| download: | index.html |
| Full analysis: | https://app.any.run/tasks/b91d6ac8-9e10-4e77-8b74-1c1eabf486bb |
| Verdict: | No threats detected |
| Analysis date: | December 15, 2019, 15:36:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 99319DD0D018B791F6A31285E4D85346 |
| SHA1: | 121C513C5DF75E060AF71C51C456297CA6163429 |
| SHA256: | 4833F97AB979465D28269B780061DB1A6C11157680D773102F828BED252C1A95 |
| SSDEEP: | 1536:SBida1kOBvcXyCMCMCMCq667Z0Z0ZIcT9rUOUjCiiHtVLL+e2ojB2rQjzV:SqXyCMCMCMCq667Z0Z0ZPTP+e2eVZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 944)
Application launched itself
- iexplore.exe (PID: 944)
Reads internet explorer settings
- iexplore.exe (PID: 3308)
Creates files in the user directory
- iexplore.exe (PID: 3308)
Reads Internet Cache Settings
- iexplore.exe (PID: 3308)
Reads settings of System Certificates
- iexplore.exe (PID: 3308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
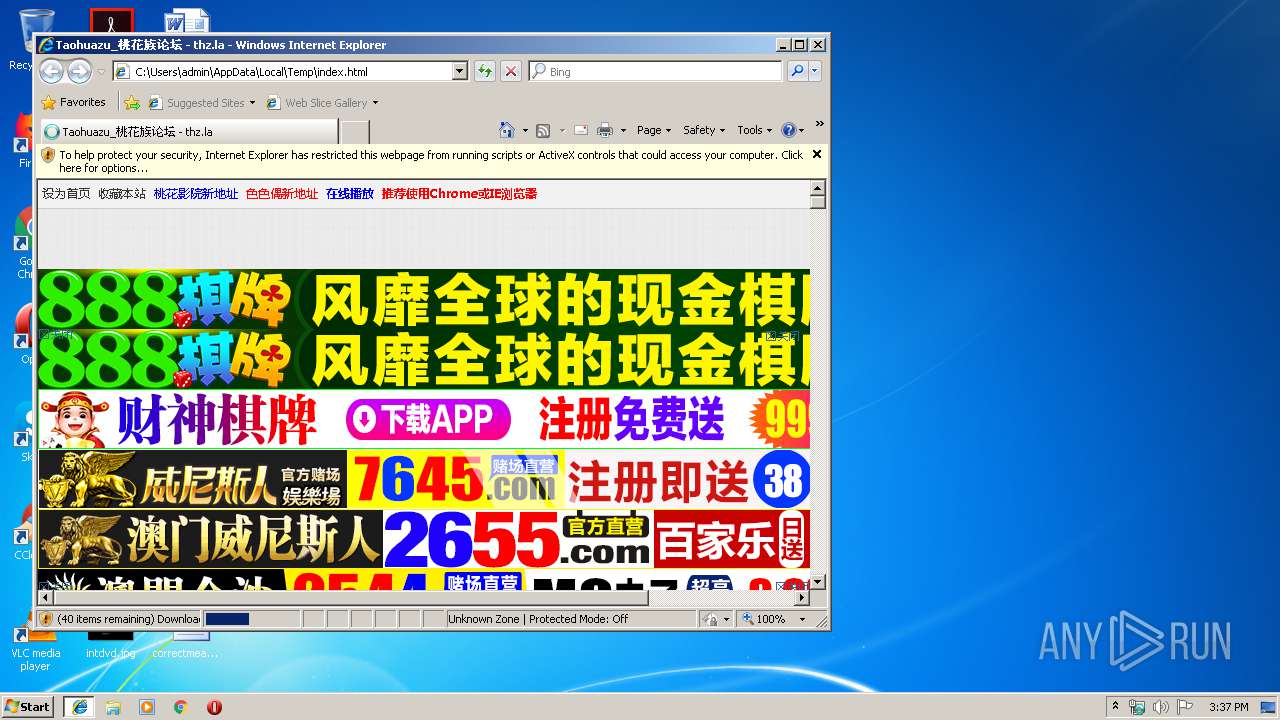
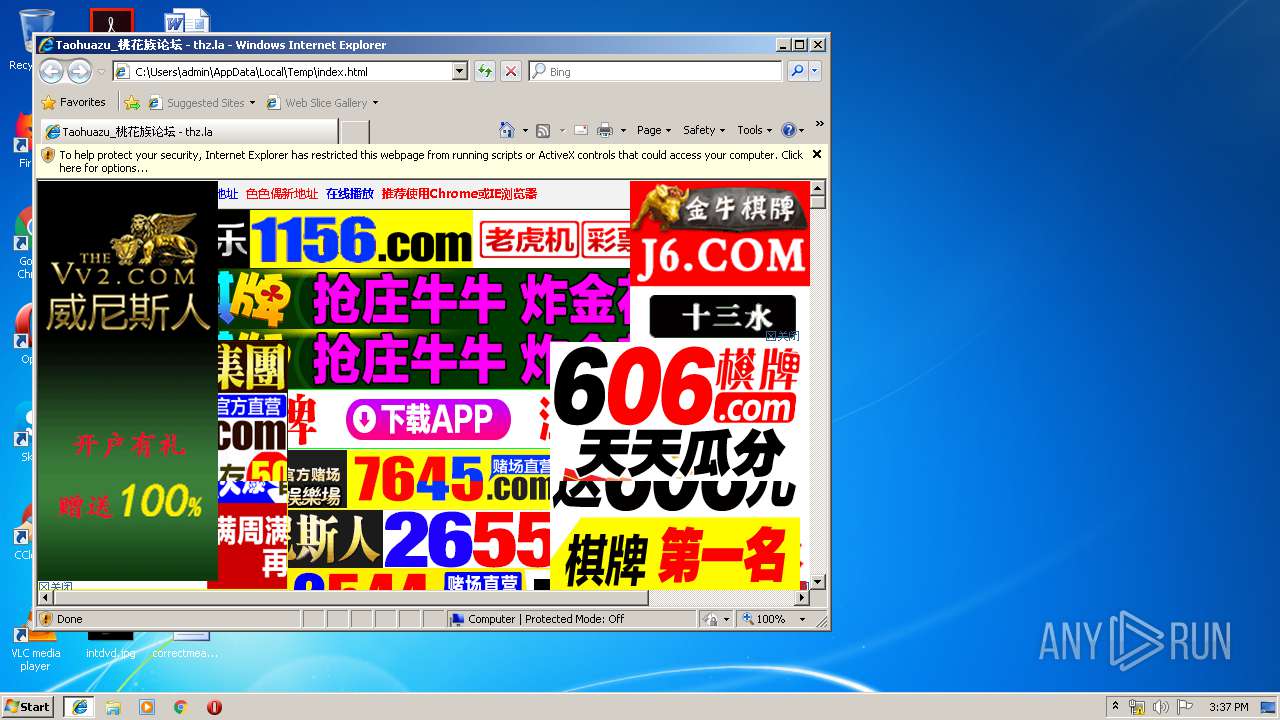
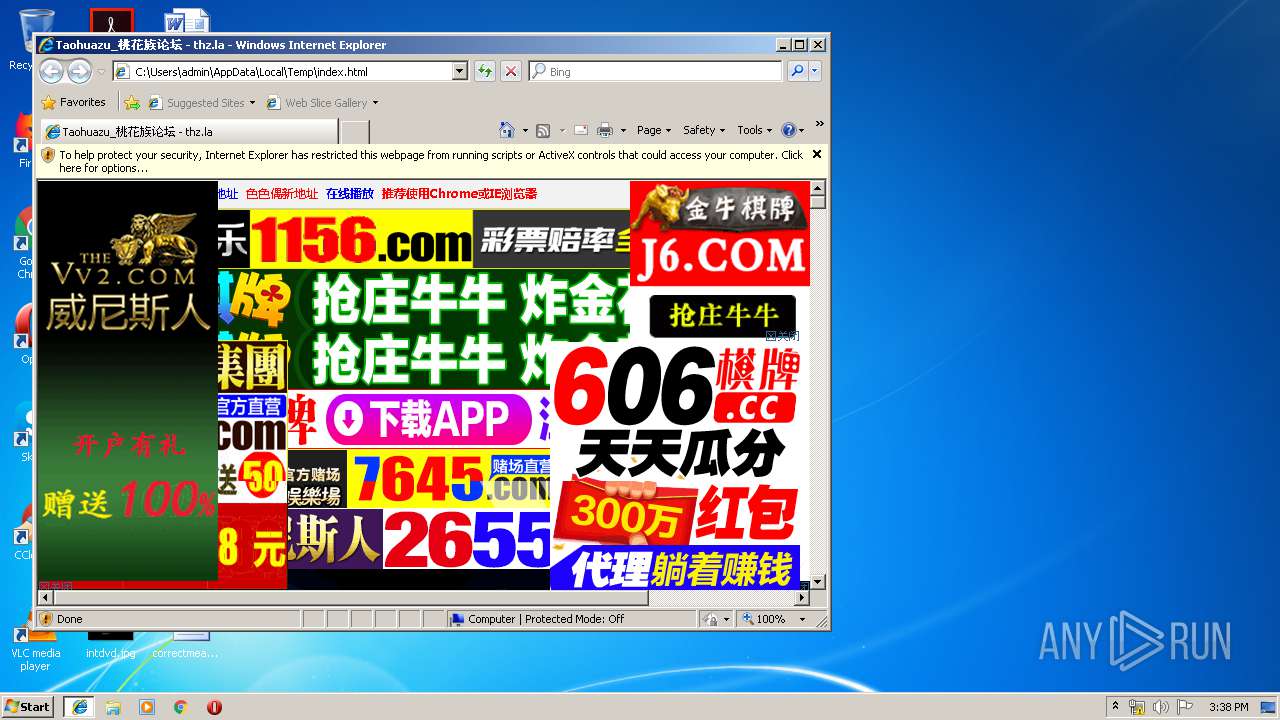
| Title: | Taohuazu_桃花族论坛 - thz.la |
| Keywords: | taohuazu,桃花族论坛,BT工厂,bt天堂 |
| Description: | Taohuazu.com桃花族论坛一手资源,是资源天堂,要找资源网站就来taohuzu,每天都有最新免费资源分享给大家! |
| Generator: | Discuz! X3.2 |
| Author: | Discuz! Team and Comsenz UI Team |
| Copyright: | 2001-2013 Comsenz Inc. |
| NoMSSmartTags: | |
| HTTPEquivMSThemeCompatible: | Yes |
| applicationName: | Taohuazu_桃花族 |
| msapplicationTooltip: | Taohuazu_桃花族 |
| msapplicationTask: | name=论坛;action-uri=http://thzggg.com/forum.php;icon-uri=http://thzggg.com/template/wxd_thinkpad/wxd_img/bbs.ico |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:944 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
392
Read events
312
Write events
79
Delete events
1
Modification events
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BD9C49C7-1F50-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C0000000F000F0025000400DC00 | |||
Executable files
0
Suspicious files
0
Text files
81
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 944 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\forum[1].js | text | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\qmenu[1].png | image | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\bg[1].png | image | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\pn[1].png | image | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\nv[1].png | image | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\common[1].js | text | |
MD5:50F0D382FB2F28AC80712B7BD08D696D | SHA256:F3F7C4045887E89F7D423ED92ED9D95F4DC8EC0229FCAA365F86F762B61E7EF6 | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\logging[1].js | text | |
MD5:4544D50D2DDE9CCCEA8012A9A5D0CFB7 | SHA256:843CA4CCC43F7C97D0F24897B2890A713355E0E5E89F6A96001E663E10282B45 | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\style_14_common[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
36
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | iexplore.exe | GET | 200 | 23.234.22.82:80 | http://thzggg.com/data/cache/forum.js?S5K | US | text | 6.72 Kb | unknown |
3308 | iexplore.exe | GET | 200 | 23.234.22.82:80 | http://thzggg.com/data/cache/style_14_forum_index.css?S5K | US | text | 1.21 Kb | unknown |
3308 | iexplore.exe | GET | 200 | 23.234.22.82:80 | http://thzggg.com/template/wxd_thinkpad/wxd_img/bg.png | US | image | 1.93 Kb | unknown |
3308 | iexplore.exe | GET | 200 | 23.225.34.138:80 | http://pic.cytcm.com/2019250044/960-60.gif | US | image | 236 Kb | suspicious |
3308 | iexplore.exe | GET | 200 | 23.234.22.82:80 | http://thzggg.com/template/wxd_thinkpad/wxd_img/logo.png | US | image | 15.1 Kb | unknown |
3308 | iexplore.exe | GET | 200 | 23.234.22.82:80 | http://thzggg.com/template/wxd_thinkpad/wxd_img/pn.png | US | image | 1.33 Kb | unknown |
3308 | iexplore.exe | GET | 200 | 23.225.34.138:80 | http://pic.cytcm.com/2019260055/960-60.gif | US | image | 194 Kb | suspicious |
3308 | iexplore.exe | GET | 200 | 47.246.43.251:80 | http://cbu01.alicdn.com/img/ibank/2019/441/888/11903888144_1095372465.jpg | US | image | 217 Kb | whitelisted |
3308 | iexplore.exe | GET | 200 | 47.246.43.251:80 | http://cbu01.alicdn.com/img/ibank/2019/254/967/12395769452_1095372465.jpg | US | image | 597 Kb | whitelisted |
3308 | iexplore.exe | GET | 200 | 47.246.43.251:80 | http://cbu01.alicdn.com/img/ibank/2019/406/694/12565496604_1095372465.jpg | US | image | 674 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | iexplore.exe | 23.225.34.138:80 | pic.cytcm.com | LANLIAN INTERNATIONAL HOLDING GROUP LIMITED | US | suspicious |
944 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3308 | iexplore.exe | 23.38.51.129:443 | sc02.alicdn.com | Akamai International B.V. | NL | whitelisted |
3308 | iexplore.exe | 154.218.3.102:443 | hj776.com | MULTACOM CORPORATION | US | unknown |
3308 | iexplore.exe | 23.234.22.82:80 | thzggg.com | HOSTSPACE NETWORKS LLC | US | unknown |
3308 | iexplore.exe | 184.25.158.9:443 | ae01.alicdn.com | Akamai International B.V. | US | whitelisted |
3308 | iexplore.exe | 47.246.43.251:443 | cbu01.alicdn.com | — | US | suspicious |
3308 | iexplore.exe | 47.246.43.251:80 | cbu01.alicdn.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thzggg.com |
| unknown |
www.bing.com |
| whitelisted |
cbu01.alicdn.com |
| whitelisted |
pic.cytcm.com |
| suspicious |
sc02.alicdn.com |
| whitelisted |
ae01.alicdn.com |
| whitelisted |
hj776.com |
| unknown |