| File name: | PYG.dll |
| Full analysis: | https://app.any.run/tasks/006da643-9a44-46b4-b8b3-f4bb8852541d |
| Verdict: | No threats detected |
| Analysis date: | August 18, 2019, 06:22:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 044C614A2842487C57CE94E224D39CF4 |
| SHA1: | FFD30BAE0649CF9966F8BAD1022F036EC45E61C3 |
| SHA256: | 48299B3F607FFC466404FE2BE02FA8A954DE2949A750397DDD5E3048BFCE52DC |
| SSDEEP: | 12288:lrkwLmvphPdYMPPKFHMVovGzRZDq6sHl7P47TgBIsCfoeuexmShSbOIEL4b0mvy9:BkrBhVpqN0K+5qtocYQ0mSg+uVvX4ZL |
MALICIOUS
No malicious indicators.SUSPICIOUS
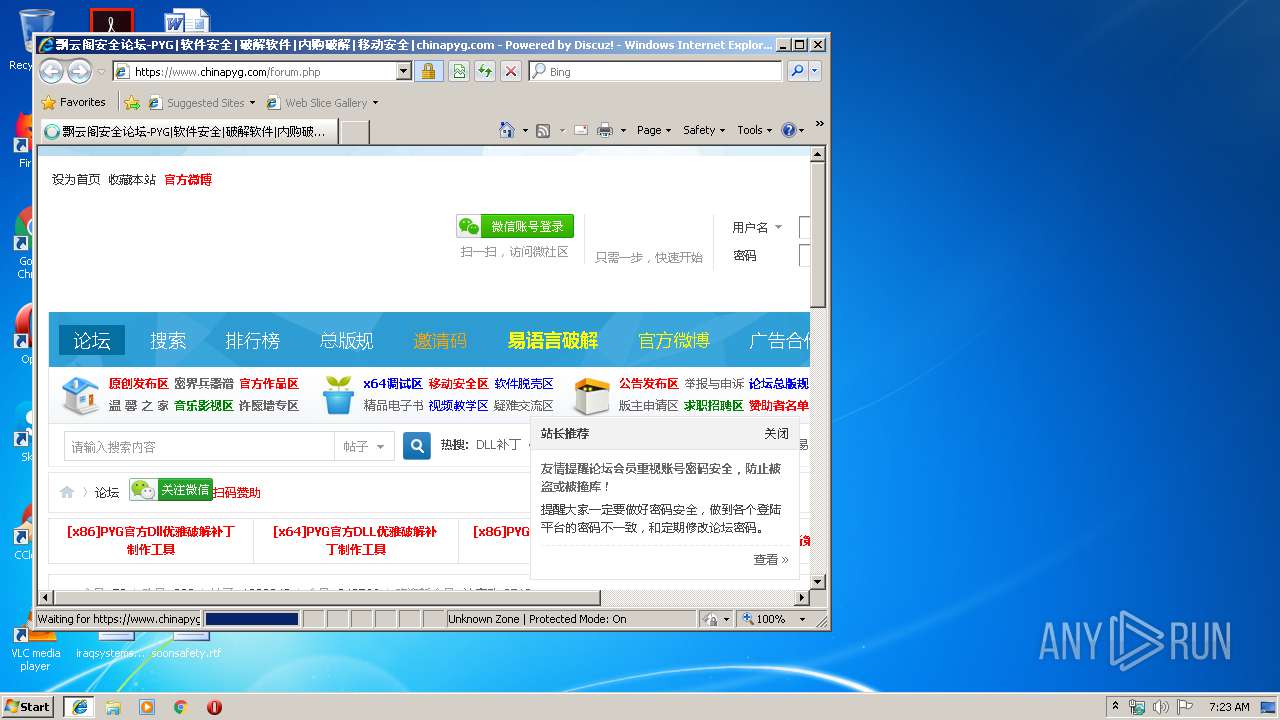
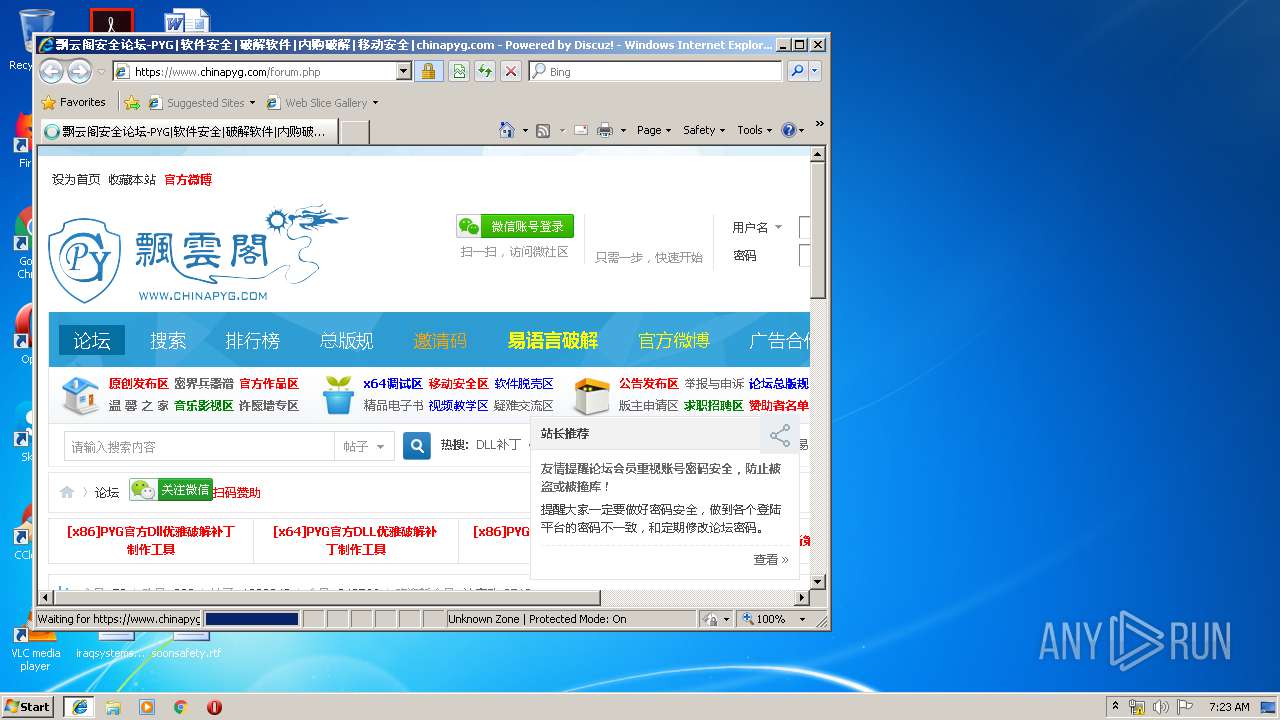
Starts Internet Explorer
- rundll32.exe (PID: 2912)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3004)
INFO
Application launched itself
- iexplore.exe (PID: 3948)
Changes internet zones settings
- iexplore.exe (PID: 3948)
Reads Internet Cache Settings
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 3948)
Loads main object executable
- rundll32.exe (PID: 2912)
Creates files in the user directory
- iexplore.exe (PID: 2292)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3004)
Reads settings of System Certificates
- iexplore.exe (PID: 3948)
Reads internet explorer settings
- iexplore.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:01 06:07:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 342016 |
| InitializedDataSize: | 150016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17a427 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.1.1011 |
| ProductVersionNumber: | 3.0.1.1011 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
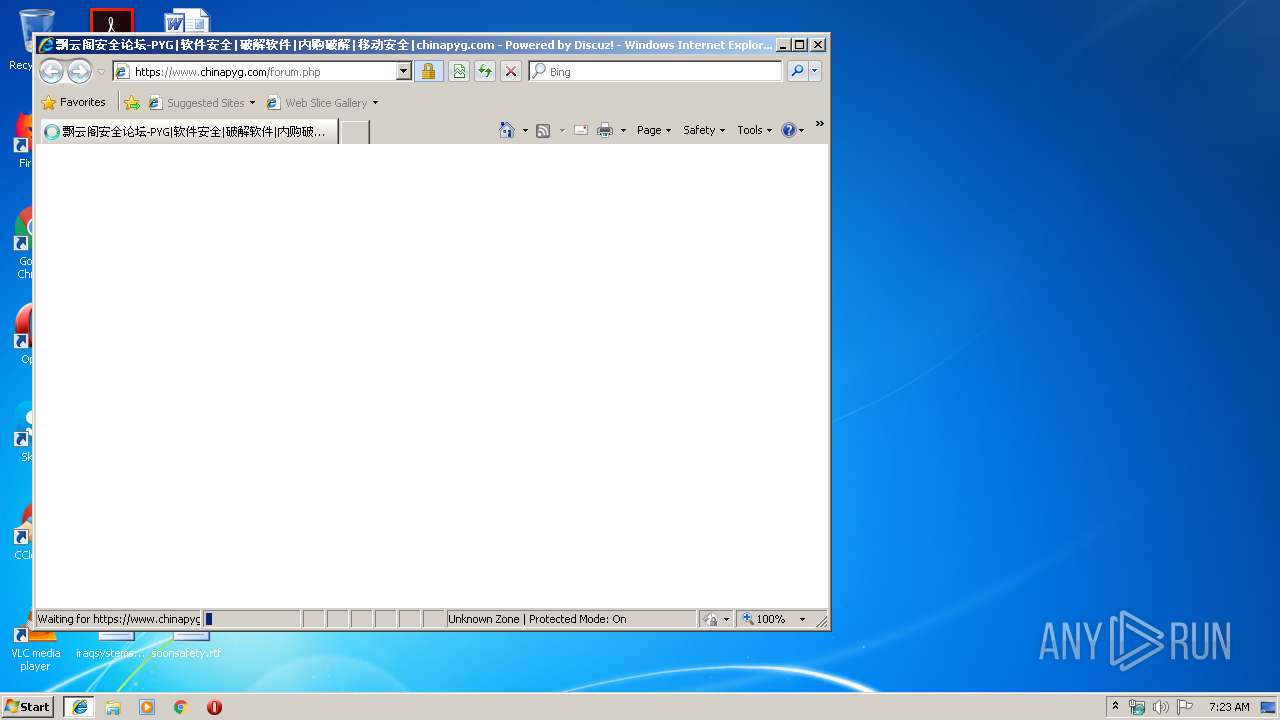
| Comments: | Www.ChinaPYG.CoM |
| CompanyName: | 飘云阁论坛官方出品 |
| FileDescription: | Baymax Patcher Tools |
| FileVersion: | 3, 0, 1, 1011 |
| InternalName: | PYG.dll |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFileName: | PYG.dll |
| ProductName: | PYG |
| ProductVersion: | 3, 0, 1, 1011 |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3948 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\PYG.dll", #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3004 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3948 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
468
Read events
394
Write events
72
Delete events
2
Modification events
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {A077A103-C180-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070800000012000600170001008902 | |||
Executable files
0
Suspicious files
1
Text files
73
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.chinapyg[1].txt | — | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6OABWQA1\forum[1].php | — | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\N5WKFYII\style_14_forum_index[1].css | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\2TWS0KIM\nc[1].js | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WV9UEW5A\csu_zk[1].css | text | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.chinapyg[2].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
19
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3948 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2292 | iexplore.exe | GET | 301 | 47.99.120.21:80 | http://bbs.chinapyg.com/forum.php | CN | html | 184 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3948 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2292 | iexplore.exe | 47.99.120.21:80 | bbs.chinapyg.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2292 | iexplore.exe | 47.99.120.21:443 | bbs.chinapyg.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2292 | iexplore.exe | 47.246.43.252:443 | g.alicdn.com | — | US | suspicious |
2292 | iexplore.exe | 47.246.43.251:443 | g.alicdn.com | — | US | suspicious |
2292 | iexplore.exe | 116.211.183.234:443 | s22.cnzz.com | CHINANET Hubei province network | CN | suspicious |
2292 | iexplore.exe | 203.119.206.95:443 | hzs1.cnzz.com | — | CN | malicious |
3948 | iexplore.exe | 47.99.120.21:443 | bbs.chinapyg.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2292 | iexplore.exe | 47.88.68.21:443 | cnzz.mmstat.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
bbs.chinapyg.com |
| unknown |
www.chinapyg.com |
| unknown |
g.alicdn.com |
| whitelisted |
at.alicdn.com |
| whitelisted |
img.alicdn.com |
| whitelisted |
s22.cnzz.com |
| suspicious |
hzs1.cnzz.com |
| whitelisted |
c.cnzz.com |
| whitelisted |
cnzz.mmstat.com |
| whitelisted |