| File name: | VpnClientSetupX86.exe |
| Full analysis: | https://app.any.run/tasks/4e44ca97-1163-4b41-ad49-3f627e287be9 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2020, 06:08:25 |
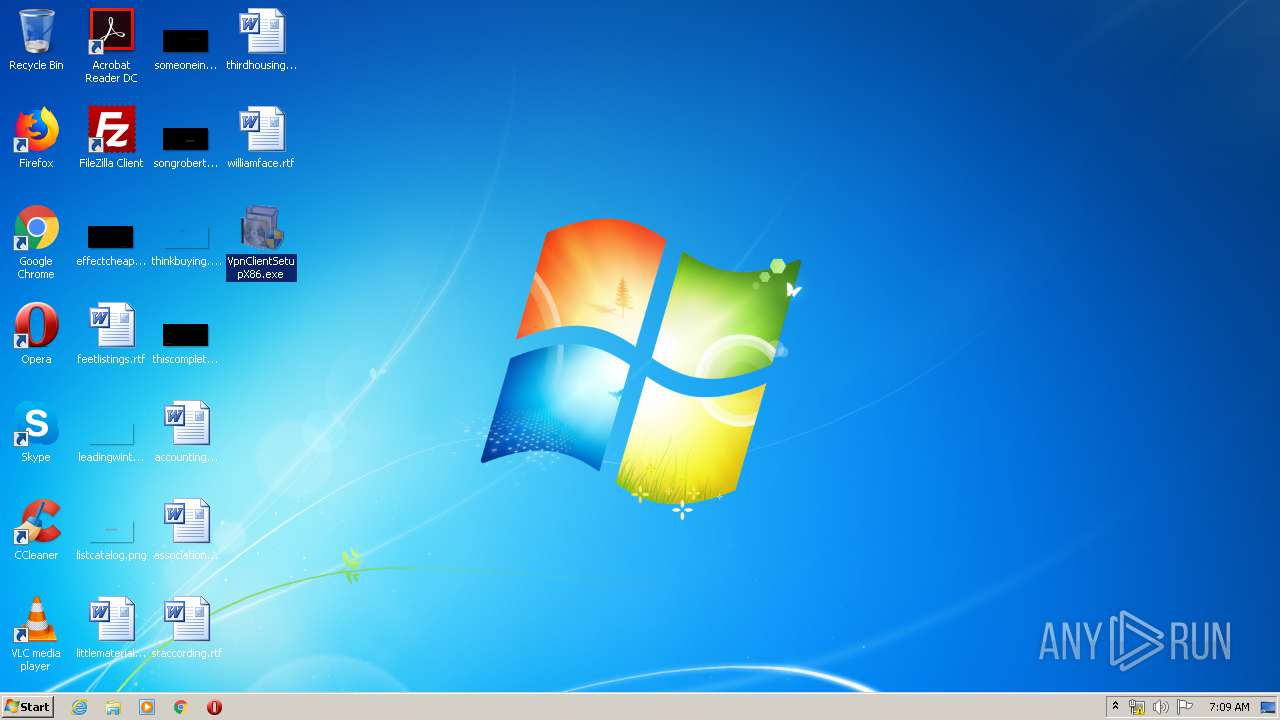
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FD002B8FAB24956675FFAEFE5CD54D6F |
| SHA1: | 872420CA6AE4445F4B9306EF76DD7EDE3EE724DE |
| SHA256: | 478B5324209644A744B325A81E7733169564F411E060C634B13A59426D000F86 |
| SSDEEP: | 3072:y75U501G5GWp1icKAArDZz4N9GhbkrNEk1yWC4vGx7hOyKZ3Csyw:tbp0yN90QE78ghOyzs |
MALICIOUS
Changes the autorun value in the registry
- VpnClientSetupX86.exe (PID: 1384)
- VpnClientSetupX86.exe (PID: 3292)
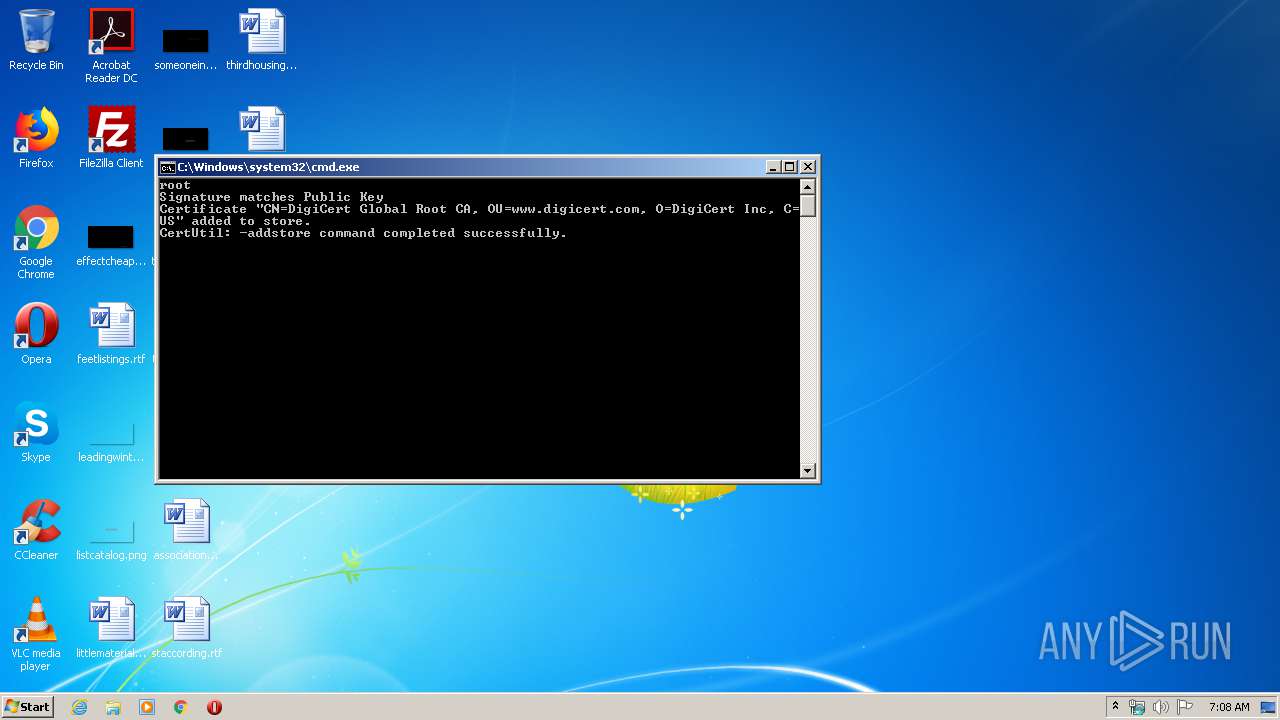
Changes settings of System certificates
- certutil.exe (PID: 1532)
Loads dropped or rewritten executable
- cmstp.exe (PID: 2812)
SUSPICIOUS
Executable content was dropped or overwritten
- VpnClientSetupX86.exe (PID: 1384)
- cmstp.exe (PID: 1736)
- VpnClientSetupX86.exe (PID: 3292)
- cmstp.exe (PID: 2812)
Creates files in the user directory
- cmstp.exe (PID: 1736)
- cmstp.exe (PID: 2812)
Uses REG.EXE to modify Windows registry
- cmstp.exe (PID: 1736)
- cmstp.exe (PID: 2812)
Starts CMD.EXE for commands execution
- cmstp.exe (PID: 1736)
- cmstp.exe (PID: 2812)
Creates files in the Windows directory
- certutil.exe (PID: 1532)
- cmstp.exe (PID: 2812)
- certutil.exe (PID: 3012)
Removes files from Windows directory
- certutil.exe (PID: 1532)
- certutil.exe (PID: 3012)
- cmstp.exe (PID: 2812)
INFO
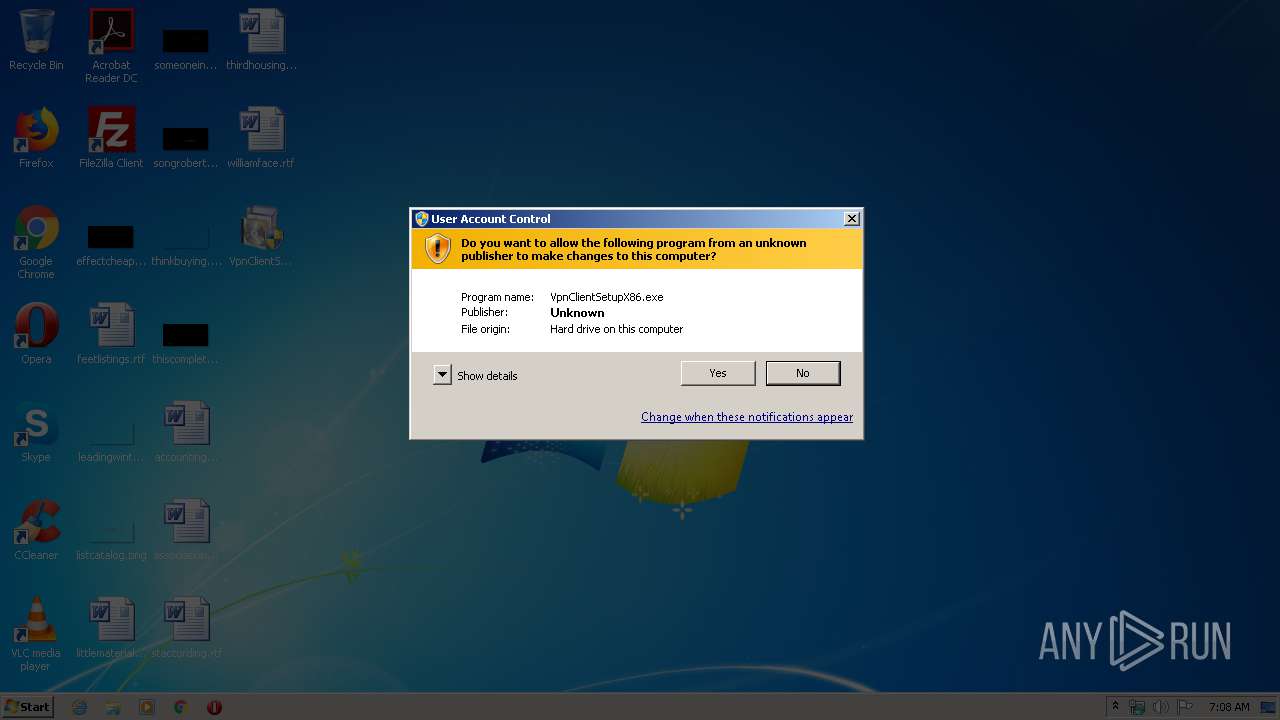
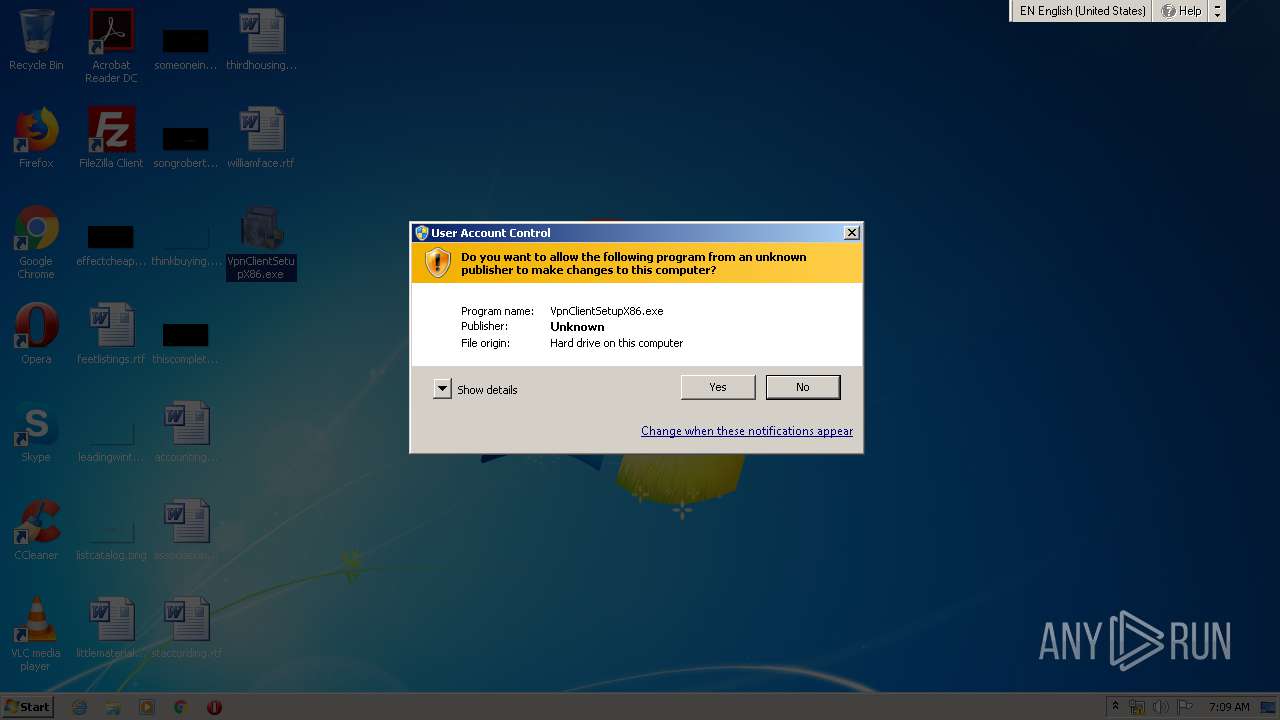
Manual execution by user
- VpnClientSetupX86.exe (PID: 1704)
- VpnClientSetupX86.exe (PID: 3292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:01 05:48:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 26112 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6bd0 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.14393.0 |
| ProductVersionNumber: | 11.0.14393.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.14393.0 (rs1_release.160715-1616) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.14393.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-2018 04:48:28 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.14393.0 (rs1_release.160715-1616) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.14393.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Jan-2018 04:48:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000651C | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.30791 |
.data | 0x00008000 | 0x00001A48 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97064 |
.idata | 0x0000A000 | 0x0000106E | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05715 |
.rsrc | 0x0000C000 | 0x00026718 | 0x00026800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.35024 |
.reloc | 0x00033000 | 0x00000890 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.27466 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.74577 | 367 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
56
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | reg add HKLM\SYSTEM\CurrentControlSet\Services\RasMan\PPP\EAP\13 /v SelectSelfSignedCert /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmstp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1384 | "C:\Users\admin\Desktop\VpnClientSetupX86.exe" | C:\Users\admin\Desktop\VpnClientSetupX86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
| 1532 | certutil -addstore root C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\a01339dd-df25-4f51-99f7-97a3f1245854.cer | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | "C:\Users\admin\Desktop\VpnClientSetupX86.exe" | C:\Users\admin\Desktop\VpnClientSetupX86.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
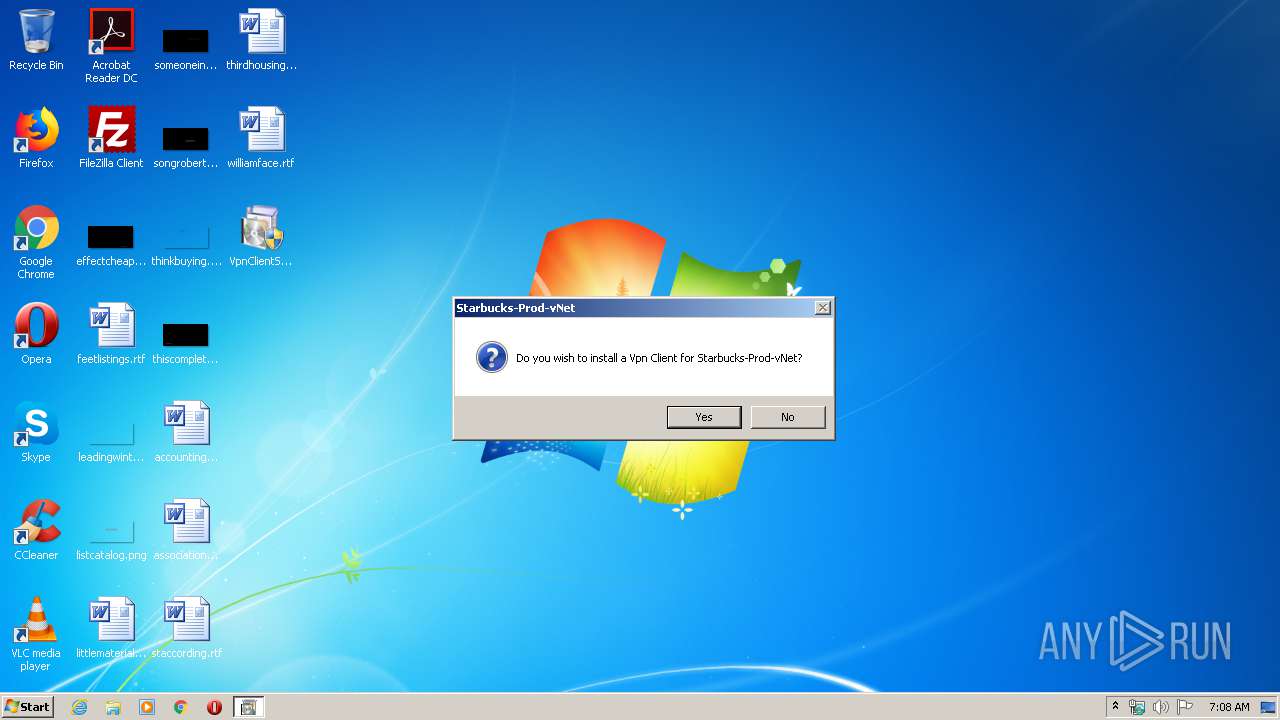
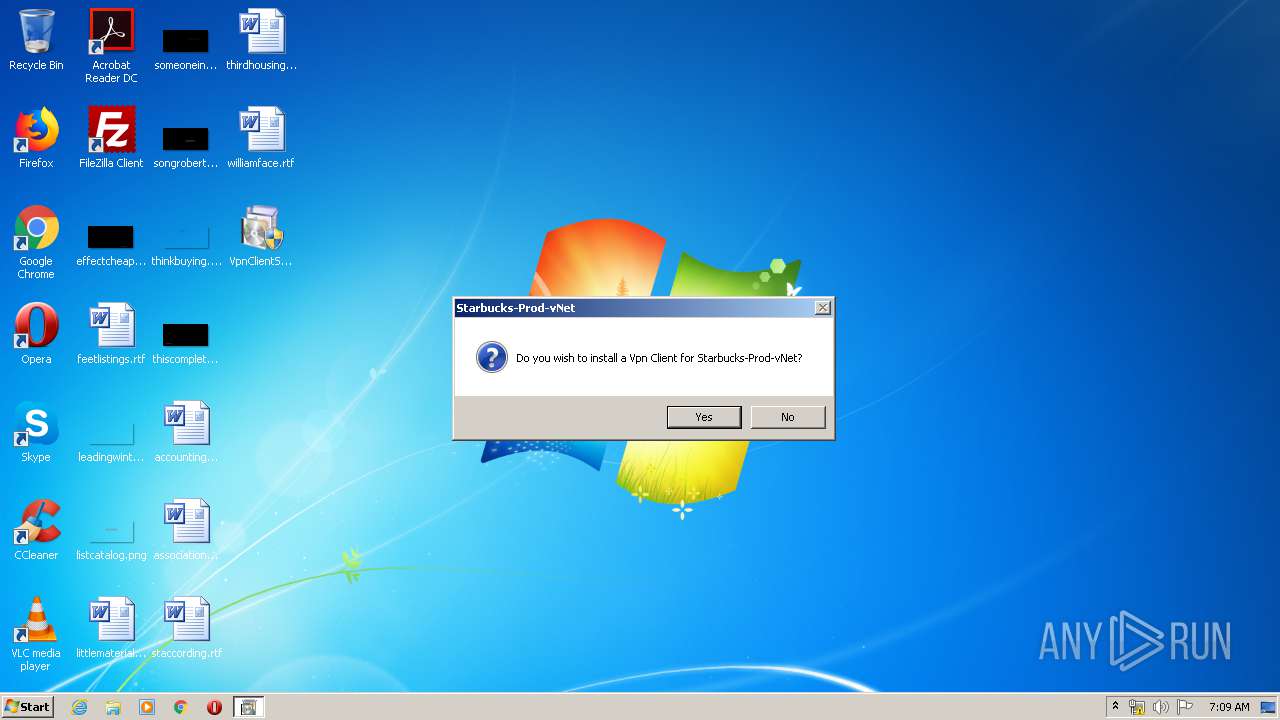
| 1736 | cmstp.exe /s /su /ns a01339dd-df25-4f51-99f7-97a3f1245854.inf | C:\Windows\system32\cmstp.exe | VpnClientSetupX86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Connection Manager Profile Installer Exit code: 1 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | cmd.exe /c certutil -addstore root %APPDATA%\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\a01339dd-df25-4f51-99f7-97a3f1245854.cer | C:\Windows\system32\cmd.exe | — | cmstp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\Desktop\VpnClientSetupX86.exe" | C:\Users\admin\Desktop\VpnClientSetupX86.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
| 2556 | reg add HKLM\SYSTEM\CurrentControlSet\Services\RasMan\PPP\EAP\13 /v SelectSelfSignedCert /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmstp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | cmstp.exe /s /su /ns a01339dd-df25-4f51-99f7-97a3f1245854.inf | C:\Windows\system32\cmstp.exe | VpnClientSetupX86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Connection Manager Profile Installer Exit code: 1 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | certutil -addstore root C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\a01339dd-df25-4f51-99f7-97a3f1245854.cer | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
96
Read events
42
Write events
50
Delete events
4
Modification events
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CMSTP |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1384) VpnClientSetupX86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Connection Manager |
| Operation: | write | Name: | ProfileInstallPath |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | SM_AccessoriesName |
Value: Accessories | |||
| (PID) Process: | (1736) cmstp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | PF_AccessoriesName |
Value: Accessories | |||
Executable files
5
Suspicious files
5
Text files
142
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD53B.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD54C.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD54D.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD55E.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD55F.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD56F.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD570.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD581.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | cmstp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\Cm\a01339dd-df25-4f51-99f7-97a3f1245854\SETD582.tmp | — | |
MD5:— | SHA256:— | |||
| 1384 | VpnClientSetupX86.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\a01339dd-df25-4f51-99f7-97a3f1245854.cmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report