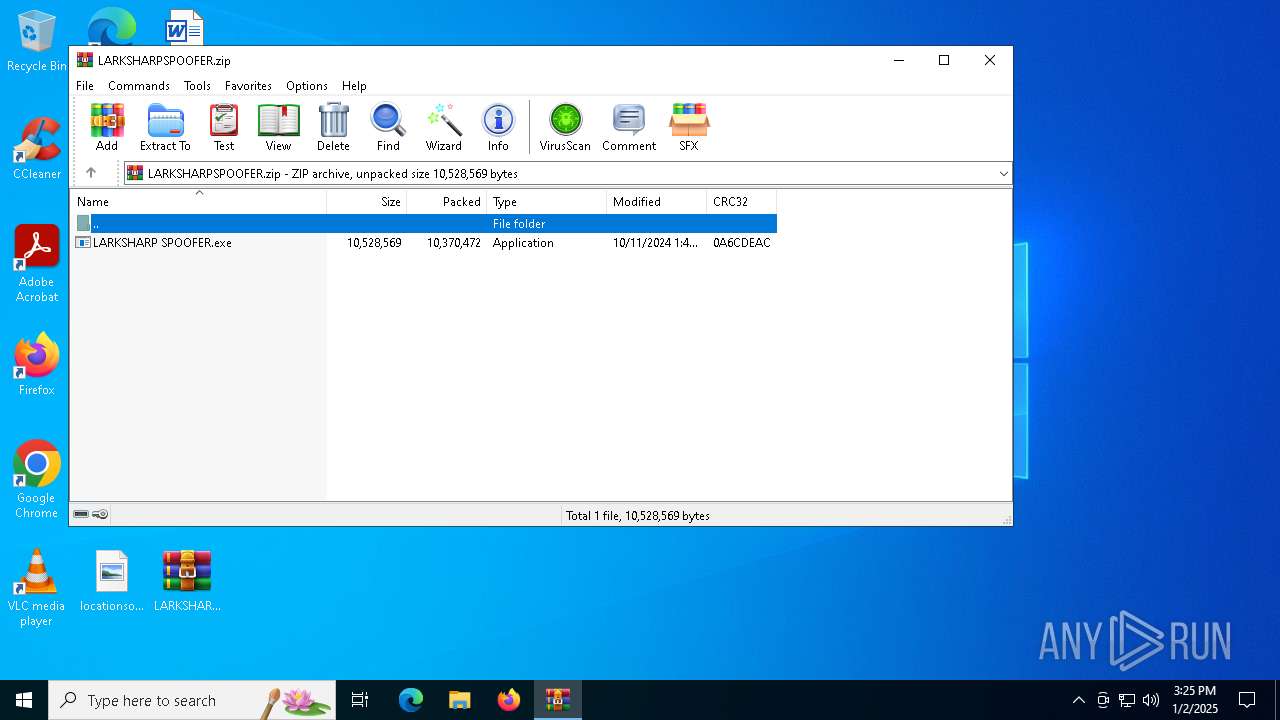
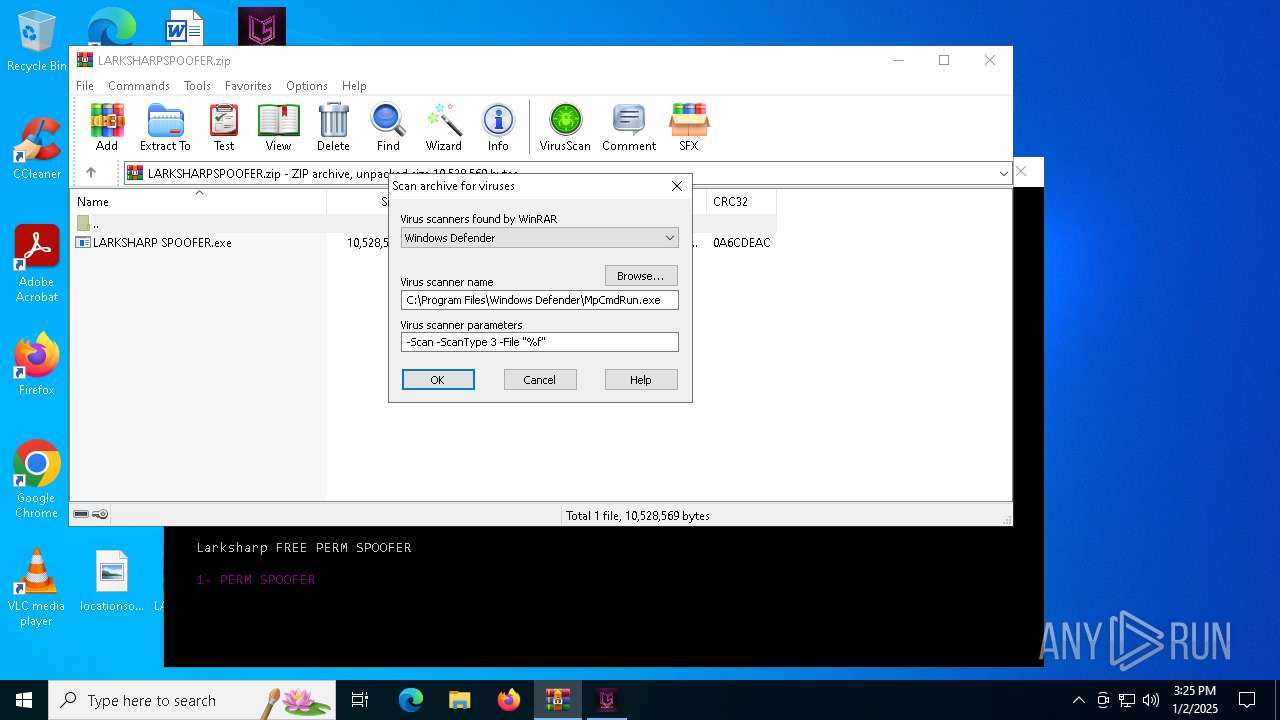
| File name: | LARKSHARPSPOOFER.zip |
| Full analysis: | https://app.any.run/tasks/bff72926-9841-43b3-b63e-bfcaaf7e90c1 |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2025, 15:25:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5E5A8A54FC1283A440CE9D35DF48551D |
| SHA1: | 2EBCE3A9C9F3A514F7F35E180400E7AB4DC12EDC |
| SHA256: | 47F42570C1328798A903A976412A5D004FA38CA514F7262CD2FD3F80F55D02DA |
| SSDEEP: | 98304:oxZ5IVvggs2lCJL3KK6NC6/lmNVD0Z9Nu6HYWFV5kAwtL7ex00CQVXe5plC964U5:EbZIDf89VLE4iF85yfepv |
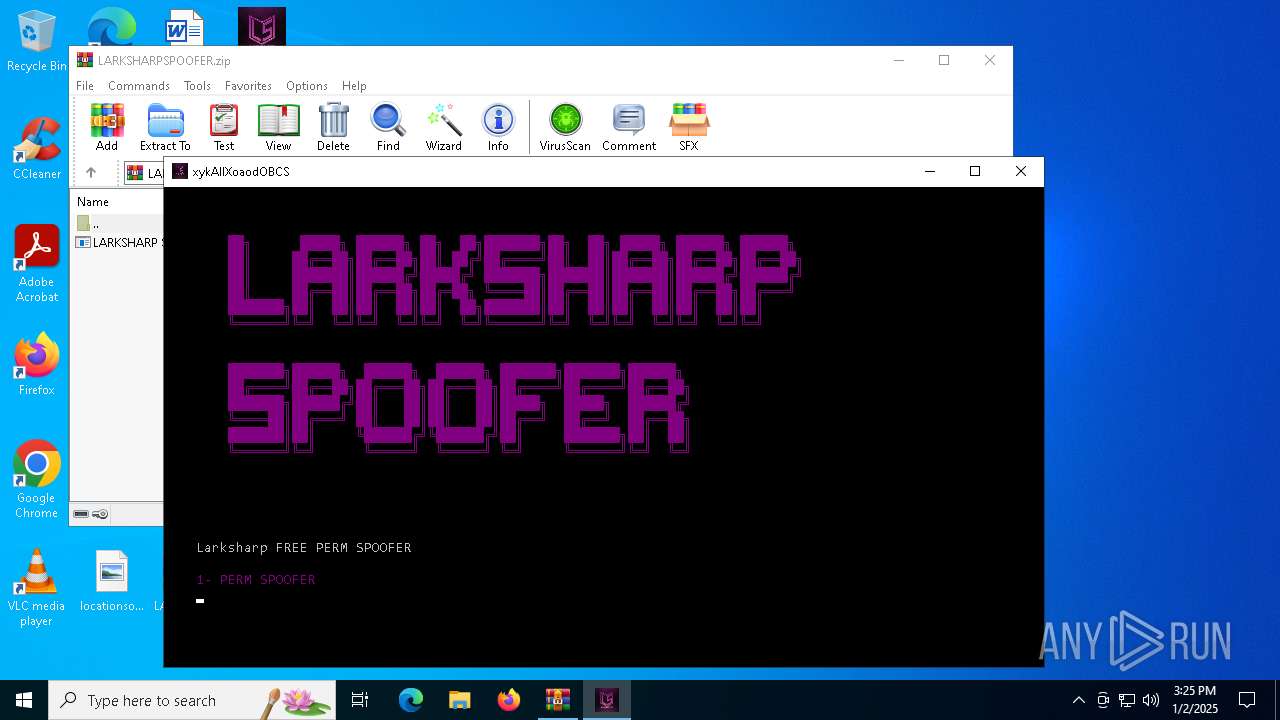
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6256)
SUSPICIOUS
The process drops C-runtime libraries
- LARKSHARP SPOOFER.exe (PID: 6712)
Process drops legitimate windows executable
- LARKSHARP SPOOFER.exe (PID: 6712)
Process drops python dynamic module
- LARKSHARP SPOOFER.exe (PID: 6712)
Drops a system driver (possible attempt to evade defenses)
- LARKSHARP SPOOFER.exe (PID: 6712)
Executable content was dropped or overwritten
- LARKSHARP SPOOFER.exe (PID: 6712)
Application launched itself
- LARKSHARP SPOOFER.exe (PID: 6712)
Loads Python modules
- LARKSHARP SPOOFER.exe (PID: 6808)
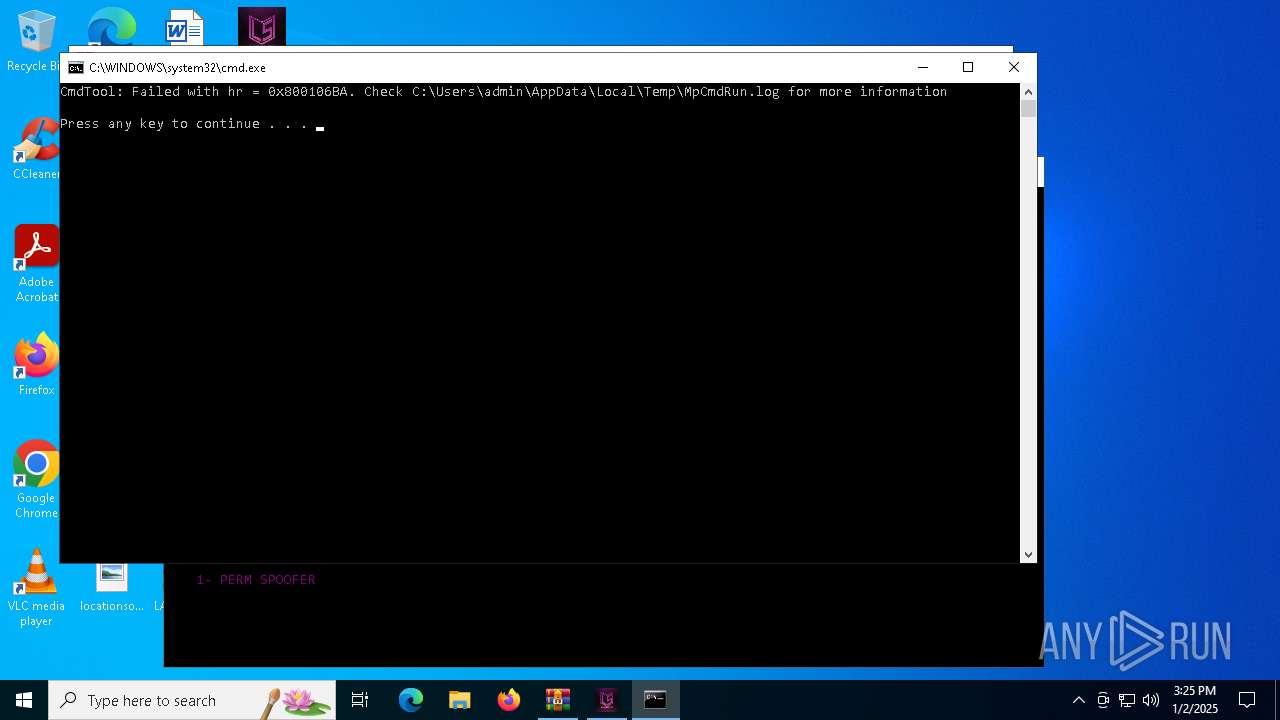
Starts CMD.EXE for commands execution
- LARKSHARP SPOOFER.exe (PID: 6808)
- WinRAR.exe (PID: 6256)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6256)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 6256)
INFO
Manual execution by a user
- LARKSHARP SPOOFER.exe (PID: 6712)
Checks supported languages
- LARKSHARP SPOOFER.exe (PID: 6712)
- LARKSHARP SPOOFER.exe (PID: 6808)
- mode.com (PID: 6852)
- MpCmdRun.exe (PID: 6972)
The sample compiled with english language support
- LARKSHARP SPOOFER.exe (PID: 6712)
Reads the computer name
- LARKSHARP SPOOFER.exe (PID: 6712)
- MpCmdRun.exe (PID: 6972)
Reads the machine GUID from the registry
- LARKSHARP SPOOFER.exe (PID: 6808)
Create files in a temporary directory
- LARKSHARP SPOOFER.exe (PID: 6712)
- MpCmdRun.exe (PID: 6972)
Starts MODE.COM to configure console settings
- mode.com (PID: 6852)
PyInstaller has been detected (YARA)
- LARKSHARP SPOOFER.exe (PID: 6712)
- LARKSHARP SPOOFER.exe (PID: 6808)
The process uses the downloaded file
- WinRAR.exe (PID: 6256)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:11 09:49:10 |
| ZipCRC: | 0x0a6cdeac |
| ZipCompressedSize: | 10370472 |
| ZipUncompressedSize: | 10528569 |
| ZipFileName: | LARKSHARP SPOOFER.exe |
Total processes
128
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
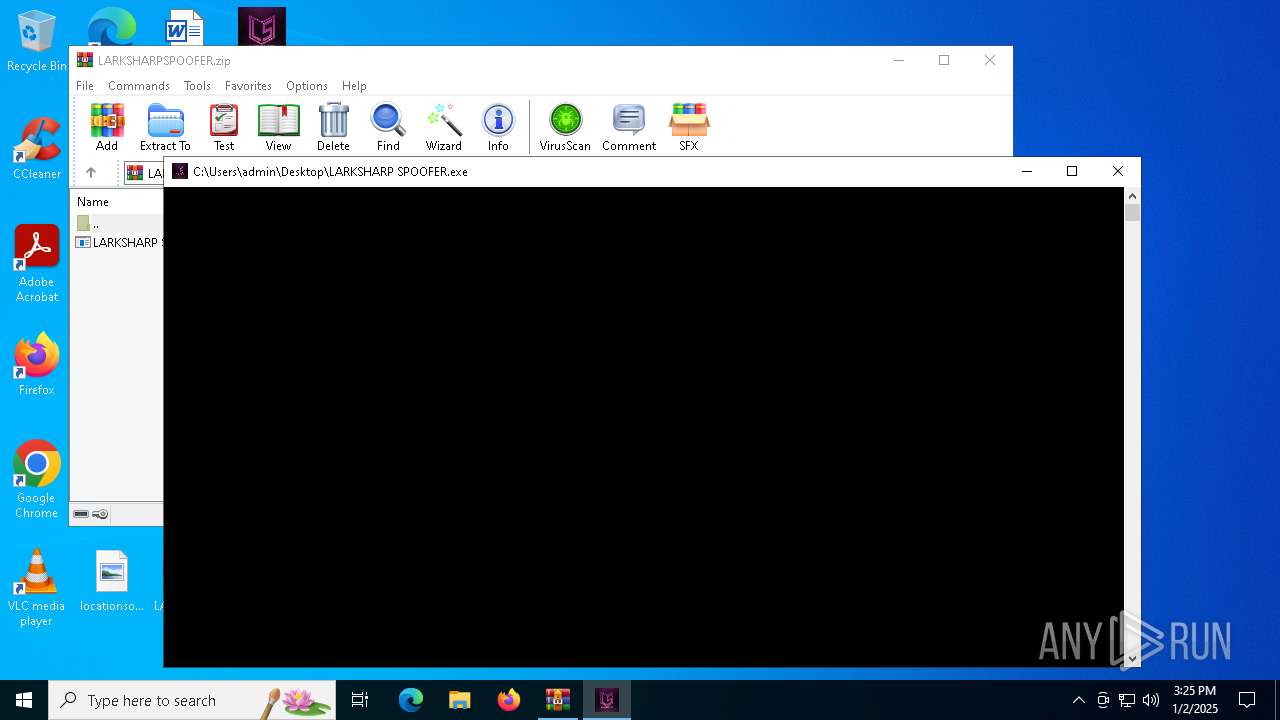
| 6256 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\LARKSHARPSPOOFER.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6712 | "C:\Users\admin\Desktop\LARKSHARP SPOOFER.exe" | C:\Users\admin\Desktop\LARKSHARP SPOOFER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | LARKSHARP SPOOFER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6808 | "C:\Users\admin\Desktop\LARKSHARP SPOOFER.exe" | C:\Users\admin\Desktop\LARKSHARP SPOOFER.exe | — | LARKSHARP SPOOFER.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6836 | C:\WINDOWS\system32\cmd.exe /c mode con: cols=110 lines=30 | C:\Windows\System32\cmd.exe | — | LARKSHARP SPOOFER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6852 | mode con: cols=110 lines=30 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6912 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR6256.34717\Rar$Scan16994.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR6256.34717" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 669
Read events
1 660
Write events
9
Delete events
0
Modification events
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\LARKSHARPSPOOFER.zip | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
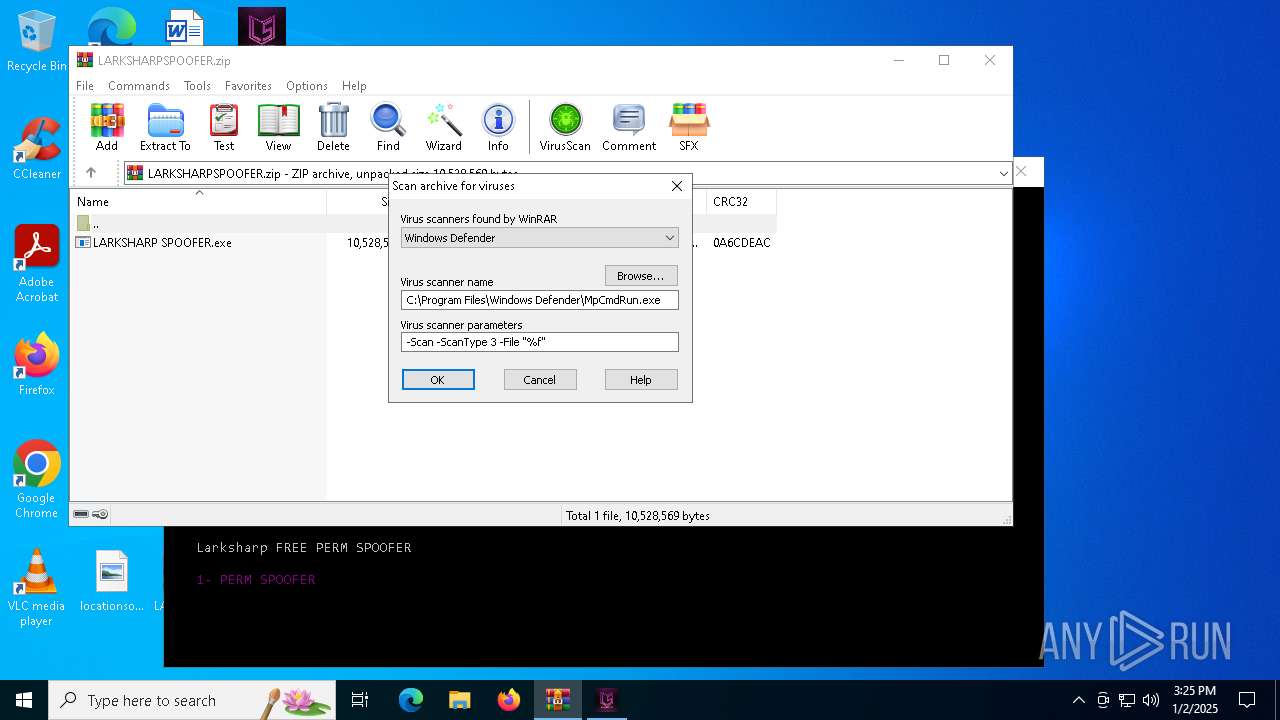
| (PID) Process: | (6256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
21
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\MSVCP140.dll | executable | |
MD5:72F3D84384E888BF0D38852EB863026B | SHA256:A4C2229BDC2A2A630ACDC095B4D86008E5C3E3BC7773174354F3DA4F5BEB9CDE | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\libcrypto-1_1.dll | executable | |
MD5:89511DF61678BEFA2F62F5025C8C8448 | SHA256:296426E7CE11BC3D1CFA9F2AEB42F60C974DA4AF3B3EFBEB0BA40E92E5299FDF | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\mac.EXE | executable | |
MD5:AED42FF110A595753BB2F83171727285 | SHA256:A124932386DBCC5E6B5901F2460F68E7CFB1DFF1406CD899620E8880461C60FB | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_bz2.pyd | executable | |
MD5:A49C5F406456B79254EB65D015B81088 | SHA256:CE4EF8ED1E72C1D3A6082D500A17A009EB6E8ED15022BF3B68A22291858FECED | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_socket.pyd | executable | |
MD5:4827652DE133C83FA1CAE839B361856C | SHA256:87832A3B89E2ADA8F704A8F066013660D591D9CE01CE901CC57A3B973F0858BA | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\_ctypes.pyd | executable | |
MD5:291A0A9B63BAE00A4222A6DF71A22023 | SHA256:820E840759EED12E19F3C485FD819B065B49D9DC704AE3599A63077416D63324 | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\amigendrv64.sys | executable | |
MD5:9ACCEBD928A8926FECF317F53CD1C44E | SHA256:811E5D65DF60DFB8C6E1713DA708BE16D9A13EF8DFCD1022D8D1DDA52ED057B2 | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\microsoft.vbs | text | |
MD5:AF1905DC8BD39D2D407F12FB08272BEB | SHA256:BB113A896A43CB1B03A8B57A85E8D46FAF39FE4AE4AF97581B264415EF32BD3B | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\select.pyd | executable | |
MD5:E21CFF76DB11C1066FD96AF86332B640 | SHA256:FCC2E09A2355A5546922874FB4CAC92EE00A33C0ED6ADBC440D128D1E9F4EC28 | |||
| 6712 | LARKSHARP SPOOFER.exe | C:\Users\admin\AppData\Local\Temp\_MEI67122\VCRUNTIME140.dll | executable | |
MD5:4A365FFDBDE27954E768358F4A4CE82E | SHA256:6A0850419432735A98E56857D5CFCE97E9D58A947A9863CA6AFADD1C7BCAB27C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
20
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
536 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1512 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
536 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1512 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
536 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1512 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
536 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1512 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
536 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |