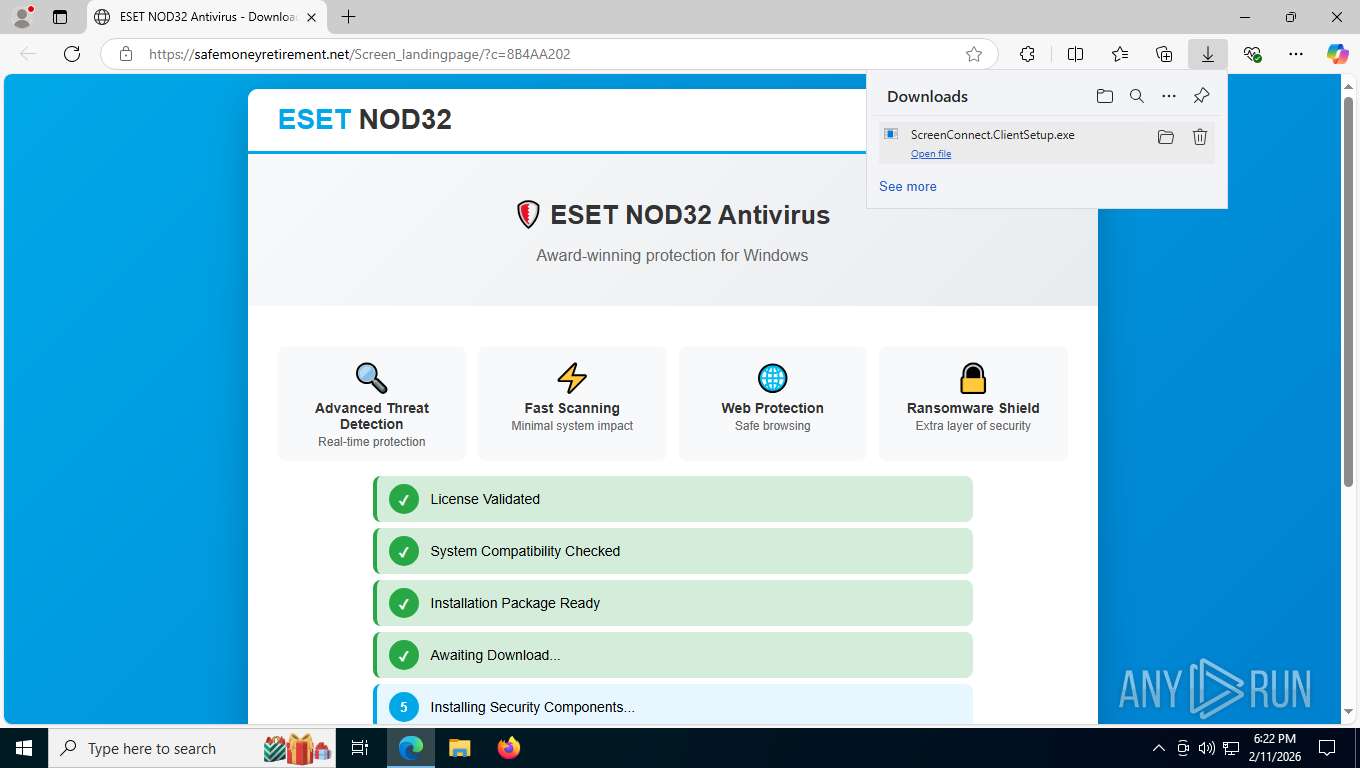
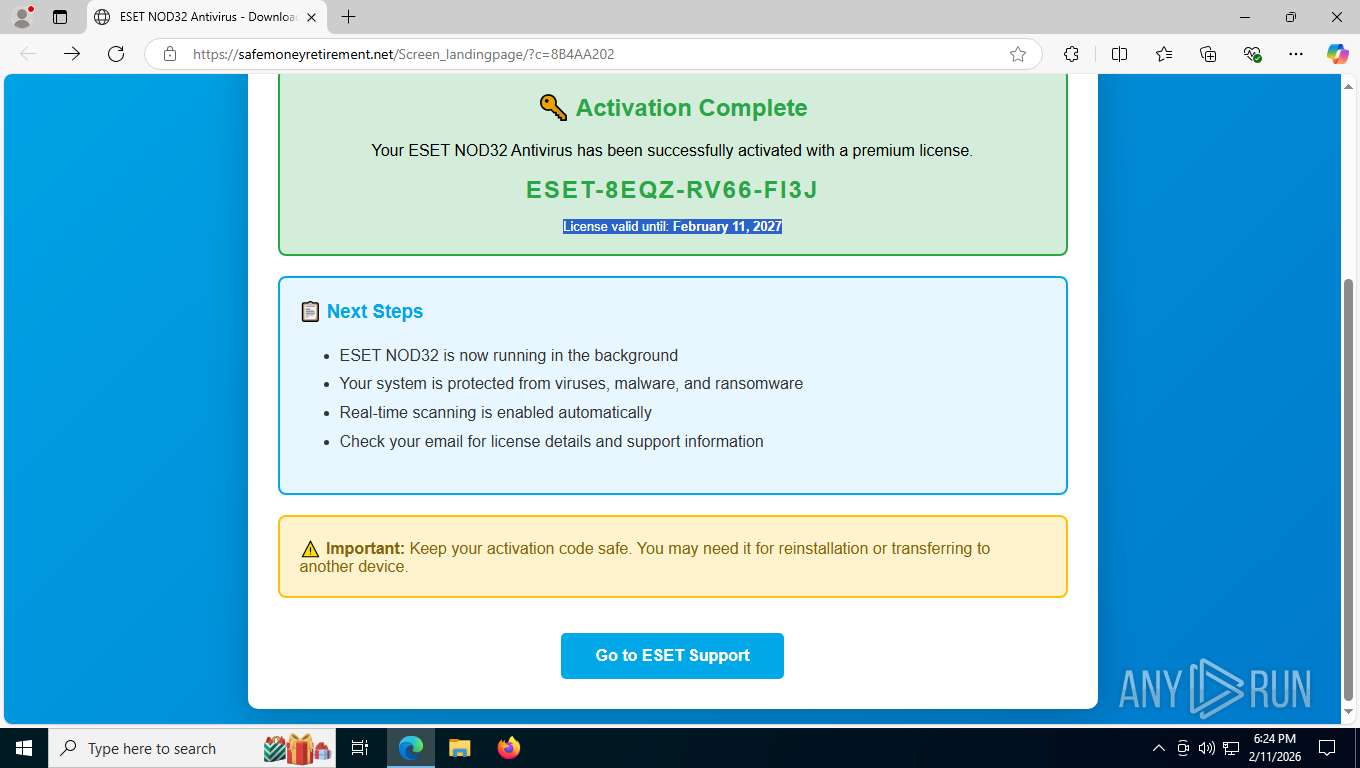
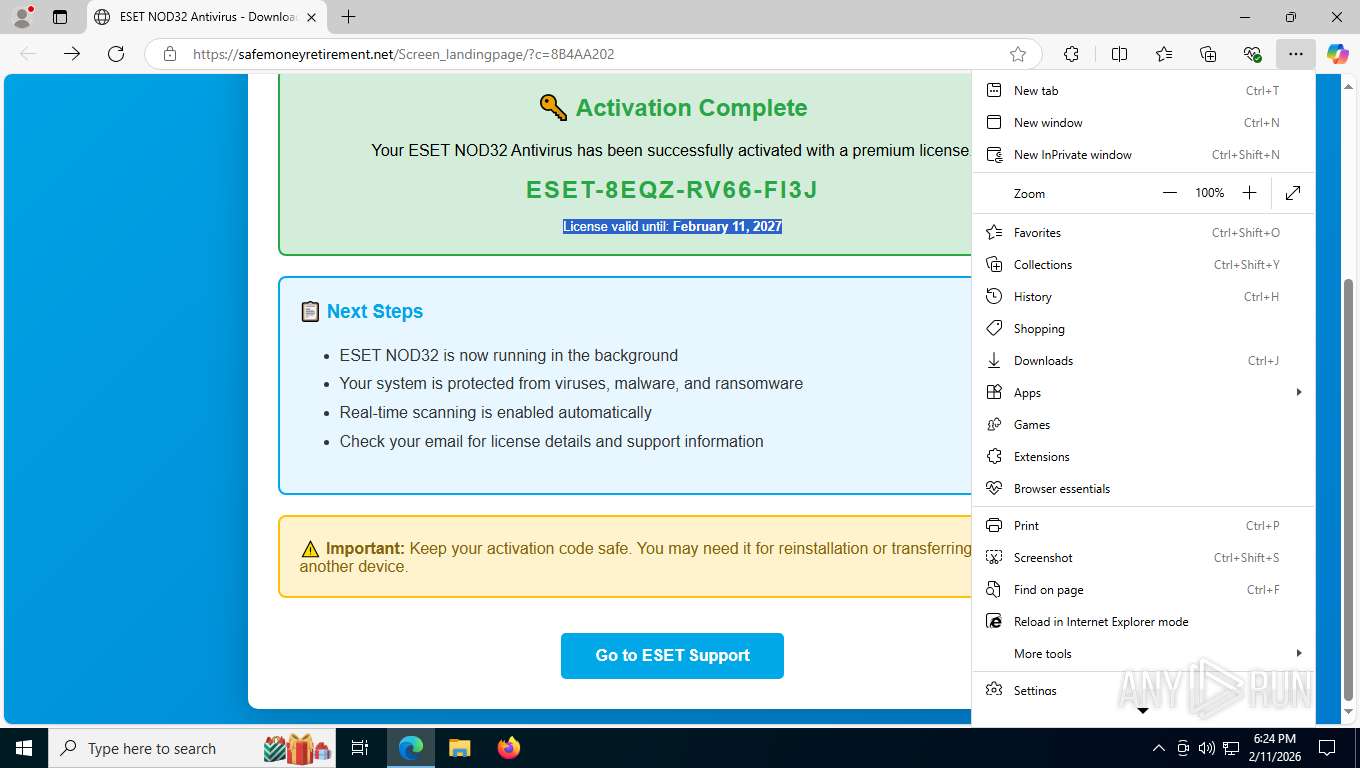
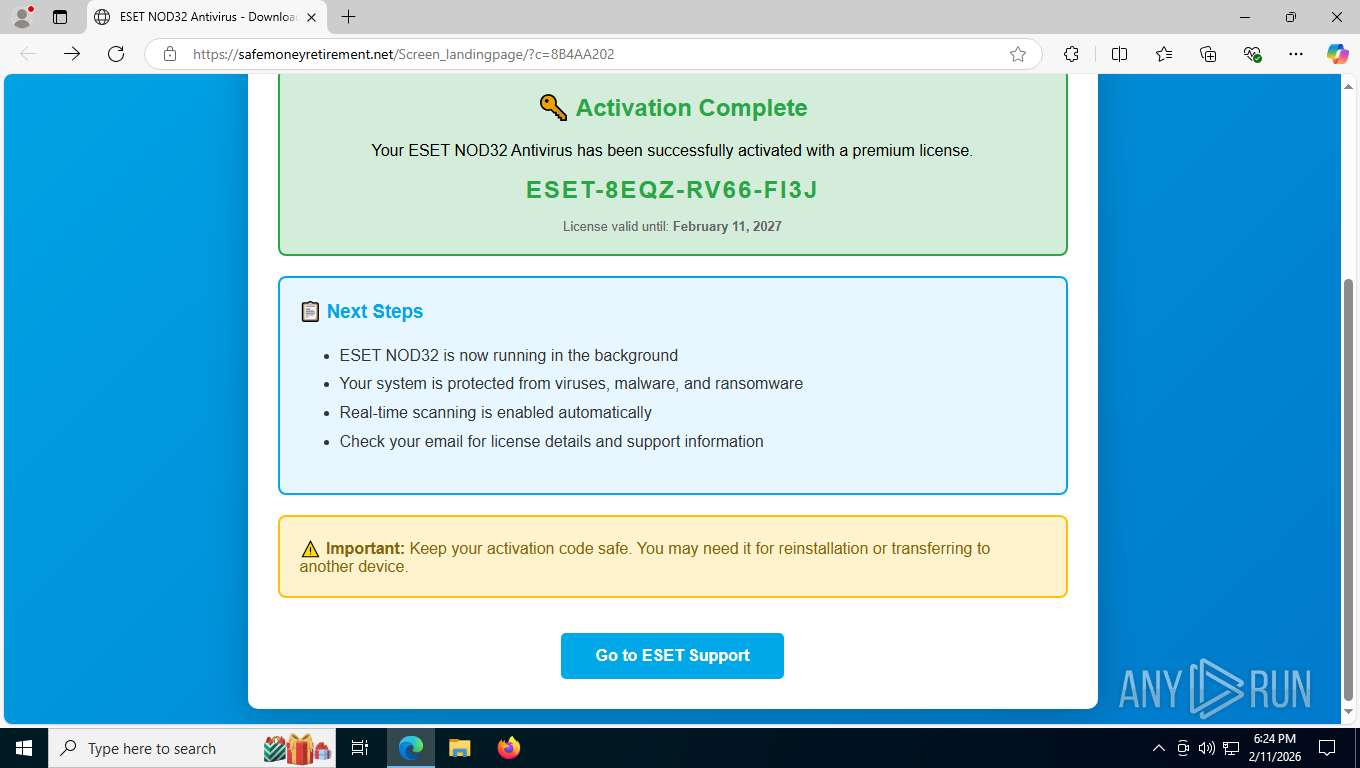
| URL: | https://xianshuabao.com/redirect.aspx?url=https%3A%2F%2Fsafemoneyretirement.net%2FScreen_landingpage%2F%3Fc%3D8B4AA202 |
| Full analysis: | https://app.any.run/tasks/30c92c4c-04a0-43db-85d0-d14b8846229d |
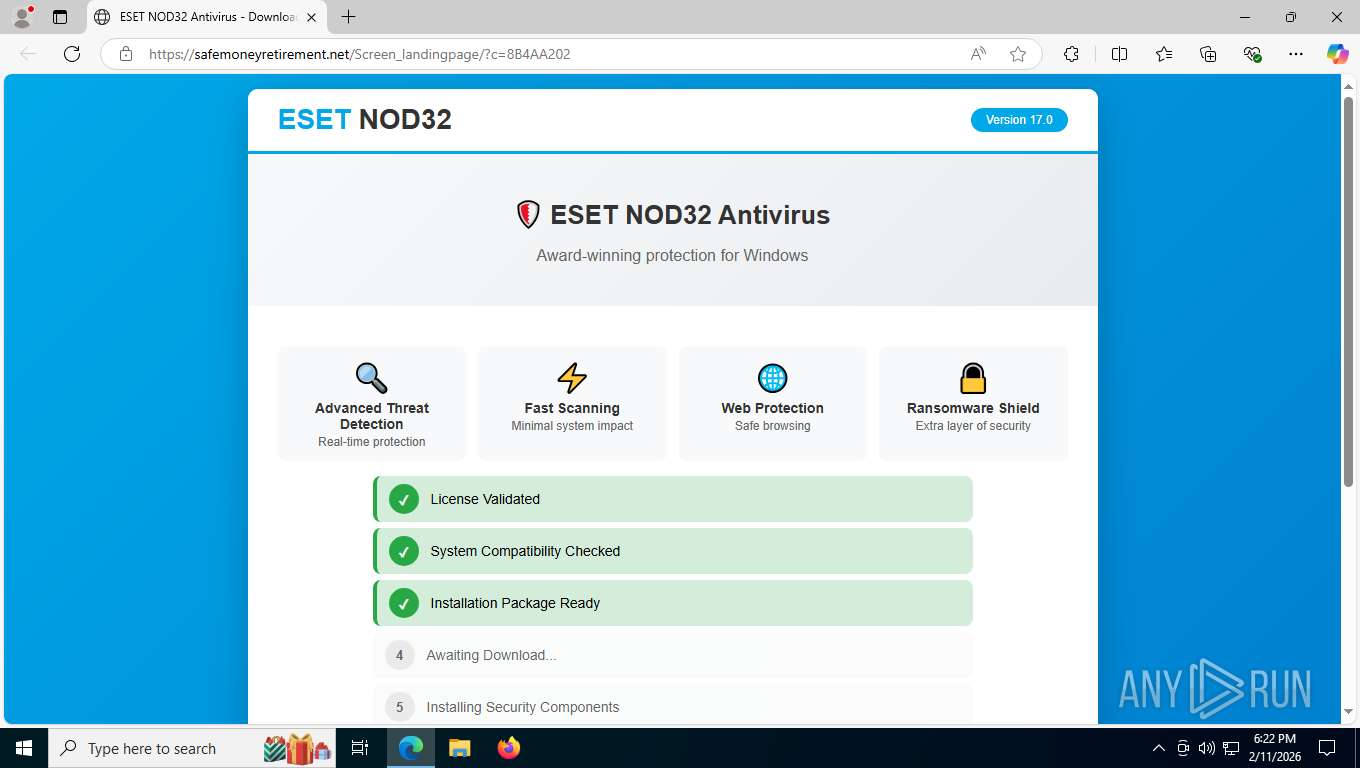
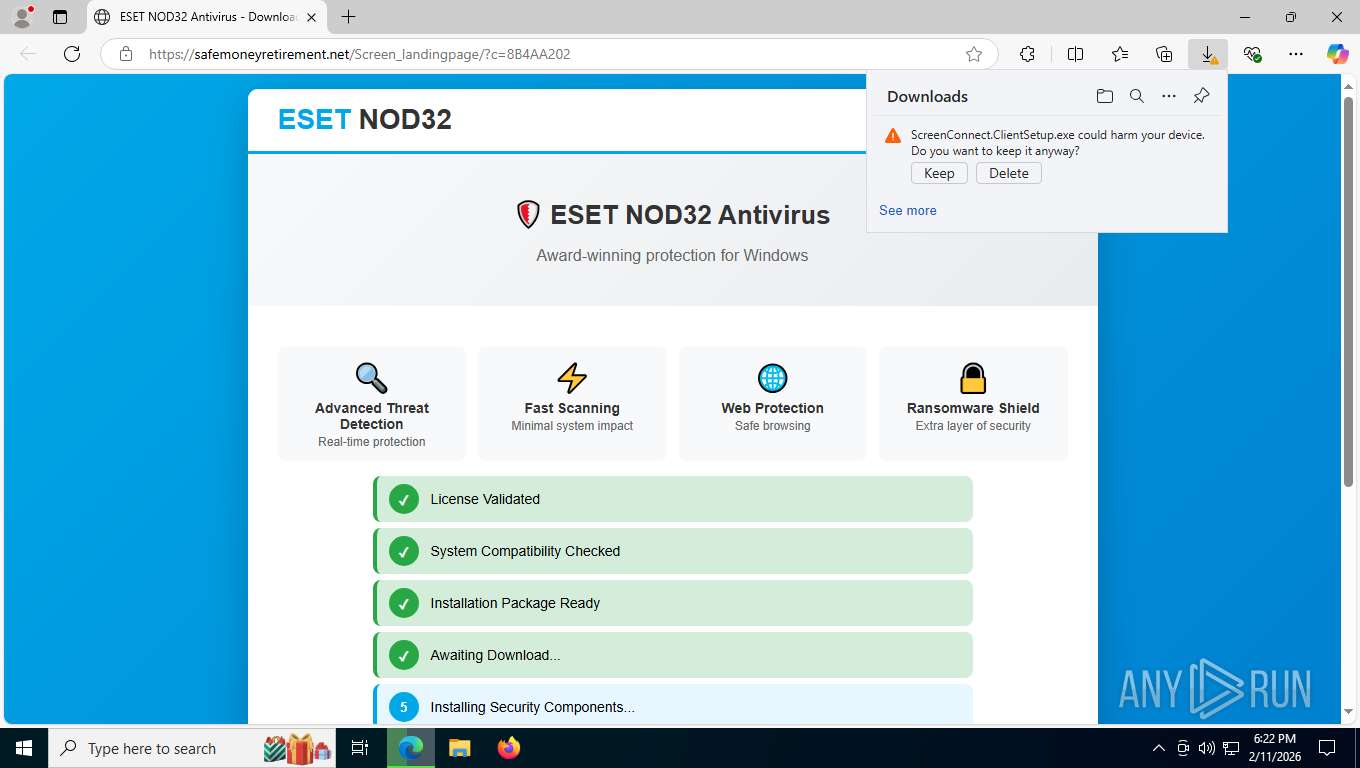
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2026, 23:22:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 837EA79A503339CFF9D139997DE3BD85 |
| SHA1: | 1776981E9577788B0CDD6630E47AF400E960BBD9 |
| SHA256: | 47F249CBAC034AC1BA62FE77E5414CCC477A8F75576373B46D3CCB4AF48098D2 |
| SSDEEP: | 3:N8gELWHWKtaWV8VHWCXjoIKLA3RWAIACDfJE5rBjGNdnRkkFXn:2gEi2Ktd+3zVKLOsAEDfSidRPXn |
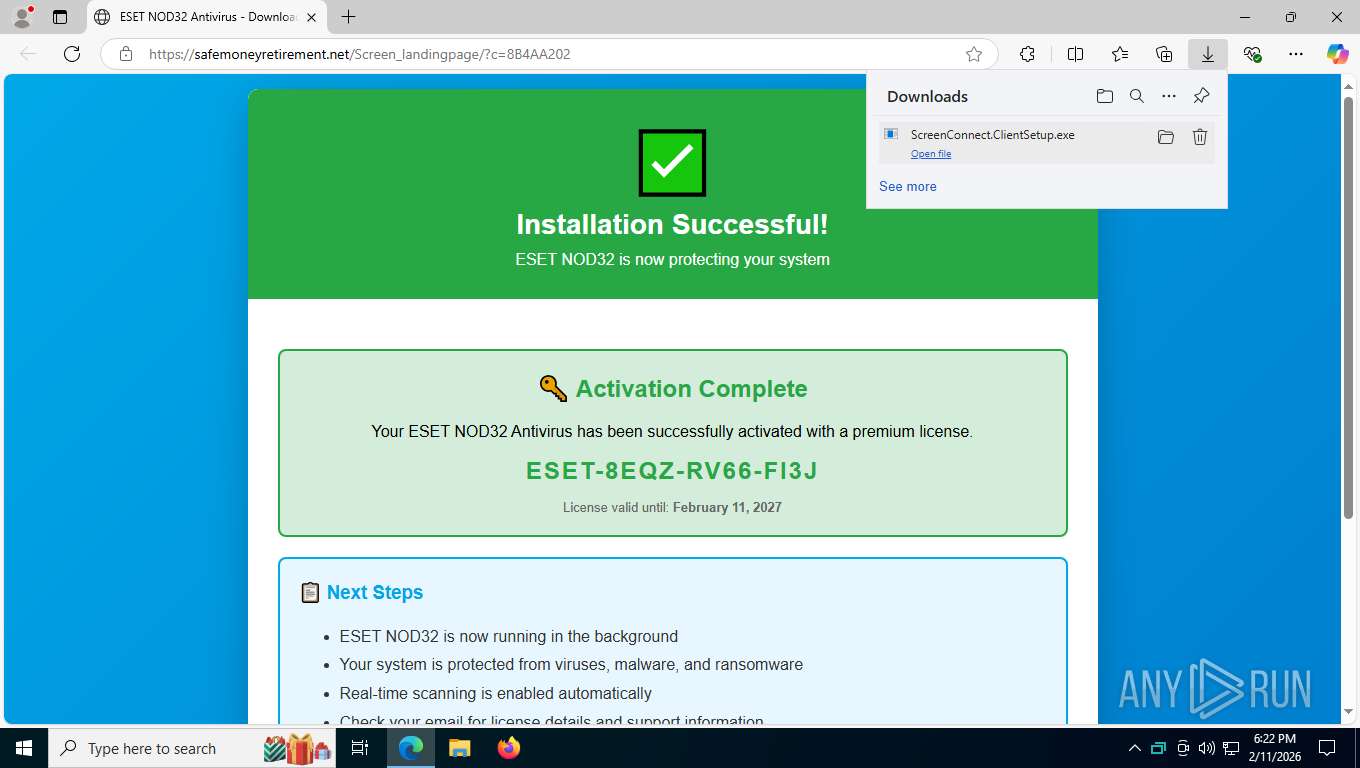
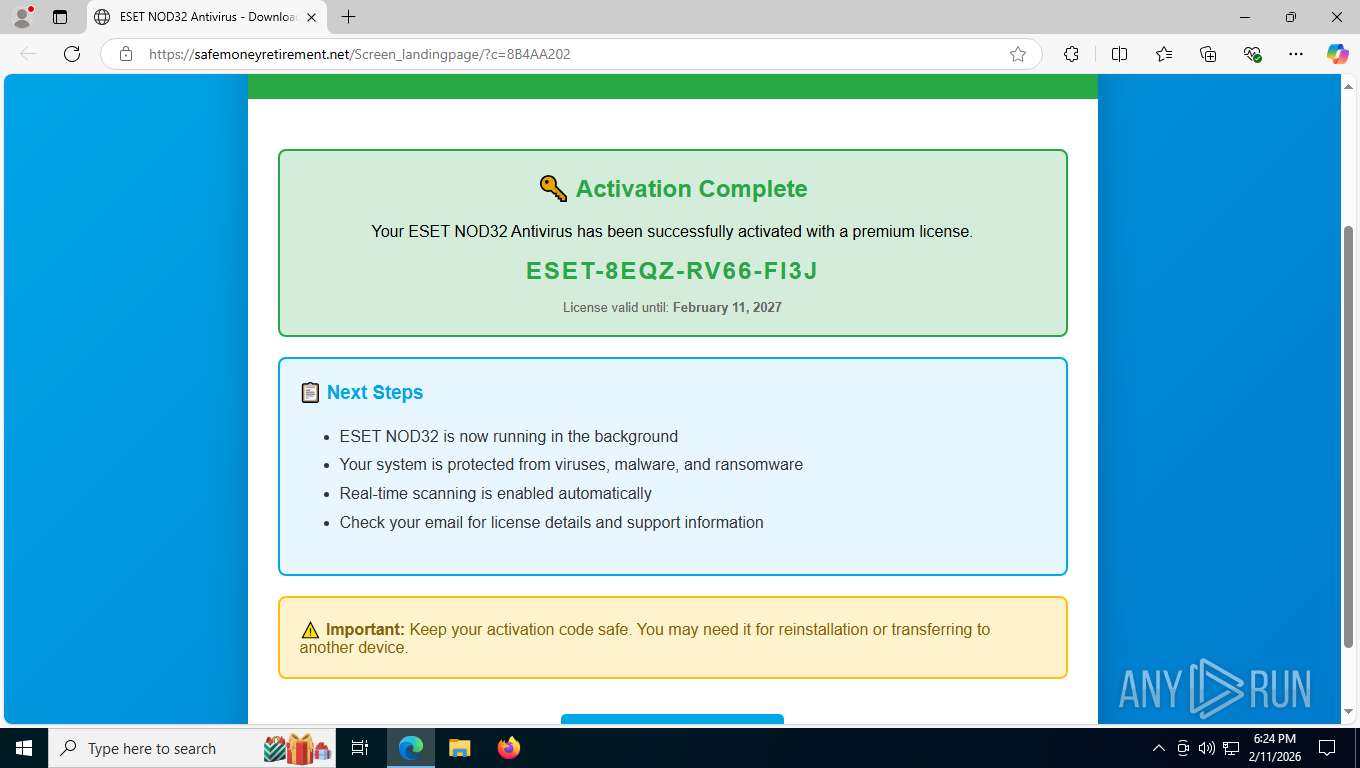
MALICIOUS
SCREENCONNECT has been detected
- msedge.exe (PID: 8864)
- rundll32.exe (PID: 7020)
- msedge.exe (PID: 8020)
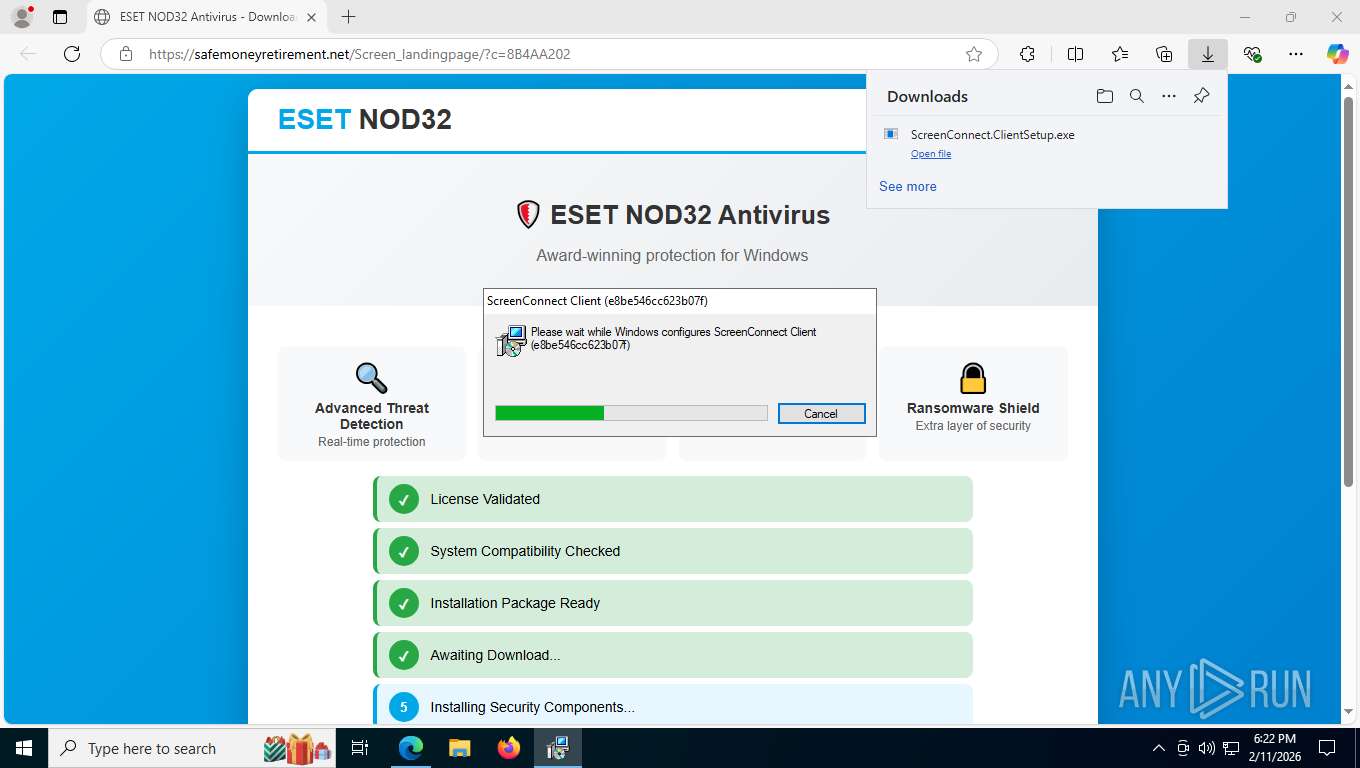
- msiexec.exe (PID: 7480)
- rundll32.exe (PID: 1136)
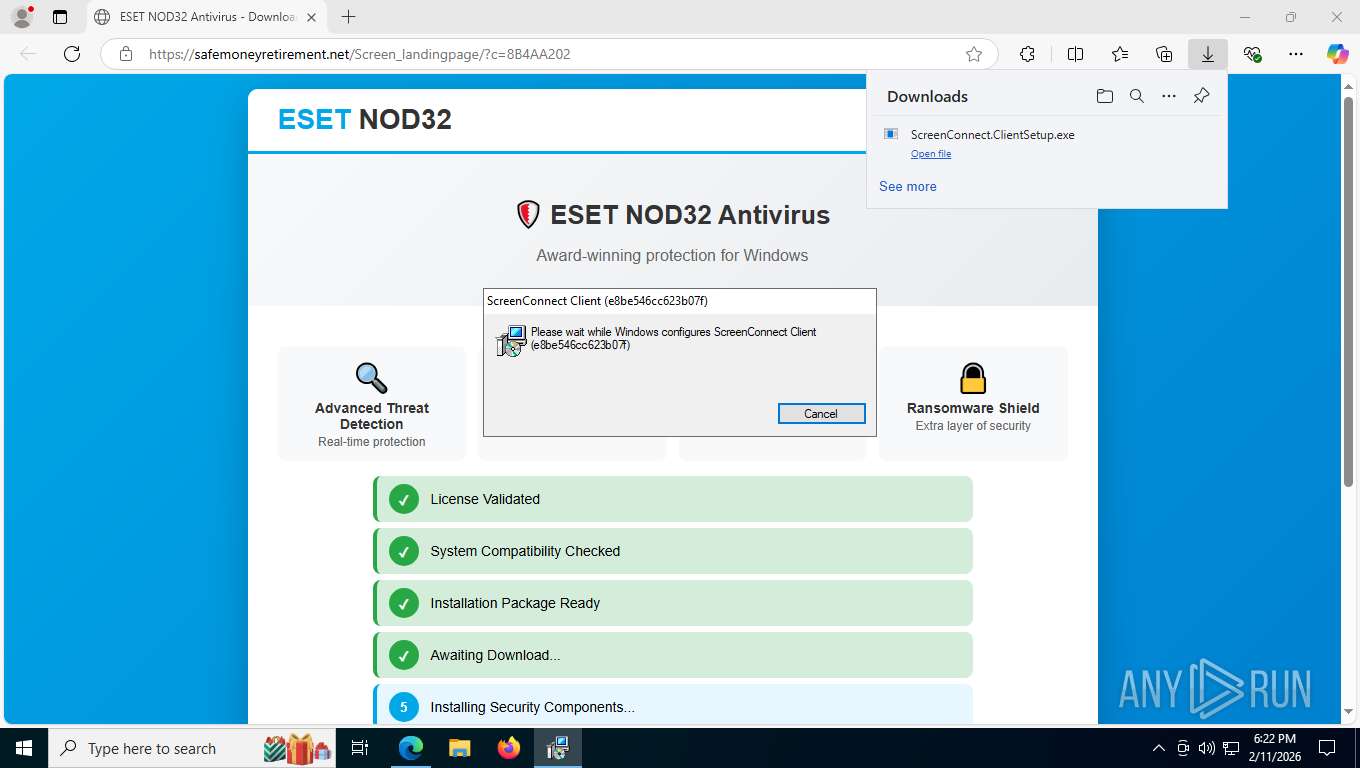
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6272)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 7020)
- rundll32.exe (PID: 1136)
Executes as Windows Service
- VSSVC.exe (PID: 8228)
- ScreenConnect.ClientService.exe (PID: 6272)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6272)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 6272)
- rundll32.exe (PID: 1136)
- ScreenConnect.ClientService.exe (PID: 6272)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 6272)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6272)
Detects ScreenConnect RAT (YARA)
- ScreenConnect.ClientService.exe (PID: 6272)
INFO
Drops script file
- msedge.exe (PID: 8864)
- msedge.exe (PID: 5164)
Checks supported languages
- identity_helper.exe (PID: 5548)
- ScreenConnect.ClientSetup.exe (PID: 8596)
- msiexec.exe (PID: 2460)
- msiexec.exe (PID: 7480)
- msiexec.exe (PID: 2864)
- msiexec.exe (PID: 7780)
- ScreenConnect.ClientService.exe (PID: 6272)
- ScreenConnect.WindowsClient.exe (PID: 8700)
- ScreenConnect.WindowsClient.exe (PID: 4664)
- identity_helper.exe (PID: 8040)
- ScreenConnect.ClientSetup.exe (PID: 2992)
- msiexec.exe (PID: 7940)
- msiexec.exe (PID: 5636)
Application launched itself
- msedge.exe (PID: 8864)
Executable content was dropped or overwritten
- msedge.exe (PID: 2456)
- msedge.exe (PID: 8864)
- msiexec.exe (PID: 6096)
- msiexec.exe (PID: 7480)
- msiexec.exe (PID: 2236)
Reads the computer name
- identity_helper.exe (PID: 5548)
- msiexec.exe (PID: 7480)
- msiexec.exe (PID: 2460)
- msiexec.exe (PID: 2864)
- ScreenConnect.ClientSetup.exe (PID: 8596)
- msiexec.exe (PID: 7780)
- ScreenConnect.ClientService.exe (PID: 6272)
- ScreenConnect.WindowsClient.exe (PID: 8700)
- ScreenConnect.WindowsClient.exe (PID: 4664)
- identity_helper.exe (PID: 8040)
- ScreenConnect.ClientSetup.exe (PID: 2992)
- msiexec.exe (PID: 7940)
- msiexec.exe (PID: 5636)
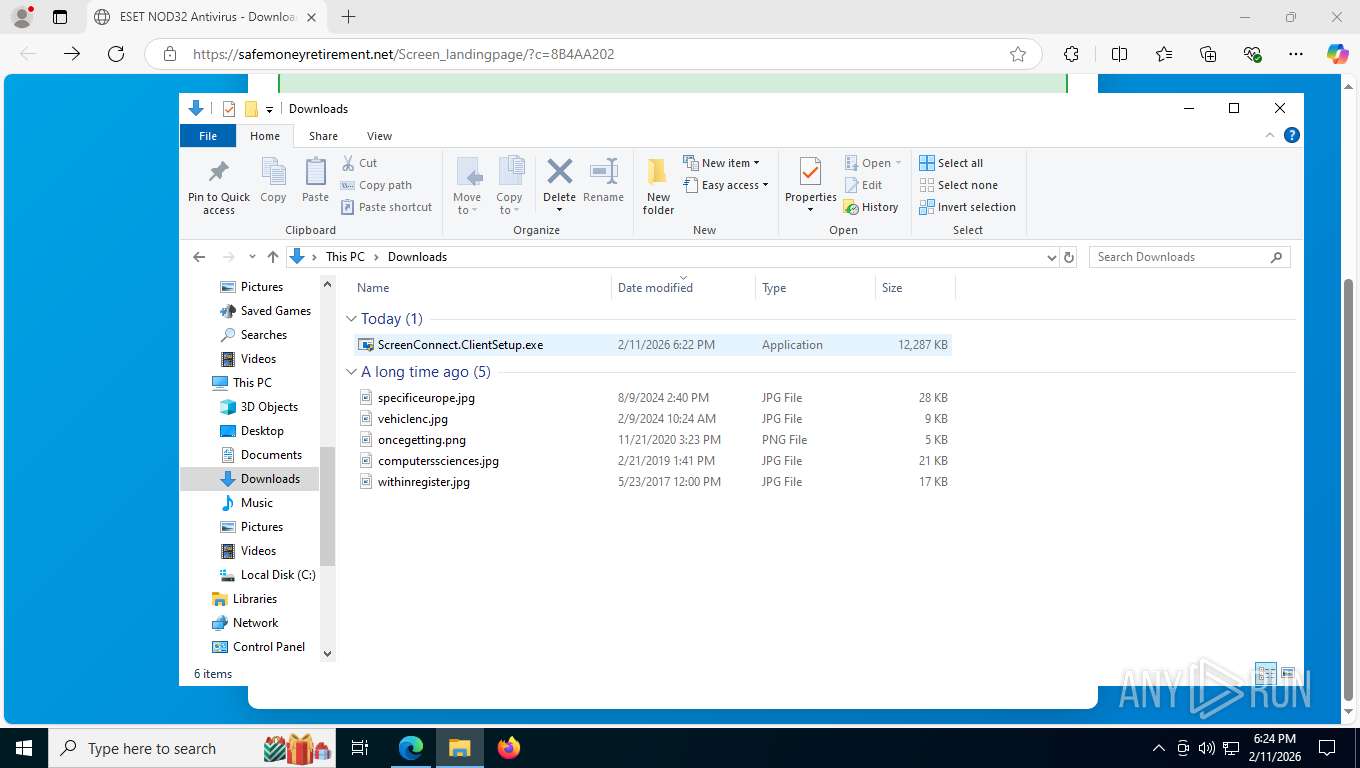
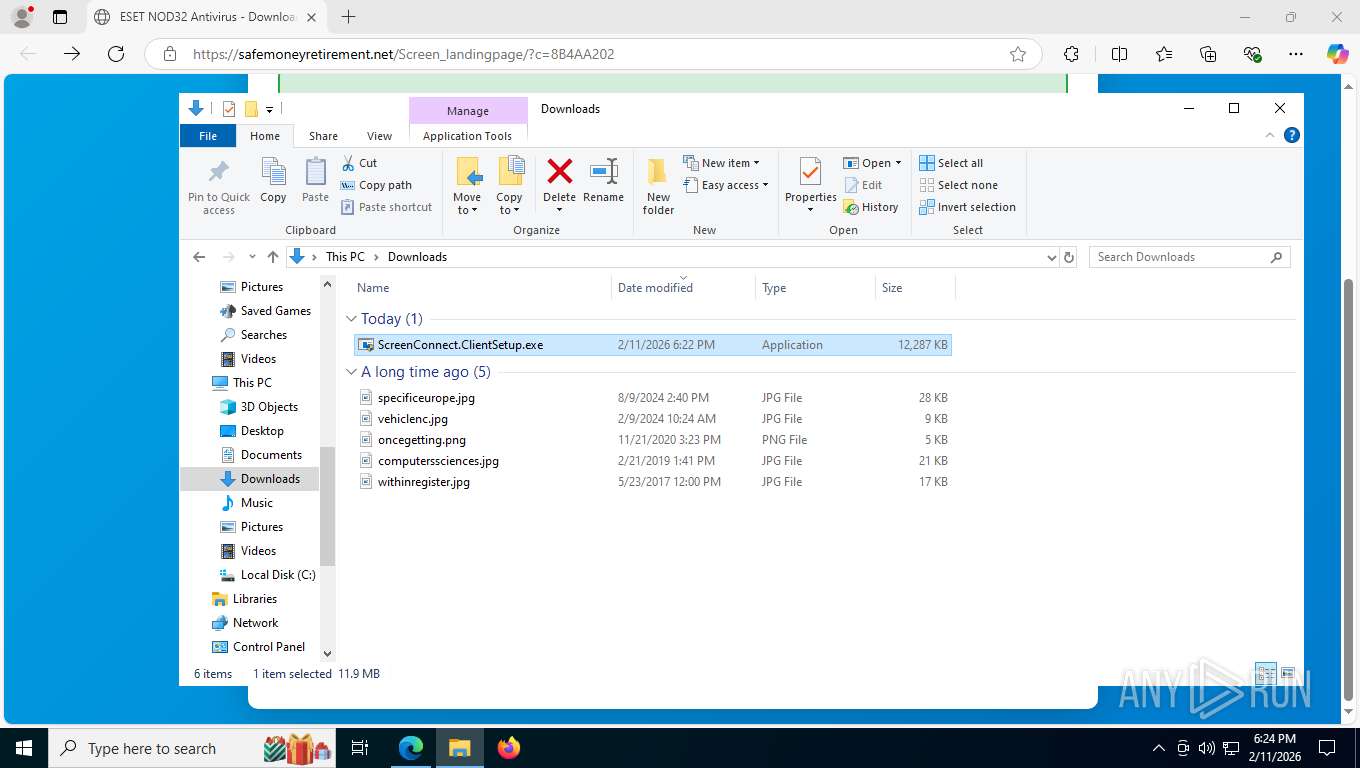
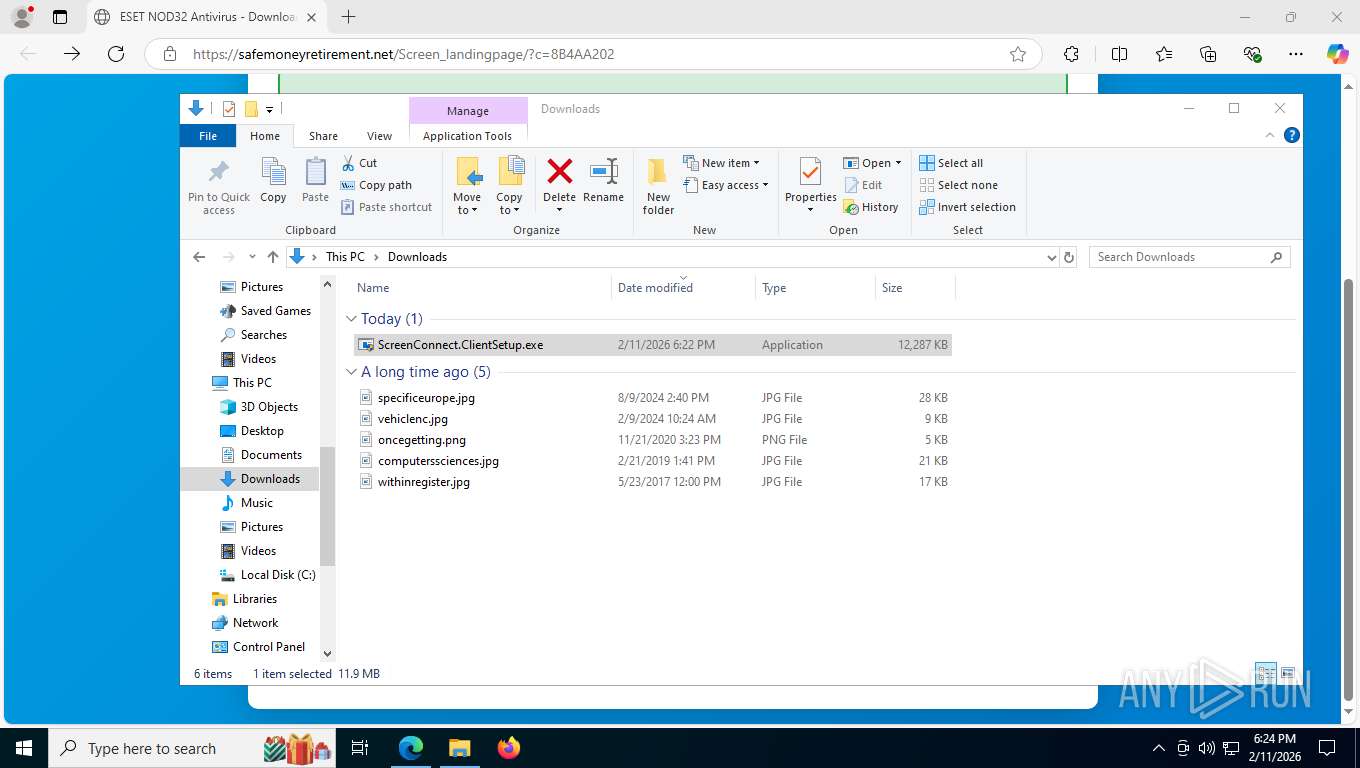
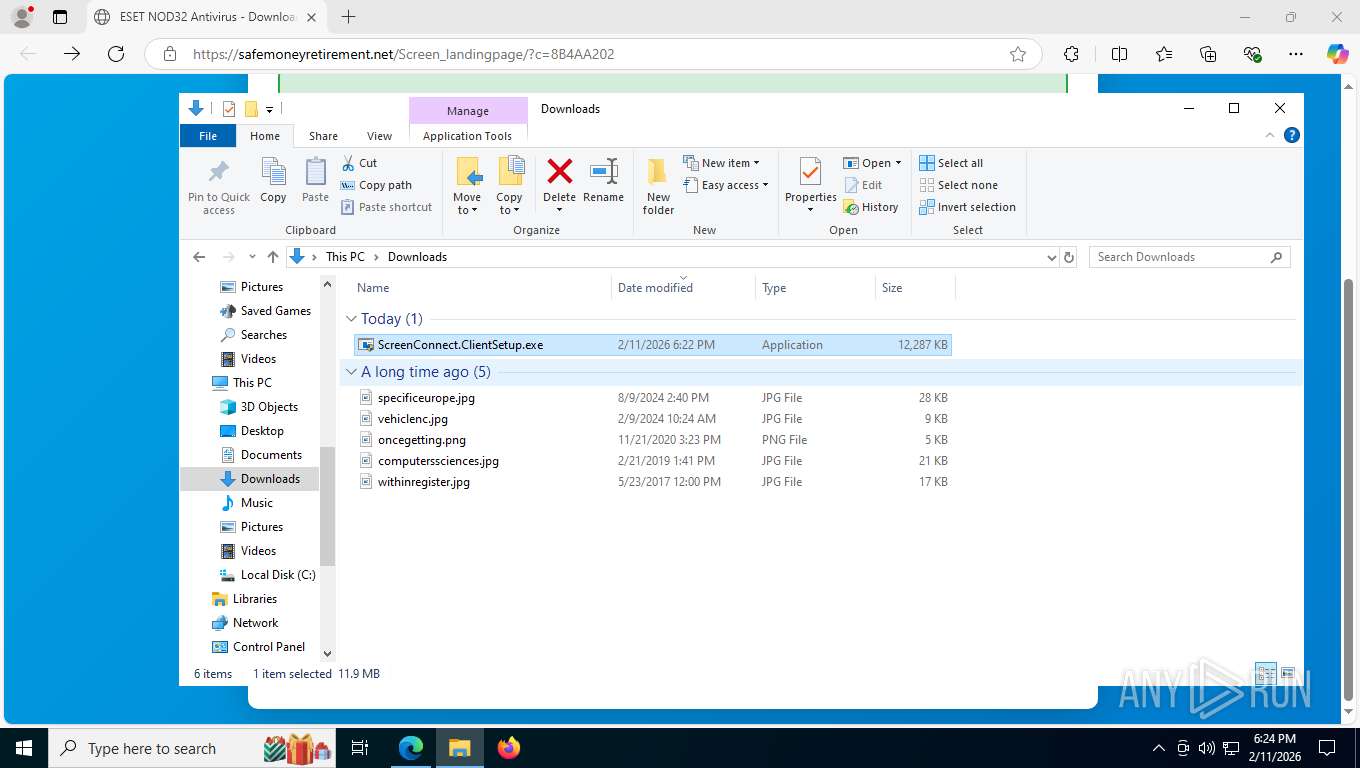
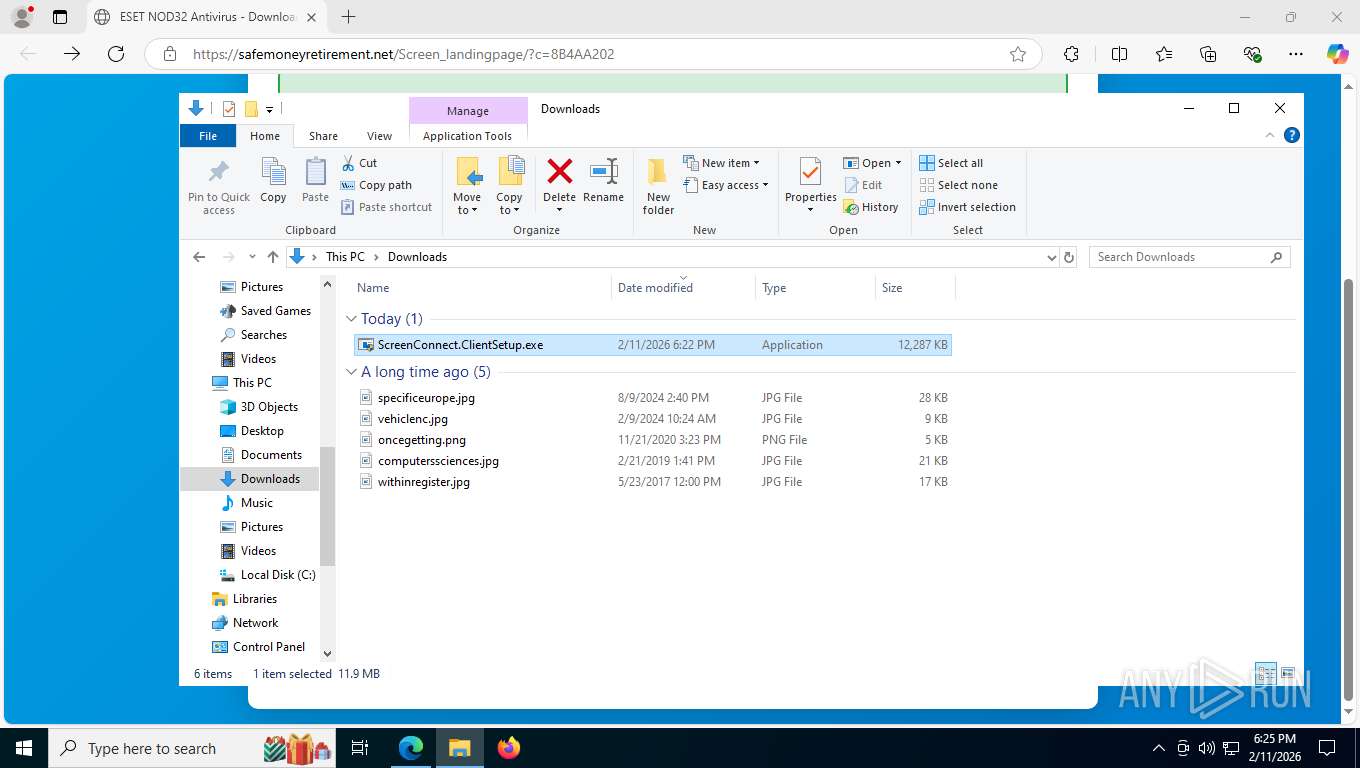
Launching a file from the Downloads directory
- msedge.exe (PID: 8864)
Reads security settings of Internet Explorer
- ScreenConnect.ClientSetup.exe (PID: 8596)
- msiexec.exe (PID: 6096)
- ScreenConnect.ClientService.exe (PID: 6272)
- ScreenConnect.WindowsClient.exe (PID: 8700)
- ScreenConnect.WindowsClient.exe (PID: 4664)
- ScreenConnect.ClientSetup.exe (PID: 2992)
Process checks computer location settings
- ScreenConnect.ClientSetup.exe (PID: 8596)
- ScreenConnect.ClientSetup.exe (PID: 2992)
Create files in a temporary directory
- ScreenConnect.ClientSetup.exe (PID: 8596)
- rundll32.exe (PID: 7020)
- ScreenConnect.ClientSetup.exe (PID: 2992)
- rundll32.exe (PID: 1136)
Creates files or folders in the user directory
- msiexec.exe (PID: 6096)
Checks proxy server information
- msiexec.exe (PID: 6096)
- slui.exe (PID: 2864)
Reads Environment values
- identity_helper.exe (PID: 5548)
- identity_helper.exe (PID: 8040)
Manages system restore points
- SrTasks.exe (PID: 1632)
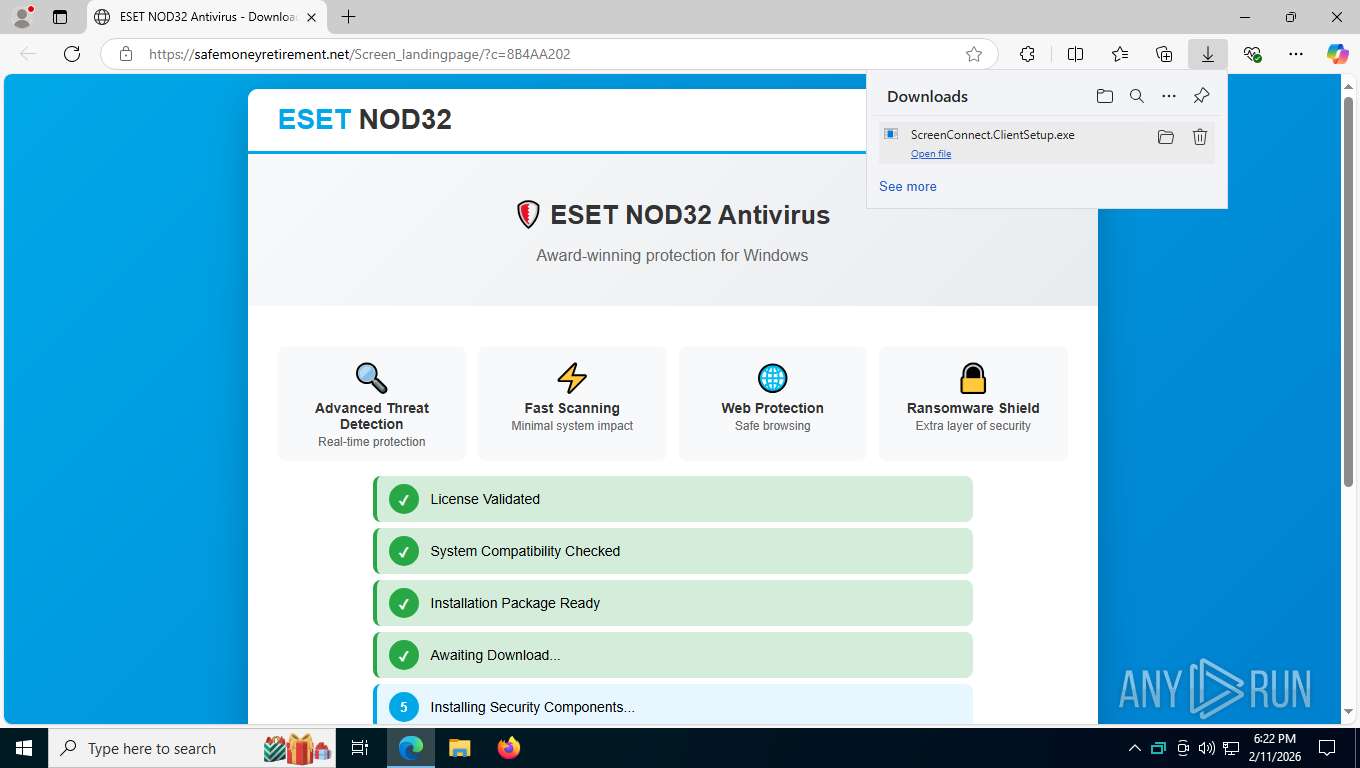
CONNECTWISE has been detected
- msiexec.exe (PID: 6096)
- ScreenConnect.ClientService.exe (PID: 6272)
- ScreenConnect.WindowsClient.exe (PID: 8700)
- ScreenConnect.WindowsClient.exe (PID: 4664)
- msiexec.exe (PID: 2236)
Reads the machine GUID from the registry
- ScreenConnect.ClientSetup.exe (PID: 8596)
- ScreenConnect.ClientService.exe (PID: 6272)
- ScreenConnect.WindowsClient.exe (PID: 8700)
- ScreenConnect.WindowsClient.exe (PID: 4664)
- ScreenConnect.ClientSetup.exe (PID: 2992)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 6272)
- rundll32.exe (PID: 1136)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 4664)
Manual execution by a user
- ScreenConnect.ClientSetup.exe (PID: 2992)
- ScreenConnect.ClientSetup.exe (PID: 6476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
65
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIBCAD.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_2145500 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5708,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6952 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2792,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2804 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:15 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4236,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4264 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2288,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2268 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2236 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\25.9.5.9473\e8be546cc623b07f\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | ScreenConnect.ClientSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7344,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7484 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=31 --always-read-main-dll --field-trial-handle=5268,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=8100 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2352,i,1169906503401772203,2024483578152313291,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2512 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
12 661
Read events
12 501
Write events
151
Delete events
9
Modification events
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000EE7D154CAD9BDC01381D0000A41F0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000B090284CAD9BDC01381D0000A41F0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000030F32A4CAD9BDC01381D0000DC180000E803000001000000000000000000000006B52BEA7AA29C4396AAF799F1DC277600000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000763AD04BAD9BDC01381D0000A41F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000002191D04BAD9BDC01381D0000A41F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000811B134CAD9BDC01381D0000A41F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000811B134CAD9BDC01381D0000A41F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000811B134CAD9BDC01381D0000A41F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8228) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000093DE364CAD9BDC0124200000041E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
35
Suspicious files
251
Text files
339
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e4da1.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e4db0.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e4db0.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e4dc0.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e4dc0.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
490
TCP/UDP connections
232
DNS requests
264
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2456 | msedge.exe | GET | 302 | 188.114.97.3:443 | https://safemoneyretirement.net/cdn-cgi/challenge-platform/scripts/jsd/main.js | unknown | — | — | unknown |
2456 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=jIXIAX3vi%2F7AYwli1IoTYnqwgizRQKpU3I7E14%2F0zFbSR8P0g%2FjufMcUC8WjXBIwaz6aw1aWUJ55shLXh6VF%2Bk4X6xqjW7vscFzzLZS2DbCt9UqkkD5Z | unknown | — | — | unknown |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
2456 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:yt2PpkmhG2weOFBZlz_kbrC9CZBpwg0Z_58s1IzhHEk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2456 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
2456 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
2456 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | binary | 82 b | whitelisted |
2456 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://safemoneyretirement.net/Screen_landingpage/?c=8B4AA202 | unknown | html | 19.3 Kb | unknown |
2456 | msedge.exe | GET | 200 | 52.123.243.200:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4936 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7212 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 95.100.158.122:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2456 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2456 | msedge.exe | 52.123.243.200:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2456 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
xianshuabao.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2456 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2456 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2456 | msedge.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2456 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
2456 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
2456 | msedge.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
2456 | msedge.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
2456 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |