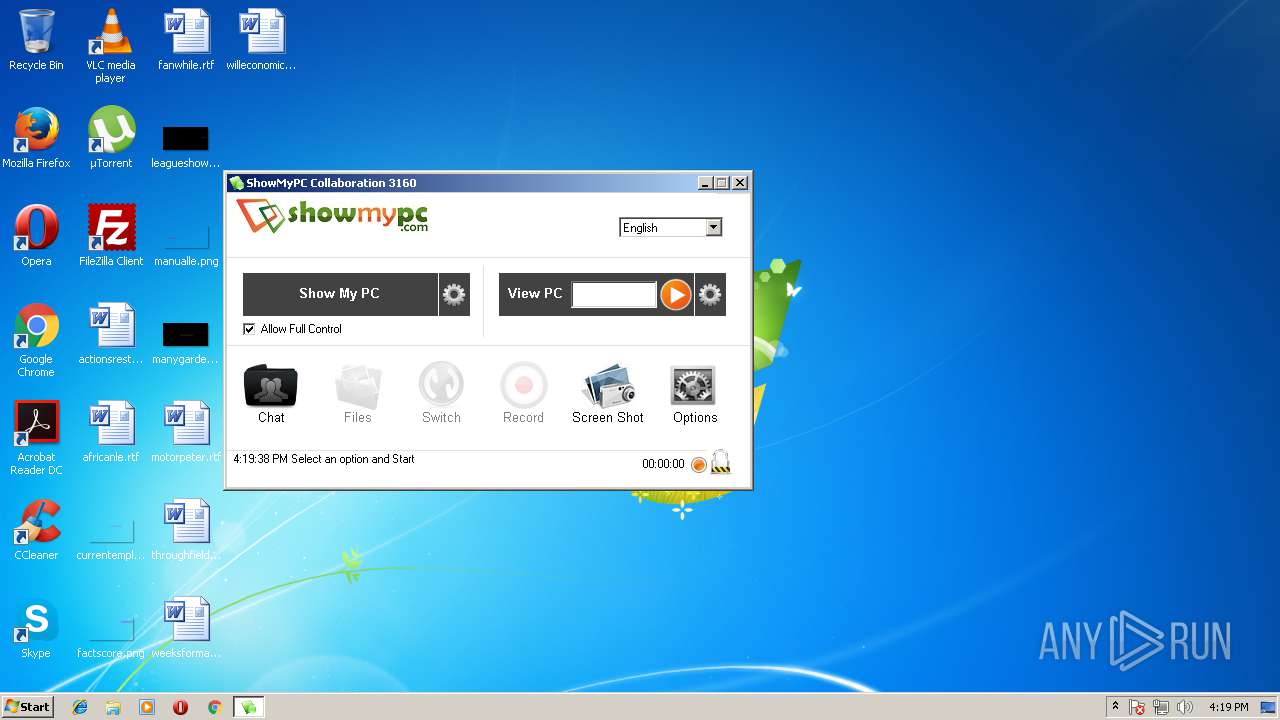
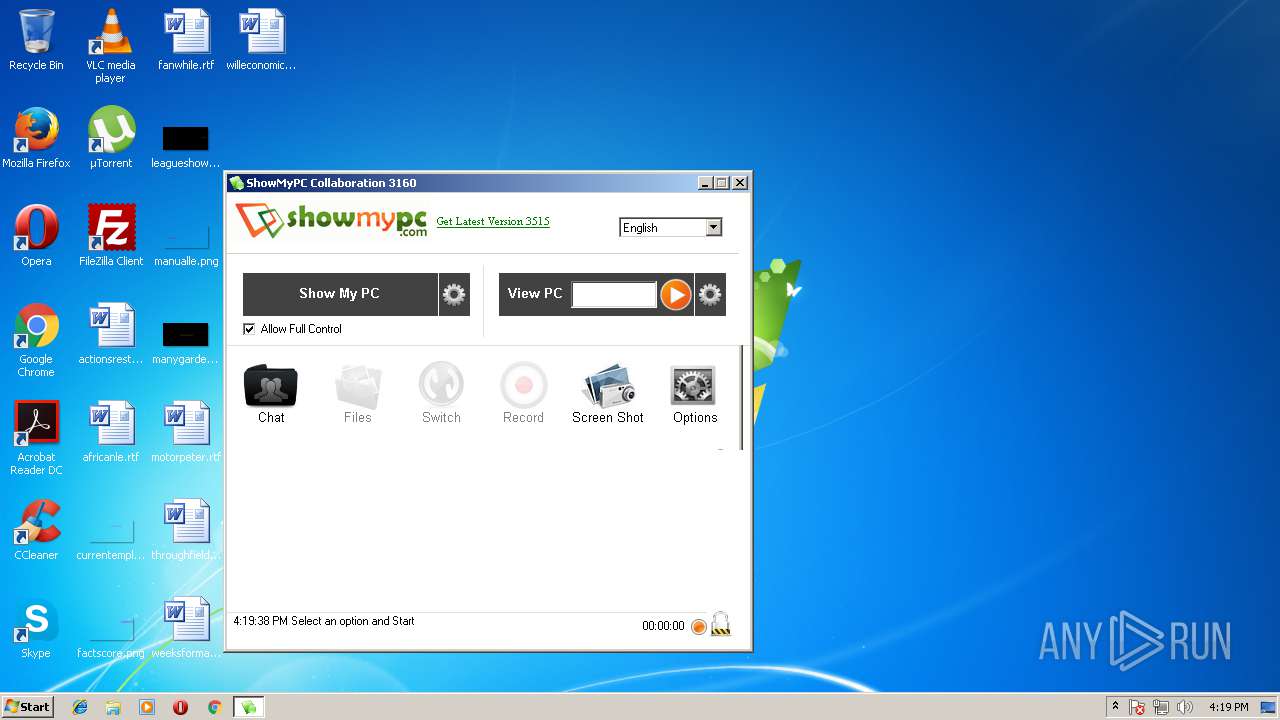
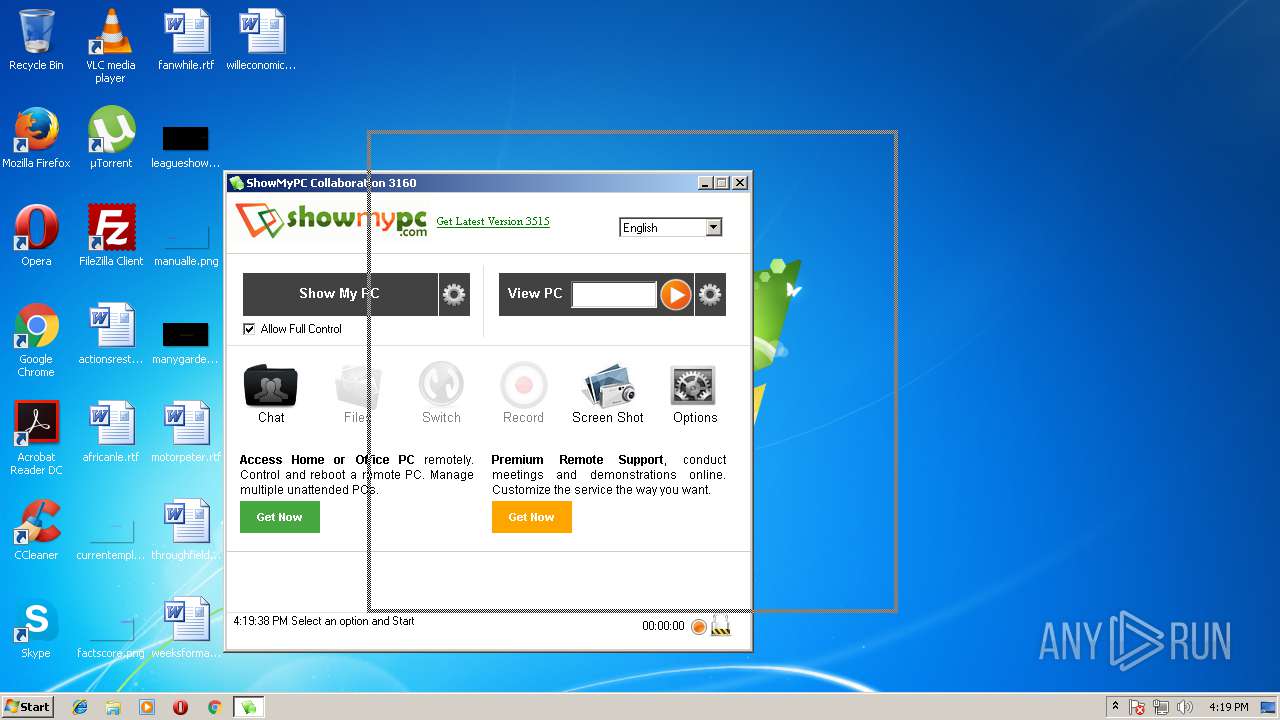
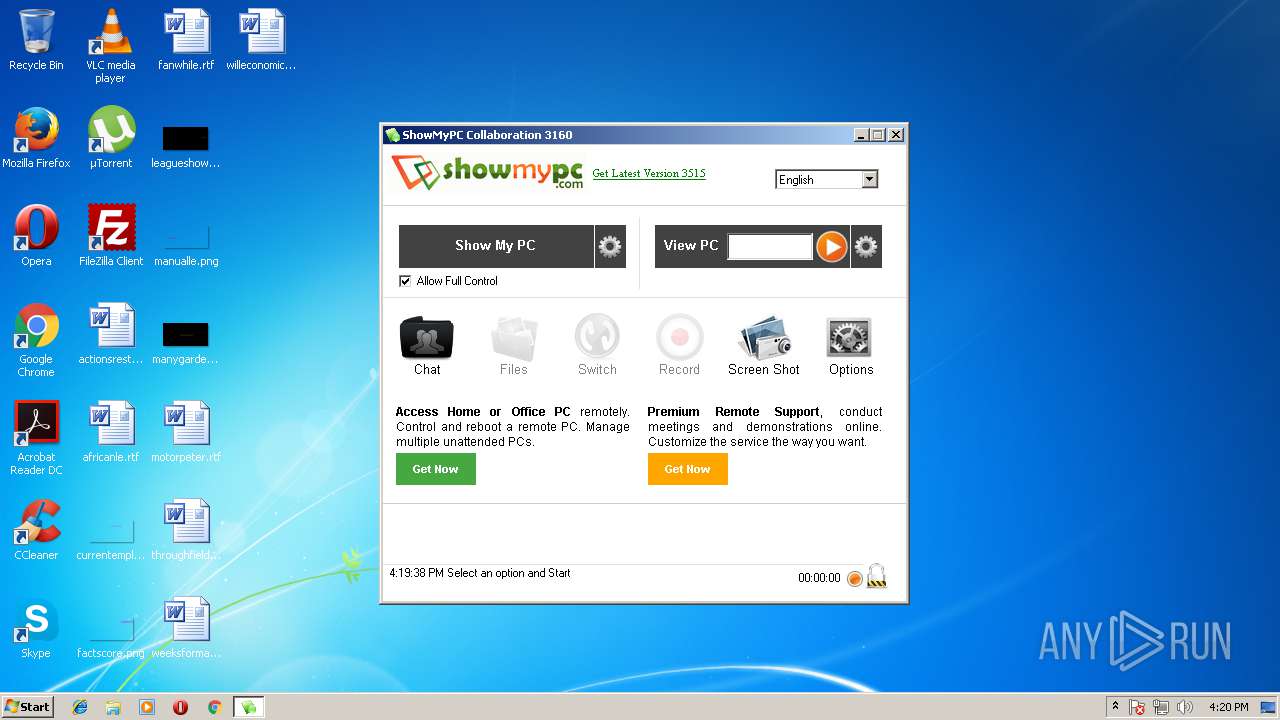
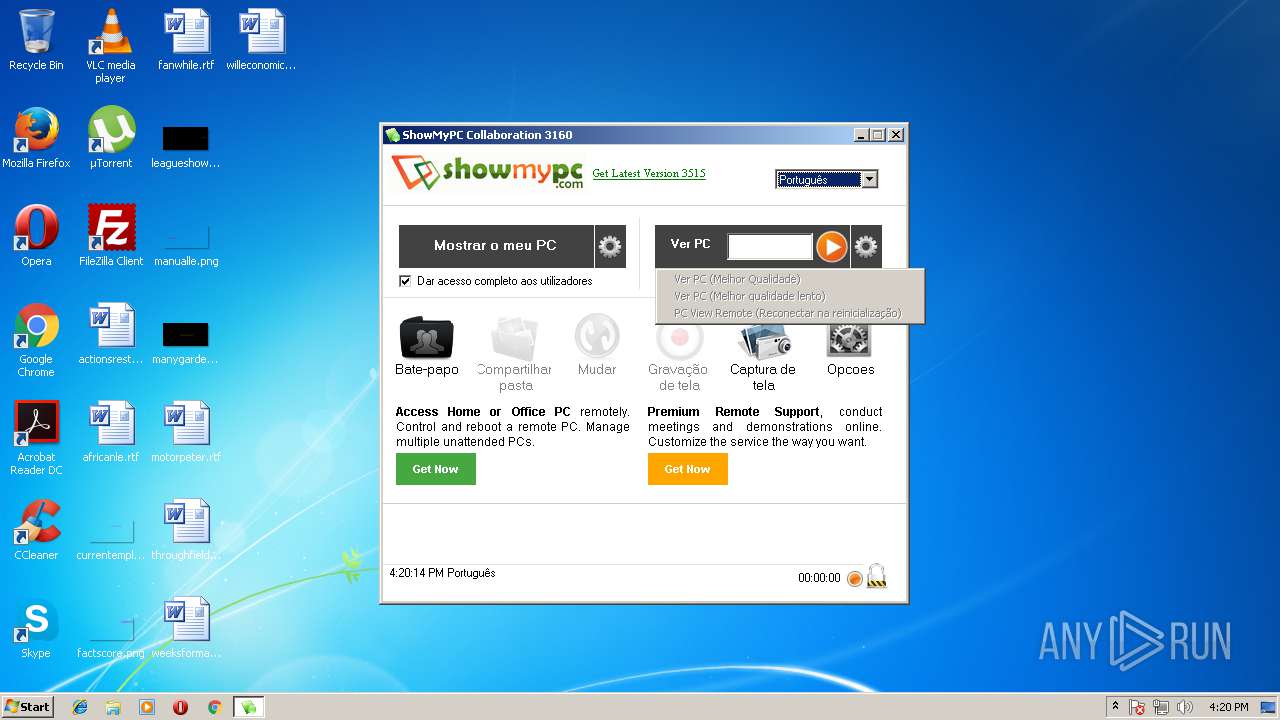
| File name: | ShowMyPC3160.exe |
| Full analysis: | https://app.any.run/tasks/c5110c45-847e-4da3-80fe-1fc3074214b6 |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2018, 15:19:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AD1BC8037BD26CF6C4B63EF53561C938 |
| SHA1: | EBFE0E470456C9BE61ED63CFF39A270B0E5AC673 |
| SHA256: | 47C496EF71B8B680DB070709980AF073C7854072051A8977E541331240A06839 |
| SSDEEP: | 49152:UelPRriykVyEPaPwA40qlg/mMLVd5ZeJoR/w:UePYhsn4Ll3KeWR/w |
MALICIOUS
Application was dropped or rewritten from another process
- SMPCSetup.exe (PID: 2984)
Changes settings of System certificates
- SMPCSetup.exe (PID: 2984)
Starts NET.EXE for service management
- SMPCSetup.exe (PID: 2984)
Loads dropped or rewritten executable
- SMPCSetup.exe (PID: 2984)
- ShowMyPC3160.exe (PID: 3152)
SUSPICIOUS
Executable content was dropped or overwritten
- ShowMyPC3160.exe (PID: 3152)
Creates files in the user directory
- SMPCSetup.exe (PID: 2984)
Reads Internet Cache Settings
- SMPCSetup.exe (PID: 2984)
Check for Java to be installed
- iexplore.exe (PID: 2680)
Adds / modifies Windows certificates
- SMPCSetup.exe (PID: 2984)
Creates COM task schedule object
- SMPCSetup.exe (PID: 2984)
Creates files in the program directory
- SMPCSetup.exe (PID: 2984)
Reads internet explorer settings
- SMPCSetup.exe (PID: 2984)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2680)
Dropped object may contain URL's
- SMPCSetup.exe (PID: 2984)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3200)
- ShowMyPC3160.exe (PID: 3152)
Application launched itself
- iexplore.exe (PID: 2680)
Reads Internet Cache Settings
- iexplore.exe (PID: 3200)
Reads internet explorer settings
- iexplore.exe (PID: 3200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x0002A1C8 | 0x0002A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16287 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.78198 | 67624 | UNKNOWN | English - United States | RT_ICON |
2 | 5.21478 | 38056 | UNKNOWN | English - United States | RT_ICON |
3 | 5.27453 | 21640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.27015 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 5.41739 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.73927 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 5.45835 | 3752 | UNKNOWN | English - United States | RT_ICON |
8 | 5.93162 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 5.88793 | 2216 | UNKNOWN | English - United States | RT_ICON |
10 | 5.88445 | 1736 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
50
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | C:\Windows\system32\net1 stop winvnc4 | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 916 | C:\Windows\system32\net1 stop tvnserver | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1488 | net stop tvnserver | C:\Windows\system32\net.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\Temp\ShowMyPC3160.exe" | C:\Users\admin\AppData\Local\Temp\ShowMyPC3160.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2648 | net stop uvnc_service | C:\Windows\system32\net.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
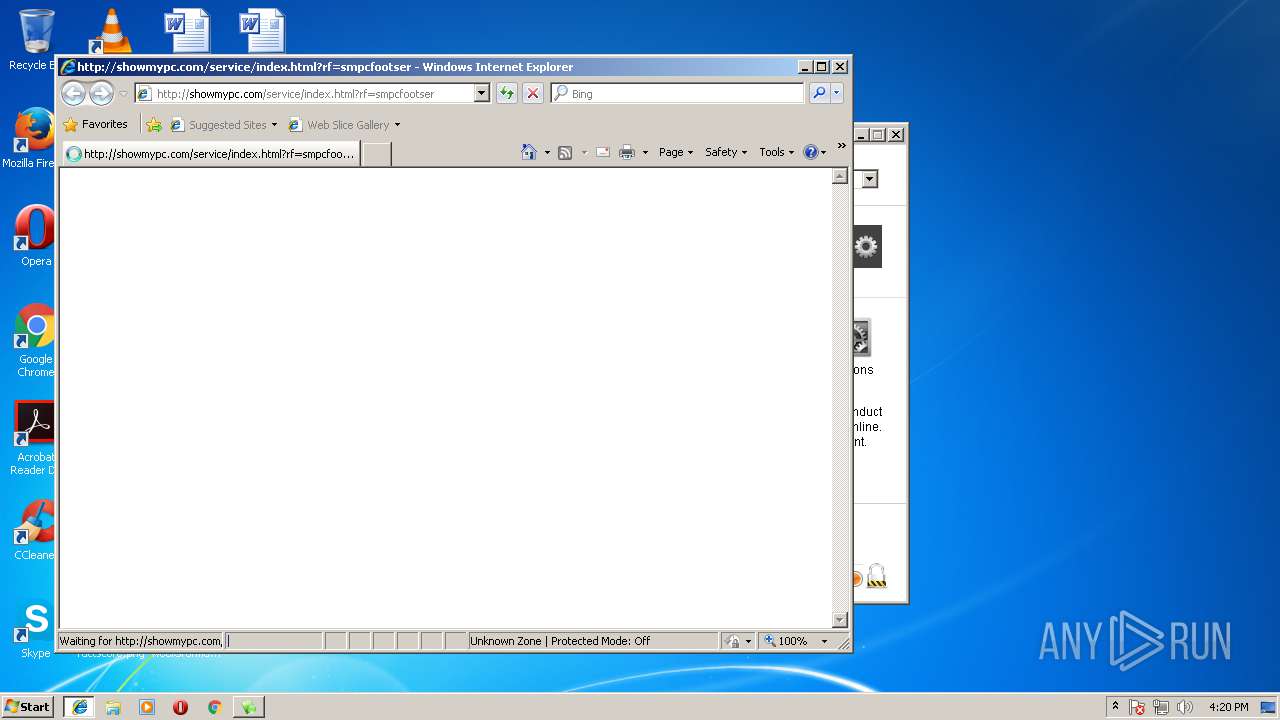
| 2680 | "C:\Program Files\Internet Explorer\iexplore.exe" -startmediumtab -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\SMPCSetup.exe" | C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\SMPCSetup.exe | ShowMyPC3160.exe | ||||||||||||
User: admin Company: ShowMyPC Integrity Level: HIGH Exit code: 0 Version: 6.01.2033 Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\ShowMyPC3160.exe" | C:\Users\admin\AppData\Local\Temp\ShowMyPC3160.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2680 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3244 | C:\Windows\system32\net1 stop uvnc_service | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 049
Read events
778
Write events
270
Delete events
1
Modification events
| (PID) Process: | (3152) ShowMyPC3160.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3152) ShowMyPC3160.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\tvnserver |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\SMPCHelper |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SMPCSetup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SMPCSetup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SMPCSetup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2984) SMPCSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SMPCSetup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
15
Suspicious files
2
Text files
51
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\smpcview.exe | executable | |
MD5:— | SHA256:— | |||
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\settings.ini | text | |
MD5:— | SHA256:— | |||
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\nsd908A.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | SMPCSetup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\dnserrordiagoff_webOC[1] | — | |
MD5:— | SHA256:— | |||
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\smpcview.exe.config | xml | |
MD5:6F5F9D82CF78ECC5FAFD9B68D5150328 | SHA256:800E9DD5D86CD73632E54373D2CCB3AC57587B0359186CDB3CC69B2C59960EE4 | |||
| 2984 | SMPCSetup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\ErrorPageTemplate[1] | — | |
MD5:— | SHA256:— | |||
| 2984 | SMPCSetup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\OP5DQHUV\errorPageStrings[1] | — | |
MD5:— | SHA256:— | |||
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\nsd908B.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\mm2.res | text | |
MD5:F5F3EC013C648439DD3A5E3F3FD518B9 | SHA256:E52B378BB5CFB59A9936161F340456238A98965C07DFD2F5F801A95D92441379 | |||
| 3152 | ShowMyPC3160.exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\smpc3160\smwg.exe | executable | |
MD5:491E99207BBA55D1BBB03346B0AE3A4E | SHA256:F95B86E4BC71471C0758118FC3311FD9F35DA15905ECD84EAB97247FAC670DEC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | SMPCSetup.exe | GET | 200 | 64.22.103.52:80 | http://download3.showmypc.com/app/about-us.html?lang=CHN&version=3160&seq=7/9/20184:19:38%20PM | US | html | 3.54 Kb | malicious |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.datepicker.css | US | text | 3.90 Kb | shared |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.theme.css | US | text | 17.5 Kb | shared |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/images/logo-showmypc-210-50.gif | US | image | 3.84 Kb | shared |
2984 | SMPCSetup.exe | GET | 200 | 216.58.215.238:80 | http://www.google-analytics.com/r/__utm.gif?utmwv=5.7.2&utms=1&utmn=418579489&utmhn=download3.showmypc.com&utmcs=utf-8&utmsr=1280x720&utmvp=526x60&utmsc=32-bit&utmul=en-us&utmje=1&utmfl=27.0%20r0&utmhid=1933610130&utmr=-&utmp=%2Fapp%2Fappheader.html%3Fversion%3D3160%26lang%3DCHN&utmht=1531149579838&utmac=UA-3896280-1&utmcc=__utma%3D172476214.1009854060.1531149580.1531149580.1531149580.1%3B%2B__utmz%3D172476214.1531149580.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B&utmjid=1214445996&utmredir=1&utmu=DAAAAAAAAAAAAAAAAAAAAAAE~ | US | image | 35 b | whitelisted |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.resizable.css | US | text | 1005 b | shared |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.core.css | US | text | 1.35 Kb | shared |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.dialog.css | US | text | 1.15 Kb | shared |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.slider.css | US | text | 947 b | shared |
2984 | SMPCSetup.exe | GET | 200 | 52.216.18.179:80 | http://s3.showmypc.com/js/themes/base/ui.accordion.css | US | text | 739 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | SMPCSetup.exe | 52.216.18.179:80 | s3.showmypc.com | Amazon.com, Inc. | US | unknown |
2984 | SMPCSetup.exe | 172.217.168.34:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2984 | SMPCSetup.exe | 216.58.210.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2680 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2984 | SMPCSetup.exe | 172.217.168.34:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3200 | iexplore.exe | 173.255.253.123:80 | showmypc.com | Linode, LLC | US | unknown |
2984 | SMPCSetup.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2984 | SMPCSetup.exe | 64.22.103.52:80 | download3.showmypc.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download3.showmypc.com |
| malicious |
pagead2.googlesyndication.com |
| whitelisted |
s3.showmypc.com |
| shared |
www.google-analytics.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
www.bing.com |
| whitelisted |
showmypc.com |
| malicious |