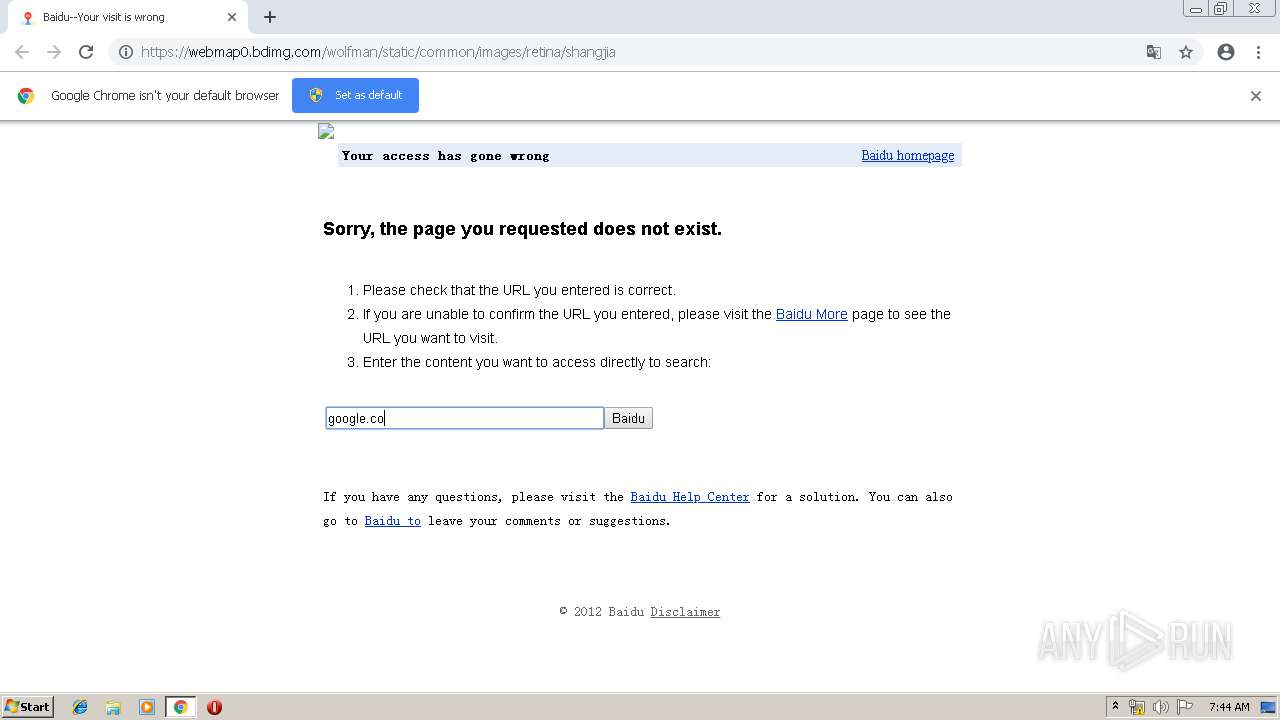
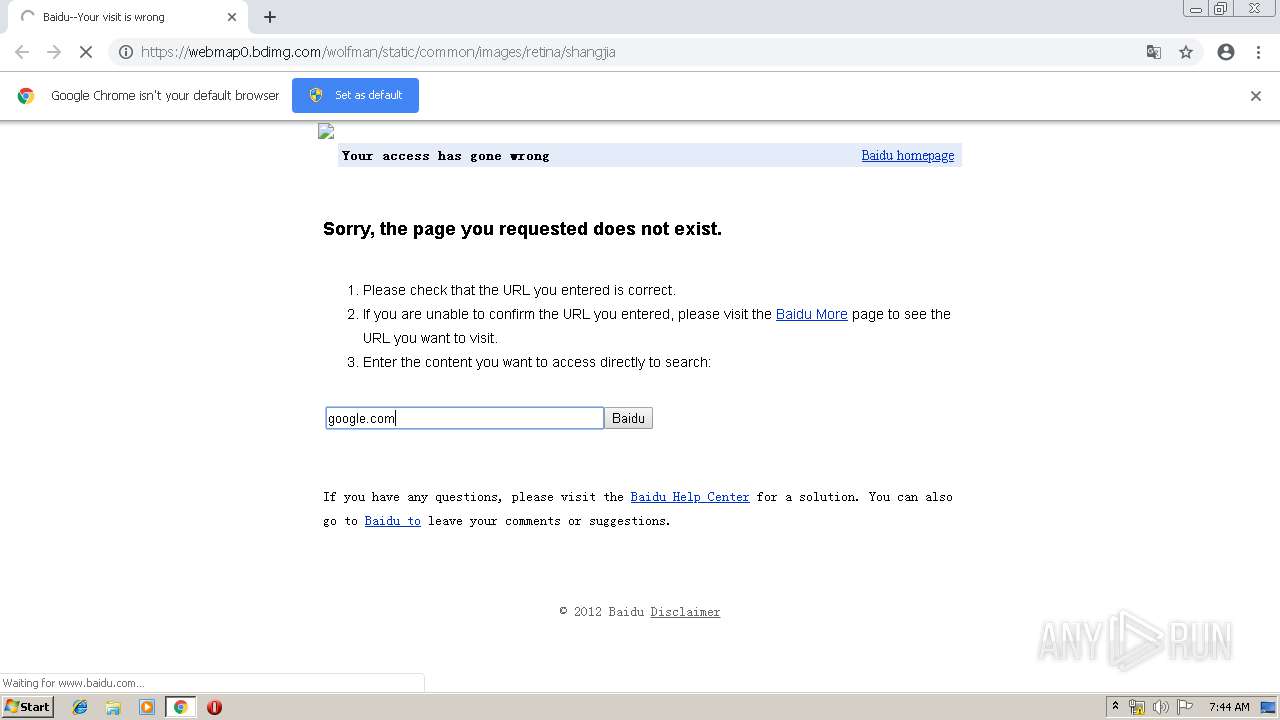
| URL: | https://webmap0.bdimg.com/wolfman/static/common/images/retina/shangjia |
| Full analysis: | https://app.any.run/tasks/c8157653-de66-43bb-83da-6ce9eeac3efa |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 06:43:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9B95001C357B56EF4C1CB2BC162B9DA0 |
| SHA1: | F66A6A72D1AD2B06825BA599BC8DD840193F07C9 |
| SHA256: | 47FF327146A8B0D8EB115E395A917F3DC3A56490C0FE83FAFF12C1C30AC54ECD |
| SSDEEP: | 3:N8RoEVRBdTKSKYHK1rFRKEfZMEn:2ekB1J0rFRKEfZME |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1640)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 1640)
Application launched itself
- chrome.exe (PID: 1640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9168842765766601544 --mojo-platform-channel-handle=4224 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1272521313272706420 --mojo-platform-channel-handle=2792 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --service-pipe-token=11283951524276560426 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11283951524276560426 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://webmap0.bdimg.com/wolfman/static/common/images/retina/shangjia | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --service-pipe-token=15672624611245466660 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15672624611245466660 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --service-pipe-token=8384411048065583412 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8384411048065583412 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2168 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8079450192483914017 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,18136633527399935463,2423146581698343653,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14995694063695968532 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14995694063695968532 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f3f0f18,0x6f3f0f28,0x6f3f0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
546
Read events
459
Write events
82
Delete events
5
Modification events
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1640-13200561834619750 |
Value: 259 | |||
Executable files
0
Suspicious files
24
Text files
124
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e88f7fab-bb88-4d8a-9ec5-fec8b68d7635.tmp | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
46
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1640 | chrome.exe | GET | 200 | 153.37.235.78:80 | http://nsclick.baidu.com/v.gif?pid=201&fm=none_show&tab=2&pj=ui_none&path=http%3A%2F%2Fwww.baidu.com%2Fs%3Fwd%3Dgoogle.com%26cl%3D3%26tn%3Dbaiduerr&wd=google%2Ecom&rsv_sid=1461_28804_21112_28774_28724_28834_28585_28604_28892&rsv_did=&t=1556088288909 | CN | — | — | whitelisted |
1640 | chrome.exe | GET | 200 | 185.10.104.120:80 | http://t12.baidu.com/it/u=4245892556,1068472290&fm=58 | unknown | image | 2.33 Kb | whitelisted |
1640 | chrome.exe | GET | 200 | 194.9.25.78:80 | http://r3---sn-5uh5o-f5fs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.219.109&mm=28&mn=sn-5uh5o-f5fs&ms=nvh&mt=1556088095&mv=m&pl=24&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
1640 | chrome.exe | GET | 200 | 103.235.46.82:80 | http://map.baidu.com/search/img/logo.gif | HK | html | 24.7 Kb | unknown |
1640 | chrome.exe | GET | 200 | 103.235.47.69:80 | http://s1.bdstatic.com/r/www/cache/static/global/img/icons_5859e57.png | HK | image | 14.0 Kb | whitelisted |
1640 | chrome.exe | GET | 200 | 103.235.46.39:80 | http://www.baidu.com/img/baidu_resultlogo@2.png | HK | image | 6.36 Kb | whitelisted |
1640 | chrome.exe | GET | 200 | 185.10.104.120:80 | http://t10.baidu.com/it/u=2031118386,2438077326&fm=58 | unknown | image | 2.64 Kb | whitelisted |
1640 | chrome.exe | GET | 200 | 103.235.47.69:80 | http://s1.bdstatic.com/r/www/cache/static/global/js/all_async_search_b321eb2.js | HK | text | 85.6 Kb | whitelisted |
1640 | chrome.exe | GET | 200 | 185.10.104.120:80 | http://i8.baidu.com/it/u=772521751,490453158&fm=85 | unknown | image | 2.01 Kb | whitelisted |
— | — | GET | 200 | 185.10.104.120:80 | http://t10.baidu.com/it/u=3053831727,4262545098&fm=58 | unknown | image | 1.95 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1640 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 103.235.46.82:80 | map.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
— | — | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 194.9.25.78:80 | r3---sn-5uh5o-f5fs.gvt1.com | ATM S.A. | PL | whitelisted |
— | — | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 103.235.46.39:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
1640 | chrome.exe | 103.235.47.69:80 | s1.bdstatic.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
webmap0.bdimg.com |
| suspicious |
accounts.google.com |
| shared |
map.baidu.com |
| unknown |
clients1.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
translate.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |