| File name: | al-khaser.exe |
| Full analysis: | https://app.any.run/tasks/bc623f07-fef5-4b51-a2d6-ef81a252eb82 |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 17:19:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | E6F50C90322B7F0765F10977031A3712 |
| SHA1: | 287ED21FA7DB27C7CEAF7EEFEDDBBBCB298877B0 |
| SHA256: | 4825E3A250763372FB1B4EC6D6C545C8D4A7213DC826969BD8C372888E29F1B5 |
| SSDEEP: | 6144:muJ1sWHcHJNQhg9c7uLSO/JgzNX2NNNyfCx:vJ1sWyTgJmN9x |
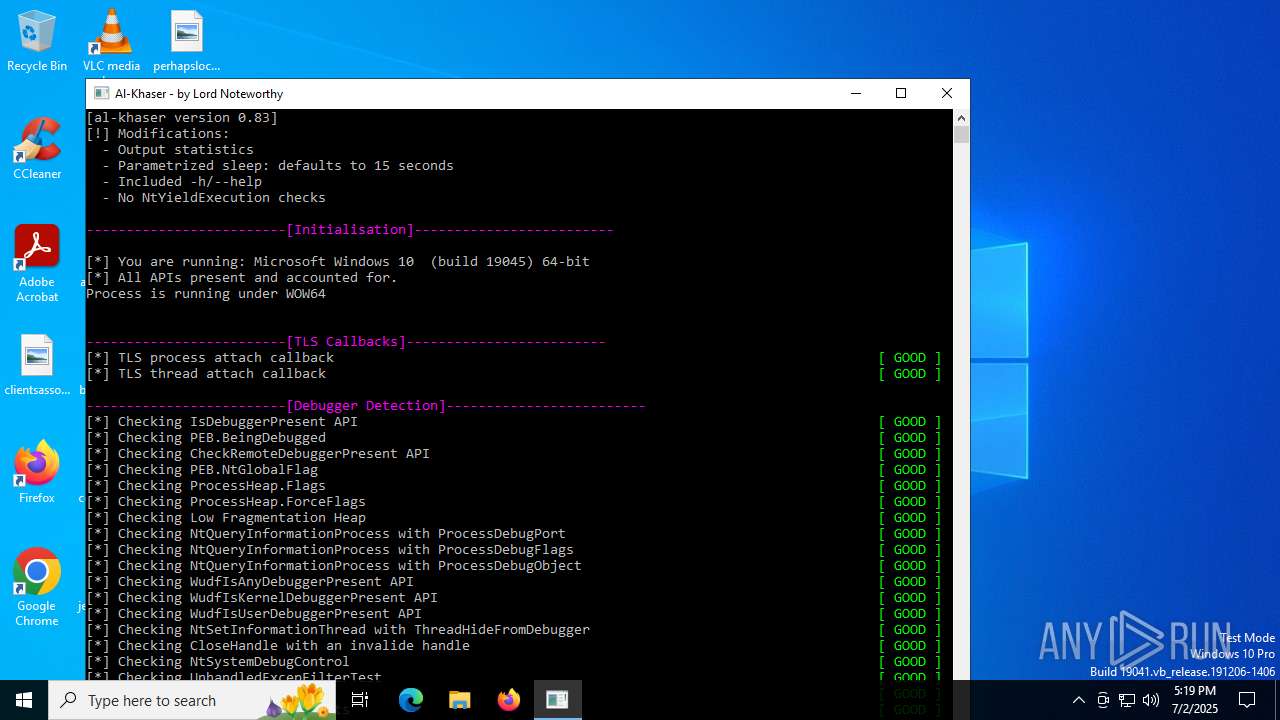
MALICIOUS
No malicious indicators.SUSPICIOUS
Detected use of alternative data streams (AltDS)
- al-khaser.exe (PID: 6240)
There is functionality for taking screenshot (YARA)
- al-khaser.exe (PID: 6240)
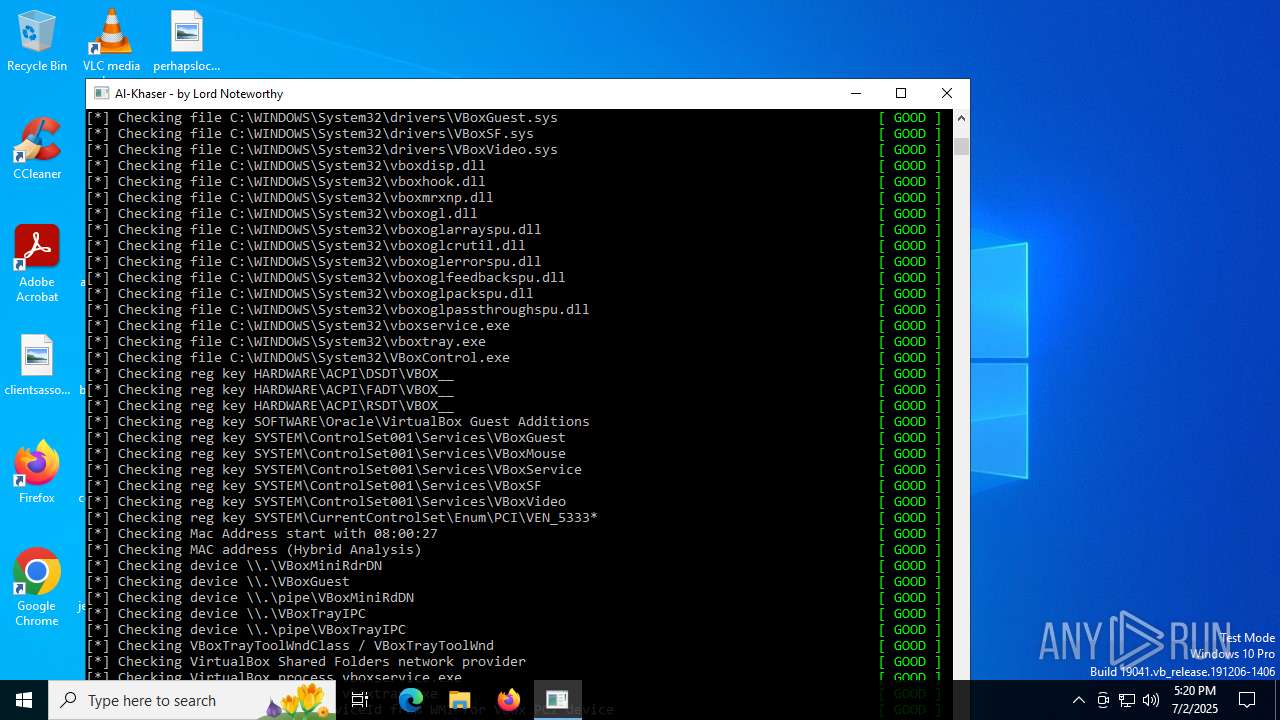
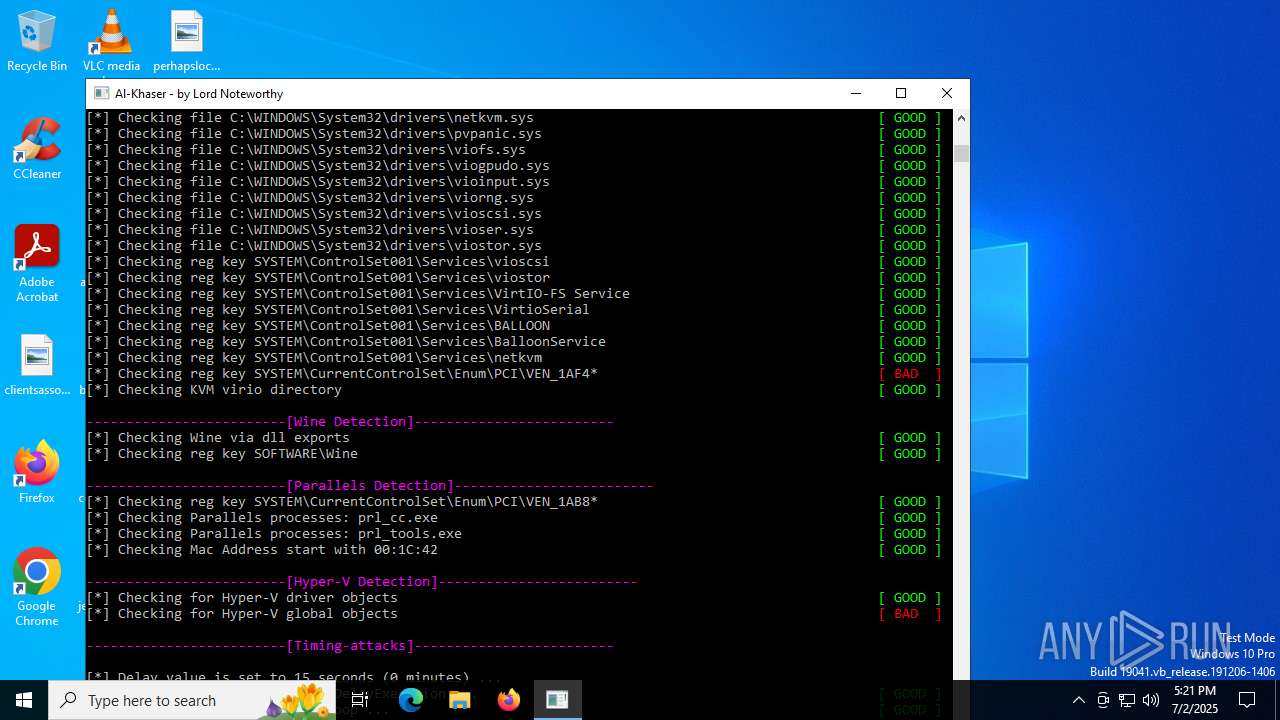
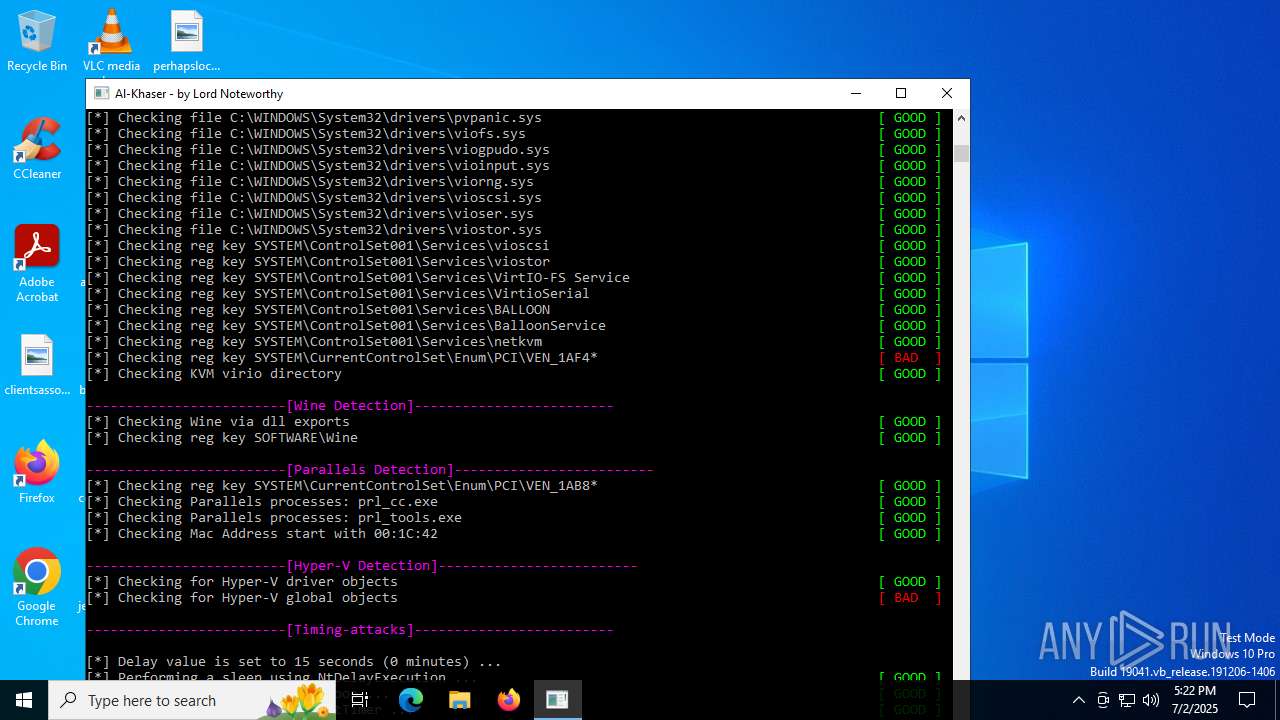
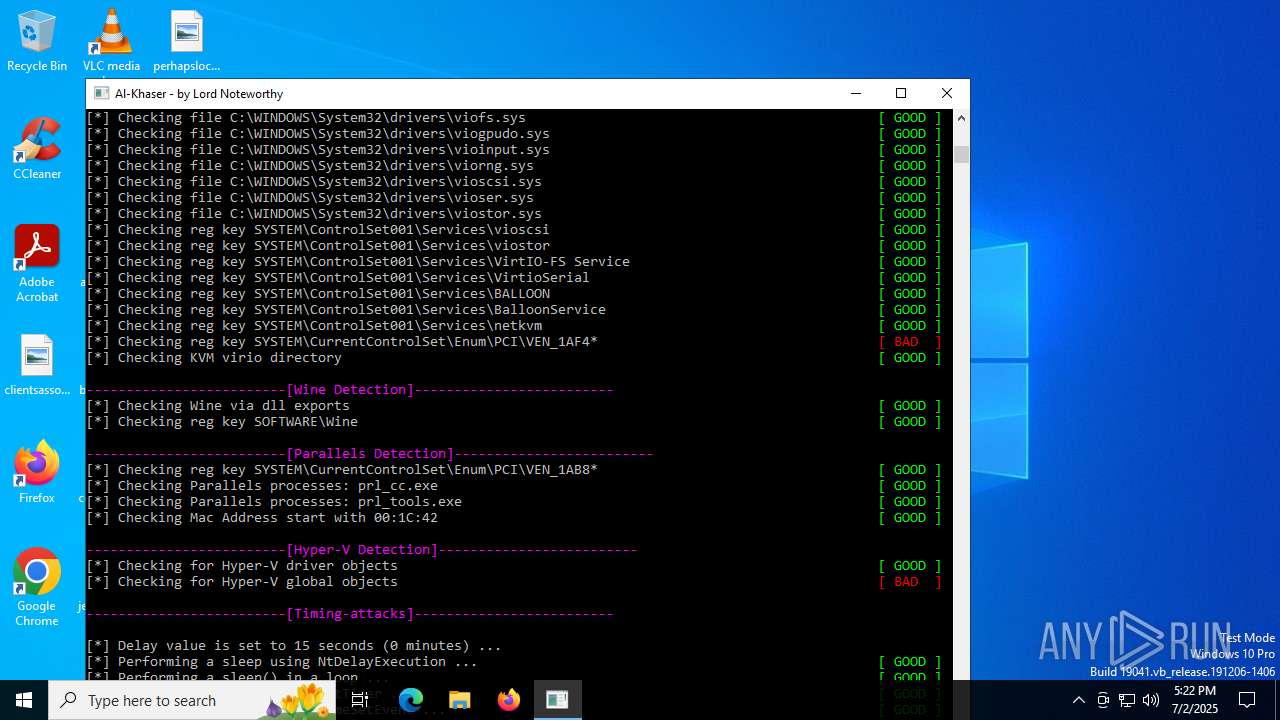
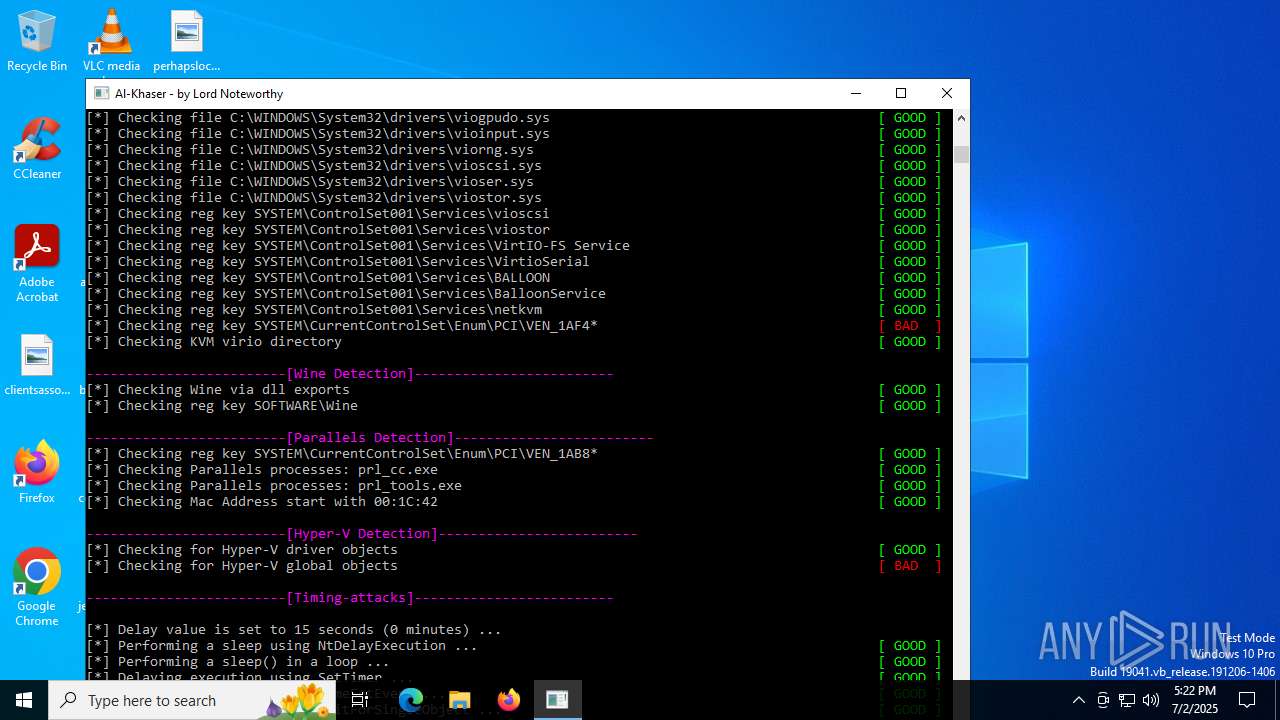
There is functionality for VM detection VirtualBox (YARA)
- al-khaser.exe (PID: 6240)
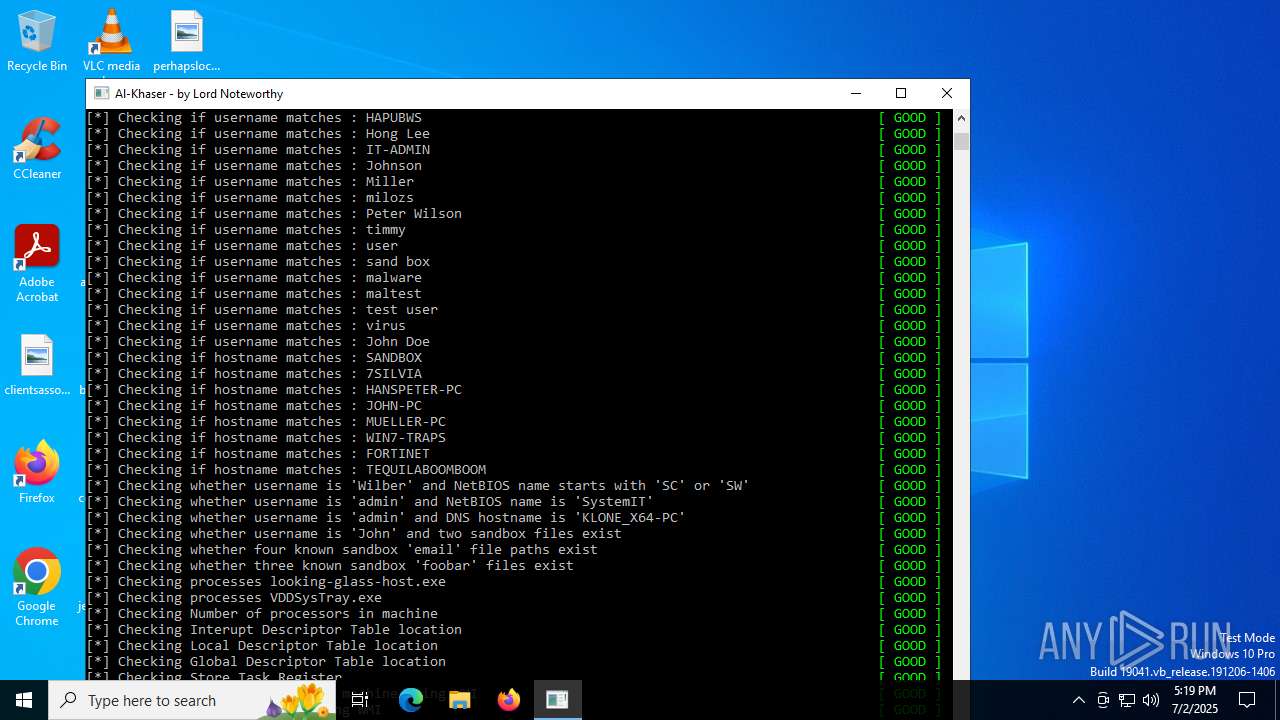
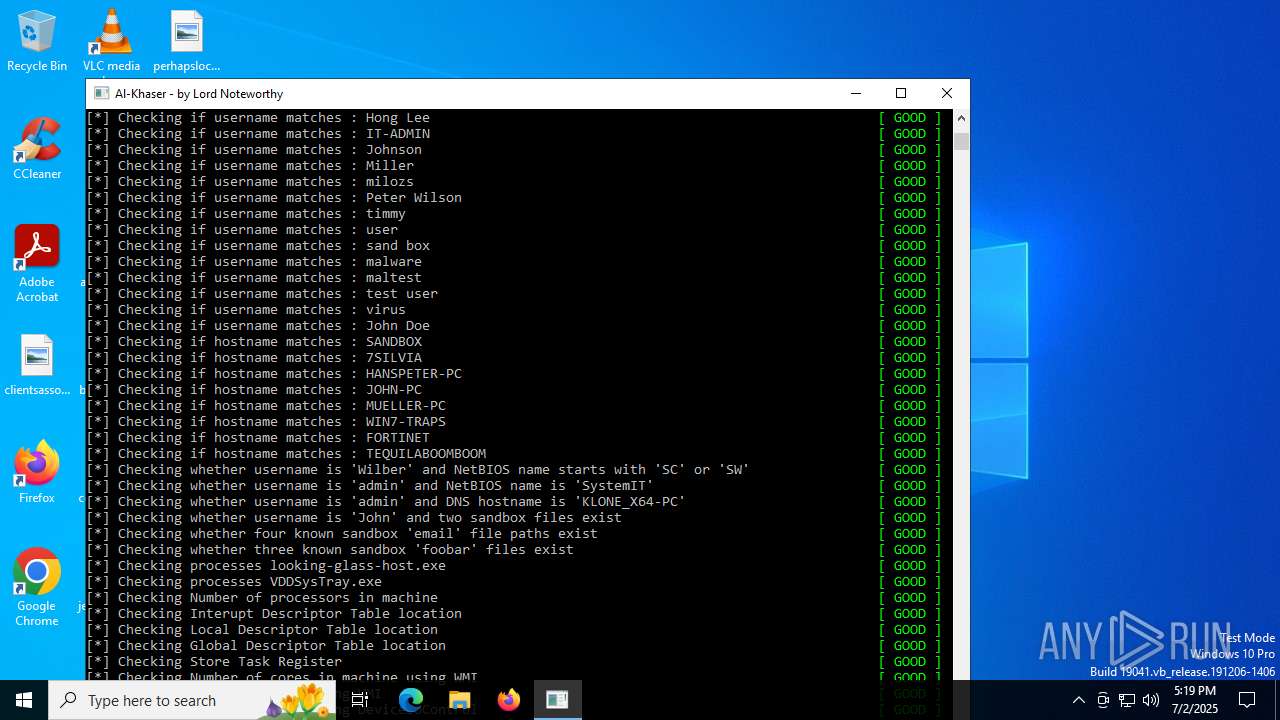
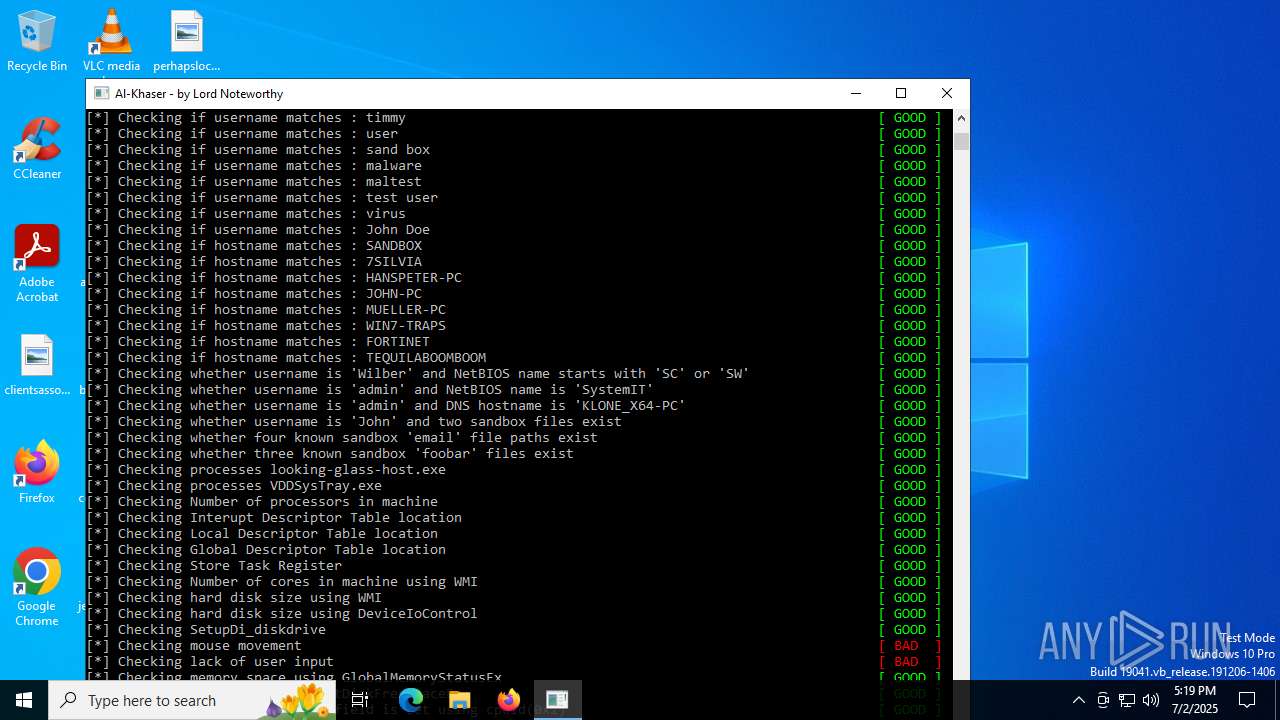
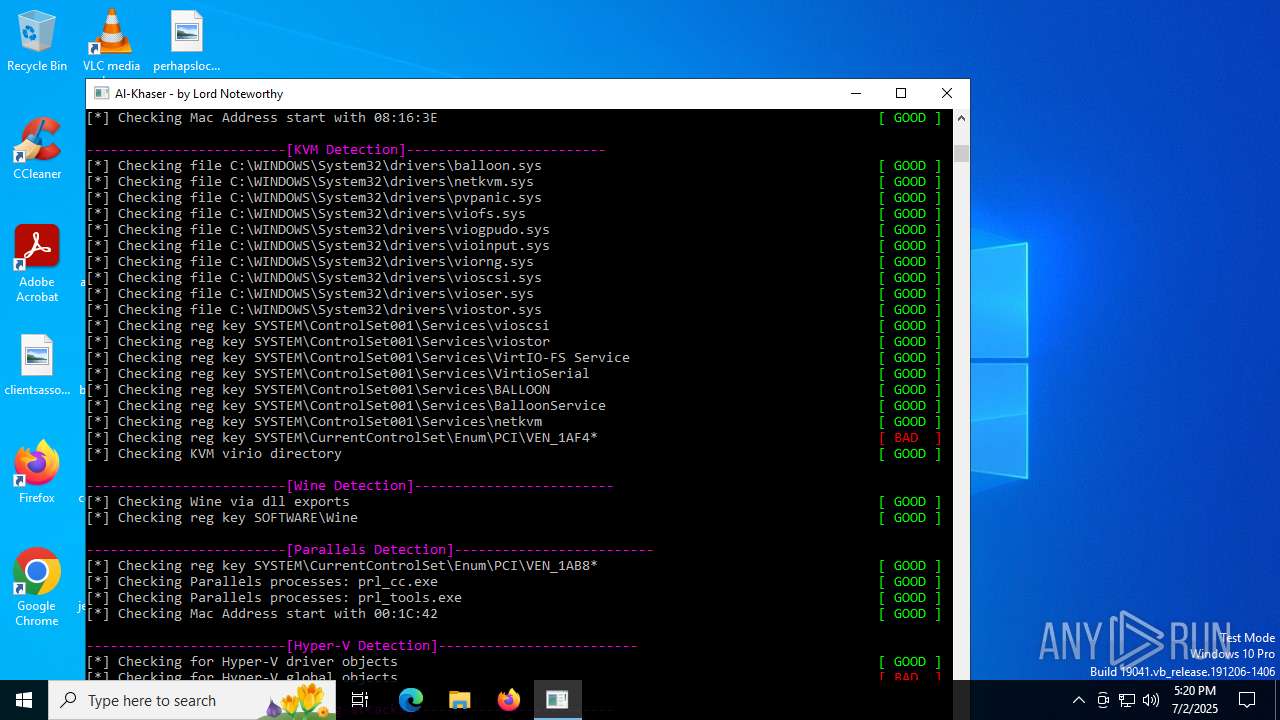
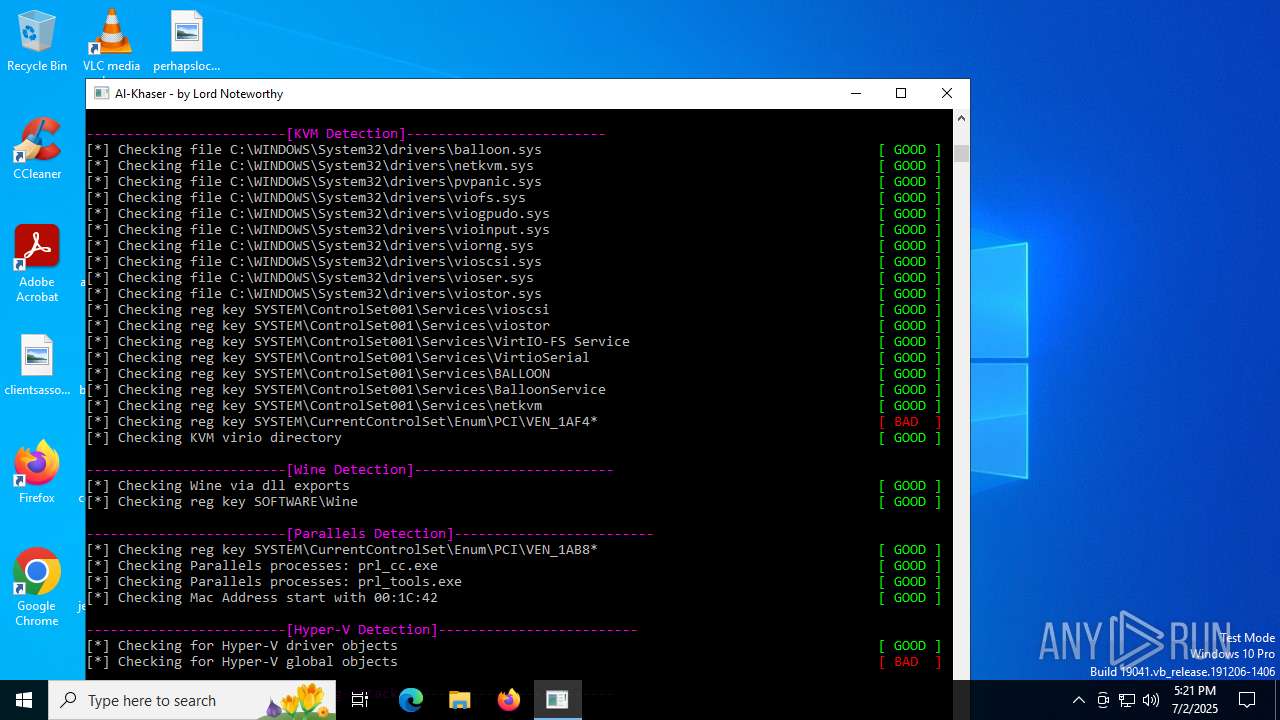
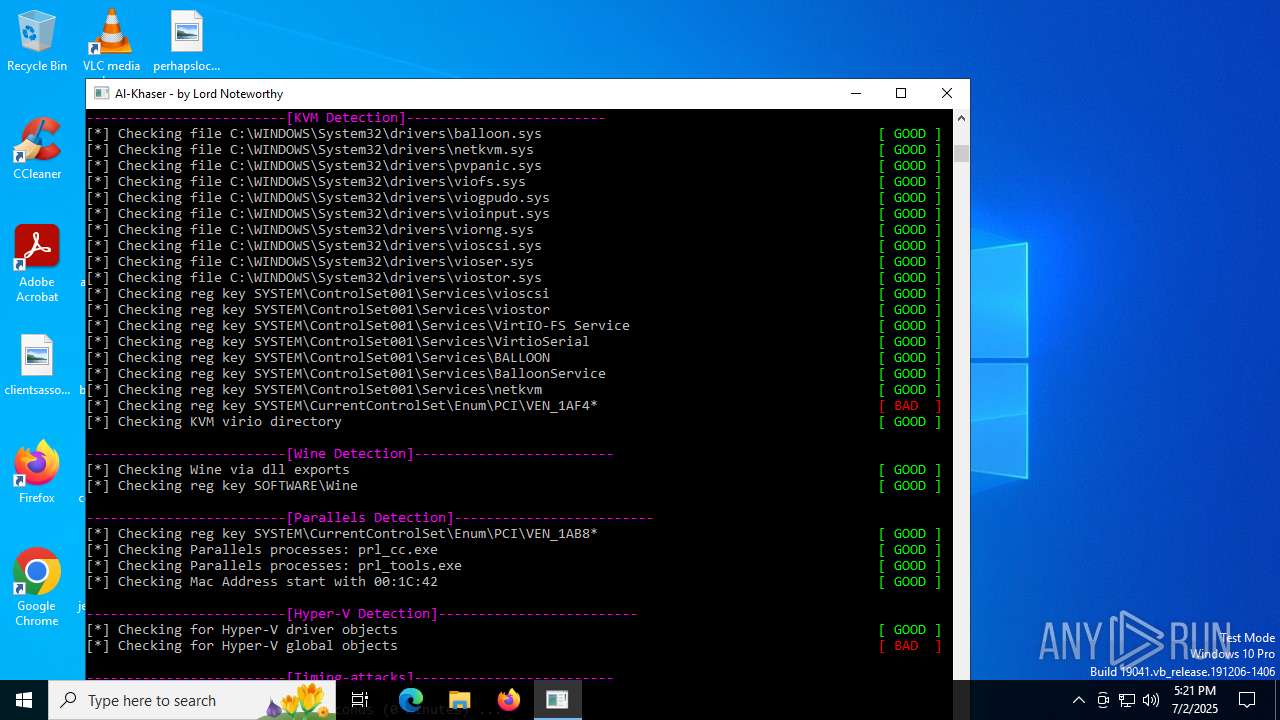
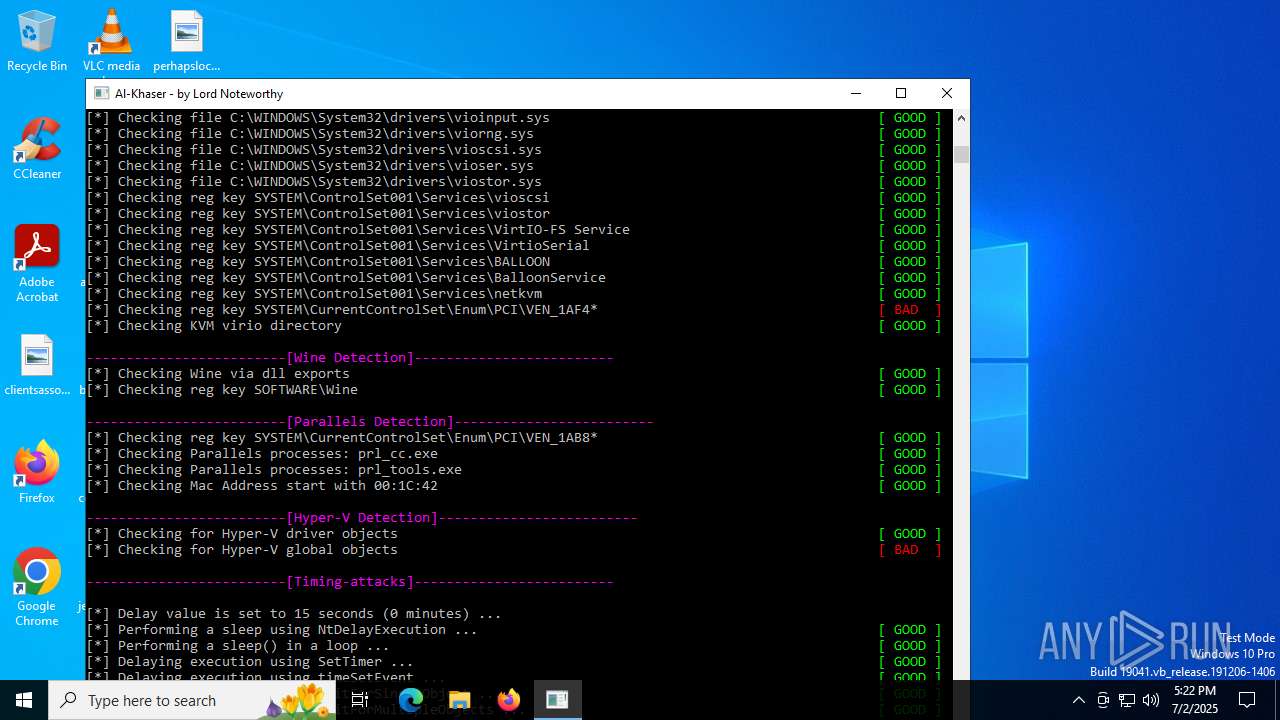
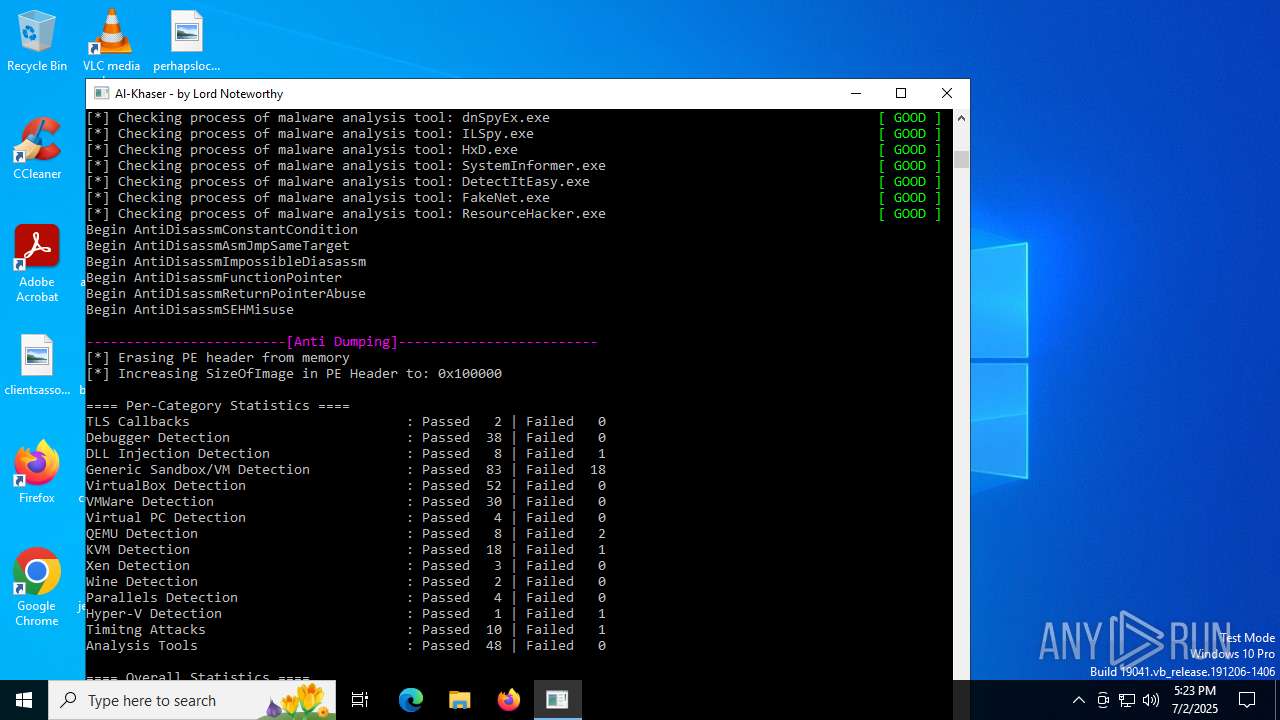
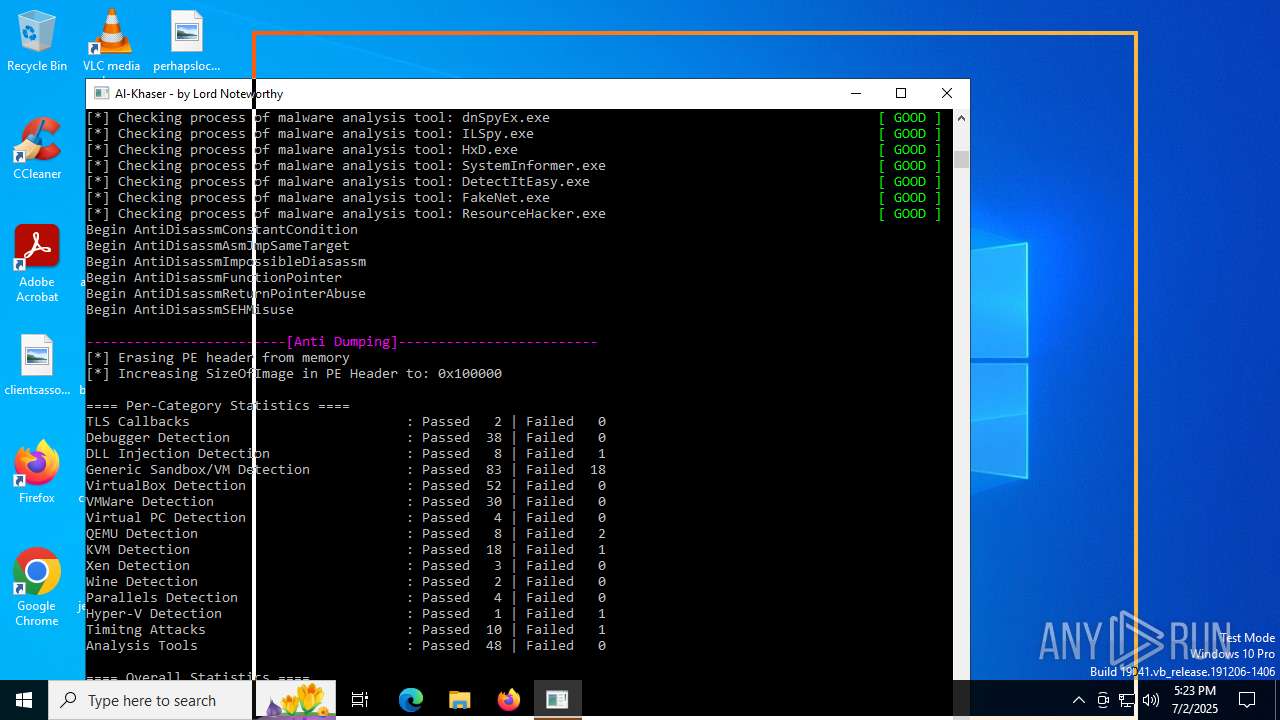
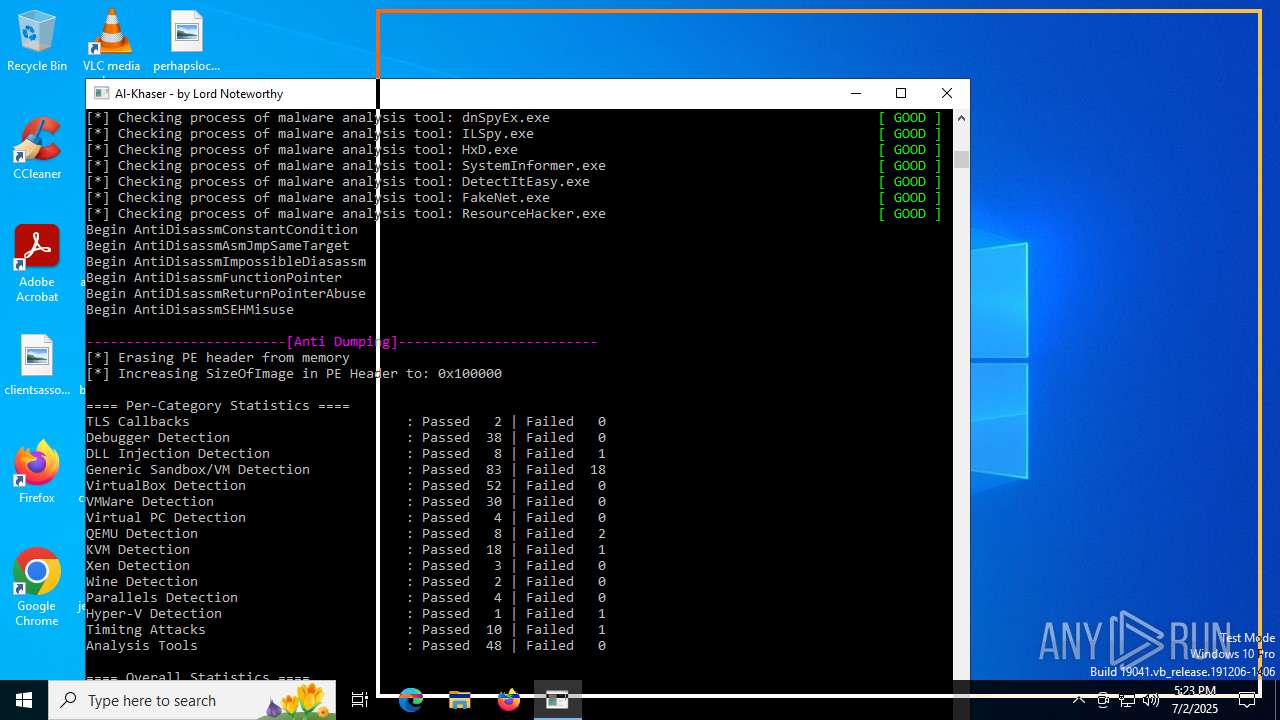
The process checks if it is being run in the virtual environment
- al-khaser.exe (PID: 6240)
Checks for external IP
- al-khaser.exe (PID: 6240)
- svchost.exe (PID: 2200)
Executes as Windows Service
- WmiApSrv.exe (PID: 4700)
Read disk information to detect sandboxing environments
- al-khaser.exe (PID: 6240)
Reads the BIOS version
- al-khaser.exe (PID: 6240)
INFO
Create files in a temporary directory
- al-khaser.exe (PID: 6240)
Reads the computer name
- al-khaser.exe (PID: 6240)
Checks supported languages
- al-khaser.exe (PID: 6240)
Checks proxy server information
- slui.exe (PID: 6164)
Reads the software policy settings
- slui.exe (PID: 6164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (49.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.8) |
| .exe | | | Win32 Executable (generic) (5.3) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:02 16:49:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.34 |
| CodeSize: | 93696 |
| InitializedDataSize: | 163328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1720f |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
147
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | al-khaser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4700 | C:\WINDOWS\system32\wbem\WmiApSrv.exe | C:\Windows\System32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6164 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | "C:\Users\admin\AppData\Local\Temp\al-khaser.exe" | C:\Users\admin\AppData\Local\Temp\al-khaser.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 653
Read events
3 652
Write events
1
Delete events
0
Modification events
| (PID) Process: | (4700) WmiApSrv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Wbem\PROVIDERS\Performance |
| Operation: | write | Name: | Performance Refreshed |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6240 | al-khaser.exe | C:\Users\admin\AppData\Local\Temp\log.txt | text | |
MD5:C0BE9298E1CDBD9AF33B141F51A3B365 | SHA256:890359EF9037359713B2DEF62C7AD76D6AF0588618E55A8ECF55A3A32AA6883B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
28
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6240 | al-khaser.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=hosting | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2428 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4372 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6240 | al-khaser.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2428 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ip-api.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6240 | al-khaser.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
Process | Message |
|---|---|
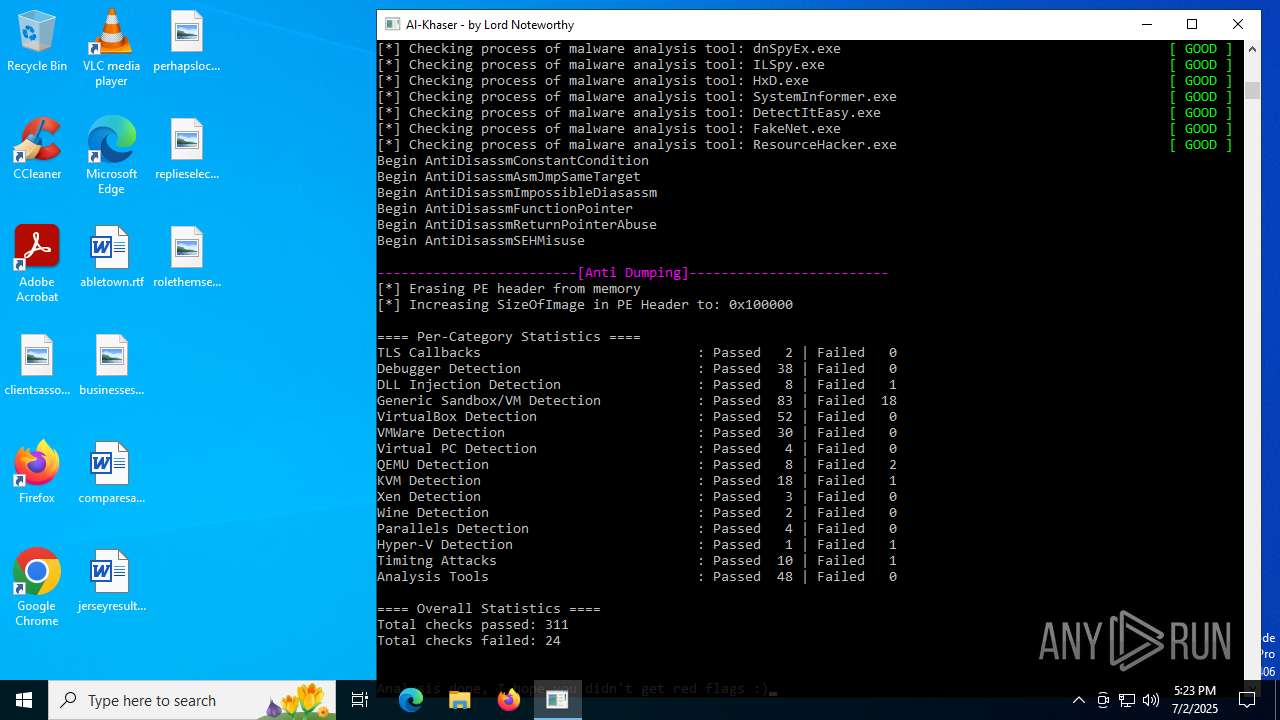
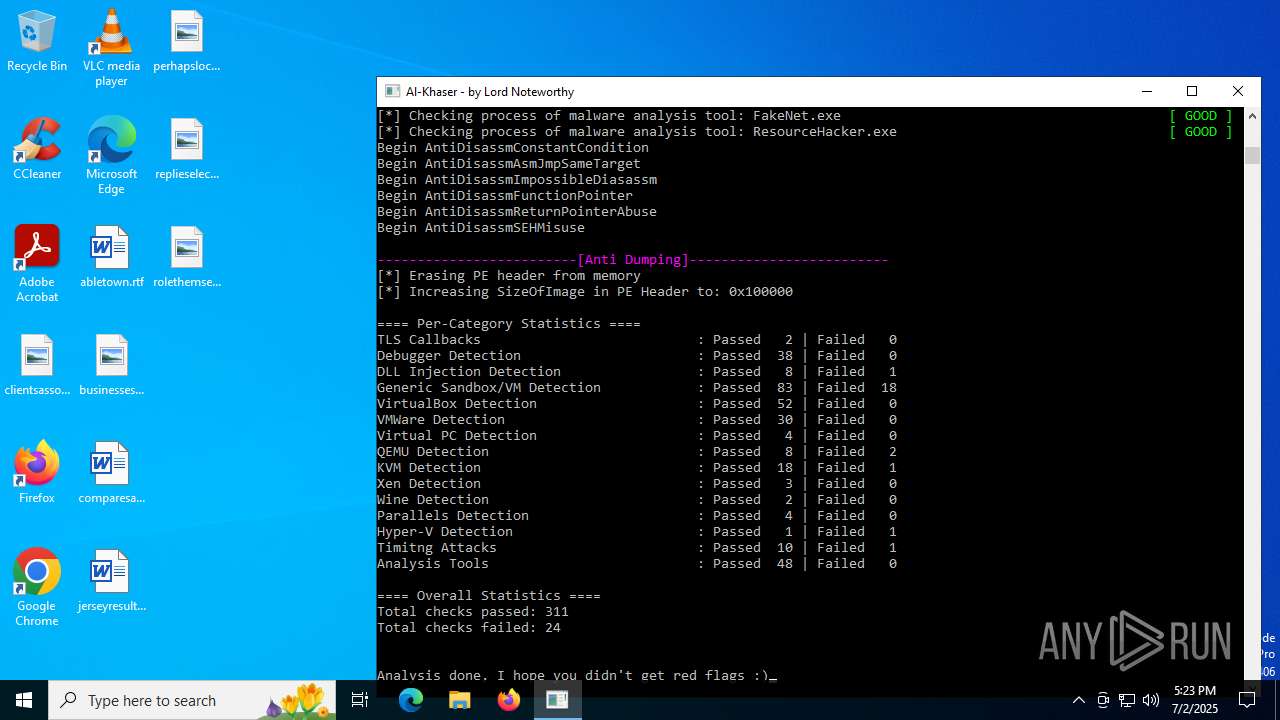
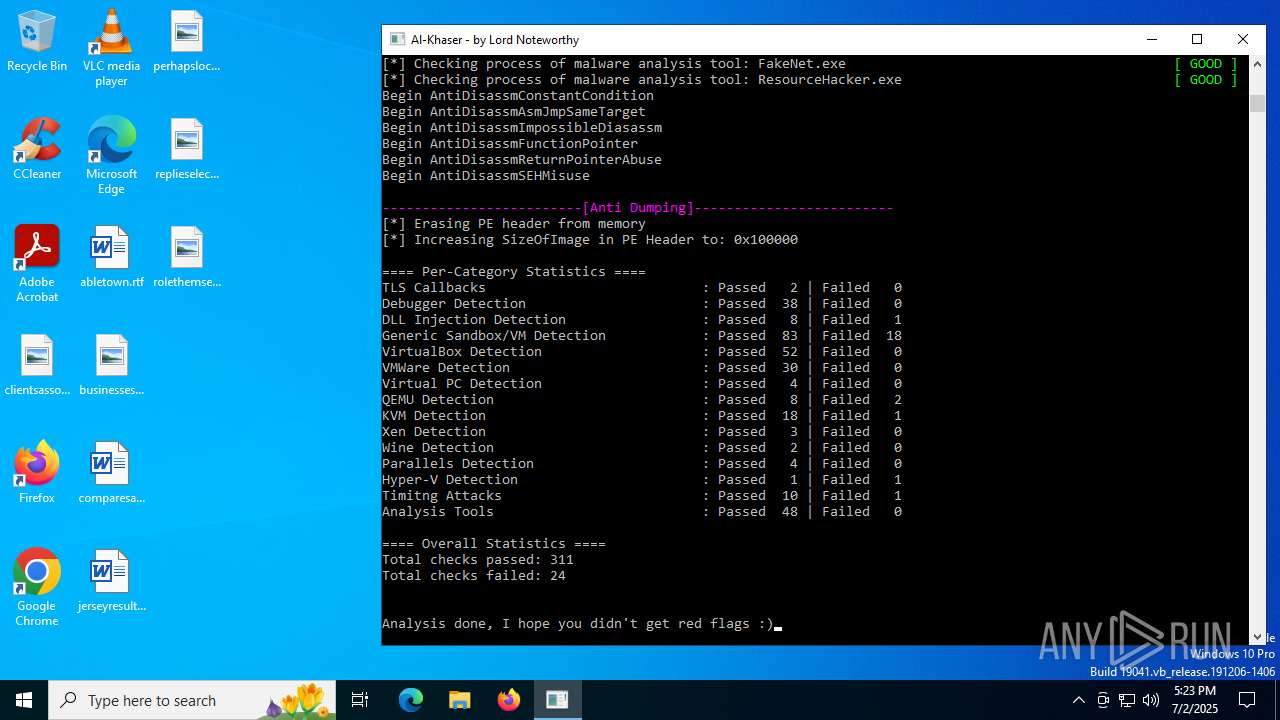
al-khaser.exe | TLS callback: process attach |
al-khaser.exe | All seems fine for TLSCallbackThread. |
al-khaser.exe | TLS callback: thread attach |
al-khaser.exe | All seems fine for TLSCallbackProcess. |
al-khaser.exe | TLS callback: dummy thread launched |
al-khaser.exe | TLS callback: thread attach |
al-khaser.exe | TLS callback: thread attach |
al-khaser.exe | TLS callback: thread attach |
al-khaser.exe | TLS callback: thread attach |