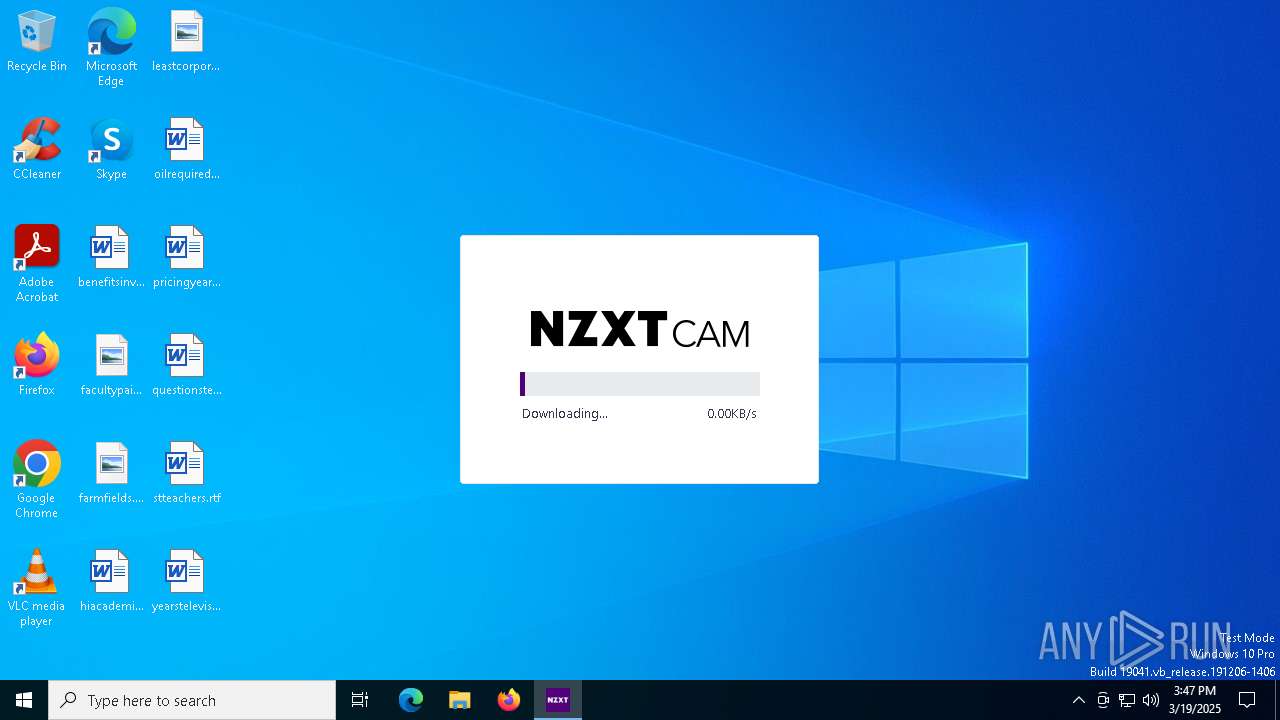
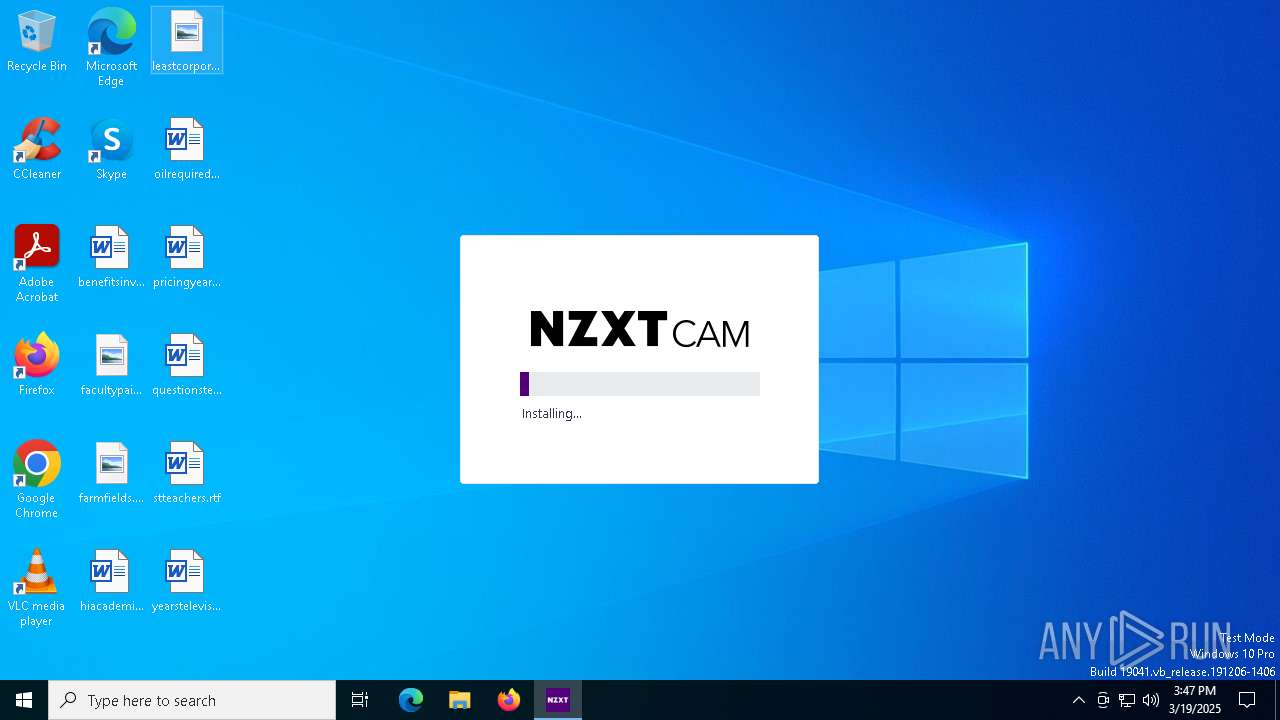
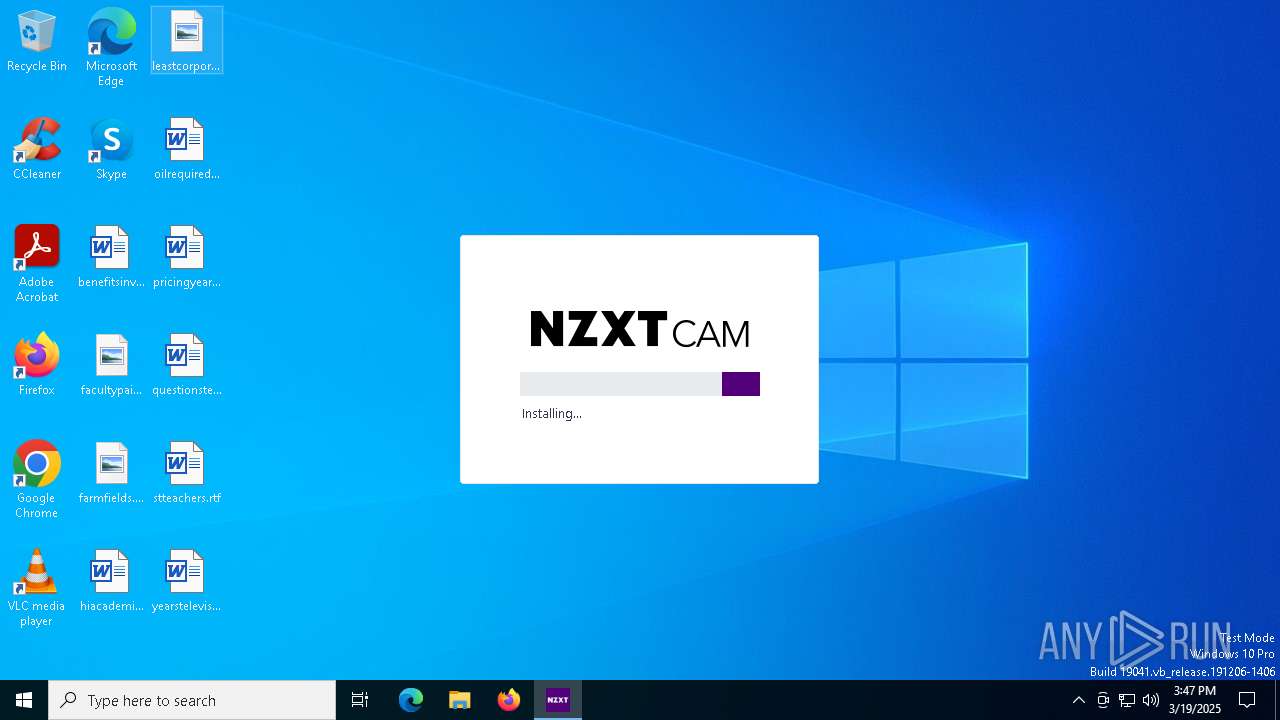
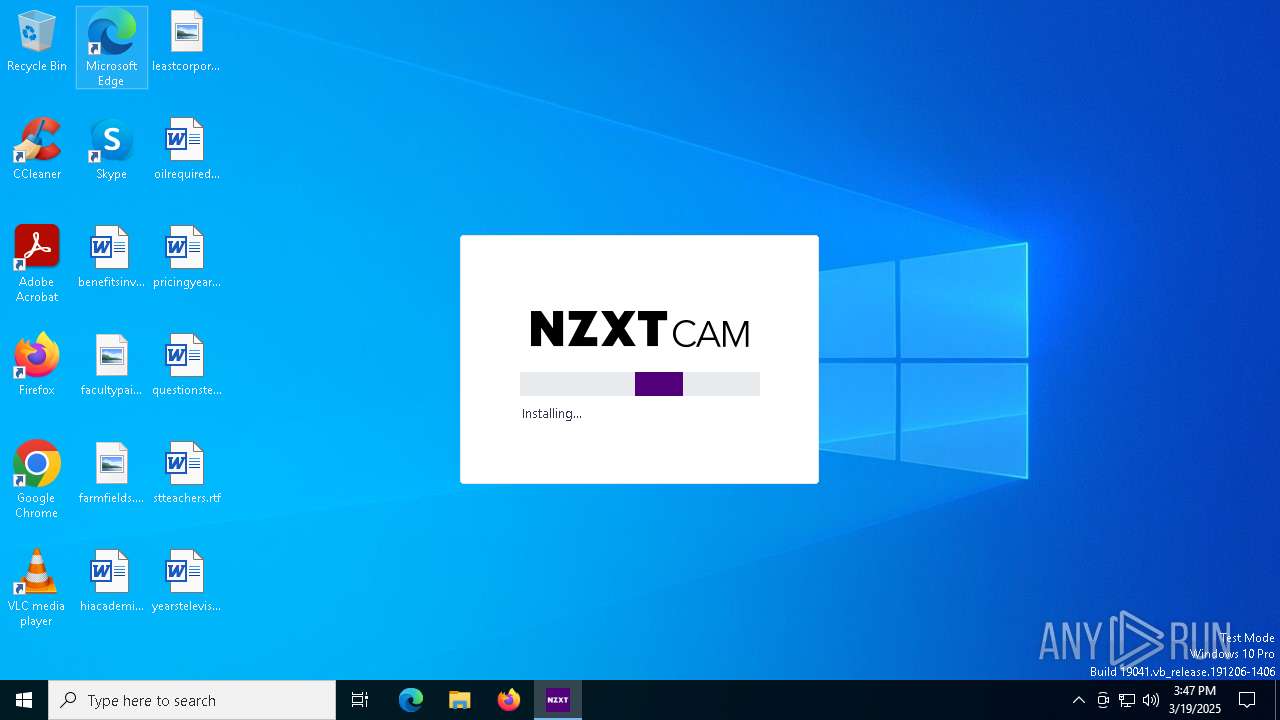
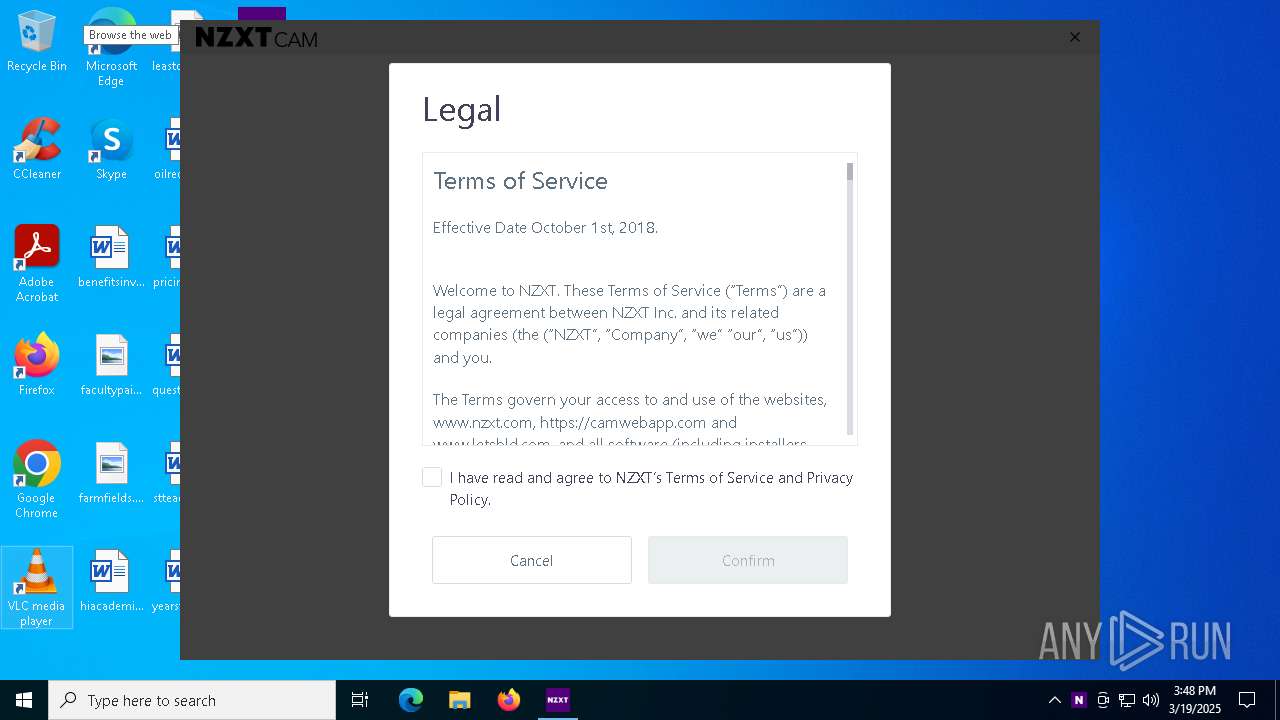
| File name: | NZXT-CAM-Setup.exe |
| Full analysis: | https://app.any.run/tasks/114a93d0-ddc8-41e3-a914-f3cf75375093 |
| Verdict: | Malicious activity |
| Threats: | Kraken is a trojan malware with infostealing capabilities that was first spotted in May of 2023. The malware can perform a wide range of malicious activities, including logging users’ keystrokes. The data then can be sent to the attacker using several protocols. The operators behind the Kraken stealer usually distribute it via phishing emails. |
| Analysis date: | March 19, 2025, 15:47:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 7BC1AB23AE2769AAFB891308034C41BA |
| SHA1: | 8795024B6BF5F9B9E3A2CFBEE9787EC47D38F4A9 |
| SHA256: | 47C83AC3471B06F61AA938F66D26A578FE6996910BB2ECFB825823A8D92CADB7 |
| SSDEEP: | 49152:Pyx8qOaB4rYjlTBw9BzojH1ts4d0pheM0u3iuNocow:Pyx8qOSVjltwvzorzs4dIhee3 |
MALICIOUS
Kraken Ransomware is detected
- fd57-68c0-2725-1d0d.exe (PID: 6272)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- fd57-68c0-2725-1d0d.exe (PID: 6272)
Process requests binary or script from the Internet
- NZXT-CAM-Setup.exe (PID: 1280)
Reads security settings of Internet Explorer
- NZXT-CAM-Setup.exe (PID: 1280)
Potential Corporate Privacy Violation
- NZXT-CAM-Setup.exe (PID: 1280)
Drops 7-zip archiver for unpacking
- fd57-68c0-2725-1d0d.exe (PID: 6272)
Executable content was dropped or overwritten
- fd57-68c0-2725-1d0d.exe (PID: 6272)
- cam_helper.exe (PID: 5512)
Drops a system driver (possible attempt to evade defenses)
- fd57-68c0-2725-1d0d.exe (PID: 6272)
- cam_helper.exe (PID: 5512)
Starts CMD.EXE for commands execution
- NZXT CAM.exe (PID: 2980)
- NZXT CAM.exe (PID: 4428)
Executes as Windows Service
- service.exe (PID: 2420)
- WmiApSrv.exe (PID: 7176)
Application launched itself
- NZXT CAM.exe (PID: 4428)
- cam_helper.exe (PID: 132)
Get information on the list of running processes
- cmd.exe (PID: 5212)
- NZXT CAM.exe (PID: 4428)
Process drops legitimate windows executable
- fd57-68c0-2725-1d0d.exe (PID: 6272)
The process checks if it is being run in the virtual environment
- cam_helper.exe (PID: 5512)
INFO
Checks proxy server information
- NZXT-CAM-Setup.exe (PID: 1280)
Reads the computer name
- NZXT-CAM-Setup.exe (PID: 1280)
- NZXT CAM.exe (PID: 4428)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6652)
- NZXT CAM.exe (PID: 4428)
- NZXT CAM.exe (PID: 2980)
- cam_helper.exe (PID: 132)
The sample compiled with english language support
- NZXT-CAM-Setup.exe (PID: 1280)
- fd57-68c0-2725-1d0d.exe (PID: 6272)
- cam_helper.exe (PID: 5512)
Checks supported languages
- NZXT-CAM-Setup.exe (PID: 1280)
- NZXT CAM.exe (PID: 6640)
- NZXT CAM.exe (PID: 4428)
- cam_helper.exe (PID: 132)
Reads the machine GUID from the registry
- NZXT-CAM-Setup.exe (PID: 1280)
Create files in a temporary directory
- NZXT-CAM-Setup.exe (PID: 1280)
- fd57-68c0-2725-1d0d.exe (PID: 6272)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5436)
- BackgroundTransferHost.exe (PID: 6652)
The sample compiled with arabic language support
- fd57-68c0-2725-1d0d.exe (PID: 6272)
Creates files in the program directory
- fd57-68c0-2725-1d0d.exe (PID: 6272)
Reads the software policy settings
- slui.exe (PID: 5380)
- service.exe (PID: 2420)
The sample compiled with french language support
- fd57-68c0-2725-1d0d.exe (PID: 6272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:03:04 17:18:28+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 1025024 |
| InitializedDataSize: | 470528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa1960 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
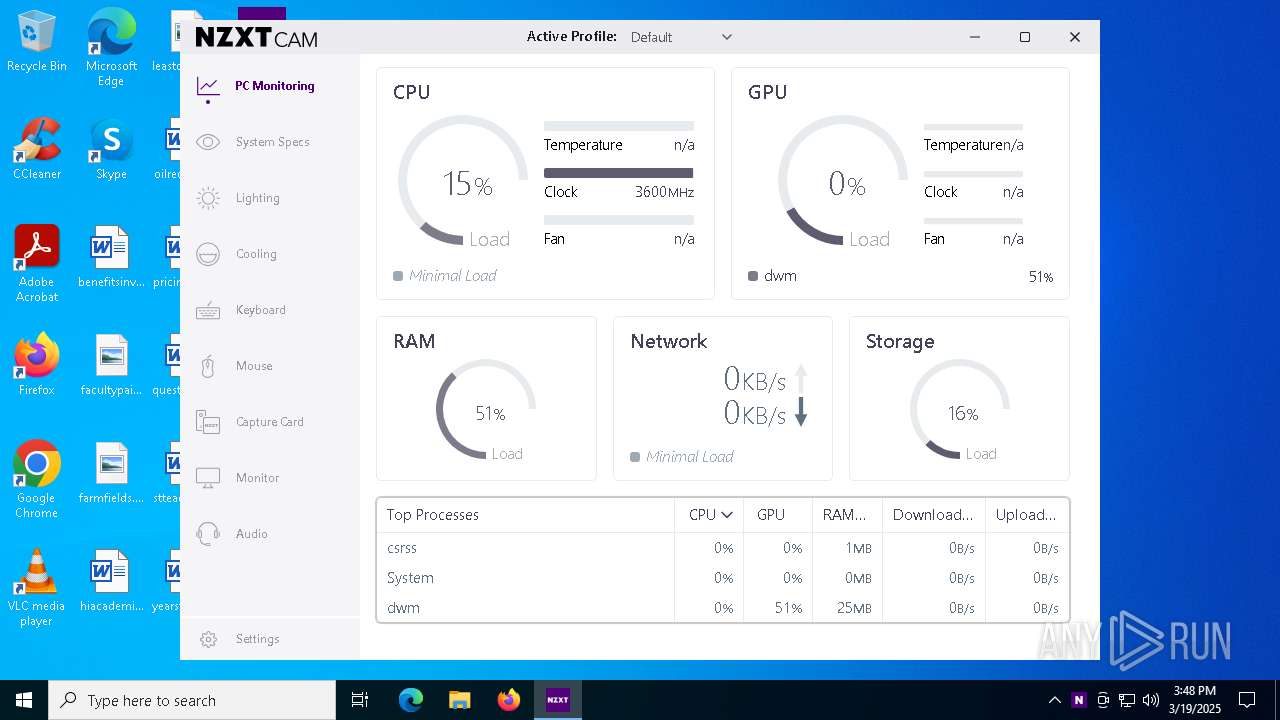
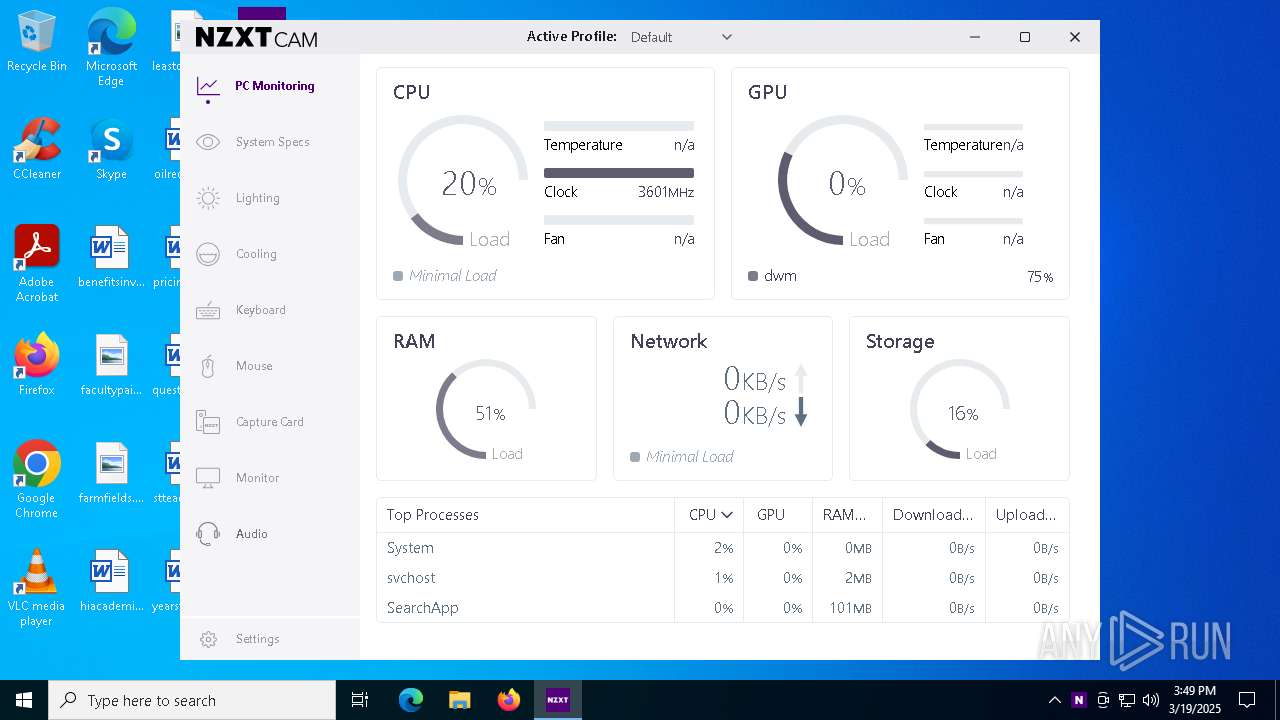
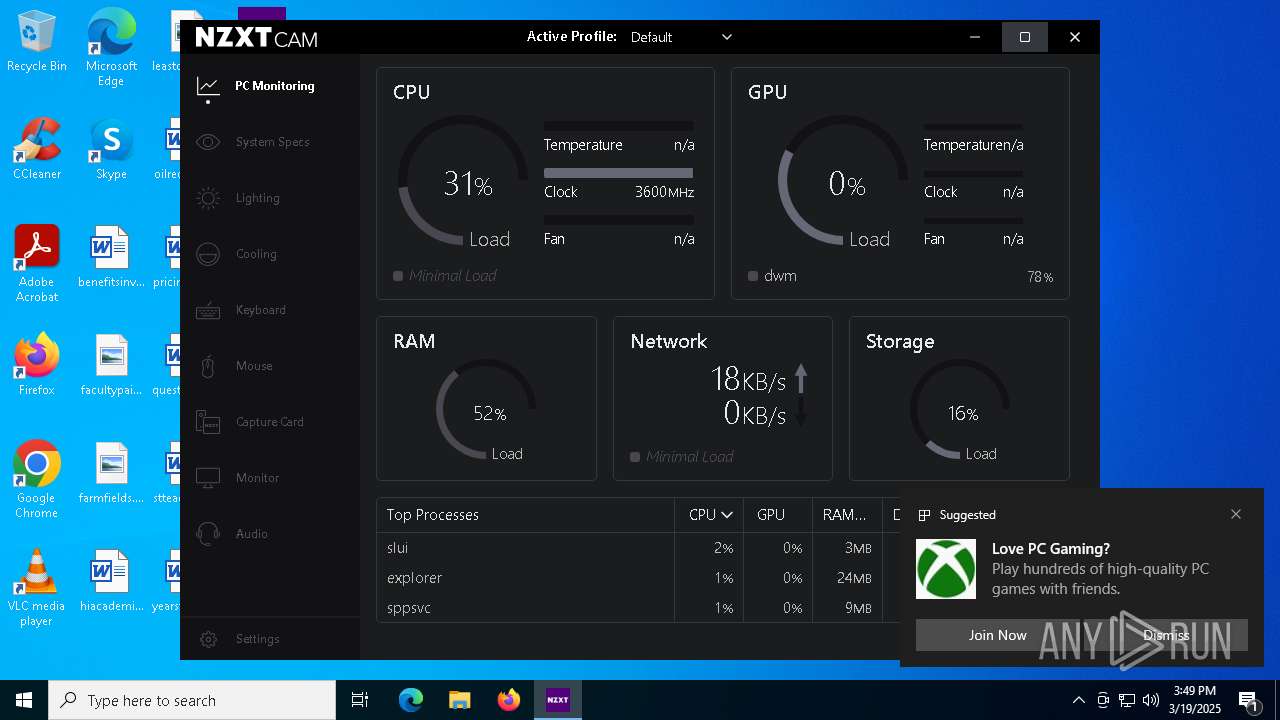
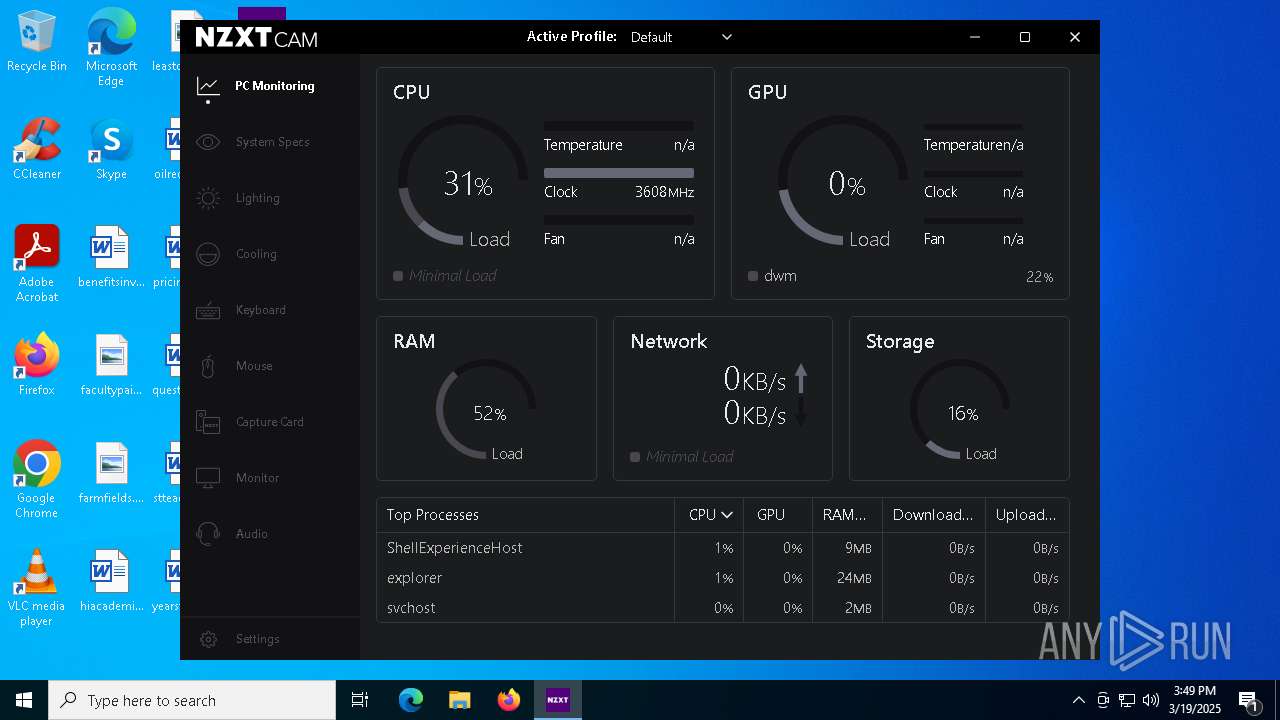
Total processes
189
Monitored processes
46
Malicious processes
3
Suspicious processes
2
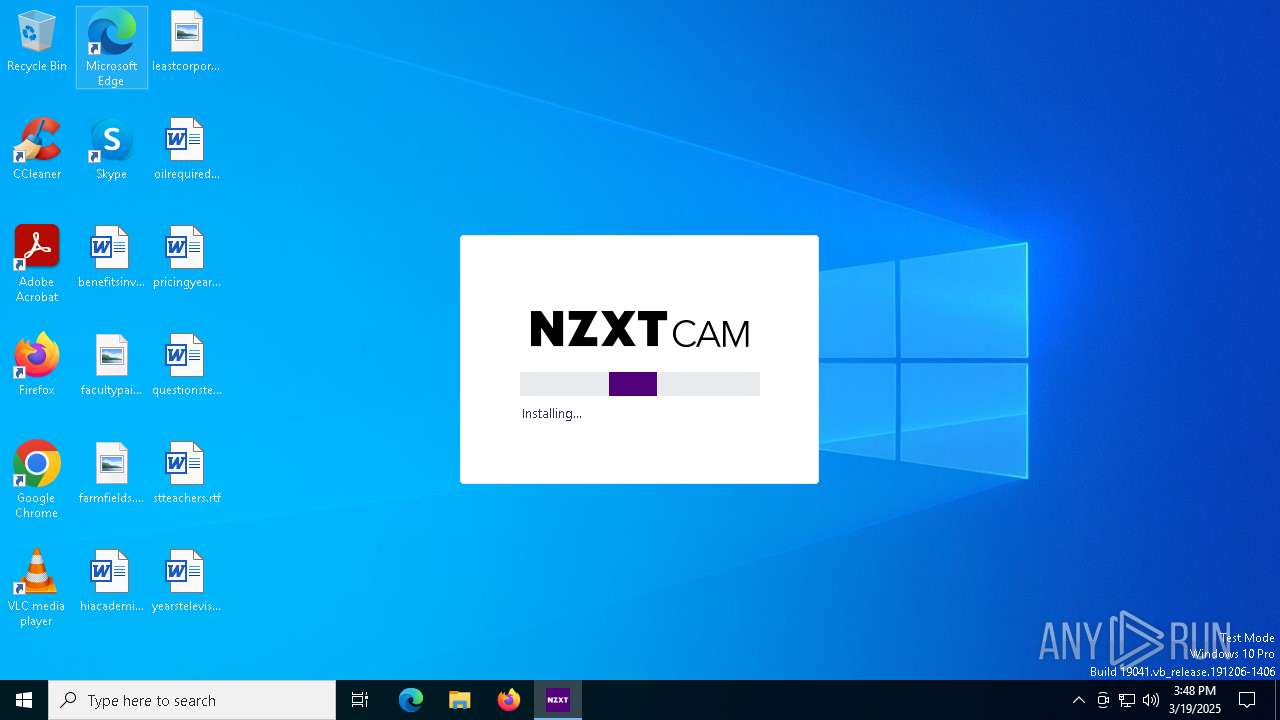
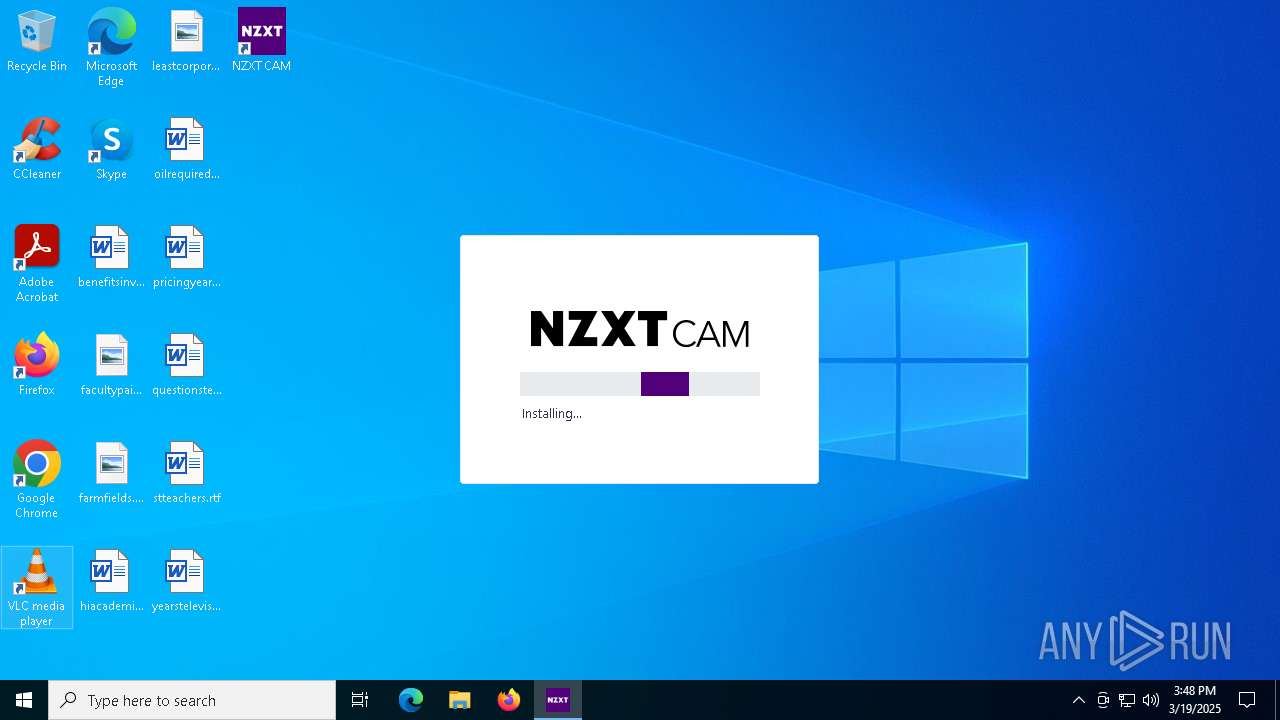
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "--elevation-server" "51cebafd-7df5-41d5-82c4-5f8ee955c555" "--run-id" "6812f21e9a3a41518675cf9f254ba4ac" "--app-version" "NZXT CAM@4.74.0" "--environment" "production" "--log-directory" "C:\Users\admin\AppData\Roaming\NZXT CAM\logs" "--log-level" "INFO" "--app-instance-id" "bb926e54-e3ca-40fd-ae90-2764341e7792" | C:\Program Files\NZXT CAM\resources\app.asar.unpacked\node_modules\@nzxt\cam-core\dist\cam_helper.exe | — | NZXT CAM.exe | |||||||||||
User: admin Integrity Level: HIGH Description: cam_helper Version: 71.0.1 Modules
| |||||||||||||||
| 236 | C:\WINDOWS\System32\REG.exe QUERY HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography /v MachineGuid | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\system32\cmd.exe /d /s /c "%windir%\System32\REG.exe QUERY HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography /v MachineGuid" | C:\Windows\System32\cmd.exe | — | NZXT CAM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | C:\WINDOWS\system32\cmd.exe /d /s /c "%windir%\System32\REG.exe QUERY HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography /v MachineGuid" | C:\Windows\System32\cmd.exe | — | NZXT CAM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\Users\admin\AppData\Local\Temp\NZXT-CAM-Setup.exe" | C:\Users\admin\AppData\Local\Temp\NZXT-CAM-Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cam_helper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2104 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\NZXT CAM\NZXT CAM.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\NZXT CAM" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --app-user-model-id=NZXT.CAM --app-path="C:\Program Files\NZXT CAM\resources\app.asar" --no-sandbox --no-zygote --js-flags=--expose-gc --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=2552,i,12059524499101793300,254110490673518798,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2548 /prefetch:1 | C:\Program Files\NZXT CAM\NZXT CAM.exe | — | NZXT CAM.exe | |||||||||||
User: admin Company: NZXT, Inc. Integrity Level: HIGH Description: NZXT CAM Exit code: 0 Version: 4.74.0.6 Modules
| |||||||||||||||
Total events
15 050
Read events
14 976
Write events
43
Delete events
31
Modification events
| (PID) Process: | (5436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6652) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6652) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6652) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7084) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7084) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7084) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6824) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
76
Suspicious files
746
Text files
276
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6652 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\af64f818-76f1-4800-9f6f-2e6d7e6d848f.down_data | — | |
MD5:— | SHA256:— | |||
| 1280 | NZXT-CAM-Setup.exe | C:\Users\admin\AppData\Local\Temp\fd57-68c0-2725-1d0d.exe | — | |
MD5:— | SHA256:— | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\app-64.7z | — | |
MD5:— | SHA256:— | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\7z-out\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\7z-out\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\7z-out\locales\ar.pak | binary | |
MD5:6E2D0C439BAC4243B8A544777F47472F | SHA256:4A9404C8DBA056A7F44FDBA8BCCB4C34508D4FE77DEE84DE327DB50DCA511A5E | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\nsProcess.dll | executable | |
MD5:F0438A894F3A7E01A4AAE8D1B5DD0289 | SHA256:30C6C3DD3CC7FCEA6E6081CE821ADC7B2888542DAE30BF00E881C0A105EB4D11 | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\7z-out\chrome_100_percent.pak | binary | |
MD5:3C72D78266A90ED10DC0B0DA7FDC6790 | SHA256:14A6A393C60F62DF9BC1036E98346CD557E0AE73E8C7552D163FA64DA77804D7 | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\7z-out\LICENSE.electron.txt | text | |
MD5:4D42118D35941E0F664DDDBD83F633C5 | SHA256:5154E165BD6C2CC0CFBCD8916498C7ABAB0497923BAFCD5CB07673FE8480087D | |||
| 6272 | fd57-68c0-2725-1d0d.exe | C:\Users\admin\AppData\Local\Temp\nss47D5.tmp\7z-out\locales\af.pak | binary | |
MD5:08D18B6EB81B4941C6826390DBF377C5 | SHA256:B5F0DB313F2036793748CCE591917AFE5658879AF29E5F68A4BA75CB4F2259BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
37
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1280 | NZXT-CAM-Setup.exe | GET | 200 | 138.199.37.232:80 | http://nzxt-app.nzxt.com/NZXT%20CAM%20Setup%204.74.0.exe | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1280 | NZXT-CAM-Setup.exe | GET | 200 | 138.199.37.232:80 | http://nzxt-app.nzxt.com/latest.yml | unknown | — | — | whitelisted |
5056 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6652 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2420 | service.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2420 | service.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
2420 | service.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAdKU8tyMQM2IeTgRbWLxck%3D | unknown | — | — | whitelisted |
4428 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1280 | NZXT-CAM-Setup.exe | 138.199.37.232:80 | nzxt-app.nzxt.com | Datacamp Limited | DE | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5056 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nzxt-app.nzxt.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1280 | NZXT-CAM-Setup.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |