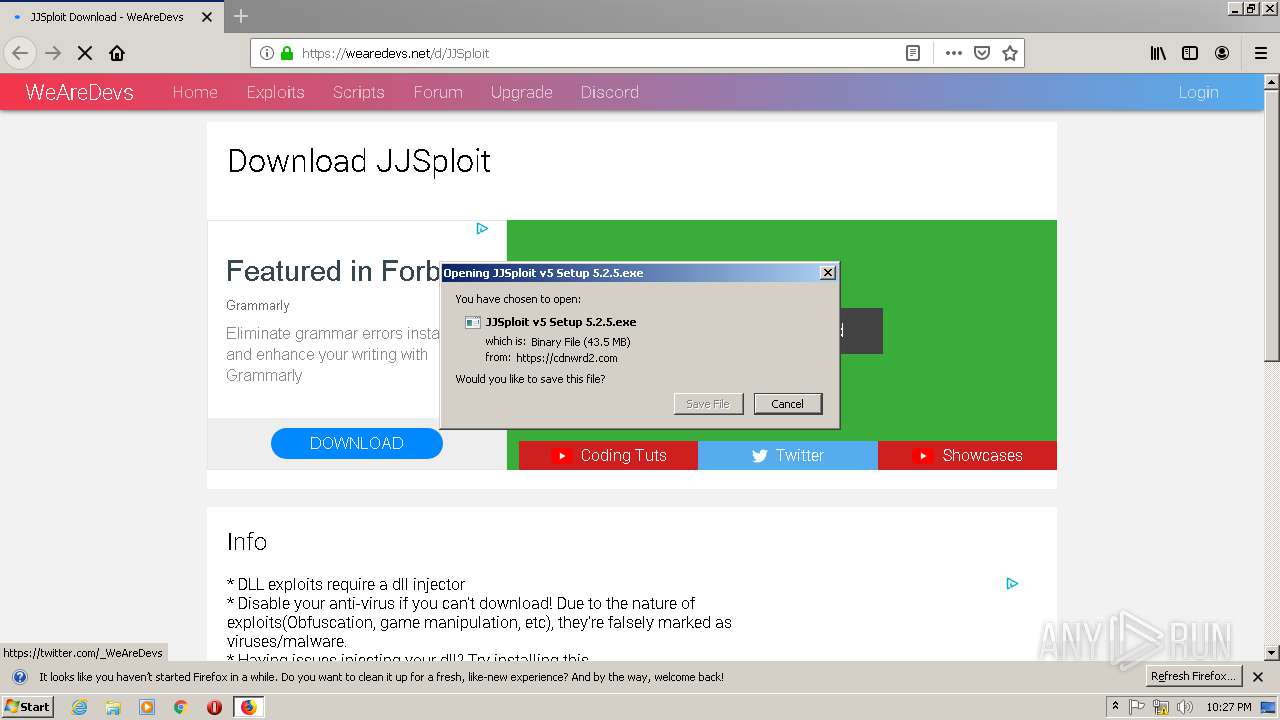
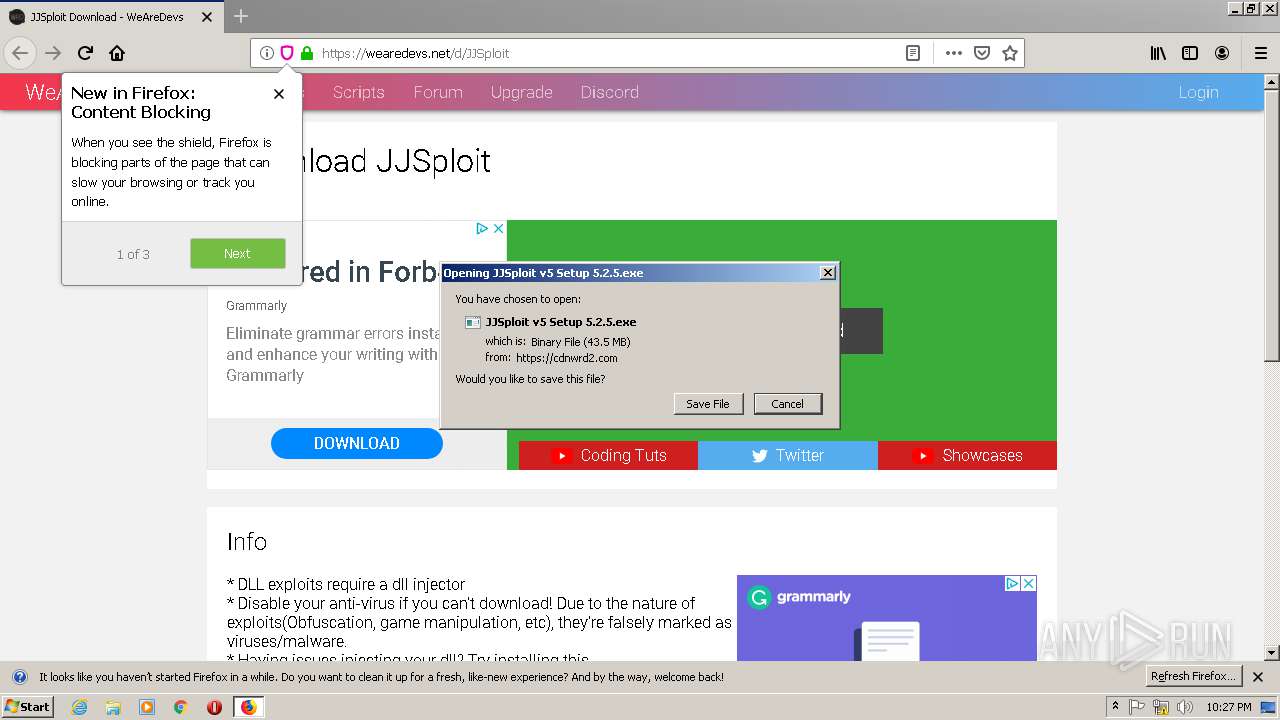
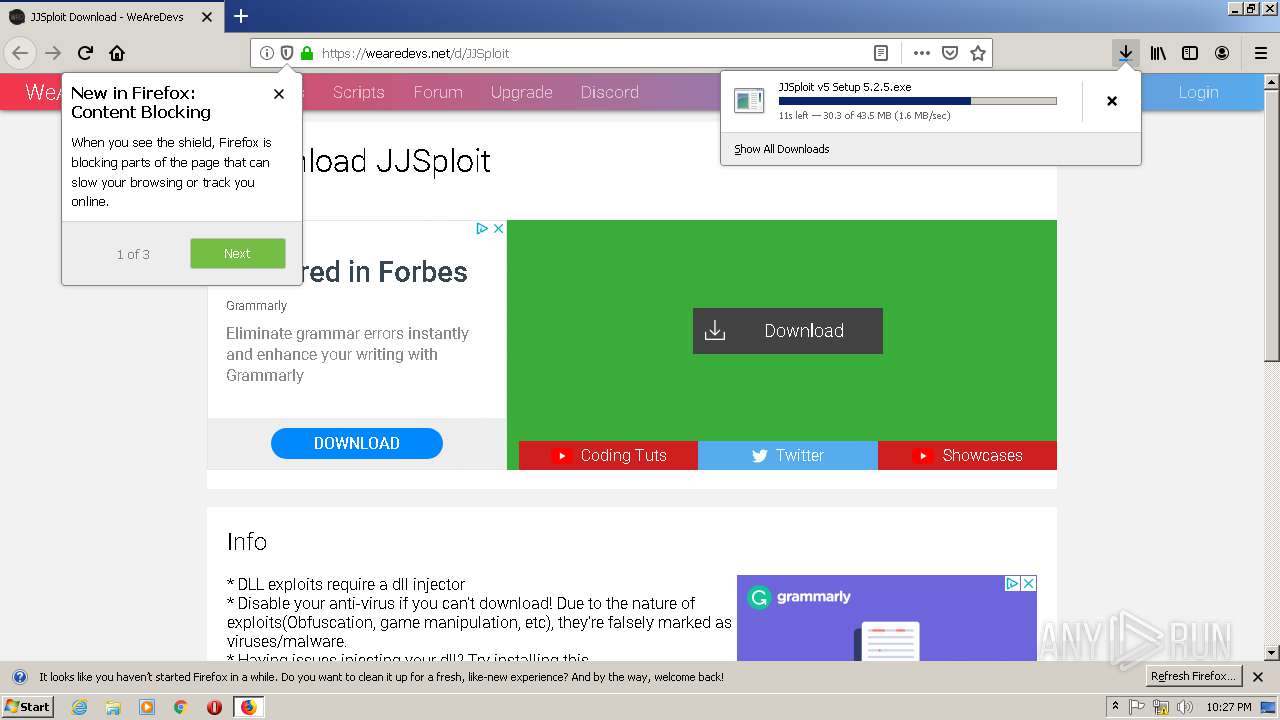
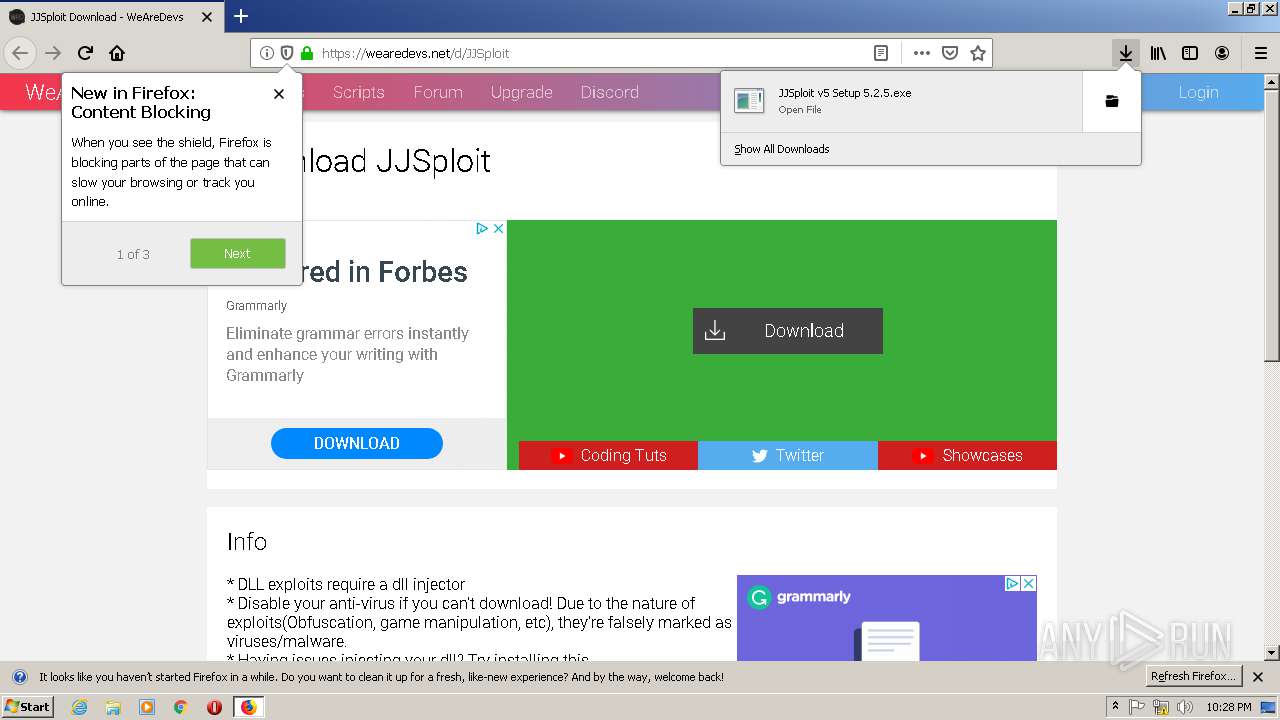
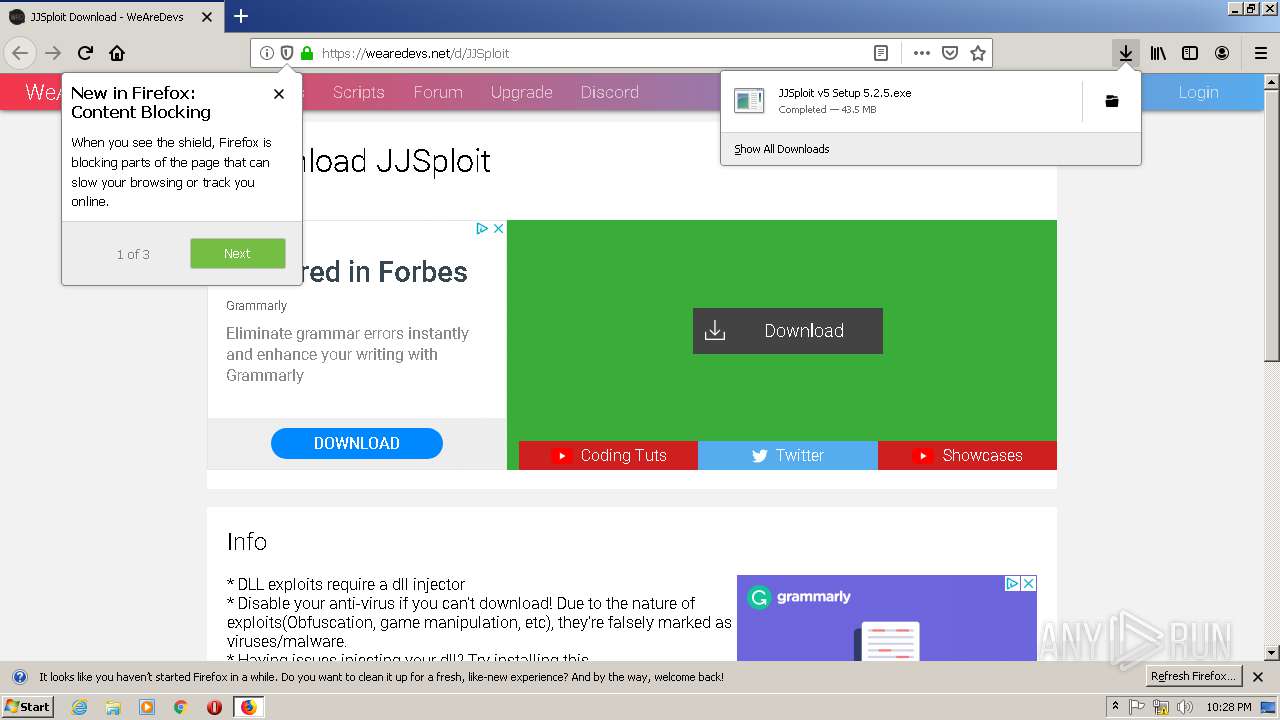
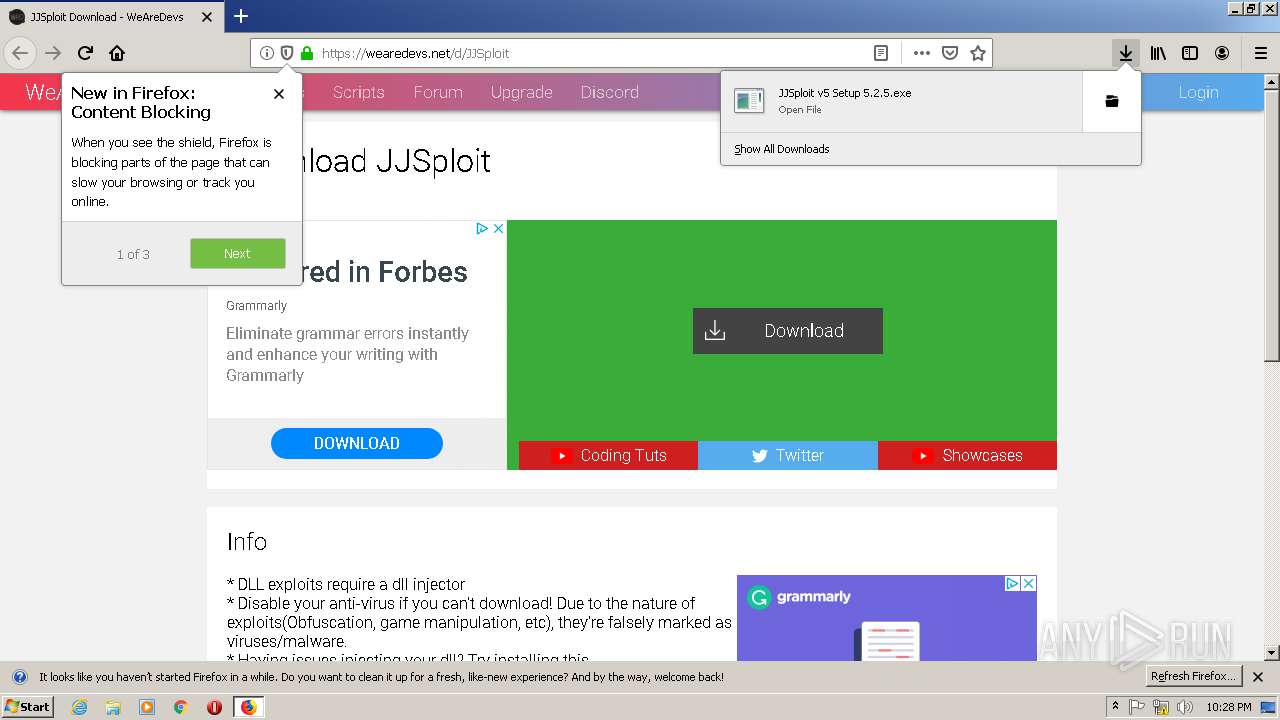
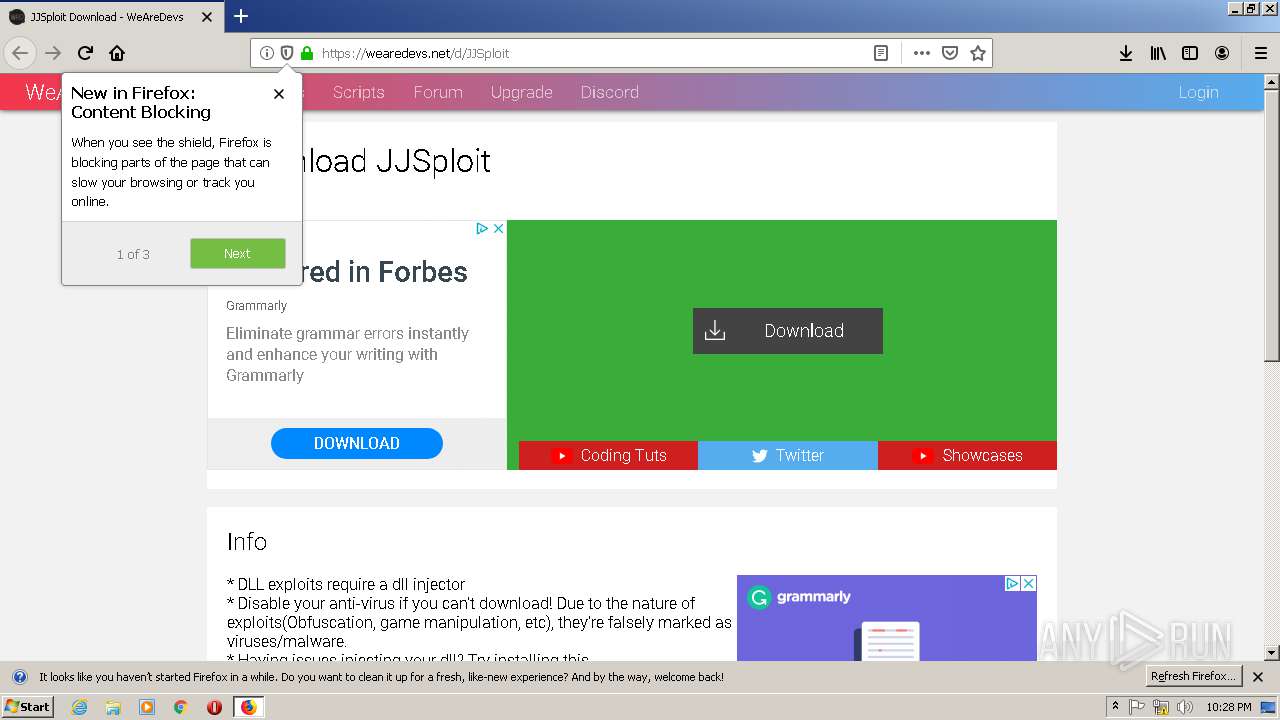
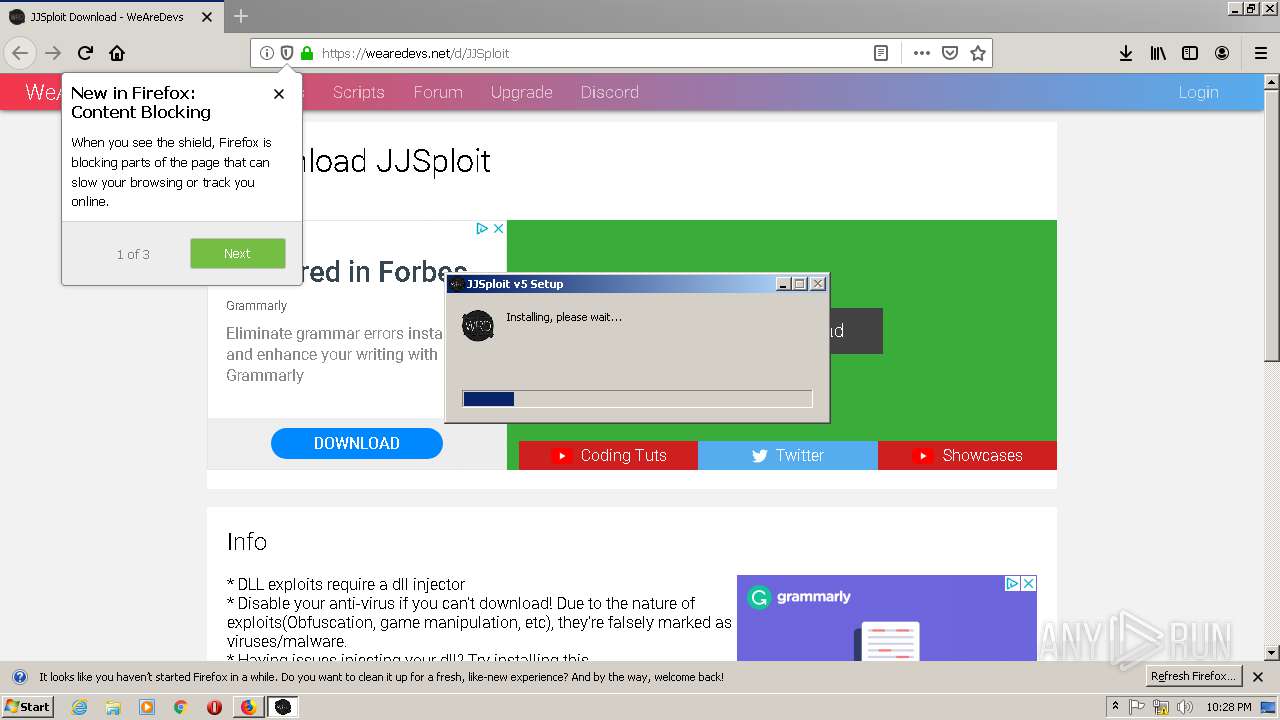
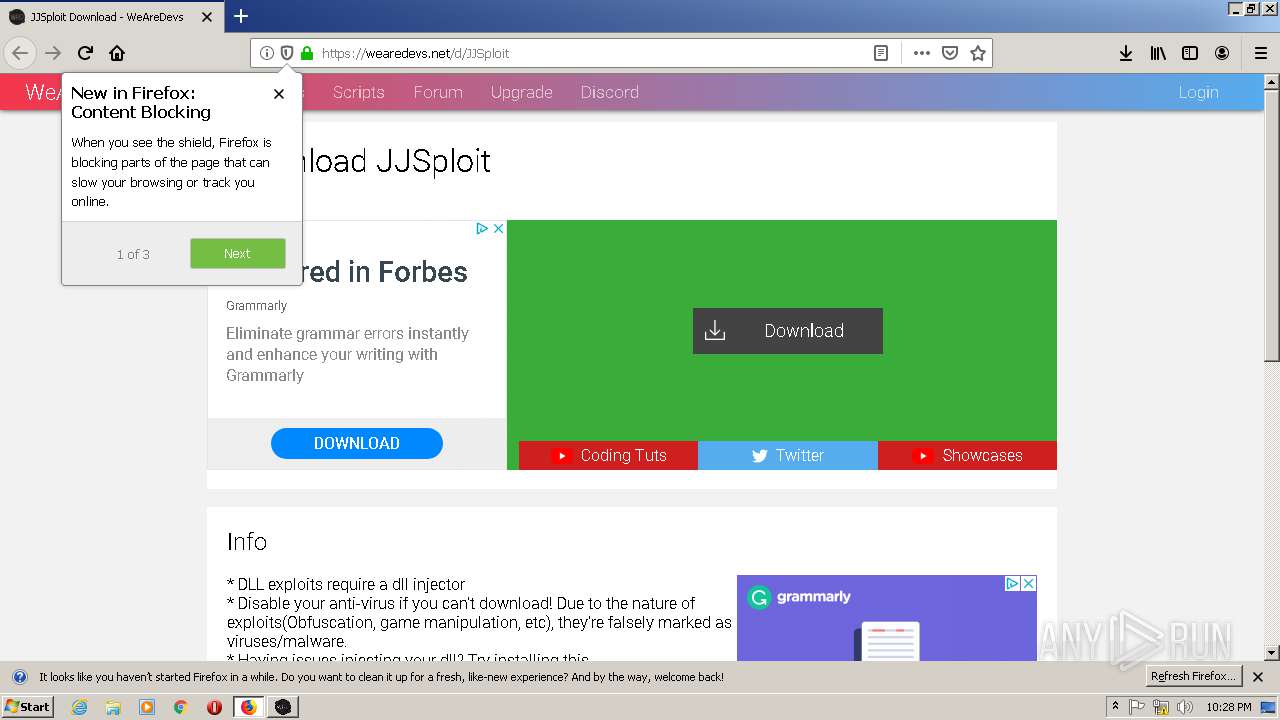
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/2ebc9239-2dfb-4dda-bd9f-9b3bdfb6aeb4 |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2020, 21:27:12 |
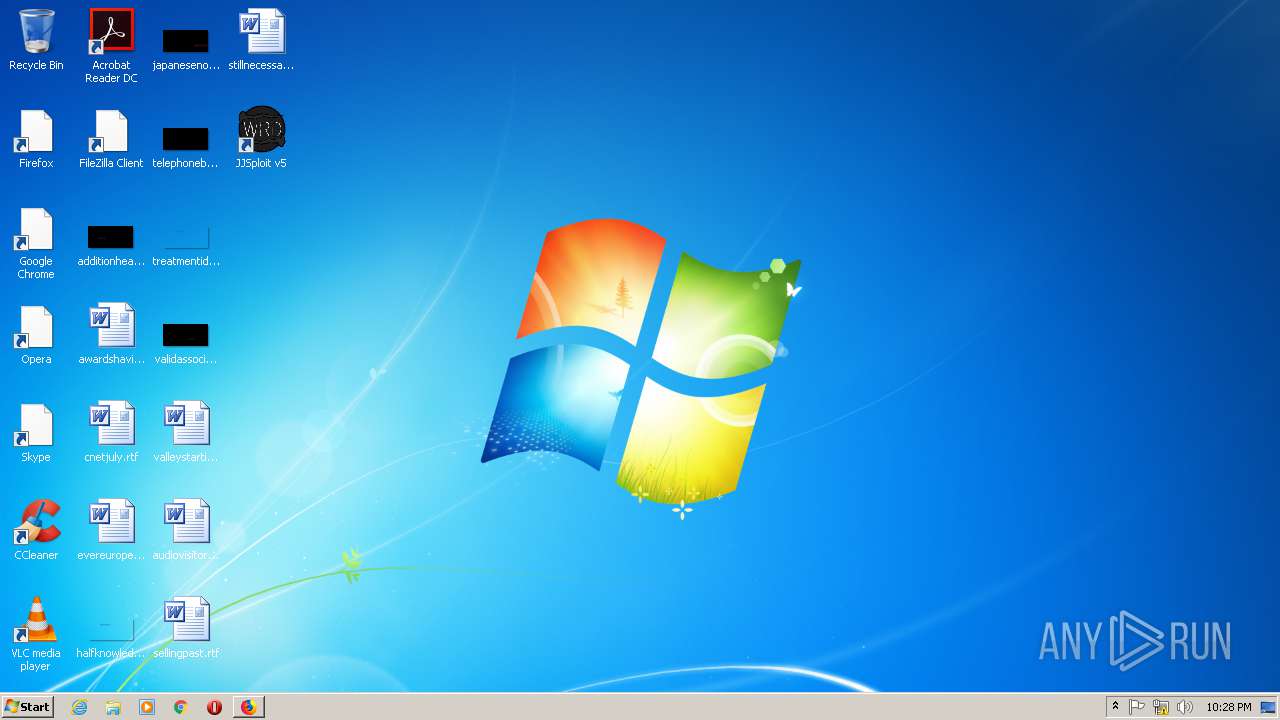
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
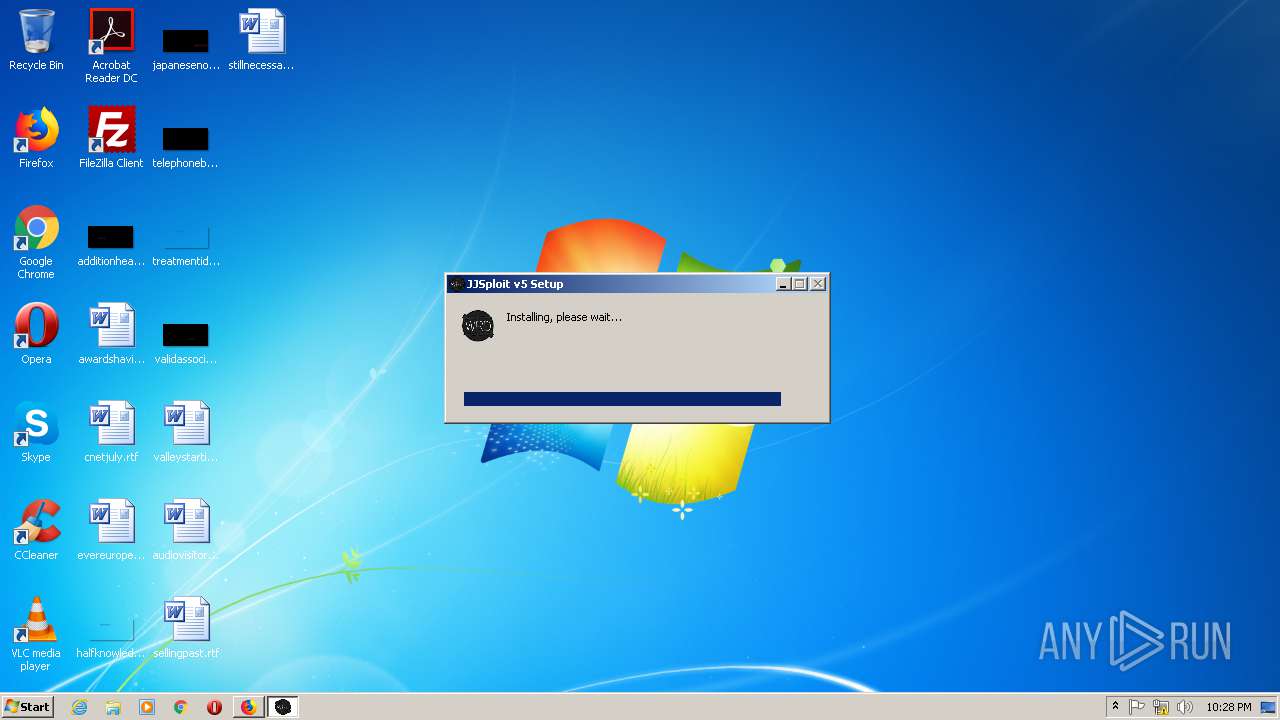
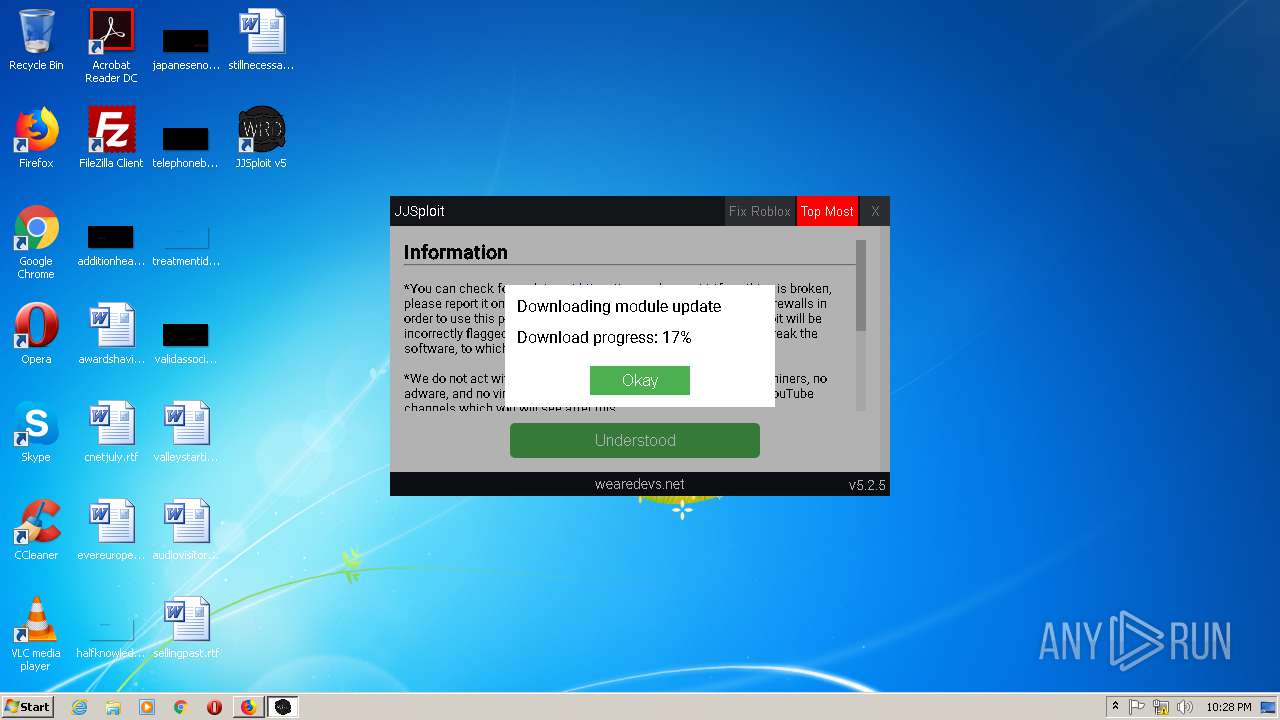
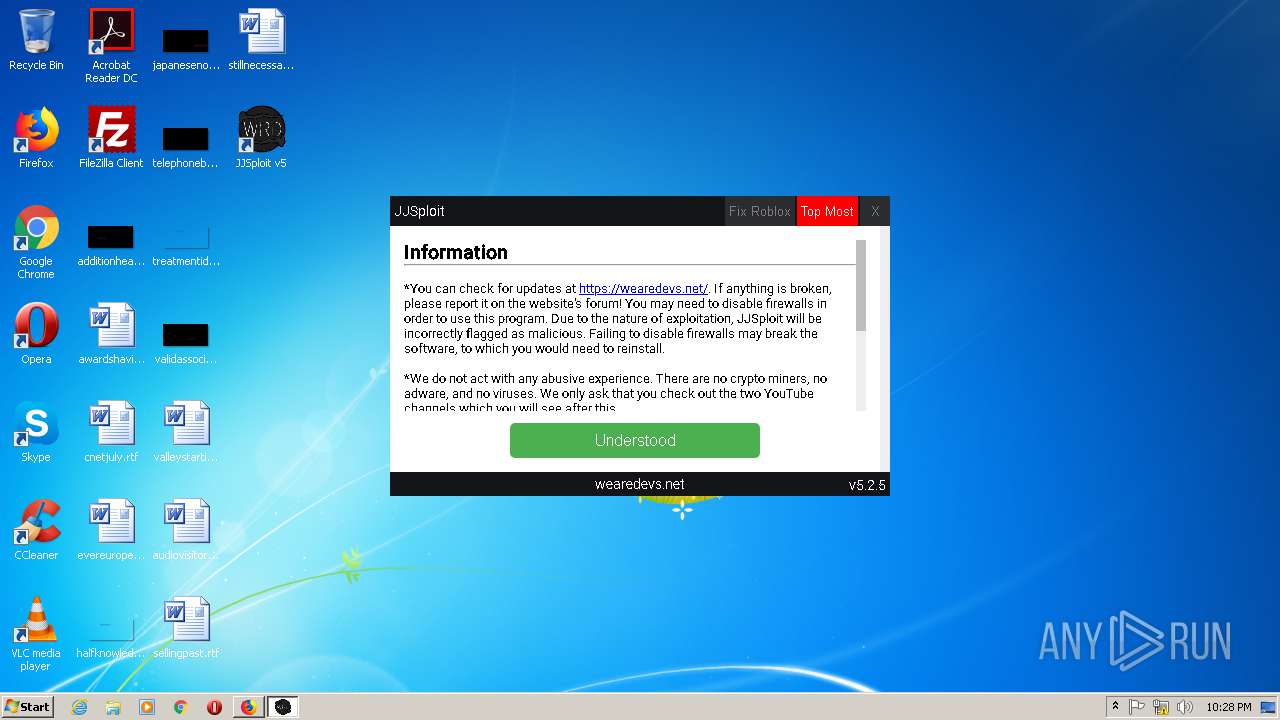
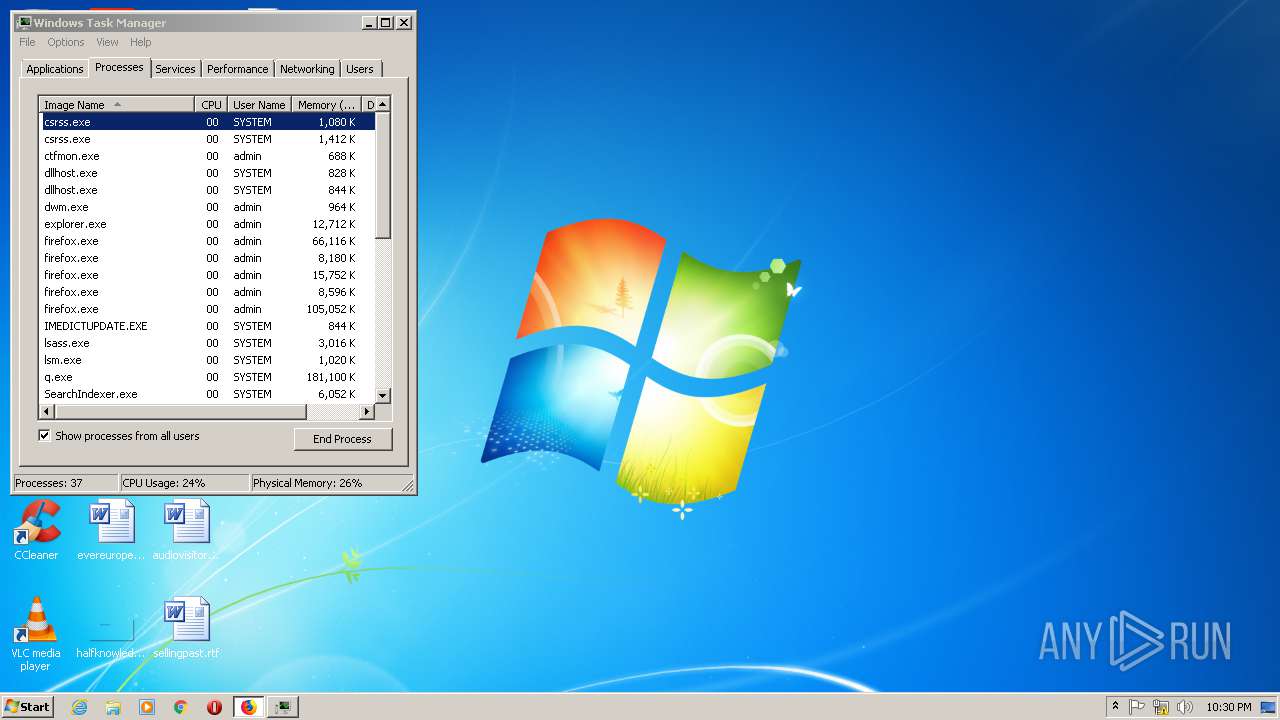
MALICIOUS
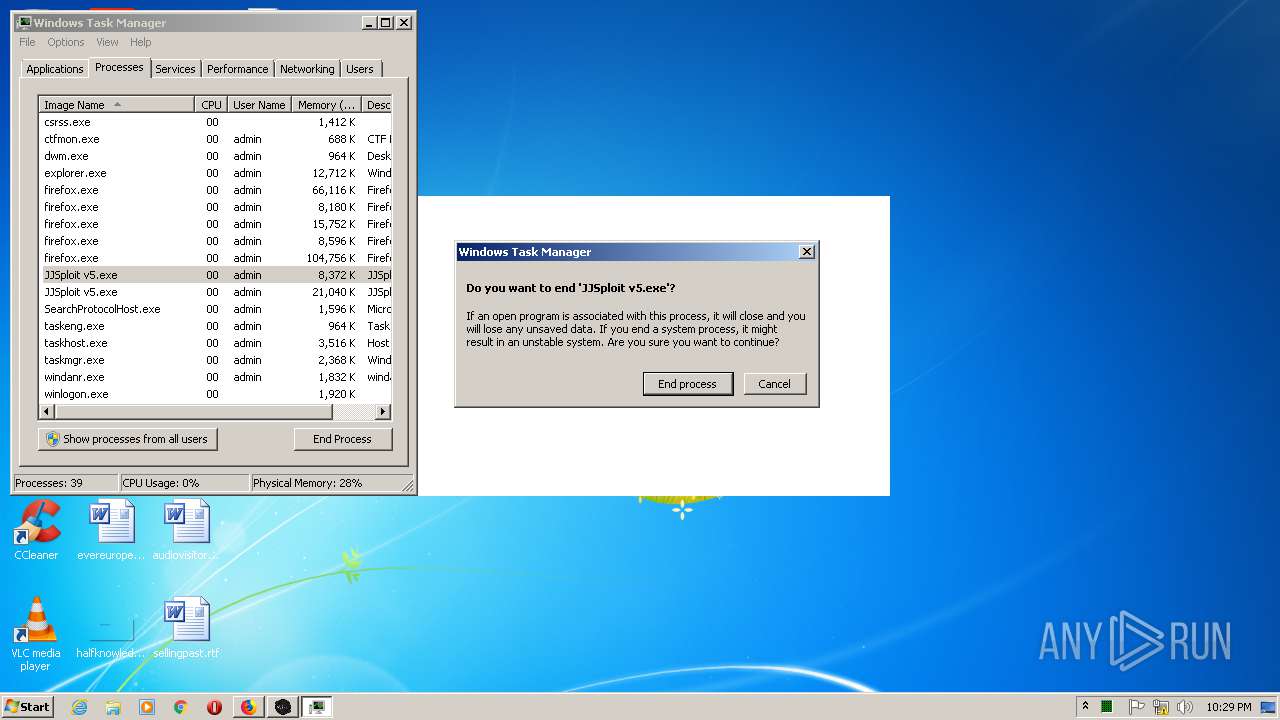
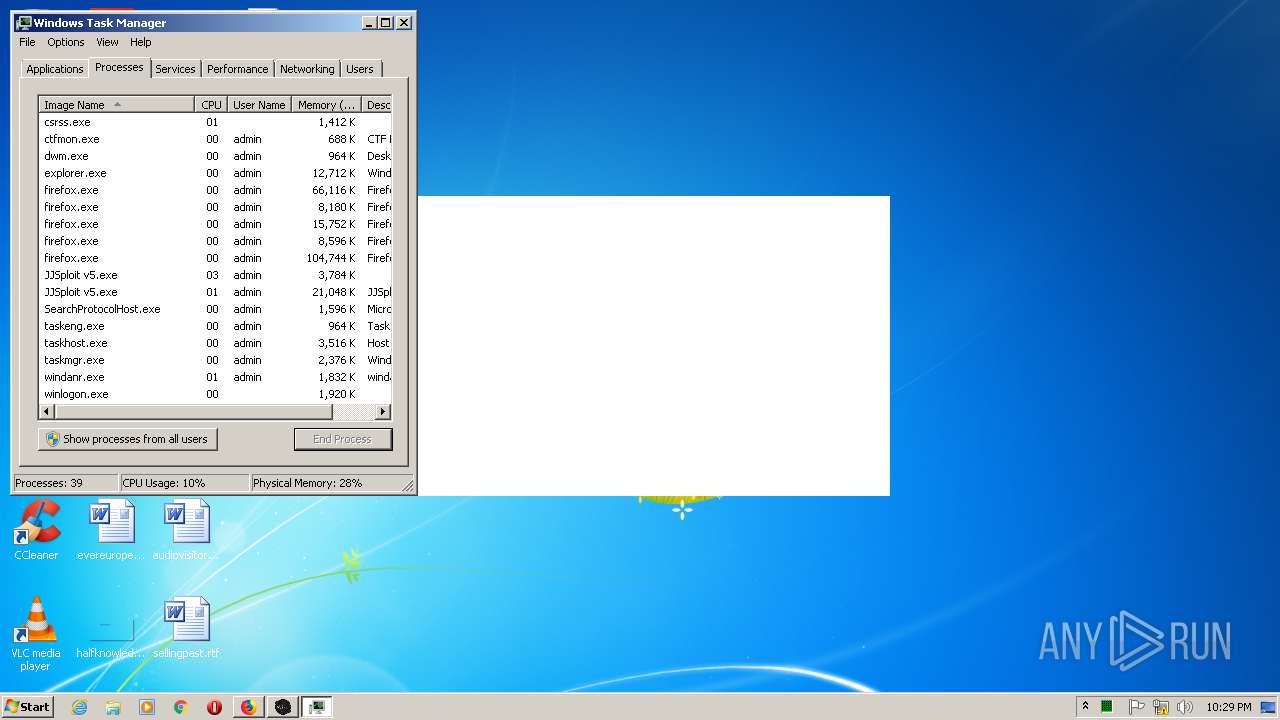
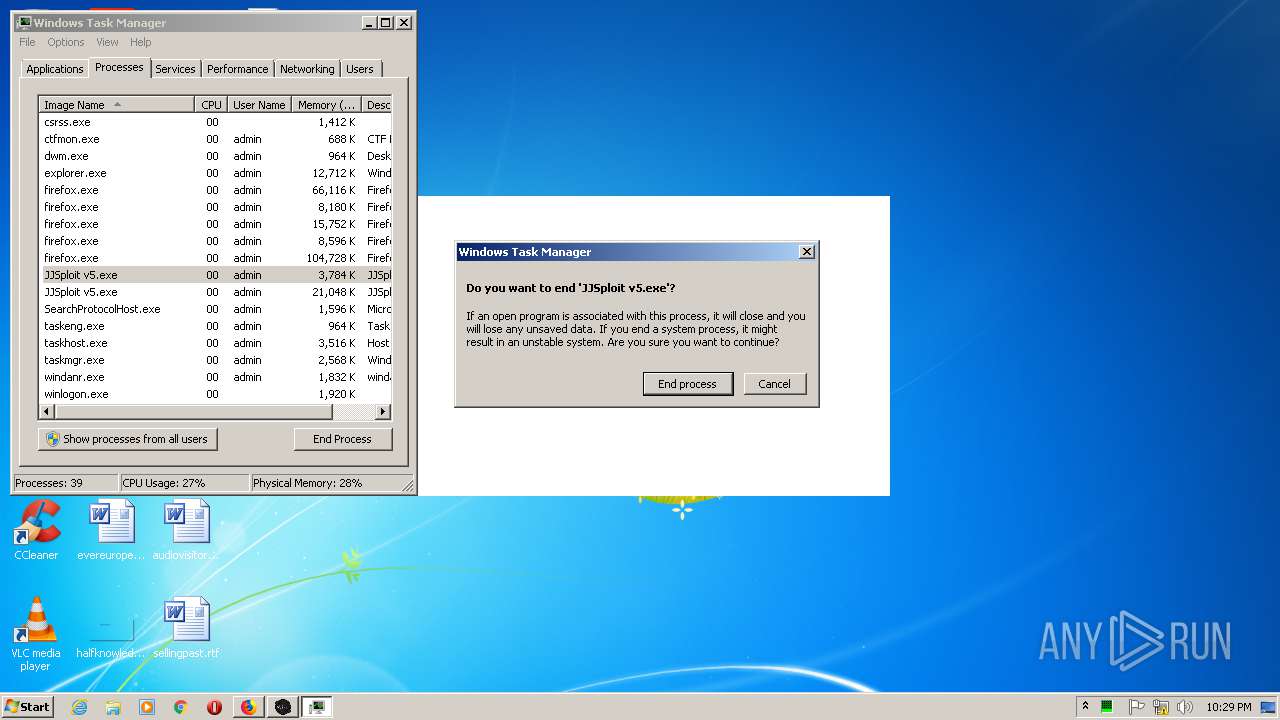
Loads dropped or rewritten executable
- JJSploit v5 Setup 5.2.5.exe (PID: 2964)
- JJSploit v5.exe (PID: 3188)
- JJSploit v5.exe (PID: 2728)
- JJSploit v5.exe (PID: 824)
- JJSploit v5.exe (PID: 1596)
- JJSploit v5.exe (PID: 3428)
- JJSploit v5.exe (PID: 1492)
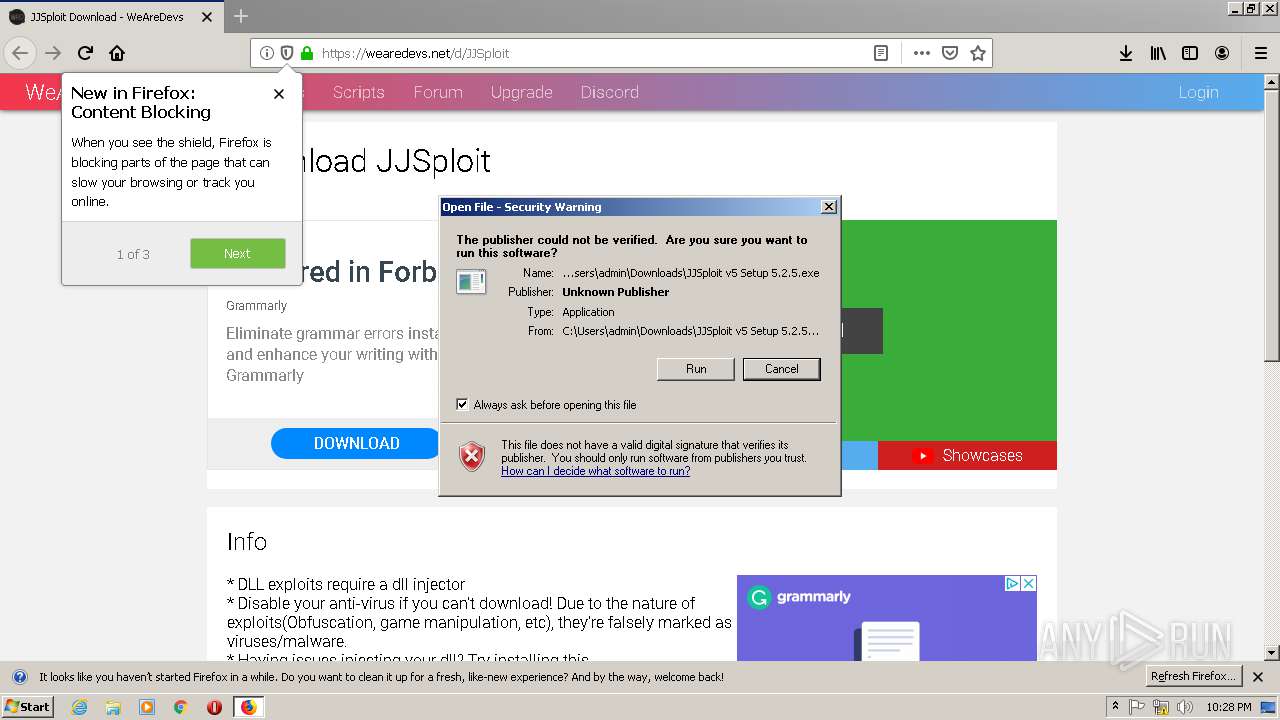
Application was dropped or rewritten from another process
- JJSploit v5 Setup 5.2.5.exe (PID: 2964)
SUSPICIOUS
Executable content was dropped or overwritten
- JJSploit v5 Setup 5.2.5.exe (PID: 2964)
- JJSploit v5.exe (PID: 3188)
- firefox.exe (PID: 3196)
Creates files in the program directory
- firefox.exe (PID: 3196)
Creates a software uninstall entry
- JJSploit v5 Setup 5.2.5.exe (PID: 2964)
Creates files in the user directory
- JJSploit v5.exe (PID: 3188)
- JJSploit v5 Setup 5.2.5.exe (PID: 2964)
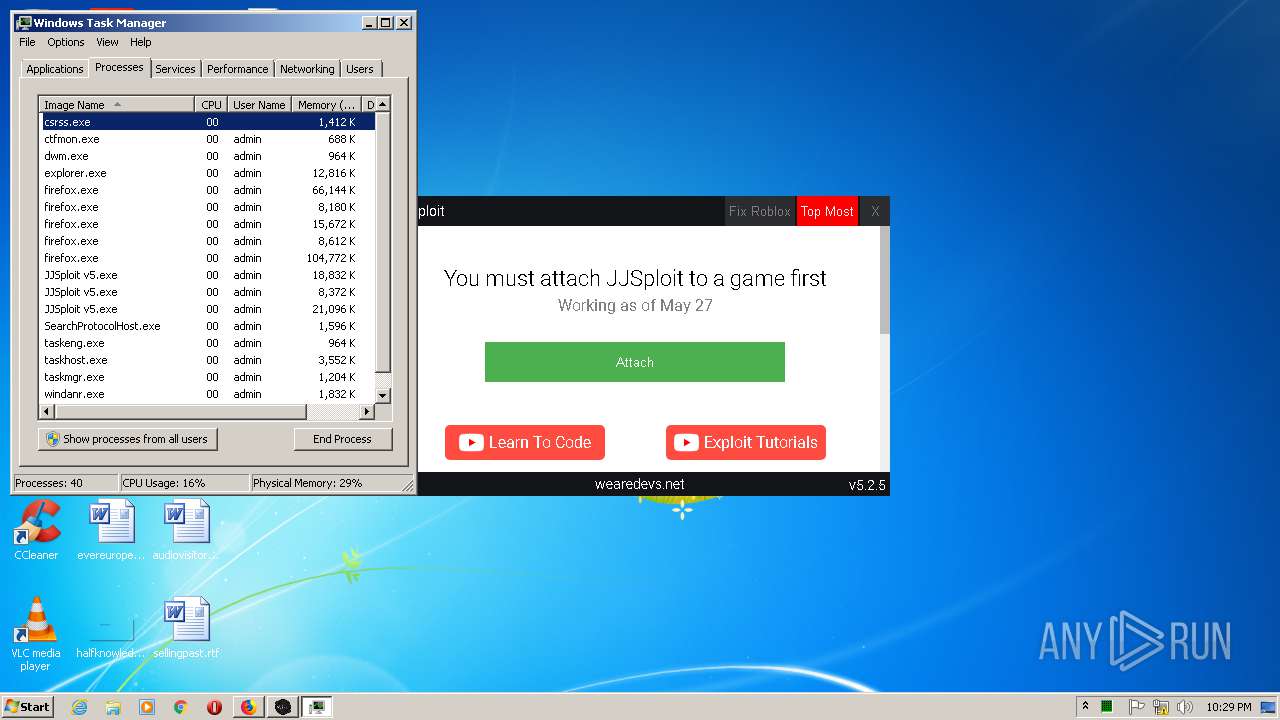
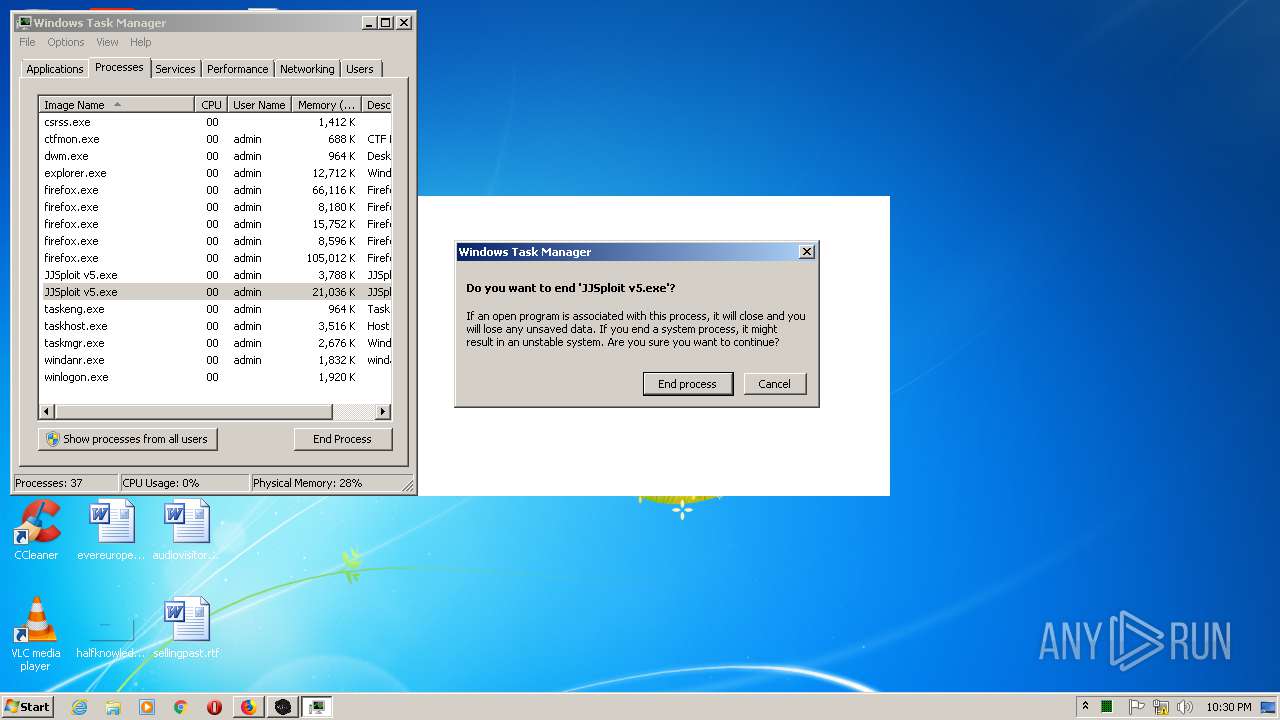
Application launched itself
- JJSploit v5.exe (PID: 3188)
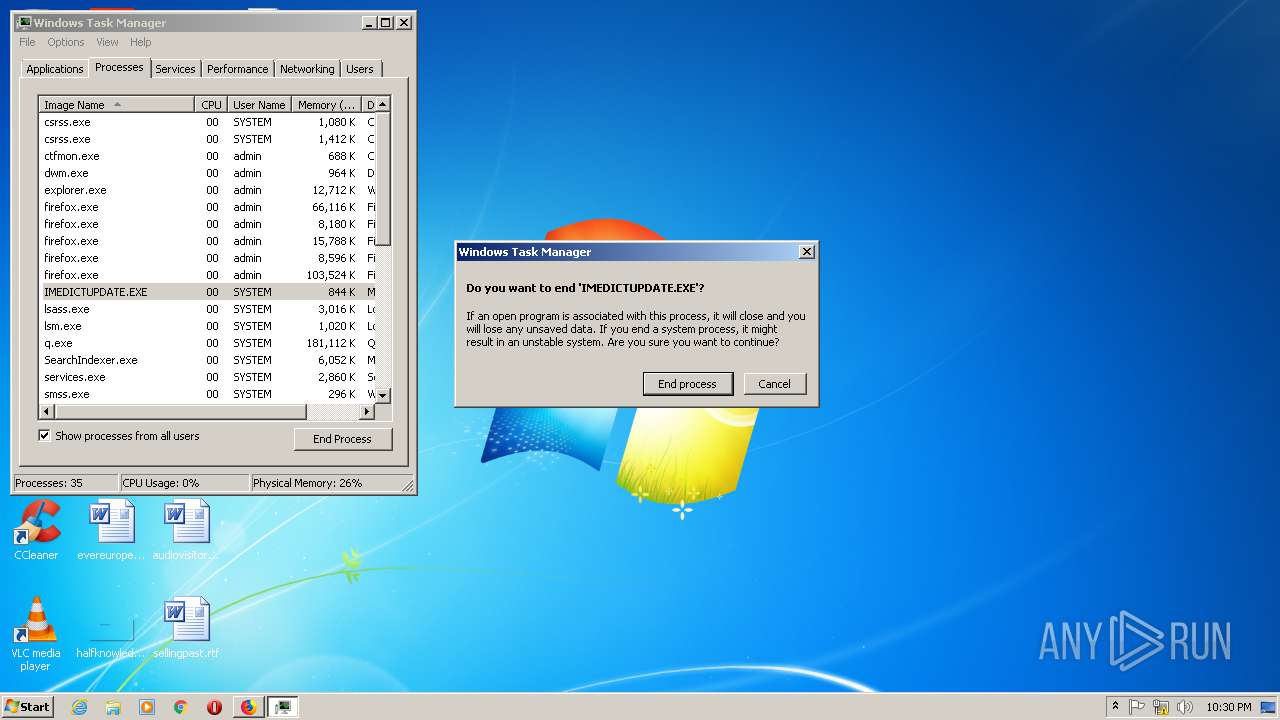
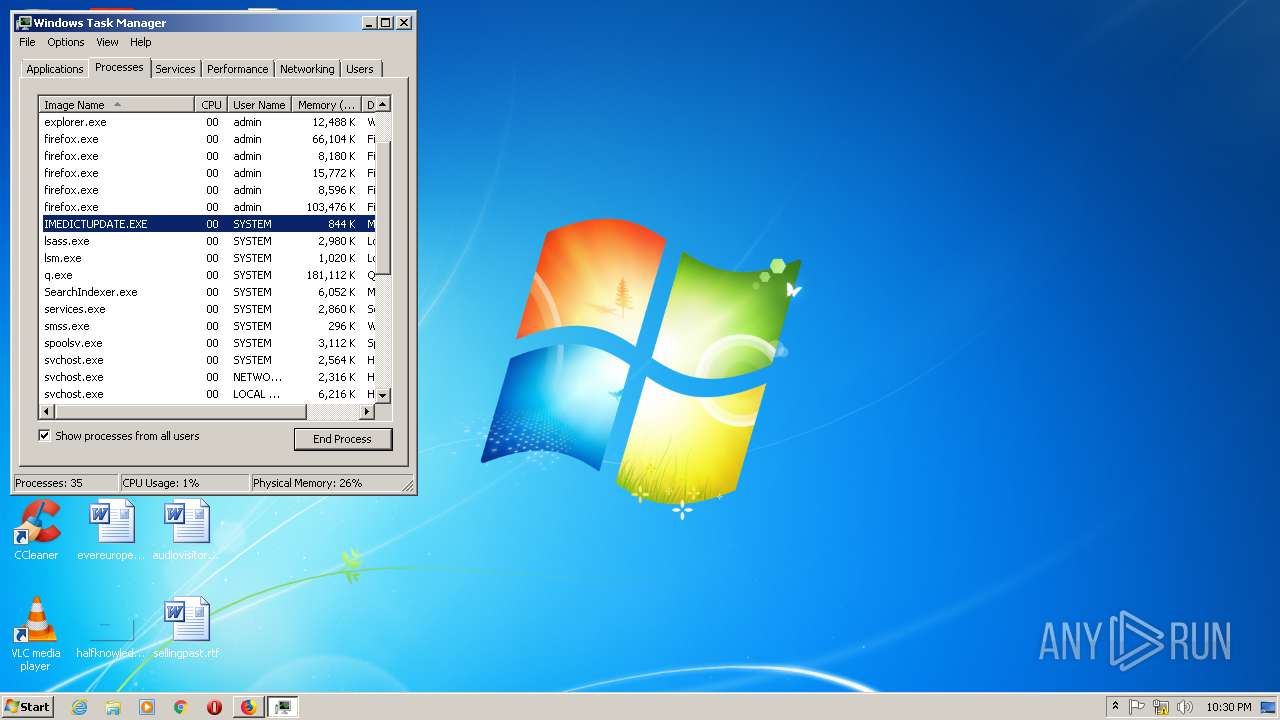
- taskmgr.exe (PID: 3108)
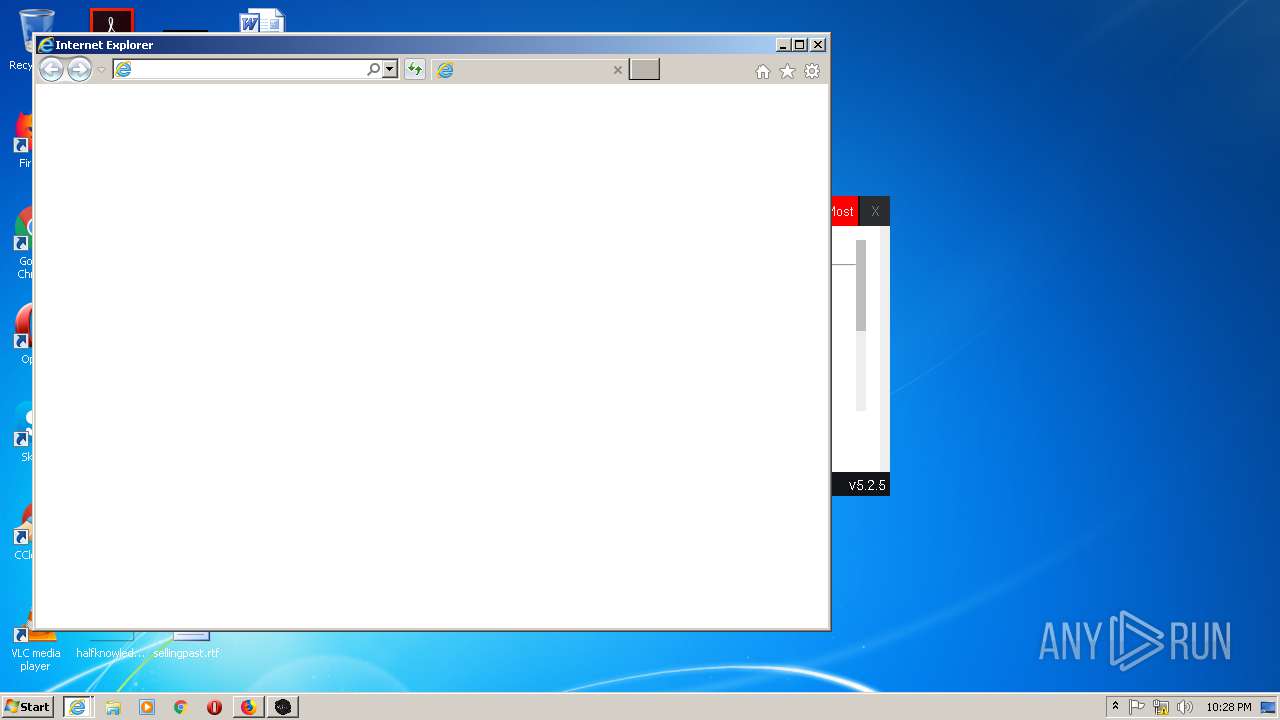
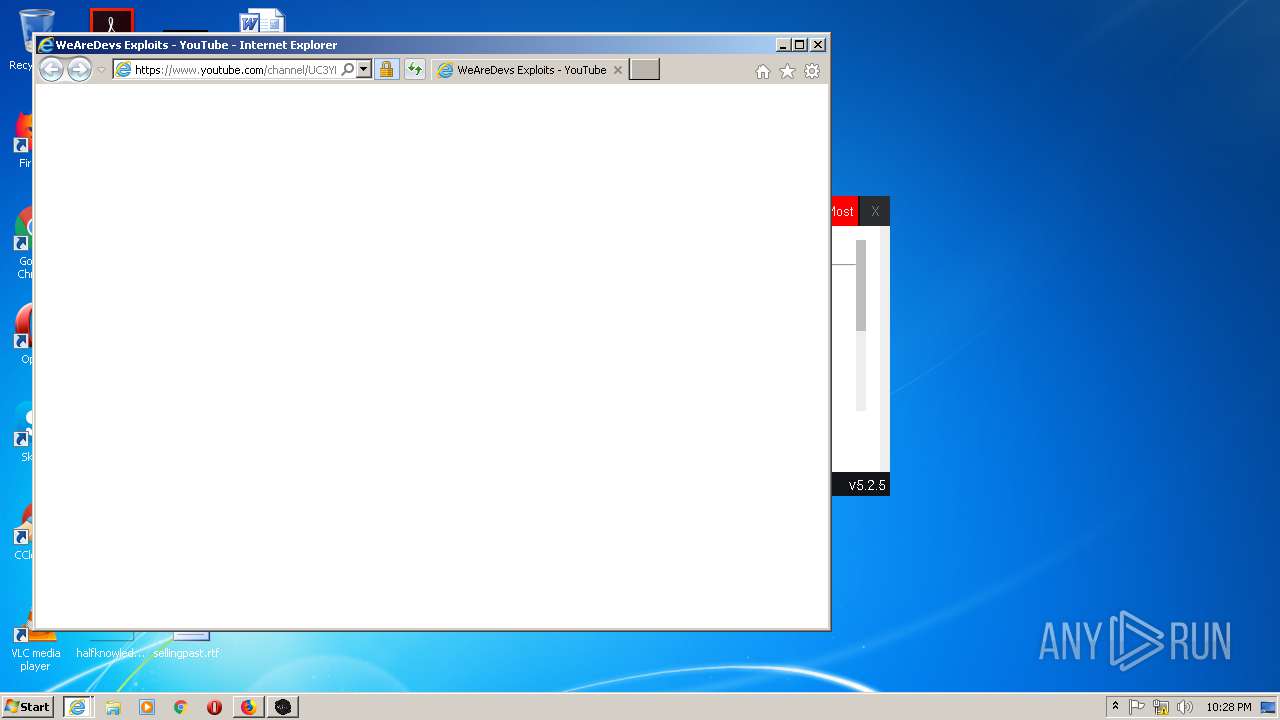
Starts Internet Explorer
- JJSploit v5.exe (PID: 3188)
INFO
Reads CPU info
- firefox.exe (PID: 3196)
Application launched itself
- firefox.exe (PID: 3196)
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 888)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3196)
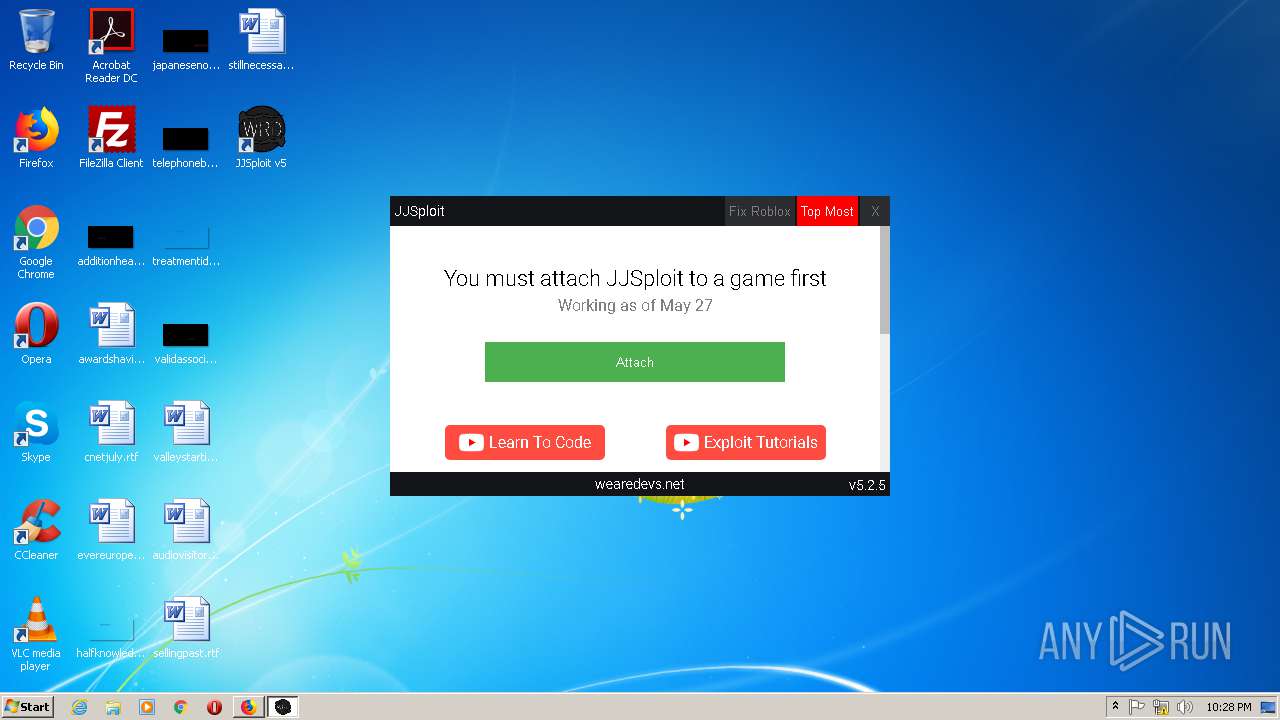
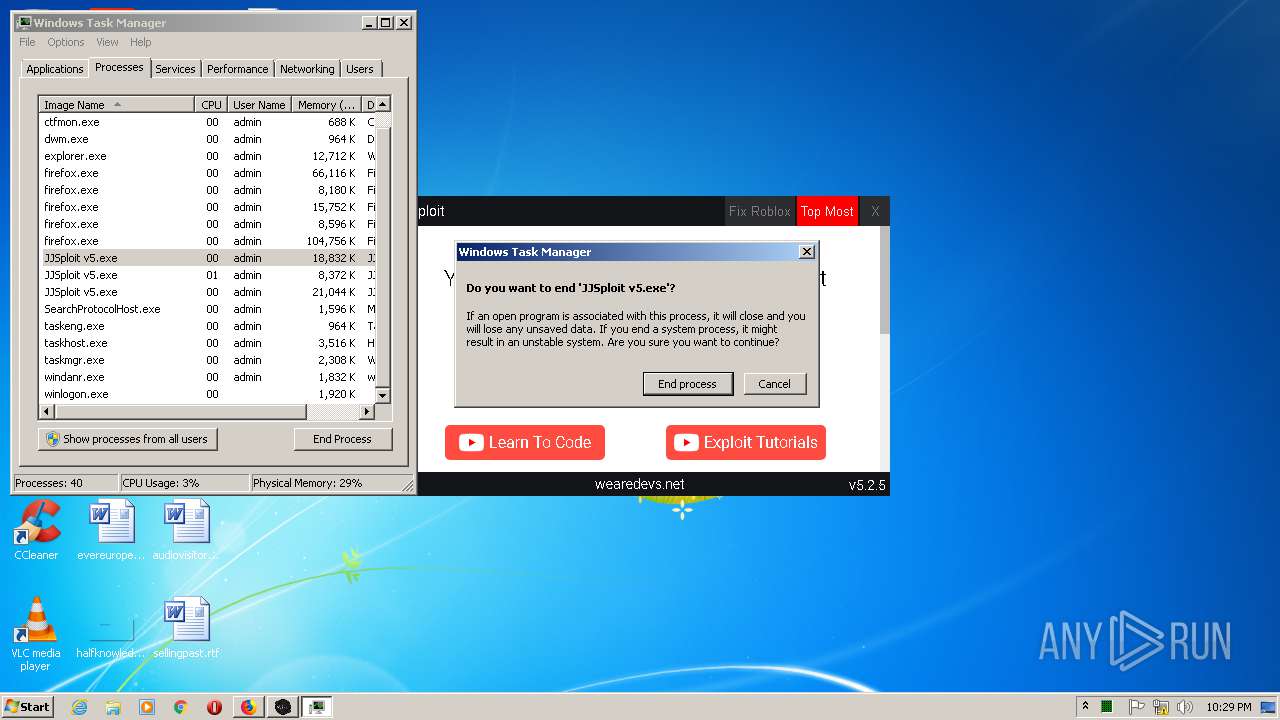
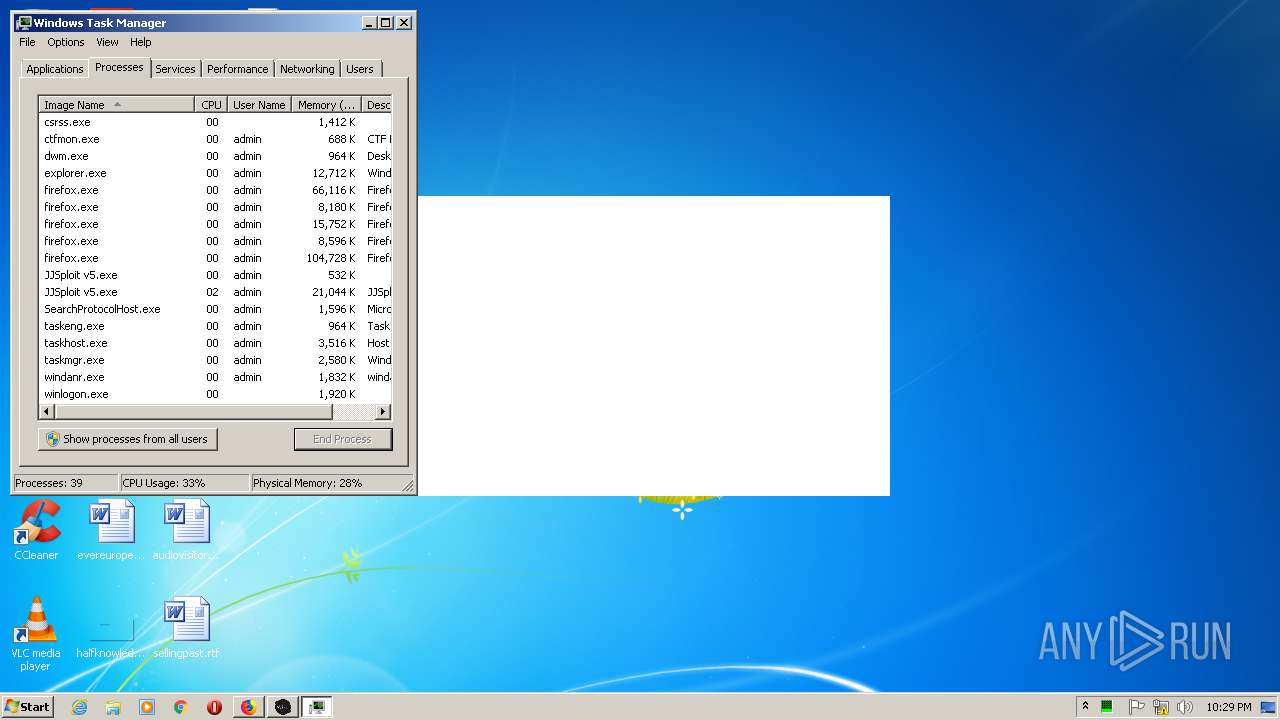
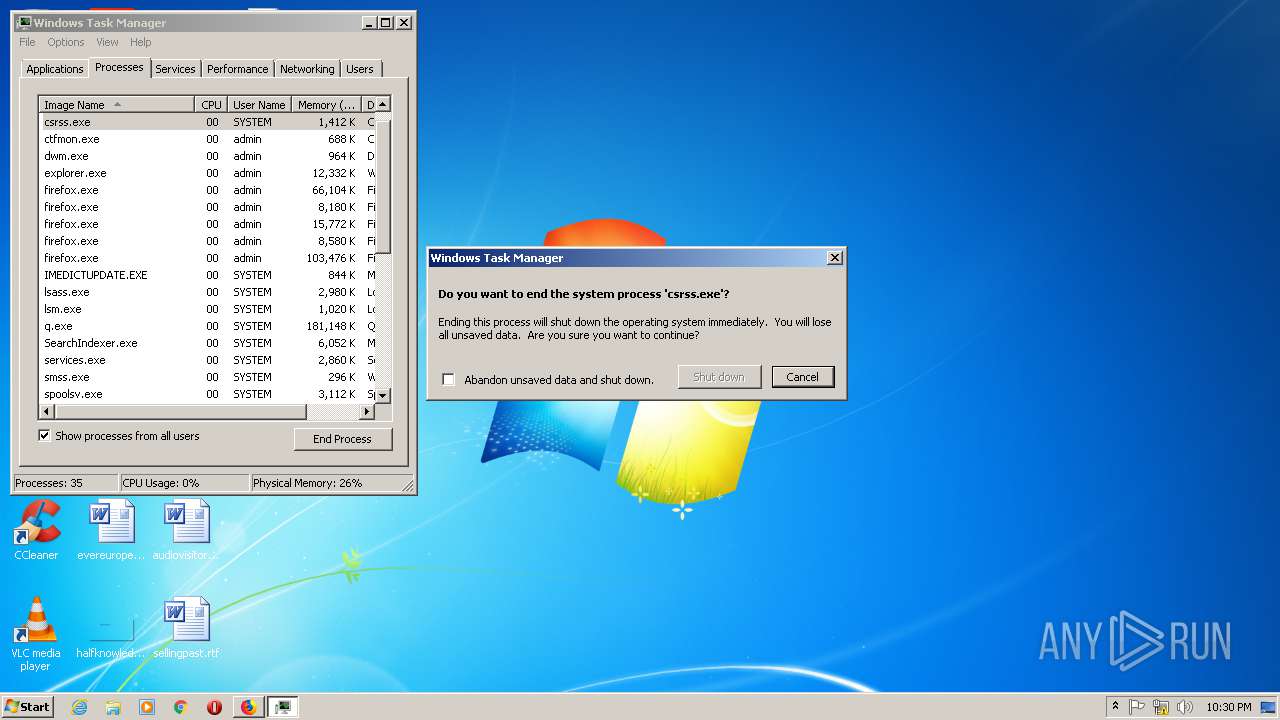
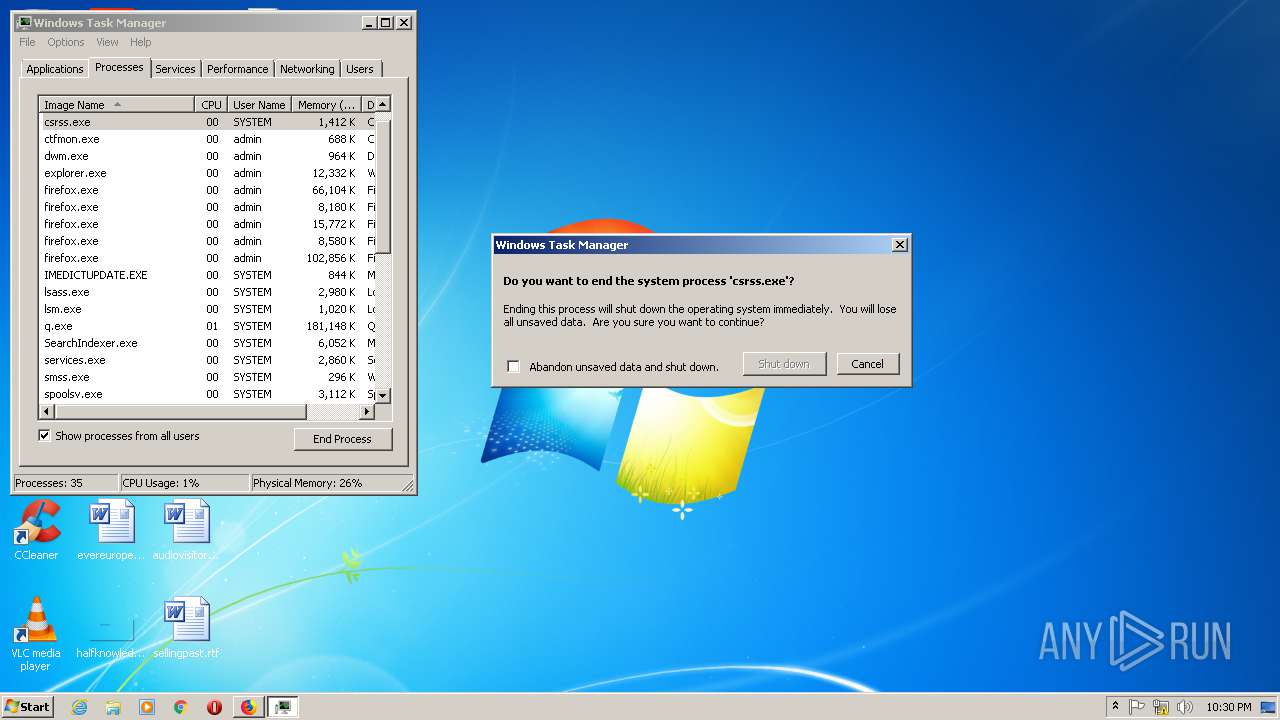
Manual execution by user
- JJSploit v5.exe (PID: 3188)
- taskmgr.exe (PID: 3108)
Reads the hosts file
- JJSploit v5.exe (PID: 3188)
Reads Internet Cache Settings
- iexplore.exe (PID: 888)
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 3480)
- firefox.exe (PID: 3196)
Reads settings of System Certificates
- iexplore.exe (PID: 3480)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 888)
Creates files in the user directory
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 3480)
- firefox.exe (PID: 3196)
Changes internet zones settings
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 888)
Reads internet explorer settings
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 3480)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 888)
Changes settings of System certificates
- iexplore.exe (PID: 888)
- iexplore.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
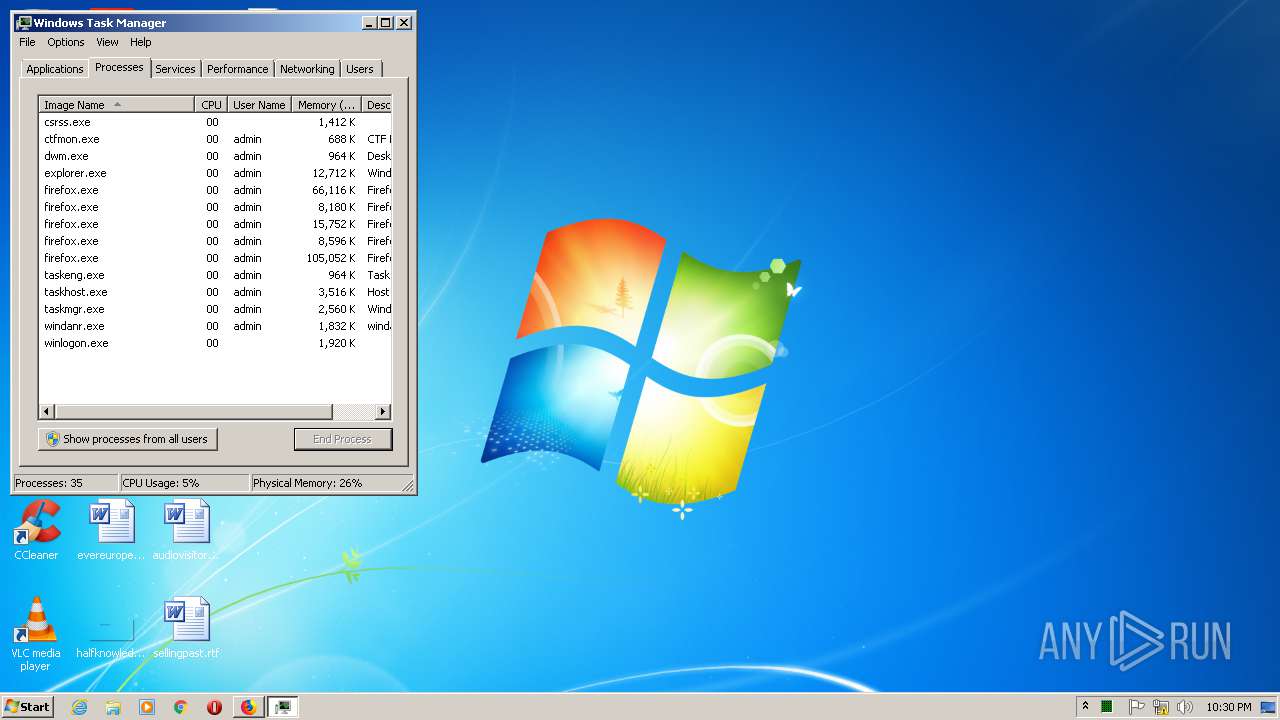
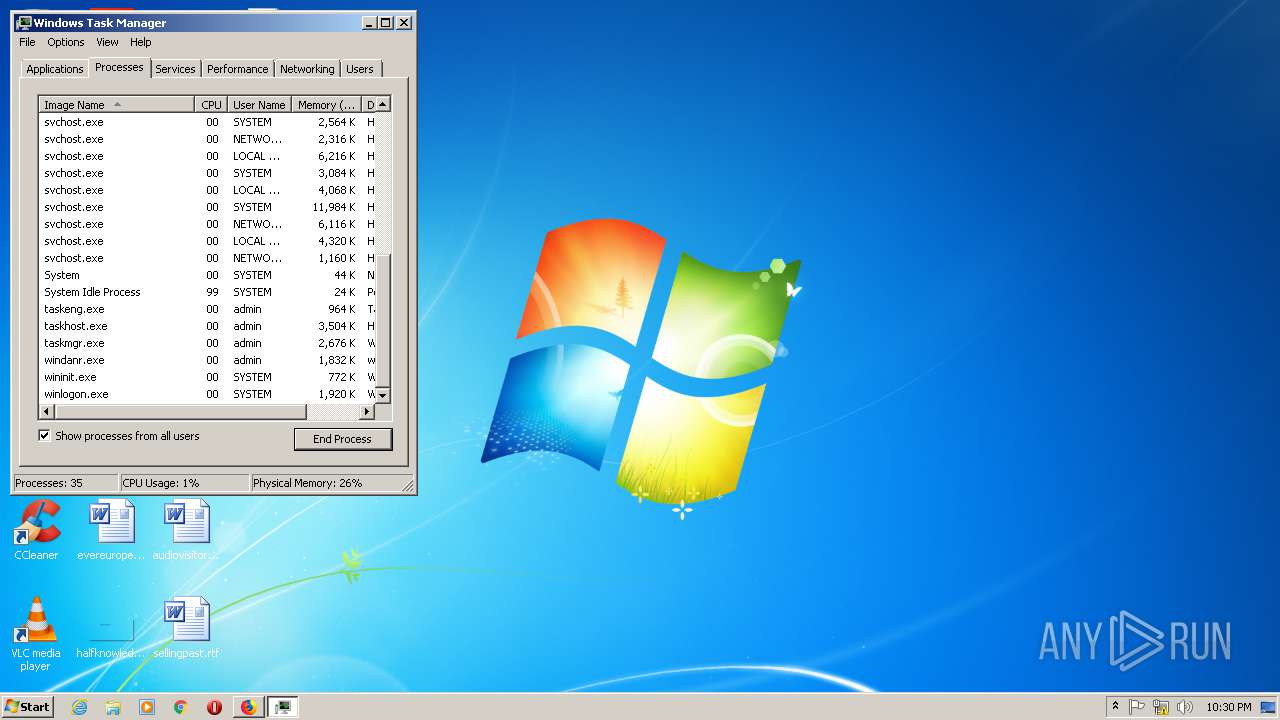
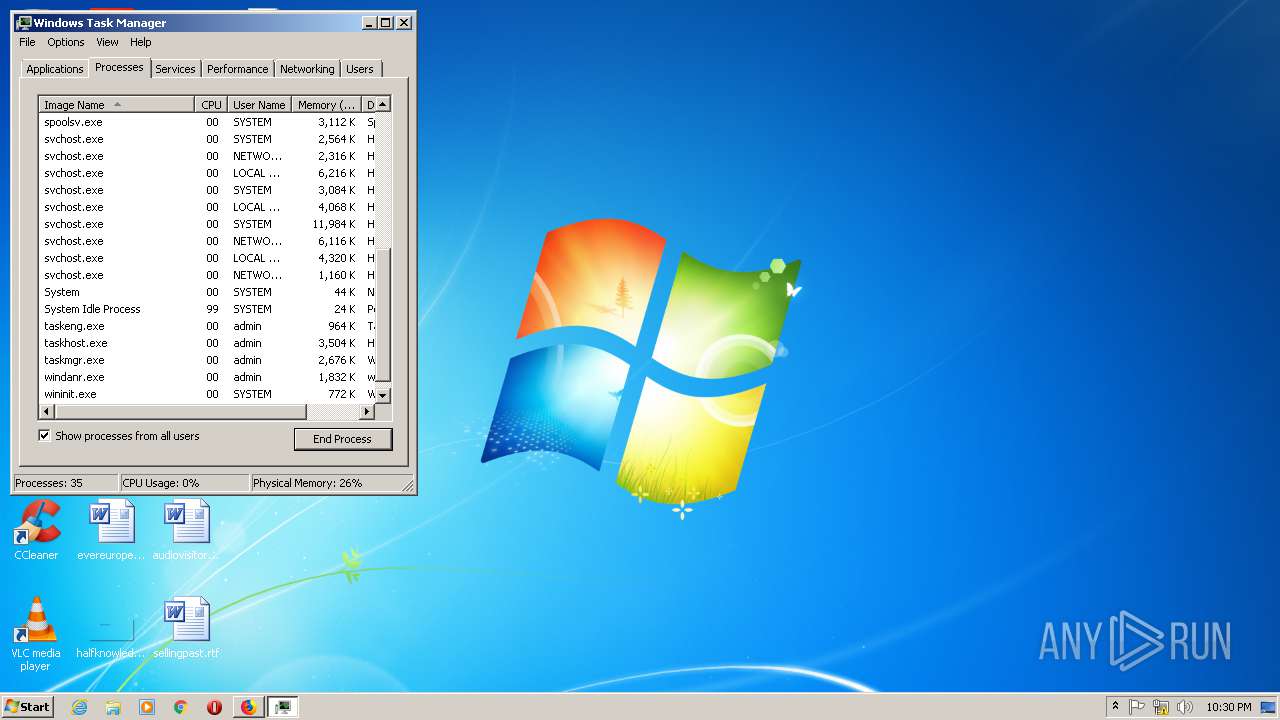
Total processes
57
Monitored processes
19
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=renderer --disable-features=SpareRendererForSitePerProcess --service-pipe-token=1914946451102844682 --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar\build\preload.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1914946451102844682 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1560 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 1 Version: 5.2.5 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC4fs_zKuE1lsXbCLS_Y9UTA?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3196.3.116247629\811868707" -childID 1 -isForBrowser -prefsHandle 836 -prefMapHandle 852 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3196 "\\.\pipe\gecko-crash-server-pipe.3196" 1744 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1492 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12659017831712164655 --mojo-platform-channel-handle=1632 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 0 Version: 5.2.5 Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10775901337539670357 --mojo-platform-channel-handle=1296 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 1 Version: 5.2.5 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3196.0.1444724317\453488677" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3196 "\\.\pipe\gecko-crash-server-pipe.3196" 1204 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3196.13.264223294\2019996188" -childID 2 -isForBrowser -prefsHandle 2892 -prefMapHandle 2928 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3196 "\\.\pipe\gecko-crash-server-pipe.3196" 2952 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://wearedevs.net/d/JJSploit" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC3YNONzSHPW12m3AT48fMHw?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15598092811315686072 --mojo-platform-channel-handle=1136 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 1 Version: 5.2.5 Modules
| |||||||||||||||
Total events
13 638
Read events
3 140
Write events
7 039
Delete events
3 459
Modification events
| (PID) Process: | (3196) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 3465060100000000 | |||
| (PID) Process: | (2384) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 3465060100000000 | |||
| (PID) Process: | (3196) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3196) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3196) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3196) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2964) JJSploit v5 Setup 5.2.5.exe | Key: | HKEY_CURRENT_USER\Software\0dc89eee-466e-5758-9507-219f65134c5e |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\jjsploitv5 | |||
| (PID) Process: | (2964) JJSploit v5 Setup 5.2.5.exe | Key: | HKEY_CURRENT_USER\Software\0dc89eee-466e-5758-9507-219f65134c5e |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (2964) JJSploit v5 Setup 5.2.5.exe | Key: | HKEY_CURRENT_USER\Software\0dc89eee-466e-5758-9507-219f65134c5e |
| Operation: | write | Name: | ShortcutName |
Value: JJSploit v5 | |||
Executable files
20
Suspicious files
188
Text files
273
Unknown types
168
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3196 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
48
DNS requests
96
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | firefox.exe | POST | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | — | — | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | — | 472 b | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | — | 471 b | whitelisted |
3196 | firefox.exe | POST | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | — | — | whitelisted |
3196 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | firefox.exe | 2.16.107.58:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
3196 | firefox.exe | 52.26.114.88:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3196 | firefox.exe | 54.201.38.189:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3196 | firefox.exe | 52.222.167.14:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3196 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3196 | firefox.exe | 52.222.167.196:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3196 | firefox.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3196 | firefox.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3196 | firefox.exe | 104.16.133.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3196 | firefox.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |