| File name: | ppcTHpZsqIl.exe |
| Full analysis: | https://app.any.run/tasks/2bedf0c3-d373-4032-a646-a616bdb2c5ea |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 21:05:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 55DD371F5811A7CAECBA49C5B49B8551 |
| SHA1: | FF9D11710220E02A744C2DEDC15199AE66B416C8 |
| SHA256: | 47C3F56368C4CFBBA9D73681375D06BE2419E65E78A07C8B10D671207BCDE2F3 |
| SSDEEP: | 12288:Ajs3q8lakuxcK/vfe3NmTXajy/LCVwdOqTwh2ch19Ool9UXUXU:Vjo7/vyNmpQqTwh2y9Dl9UXUXU |
MALICIOUS
EMOTET was detected
- serialfunc.exe (PID: 3096)
- serialfunc.exe (PID: 2400)
Emotet process was detected
- ppcTHpZsqIl.exe (PID: 792)
- r46Aj5FxjtIspIgsK9.exe (PID: 2548)
Connects to CnC server
- serialfunc.exe (PID: 3096)
- serialfunc.exe (PID: 2400)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3096)
- serialfunc.exe (PID: 2400)
Stealing of credential data
- serialfunc.exe (PID: 2928)
SUSPICIOUS
Connects to server without host name
- serialfunc.exe (PID: 3096)
- serialfunc.exe (PID: 2400)
Starts itself from another location
- ppcTHpZsqIl.exe (PID: 792)
- serialfunc.exe (PID: 3096)
- r46Aj5FxjtIspIgsK9.exe (PID: 2548)
Executable content was dropped or overwritten
- ppcTHpZsqIl.exe (PID: 792)
- serialfunc.exe (PID: 3096)
- r46Aj5FxjtIspIgsK9.exe (PID: 2548)
Application launched itself
- serialfunc.exe (PID: 2168)
- serialfunc.exe (PID: 3096)
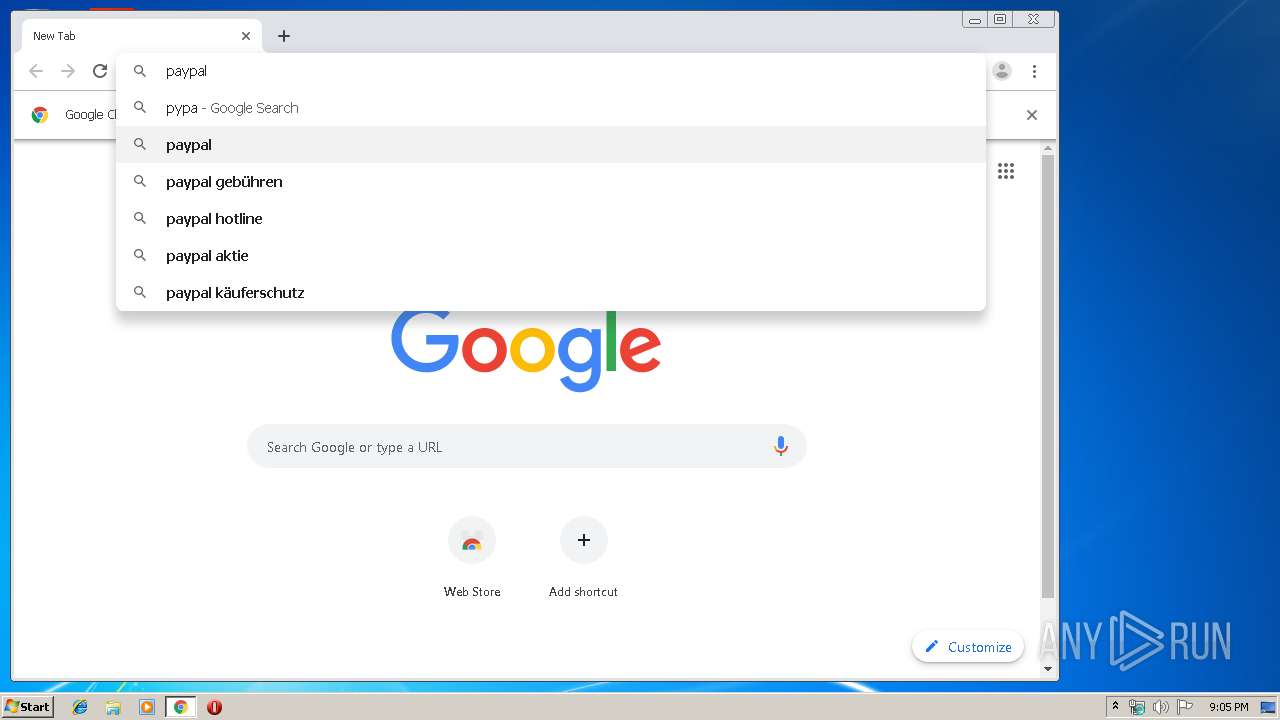
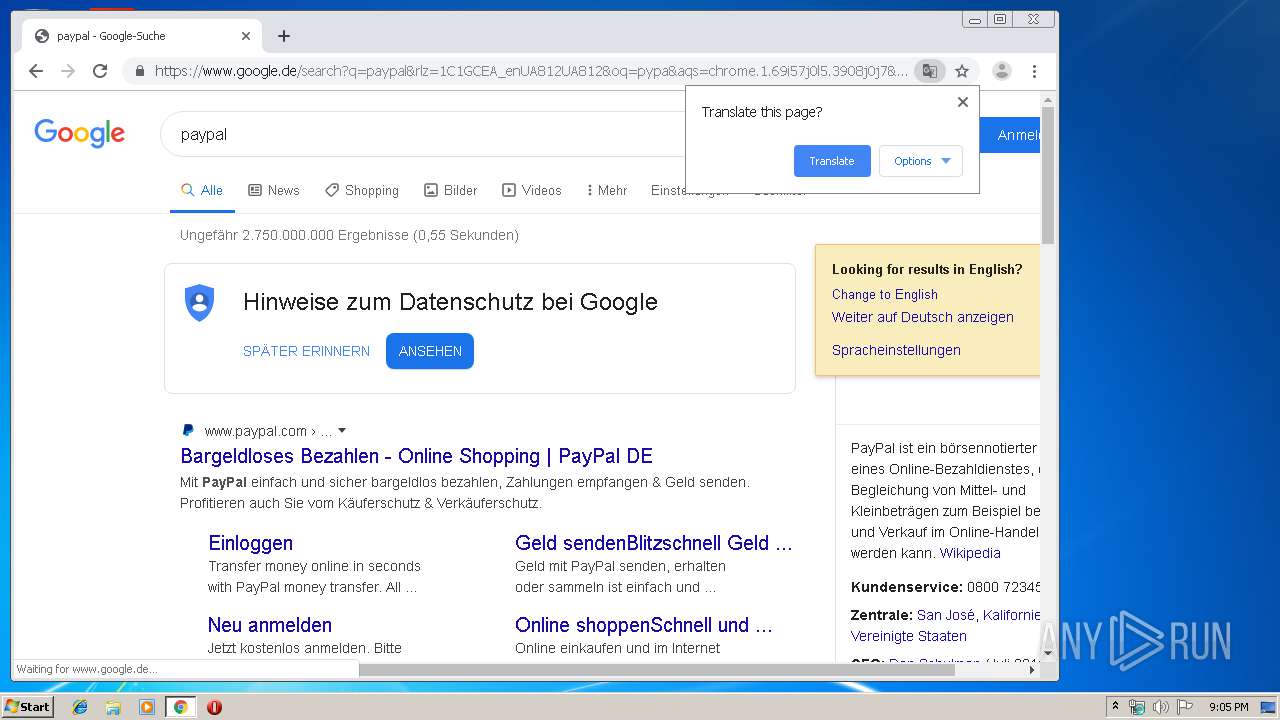
Modifies files in Chrome extension folder
- chrome.exe (PID: 3888)
Creates files in the program directory
- serialfunc.exe (PID: 3096)
Connects to SMTP port
- serialfunc.exe (PID: 2400)
Connects to unusual port
- serialfunc.exe (PID: 2400)
INFO
Application launched itself
- chrome.exe (PID: 3888)
Manual execution by user
- chrome.exe (PID: 3888)
Reads settings of System Certificates
- chrome.exe (PID: 3432)
Reads the hosts file
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3432)
Reads Microsoft Office registry keys
- serialfunc.exe (PID: 2928)
- serialfunc.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:17 14:08:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 436736 |
| InitializedDataSize: | 289792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3c6f3 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | PromptEdit_Demo MFC Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | PromptEdit_Demo |
| LegalCopyright: | Copyright (C) 2002 |
| LegalTrademarks: | - |
| OriginalFileName: | PromptEdit_Demo.EXE |
| ProductName: | PromptEdit_Demo Application |
| ProductVersion: | 1, 0, 0, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2020 13:08:14 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileDescription: | PromptEdit_Demo MFC Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | PromptEdit_Demo |
| LegalCopyright: | Copyright (C) 2002 |
| LegalTrademarks: | - |
| OriginalFilename: | PromptEdit_Demo.EXE |
| ProductName: | PromptEdit_Demo Application |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 17-Jan-2020 13:08:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006A965 | 0x0006AA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50205 |
.rdata | 0x0006C000 | 0x00017598 | 0x00017600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.194 |
.data | 0x00084000 | 0x00006560 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.3358 |
.rsrc | 0x0008B000 | 0x0002CB34 | 0x0002CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.84321 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.68558 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.4754 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.97205 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.25983 | 168 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.57142 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.726 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.9116 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.43845 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 1.50219 | 1160 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
Total processes
83
Monitored processes
48
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=761875241142370431 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16395808212404517512 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d90a9d0,0x6d90a9e0,0x6d90a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | --4faf7920 | C:\Users\admin\Desktop\ppcTHpZsqIl.exe | ppcTHpZsqIl.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16344511814781546272 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | r46Aj5FxjtIspIgsK9.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8958753992360482320 --mojo-platform-channel-handle=4412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4097871625220076291 --mojo-platform-channel-handle=4052 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4715512057500396364 --mojo-platform-channel-handle=4460 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1165725273079429375,15435747164423045023,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18267491903059770673 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
666
Read events
504
Write events
158
Delete events
4
Modification events
| (PID) Process: | (4028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3888-13223768748683250 |
Value: 259 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3888-13223768748683250 |
Value: 259 | |||
Executable files
3
Suspicious files
92
Text files
344
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e6dfa5fc-ecb4-490b-ba6a-62d8c50a8c4b.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39be59.TMP | text | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39be3a.TMP | text | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
85
DNS requests
87
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3432 | chrome.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEHiupDHBXOt1ew2KYQp0jmc%3D | NL | der | 1.71 Kb | shared |
3096 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/W1Wv8trtEt4yImnGt | US | binary | 148 b | malicious |
3432 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
3432 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
3096 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/lbyTxwo5h8vBzOYG3 | PL | binary | 148 b | malicious |
3432 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3432 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQu7Xbjq6rqggE7PFAsQRgy8Q8tzwQUkEeKG4TToN%2BkJNYZtBf1IaOym6gCEA7fr0YLsTZHJYxFeyuWNYA%3D | US | der | 471 b | whitelisted |
3096 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/K5zX4si | US | binary | 2.12 Mb | malicious |
2400 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/vDLJ | PL | binary | 148 b | malicious |
3096 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/lbyTxwo5h8vBzOYG3 | PL | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 216.239.36.117:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 216.239.38.117:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.16.142:443 | ogs.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 173.194.188.106:80 | r5---sn-4g5ednss.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.de |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3096 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3096 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3096 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3096 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3096 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3096 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3096 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3096 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3096 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3096 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |