| File name: | Support.Client.exe |
| Full analysis: | https://app.any.run/tasks/bd2be4c0-beaa-4b60-9fe0-581f1be03f0c |
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2023, 17:12:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 31F50E3340C13B7D6C8204A84AB64E98 |
| SHA1: | F0B0505A4866A8D9E4D81FCE307CB6CB32613AAB |
| SHA256: | 47A799A09AACE4DA6306E9BBCAFE11BB61C2B43C651466492AE6A833149F2896 |
| SSDEEP: | 3072:9dyfcQ73rZy2kBjfNTMpjfJVOxz8lzqEO:Oce3rEBxItlO |
MALICIOUS
Drops the executable file immediately after the start
- dfsvc.exe (PID: 4000)
Loads dropped or rewritten executable
- dfsvc.exe (PID: 4000)
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.WindowsClient.exe (PID: 2628)
- ScreenConnect.ClientService.exe (PID: 2860)
- ScreenConnect.WindowsClient.exe (PID: 3684)
- ScreenConnect.ClientService.exe (PID: 2232)
- ScreenConnect.WindowsClient.exe (PID: 2796)
Application was dropped or rewritten from another process
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.ClientService.exe (PID: 2860)
- ScreenConnect.ClientService.exe (PID: 2232)
- ScreenConnect.WindowsClient.exe (PID: 3684)
- ScreenConnect.WindowsClient.exe (PID: 2628)
- ScreenConnect.WindowsClient.exe (PID: 2796)
SCREENCONNECT was detected
- ScreenConnect.ClientService.exe (PID: 2232)
Creates a writable file the system directory
- ScreenConnect.WindowsClient.exe (PID: 3684)
- ScreenConnect.WindowsClient.exe (PID: 2796)
Deletes the SafeBoot registry key
- ScreenConnect.ClientService.exe (PID: 2232)
SUSPICIOUS
Reads settings of System Certificates
- dfsvc.exe (PID: 4000)
Reads the Internet Settings
- dfsvc.exe (PID: 4000)
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.ClientService.exe (PID: 2860)
- ScreenConnect.WindowsClient.exe (PID: 2628)
Checks Windows Trust Settings
- dfsvc.exe (PID: 4000)
Reads Internet Explorer settings
- dfsvc.exe (PID: 4000)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 4000)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 2232)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 2232)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 2232)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3680)
- Support.Client.exe (PID: 1040)
- dfsvc.exe (PID: 4000)
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.ClientService.exe (PID: 2860)
- ScreenConnect.ClientService.exe (PID: 2232)
- ScreenConnect.WindowsClient.exe (PID: 3684)
- ScreenConnect.WindowsClient.exe (PID: 2628)
- ScreenConnect.WindowsClient.exe (PID: 2796)
Checks supported languages
- wmpnscfg.exe (PID: 3680)
- Support.Client.exe (PID: 1040)
- dfsvc.exe (PID: 4000)
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.ClientService.exe (PID: 2860)
- ScreenConnect.ClientService.exe (PID: 2232)
- ScreenConnect.WindowsClient.exe (PID: 3684)
- ScreenConnect.WindowsClient.exe (PID: 2628)
- ScreenConnect.WindowsClient.exe (PID: 2796)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3680)
- dfsvc.exe (PID: 4000)
- Support.Client.exe (PID: 1040)
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.ClientService.exe (PID: 2860)
- ScreenConnect.ClientService.exe (PID: 2232)
- ScreenConnect.WindowsClient.exe (PID: 2628)
- ScreenConnect.WindowsClient.exe (PID: 3684)
- ScreenConnect.WindowsClient.exe (PID: 2796)
Checks proxy server information
- dfsvc.exe (PID: 4000)
Reads Environment values
- dfsvc.exe (PID: 4000)
- ScreenConnect.ClientService.exe (PID: 2232)
Create files in a temporary directory
- dfsvc.exe (PID: 4000)
Creates files or folders in the user directory
- dfsvc.exe (PID: 4000)
- ScreenConnect.WindowsClient.exe (PID: 3704)
- ScreenConnect.ClientService.exe (PID: 2232)
Process checks are UAC notifies on
- dfsvc.exe (PID: 4000)
Manual execution by a user
- chrome.exe (PID: 3852)
- msedge.exe (PID: 3816)
Application launched itself
- chrome.exe (PID: 3852)
- msedge.exe (PID: 3816)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:05:18 18:07:24+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 44032 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16e7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
96
Monitored processes
56
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3692 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=5336 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=4724 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=3528 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\AppData\Local\Temp\Support.Client.exe" | C:\Users\admin\AppData\Local\Temp\Support.Client.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=5784 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4200 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6ac9f598,0x6ac9f5a8,0x6ac9f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1640 --field-trial-handle=1248,i,12520048296249874237,9947790272844844346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2104 --field-trial-handle=1172,i,13660419118416574159,9501672745172067247,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
12 925
Read events
12 764
Write events
130
Delete events
31
Modification events
| (PID) Process: | (3680) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{DA334ABE-5D94-4309-B0F6-FAB1C166D2F5}\{CC168C0C-43C7-4834-B547-C3F00ED61A27} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3680) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{DA334ABE-5D94-4309-B0F6-FAB1C166D2F5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3680) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{30FDD517-EE35-48A0-BBB7-88CECA095FBA} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1040) Support.Client.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4000) dfsvc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4000) dfsvc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4000) dfsvc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4000) dfsvc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4000) dfsvc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4000) dfsvc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000056010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
81
Suspicious files
1 607
Text files
118
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4000 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C56C4404C4DEF0DC88E5FCD9F09CB2F1 | binary | |
MD5:D91299E84355CD8D5A86795A0118B6E9 | SHA256:46011EDE1C147EB2BC731A539B7C047B7EE93E48B9D3C3BA710CE132BBDFAC6B | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.WindowsClient.exe.manifest | xml | |
MD5:9E9DF91A0CF5DA1395482E686AD6FEA6 | SHA256:19C4E673613AAD3E76EF9138BC7FBF4FA4AB847D47FD74302C0CF8C2881C875A | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.ClientService.exe | executable | |
MD5:26A1F2D1396B5E6588F45647962E8E63 | SHA256:5C2EDB37FA30C699F661ED1ED7BF1C326F3558AC599173599615BA8B95C42A8B | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.WindowsClient.exe | executable | |
MD5:2AF189AD6A44AF1211EF19FE336C8811 | SHA256:CDCDC9F22050D6F6BFA016F62323BC86EA348A89B846F2C15184BA90CB045E33 | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.WindowsBackstageShell.exe.config | xml | |
MD5:728175E20FFBCEB46760BB5E1112F38B | SHA256:87C640D3184C17D3B446A72D5F13D643A774B4ECC7AFBEDFD4E8DA7795EA8077 | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.WindowsBackstageShell.exe | executable | |
MD5:06F210BAB663BFB4514C026105A53164 | SHA256:F6152430FF0E54DED3F6F493FDDB5A8464DE3BA7E614702640A6110520E35F63 | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.WindowsClient.exe.config | xml | |
MD5:728175E20FFBCEB46760BB5E1112F38B | SHA256:87C640D3184C17D3B446A72D5F13D643A774B4ECC7AFBEDFD4E8DA7795EA8077 | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.Windows.dll | executable | |
MD5:22EEA022D4B3F4637F7FDB7008DA0C5E | SHA256:106CF983FBD5A2377B67EA2DCD34B31BABF151EBBC35066765FBF697A1F1E182 | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.Client.dll | executable | |
MD5:55C13DFABBBF6625167FBEE665E9020B | SHA256:2E12B4914F116088FCE8B3EDB27BCD10FB5CB95F91EE47E62964BEE492BC398B | |||
| 4000 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\KPA9JH5K.J67\MRZ52CVG.K5M\ScreenConnect.Core.dll | executable | |
MD5:D10F4EC9DD6BE5277FFC3473A09E9F8A | SHA256:36A658B7B88CE49F0FFD9A54ED9465DC9963D6AA78D1C6348738542C7FCA2BF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
257
DNS requests
332
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4000 | dfsvc.exe | GET | 200 | 192.229.221.95:80 | http://cacerts.digicert.com/DigiCertTrustedG4CodeSigningRSA4096SHA3842021CA1.crt | US | binary | 1.68 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
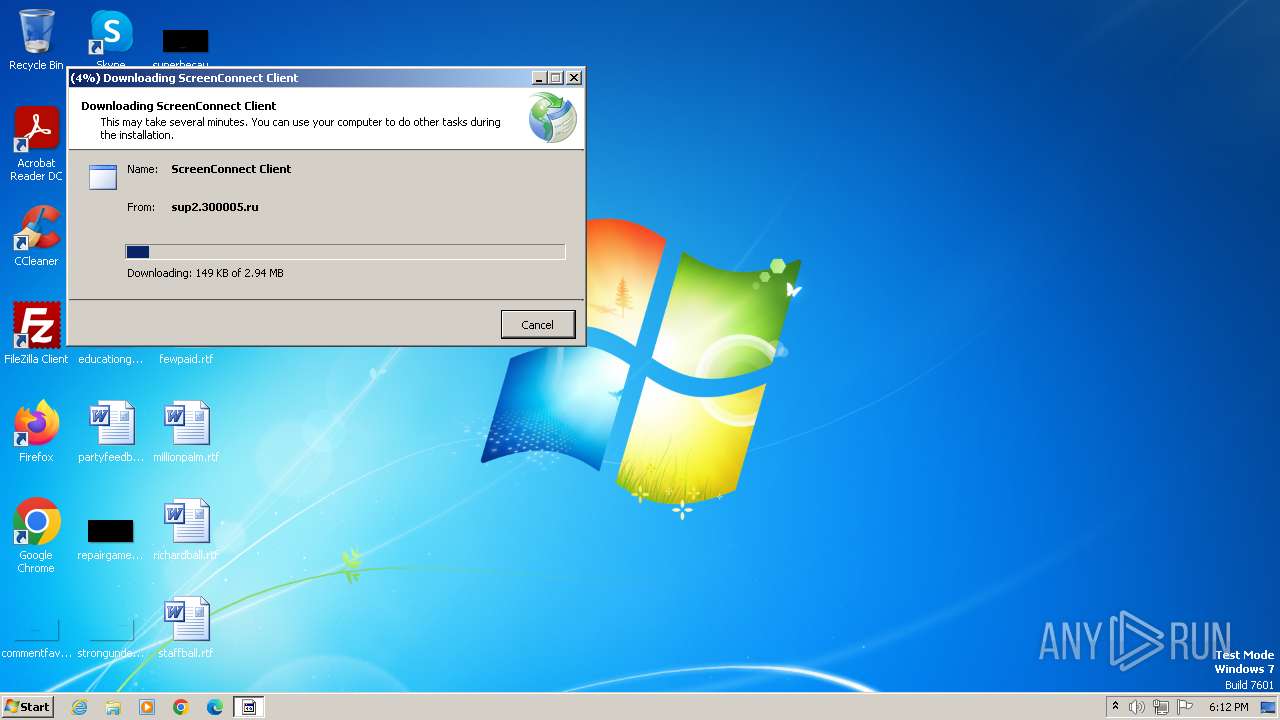
4000 | dfsvc.exe | 45.227.255.41:443 | sup2.300005.ru | NForce Entertainment B.V. | PA | unknown |
4000 | dfsvc.exe | 192.229.221.95:80 | cacerts.digicert.com | EDGECAST | US | whitelisted |
2232 | ScreenConnect.ClientService.exe | 45.227.255.41:8041 | sup2.300005.ru | NForce Entertainment B.V. | PA | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3852 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2400 | chrome.exe | 172.217.17.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3816 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3952 | msedge.exe | 204.79.197.203:443 | ntp.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sup2.300005.ru |
| unknown |
cacerts.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
assets.msn.com |
| whitelisted |
img-s-msn-com.akamaized.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
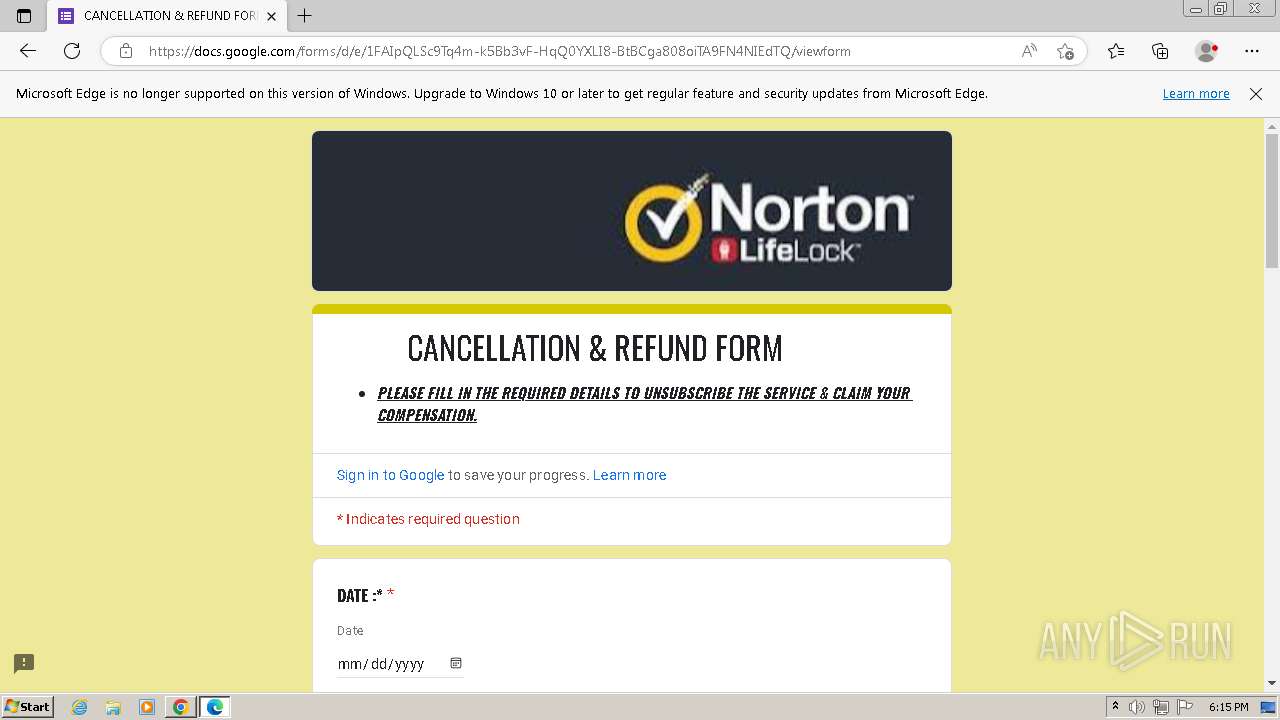
1088 | svchost.exe | Possible Social Engineering Attempted | ET PHISHING DNS Query to TOAD Domain (300005 .ru) |
4000 | dfsvc.exe | Possible Social Engineering Attempted | ET PHISHING Observed TOAD Domain (300005 .ru in TLS SNI) |
2232 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
2232 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|