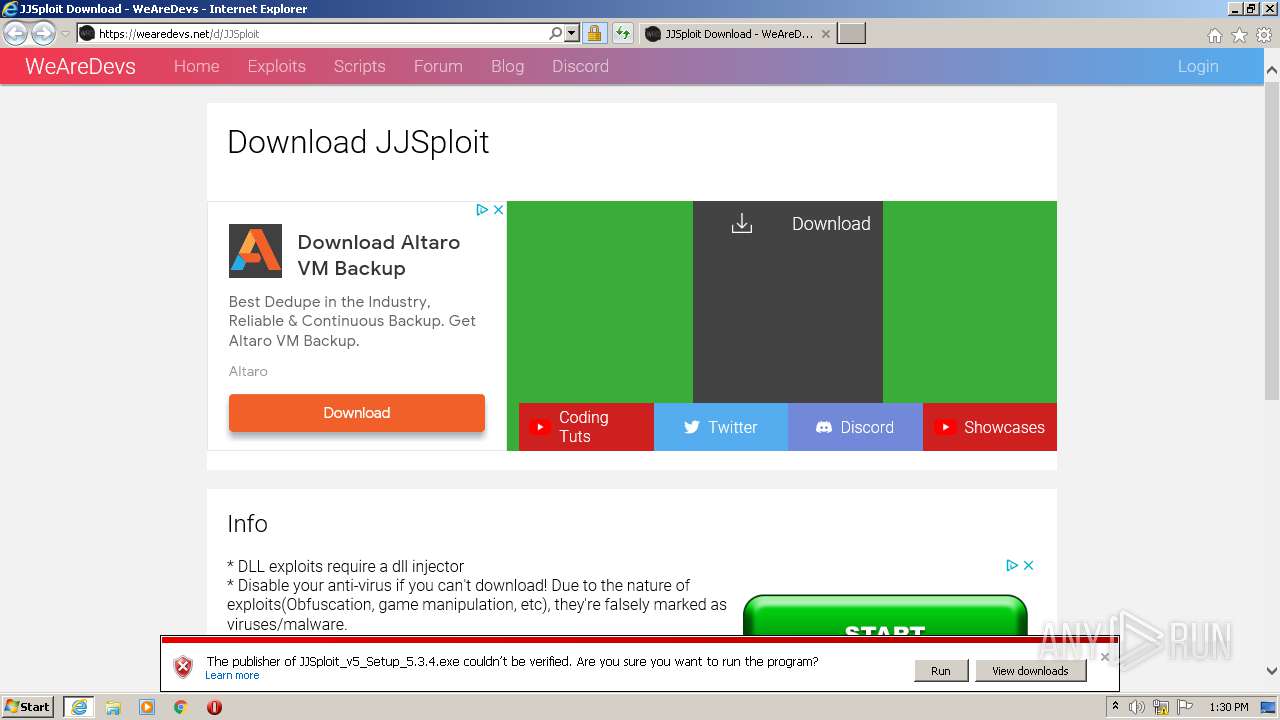
Drops executable file immediately after starts
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
- JJSploit v5.exe (PID: 3196)
- JJSploit v5.exe (PID: 2260)
- JJSploit v5.exe (PID: 1464)
SUSPICIOUS
Executable content was dropped or overwritten
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
- JJSploit v5.exe (PID: 3196)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
- JJSploit v5.exe (PID: 3196)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 668)
- JJSploit v5.exe (PID: 3196)
Drops a file with a compile date too recent
- JJSploit v5.exe (PID: 3196)
Application launched itself
- JJSploit v5.exe (PID: 3196)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1632)
Reads settings of System Certificates
- iexplore.exe (PID: 1632)
Changes settings of System certificates
- iexplore.exe (PID: 1632)
Creates files in the user directory
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 1632)
- iexplore.exe (PID: 1392)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1632)
Application launched itself
- iexplore.exe (PID: 1632)
Reads internet explorer settings
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 1392)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1632)
Reads the hosts file
- JJSploit v5.exe (PID: 3196)
Manual execution by user
- JJSploit v5.exe (PID: 3196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JJSploit_v5_Setup_5.3.4.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JJSploit_v5_Setup_5.3.4.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1632 CREDAT:3544349 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=renderer --disable-features=SpareRendererForSitePerProcess --service-pipe-token=4319071087767134910 --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar\build\preload.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4319071087767134910 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1556 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://wearedevs.net/d/JJSploit" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18379595200261804771 --mojo-platform-channel-handle=1160 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 3260 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1632 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3488 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3284411050737028218 --mojo-platform-channel-handle=2420 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
Total events
1 661
Read events
1 419
Write events
238
Delete events
4
Modification events
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3604053544 | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30883461 | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
18
Suspicious files
91
Text files
102
Unknown types
110
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF04E.tmp | — | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF04F.tmp | — | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\DYI6kXcOcxKbTp9LDOkriR11YHo[1].js | text | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\JJSploit[1].htm | html | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TZHU91LM.txt | text | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\download[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
103
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDvBKQuWMzhNCQAAAABiFes%3D | US | der | 471 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCu4OaM8pepHQMAAAAAy%2FdW | US | der | 472 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXZtUP98pi%2BwkAAAAAYhXq | US | der | 472 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCU0iXXU3ZZIgkAAAAAYhal | US | der | 472 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDtqToB6jJa2wMAAAAAy%2FdX | US | der | 472 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEB4LVgjgb8jnCQAAAABiFe8%3D | US | der | 471 b | whitelisted |
3260 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXZtUP98pi%2BwkAAAAAYhXq | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | iexplore.exe | 172.67.71.2:443 | wearedevs.net | — | US | suspicious |
3260 | iexplore.exe | 172.217.20.2:443 | pagead2.googlesyndication.com | Google Inc. | US | unknown |
3260 | iexplore.exe | 142.250.185.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3260 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3260 | iexplore.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3260 | iexplore.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
3260 | iexplore.exe | 142.250.185.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3260 | iexplore.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3260 | iexplore.exe | 142.250.186.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3260 | iexplore.exe | 172.217.16.130:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |