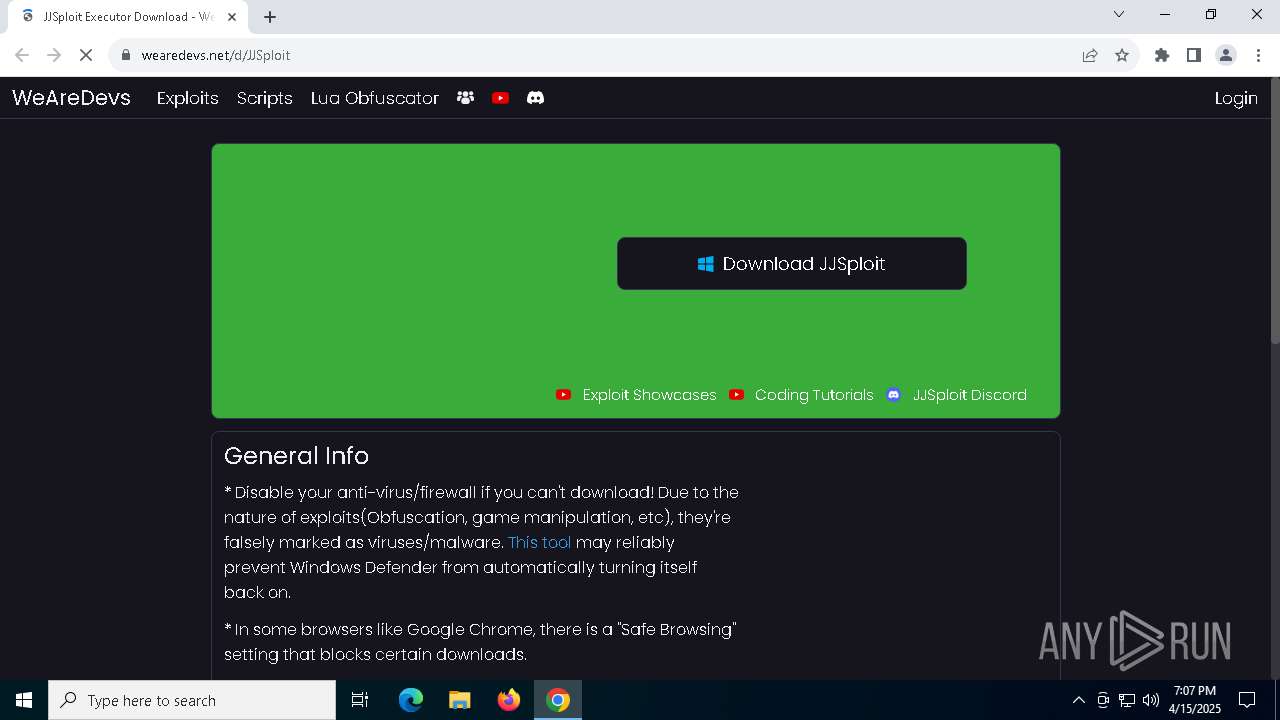
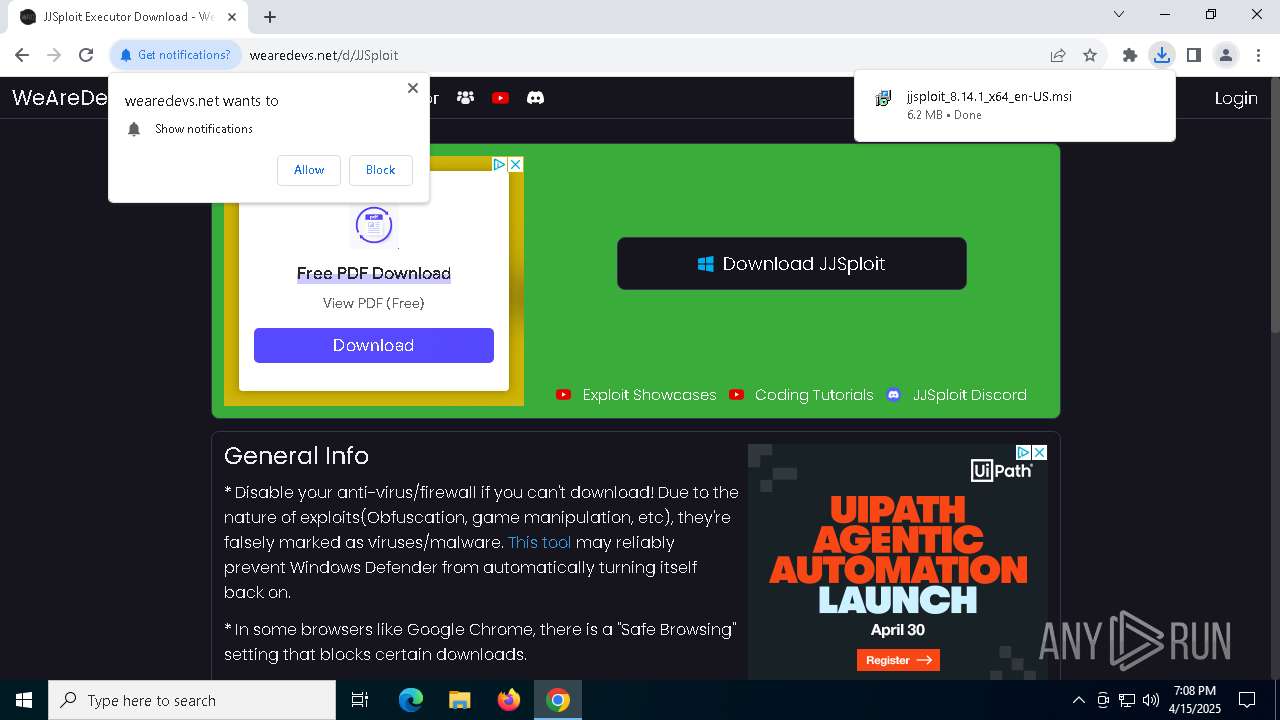
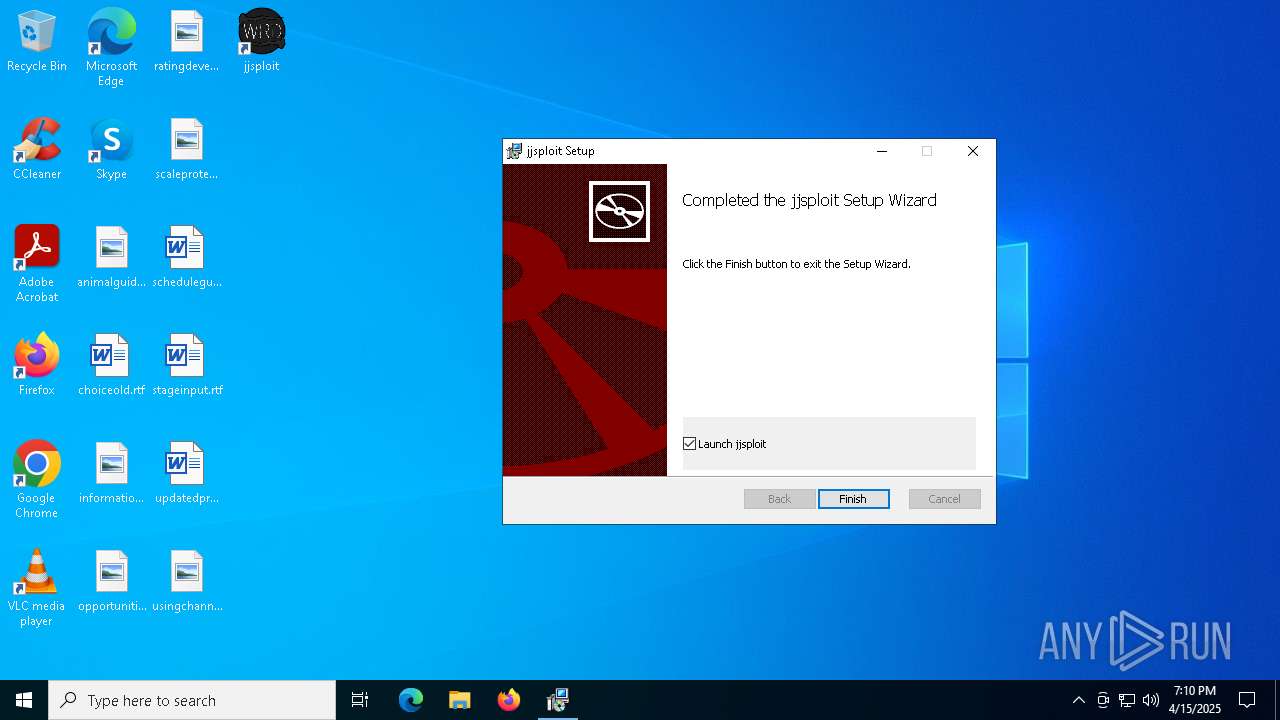
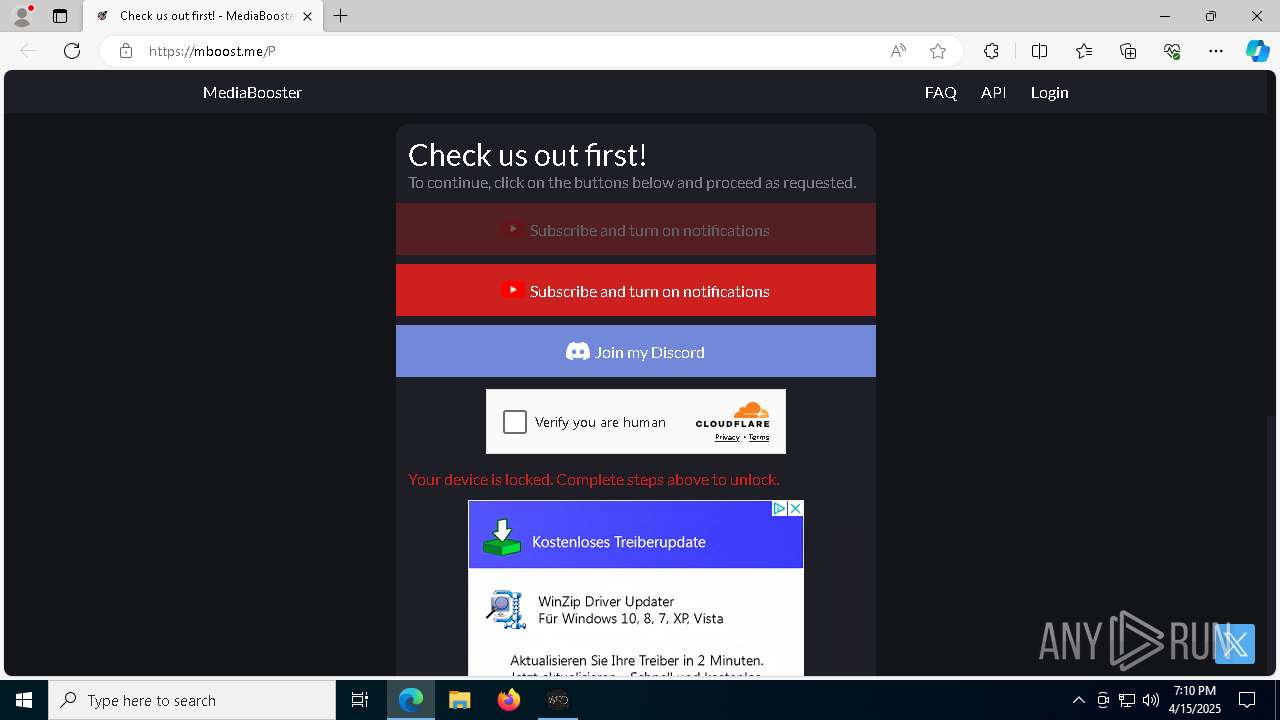
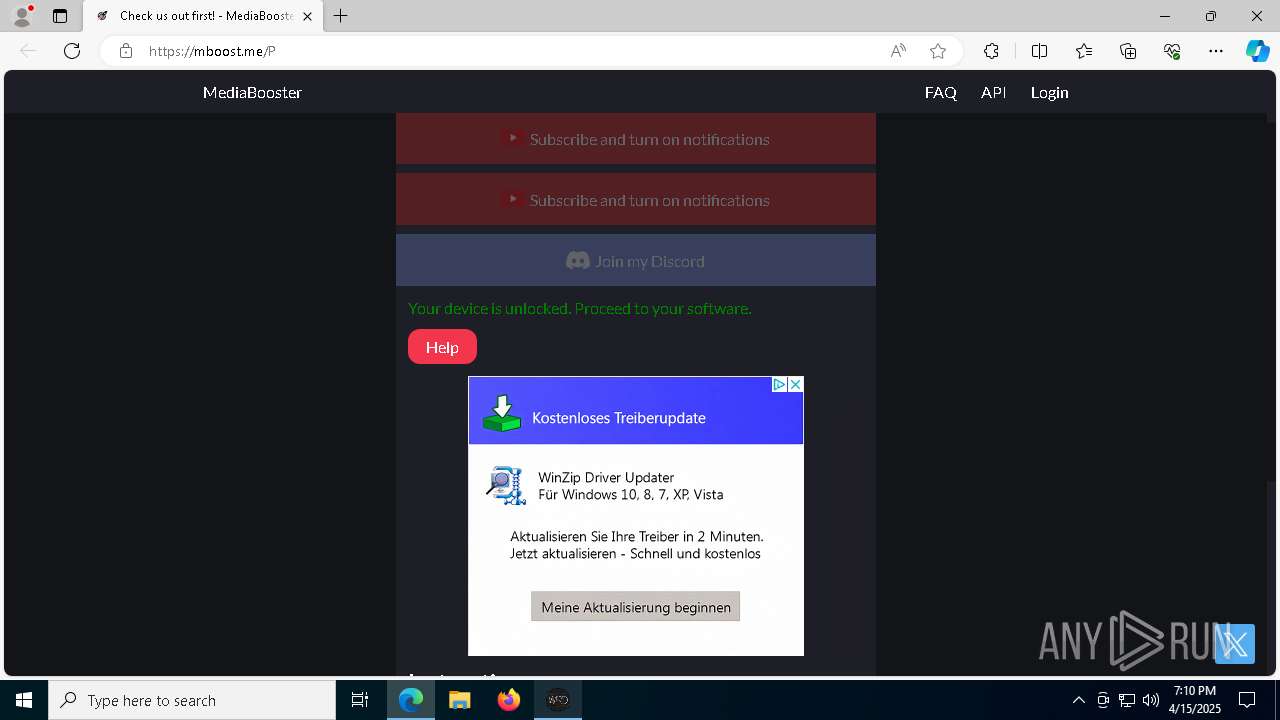
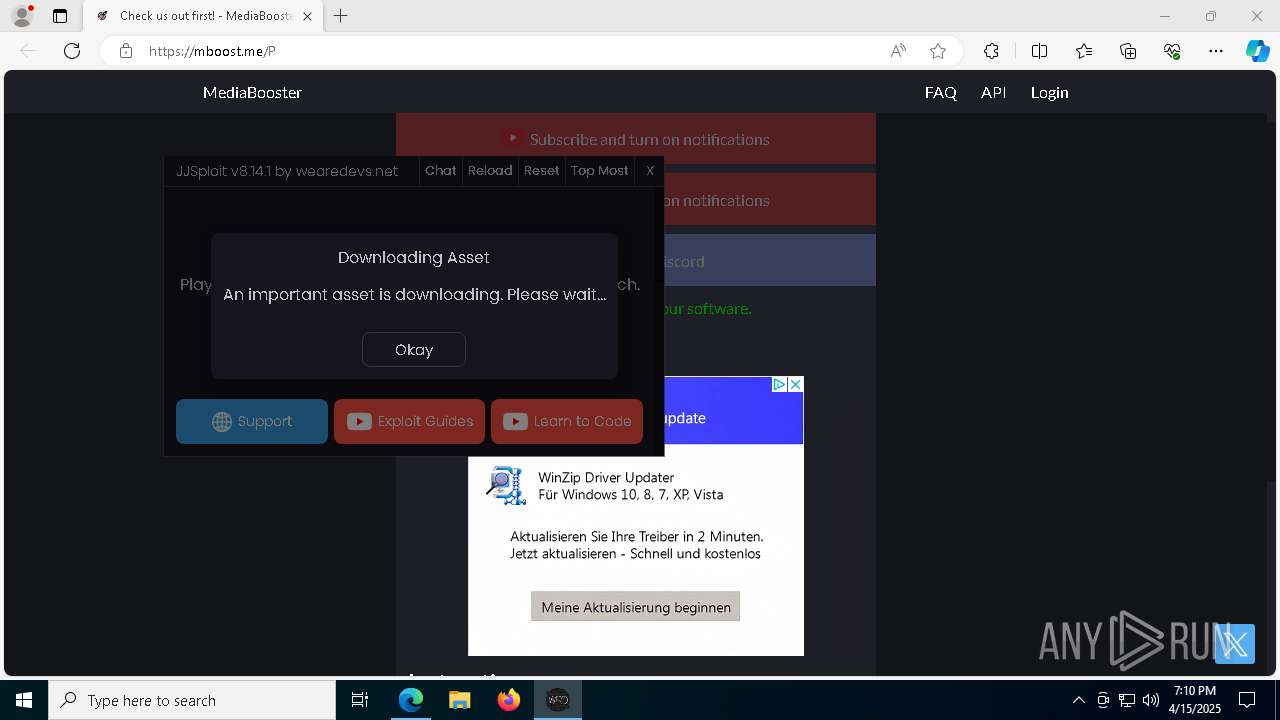
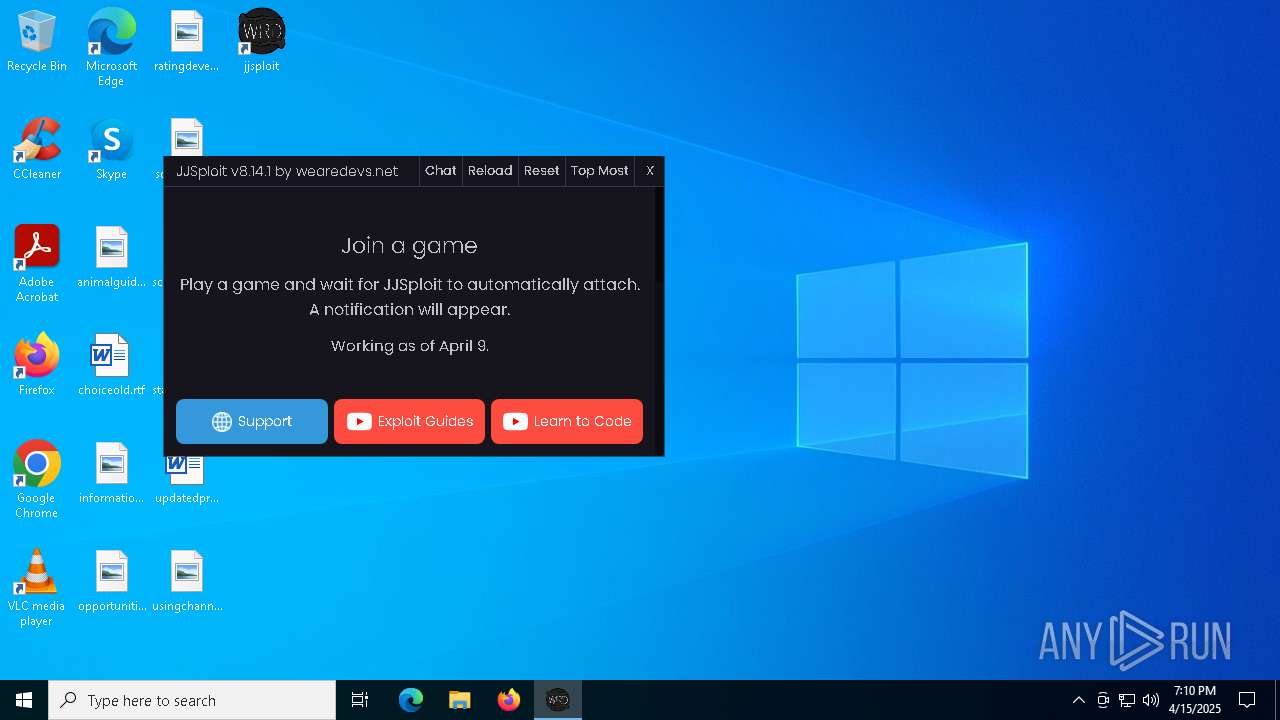
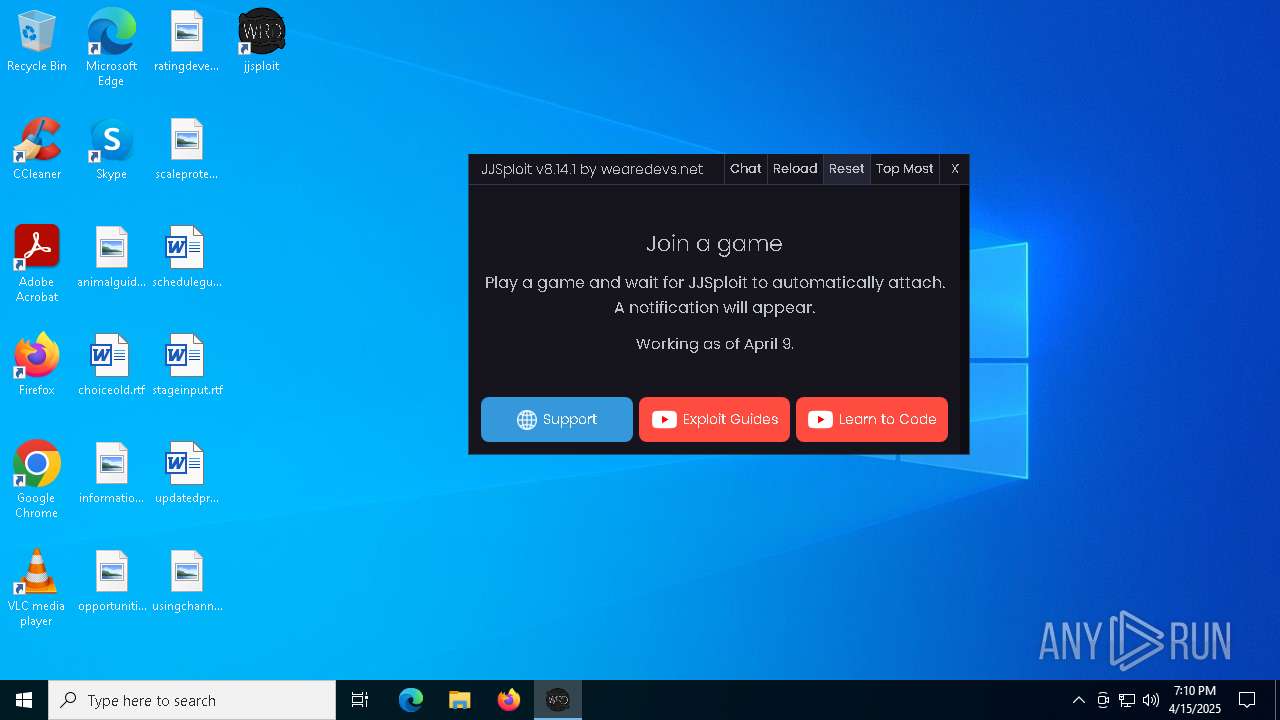
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/2728b002-42c9-4d6f-89db-7d5104e97f6d |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 19:07:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
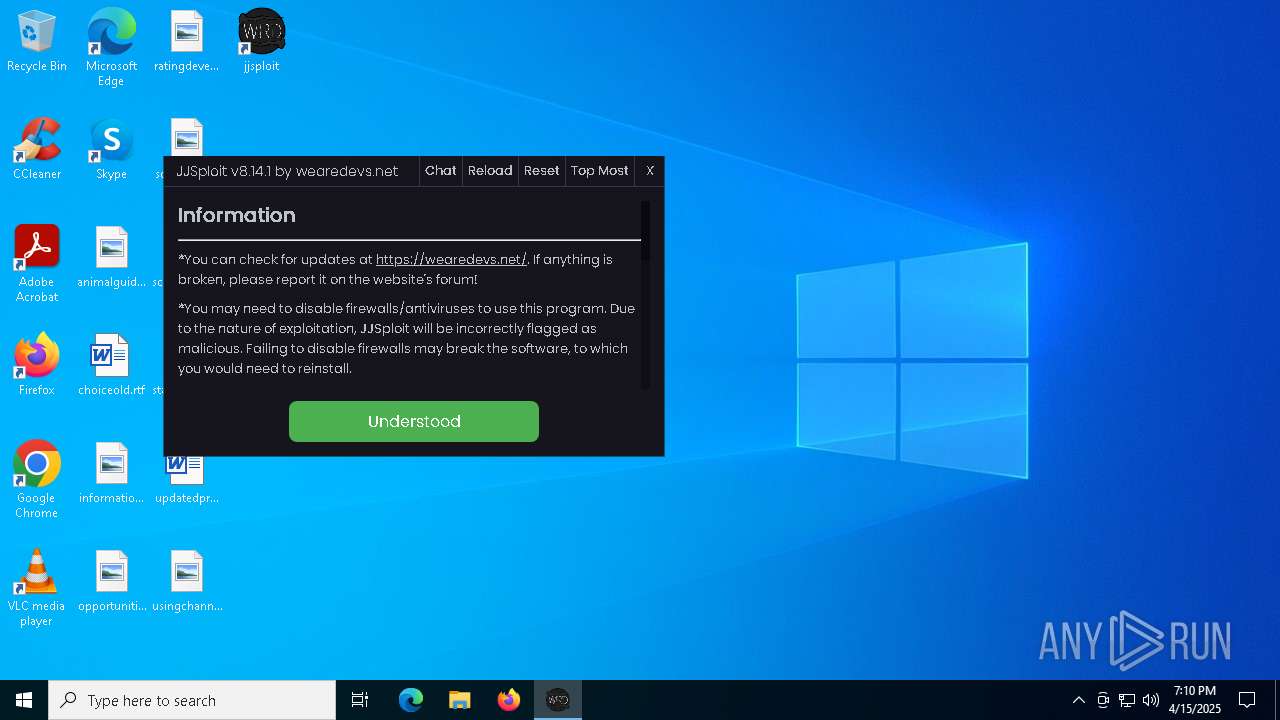
MALICIOUS
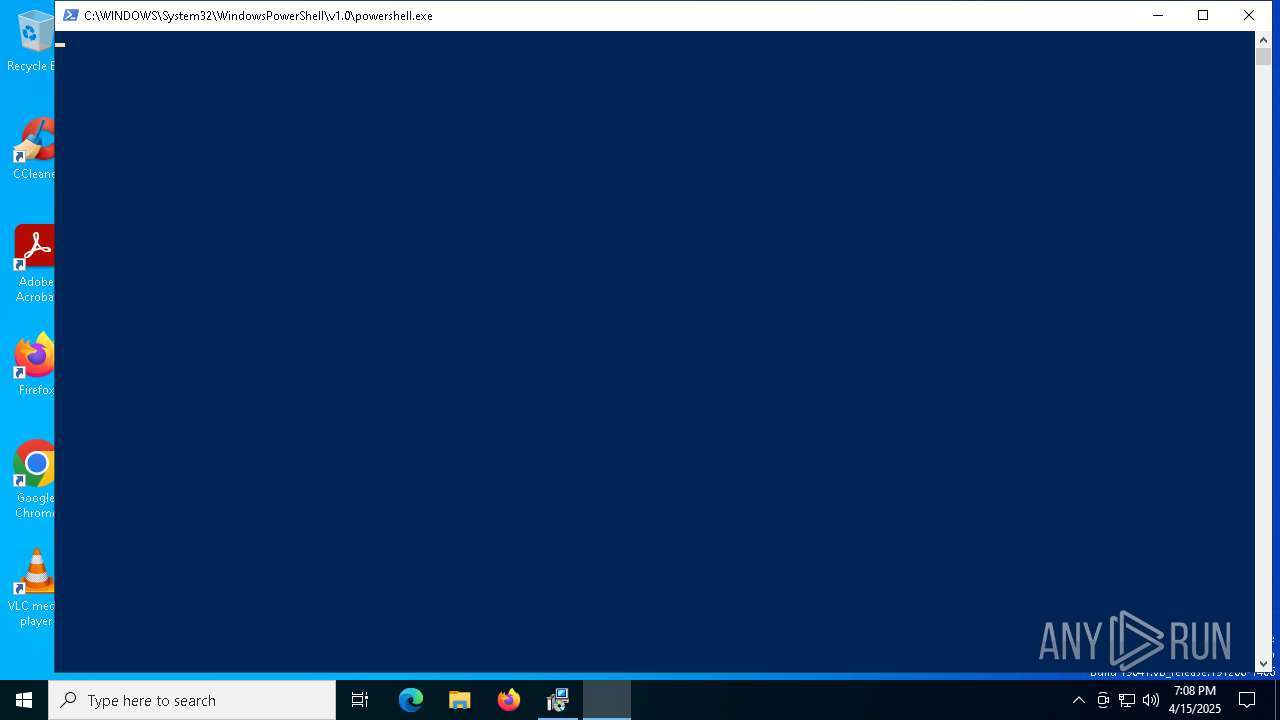
Run PowerShell with an invisible window
- powershell.exe (PID: 7692)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 7648)
The DLL Hijacking
- msedgewebview2.exe (PID: 7988)
Scans artifacts that could help determine the target
- msedgewebview2.exe (PID: 7368)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 8184)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4068)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4068)
Manipulates environment variables
- powershell.exe (PID: 7692)
Downloads file from URI via Powershell
- powershell.exe (PID: 7692)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4068)
Starts process via Powershell
- powershell.exe (PID: 7692)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7692)
Executable content was dropped or overwritten
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
- powershell.exe (PID: 7692)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- setup.exe (PID: 7312)
- MicrosoftEdge_X64_135.0.3179.73.exe (PID: 7232)
- jjsploit.exe (PID: 7800)
Process drops legitimate windows executable
- powershell.exe (PID: 7692)
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- setup.exe (PID: 7312)
- MicrosoftEdge_X64_135.0.3179.73.exe (PID: 7232)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
- MicrosoftEdgeUpdate.exe (PID: 7648)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7648)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdate.exe (PID: 7536)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7484)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7476)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5008)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 7356)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- msedgewebview2.exe (PID: 7368)
- jjsploit.exe (PID: 7800)
Application launched itself
- setup.exe (PID: 7312)
- MicrosoftEdgeUpdate.exe (PID: 7356)
- msedgewebview2.exe (PID: 7368)
Creates a software uninstall entry
- setup.exe (PID: 7312)
Searches for installed software
- setup.exe (PID: 7312)
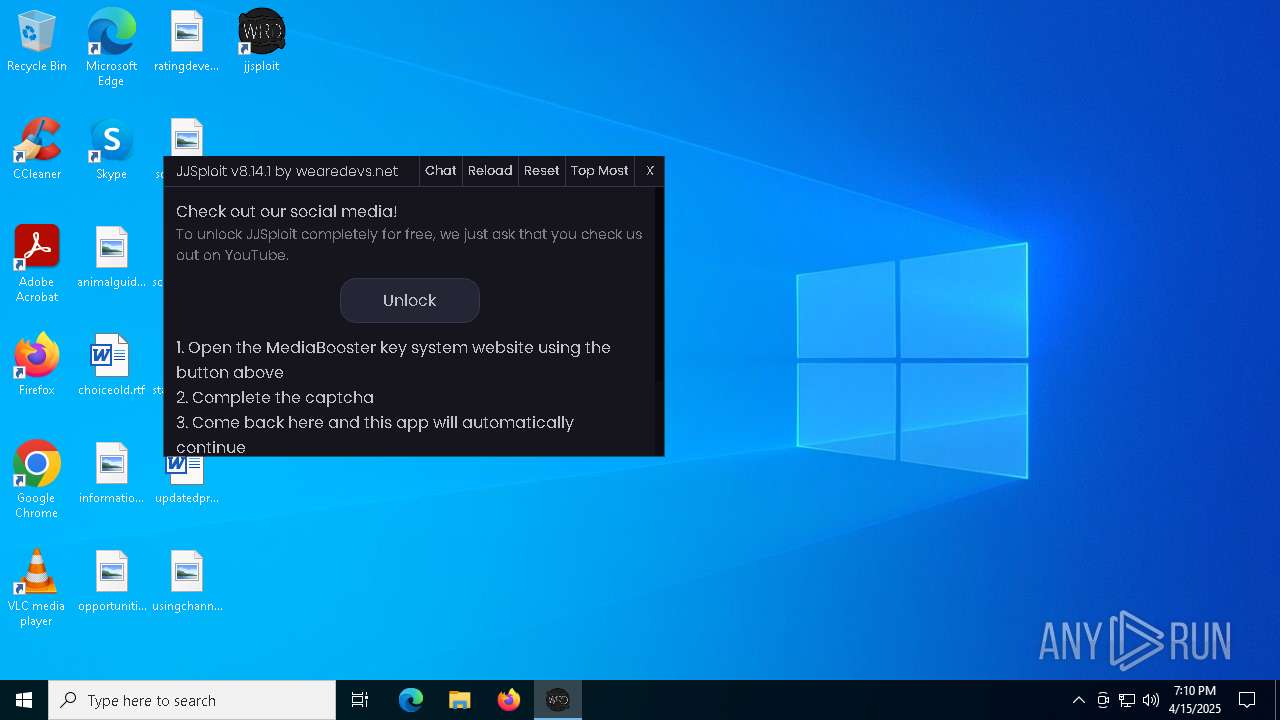
The process checks if it is being run in the virtual environment
- jjsploit.exe (PID: 7800)
INFO
Application launched itself
- chrome.exe (PID: 7380)
- msedge.exe (PID: 8444)
- msedge.exe (PID: 8064)
Reads the computer name
- msiexec.exe (PID: 4068)
- msiexec.exe (PID: 6192)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- MicrosoftEdgeUpdate.exe (PID: 7536)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5008)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7484)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7476)
- MicrosoftEdgeUpdate.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 7360)
- MicrosoftEdgeUpdate.exe (PID: 7356)
- MicrosoftEdge_X64_135.0.3179.73.exe (PID: 7232)
- setup.exe (PID: 7312)
- MicrosoftEdgeUpdate.exe (PID: 6416)
- jjsploit.exe (PID: 7800)
- msedgewebview2.exe (PID: 7368)
- msedgewebview2.exe (PID: 7988)
- msedgewebview2.exe (PID: 7980)
- identity_helper.exe (PID: 8468)
- identity_helper.exe (PID: 4620)
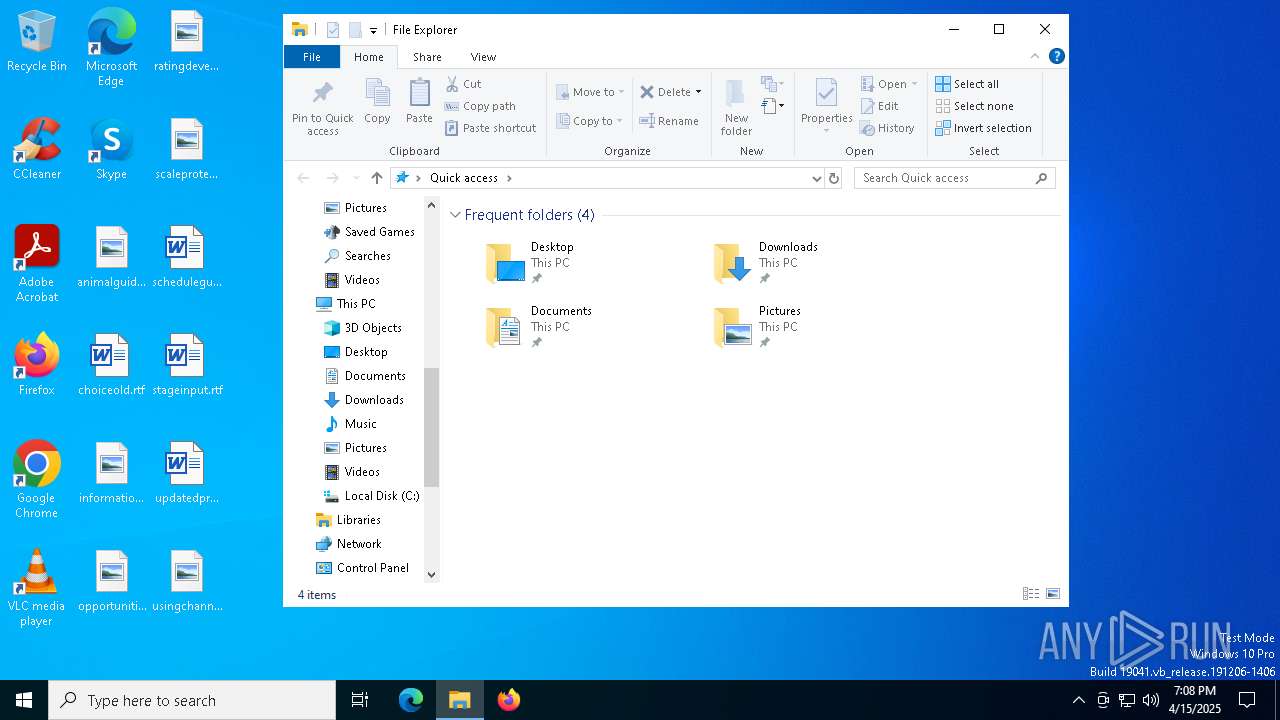
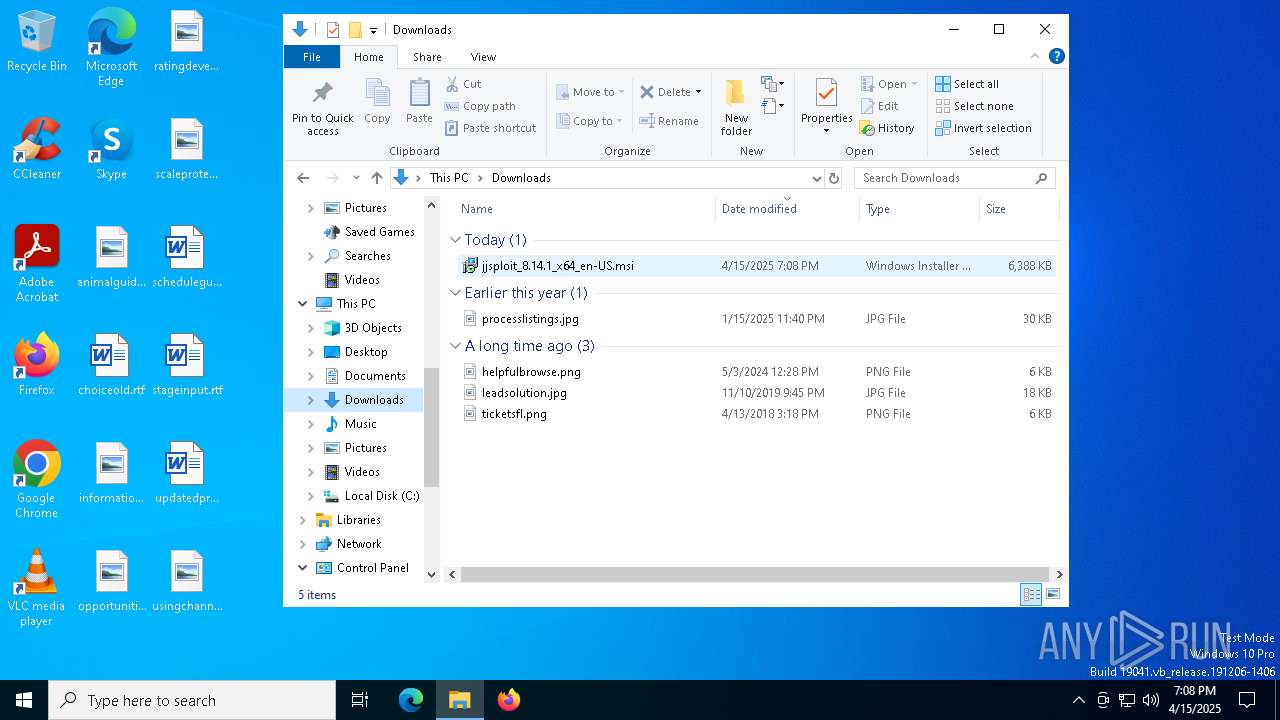
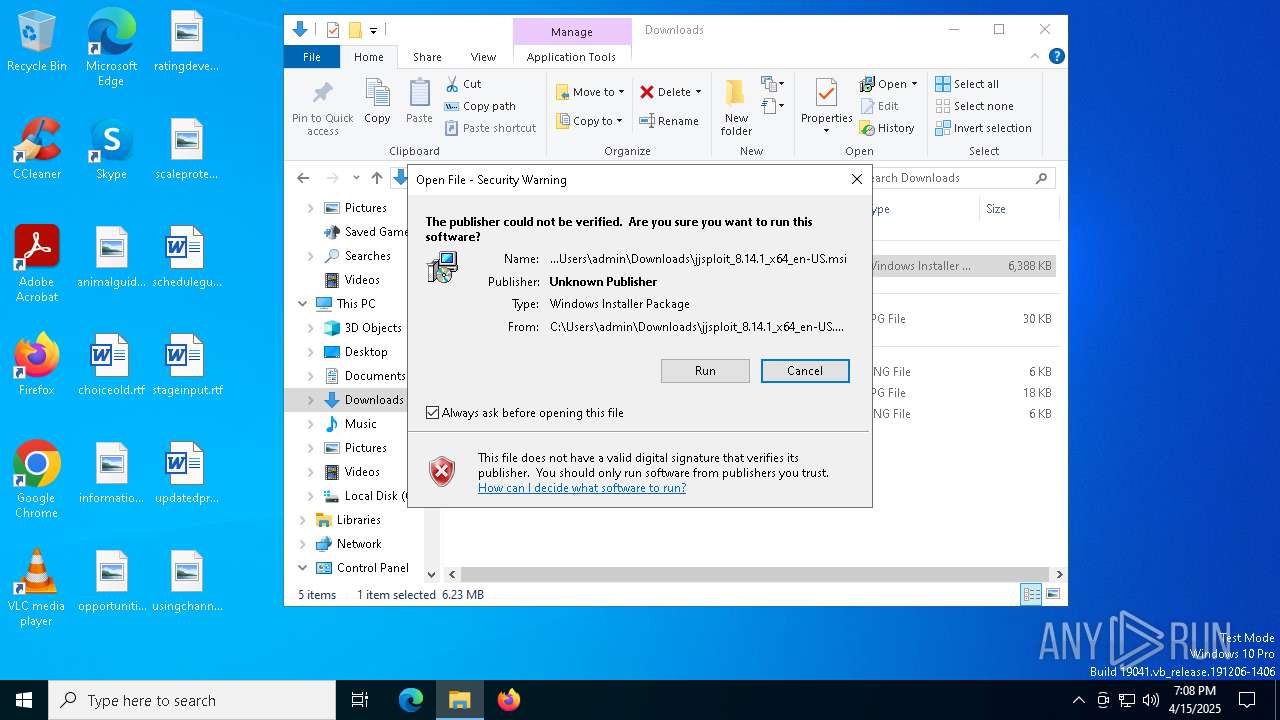
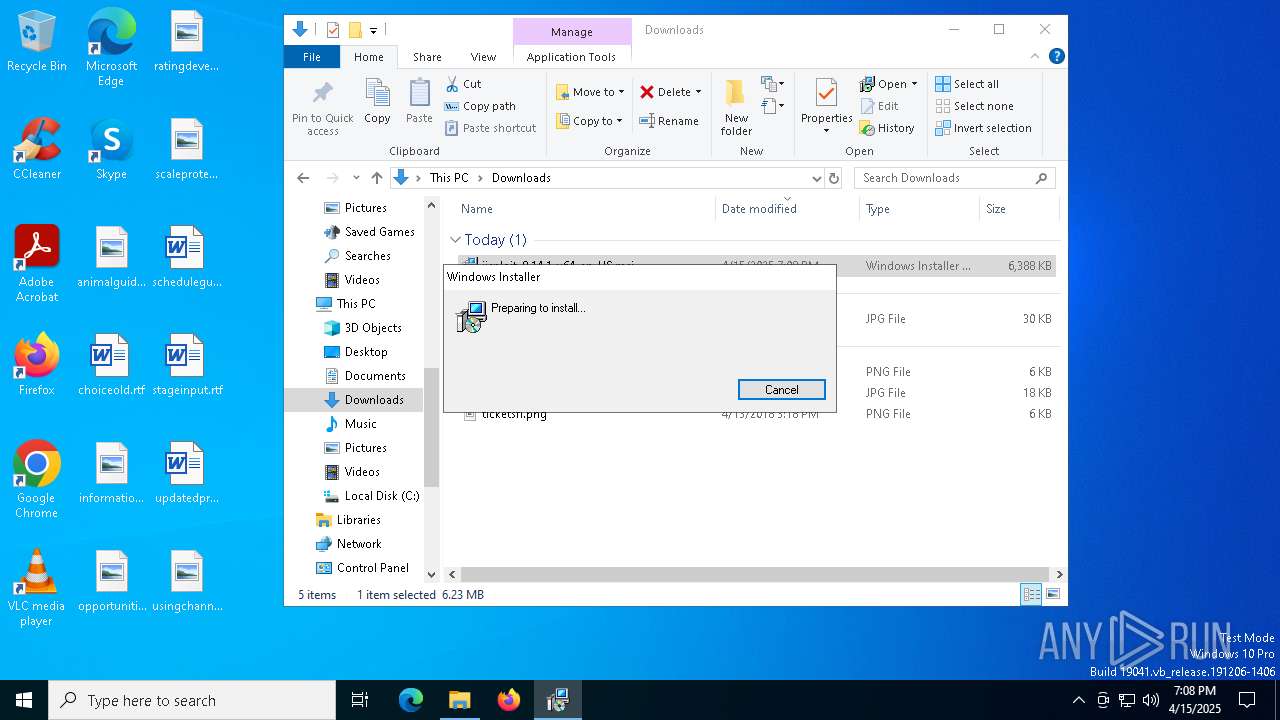
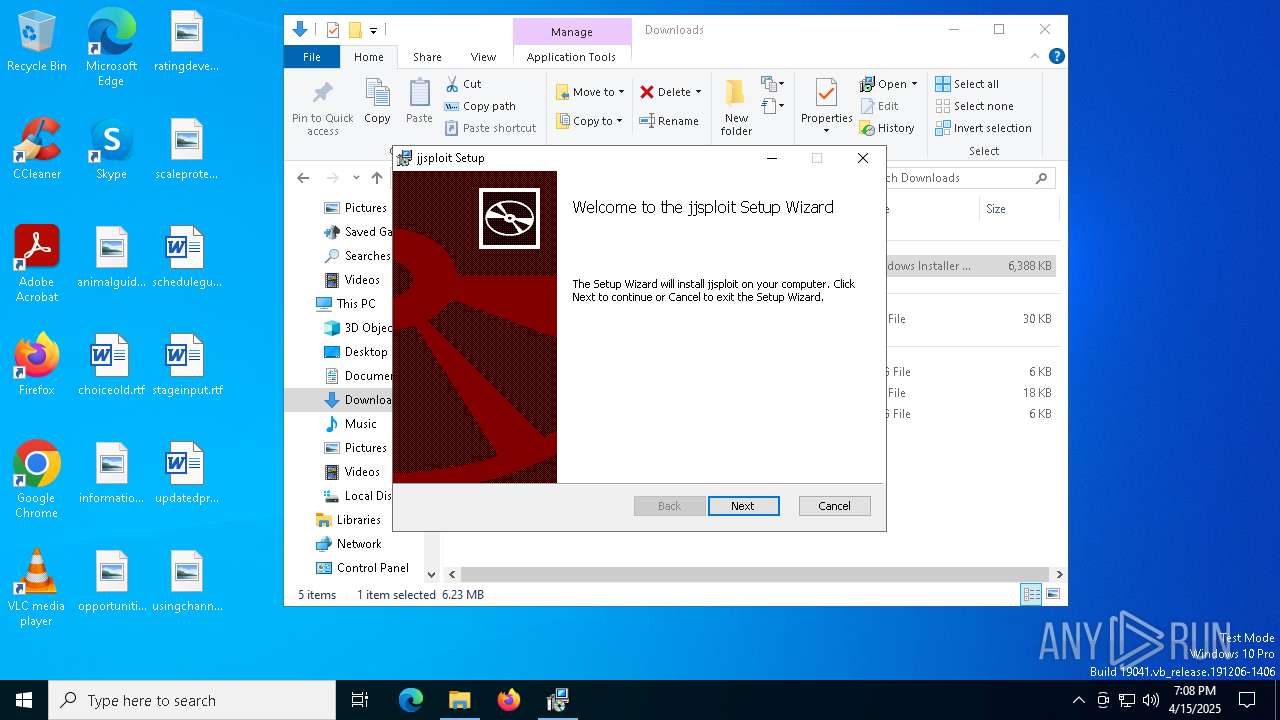
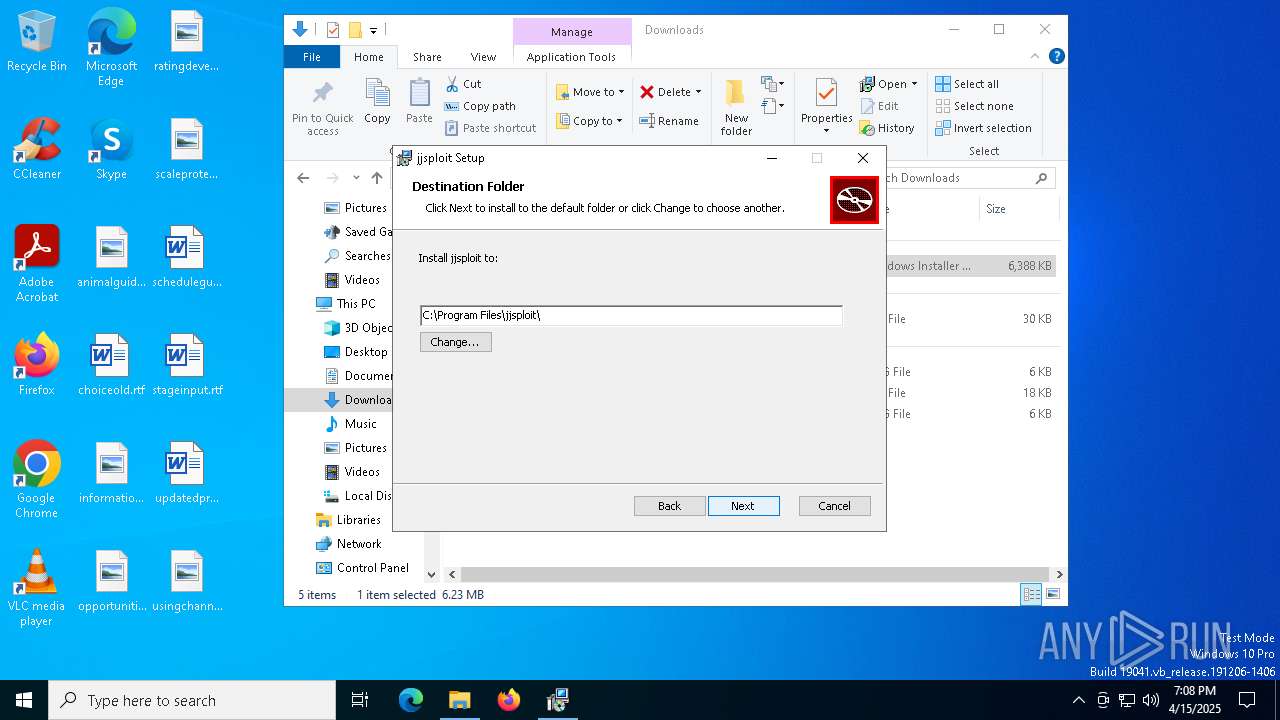
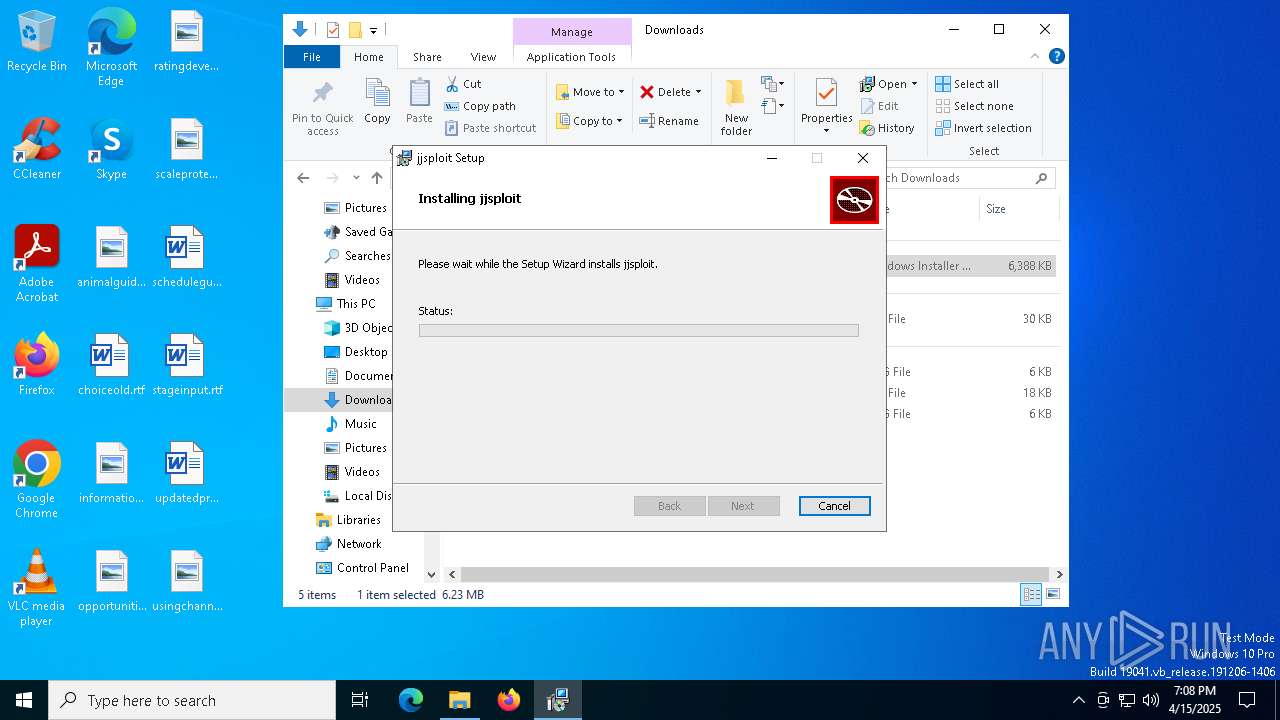
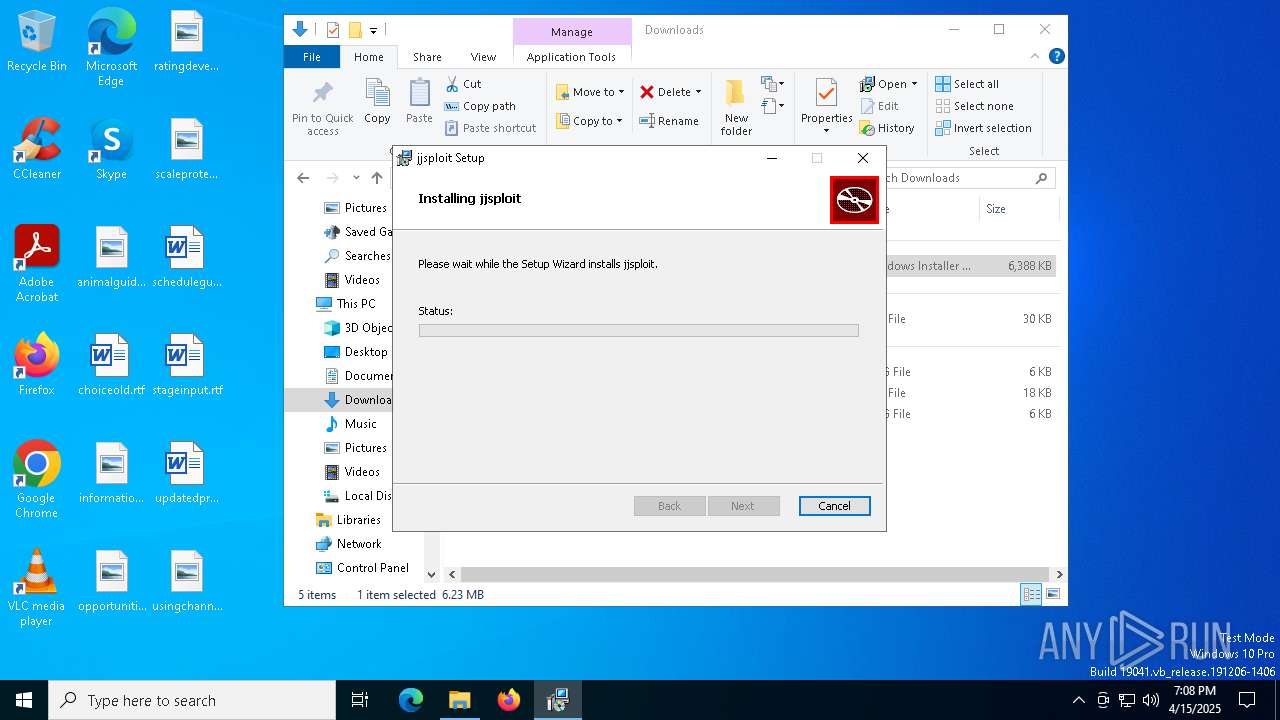
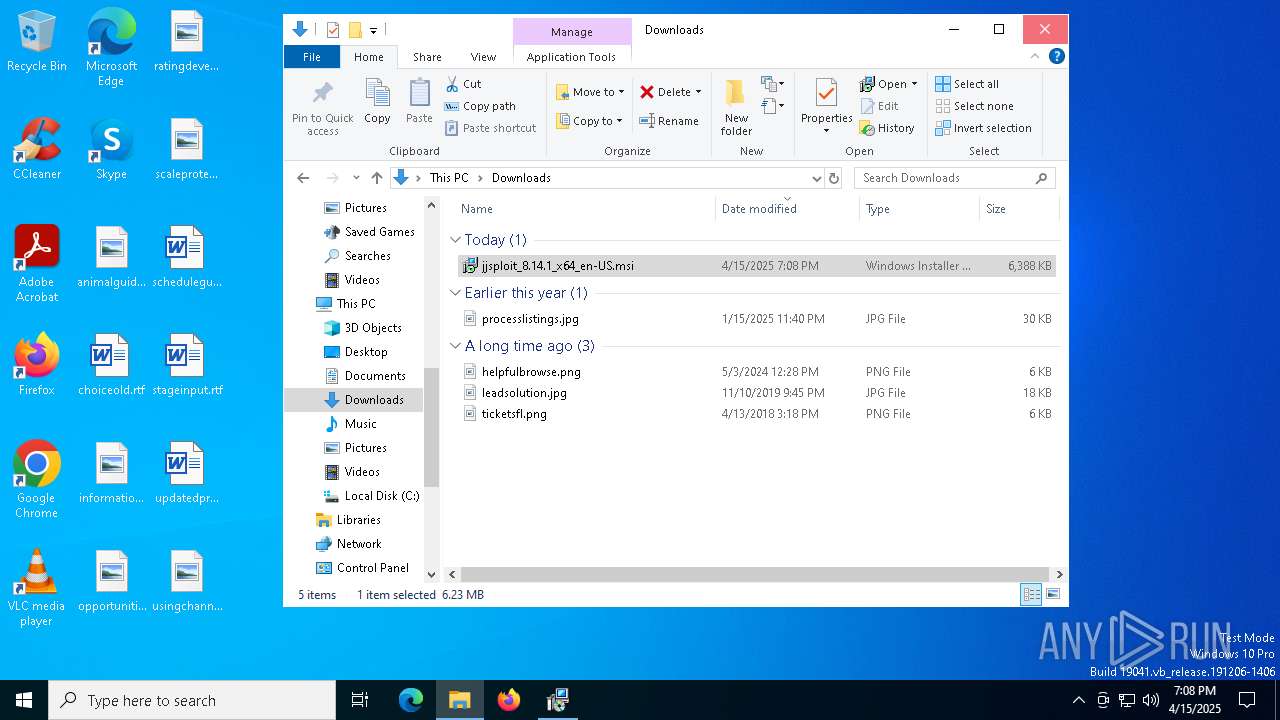
Manual execution by a user
- msiexec.exe (PID: 632)
Checks supported languages
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 4068)
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5008)
- MicrosoftEdgeUpdate.exe (PID: 7536)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7484)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7476)
- MicrosoftEdgeUpdate.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 7356)
- MicrosoftEdgeUpdate.exe (PID: 7360)
- MicrosoftEdge_X64_135.0.3179.73.exe (PID: 7232)
- setup.exe (PID: 7312)
- setup.exe (PID: 2064)
- jjsploit.exe (PID: 7800)
- msedgewebview2.exe (PID: 7368)
- MicrosoftEdgeUpdate.exe (PID: 6416)
- msedgewebview2.exe (PID: 7988)
- msedgewebview2.exe (PID: 2960)
- msedgewebview2.exe (PID: 7980)
- msedgewebview2.exe (PID: 6244)
- msedgewebview2.exe (PID: 3796)
- identity_helper.exe (PID: 8468)
- identity_helper.exe (PID: 4620)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4068)
- msiexec.exe (PID: 632)
Manages system restore points
- SrTasks.exe (PID: 8040)
Creates a software uninstall entry
- msiexec.exe (PID: 4068)
Disables trace logs
- powershell.exe (PID: 7692)
Checks proxy server information
- powershell.exe (PID: 7692)
- MicrosoftEdgeUpdate.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 7356)
- slui.exe (PID: 5576)
- MicrosoftEdgeUpdate.exe (PID: 6416)
- msedgewebview2.exe (PID: 7368)
- jjsploit.exe (PID: 7800)
The sample compiled with english language support
- powershell.exe (PID: 7692)
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- setup.exe (PID: 7312)
- MicrosoftEdge_X64_135.0.3179.73.exe (PID: 7232)
- jjsploit.exe (PID: 7800)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- msedgewebview2.exe (PID: 7368)
- jjsploit.exe (PID: 7800)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 7624)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 6416)
- msedgewebview2.exe (PID: 7368)
- identity_helper.exe (PID: 8468)
- identity_helper.exe (PID: 4620)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 7648)
- MicrosoftEdgeUpdate.exe (PID: 7356)
- MicrosoftEdge_X64_135.0.3179.73.exe (PID: 7232)
- setup.exe (PID: 2064)
- setup.exe (PID: 7312)
- msedgewebview2.exe (PID: 2960)
- msedgewebview2.exe (PID: 7368)
- msedgewebview2.exe (PID: 7980)
- jjsploit.exe (PID: 7800)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 7648)
- setup.exe (PID: 7312)
- msedgewebview2.exe (PID: 7368)
- msedgewebview2.exe (PID: 3796)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 6148)
- MicrosoftEdgeUpdate.exe (PID: 7356)
- slui.exe (PID: 8104)
- slui.exe (PID: 5576)
- MicrosoftEdgeUpdate.exe (PID: 6416)
- jjsploit.exe (PID: 7800)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 7356)
- msedgewebview2.exe (PID: 7368)
Reads CPU info
- msedgewebview2.exe (PID: 7368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
103
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\Downloads\jjsploit_8.14.1_x64_en-US.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2300 --field-trial-handle=2332,i,6146243709698318805,3341925529908909448,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6328 --field-trial-handle=2332,i,6146243709698318805,3341925529908909448,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4440 --field-trial-handle=2332,i,6146243709698318805,3341925529908909448,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2064 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{5B181516-0D8B-4B86-B8FB-B52DE49036C4}\EDGEMITMP_54F83.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=135.0.7049.85 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{5B181516-0D8B-4B86-B8FB-B52DE49036C4}\EDGEMITMP_54F83.tmp\setup.exe --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=135.0.3179.73 --initial-client-data=0x24c,0x250,0x254,0x228,0x258,0x7ff65a12c888,0x7ff65a12c894,0x7ff65a12c8a0 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{5B181516-0D8B-4B86-B8FB-B52DE49036C4}\EDGEMITMP_54F83.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 135.0.3179.73 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=4924 --field-trial-handle=1896,i,16131458438874620289,14678132312014487460,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6096 --field-trial-handle=2332,i,6146243709698318805,3341925529908909448,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4424 --field-trial-handle=1896,i,16131458438874620289,14678132312014487460,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=4472 --field-trial-handle=1896,i,16131458438874620289,14678132312014487460,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=6408 --field-trial-handle=2332,i,6146243709698318805,3341925529908909448,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
33 441
Read events
30 694
Write events
2 661
Delete events
86
Modification events
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5504) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000008CC201B639AEDB01 | |||
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (7380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (4068) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000CBC430BF39AEDB01E40F000060140000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000CBC430BF39AEDB01E40F000060140000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
233
Suspicious files
376
Text files
135
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c20a.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c20a.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c219.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c219.TMP | — | |
MD5:— | SHA256:— | |||
| 7380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c219.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
223
DNS requests
207
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5376 | svchost.exe | HEAD | 200 | 2.16.16.146:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8c49ad4b-ce37-4643-875c-49c3054ce2e6?P1=1745348926&P2=404&P3=2&P4=mK5A3INmFTf8Ee8ztHMJSTYZ3h76X3kKOglJ3vZltwN%2bel3%2fOYqd5IFPtRfuu62KTo6ADrLeOyB73GfrDqGU8g%3d%3d | unknown | — | — | whitelisted |
1244 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1244 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5376 | svchost.exe | GET | — | 2.16.16.146:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8c49ad4b-ce37-4643-875c-49c3054ce2e6?P1=1745348926&P2=404&P3=2&P4=mK5A3INmFTf8Ee8ztHMJSTYZ3h76X3kKOglJ3vZltwN%2bel3%2fOYqd5IFPtRfuu62KTo6ADrLeOyB73GfrDqGU8g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.24.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7380 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7600 | chrome.exe | 104.26.6.147:443 | wearedevs.net | CLOUDFLARENET | US | whitelisted |
7600 | chrome.exe | 108.177.14.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7600 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
wearedevs.net |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
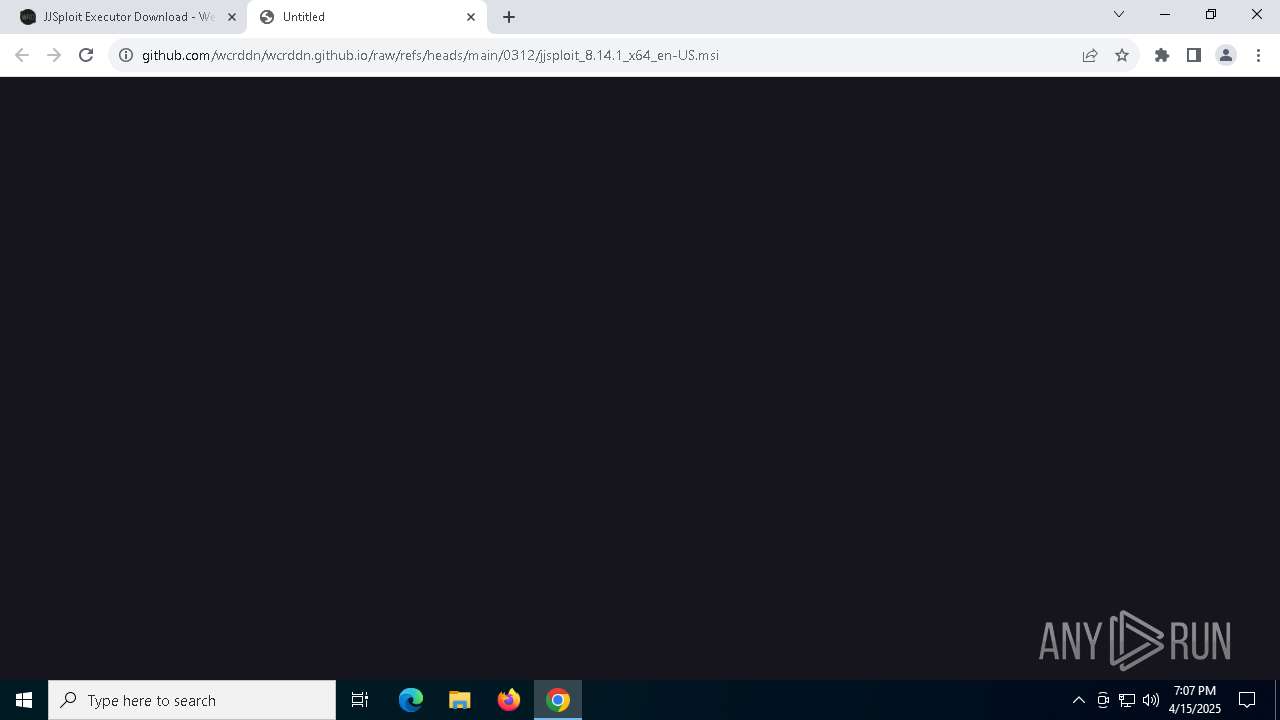
7600 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7600 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Misc activity | ET INFO Packed Executable Download |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7980 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |