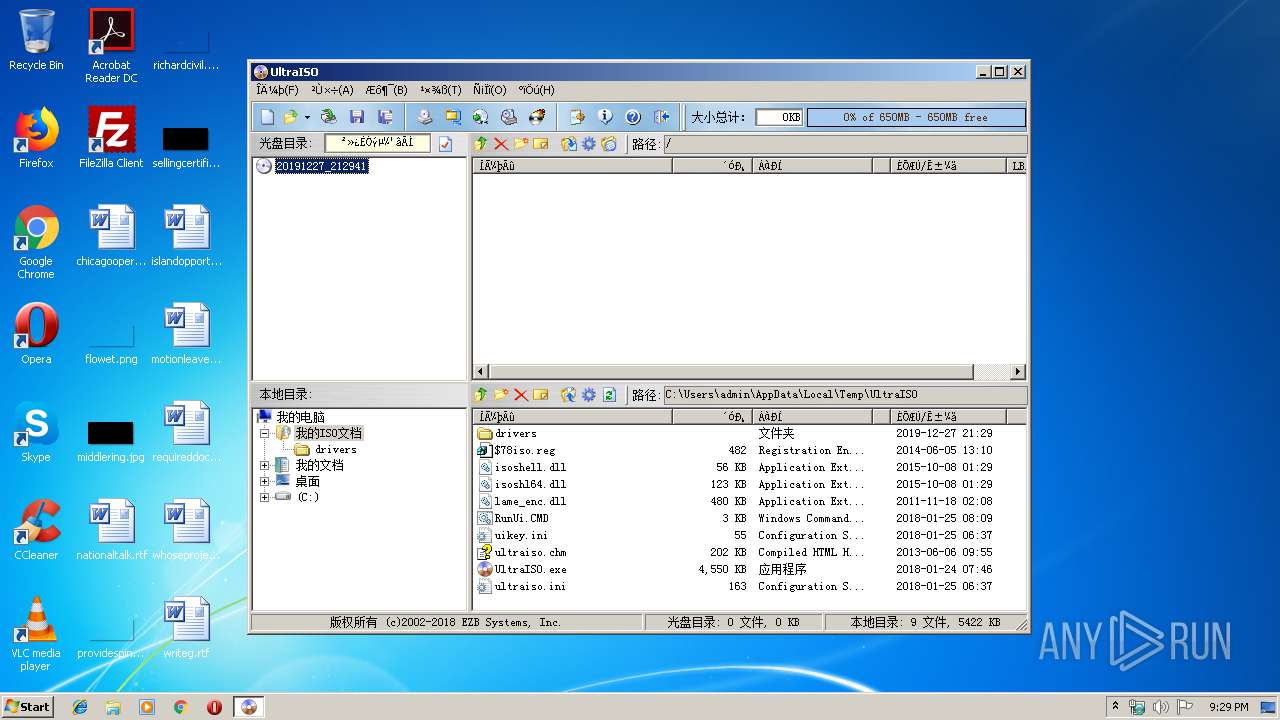
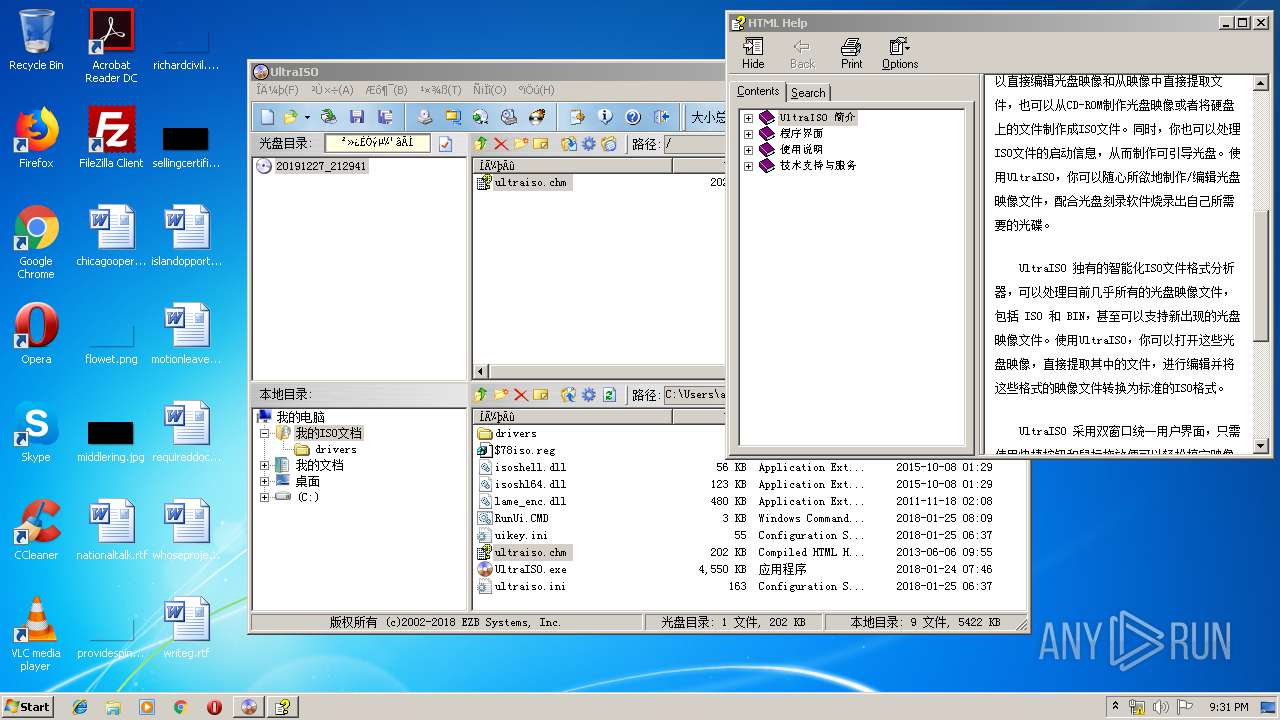
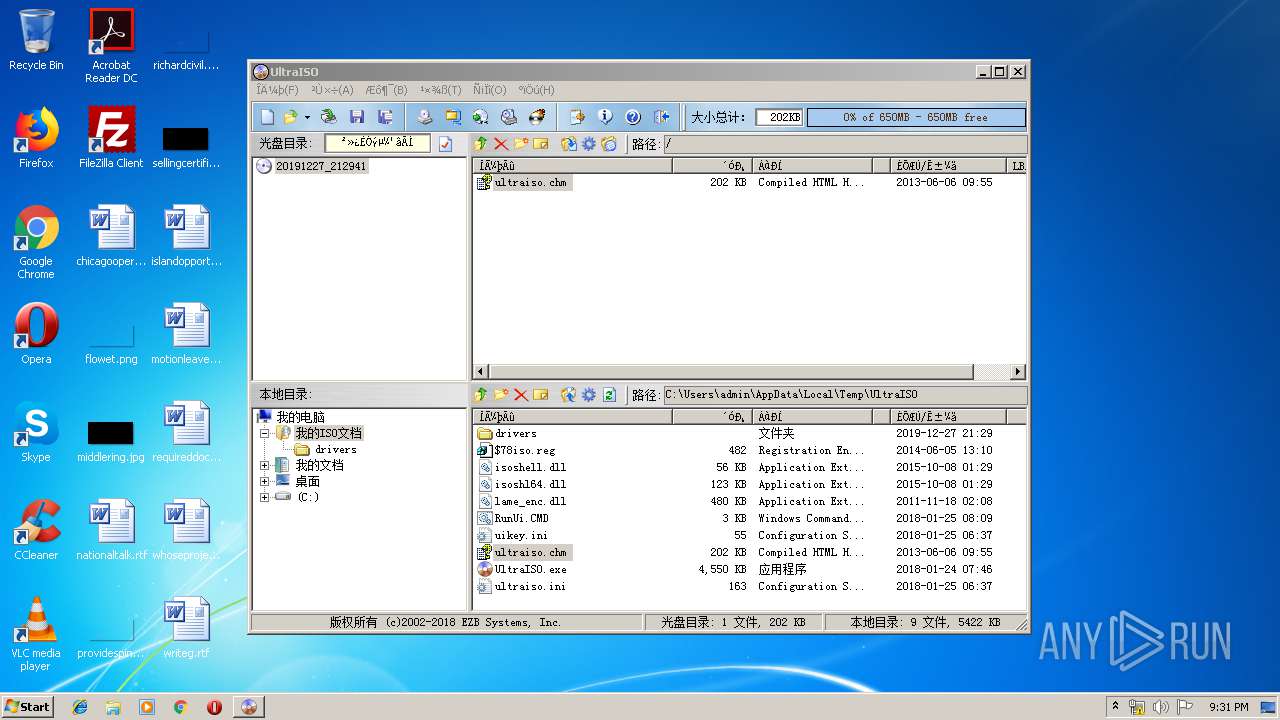
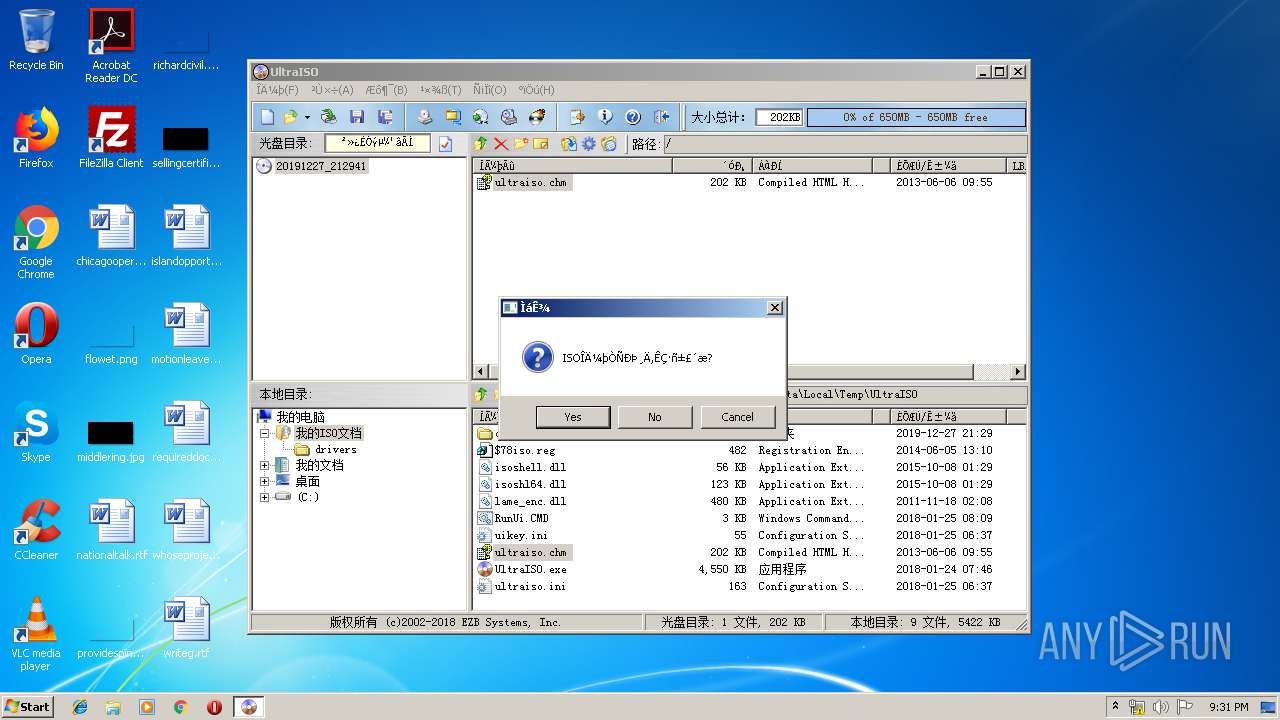
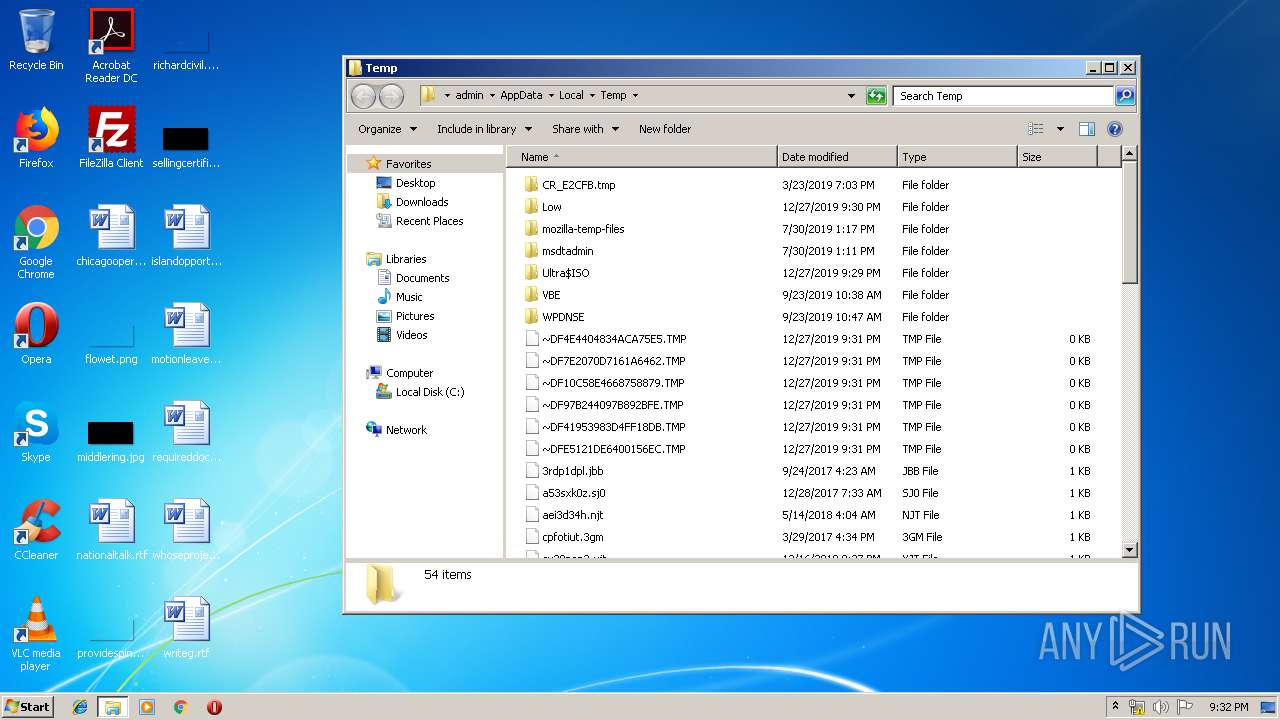
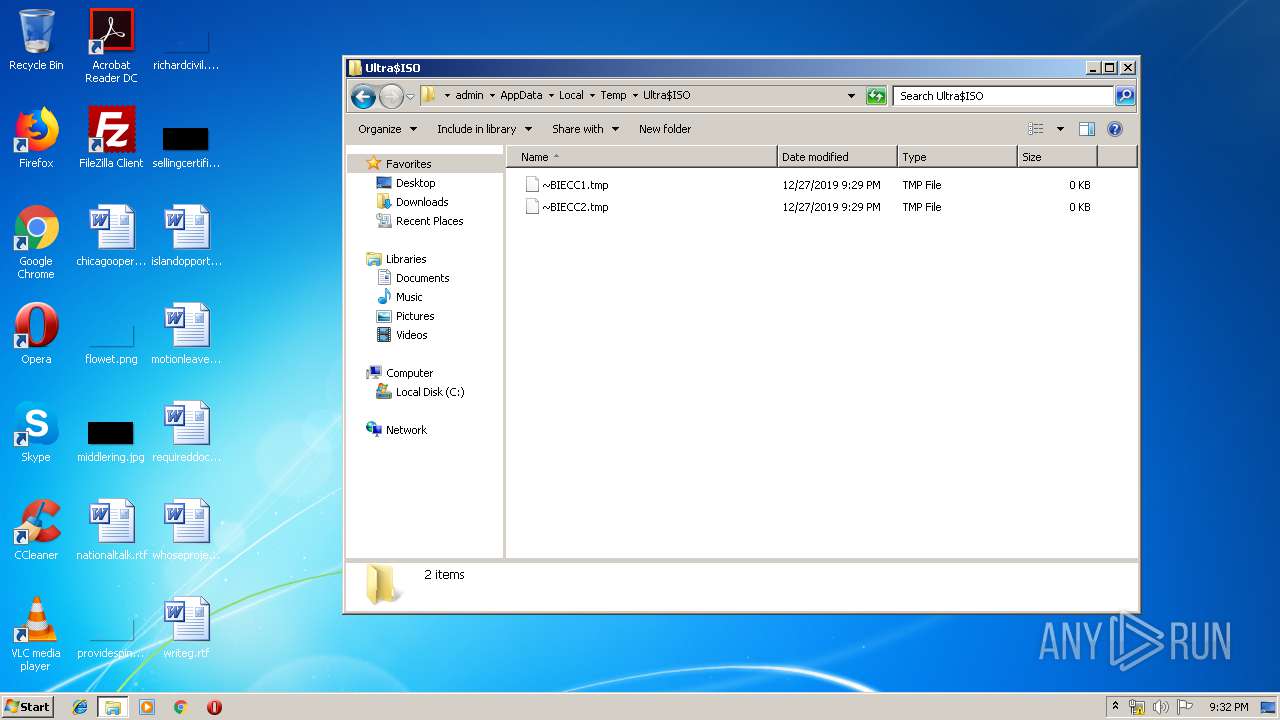
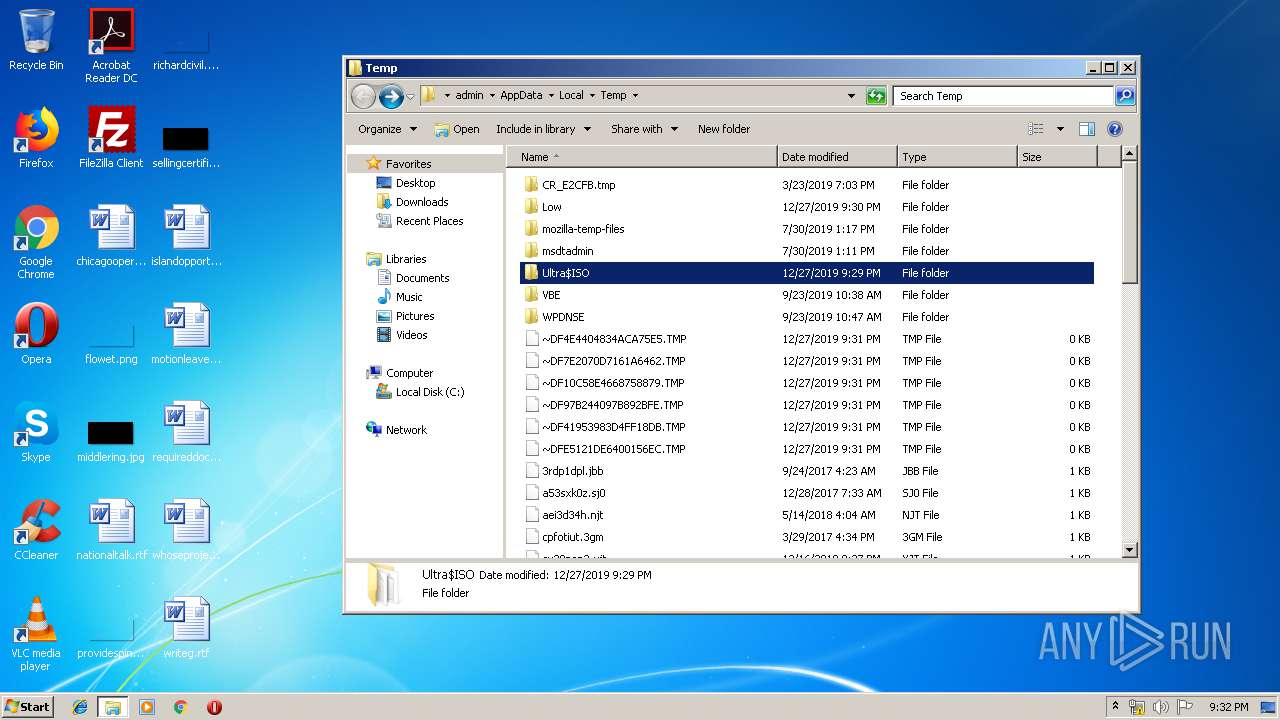
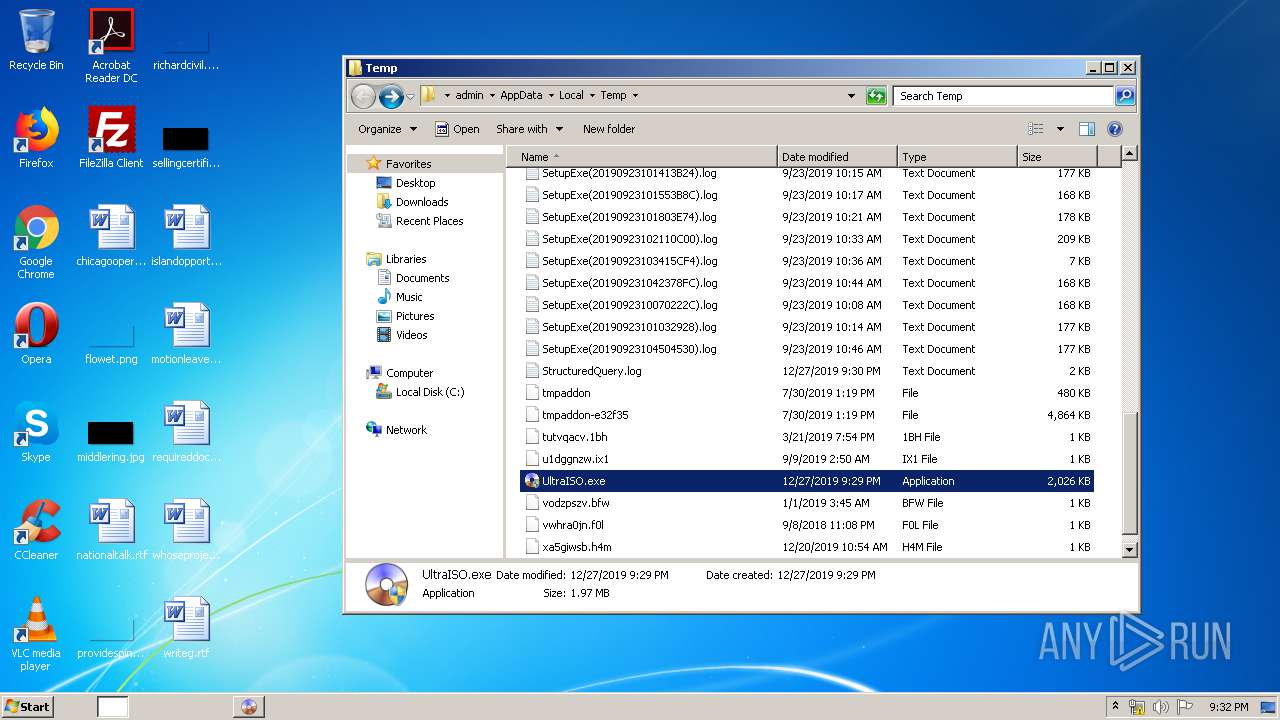
| File name: | UltraISO.exe |
| Full analysis: | https://app.any.run/tasks/b4ebbaf0-7edc-4374-8a3e-0007f305f56e |
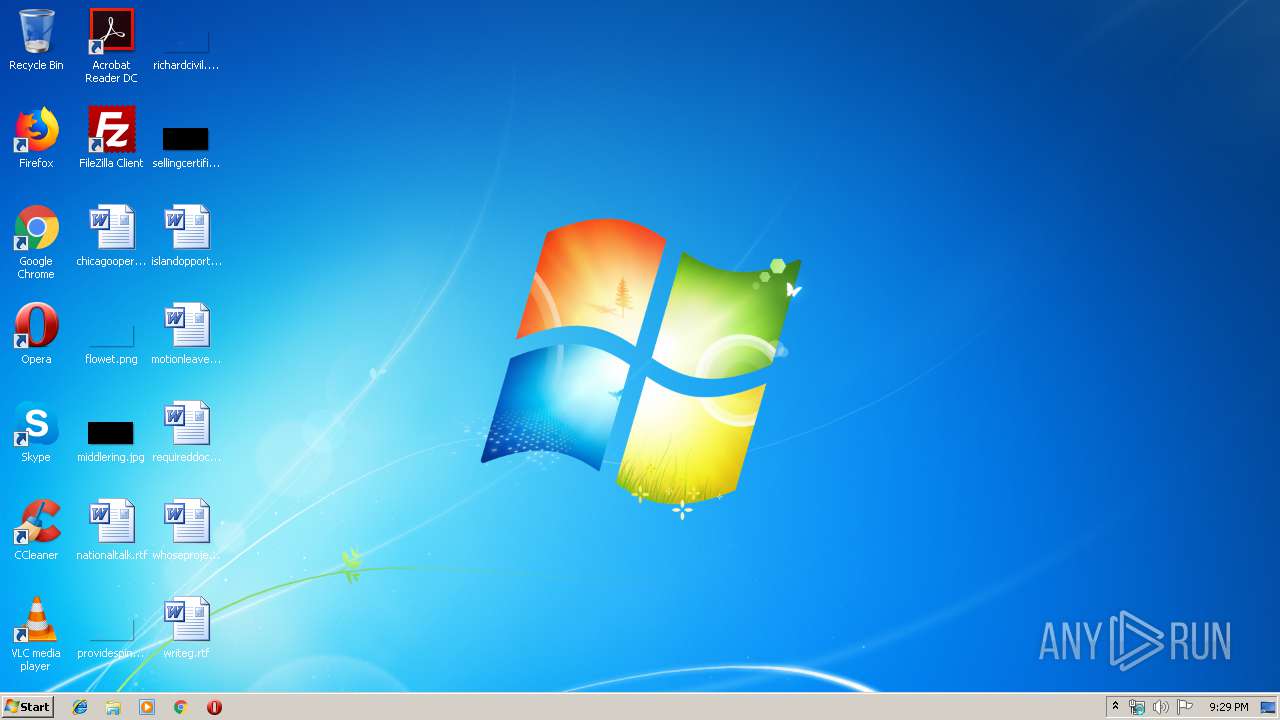
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2019, 21:29:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0B4B5D2AC481ADC154934288AB68B3C7 |
| SHA1: | 4550ED3E49CA74FA888F83F64B986095E1AEEA59 |
| SHA256: | 4782DD3C66AFE7BC5369290F84B2BEC6A5413653F6517ABCB841993B31DF0723 |
| SSDEEP: | 49152:svJdigE83sbIIOfMjaSB8QKhwtLiHHeNjB/Pdr:svJdhOIYeu |
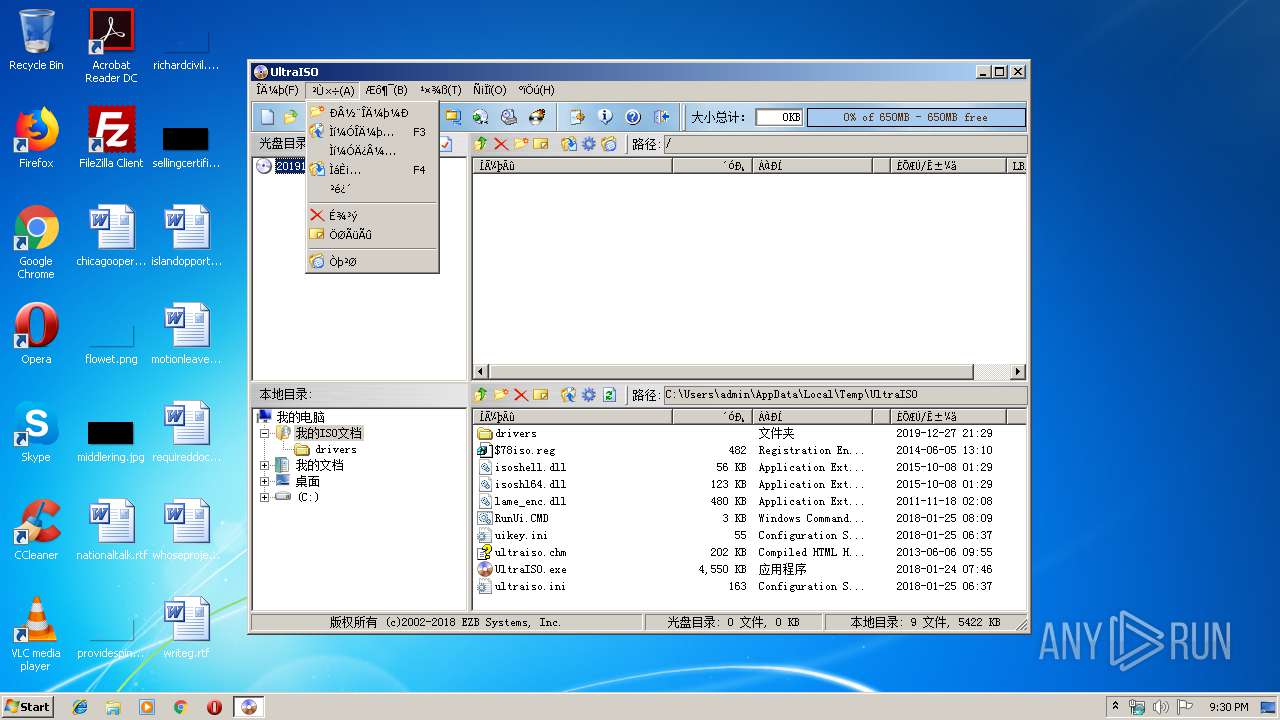
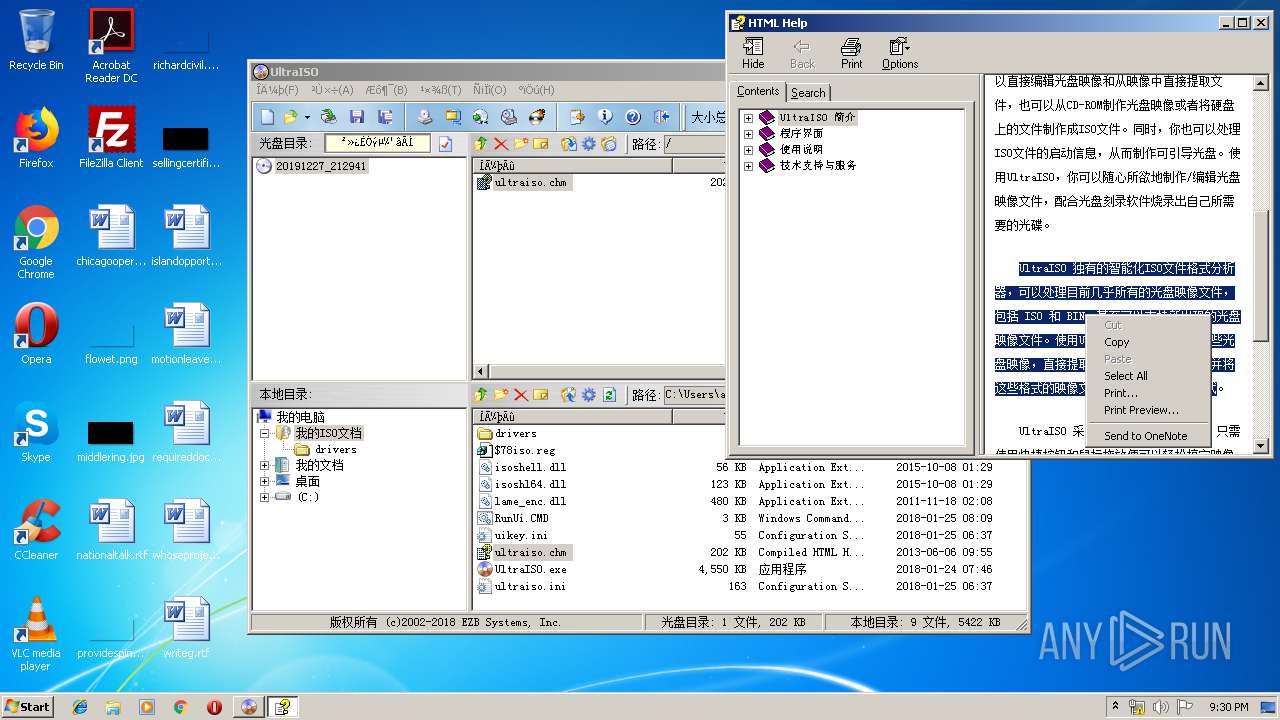
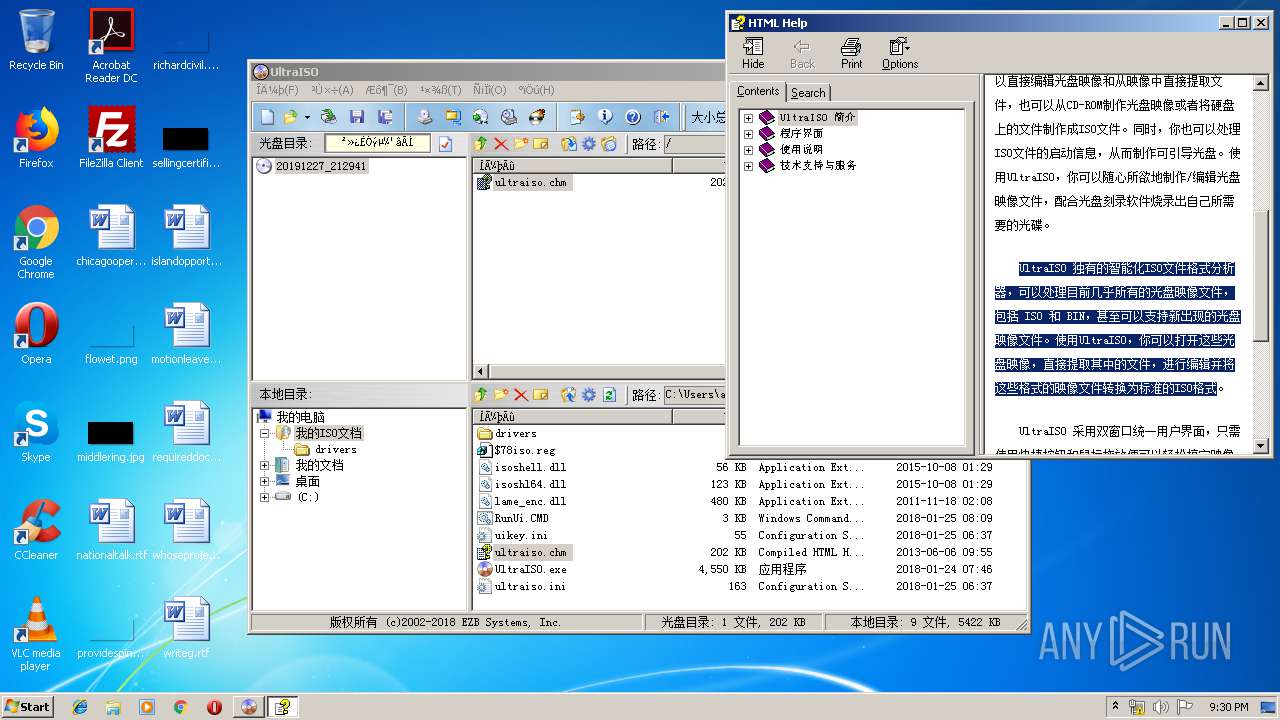
MALICIOUS
Loads dropped or rewritten executable
- UltraISO.exe (PID: 236)
Application was dropped or rewritten from another process
- UltraISO.exe (PID: 236)
- IsoCmd.exe (PID: 2376)
- UltraISO.exe (PID: 3564)
SUSPICIOUS
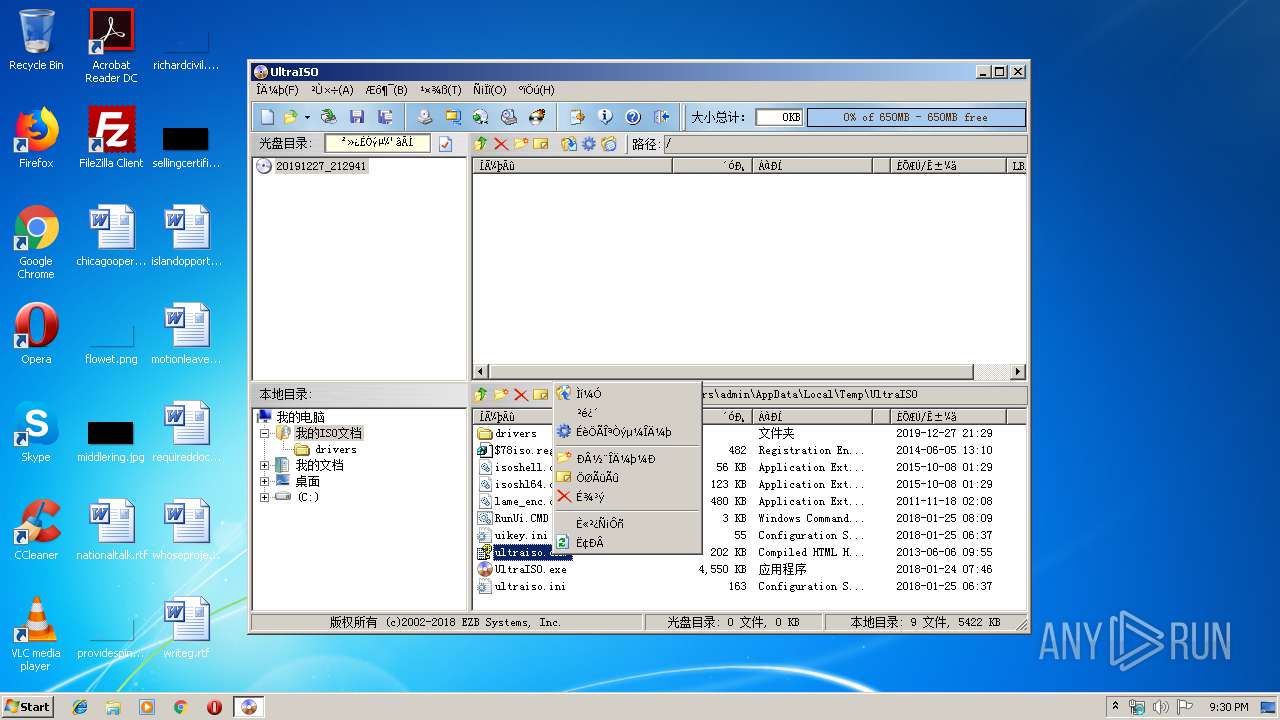
Executable content was dropped or overwritten
- UltraISO.exe (PID: 1732)
- UltraISO.exe (PID: 3520)
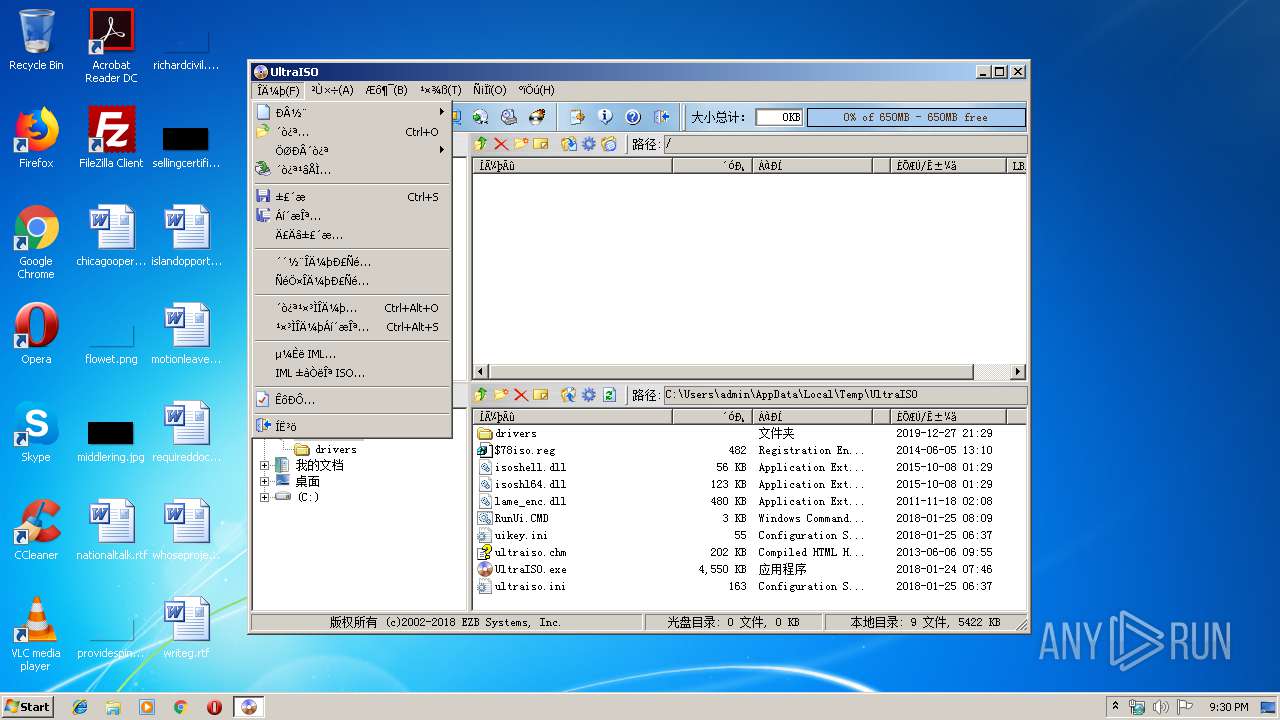
Modifies the open verb of a shell class
- cmd.exe (PID: 1972)
- cmd.exe (PID: 3152)
Starts CMD.EXE for commands execution
- UltraISO.exe (PID: 1732)
- cmd.exe (PID: 1972)
- cmd.exe (PID: 3152)
- UltraISO.exe (PID: 3520)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1972)
- cmd.exe (PID: 3152)
Application launched itself
- cmd.exe (PID: 1972)
- cmd.exe (PID: 3152)
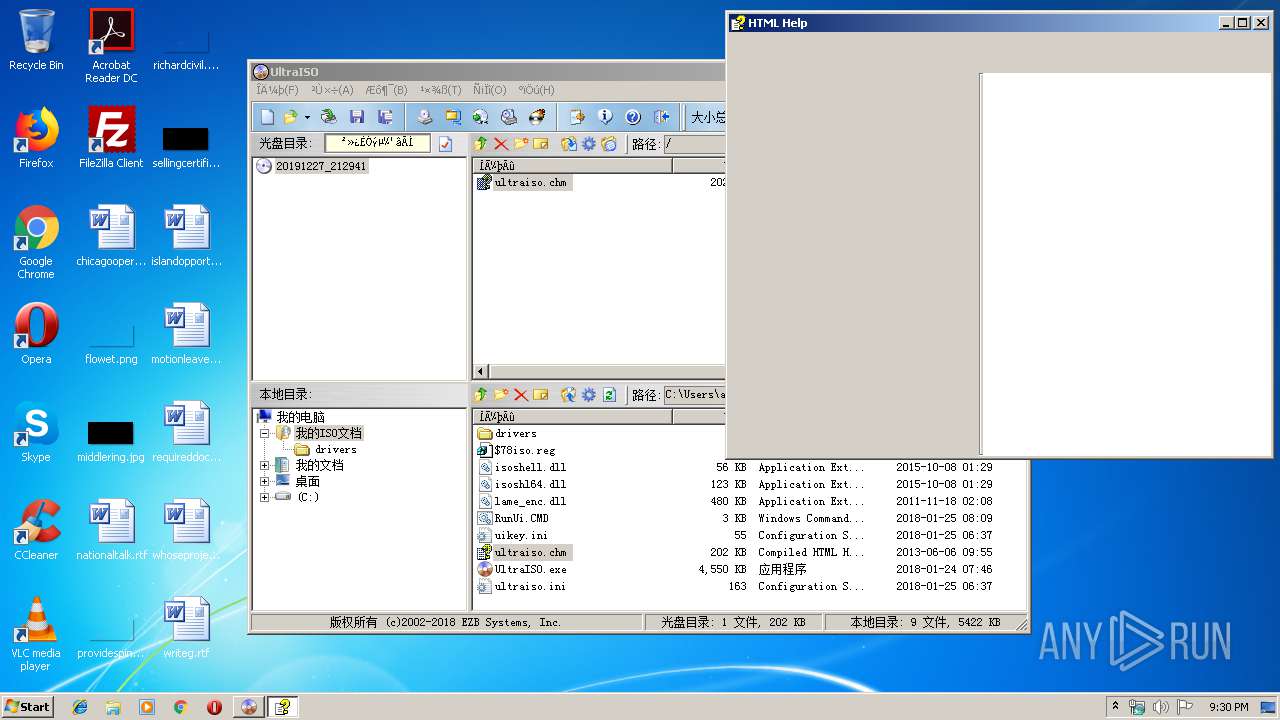
Reads internet explorer settings
- hh.exe (PID: 3692)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3040)
INFO
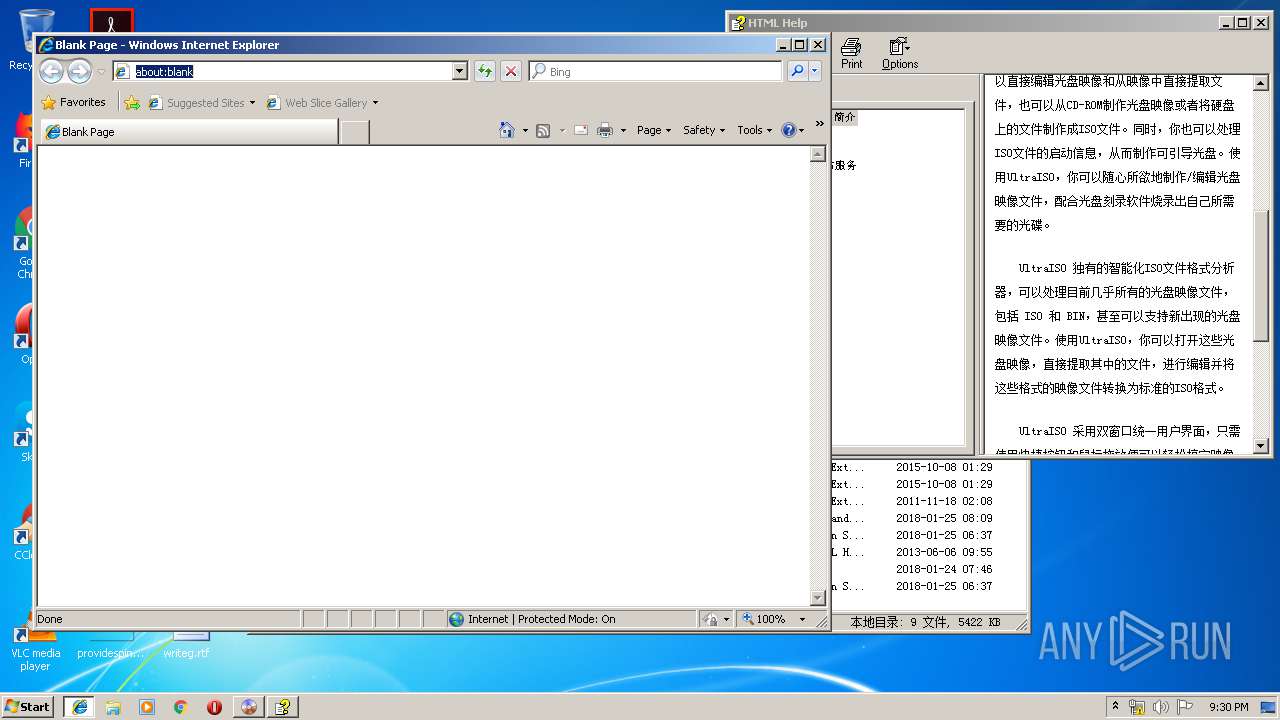
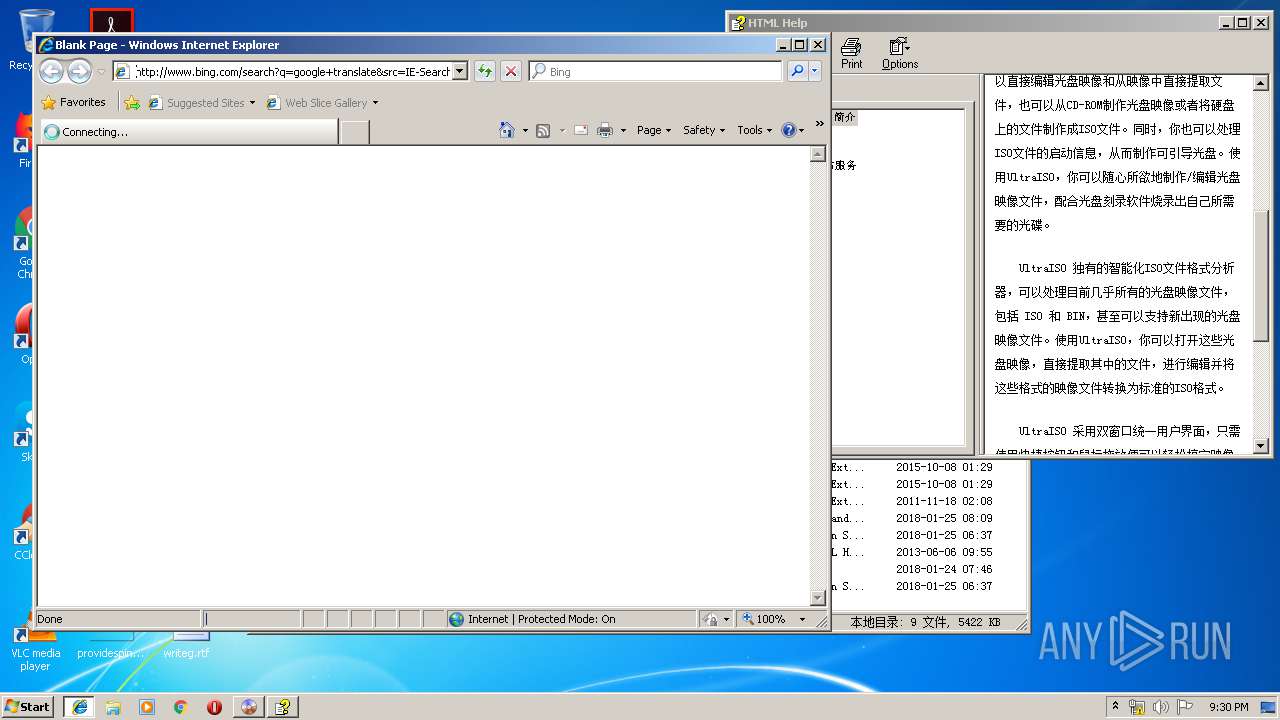
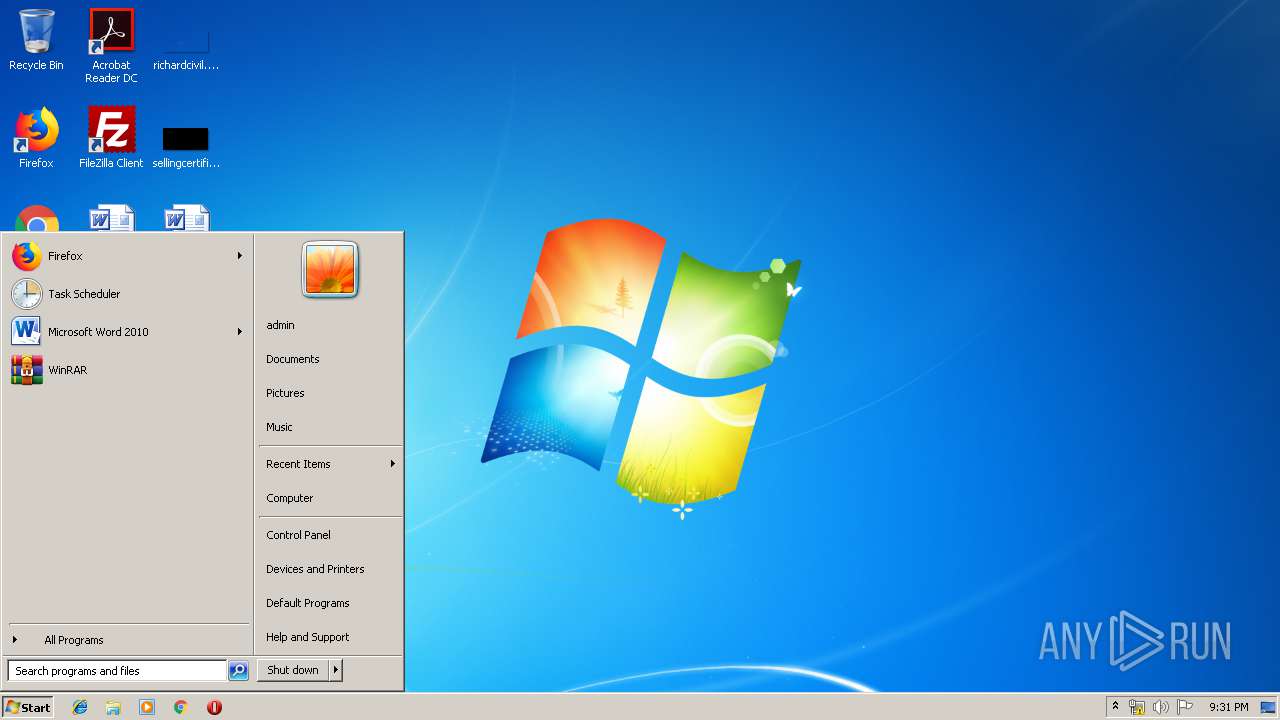
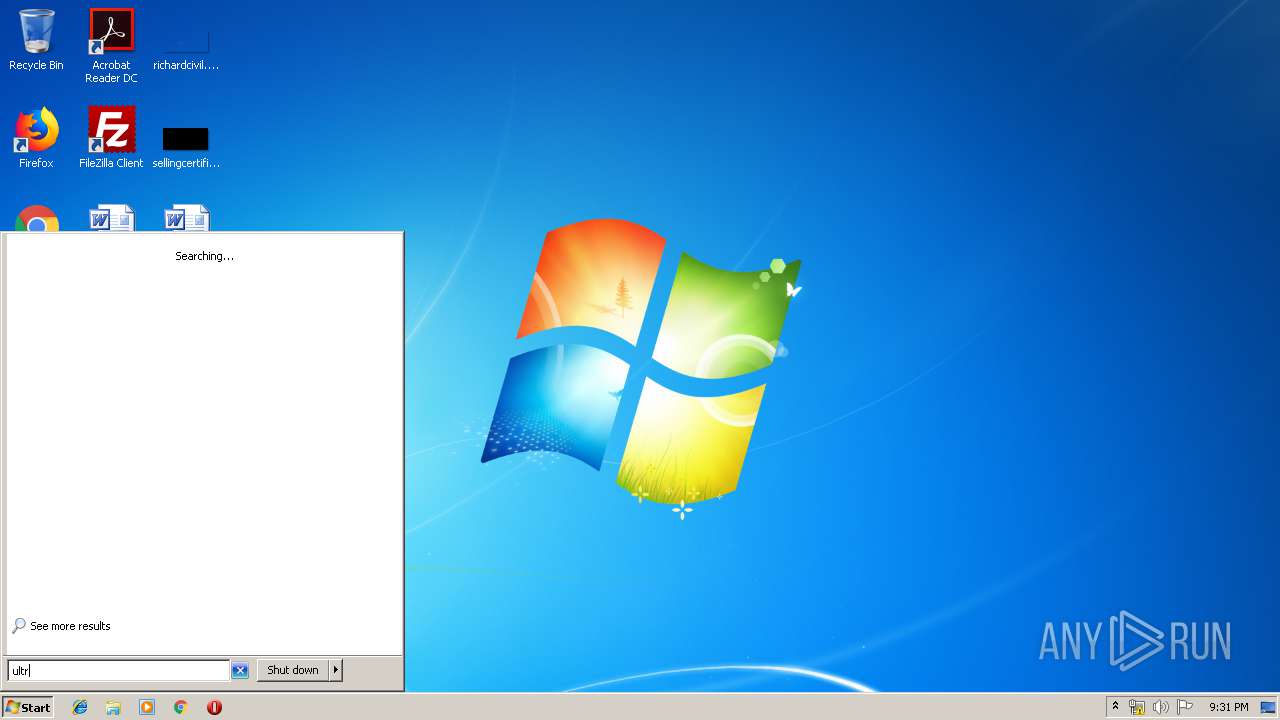
Manual execution by user
- iexplore.exe (PID: 3916)
- UltraISO.exe (PID: 3520)
- verclsid.exe (PID: 2060)
- UltraISO.exe (PID: 2748)
Changes internet zones settings
- iexplore.exe (PID: 3916)
Creates files in the user directory
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 584)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3040)
Reads Internet Cache Settings
- iexplore.exe (PID: 584)
Application launched itself
- iexplore.exe (PID: 3916)
Reads internet explorer settings
- iexplore.exe (PID: 584)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 584)
Reads settings of System Certificates
- iexplore.exe (PID: 584)
- iexplore.exe (PID: 3916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:05:24 17:16:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 72192 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x123df |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.7.1.3519 |
| ProductVersionNumber: | 9.7.1.3519 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
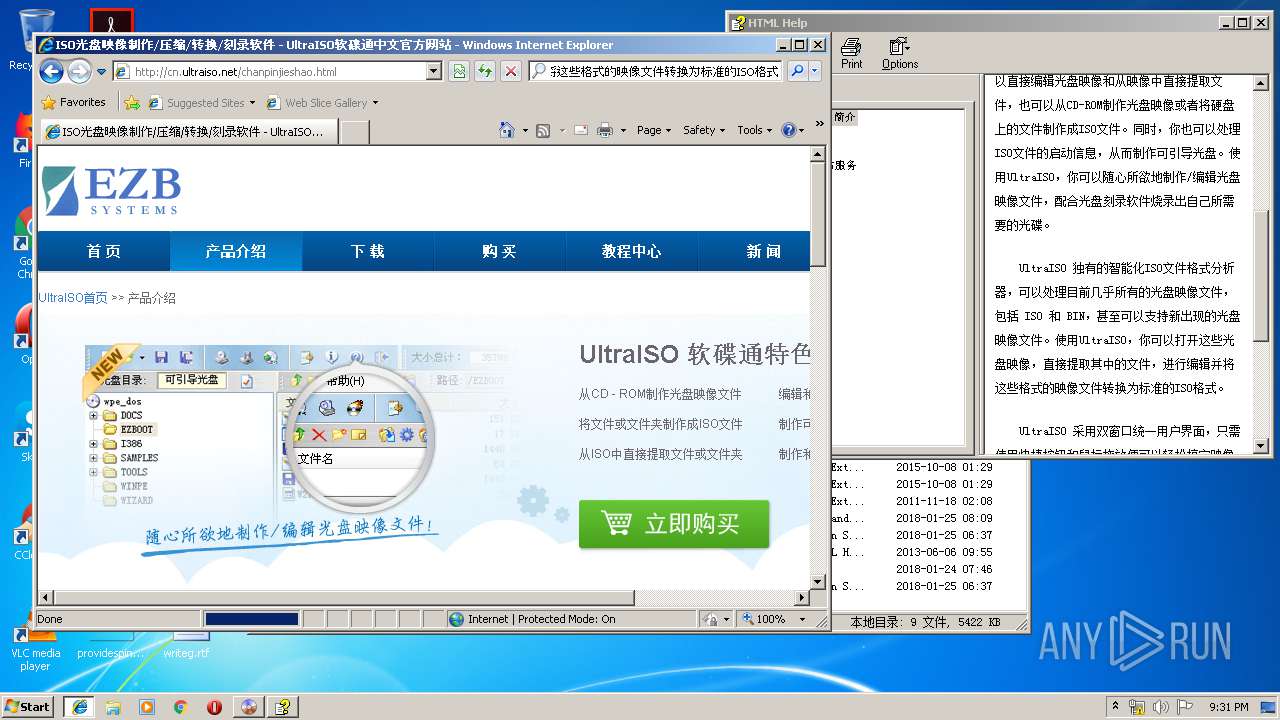
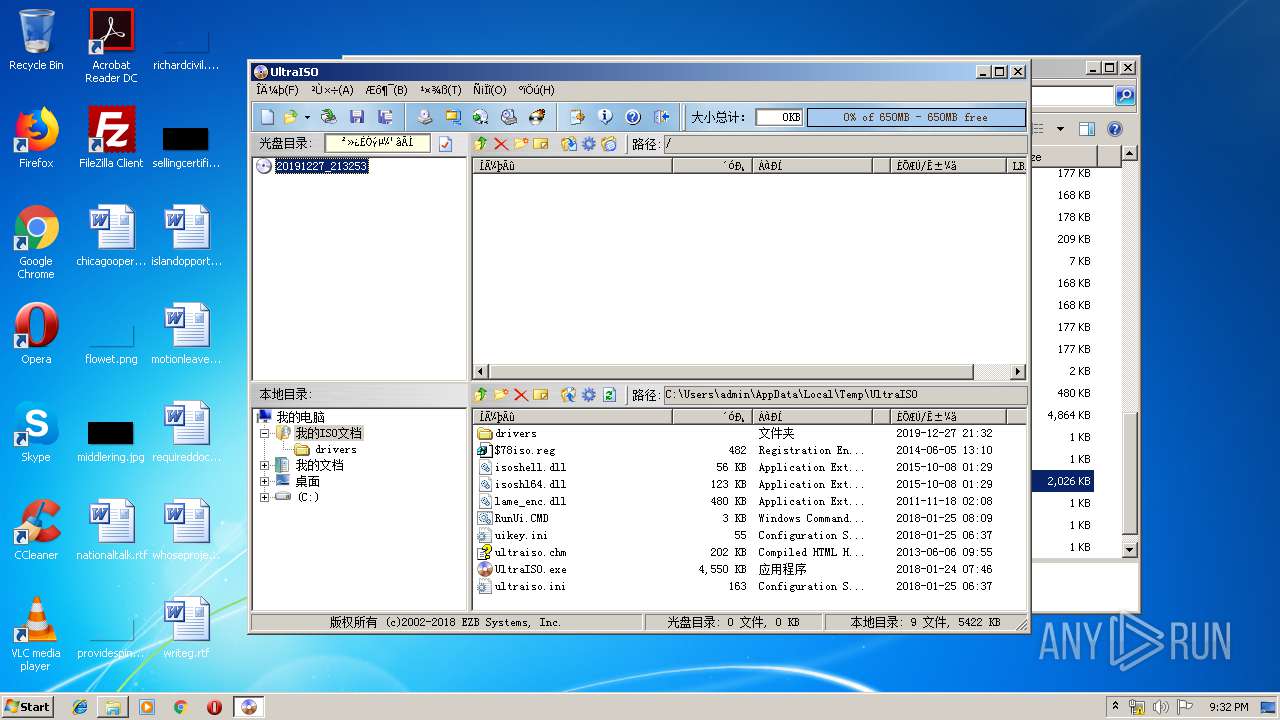
| CompanyName: | EZB Systems, Inc. |
| FileDescription: | UltraISO Premium |
| FileVersion: | 9.7.1.3519 |
| InternalName: | UltraISO |
| LegalCopyright: | Copyright (c) EZB Systems, Inc. |
| LegalTrademarks: | EZB(R) |
| OriginalFileName: | ultraiso.exe |
| ProductName: | UltraISO Premium |
| ProductVersion: | V9.71 |
| Comments: | http://www.ezbsystems.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-May-2011 15:16:01 |
| Detected languages: |
|
| CompanyName: | EZB Systems, Inc. |
| FileDescription: | UltraISO Premium |
| FileVersion: | 9.7.1.3519 |
| InternalName: | UltraISO |
| LegalCopyright: | Copyright (c) EZB Systems, Inc. |
| LegalTrademarks: | EZB(R) |
| OriginalFilename: | ultraiso.exe |
| ProductName: | UltraISO Premium |
| ProductVersion: | V9.71 |
| Comments: | http://www.ezbsystems.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 24-May-2011 15:16:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011913 | 0x00011A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57751 |
.rdata | 0x00013000 | 0x0000352C | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97569 |
.data | 0x00017000 | 0x0000296C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.68735 |
.rsrc | 0x0001A000 | 0x00004000 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.6233 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1279 | 1574 | Latin 1 / Western European | English - United States | RT_MANIFEST |
101 | 1.5789 | 20 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
103
Monitored processes
56
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Users\admin\AppData\Local\Temp\UltraISO\UltraISO.exe | C:\Users\admin\AppData\Local\Temp\UltraISO\UltraISO.exe | — | cmd.exe | |||||||||||
User: admin Company: EZB Systems, Inc. Integrity Level: HIGH Description: UltraISO Premium Exit code: 0 Version: 9.7.1.3519 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3916 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | regedit /s "C:\Users\admin\AppData\Local\Temp\UltraISO\$78iso.reg" | C:\Windows\regedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | reg export HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iso "C:\Users\admin\AppData\Local\Temp\UltraISO\$isoszr.reg" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | REG DELETE HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ISO\OpenWithProgids\ /v isoui /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | REG DELETE HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.isz /v Progid /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | REG DELETE HKCU\Software\Classes\.img /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | REG ADD HKCR\isoui\DefaultIcon /ve /t REG_SZ /d "C:\Users\admin\AppData\Local\Temp\UltraISO\UltraISO.EXE,0" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | REG DELETE HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iso /v Progid /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | REG.exe query "HKU\S-1-5-19" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 784
Read events
1 624
Write events
147
Delete events
13
Modification events
| (PID) Process: | (1732) UltraISO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1732) UltraISO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\isoui\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\UltraISO\UltraISO.EXE,0 | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.iso |
| Operation: | write | Name: | |
Value: isoui | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 74 | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.isz |
| Operation: | write | Name: | |
Value: isoui | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 75 | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.img |
| Operation: | write | Name: | |
Value: isoui | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 76 | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ima |
| Operation: | write | Name: | |
Value: isoui | |||
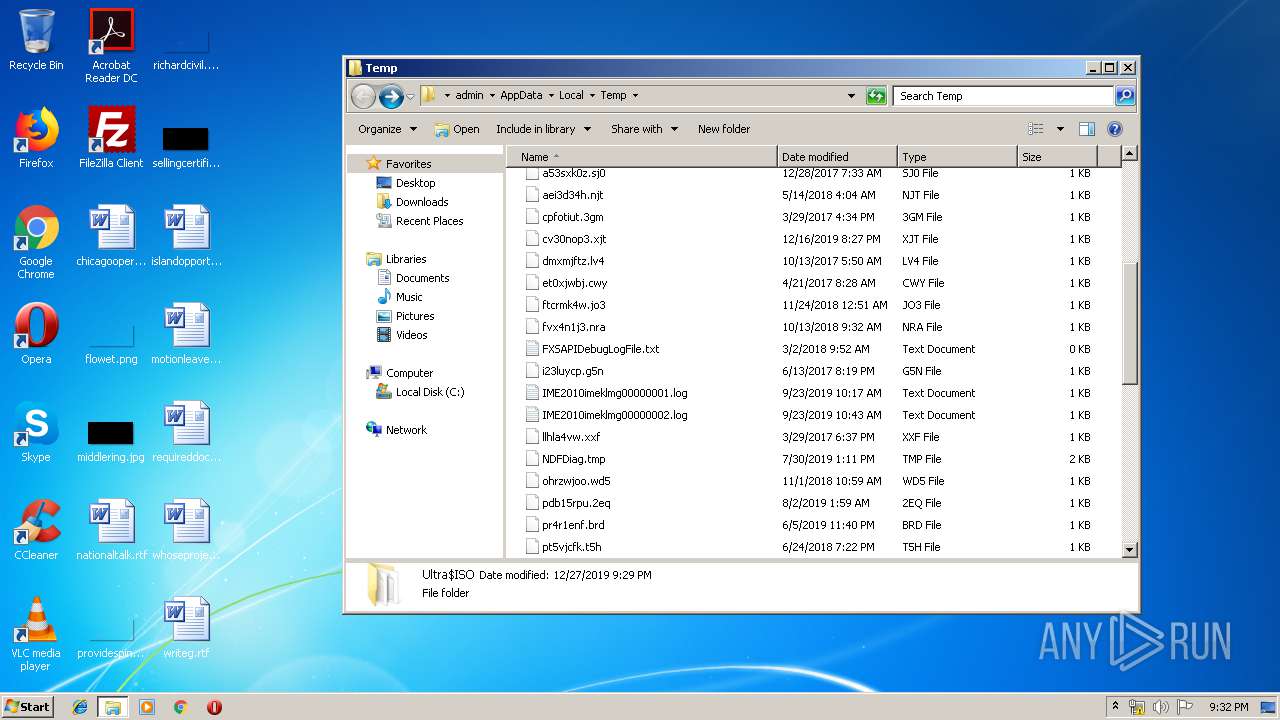
Executable files
20
Suspicious files
4
Text files
91
Unknown types
18
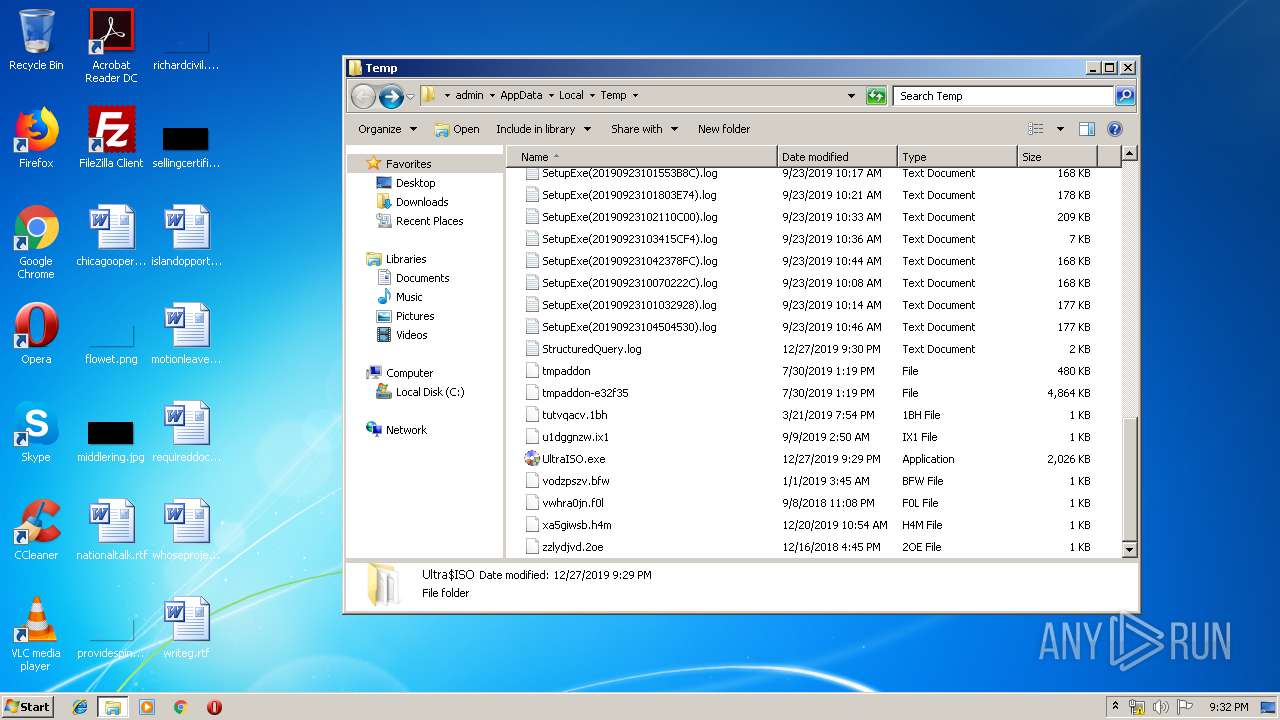
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | UltraISO.exe | C:\Users\admin\AppData\Local\Temp\UltraISO\$78iso.reg | text | |
MD5:E0A999E9F61E7CF24AD1126C793CE45F | SHA256:47C3D02B78A71CF87A02B266737D525F70B73542B3D925242C0608B3CFF71B80 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1732 | UltraISO.exe | C:\Users\admin\AppData\Local\Temp\UltraISO\RunUi.CMD | text | |
MD5:267CF6DDD29E6B7C91E4F4B8DBE41E7B | SHA256:5FDEC504E7D1EE81E86D7DE8A6CC0AC2D3F422938B38E3B4F23C516A5498B31A | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1732 | UltraISO.exe | C:\Users\admin\AppData\Local\Temp\UltraISO\ultraiso.ini | text | |
MD5:1BB103A691704859B45FFEAAD3A49D34 | SHA256:8D4E30EBDDAFBD7BADF585ADD1BA61FC620F1CDA6C885C5DAC08FA40CD3D880A | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:E392333BAC2B9F26CE680603B89CBD3E | SHA256:30B3F264FBBFA19955D2A9076E82B00819660DC5DE0F151131314C032C04833B | |||
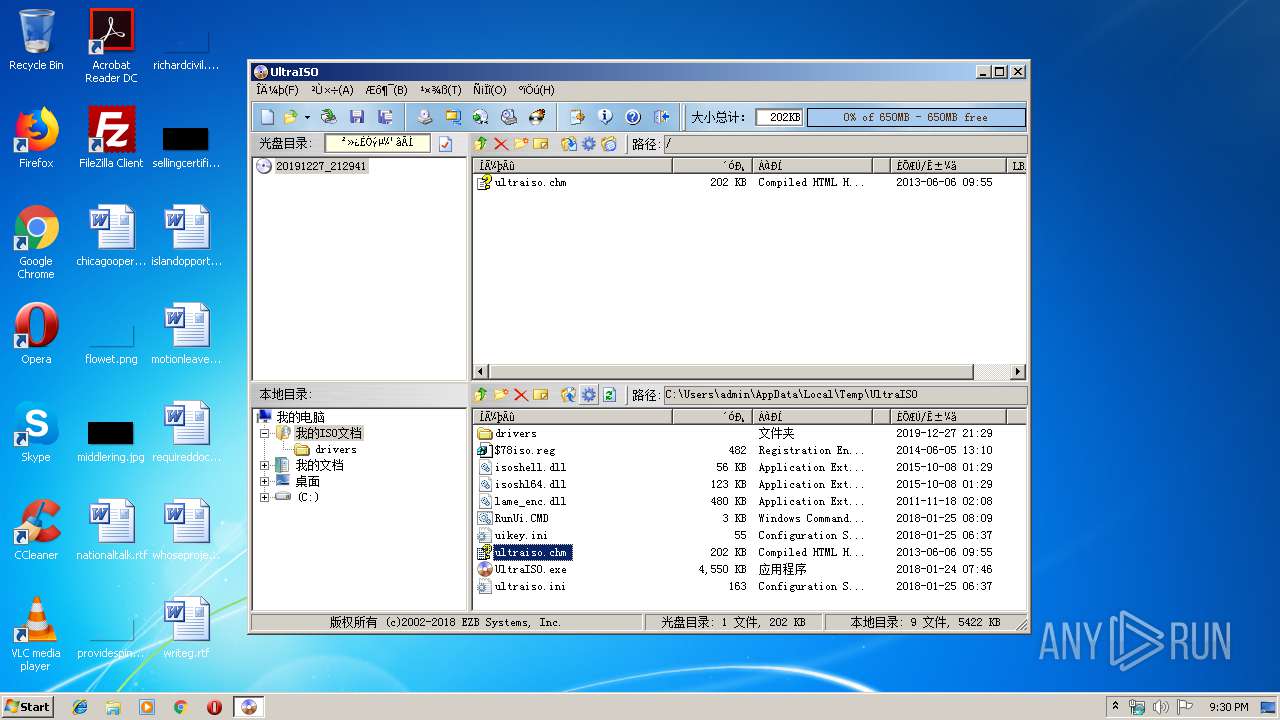
| 1732 | UltraISO.exe | C:\Users\admin\AppData\Local\Temp\UltraISO\ultraiso.chm | chm | |
MD5:BB10359A30004BCA489BC091E6FF1C60 | SHA256:173DB8B3F2132E1862EBA21AB92EEA0847FE538DCB9968F321E1EDD59D0FE469 | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\JF3LH4II\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 1732 | UltraISO.exe | C:\Users\admin\AppData\Local\Temp\UltraISO\uikey.ini | text | |
MD5:5B41019CB21245DFFEBA2994A9DB2BCE | SHA256:37D2A73EF8B0FD7E2B08FAA4F23C3419E053E910AF962F046E46236DBBF2F1BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
89
TCP/UDP connections
54
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3916 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
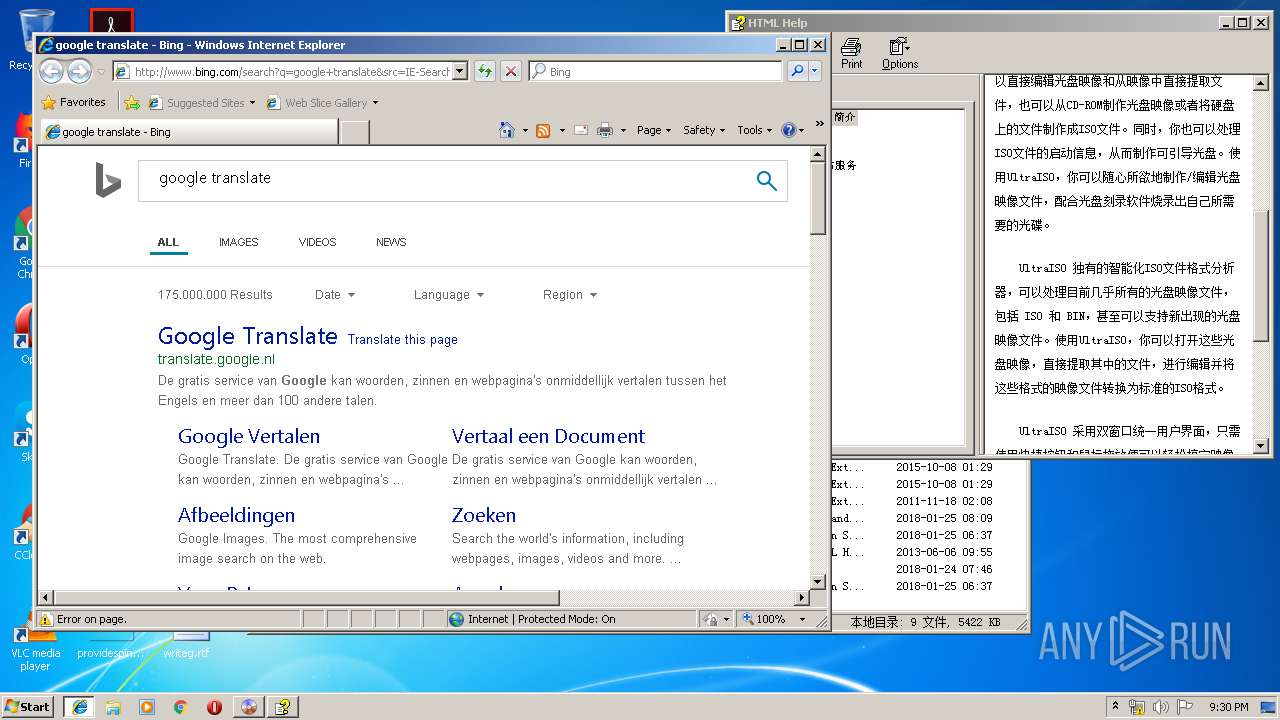
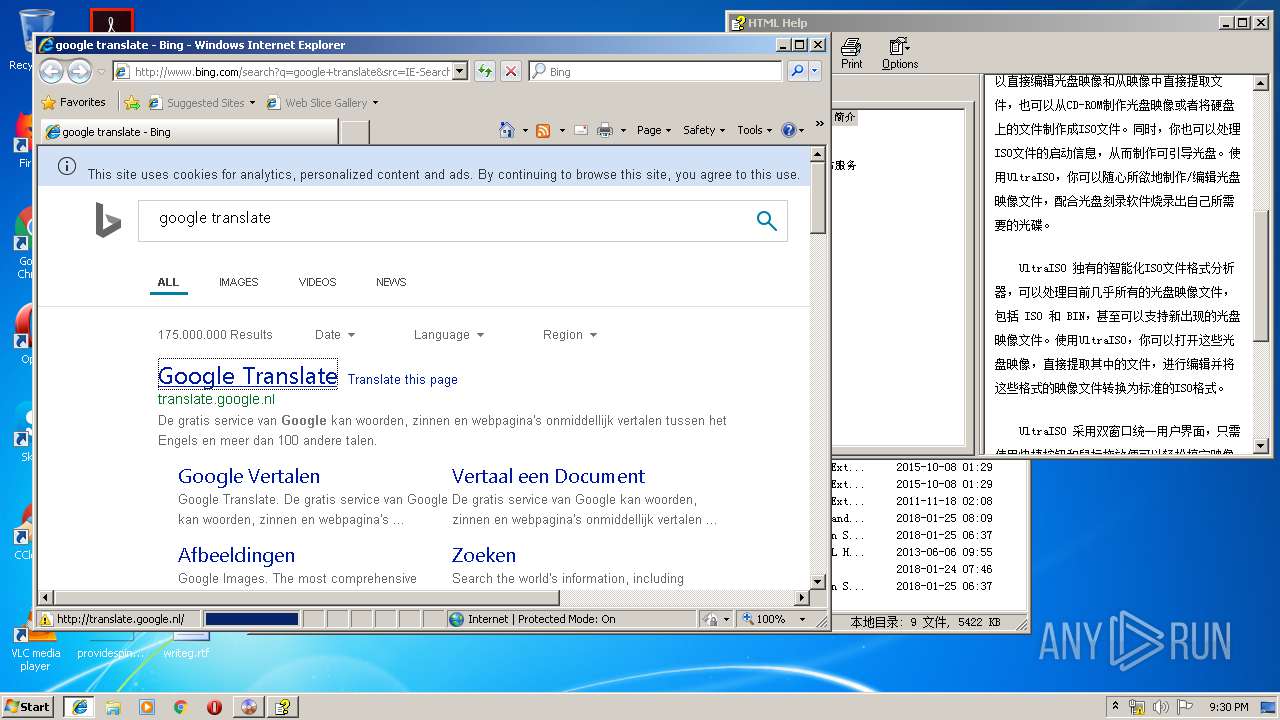
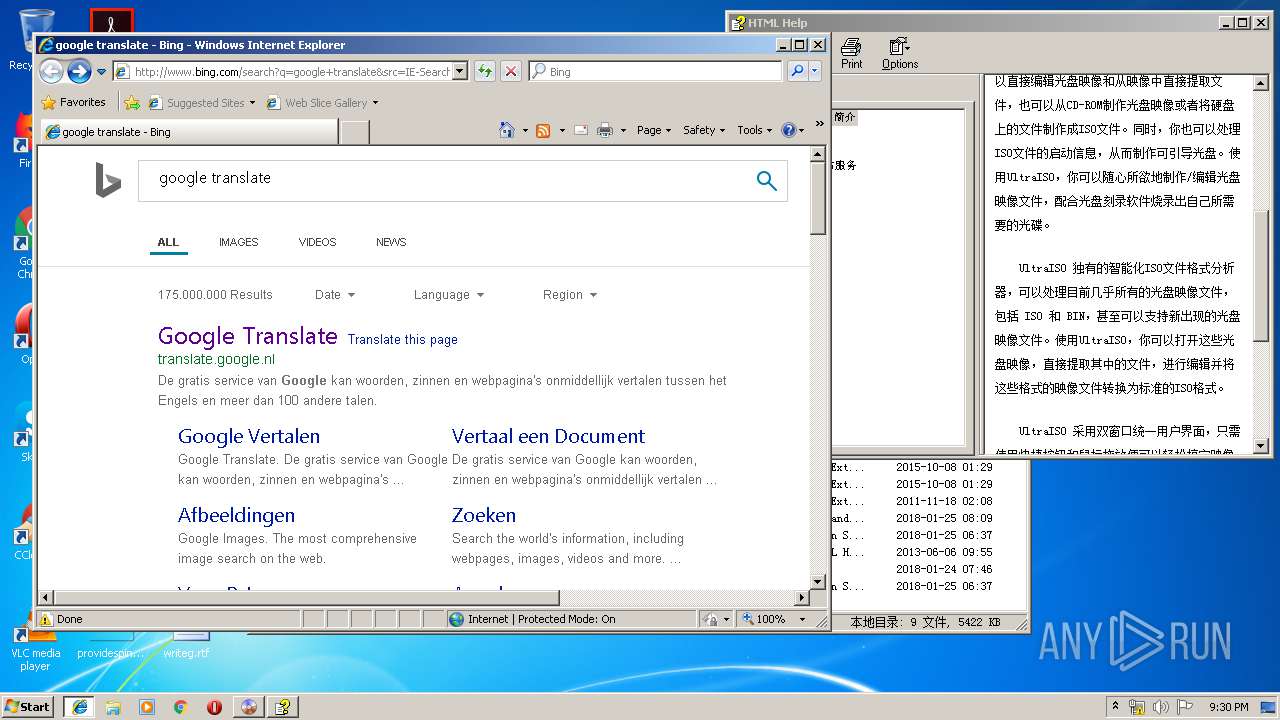
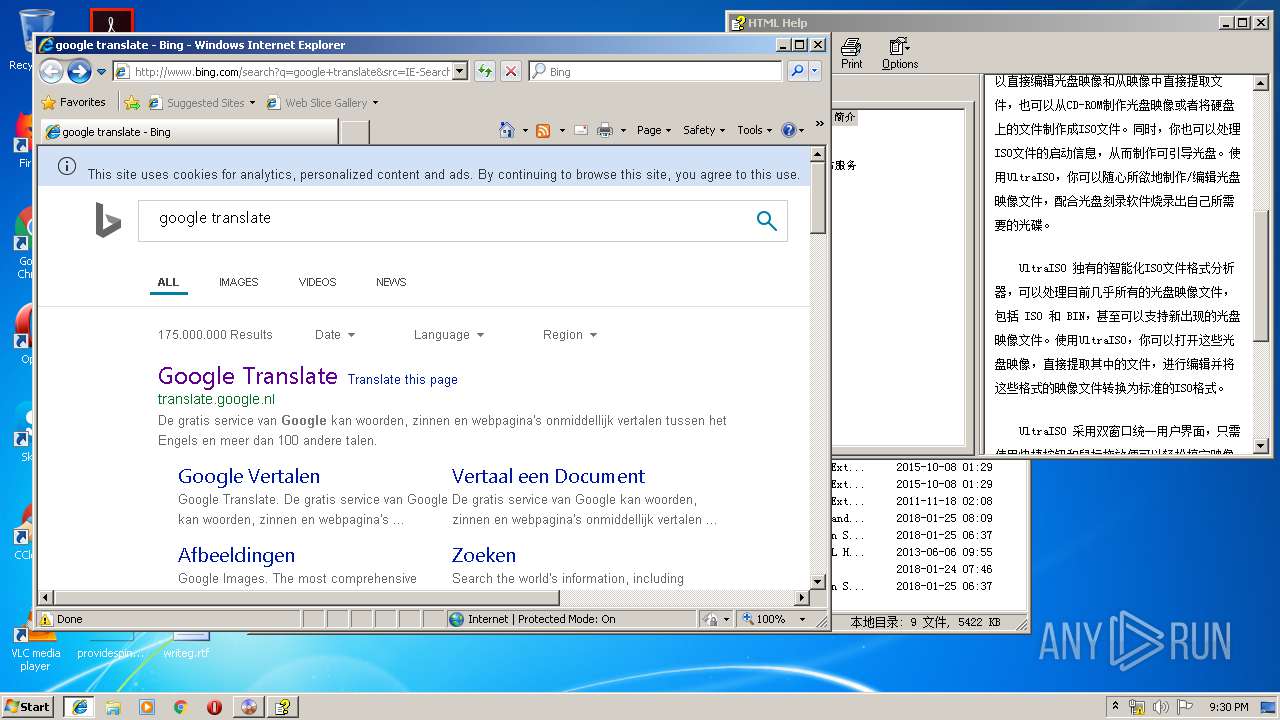
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=google+translate&src=IE-SearchBox&FORM=IE8SRC | US | html | 54.4 Kb | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.71 Kb | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5j/cj,nj/90d8aad0/88ef4561.js?bu=EpcgriDIH-AfjAXvH_EfxCDzH4Qg9h-wILcgoiCPH54eoR6SHw | US | text | 5.27 Kb | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=CD9E6E8DA2544FB29E004C3D9484E3C9&CID=01685B7F3BA161EF0F1355403A6B60FE&Type=Event.CPT&DATA={"pp":{"S":"L","FC":78,"BC":172,"SE":-1,"TC":-1,"H":247,"BP":303,"CT":327,"IL":6},"ad":[-1,-1,772,444,1089,498,0]}&P=SERP&DA=DUB02 | US | image | 5.71 Kb | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/27/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/2F/cj,nj/bf587ad6/f1d86b5a.js | US | text | 181 b | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/2n/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=CD9E6E8DA2544FB29E004C3D9484E3C9&CID=01685B7F3BA161EF0F1355403A6B60FE&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"Object%20doesn%27t%20support%20this%20property%20or%20method","Meta":"http%3A//www.bing.com/rs/6m/5m/cj%2Cnj/6e795a8b/1c156e04.js","Line":1,"Char":%20undefined}] | US | compressed | 1.81 Kb | whitelisted |
584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6m/5m/cj,nj/6e795a8b/1c156e04.js | US | text | 1.81 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3916 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
584 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
584 | iexplore.exe | 40.90.22.192:443 | login.live.com | Microsoft Corporation | US | malicious |
584 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
584 | iexplore.exe | 204.79.197.222:80 | aef1893a906064b20fbaa3d845af101a.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
584 | iexplore.exe | 52.231.32.10:80 | 31d4e2b3af494e0b24a78cc5b7618c47.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
584 | iexplore.exe | 13.107.42.10:80 | be8145f4a114cf179f8fe0cbe764ce46.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
584 | iexplore.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
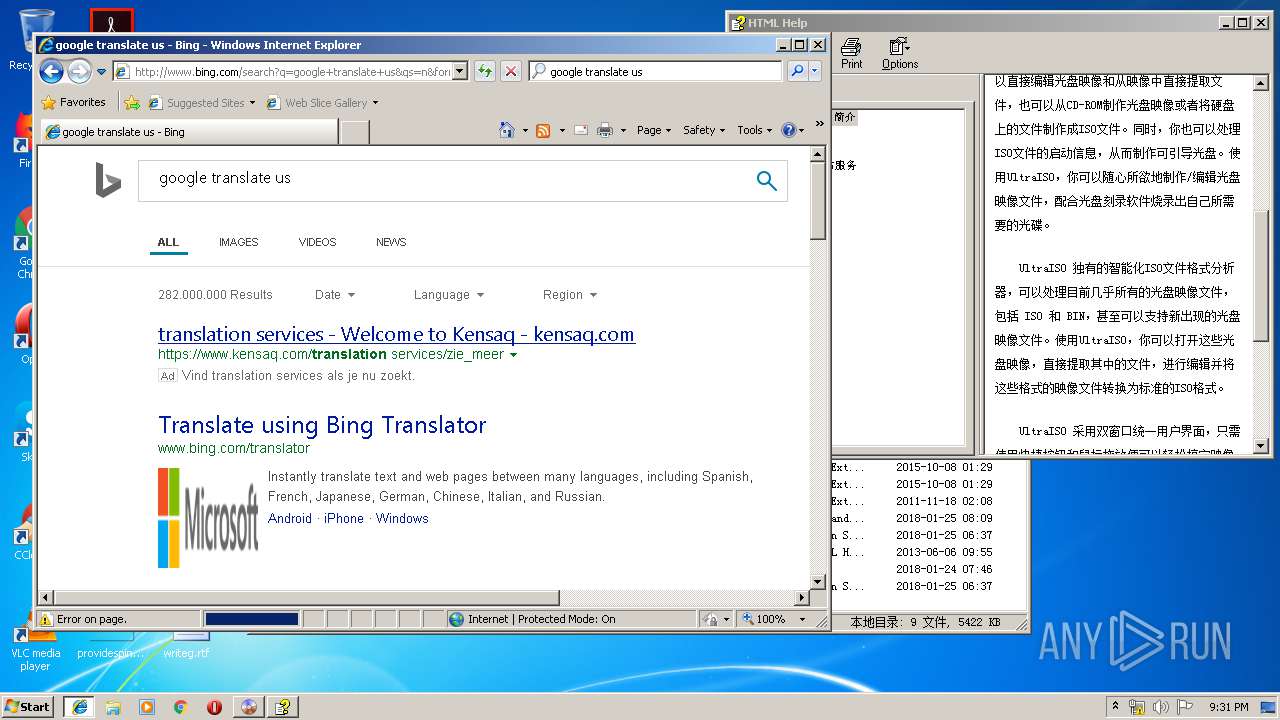
584 | iexplore.exe | 216.58.210.3:443 | translate.google.nl | Google Inc. | US | whitelisted |
584 | iexplore.exe | 216.58.210.3:80 | translate.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
aef1893a906064b20fbaa3d845af101a.clo.footprintdns.com |
| suspicious |
31d4e2b3af494e0b24a78cc5b7618c47.clo.footprintdns.com |
| unknown |
translate.google.nl |
| whitelisted |
be8145f4a114cf179f8fe0cbe764ce46.clo.footprintdns.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|