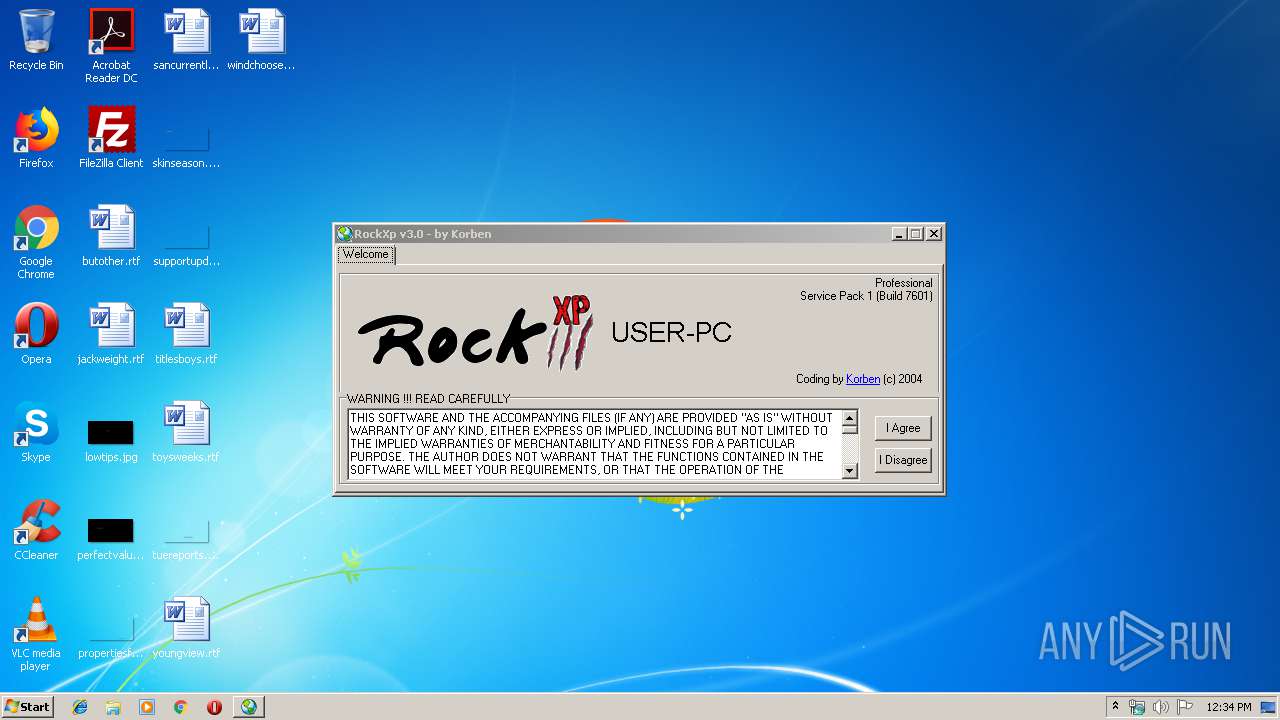
| File name: | rockxp.exe |
| Full analysis: | https://app.any.run/tasks/305fae3f-4a56-4a02-81d9-a32d9e7a8a55 |
| Verdict: | Suspicious activity |
| Analysis date: | September 26, 2019, 11:33:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, RAR self-extracting archive |
| MD5: | 28A9AC11DFA1BE9184BB01252E025B47 |
| SHA1: | 9D657F73FC028989F0A8AE89EF79E63A9A113B1F |
| SHA256: | 47C2209BF39079192197B443751968D610A024803C5AD183B5D95DBF2F74D700 |
| SSDEEP: | 12288:f2Pn6uN/0YswYciCfb+1/QpK+siqM/u3yKWLLRD:ePPNsHwtipysS/myKWLR |
MALICIOUS
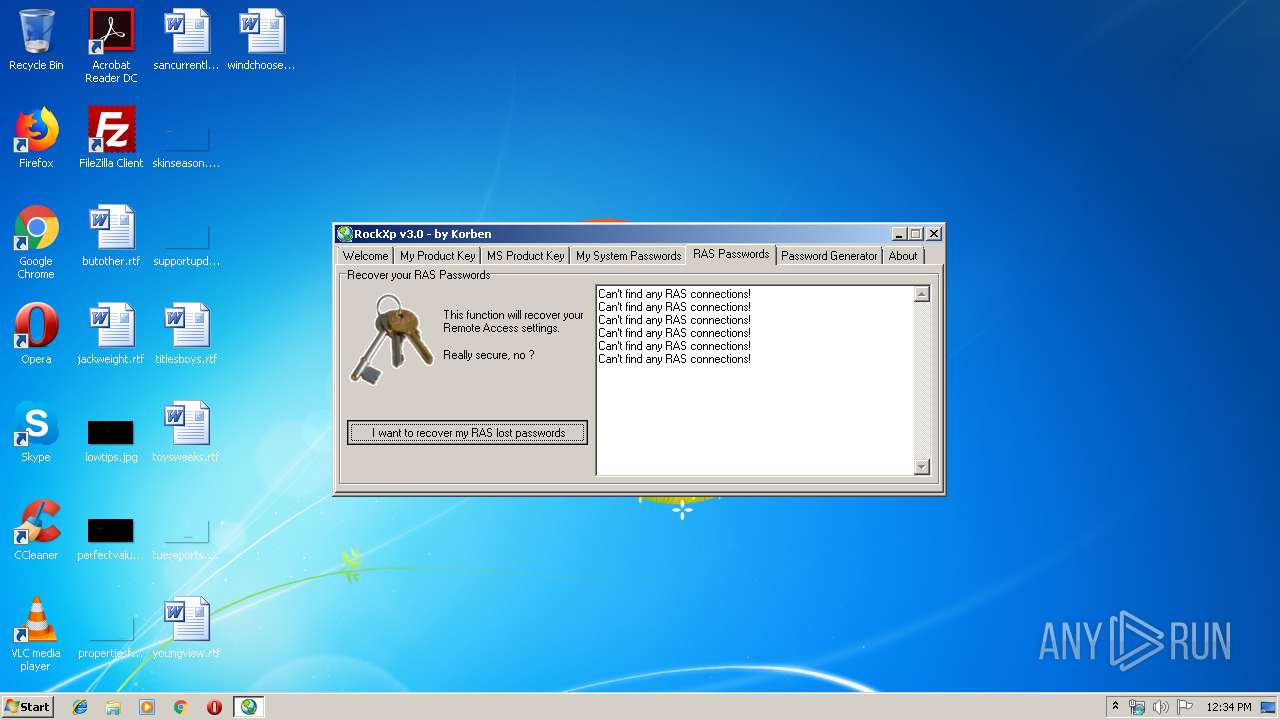
Application was dropped or rewritten from another process
- RockXP_.exe (PID: 2596)
- ras.exe (PID: 3568)
- xpkey.exe (PID: 3204)
- ras.exe (PID: 1868)
- ras.exe (PID: 1456)
- ras.exe (PID: 3012)
- ras.exe (PID: 3620)
- ras.exe (PID: 3032)
- ras.exe (PID: 3788)
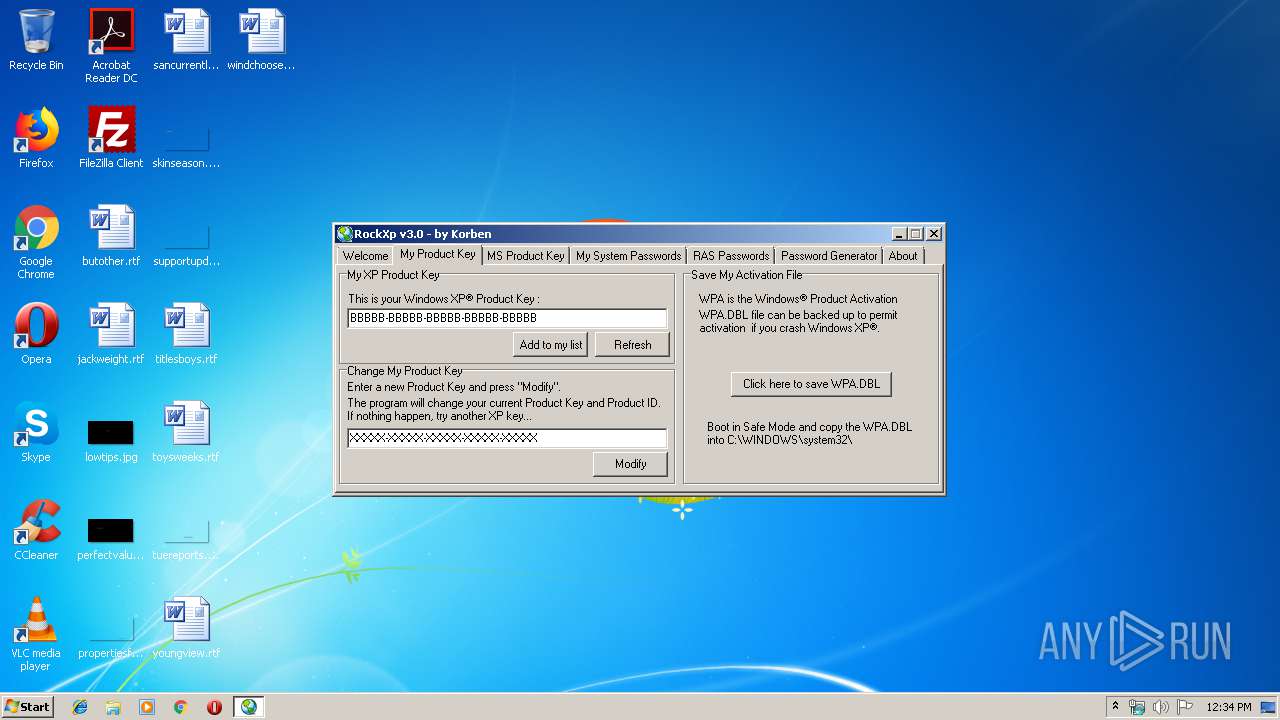
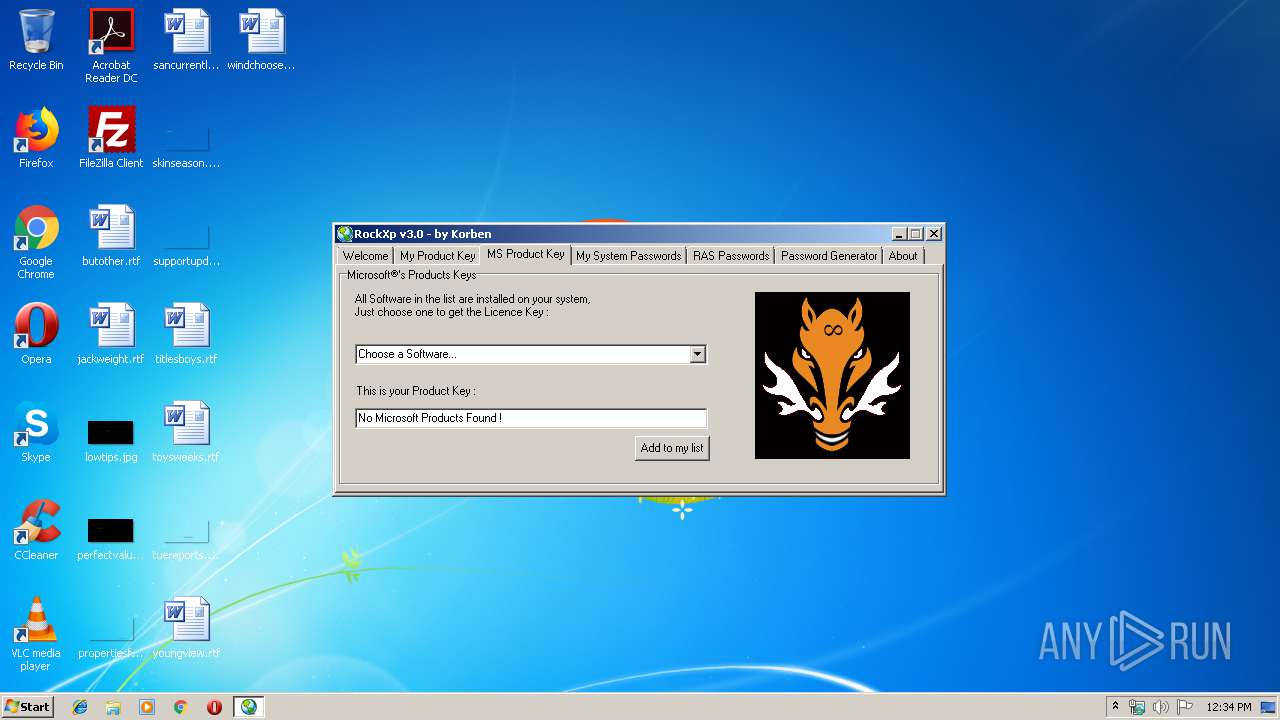
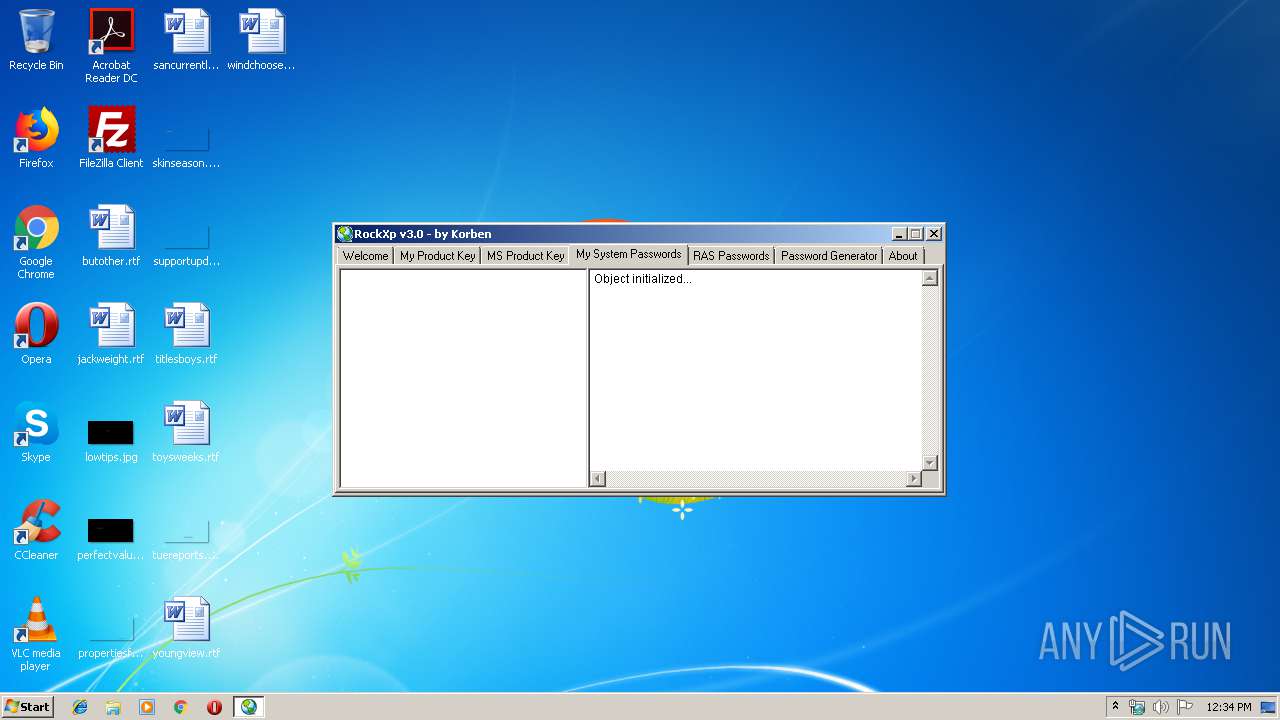
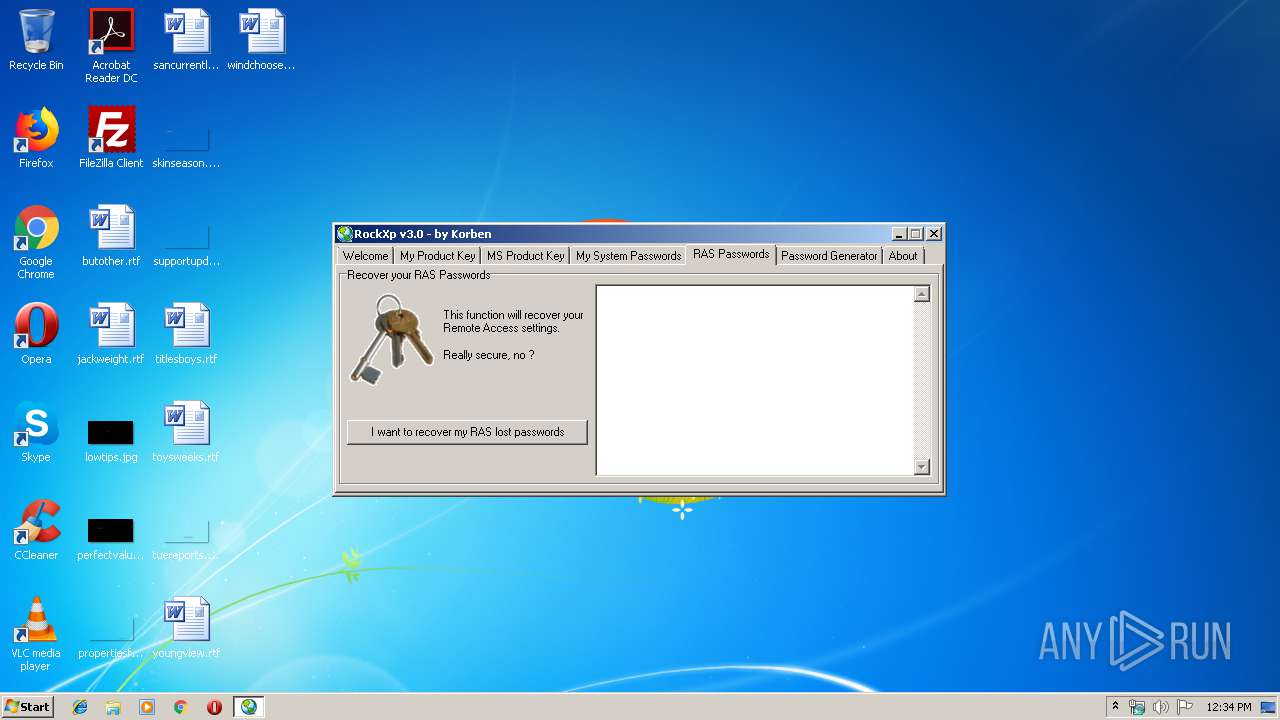
SUSPICIOUS
Executable content was dropped or overwritten
- rockxp.exe (PID: 2764)
Starts Internet Explorer
- RockXP_.exe (PID: 2596)
Creates files in the user directory
- RockXP_.exe (PID: 2596)
INFO
Application launched itself
- iexplore.exe (PID: 2468)
Changes internet zones settings
- iexplore.exe (PID: 2468)
Reads internet explorer settings
- iexplore.exe (PID: 2752)
Creates files in the user directory
- iexplore.exe (PID: 2752)
Reads Internet Cache Settings
- iexplore.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (88.2) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (4.6) |
| .exe | | | Win32 EXE Yoda's Crypter (4.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:01:22 14:36:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 45056 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 86016 |
| EntryPoint: | 0x20a70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jan-2004 13:36:06 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Jan-2004 13:36:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00015000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00016000 | 0x0000B000 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90015 |
.rsrc | 0x00021000 | 0x00002000 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.60378 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10885 | 531 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 5.97071 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 6.02051 | 2216 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 7.49135 | 556 | UNKNOWN | Russian - Russia | RT_STRING |
8 | 7.68432 | 886 | UNKNOWN | Russian - Russia | RT_STRING |
9 | 7.52066 | 530 | UNKNOWN | Russian - Russia | RT_STRING |
10 | 7.53824 | 638 | UNKNOWN | Russian - Russia | RT_STRING |
100 | 2.6902 | 62 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
101 | 7.8275 | 2998 | UNKNOWN | Russian - Russia | RT_BITMAP |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
55
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | ras.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ras.exe | — | RockXP_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1868 | ras.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ras.exe | — | RockXP_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | RockXP_.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\RockXP_.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\RockXP_.exe | rockxp.exe | ||||||||||||
User: admin Company: www.korben.tk Integrity Level: HIGH Description: "Because I Can" Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2468 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\rockxp.exe" | C:\Users\admin\AppData\Local\Temp\rockxp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3012 | ras.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ras.exe | — | RockXP_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3032 | ras.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ras.exe | — | RockXP_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\Temp\rockxp.exe" | C:\Users\admin\AppData\Local\Temp\rockxp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 3204 | xpkey.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\xpkey.exe | — | RockXP_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
673
Read events
622
Write events
51
Delete events
0
Modification events
| (PID) Process: | (2764) rockxp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2764) rockxp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3568) ras.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ras_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3568) ras.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ras_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3568) ras.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ras_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3568) ras.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ras_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3568) ras.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ras_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3568) ras.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ras_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
Executable files
4
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | xpkey.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\xpkey.txt | — | |
MD5:— | SHA256:— | |||
| 2764 | rockxp.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\xpkey.exe | executable | |
MD5:— | SHA256:— | |||
| 2764 | rockxp.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\RAS.exe | executable | |
MD5:— | SHA256:— | |||
| 2764 | rockxp.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\RockXp_.exe | executable | |
MD5:— | SHA256:— | |||
| 2764 | rockxp.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\keyms.exe | executable | |
MD5:BA47986812381F64938D22FC55D2C6E9 | SHA256:5B4FEC2EC25E488C8C377A7FE3AD90CF1AFFDA5A053A6A44EEA13CA6B98CAD9C | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\dnserror[1] | html | |
MD5:68E03ED57EC741A4AFBBCD11FAB1BDBE | SHA256:1FF3334C3EB27033F8F37029FD72F648EDD4551FCE85FC1F5159FEAEA1439630 | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\background_gradient[1] | image | |
MD5:20F0110ED5E4E0D5384A496E4880139B | SHA256:1471693BE91E53C2640FE7BAEECBC624530B088444222D93F2815DFCE1865D5B | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\down[1] | image | |
MD5:555E83CE7F5D280D7454AF334571FB25 | SHA256:70F316A5492848BB8242D49539468830B353DDAA850964DB4E60A6D2D7DB4880 | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2468 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
manumood.free.fr |
| unknown |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RockXP_.exe | 1 |
RockXP_.exe | 1 |