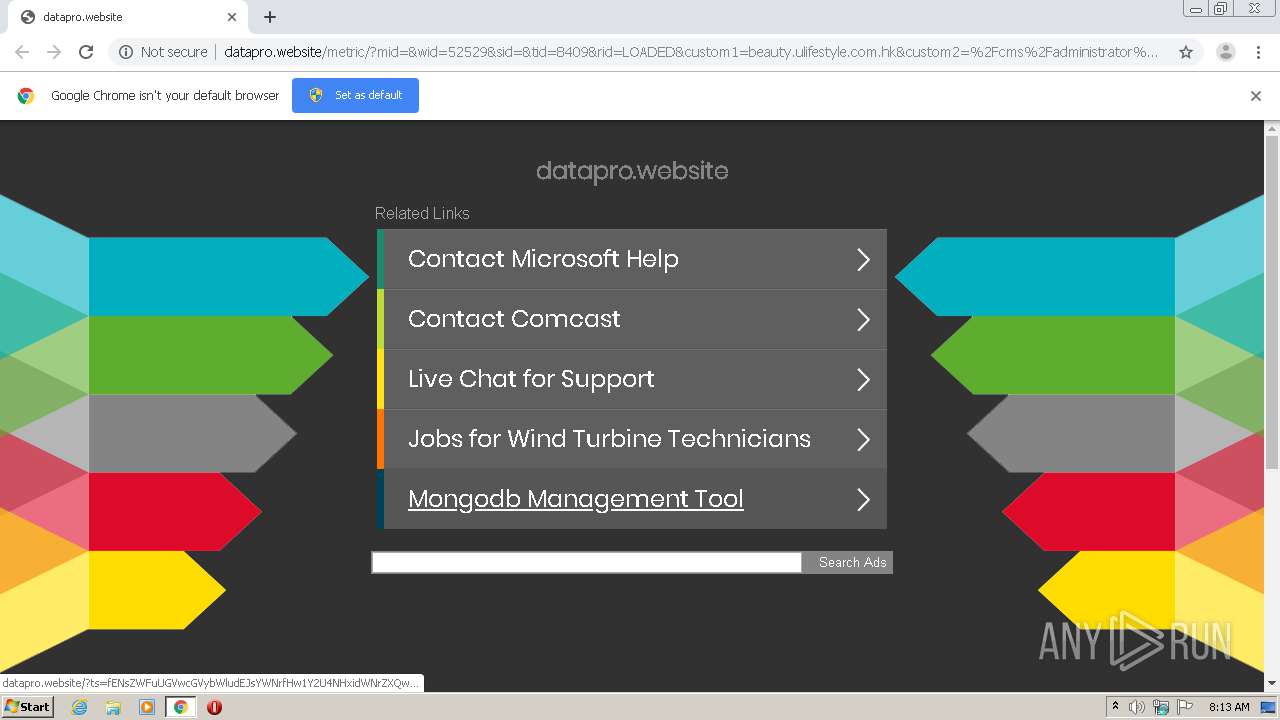
| URL: | http://datapro.website/metric/?mid=&wid=52529&sid=&tid=8409&rid=LOADED&custom1=beauty.ulifestyle.com.hk&custom2=%2Fcms%2Fadministrator%2Findex.php&t=1567413734873 |
| Full analysis: | https://app.any.run/tasks/6431bbcb-f4b5-4fda-a359-f32b9d2a1365 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 07:12:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 705D0FC79AA25D808B7FED5899EF8FD5 |
| SHA1: | 5BEB6FA39BFF109CA7D73411DC20A25184FB0246 |
| SHA256: | 47F1516D81FDA934DCDF04641AA47A3396ABDC3926726177F5F0A38F3CE6569B |
| SSDEEP: | 3:N1KaERECXMYI99a2u6xU/GR3KBDRb5/5XWR3CjKQHKEqWRdln:CajYI99a2NK/GJO9BW4+QHKE/n |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 3844)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1860)
INFO
Application launched itself
- chrome.exe (PID: 1860)
Reads the hosts file
- chrome.exe (PID: 1860)
- chrome.exe (PID: 3844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
26
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2939215525784856402 --mojo-platform-channel-handle=4732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=760 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15759319317175452531 --mojo-platform-channel-handle=4424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3505259976443173986 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16390031497934338659 --mojo-platform-channel-handle=4456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7407943316728044630 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://datapro.website/metric/?mid=&wid=52529&sid=&tid=8409&rid=LOADED&custom1=beauty.ulifestyle.com.hk&custom2=%2Fcms%2Fadministrator%2Findex.php&t=1567413734873" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4033009876749101285 --mojo-platform-channel-handle=4004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4311518096970958363 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,2871755466482350675,6969180323722827014,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1259306127178641549 --mojo-platform-channel-handle=4440 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
602
Read events
513
Write events
84
Delete events
5
Modification events
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1052) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1860-13239097983214875 |
Value: 259 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
20
Text files
196
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0C0980-744.pma | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\41ff84db-3227-4bb0-a01f-940dcad18326.tmp | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15cc33.TMP | text | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15cc33.TMP | text | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15cdf8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
29
DNS requests
15
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
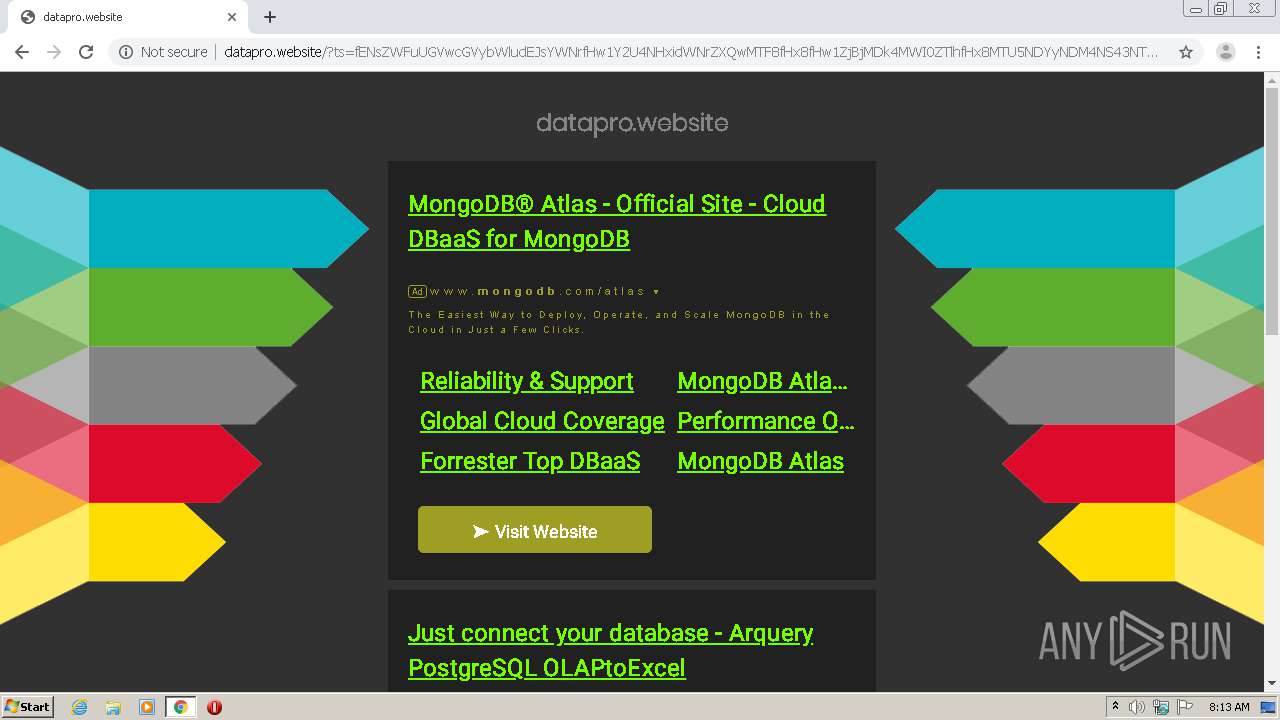
3844 | chrome.exe | GET | 200 | 75.2.37.224:80 | http://datapro.website/metric/?mid=&wid=52529&sid=&tid=8409&rid=LOADED&custom1=beauty.ulifestyle.com.hk&custom2=%2Fcms%2Fadministrator%2Findex.php&t=1567413734873 | US | html | 4.28 Kb | malicious |
3844 | chrome.exe | GET | 200 | 143.204.208.65:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/cleanPeppermint_7a82f1f3/style.css | US | text | 571 b | shared |
3844 | chrome.exe | GET | 200 | 143.204.208.65:80 | http://d1lxhc4jvstzrp.cloudfront.net/scripts/js3caf.js | US | text | 6.17 Kb | shared |
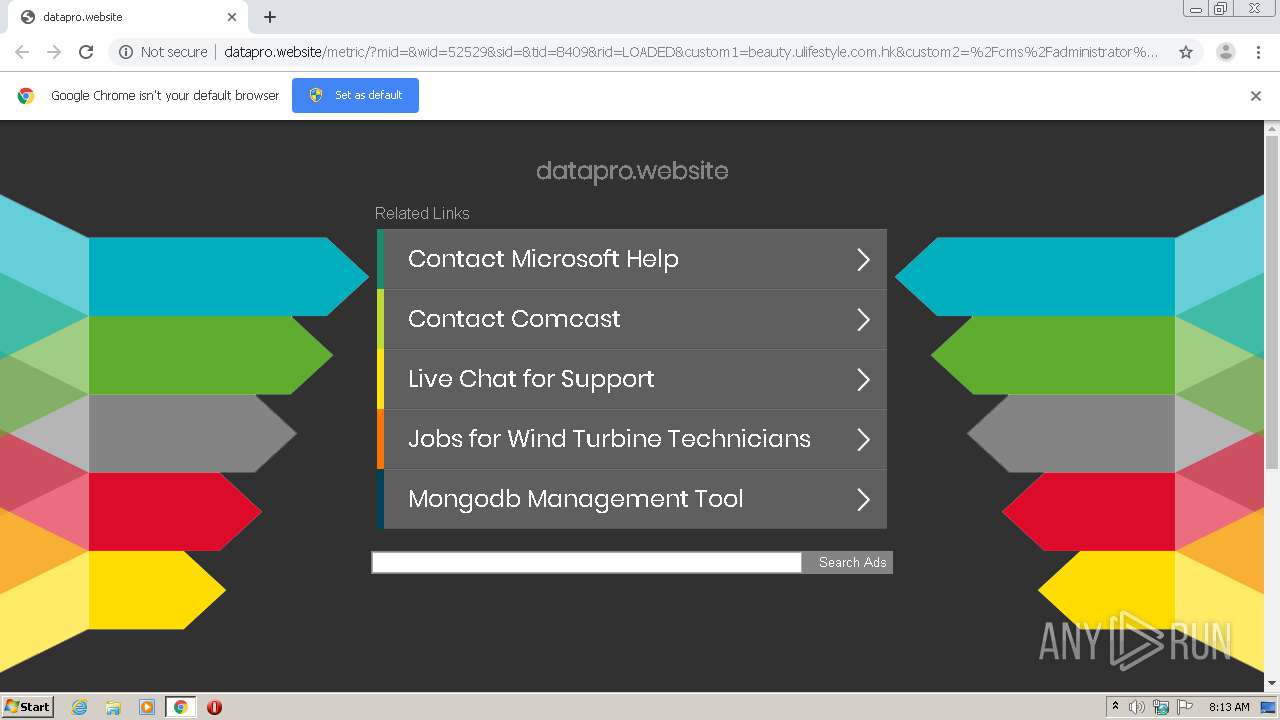
3844 | chrome.exe | GET | 200 | 75.2.37.224:80 | http://datapro.website/?ts=fENsZWFuUGVwcGVybWludEJsYWNrfHw1Y2U4NHxidWNrZXQwMTF8fHx8fHw1ZjBjMDk4MWI0ZTlhfHx8MTU5NDYyNDM4NS43NTE4fDFlMmQxYmM1MDdiYzRjZmY0NDc3NDkzZDZmZjU0MTY5NzgwMjUyNGN8fHx8fDF8fHwwfHx8fDF8fHx8fDB8MHx8fHx8fHx8fHwwfDF8fDB8MHwxfDB8MHxXMTA9fHwxfFcxMD0%3D&query=Mongodb%20Management%20Tool&afdToken=3B1ggjunaKLv4lfkwvTMYAX99adt3mkULYbIrX9OWDot-_jskpo9aISIrsFsrrfmY3LusV8dXjqFtdcT8NZv1Tu7_rNrGOfmXtFd-hLFFQ&pcsa=false | US | html | 4.56 Kb | malicious |
3844 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3844 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3844 | chrome.exe | GET | 200 | 143.204.208.65:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/assets/style.css | US | text | 343 b | shared |
3844 | chrome.exe | GET | 200 | 75.2.37.224:80 | http://datapro.website/track.php?domain=datapro.website&caf=1&toggle=answercheck&answer=yes&uid=MTU5NDYyNDM4NS43NDY0OjZiY2Y2MDBkNTFkNDk5NzhjYWRlYzAzNDdiOThhOWQyOTJmMjZhMjI4ZTliNjVlYTE1ZjlkMmRkZTc5MzAyMzI6NWYwYzA5ODFiNjM3Mw%3D%3D | US | binary | 20 b | malicious |
3844 | chrome.exe | POST | 201 | 75.2.37.224:80 | http://datapro.website/ls.php | US | compressed | 20 b | malicious |
3844 | chrome.exe | GET | 200 | 75.2.37.224:80 | http://datapro.website/favicon.ico | US | compressed | 20 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3844 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 143.204.208.65:80 | d1lxhc4jvstzrp.cloudfront.net | — | US | suspicious |
3844 | chrome.exe | 172.217.16.164:80 | www.google.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3844 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
datapro.website |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
d1lxhc4jvstzrp.cloudfront.net |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3844 | chrome.exe | A Network Trojan was detected | ET MALWARE LNKR CnC Activity M3 |
3844 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |
3844 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |