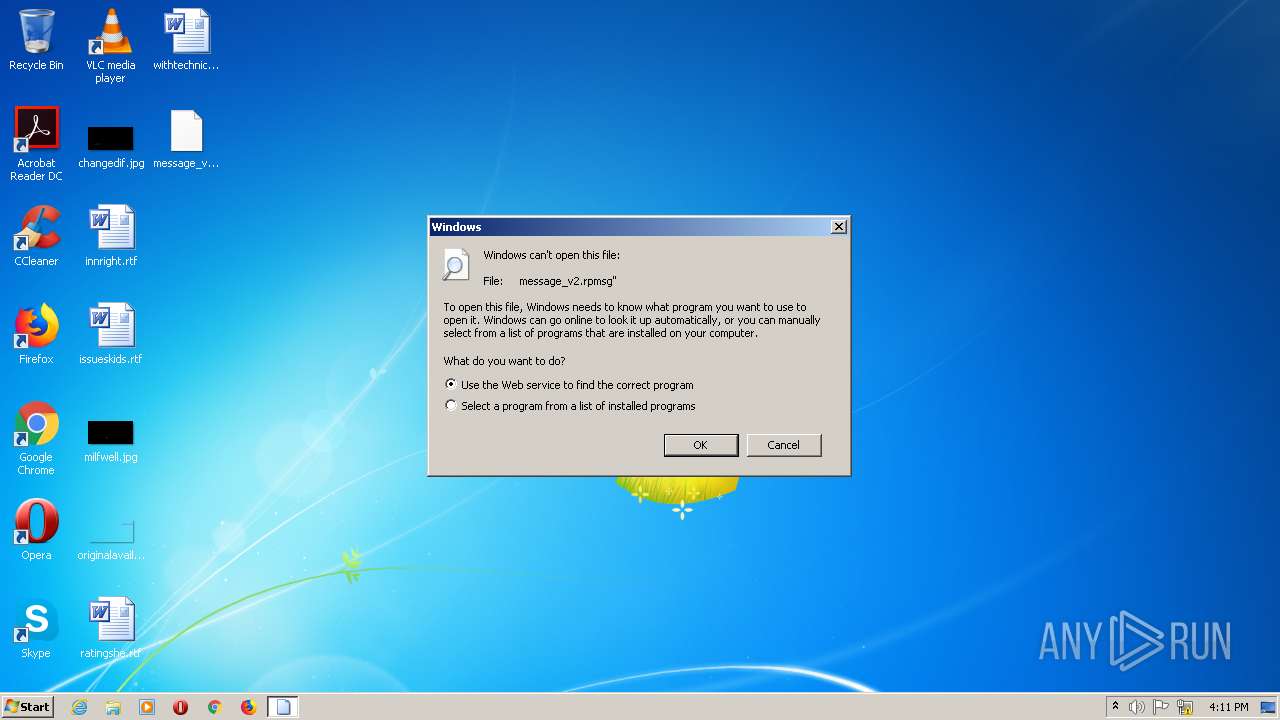
| File name: | message_v2.rpmsg |
| Full analysis: | https://app.any.run/tasks/43d2efba-5efb-4297-bc06-114185369e77 |
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2022, 16:11:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 6546F84FBF4BC736D46A0AFD76FC899F |
| SHA1: | 37224F62C4DF236EBD6037BDF94E6EF90C374C47 |
| SHA256: | 47C2AA92A9E6395B9E9DE690DA1B8C2818F6371BA7DC6E29A2888E600B598E53 |
| SSDEEP: | 6144:84AY6suJBofn9QLzHJCcH4j6zD90FOZkrynGuMzu+gYY:8O6suDouvHJCPjAD207Mzu7YY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- rundll32.exe (PID: 1416)
Executed via COM
- DllHost.exe (PID: 1876)
Reads Microsoft Outlook installation path
- IEXPLORE.EXE (PID: 1364)
- iexplore.exe (PID: 2336)
Drops a file with a compile date too recent
- DllHost.exe (PID: 1876)
INFO
Checks supported languages
- rundll32.exe (PID: 1416)
- iexplore.exe (PID: 2336)
- DllHost.exe (PID: 1876)
- IEXPLORE.EXE (PID: 1364)
Reads the computer name
- DllHost.exe (PID: 1876)
- iexplore.exe (PID: 2336)
- rundll32.exe (PID: 1416)
- IEXPLORE.EXE (PID: 1364)
Changes internet zones settings
- iexplore.exe (PID: 2336)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 1364)
- iexplore.exe (PID: 2336)
Creates files in the user directory
- iexplore.exe (PID: 2336)
- IEXPLORE.EXE (PID: 1364)
Checks Windows Trust Settings
- iexplore.exe (PID: 2336)
- IEXPLORE.EXE (PID: 1364)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 1364)
Dropped object may contain Bitcoin addresses
- DllHost.exe (PID: 1876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rpmsg | | | Restricted-Permission Message (100) |
|---|
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1364 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2336 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1416 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\message_v2.rpmsg" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | C:\Windows\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
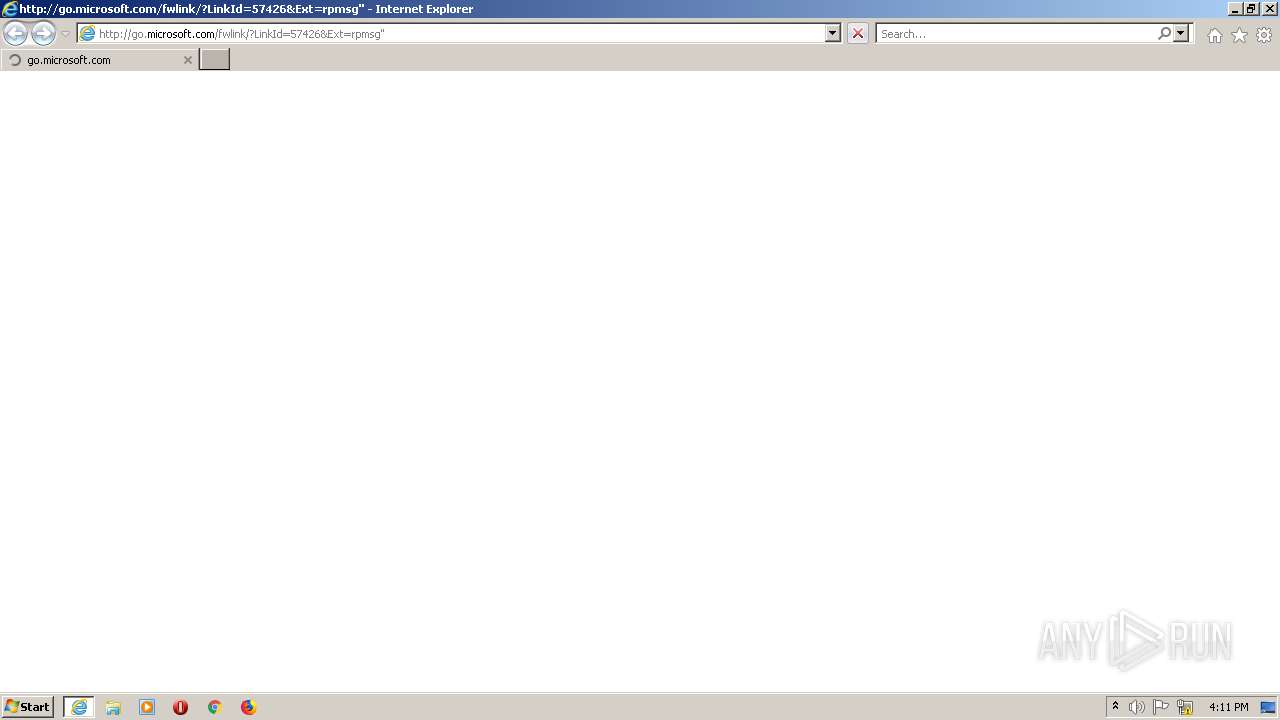
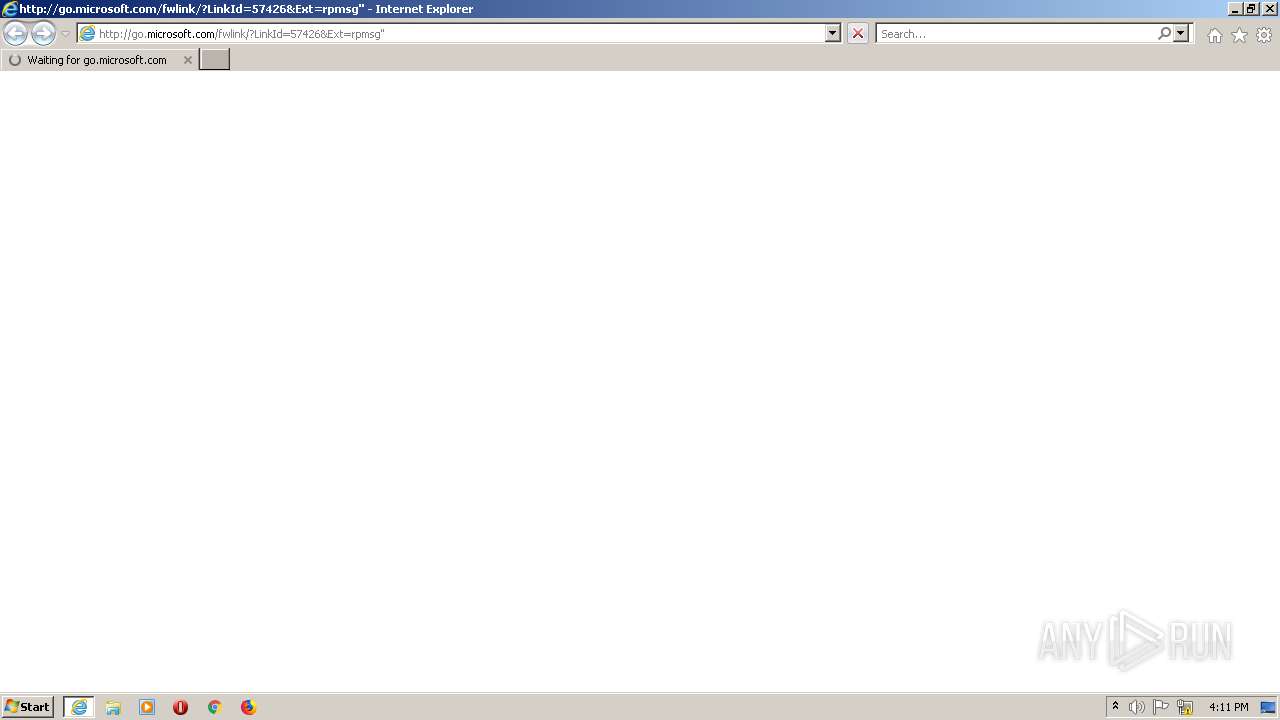
| 2336 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=rpmsg" | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 112
Read events
6 883
Write events
228
Delete events
1
Modification events
| (PID) Process: | (1416) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000EA5DA7A8CF1DD801 | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 4 | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940623 | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940623 | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
20
Text files
177
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 1876 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.log | binary | |
MD5:— | SHA256:— | |||
| 1876 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.chk | binary | |
MD5:— | SHA256:— | |||
| 1876 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V0100032.log | binary | |
MD5:— | SHA256:— | |||
| 1364 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\X5J063LC.txt | text | |
MD5:— | SHA256:— | |||
| 1364 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\CG57DEVT.txt | text | |
MD5:— | SHA256:— | |||
| 1876 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V0100031.log | binary | |
MD5:— | SHA256:— | |||
| 1876 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V0100033.log | binary | |
MD5:— | SHA256:— | |||
| 1364 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QOEMT5BO.txt | text | |
MD5:— | SHA256:— | |||
| 1364 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4Y3S9LHX.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
77
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1364 | IEXPLORE.EXE | GET | 302 | 104.111.242.51:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=rpmsg" | NL | — | — | whitelisted |
1364 | IEXPLORE.EXE | GET | 301 | 2.16.186.27:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=rpmsg%22 | unknown | — | — | whitelisted |
2336 | iexplore.exe | GET | 200 | 104.18.10.39:80 | http://cacerts.digicert.com/DigiCertGlobalRootG2.crt | US | der | 914 b | whitelisted |
2336 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?66817bc51dc4e3b1 | unknown | compressed | 59.9 Kb | whitelisted |
2336 | iexplore.exe | GET | 200 | 104.18.10.39:80 | http://cacerts.digicert.com/DigiCertGlobalRootG2.crt | US | der | 914 b | whitelisted |
2336 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5f083010183a5f05 | unknown | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1364 | IEXPLORE.EXE | 20.190.160.132:443 | login.live.com | Microsoft Corporation | US | suspicious |
2336 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2336 | iexplore.exe | 131.253.33.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2336 | iexplore.exe | 104.18.10.39:80 | cacerts.digicert.com | Cloudflare Inc | US | shared |
2336 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
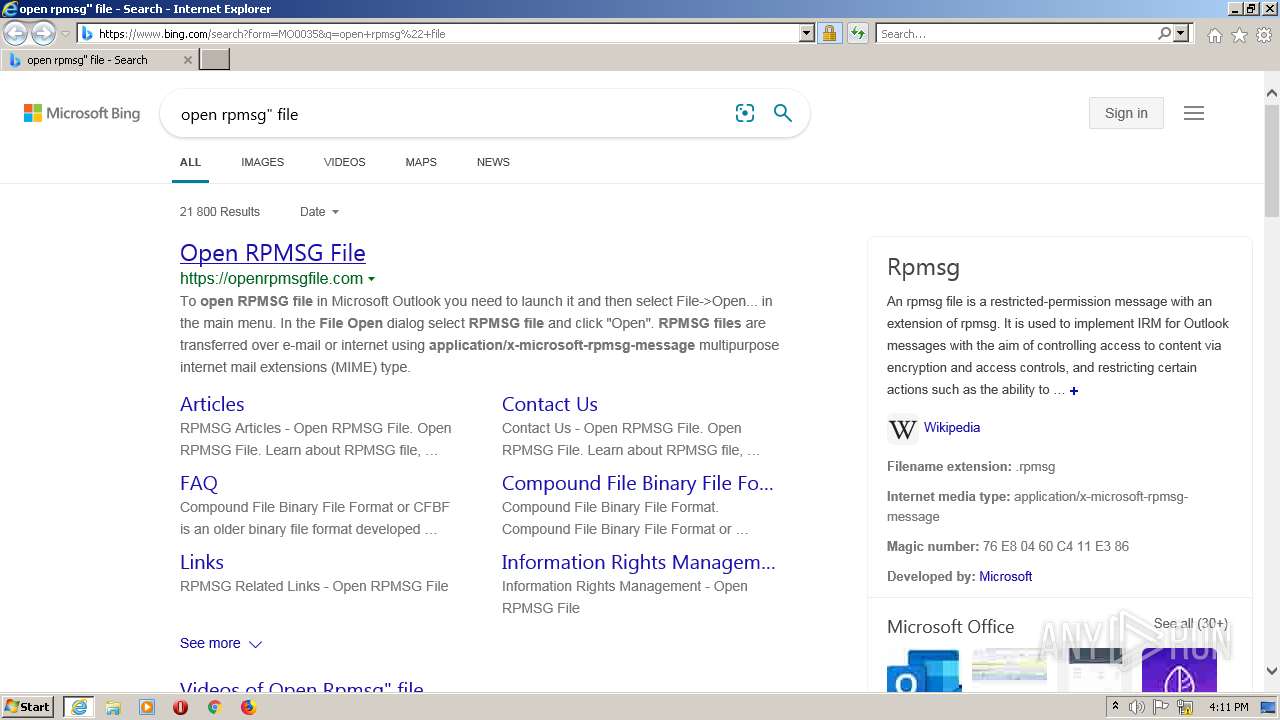
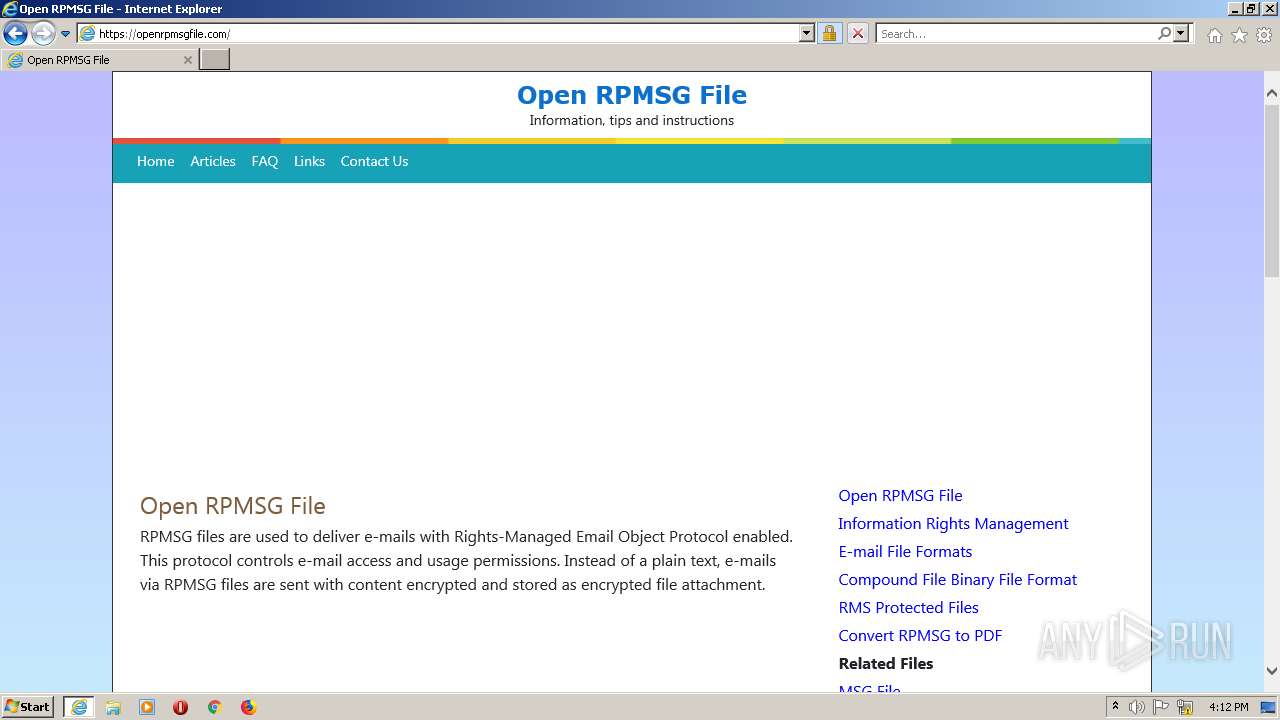
1364 | IEXPLORE.EXE | 172.67.166.124:443 | openrpmsgfile.com | — | US | unknown |
1364 | IEXPLORE.EXE | 69.16.175.42:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1364 | IEXPLORE.EXE | 104.18.11.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
— | — | 104.18.11.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
1364 | IEXPLORE.EXE | 142.250.186.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
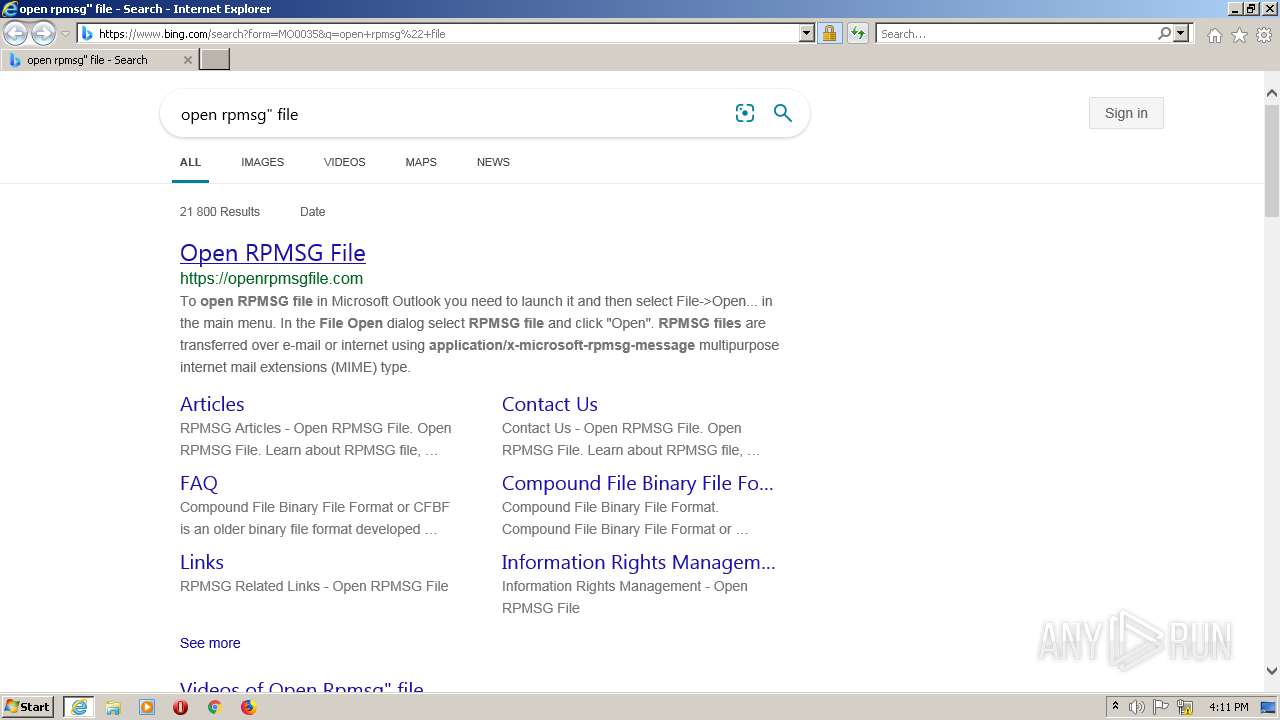
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |