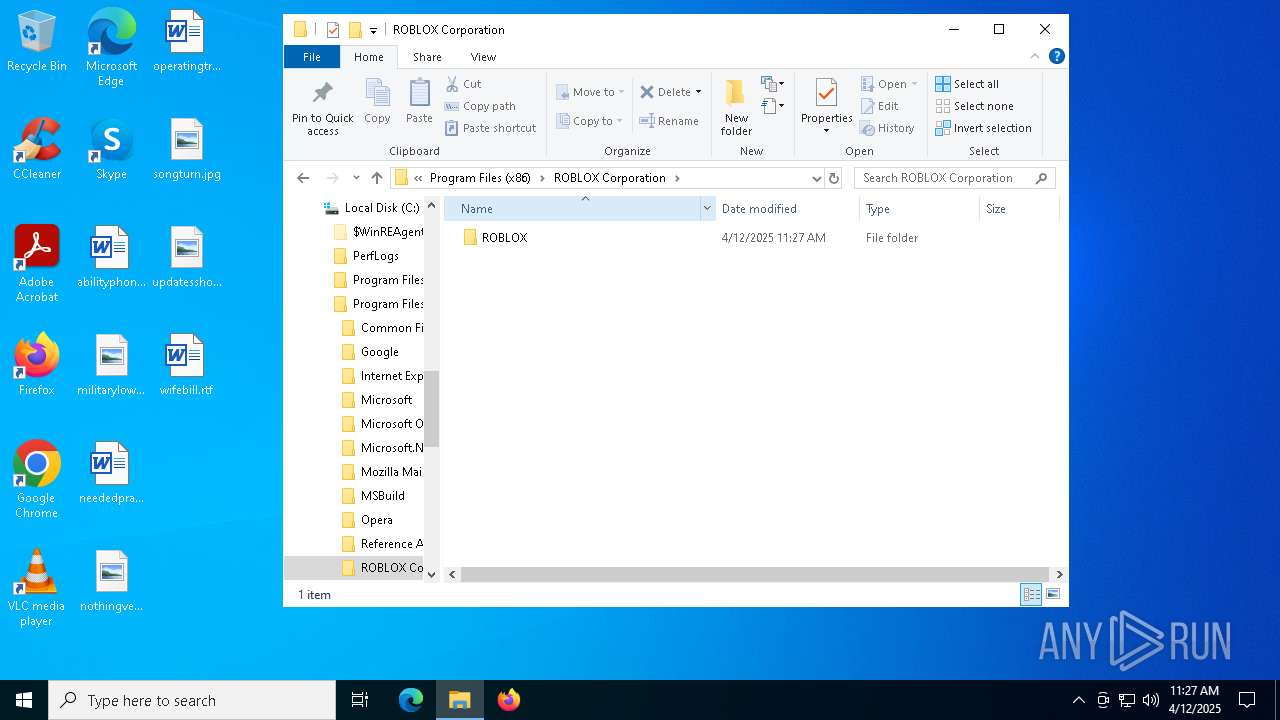
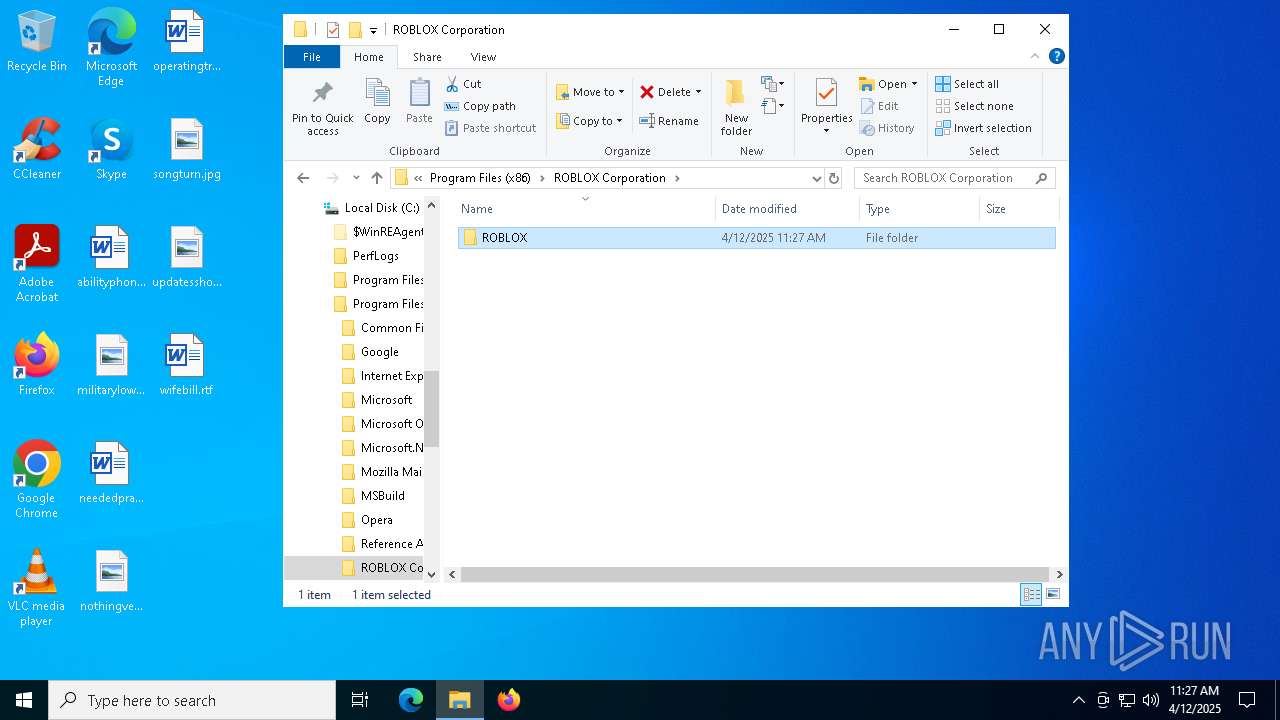
| File name: | ROBLOX.msi |
| Full analysis: | https://app.any.run/tasks/a00c4f66-9e73-401e-af16-43e458979c4c |
| Verdict: | Malicious activity |
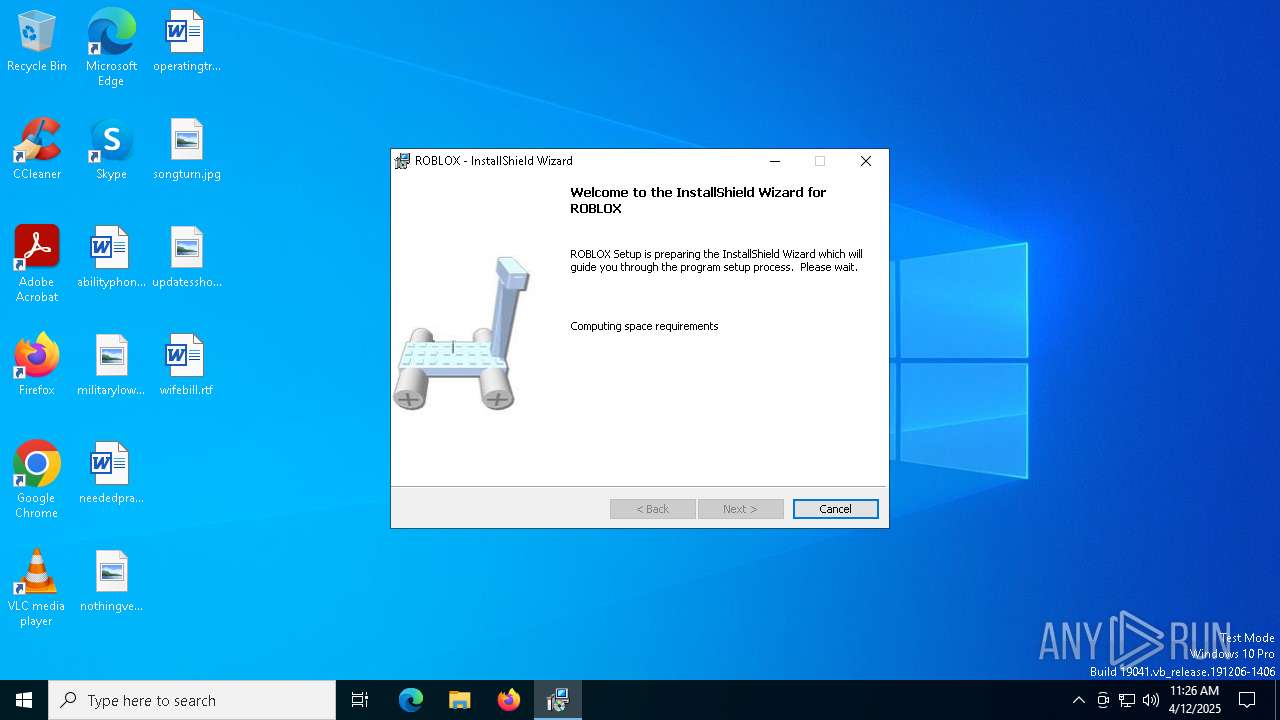
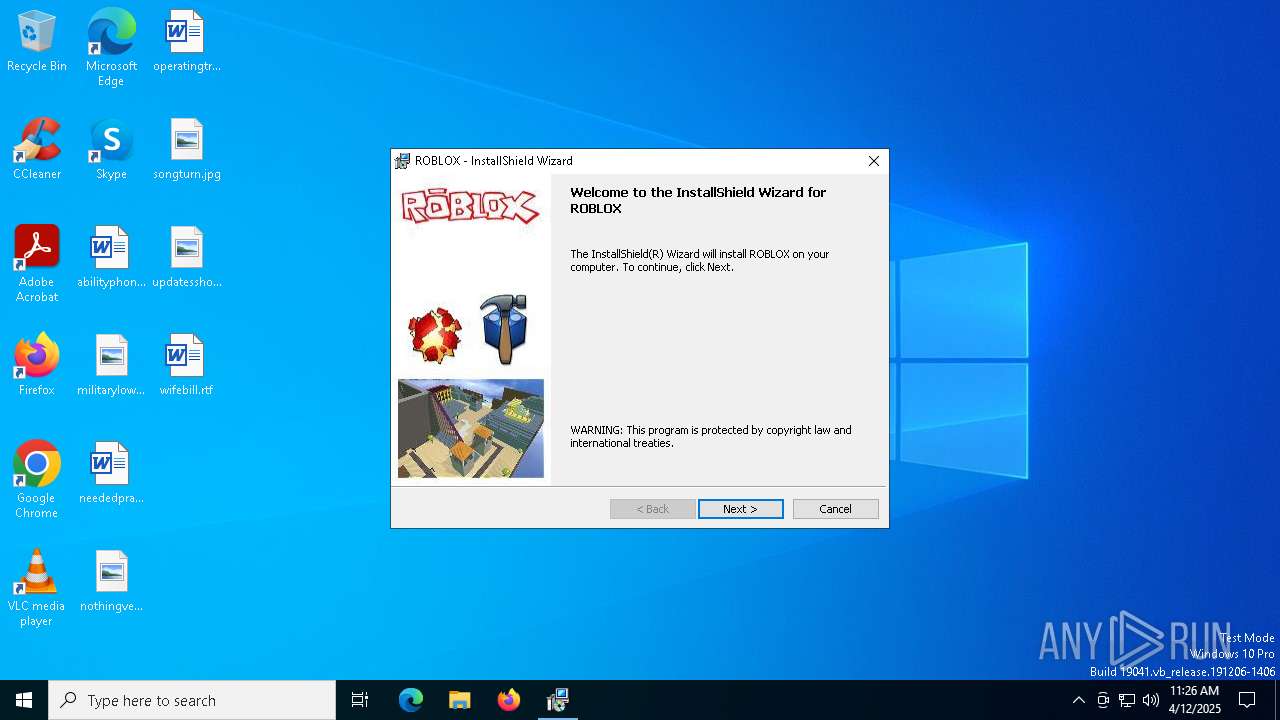
| Analysis date: | April 12, 2025, 11:26:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
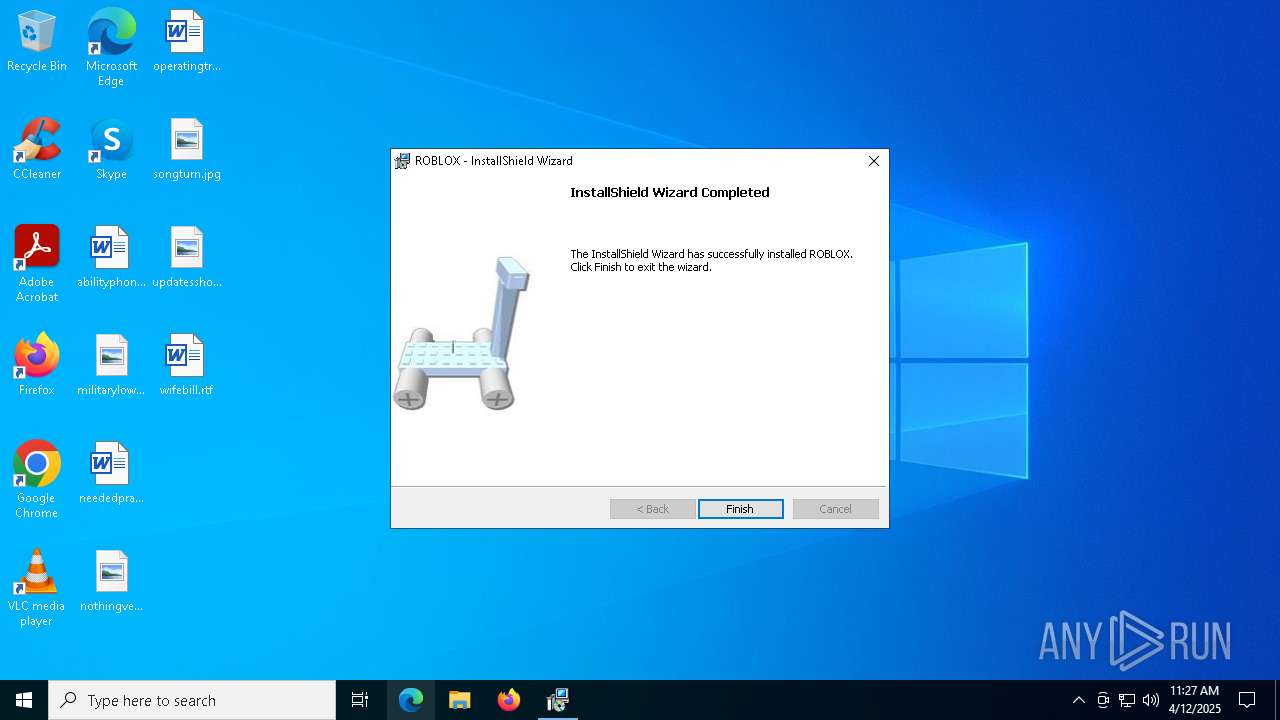
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.2, MSI Installer, Number of Characters: 0, Last Saved By: DavidHacker, Number of Words: 0, Title: Roblox Database, Comments: This installer database contains the logic and data required to install ROBLOX., Keywords: Installer,MSI,Database, Subject: ROBLOX, Author: Roblox Corporation, Security: 1, Number of Pages: 200, Name of Creating Application: InstallShield 12 - Professional Edition 12.0, Last Saved Time/Date: Wed Jan 16 14:15:17 2008, Create Time/Date: Wed Jan 16 14:15:17 2008, Last Printed: Wed Jan 16 14:15:17 2008, Revision Number: {3E85A94D-AE1B-4F82-BB83-E876CFE98859}, Code page: 1252, Template: Intel;1033 |
| MD5: | 12E30377CEDB343061EF95DA94F27A9F |
| SHA1: | 9D46A8392C6BDED0F3259EFBFAE6E97C488A3A93 |
| SHA256: | 47729BC654B0DA51D400840D9EE9781810F4EAE77E9ECE6CB0F04F26709D837F |
| SSDEEP: | 98304:boMA2pc0Yri23+zBAZU0iuhVaWUzeJt9nRmCqN7aRyqbBkERJu42CVfYT1Cqdzn/:0MI1j/1EV+Jp6k+e7CKb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 8144)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7556)
The process drops C-runtime libraries
- msiexec.exe (PID: 7556)
- TiWorker.exe (PID: 7184)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 7556)
Process drops legitimate windows executable
- msiexec.exe (PID: 7556)
- TiWorker.exe (PID: 7184)
Changes default file association
- msiexec.exe (PID: 7556)
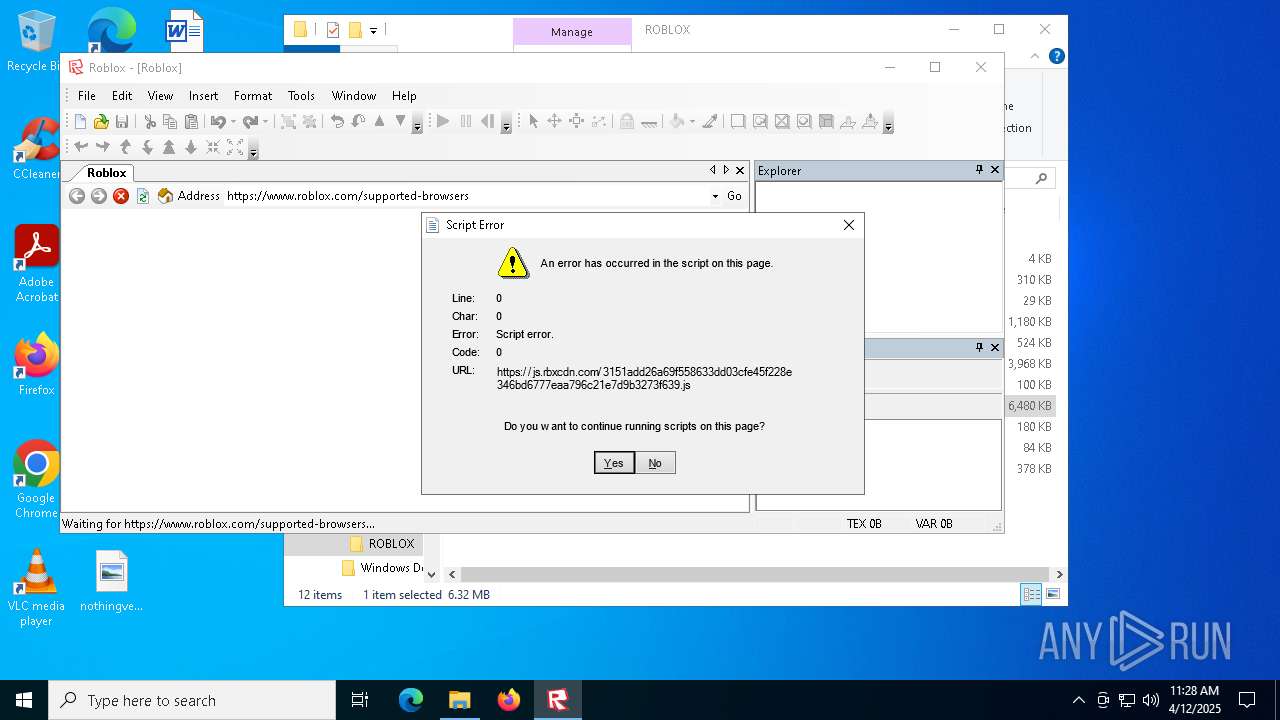
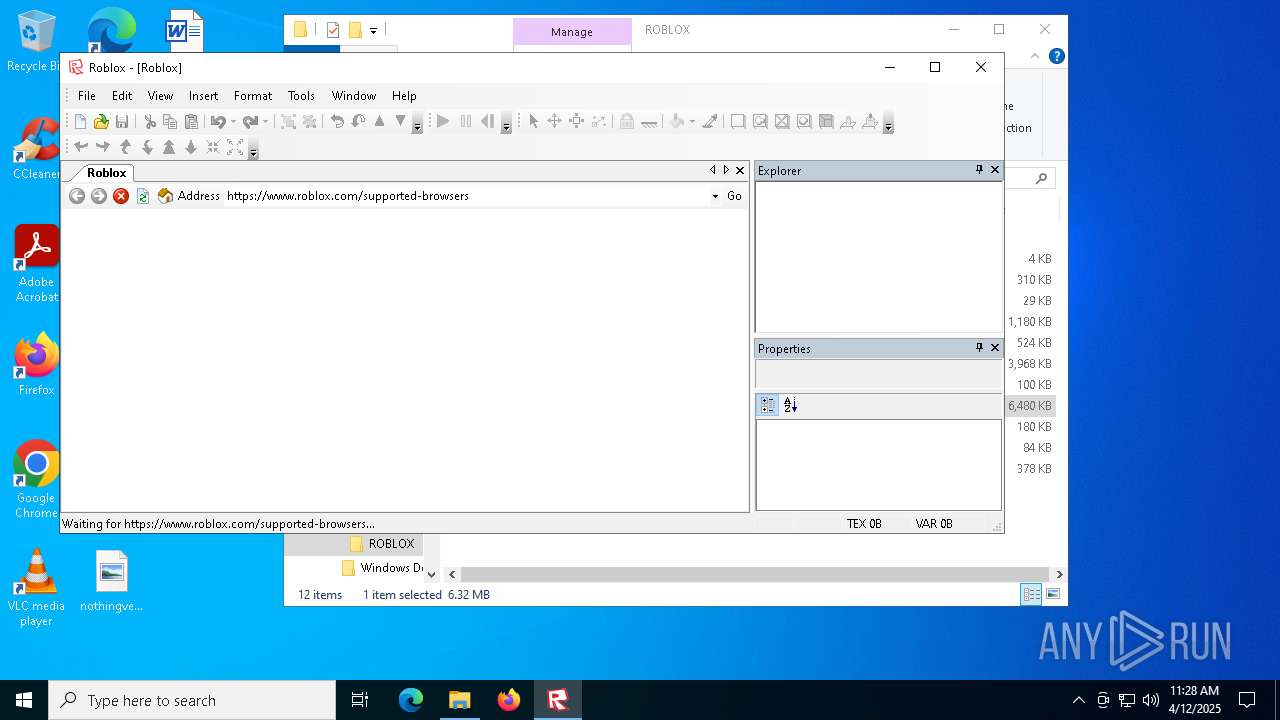
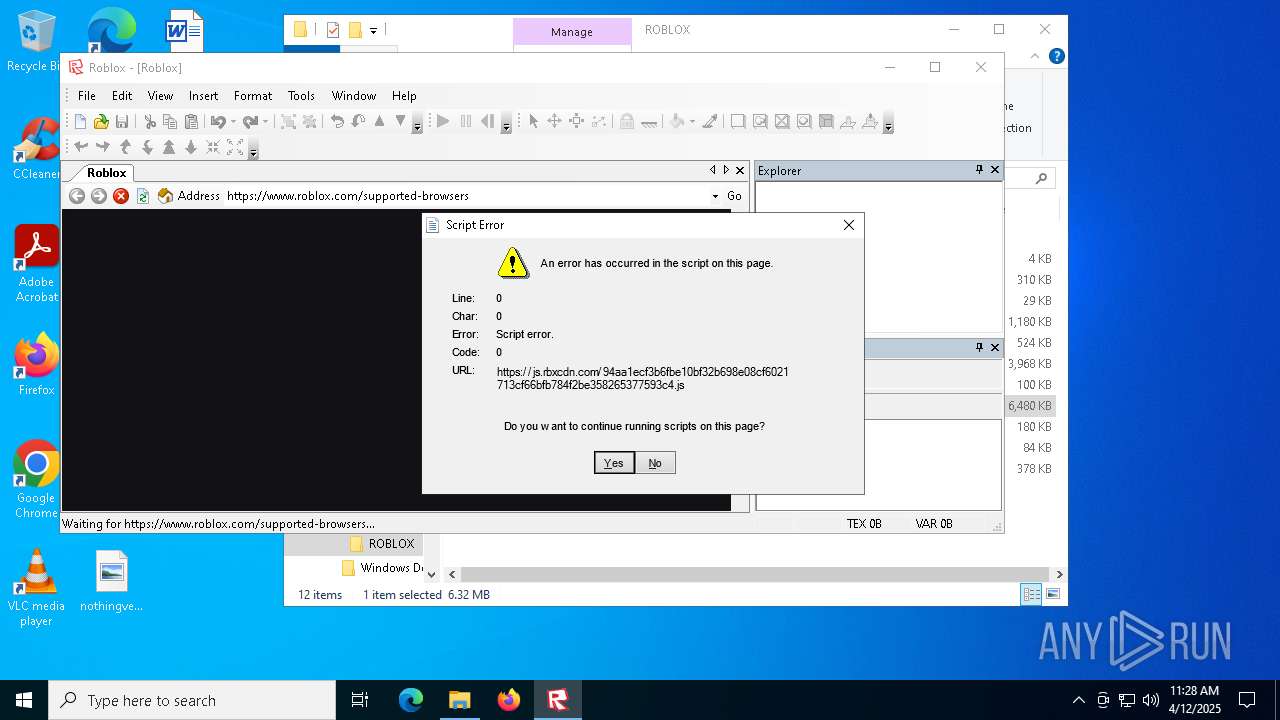
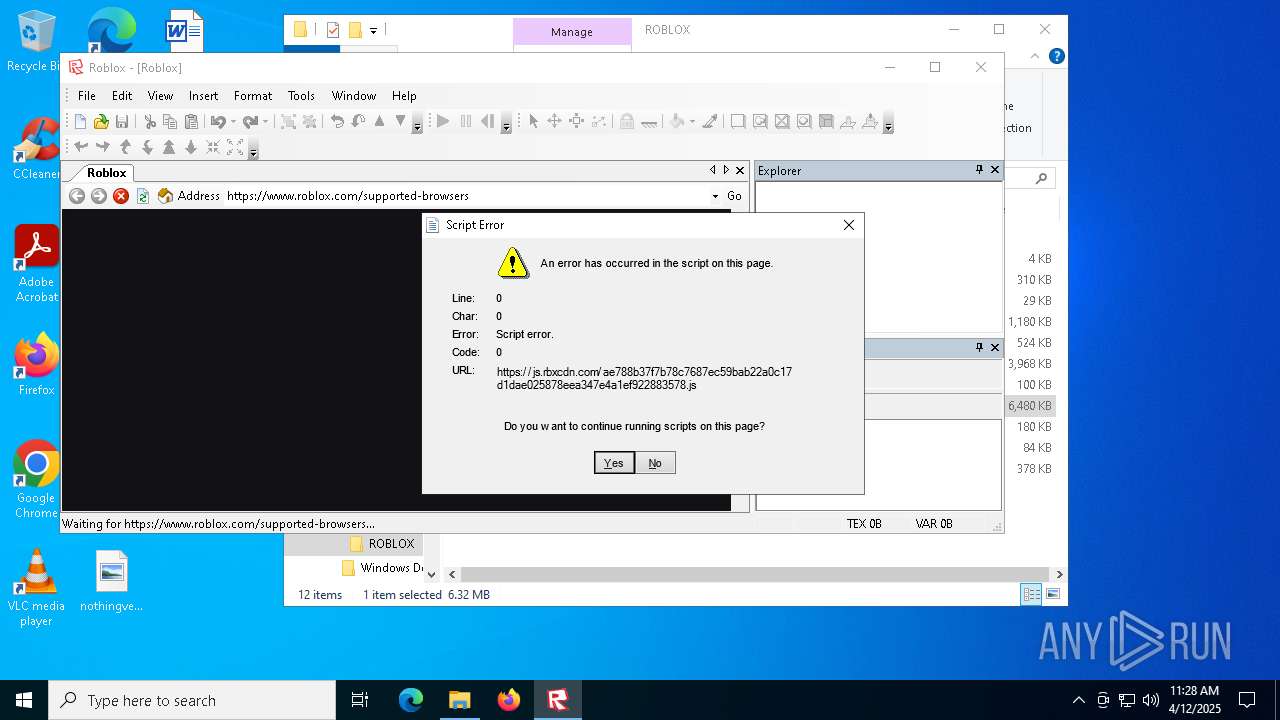
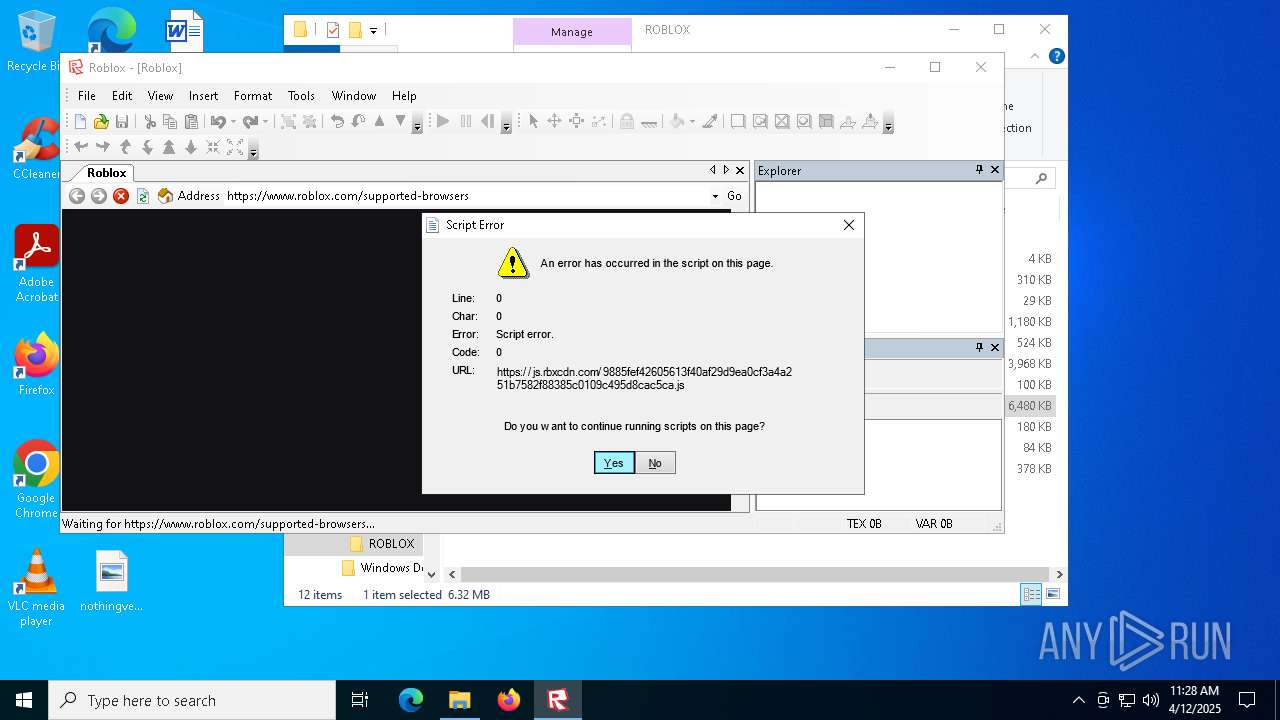
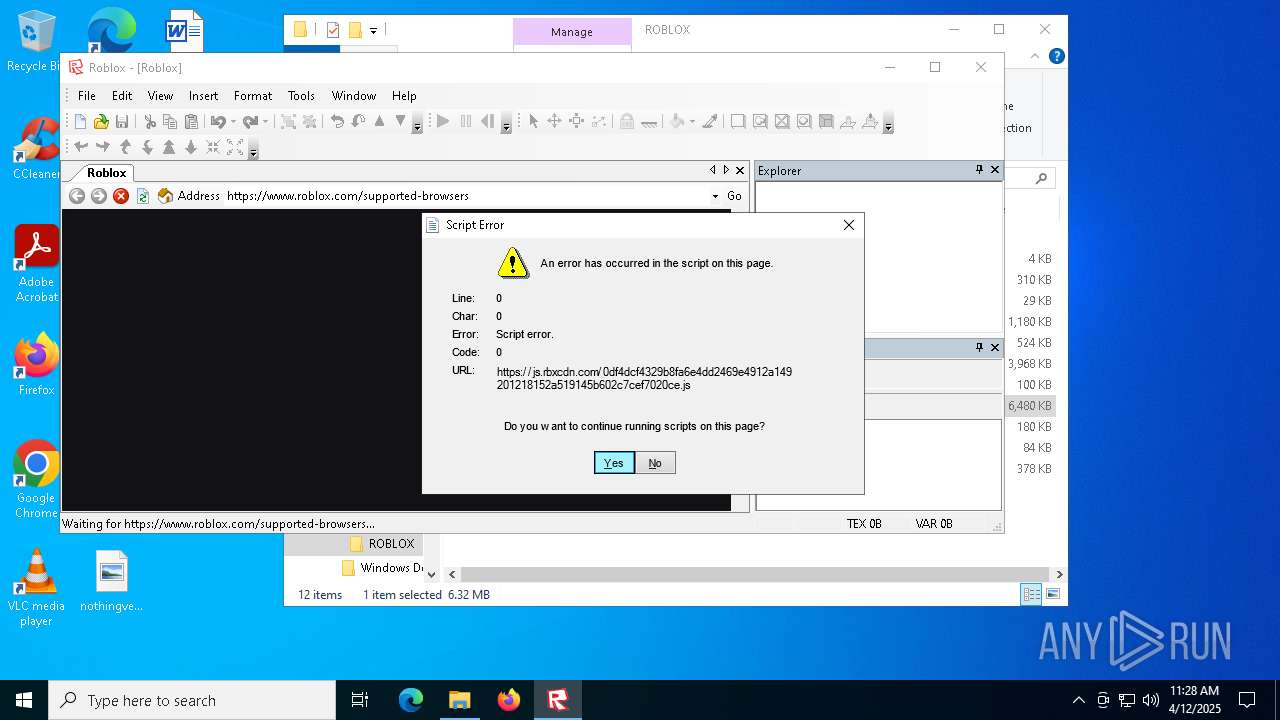
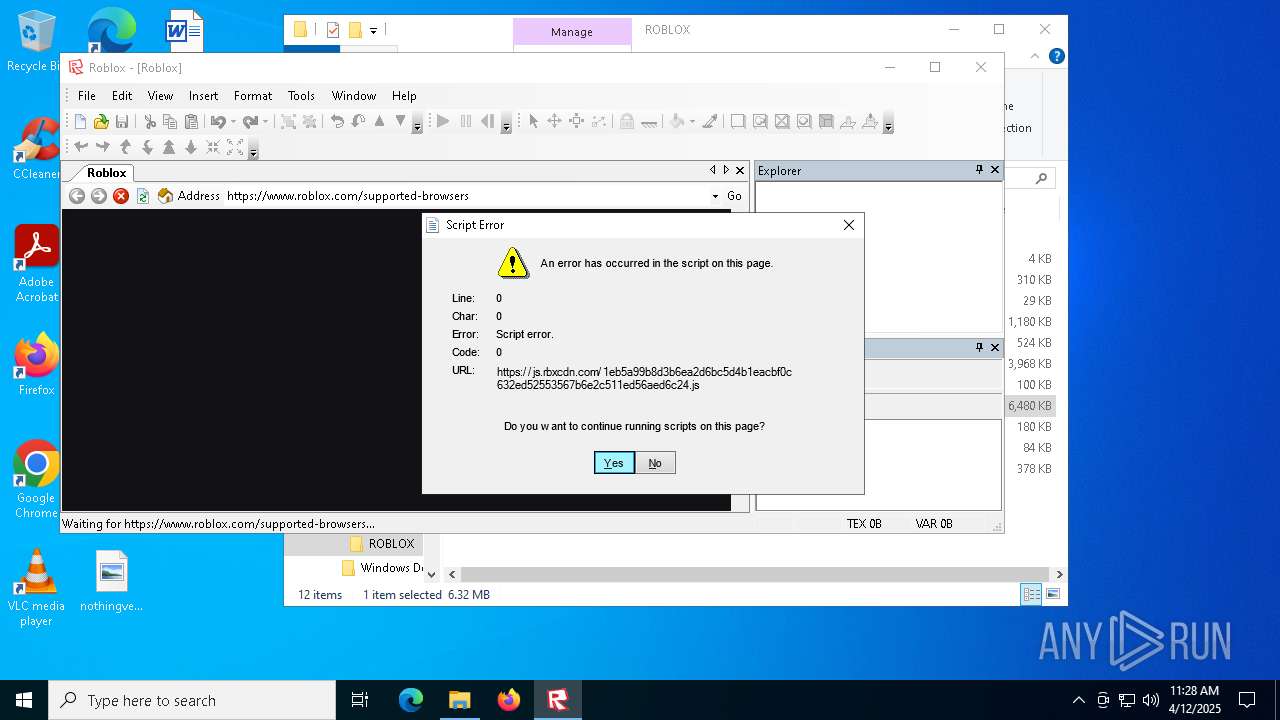
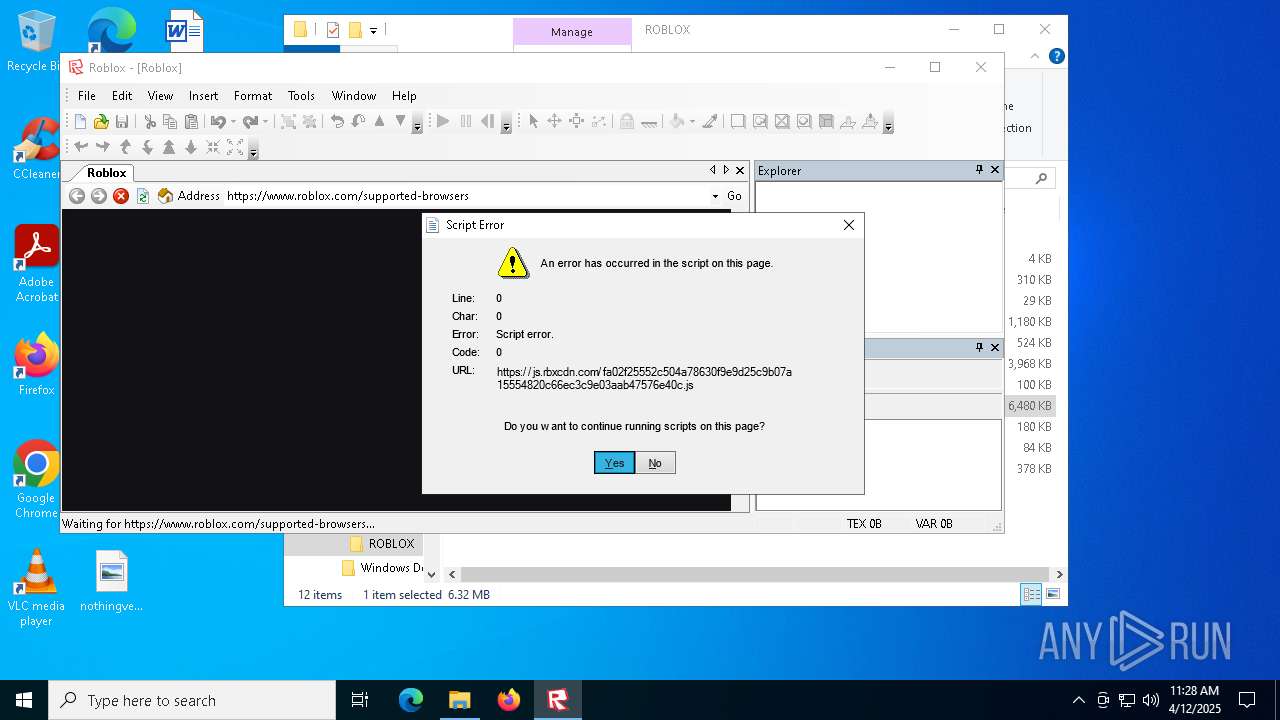
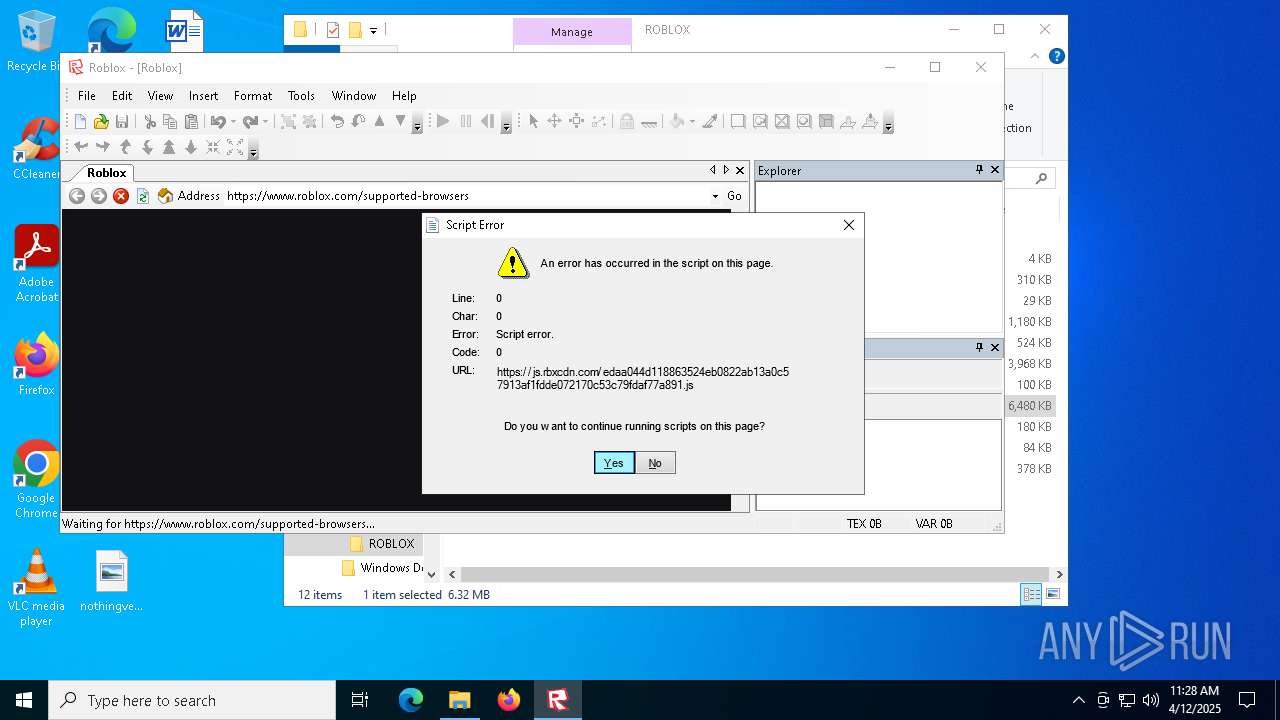
Reads security settings of Internet Explorer
- Roblox.exe (PID: 5964)
Reads Microsoft Outlook installation path
- Roblox.exe (PID: 5964)
Executable content was dropped or overwritten
- TiWorker.exe (PID: 7184)
Reads Internet Explorer settings
- Roblox.exe (PID: 5964)
INFO
The sample compiled with english language support
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 7556)
- TiWorker.exe (PID: 7184)
An automatically generated document
- msiexec.exe (PID: 7424)
Reads the computer name
- msiexec.exe (PID: 7556)
- msiexec.exe (PID: 7596)
- msiexec.exe (PID: 2284)
- msiexec.exe (PID: 732)
- Roblox.exe (PID: 5964)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7424)
- msiexec.exe (PID: 7556)
Checks supported languages
- msiexec.exe (PID: 7596)
- msiexec.exe (PID: 7556)
- msiexec.exe (PID: 2284)
- msiexec.exe (PID: 732)
- Roblox.exe (PID: 5964)
Manages system restore points
- SrTasks.exe (PID: 3180)
Creates a software uninstall entry
- msiexec.exe (PID: 7556)
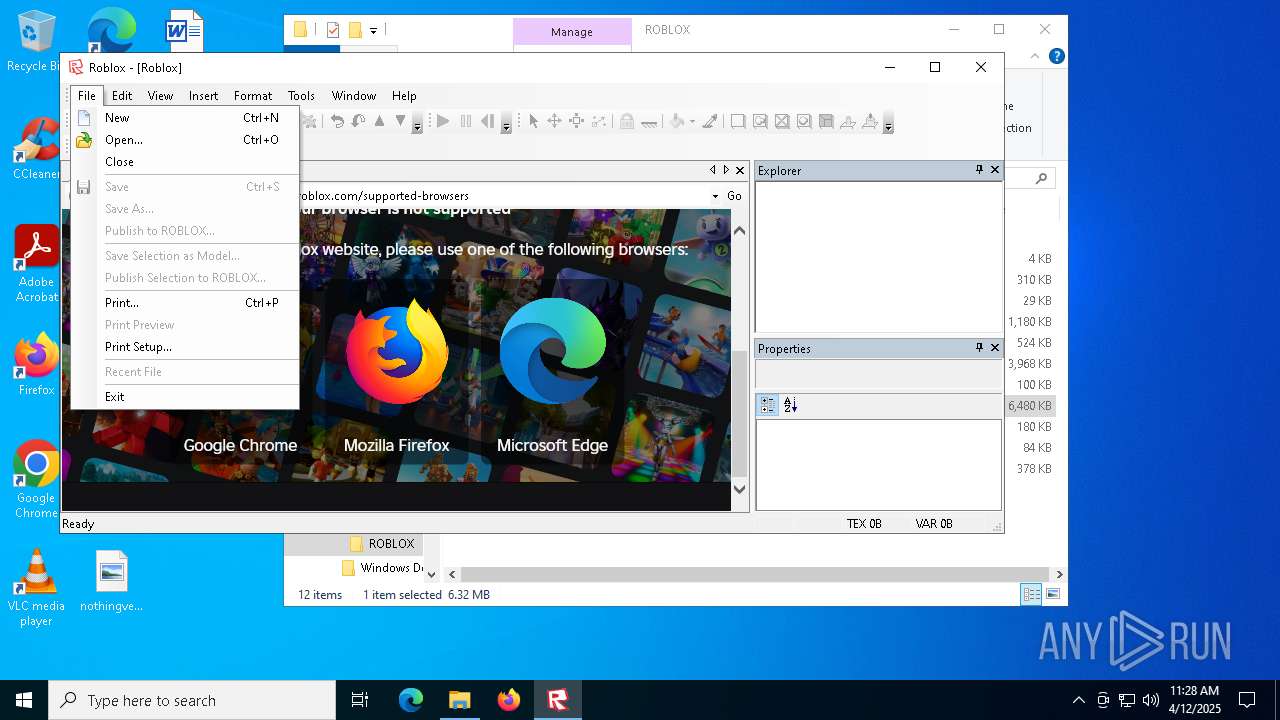
Manual execution by a user
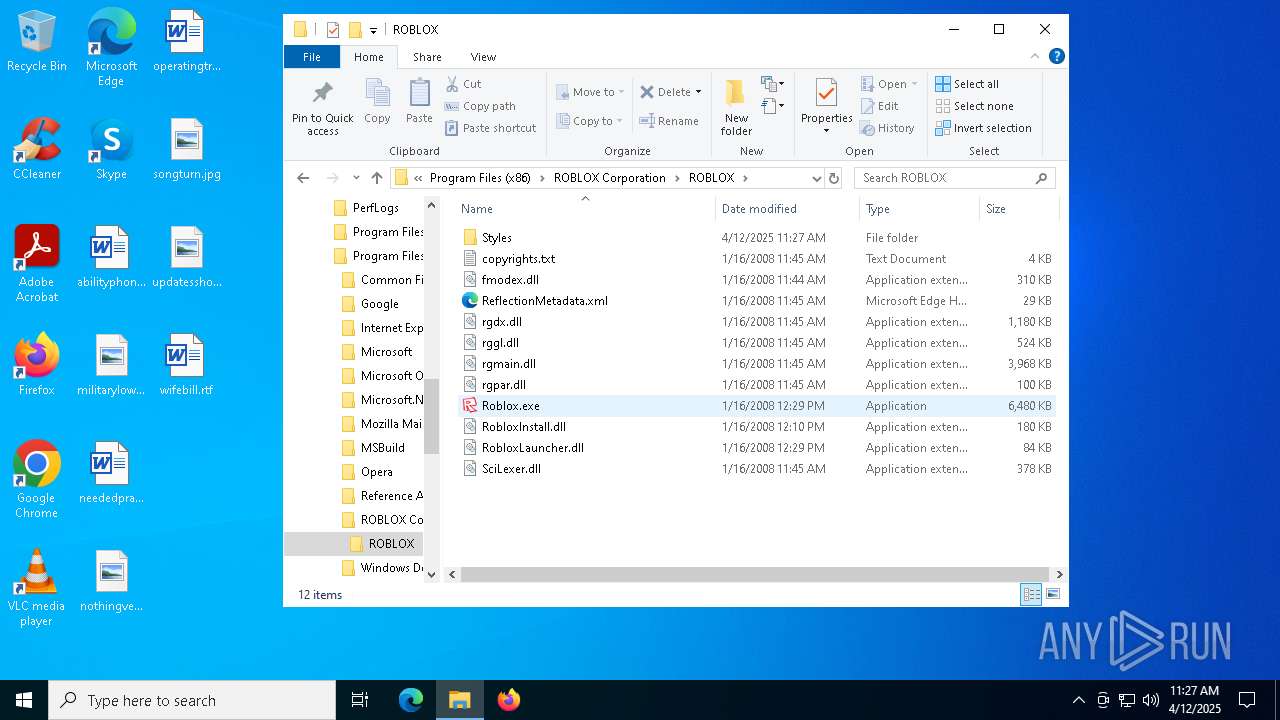
- Roblox.exe (PID: 5964)
Reads the software policy settings
- slui.exe (PID: 7744)
- Roblox.exe (PID: 5964)
Creates files or folders in the user directory
- Roblox.exe (PID: 5964)
Reads the machine GUID from the registry
- Roblox.exe (PID: 5964)
Checks proxy server information
- Roblox.exe (PID: 5964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Characters: | - |
|---|---|
| LastModifiedBy: | DavidHacker |
| Words: | - |
| Title: | Roblox Database |
| Comments: | This installer database contains the logic and data required to install ROBLOX. |
| Keywords: | Installer,MSI,Database |
| Subject: | ROBLOX |
| Author: | Roblox Corporation |
| Security: | Password protected |
| Pages: | 200 |
| Software: | InstallShield? 12 - Professional Edition 12.0 |
| ModifyDate: | 2008:01:16 14:15:17 |
| CreateDate: | 2008:01:16 14:15:17 |
| LastPrinted: | 2008:01:16 14:15:17 |
| RevisionNumber: | {3E85A94D-AE1B-4F82-BB83-E876CFE98859} |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
Total processes
147
Monitored processes
14
Malicious processes
3
Suspicious processes
0
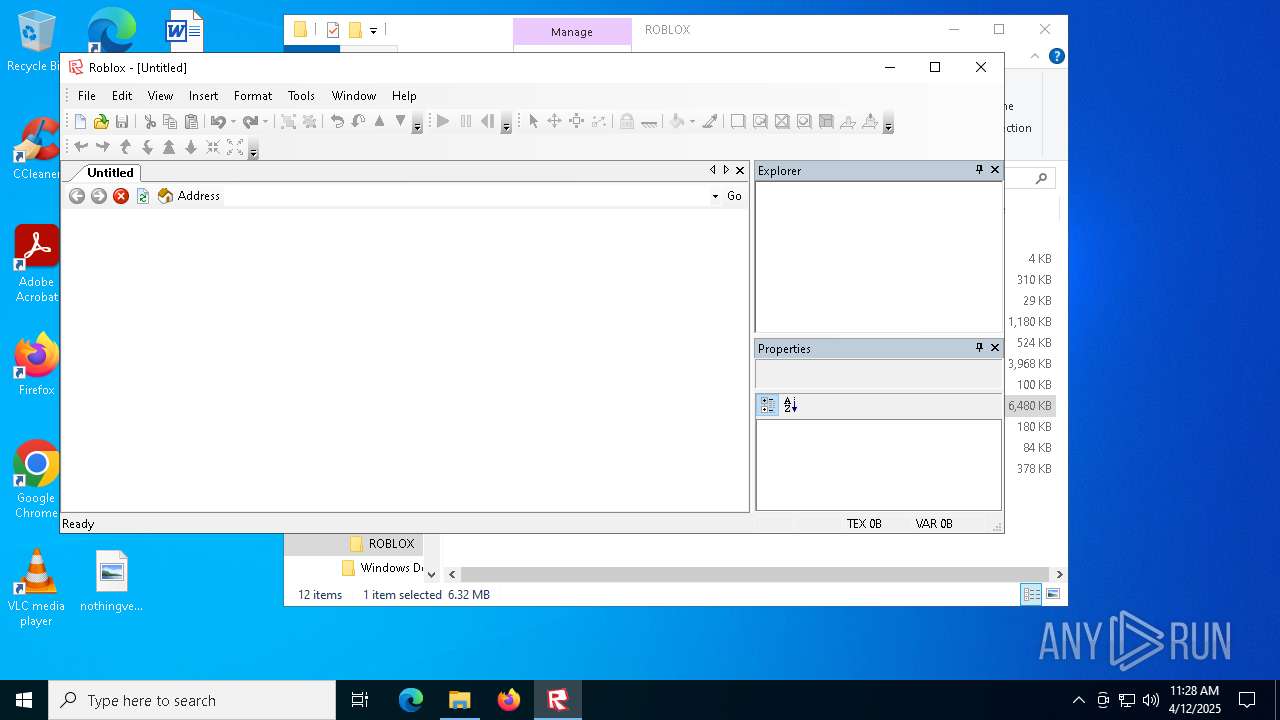
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 732 | C:\Windows\syswow64\MsiExec.exe -Embedding 69BA36ADA4B55B48E5076DD1058CA0F3 M Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\Windows\syswow64\MsiExec.exe -Embedding 440FD969B14EC96BF9A6119E111D8C79 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2772 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
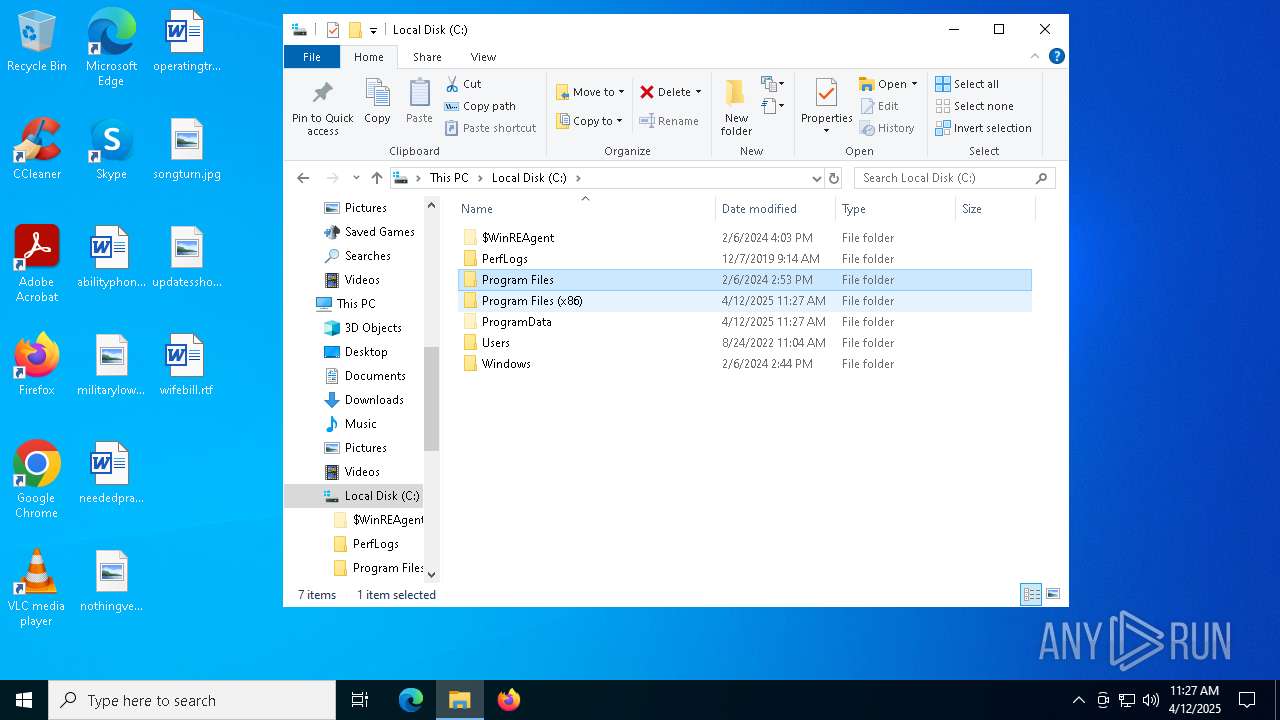
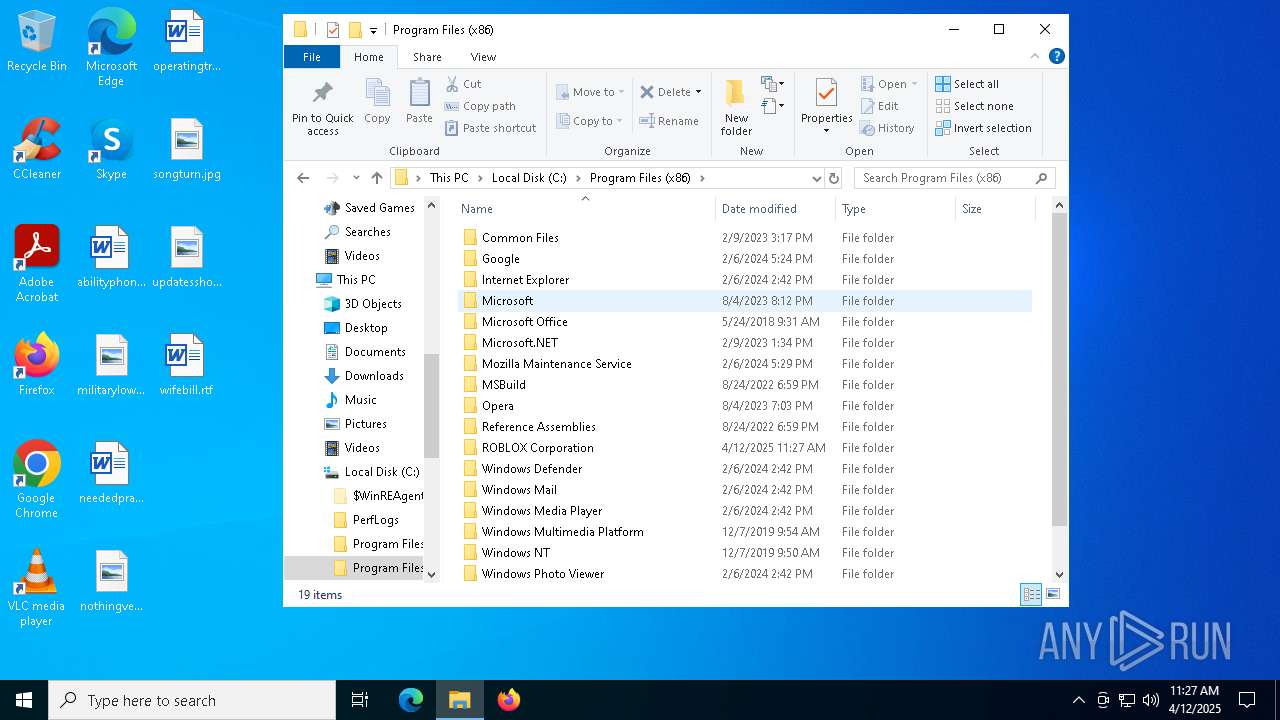
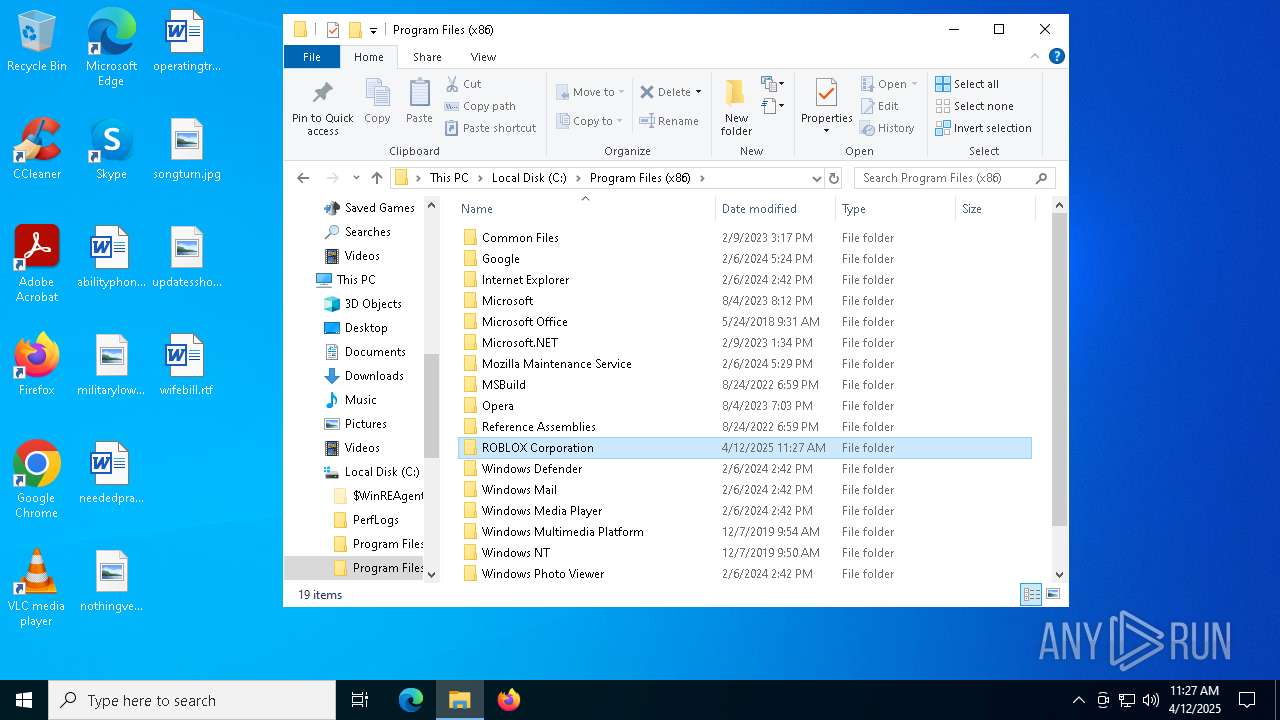
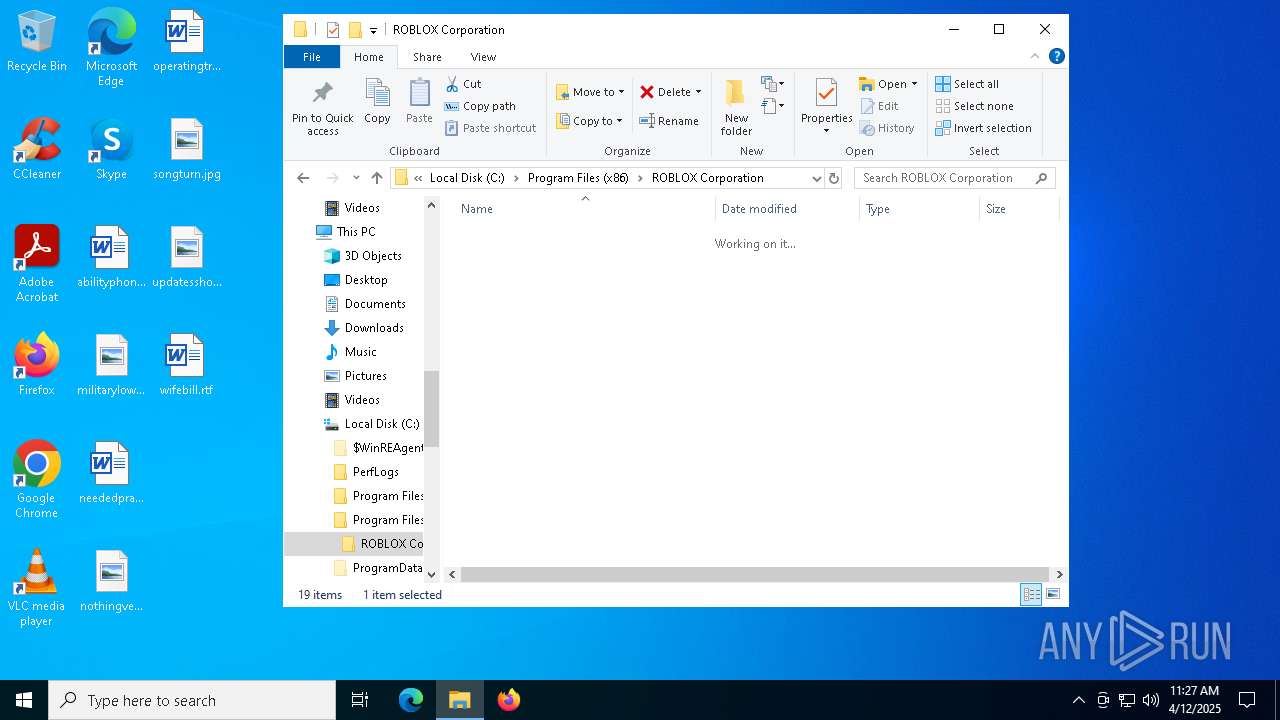
| 5964 | "C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\Roblox.exe" | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\Roblox.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: ROBLOX Game Exit code: 0 Version: 0, 3, 696, 0 Modules
| |||||||||||||||
| 7184 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7424 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\ROBLOX.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7556 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7596 | C:\Windows\syswow64\MsiExec.exe -Embedding 3C0930C0F6C3D6C65F12937C27B29F9B C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 911
Read events
8 309
Write events
552
Delete events
50
Modification events
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000F5F57DCC9DABDB01841D0000C01F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000F5F57DCC9DABDB01841D0000C01F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005A16DBCC9DABDB01841D0000C01F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005A16DBCC9DABDB01841D0000C01F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000003753DDCC9DABDB01841D0000C01F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000079B7DFCC9DABDB01841D0000C01F0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (8144) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CFED56CD9DABDB01D01F0000F8130000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8144) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CFED56CD9DABDB01D01F00002C010000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8144) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CFED56CD9DABDB01D01F0000F01F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
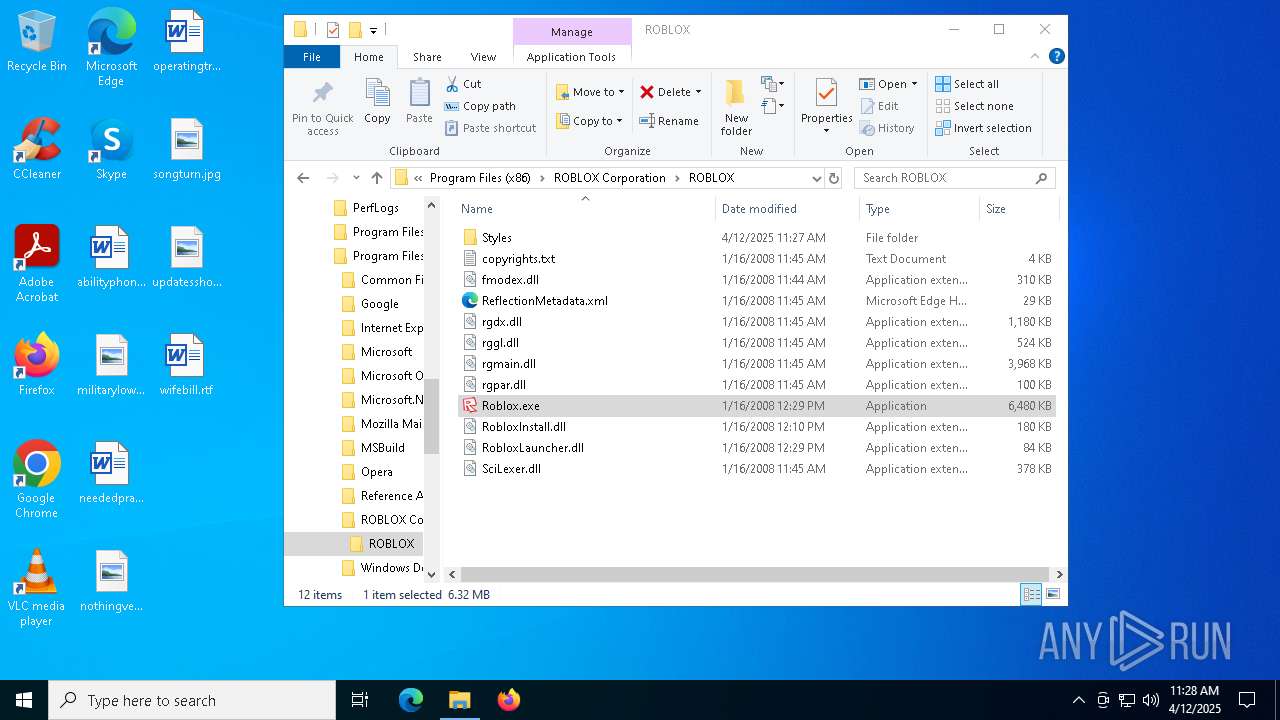
Executable files
39
Suspicious files
140
Text files
367
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
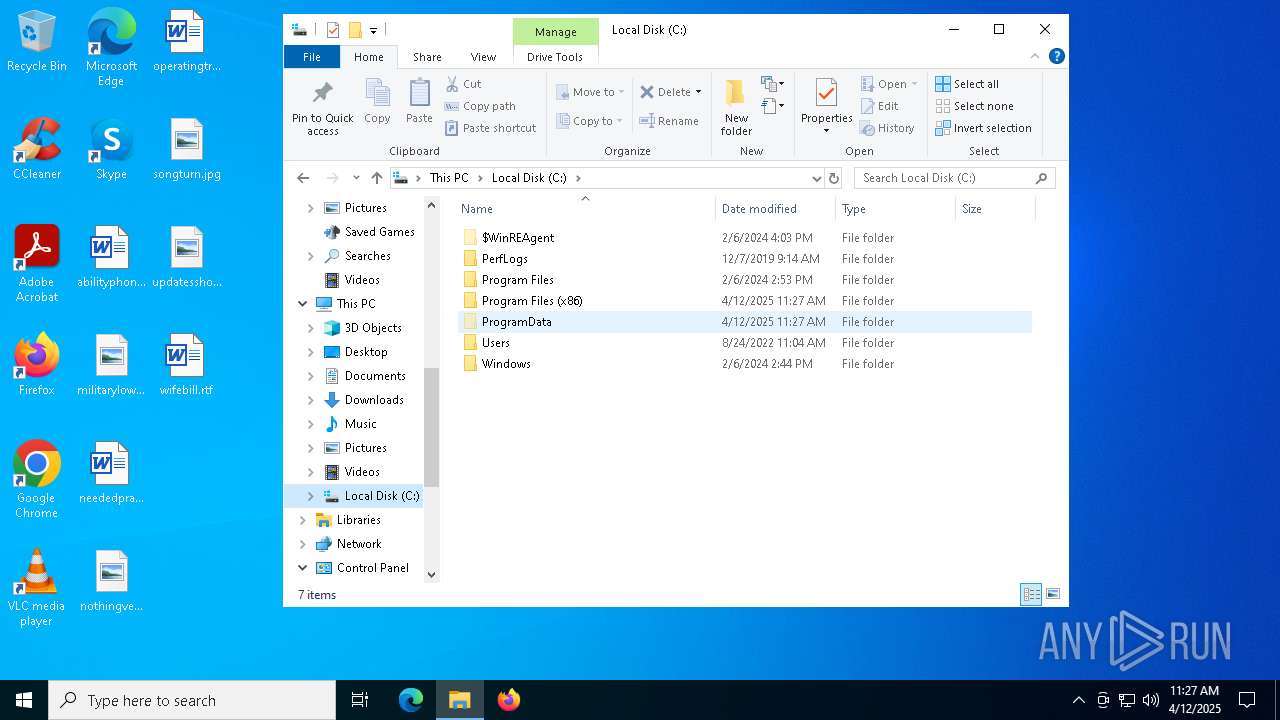
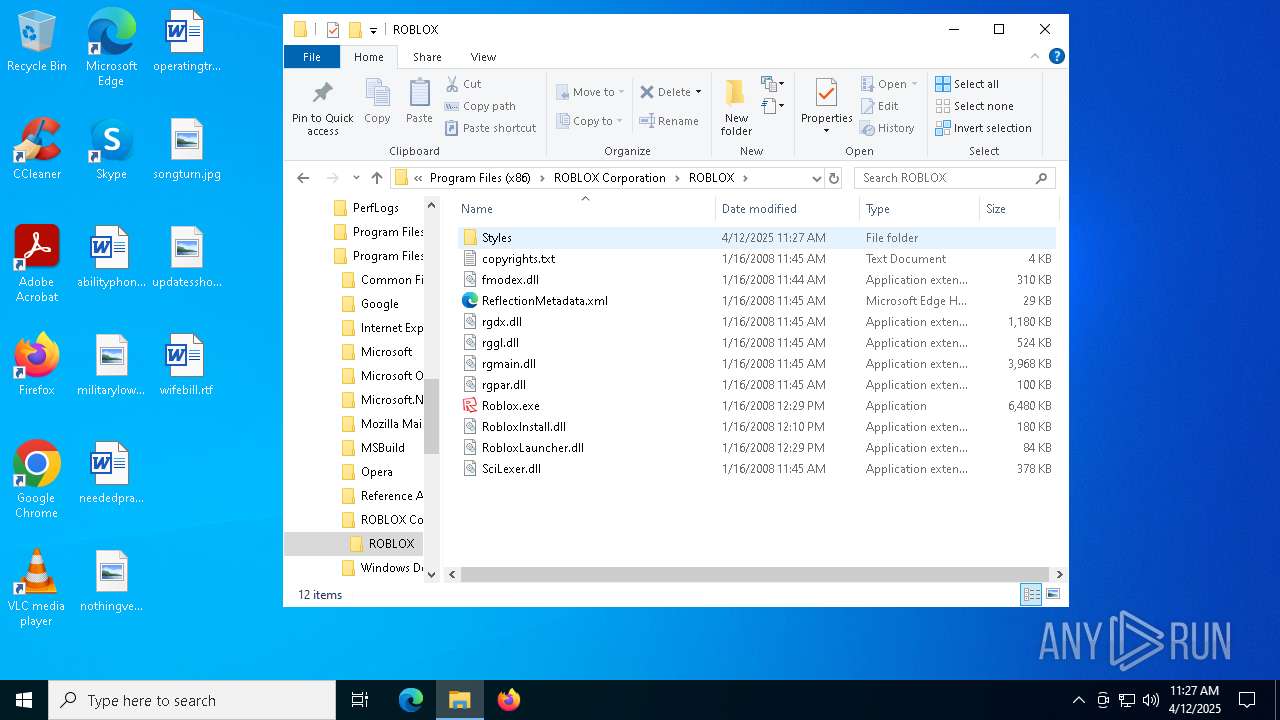
| 7556 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7556 | msiexec.exe | C:\Windows\Installer\1126a0.msi | — | |
MD5:— | SHA256:— | |||
| 7556 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:9C50E0C5A83AE8A53FFA998272B28063 | SHA256:A078FAEBF6A155250AD3B8898148FE0CBC28E4627ED7F228F0BB0AF01B79F620 | |||
| 7424 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIC0E1.tmp | executable | |
MD5:FADFFEF98D0F28368B843C6E9AFD9782 | SHA256:73F7E51214B775421F6679ACABC51AC1D34B4271116F5F3DD3426DF50D214886 | |||
| 7556 | msiexec.exe | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\ReflectionMetadata.xml | text | |
MD5:8D616FA10D308CA2AD5CE72D2D461173 | SHA256:F53FC342CB5A53C05F94F47AB31C0B9A866DCC5985D4E56DE0FD3981695272A3 | |||
| 7556 | msiexec.exe | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\fmodex.dll | executable | |
MD5:DE05CB0A9DFC8A1CD0567CD17D177164 | SHA256:8BDA3DB088FC03D1BC54BEB7CF78CD45ED088BF2C091B3131674531D44B5967D | |||
| 7556 | msiexec.exe | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\rggl.dll | executable | |
MD5:C51BE96DC363279C80A54273F7DD3F67 | SHA256:97CD0B7B2660A1F10DC4128D82587FF9B26C354327BB892B84A823B31529FD9A | |||
| 7556 | msiexec.exe | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\Roblox.exe | executable | |
MD5:90F9E253A5BA8AFE24F16FD18B8D953E | SHA256:B37432D28A80DE06F543010FF01E8D568EA5934F20EC071D3E7EA2AC49D20A7F | |||
| 7556 | msiexec.exe | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\rgdx.dll | executable | |
MD5:E023CE99F445853E244EFD51147AD157 | SHA256:EC582120C3A861196618169556C40BEB502EA1D5E870226C2B5005B93A01E656 | |||
| 7556 | msiexec.exe | C:\Program Files (x86)\ROBLOX Corporation\ROBLOX\rgpar.dll | executable | |
MD5:307D8BB1B68A17EBCD52D7ABB09497AD | SHA256:F4F8404728711802B3298EF60DC6B9BE6E5595078644312760D3D697FFF460C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
45
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1660 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1660 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
5964 | Roblox.exe | POST | 307 | 128.116.44.3:80 | http://www.roblox.com/Game/MachineConfiguration.ashx | US | — | — | whitelisted |
5964 | Roblox.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | binary | 2.18 Kb | whitelisted |
5964 | Roblox.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | whitelisted |
5964 | Roblox.exe | GET | 307 | 128.116.44.3:80 | http://www.roblox.com/IDE/Start.aspx | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7568 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1660 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |