| File name: | Eraser 6.2.0.2994.exe |
| Full analysis: | https://app.any.run/tasks/13dbb569-a165-488a-acfa-230542ea9935 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 17:43:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0A1244D8DC16D7D70E267E932042ED1C |
| SHA1: | 6647141ADF7F2742B33741D2D07D12D07E55EDBC |
| SHA256: | 47E484261A88BA1A895699D8FF0239E1F5089B4A96128E8E610E2B41A9BD4605 |
| SSDEEP: | 98304:3U9YQAY8ltNS/2CJuazPMJwt3hb8rO/jmnokZs52nCgIdVIGNnc7vegtTV3V9YaW:VZ9zIxu3abvpHUWX5J9 |
MALICIOUS
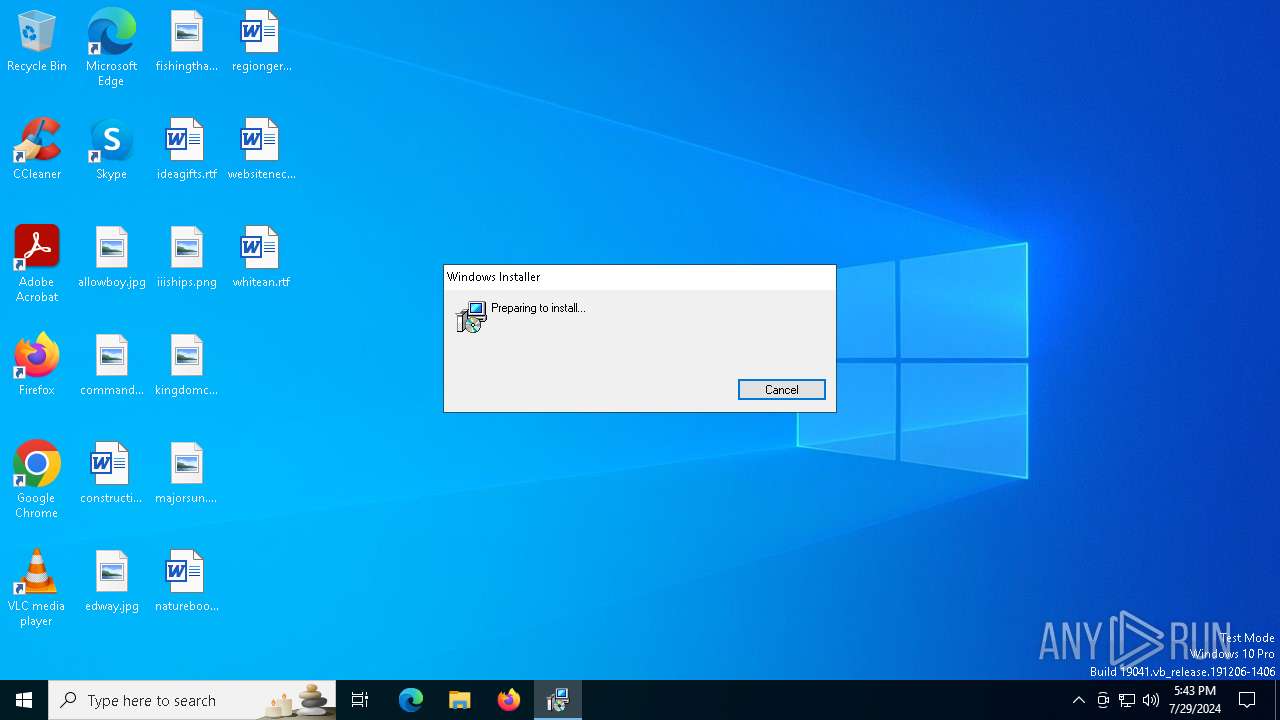
Drops the executable file immediately after the start
- Eraser 6.2.0.2994.exe (PID: 5272)
- msiexec.exe (PID: 3900)
Changes the autorun value in the registry
- msiexec.exe (PID: 3900)
SUSPICIOUS
The process creates files with name similar to system file names
- msiexec.exe (PID: 3900)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3900)
Process drops legitimate windows executable
- msiexec.exe (PID: 3900)
Adds/modifies Windows certificates
- msiexec.exe (PID: 6292)
Executes as Windows Service
- VSSVC.exe (PID: 3940)
The process drops C-runtime libraries
- msiexec.exe (PID: 3900)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3900)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7528)
- Eraser.exe (PID: 7616)
Reads the date of Windows installation
- msiexec.exe (PID: 7528)
- msiexec.exe (PID: 3900)
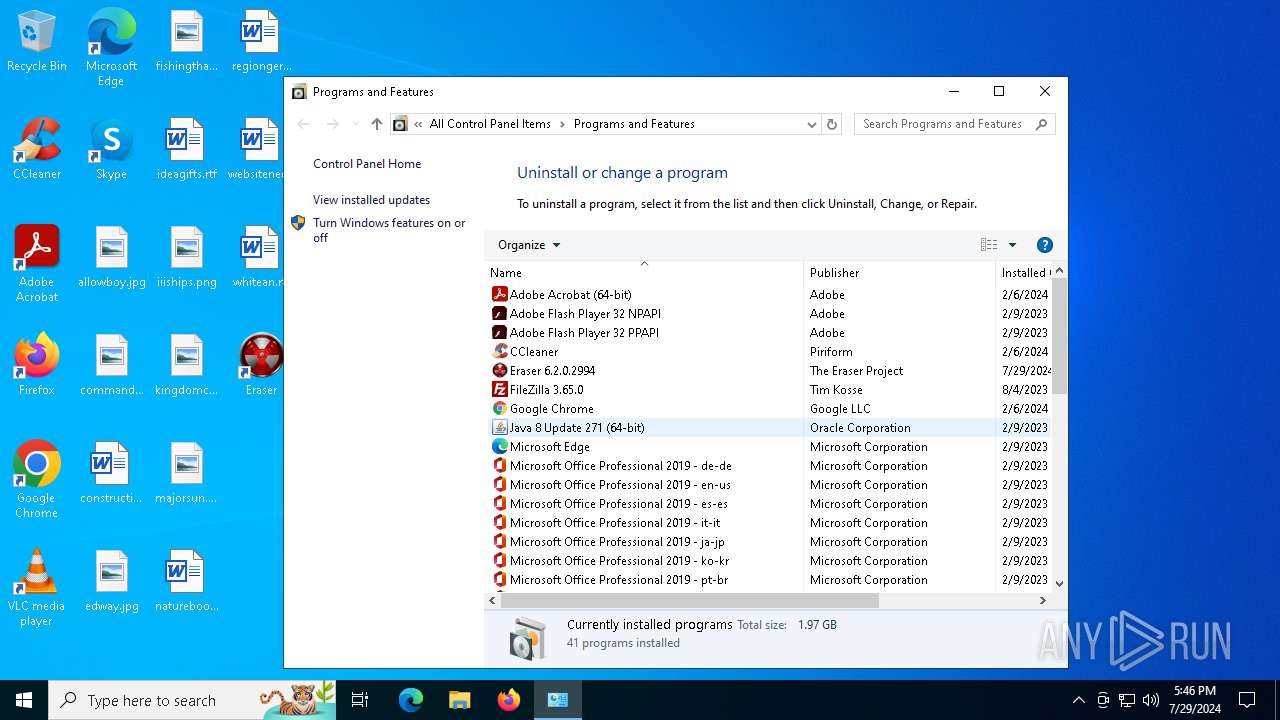
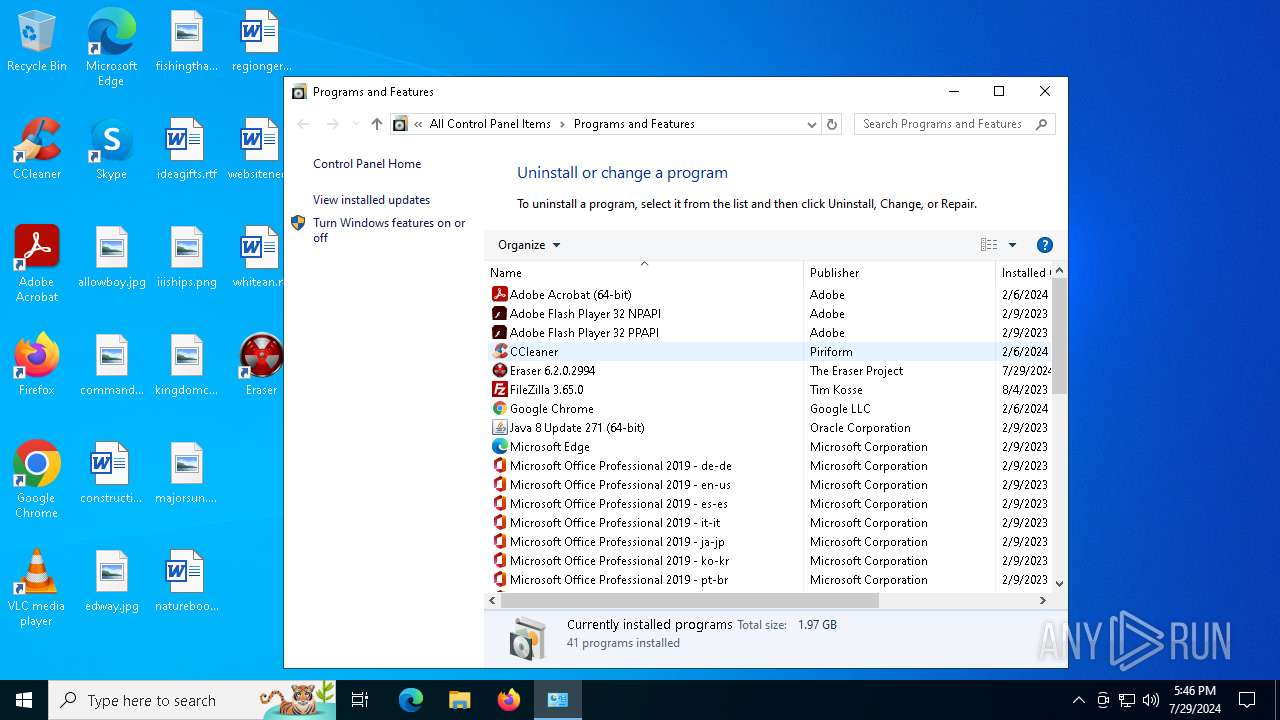
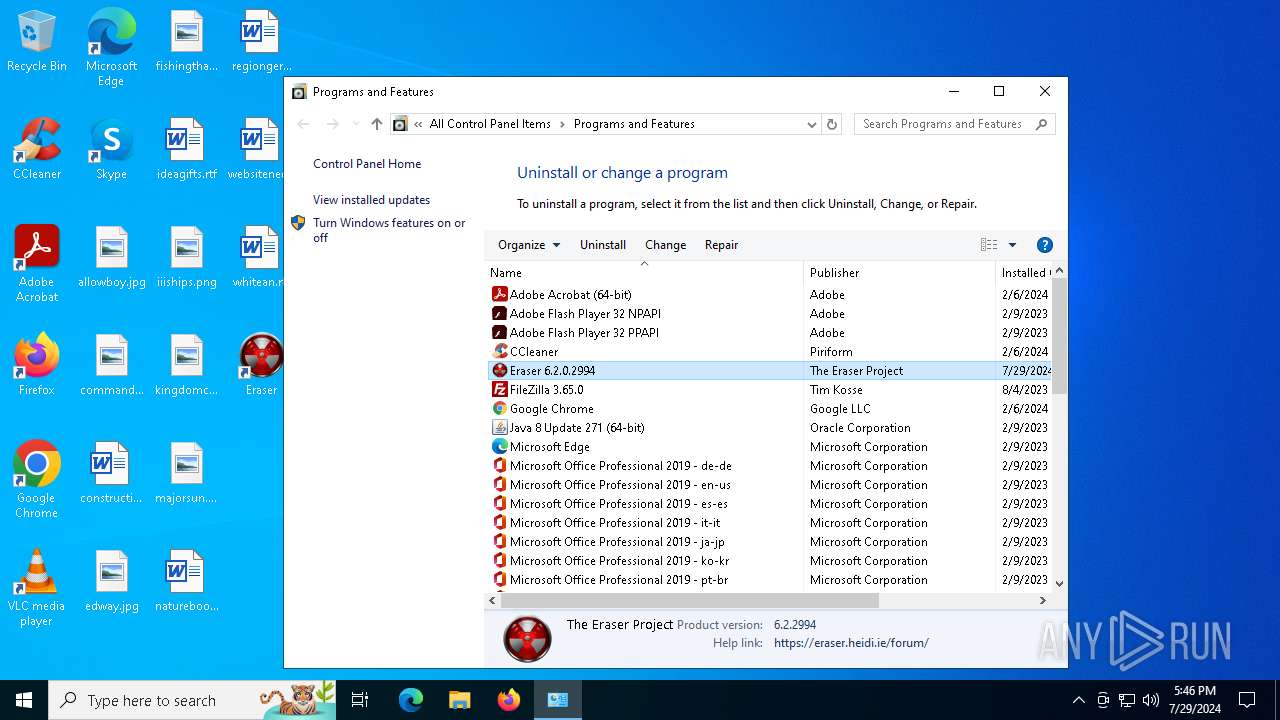
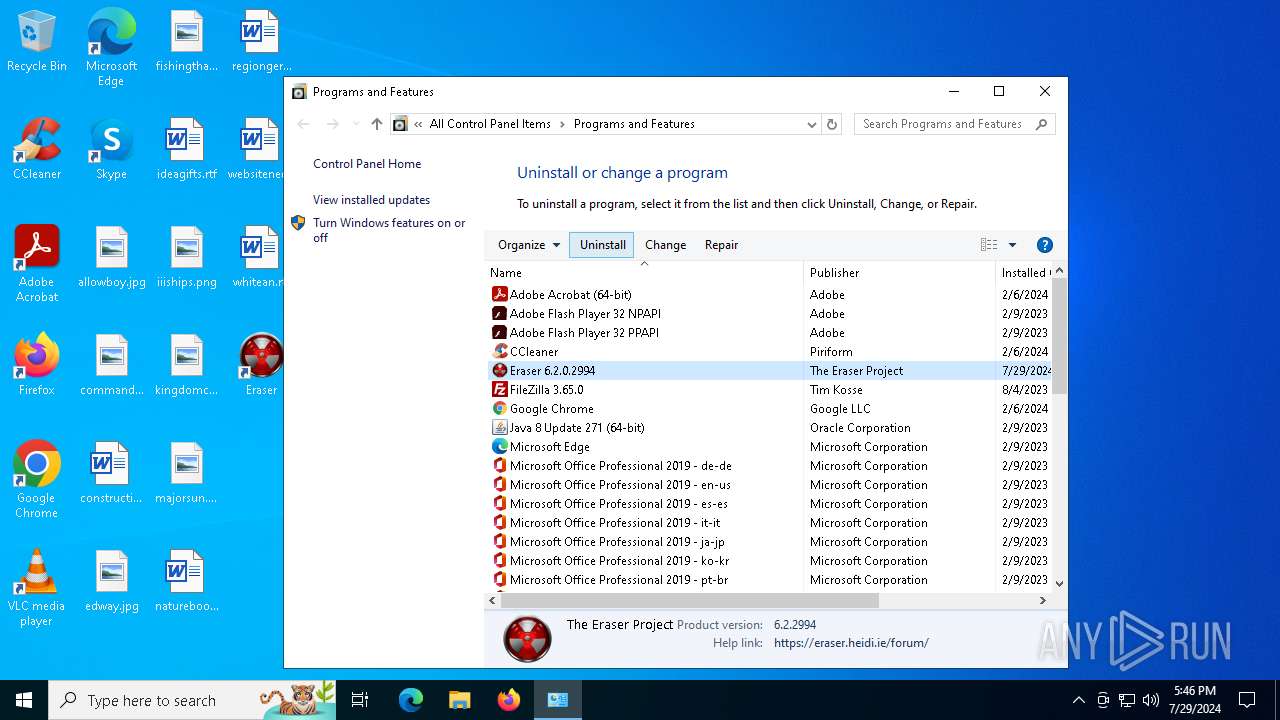
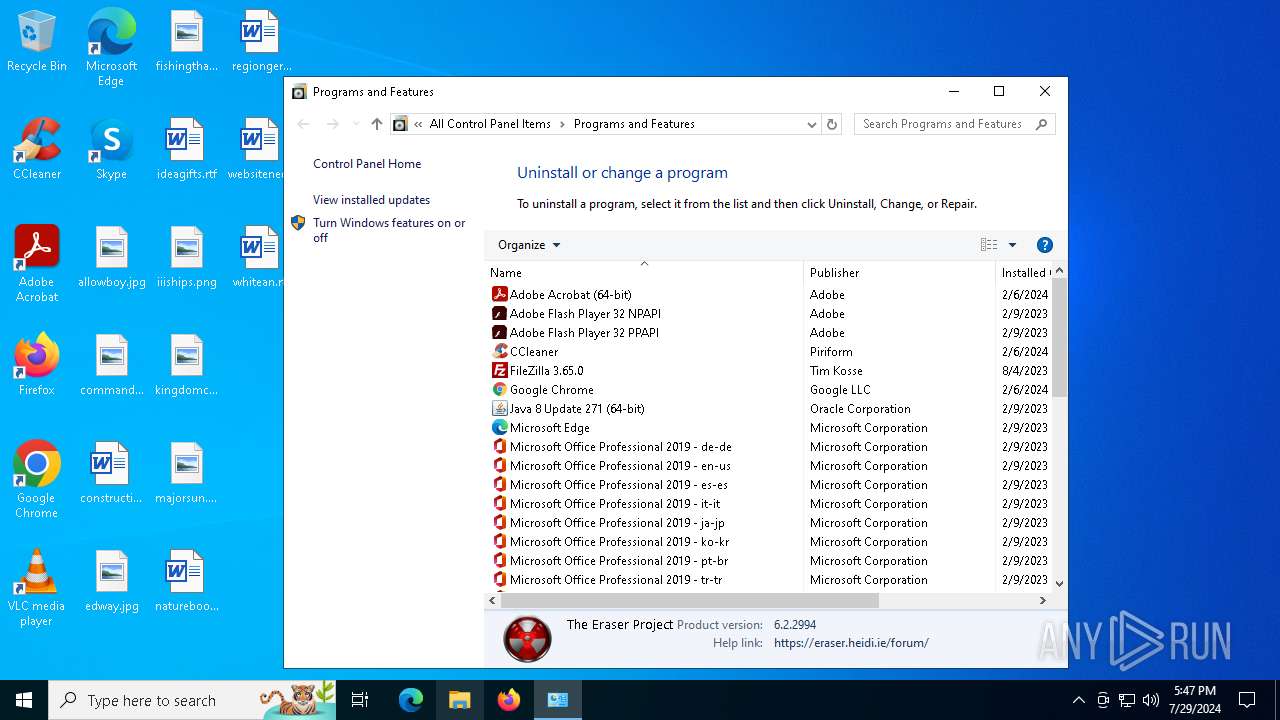
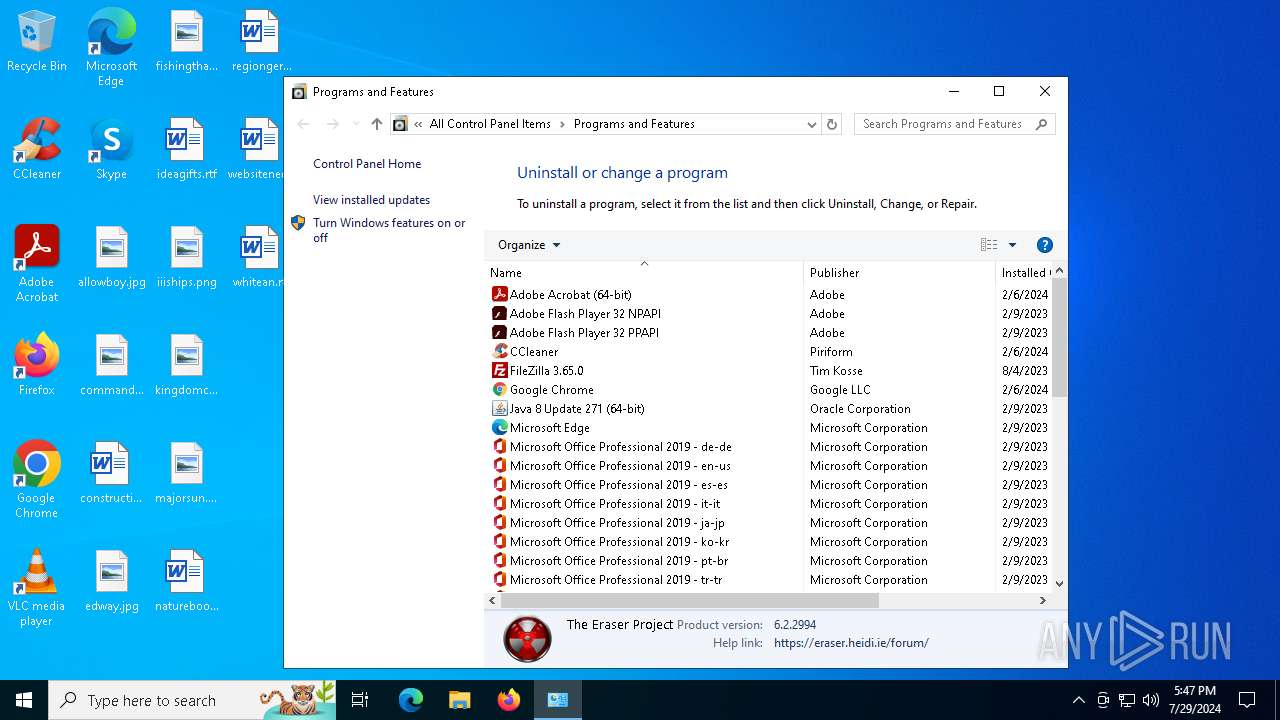
Searches for installed software
- explorer.exe (PID: 4500)
Checks Windows Trust Settings
- Eraser.exe (PID: 7616)
- msiexec.exe (PID: 3900)
INFO
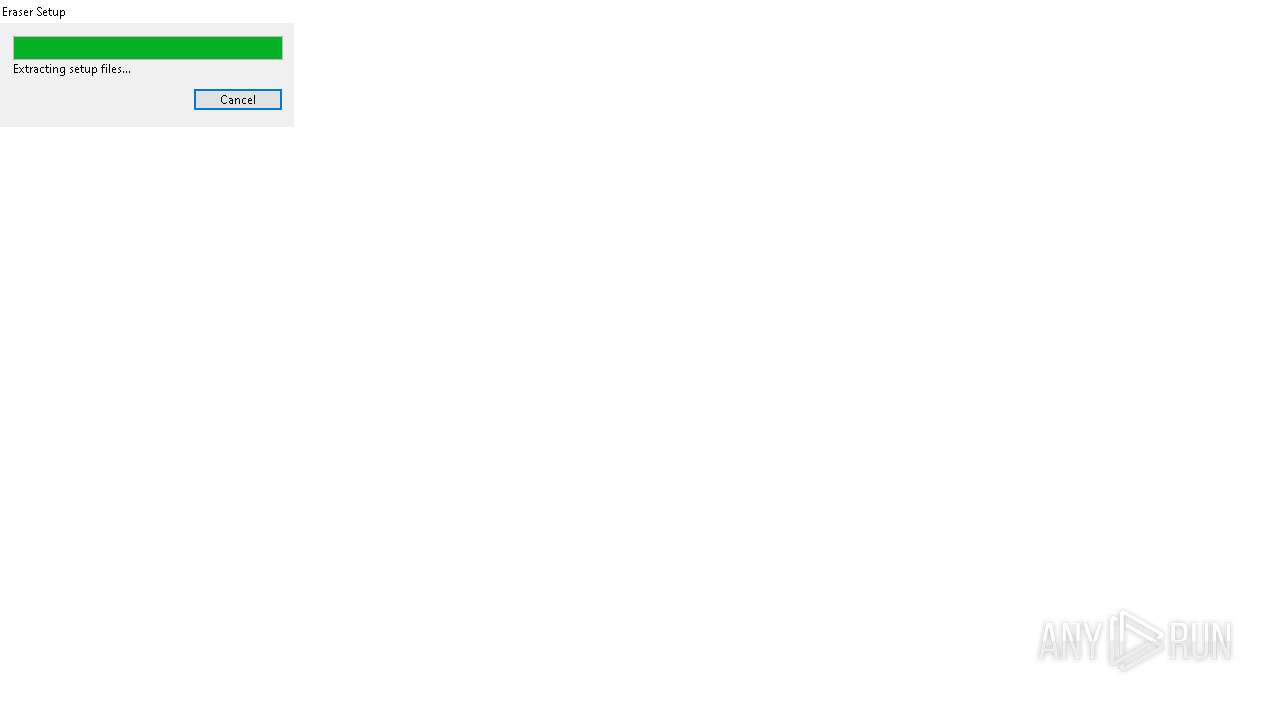
Create files in a temporary directory
- Eraser 6.2.0.2994.exe (PID: 5272)
Reads the software policy settings
- msiexec.exe (PID: 6292)
- Eraser.exe (PID: 7616)
- slui.exe (PID: 3656)
- msiexec.exe (PID: 3900)
Checks supported languages
- Eraser 6.2.0.2994.exe (PID: 5272)
- msiexec.exe (PID: 7528)
- Eraser.exe (PID: 7616)
- msiexec.exe (PID: 3900)
Reads the computer name
- Eraser 6.2.0.2994.exe (PID: 5272)
- msiexec.exe (PID: 7528)
- Eraser.exe (PID: 7616)
- msiexec.exe (PID: 3900)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3900)
- msiexec.exe (PID: 6292)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6292)
Creates files or folders in the user directory
- msiexec.exe (PID: 6292)
Checks proxy server information
- msiexec.exe (PID: 6292)
- slui.exe (PID: 3656)
Drops the executable file immediately after the start
- msiexec.exe (PID: 6292)
Process checks computer location settings
- msiexec.exe (PID: 7528)
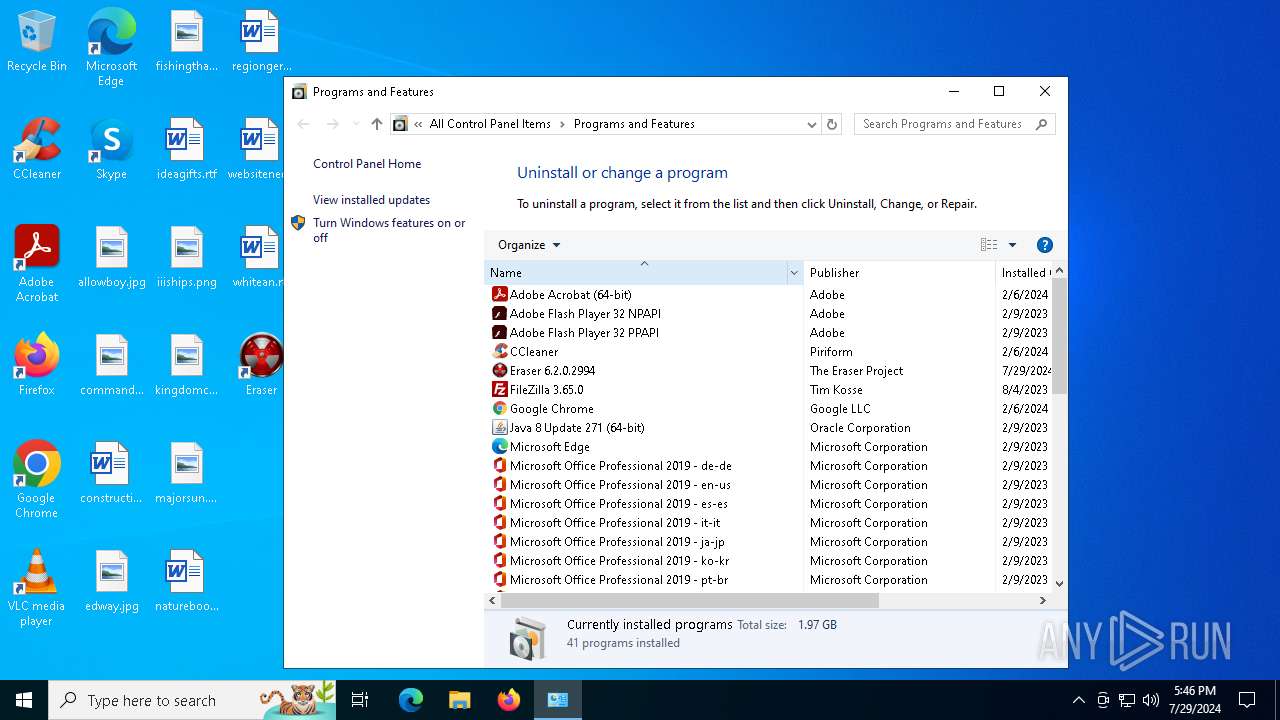
Creates a software uninstall entry
- msiexec.exe (PID: 3900)
Reads the machine GUID from the registry
- Eraser.exe (PID: 7616)
- msiexec.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 21:16:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.39 |
| CodeSize: | 99840 |
| InitializedDataSize: | 8731136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd4c7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.0.2994 |
| ProductVersionNumber: | 6.2.0.2994 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Eraser Setup Bootstrapper |
| CompanyName: | The Eraser Project |
| FileDescription: | Eraser Setup Bootstrapper |
| FileVersion: | 6.2.0.2994 |
| InternalName: | Eraser Setup Bootstrapper |
| LegalCopyright: | Copyright © 2008-2021 The Eraser Project |
| OriginalFileName: | Eraser Setup Bootstrapper |
| ProductVersion: | 6.2.0.2994 |
Total processes
169
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2188 | "C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2994.exe" | C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2994.exe | — | explorer.exe | |||||||||||
User: admin Company: The Eraser Project Integrity Level: MEDIUM Description: Eraser Setup Bootstrapper Exit code: 3221226540 Version: 6.2.0.2994 Modules
| |||||||||||||||
| 3656 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3940 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4500 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5272 | "C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2994.exe" | C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2994.exe | explorer.exe | ||||||||||||
User: admin Company: The Eraser Project Integrity Level: HIGH Description: Eraser Setup Bootstrapper Exit code: 0 Version: 6.2.0.2994 Modules
| |||||||||||||||
| 6292 | msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\Eraser (x64).msi" | C:\Windows\SysWOW64\msiexec.exe | Eraser 6.2.0.2994.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7248 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7356 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
56 893
Read events
55 979
Write events
687
Delete events
227
Modification events
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 8094640EB5A7A1CA119C1FDDD59F810263A7FBD1 |
Value: | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8094640EB5A7A1CA119C1FDDD59F810263A7FBD1 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000004FDD07E4D42264391E0C3742EAD1C6AE7A000000010000000C000000300A06082B06010505070309140000000100000014000000AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A06200000001000000200000002CABEAFE37D06CA22ABA7391C0033D25982952C453647349763A3AB5AD6CCF69090000000100000056000000305406082B0601050507030206082B06010505070303060A2B0601040182370A030C060A2B0601040182370A030406082B0601050507030406082B0601050507030906082B0601050507030106082B06010505070308190000000100000010000000CB9DD0FCEAAA492F75CE292C21BBFBDD0300000001000000140000008094640EB5A7A1CA119C1FDDD59F810263A7FBD10F0000000100000030000000EA09C51D4C3A334CE4ACD2BC08C6A9BE352E334F45C4FCCFCAB63EDB9F82DC87D4BD2ED2FADAE11163FB954809984FF153000000010000007E000000307C301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301F06092B06010401A032010230123010060A2B0601040182373C0101030200C0301B060567810C010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200360000007F0000000100000016000000301406082B0601050507030306082B060105050703091D0000000100000010000000521F5C98970D19A8E515EF6EEB6D48EF7E00000001000000080000000080C82B6886D701200000000100000087050000308205833082036BA003020102020E45E6BB038333C3856548E6FF4551300D06092A864886F70D01010C0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3134313231303030303030305A170D3334313231303030303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820222300D06092A864886F70D01010105000382020F003082020A02820201009507E873CA66F9EC14CA7B3CF70D08F1B4450B2C82B448C6EB5B3CAE83B841923314A46F7FE92ACCC6B0886BC5B689D1C6B2FF14CE511421EC4ADD1B5AC6D687EE4D3A1506ED64660B9280CA44DE73944EF3A7897F4F786308C812506D42662F4DB979284D521A8A1A80B719810E7EC48ABC644C211C4368D73D3C8AC5B266D5909AB73106C5BEE26D3206A61EF9B9EBAAA3B8BFBE826350D0F01889DFE40F79F5EAA21F2AD2702E7BE7BC93BB6D53E2487C8C100738FF66B277617EE0EA8C3CAAB4A4F6F3954A12076DFD8CB289CFD0A06177C85874B0D4233AF75D3ACAA2DB9D09DE5D442D90F181CD5792FA7EBC50046334DF6B9318BE6B36B239E4AC2436B7F0EFB61C135793B6DEB2F8E285B773A2B835AA45F2E09D36A16F548AF172566E2E88C55142441594EEA3C538969B4E4E5A0B47F30636497730BC7137E5A6EC210875FCE661163F77D5D99197840A6CD4024D74C014EDFD39FB83F25E14A104B00BE9FEEE8FE16E0BB208B36166096AB1063A659659C0F035FDC9DA288D1A118770810AA89A751D9E3A8605009EDB80D625F9DC059E27594C76395BEAF9A5A1D8830FD1FFDF3011F985CF3348F5CA6D64142C7A584FD34B0849C595641A630E793DF5B38CCA58AD9C4245796E0E87195C54B165B6BF8C9BDC13E90D6FB82EDC676EC98B11B584148A0019708379919791D41A27BF371E3207D814633C284CAF0203010001A3633061300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0301F0603551D23041830168014AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0300D06092A864886F70D01010C050003820201008325EDE8D1FD9552CD9EC004A09169E65CD084DEDCADA24FE84778D66598A95BA83C877C028AD16EB71673E65FC05498D574BEC1CDE21191AD23183DDDE1724496B4955EC07B8E99781643135657B3A2B33BB577DC4072ACA3EB9B353EB10821A1E7C443377932BEB5E79C2C4CBC4329998E30D3AC21E0E31DFAD80733765400222AB94D202E7068DAE553FC835CD39DF2FF440C4466F2D2E3BD46001A6D02BA255D8DA13151DD54461C4DDB9996EF1A1C045CA615EF78E079FE5DDB3EAA4C55FD9A15A96FE1A6FBDF7030E9C3EE4246EDC2930589FA7D637B3FD071817C00E898AE0E7834C325FBAF0A9F206BDD3B138F128CE2411A487A73A07769C7B65C7F82C81EFE581B282BA86CAD5E6DC005D27BB7EB80FE2537FE029B68AC425DC3EEF5CCDCF05075D236699CE67B04DF6E0669B6DE0A09485987EB7B14607A64AA6943EF91C74CEC18DD6CEF532D8C99E15EF2723ECF54C8BD67ECA40F4C45FFD3B93023074C8F10BF8696D9995AB499571CA4CCBB158953BA2C050FE4C49E19B11834D54C9DBAEDF71FAF24950478A803BBEE81E5DA5F7C8B4AA1907425A7B33E4BC82C56BDC7C8EF38E25C92F079F79C84BA742D6101207E7ED1F24F07595F8B2D4352EB460C94E1F566477977D5545B1FAD2437CB455A4EA04448C8D8B099C5158409F6D64949C065B8E61A716EA0A8F182E8453E6CD602D70A6783055AC9A410 | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8094640EB5A7A1CA119C1FDDD59F810263A7FBD1 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000007E00000001000000080000000080C82B6886D7011D0000000100000010000000521F5C98970D19A8E515EF6EEB6D48EF7F0000000100000016000000301406082B0601050507030306082B060105050703090B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D00200052003600000053000000010000007E000000307C301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301F06092B06010401A032010230123010060A2B0601040182373C0101030200C0301B060567810C010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00F0000000100000030000000EA09C51D4C3A334CE4ACD2BC08C6A9BE352E334F45C4FCCFCAB63EDB9F82DC87D4BD2ED2FADAE11163FB954809984FF10300000001000000140000008094640EB5A7A1CA119C1FDDD59F810263A7FBD1190000000100000010000000CB9DD0FCEAAA492F75CE292C21BBFBDD090000000100000056000000305406082B0601050507030206082B06010505070303060A2B0601040182370A030C060A2B0601040182370A030406082B0601050507030406082B0601050507030906082B0601050507030106082B060105050703086200000001000000200000002CABEAFE37D06CA22ABA7391C0033D25982952C453647349763A3AB5AD6CCF69140000000100000014000000AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A07A000000010000000C000000300A06082B060105050703090400000001000000100000004FDD07E4D42264391E0C3742EAD1C6AE200000000100000087050000308205833082036BA003020102020E45E6BB038333C3856548E6FF4551300D06092A864886F70D01010C0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3134313231303030303030305A170D3334313231303030303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820222300D06092A864886F70D01010105000382020F003082020A02820201009507E873CA66F9EC14CA7B3CF70D08F1B4450B2C82B448C6EB5B3CAE83B841923314A46F7FE92ACCC6B0886BC5B689D1C6B2FF14CE511421EC4ADD1B5AC6D687EE4D3A1506ED64660B9280CA44DE73944EF3A7897F4F786308C812506D42662F4DB979284D521A8A1A80B719810E7EC48ABC644C211C4368D73D3C8AC5B266D5909AB73106C5BEE26D3206A61EF9B9EBAAA3B8BFBE826350D0F01889DFE40F79F5EAA21F2AD2702E7BE7BC93BB6D53E2487C8C100738FF66B277617EE0EA8C3CAAB4A4F6F3954A12076DFD8CB289CFD0A06177C85874B0D4233AF75D3ACAA2DB9D09DE5D442D90F181CD5792FA7EBC50046334DF6B9318BE6B36B239E4AC2436B7F0EFB61C135793B6DEB2F8E285B773A2B835AA45F2E09D36A16F548AF172566E2E88C55142441594EEA3C538969B4E4E5A0B47F30636497730BC7137E5A6EC210875FCE661163F77D5D99197840A6CD4024D74C014EDFD39FB83F25E14A104B00BE9FEEE8FE16E0BB208B36166096AB1063A659659C0F035FDC9DA288D1A118770810AA89A751D9E3A8605009EDB80D625F9DC059E27594C76395BEAF9A5A1D8830FD1FFDF3011F985CF3348F5CA6D64142C7A584FD34B0849C595641A630E793DF5B38CCA58AD9C4245796E0E87195C54B165B6BF8C9BDC13E90D6FB82EDC676EC98B11B584148A0019708379919791D41A27BF371E3207D814633C284CAF0203010001A3633061300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0301F0603551D23041830168014AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0300D06092A864886F70D01010C050003820201008325EDE8D1FD9552CD9EC004A09169E65CD084DEDCADA24FE84778D66598A95BA83C877C028AD16EB71673E65FC05498D574BEC1CDE21191AD23183DDDE1724496B4955EC07B8E99781643135657B3A2B33BB577DC4072ACA3EB9B353EB10821A1E7C443377932BEB5E79C2C4CBC4329998E30D3AC21E0E31DFAD80733765400222AB94D202E7068DAE553FC835CD39DF2FF440C4466F2D2E3BD46001A6D02BA255D8DA13151DD54461C4DDB9996EF1A1C045CA615EF78E079FE5DDB3EAA4C55FD9A15A96FE1A6FBDF7030E9C3EE4246EDC2930589FA7D637B3FD071817C00E898AE0E7834C325FBAF0A9F206BDD3B138F128CE2411A487A73A07769C7B65C7F82C81EFE581B282BA86CAD5E6DC005D27BB7EB80FE2537FE029B68AC425DC3EEF5CCDCF05075D236699CE67B04DF6E0669B6DE0A09485987EB7B14607A64AA6943EF91C74CEC18DD6CEF532D8C99E15EF2723ECF54C8BD67ECA40F4C45FFD3B93023074C8F10BF8696D9995AB499571CA4CCBB158953BA2C050FE4C49E19B11834D54C9DBAEDF71FAF24950478A803BBEE81E5DA5F7C8B4AA1907425A7B33E4BC82C56BDC7C8EF38E25C92F079F79C84BA742D6101207E7ED1F24F07595F8B2D4352EB460C94E1F566477977D5545B1FAD2437CB455A4EA04448C8D8B099C5158409F6D64949C065B8E61A716EA0A8F182E8453E6CD602D70A6783055AC9A410 | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | D69B561148F01C77C54578C10926DF5B856976AD |
Value: | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000C5DFB849CA051355EE2DBA1AC33EB0281400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC0B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D002000520033000000090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B1D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA9532000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800001D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA953620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD0F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200330000001400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC040000000100000010000000C5DFB849CA051355EE2DBA1AC33EB0282000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
Value: | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000E94FB54871208C00DF70F708AC47085B0F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C0300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B809000000010000000C000000300A06082B060105050703031D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD91400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B53000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C06200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF860B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B4200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B40B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000006200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF8653000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C01400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B1D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD909000000010000000C000000300A06082B060105050703030300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B80F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C040000000100000010000000E94FB54871208C00DF70F708AC47085B200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (6292) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
Executable files
61
Suspicious files
36
Text files
4
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5272 | Eraser 6.2.0.2994.exe | C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\Eraser (x64).msi | — | |
MD5:— | SHA256:— | |||
| 5272 | Eraser 6.2.0.2994.exe | C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\Eraser (x86).msi | — | |
MD5:— | SHA256:— | |||
| 3900 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3900 | msiexec.exe | C:\Windows\Installer\1c7362.msi | — | |
MD5:— | SHA256:— | |||
| 6292 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A1D627669EFC8CD4F21BCF387D97F9B5_05149AD367D7C4344CC6DD778FFC4FB9 | binary | |
MD5:DF13612181ECC57E387D4671501F7D99 | SHA256:E856862D79CF6A92DE3B646BCF6324E8A29060E8594F031B2219F2DF654C2148 | |||
| 6292 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A1D627669EFC8CD4F21BCF387D97F9B5_05149AD367D7C4344CC6DD778FFC4FB9 | der | |
MD5:6D6687319289844335E1EDFC214BB14F | SHA256:21B7BCA0E9D782CDE8F67ED44AEC1FB2119E50ED860627FAA714A42327FBD1F6 | |||
| 6292 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_6C354C532D063DF5607A63BA827F5164 | der | |
MD5:ADBF195FAEBEBF153306E81EB6E79AEC | SHA256:FFA301A188ACE8CA41E43AC5F0804BB67654B6B719E108C4923E1B654D9CC1BB | |||
| 3900 | msiexec.exe | C:\Program Files\Eraser\Eraser.Plugins.dll | executable | |
MD5:0FF1914AFF85E0B5A341F3AD276F1137 | SHA256:B3CC53A654D512C469D32F2FE3307149B12AE401ACD9175B574982D682DEBD6D | |||
| 3900 | msiexec.exe | C:\Program Files\Eraser\DragDropLib.dll | executable | |
MD5:D6DC4C8148AEE62874EC498AA7AACA0D | SHA256:1FEBAF644FBB1835DD38AEA056A3C11EB9722931A863CC94DB6630BD484EE5B8 | |||
| 3900 | msiexec.exe | C:\Program Files\Eraser\Eraser Documentation.pdf | ||
MD5:A6DA393C6C58348177AD173D8246E762 | SHA256:482D088F94A1456EF0A30A7A96B0929D821B82C6170E69F12CBAC52F26726557 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
72
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6292 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgOhtwj4VKsGchDZBEc%3D | unknown | — | — | whitelisted |
6292 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDBdskHYjyw2PrHr46Q%3D%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5428 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 95.100.146.35:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
1028 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4520 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3392 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2668 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6292 | msiexec.exe | 104.18.20.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |