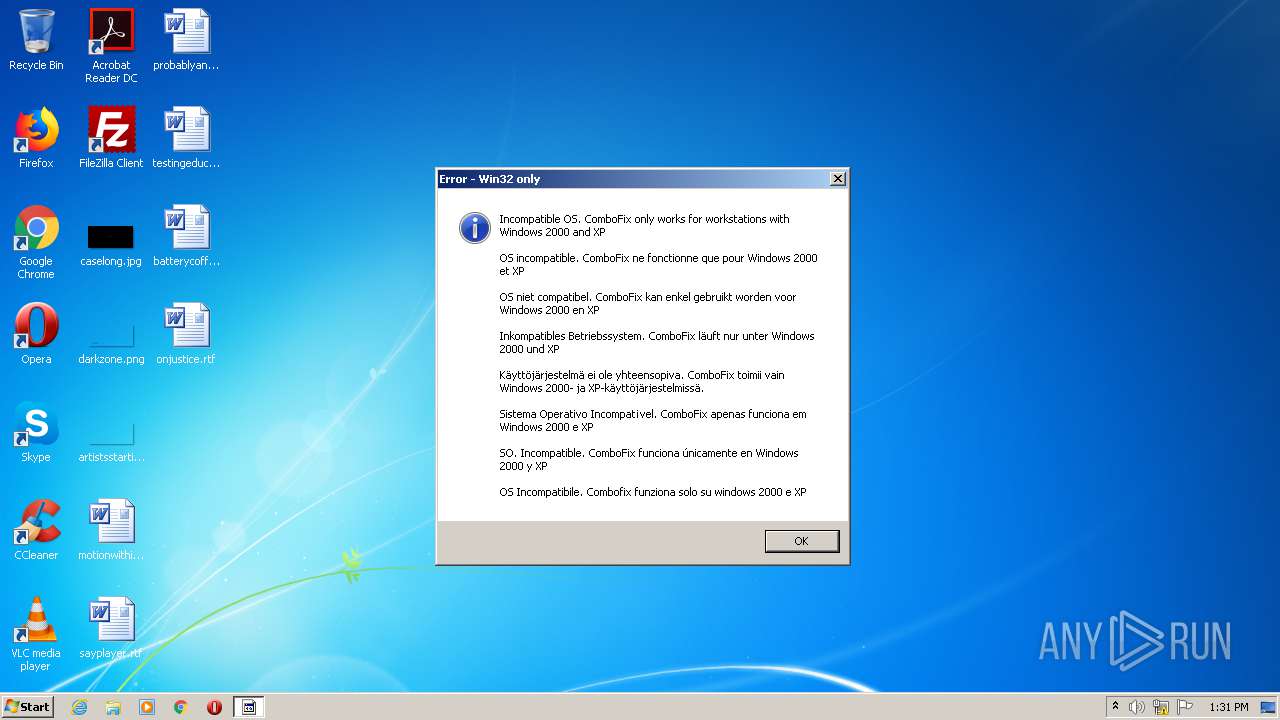
| File name: | combofix.exe |
| Full analysis: | https://app.any.run/tasks/877e28f0-bdbf-4e15-8797-f71e45239825 |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2020, 13:31:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, RAR self-extracting archive |
| MD5: | 9D28D175E0D467B683AE87FE6728CC14 |
| SHA1: | 47961B6A88BE7ADE825573579B57585004AF0977 |
| SHA256: | 47BF0BF8516951973F0AF471F3B2AA30991A99B11854CBC237482A1E333A15D0 |
| SSDEEP: | 49152:pyhan2svON6Effh+tdbgaWvyaJ6zbfDxY0+r8vHPZAU0NxELRIbYTnw+sOuAtIdy:pQPJNrffh+t9mvyaJ6zjVY0RvHPZAU0g |
MALICIOUS
Application was dropped or rewritten from another process
- iexplore.exe (PID: 3732)
- iexplore.exe (PID: 868)
- n.pif (PID: 2488)
- pv.com (PID: 3160)
- hidec.exe (PID: 628)
- n.pif (PID: 2144)
- pev.exe (PID: 2652)
- n.pif (PID: 256)
- swreg.exe (PID: 2276)
- swreg.exe (PID: 2828)
- SWXCACLS.cfxxe (PID: 3024)
- hidec.exe (PID: 1356)
- swreg.exe (PID: 3660)
- n.pif (PID: 2996)
- hidec.exe (PID: 548)
- hidec.exe (PID: 2676)
- hidec.exe (PID: 1940)
- hidec.exe (PID: 2840)
- hidec.exe (PID: 3388)
- swreg.exe (PID: 2764)
- hidec.exe (PID: 2220)
- SWREG.exe (PID: 2508)
- n.pif (PID: 3708)
- nircmd.cfxxe (PID: 128)
- GSAR.cfxxe (PID: 3448)
- GSAR.cfxxe (PID: 3092)
- n.pif (PID: 3376)
- SWREG.exe (PID: 3348)
- SWREG.exe (PID: 3440)
- SWREG.exe (PID: 956)
- n.pif (PID: 2908)
- NirCmd.cfxxe (PID: 1808)
- cmd.execf (PID: 3096)
- NirCmd.cfxxe (PID: 800)
- grep.cfxxe (PID: 3716)
- swreg.exe (PID: 3396)
- pev.exe (PID: 3288)
- PV.cfxxe (PID: 2592)
- grep.cfxxe (PID: 2964)
- grep.cfxxe (PID: 2708)
- swreg.exe (PID: 1504)
- nircmd.cfxxe (PID: 3532)
- swreg.exe (PID: 1976)
- NircmdB.exe (PID: 4056)
- grep.cfxxe (PID: 3296)
- swreg.exe (PID: 704)
- grep.cfxxe (PID: 2328)
- swreg.exe (PID: 3864)
Changes the autorun value in the registry
- InfDefaultInstall.exe (PID: 2108)
SUSPICIOUS
Executable content was dropped or overwritten
- combofix.exe (PID: 2704)
- GSAR.cfxxe (PID: 3448)
- GSAR.cfxxe (PID: 3092)
- cmd.execf (PID: 3096)
Creates executable files which already exist in Windows
- combofix.exe (PID: 2704)
Starts application with an unusual extension
- combofix.exe (PID: 2704)
- n.pif (PID: 2488)
- hidec.exe (PID: 3388)
- n.pif (PID: 3708)
- nircmd.cfxxe (PID: 128)
- n.pif (PID: 3376)
- cmd.execf (PID: 3096)
Modifies the open verb of a shell class
- InfDefaultInstall.exe (PID: 2108)
- swreg.exe (PID: 2764)
- swreg.exe (PID: 3396)
Creates files in the Windows directory
- GSAR.cfxxe (PID: 3448)
Starts CMD.EXE for commands execution
- n.pif (PID: 3376)
INFO
Dropped object may contain Bitcoin addresses
- combofix.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:20 10:15:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 45056 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 106496 |
| EntryPoint: | 0x25a60 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jul-2009 08:15:43 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Jul-2009 08:15:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0001A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0001B000 | 0x0000B000 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90924 |
.rsrc | 0x00026000 | 0x00002000 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.36398 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
105
Monitored processes
54
Malicious processes
9
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\32788R22FWJFW\nircmd.cfxxe" exec hide 32788R22FWJFW\GSAR.cfxxe -if -s\:000M:000i:000c:000r:000o -r\:001M:000i:000c:000r:000o "C:\Windows\system32\cmd.exe" "C:\Windows\system32\cmd.execf" | C:\32788R22FWJFW\nircmd.cfxxe | — | combofix.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 0 Version: 2.35 Modules
| |||||||||||||||
| 256 | "C:\32788R22FWJFW\n.pif" exec hide 32788R22FWJFW\SWREG.exe acl "hklm\software\microsoft\windows nt\currentversion\windows" /O Guest /Q | C:\32788R22FWJFW\n.pif | — | combofix.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 0 Version: 2.35 Modules
| |||||||||||||||
| 548 | "C:\32788R22FWJFW\hidec.exe" 32788R22FWJFW\swreg.exe import 32788R22FWJFW\EXE.reg | C:\32788R22FWJFW\hidec.exe | — | combofix.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 628 | "C:\32788R22FWJFW\hidec.exe" 32788R22FWJFW\pev.exe -k * and { *Antivirus*Pro.exe or svchast.exe or winupdate.exe or or ANTI_files.exe or dbsinit.exe or desot.exe or aap.exe or -preg"\d{3,}.exe" } | C:\32788R22FWJFW\hidec.exe | — | combofix.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 704 | SWREG.exe QUERY "hklm\software\microsoft\windows nt\currentversion" /v currentversion | C:\32788R22FWJFW\swreg.exe | — | cmd.execf | |||||||||||
User: admin Company: SteelWerX Integrity Level: HIGH Description: Freeware implementation of REG.EXE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 800 | 32788R22FWJFW\Nircmd.cfxxe killprocess "C:\Users\admin\AppData\Local\Temp\combofix.exe" | C:\32788R22FWJFW\NirCmd.cfxxe | — | cmd.execf | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 0 Version: 2.35 Modules
| |||||||||||||||
| 868 | "C:\32788R22FWJFW\iexplore.exe" win close ititle "SysInternals" | C:\32788R22FWJFW\iexplore.exe | — | combofix.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 0 Version: 2.35 Modules
| |||||||||||||||
| 956 | 32788R22FWJFW\SWREG.exe acl "hklm\software\microsoft\windows nt\currentversion\windows" /DE:F /Q | C:\32788R22FWJFW\SWREG.exe | — | n.pif | |||||||||||
User: admin Company: SteelWerX Integrity Level: HIGH Description: Freeware implementation of REG.EXE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 1356 | "C:\32788R22FWJFW\hidec.exe" 32788R22FWJFW\SWREG.exe acl "hklm\software\microsoft\windows nt\currentversion\windows" /O Guest /Q | C:\32788R22FWJFW\hidec.exe | — | combofix.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1504 | 32788R22FWJFW\swreg.exe acl "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Drivers32" /reset /q | C:\32788R22FWJFW\swreg.exe | — | n.pif | |||||||||||
User: admin Company: SteelWerX Integrity Level: HIGH Description: Freeware implementation of REG.EXE Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
334
Read events
121
Write events
106
Delete events
107
Modification events
| (PID) Process: | (2704) combofix.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2704) combofix.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3160) pv.com | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2144) n.pif | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2144) n.pif | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2956) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (2956) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2108) InfDefaultInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (2108) InfDefaultInstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | (default) |
Value: | |||
Executable files
33
Suspicious files
11
Text files
107
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | combofix.exe | C:\32788R22FWJFW\License\dumphive-license.txt | text | |
MD5:150E9FCC32EC4E0D58DAB2095A7B6067 | SHA256:CAD685EDEA1E7EEA8F47D43A3BDC62407438C144209D79936297065A1D0CC084 | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\License\Curl - license.txt | text | |
MD5:3D0BA9A767ABC47D7D10AC8D7447A1ED | SHA256:5127082E64CB0EFF2313649251DDB2CC8149962E263BEB01EA5CE62C1AEEAD3D | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\License\FI - license.txt | text | |
MD5:692FF0A53727BD54ACF4C43F73F6F96A | SHA256:3E940588E4C723878C11FEEB2466BF8E38BD36428959D1BE4FA6A287B5BB794A | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\Lang.bat | text | |
MD5:— | SHA256:— | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\Kollect.bat | text | |
MD5:— | SHA256:— | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\License\EXTRACT.TXT | text | |
MD5:20D98EC0A14AC3B1AC28C3E499BD059D | SHA256:BBD4D7FCE3B739AE201E7568C7A97AA2ECAE5477D374671495ACD98D9333145E | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\List-D.bat | text | |
MD5:— | SHA256:— | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\List-C.bat | binary | |
MD5:— | SHA256:— | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\List.bat | text | |
MD5:— | SHA256:— | |||
| 2704 | combofix.exe | C:\32788R22FWJFW\Boot.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report