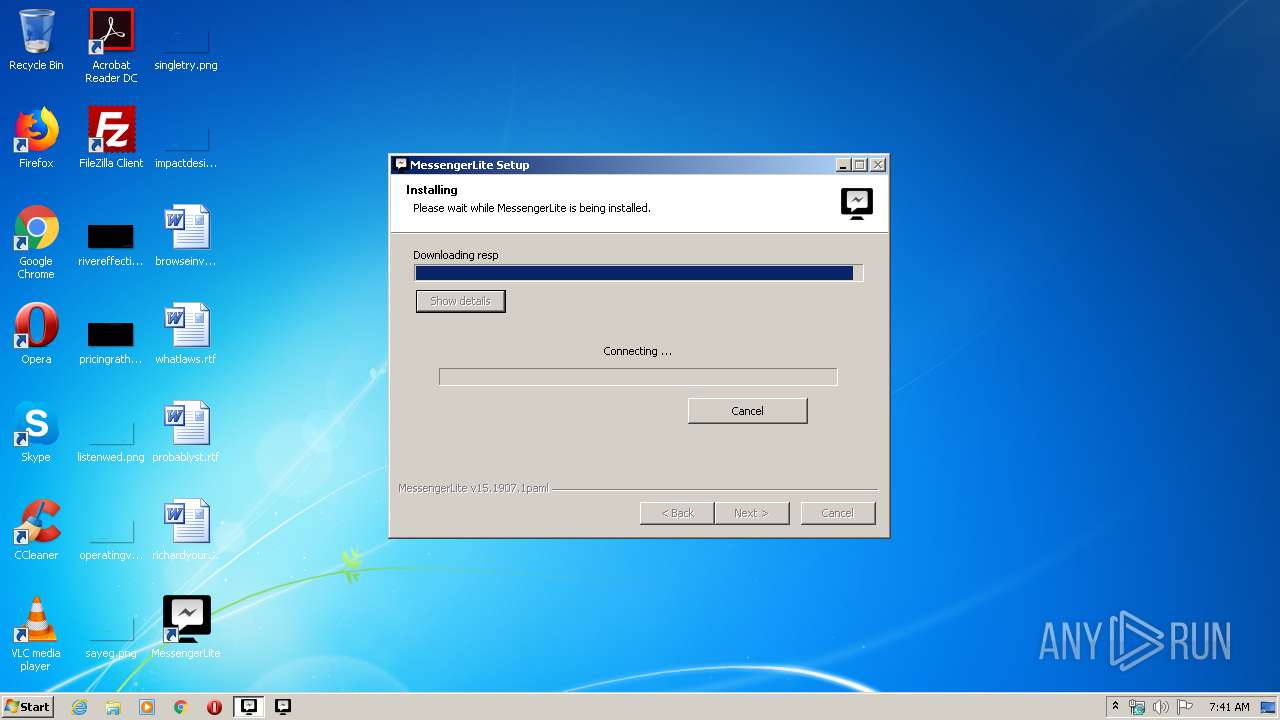
| download: | paml |
| Full analysis: | https://app.any.run/tasks/41cb82c1-3995-4bd6-8758-63886a048337 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 07:40:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 56C150333A192FA1363AA54F0EDC1C46 |
| SHA1: | D24ABDBC134F105651B926780768745F2D7DE0E5 |
| SHA256: | 47707BBC8D3EC1A1A33461ACAE0FE841AB6DA7A5D11EE5BA1FC7CC5705534D97 |
| SSDEEP: | 786432:92IBEBiw4mgmz4USreE6GNq6myVEK2LIQjJ1:92IOEmgmKy5GNqLIa1 |
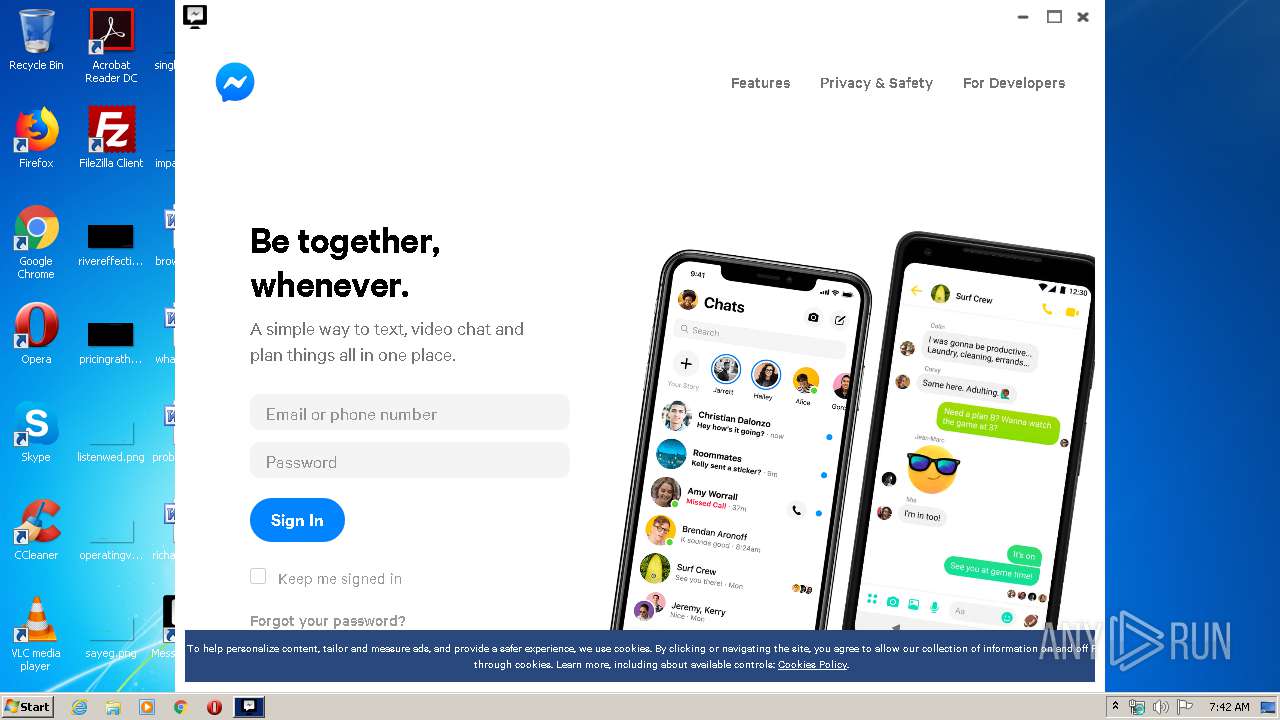
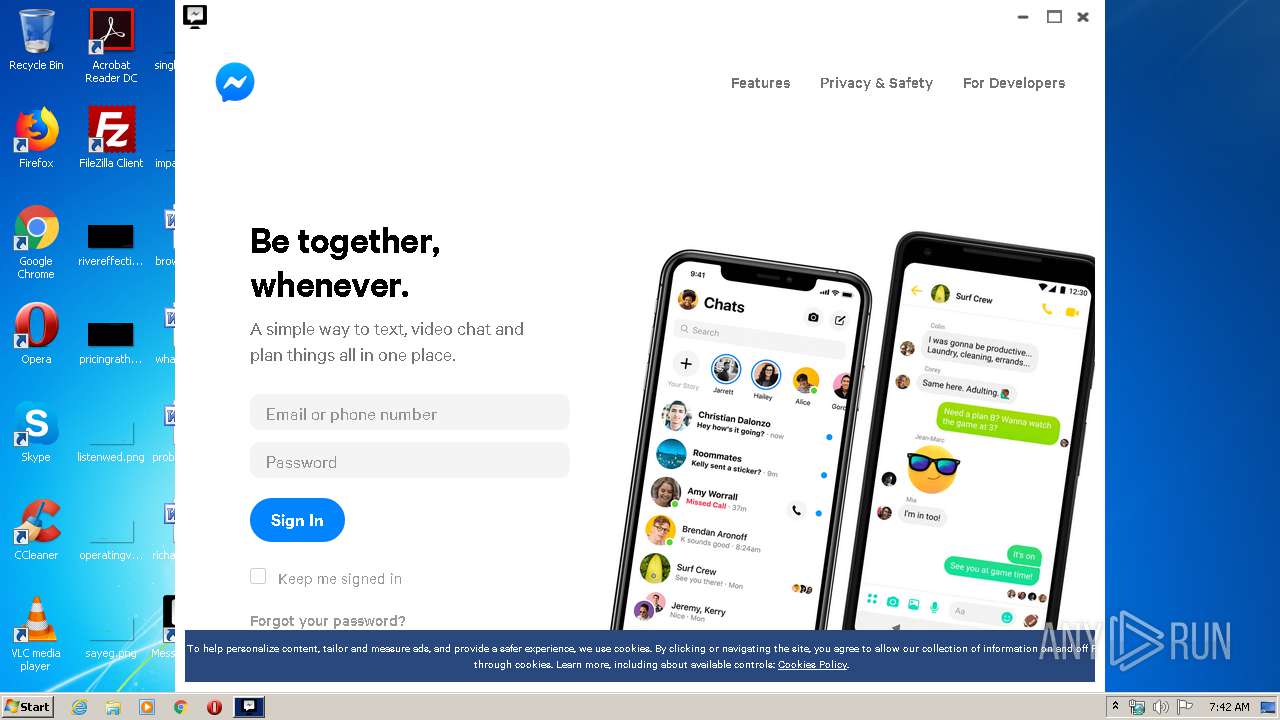
MALICIOUS
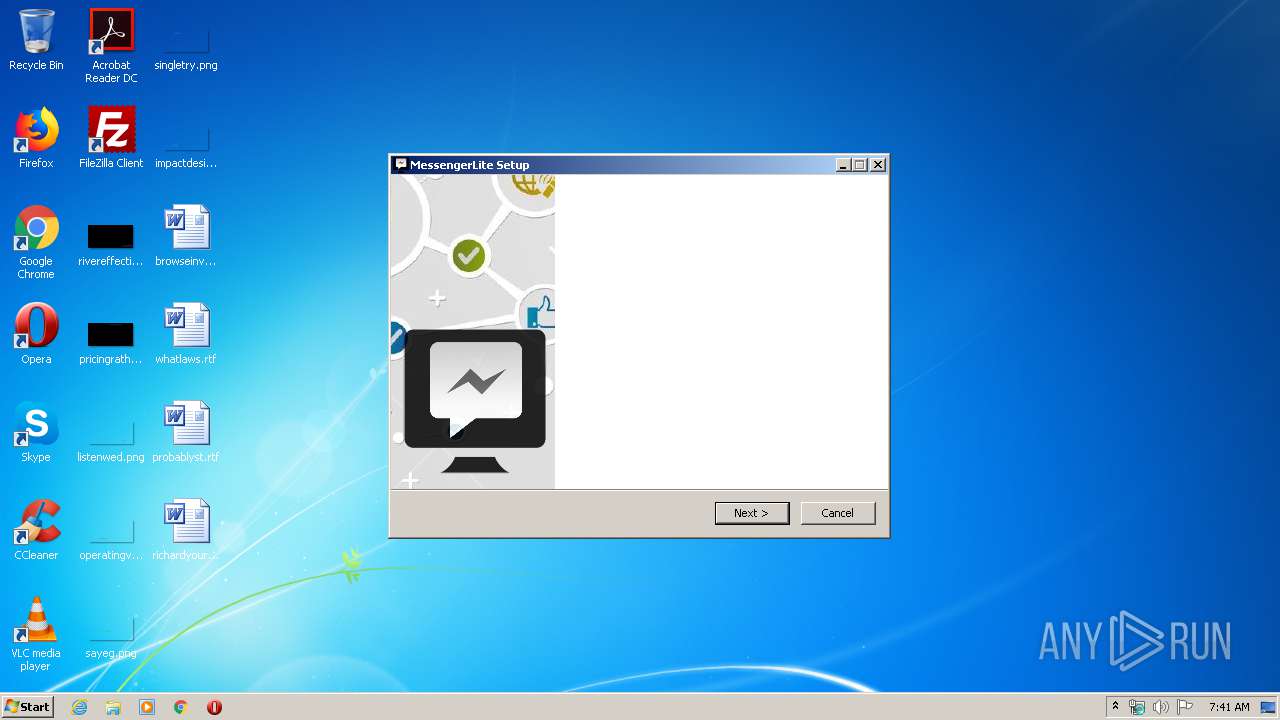
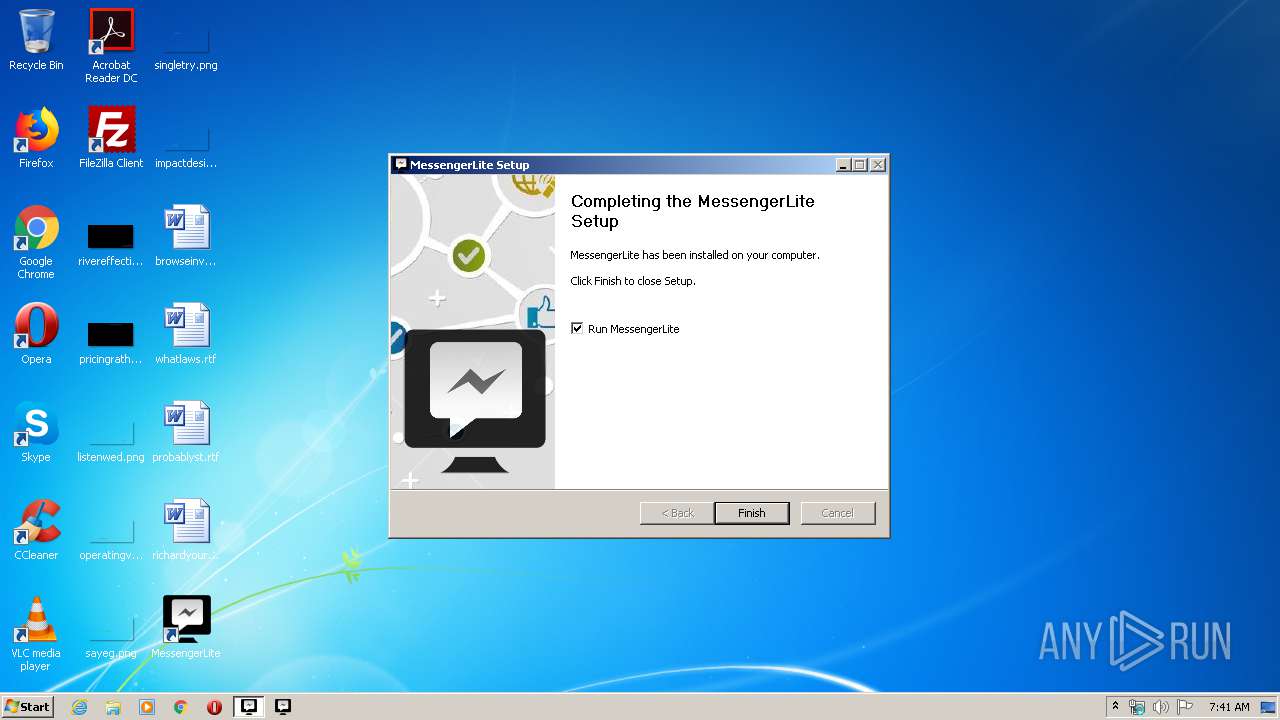
Loads dropped or rewritten executable
- paml.exe (PID: 3340)
- MessengerLite.exe (PID: 3104)
- MessengerLite.exe (PID: 628)
Changes the autorun value in the registry
- paml.exe (PID: 3340)
Changes settings of System certificates
- paml.exe (PID: 3340)
SUSPICIOUS
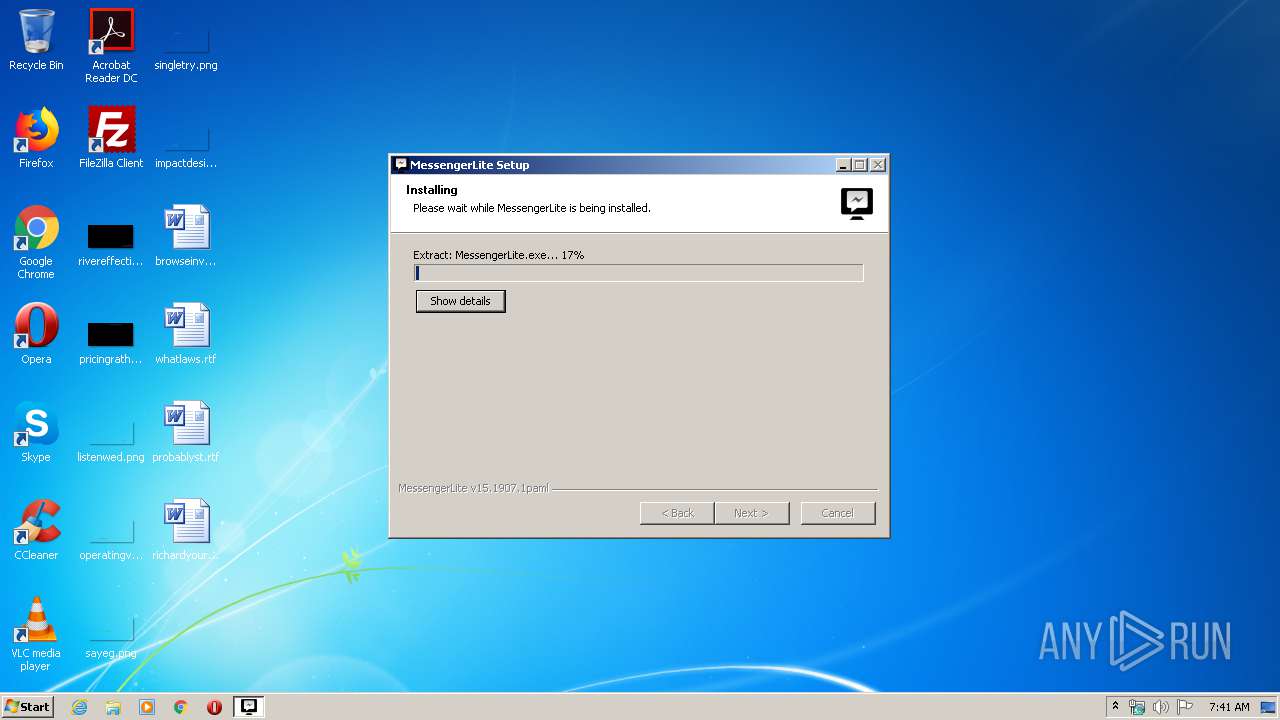
Executable content was dropped or overwritten
- paml.exe (PID: 3340)
Creates files in the user directory
- paml.exe (PID: 3340)
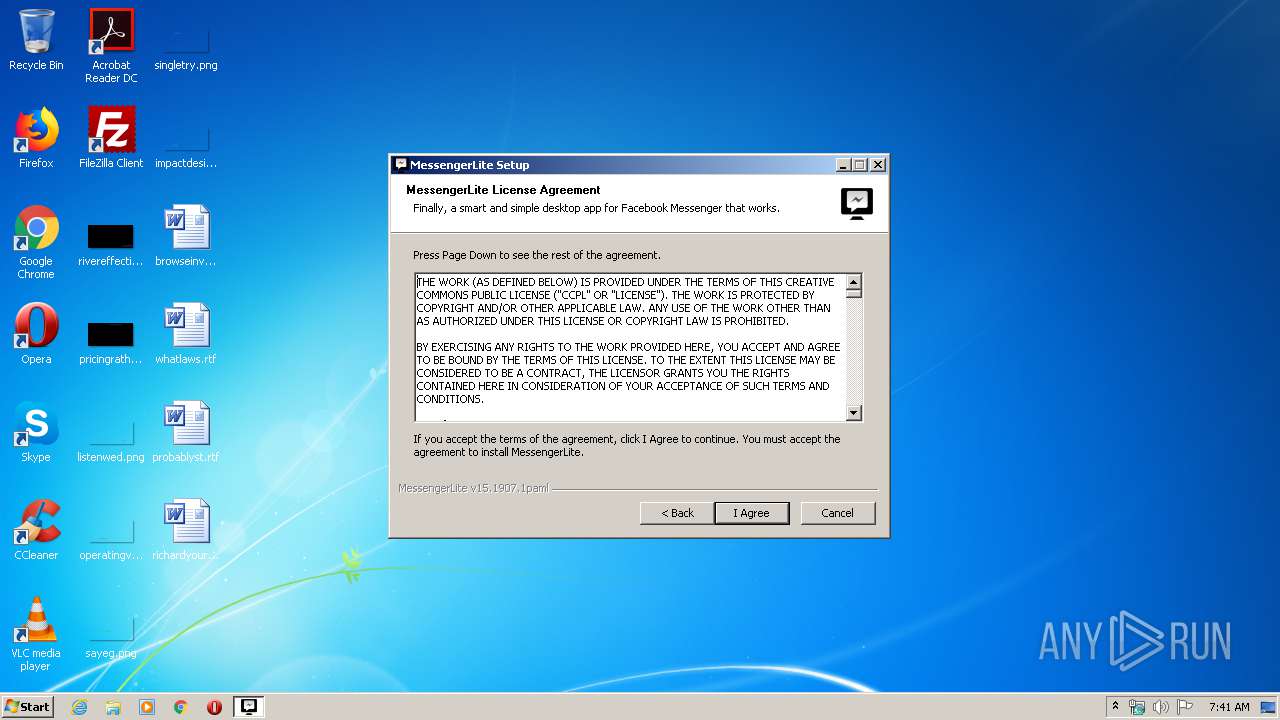
Creates a software uninstall entry
- paml.exe (PID: 3340)
Starts CMD.EXE for commands execution
- paml.exe (PID: 3340)
- MessengerLite.exe (PID: 3104)
Starts SC.EXE for service management
- cmd.exe (PID: 816)
Executed via COM
- explorer.exe (PID: 3672)
Reads Internet Cache Settings
- paml.exe (PID: 3340)
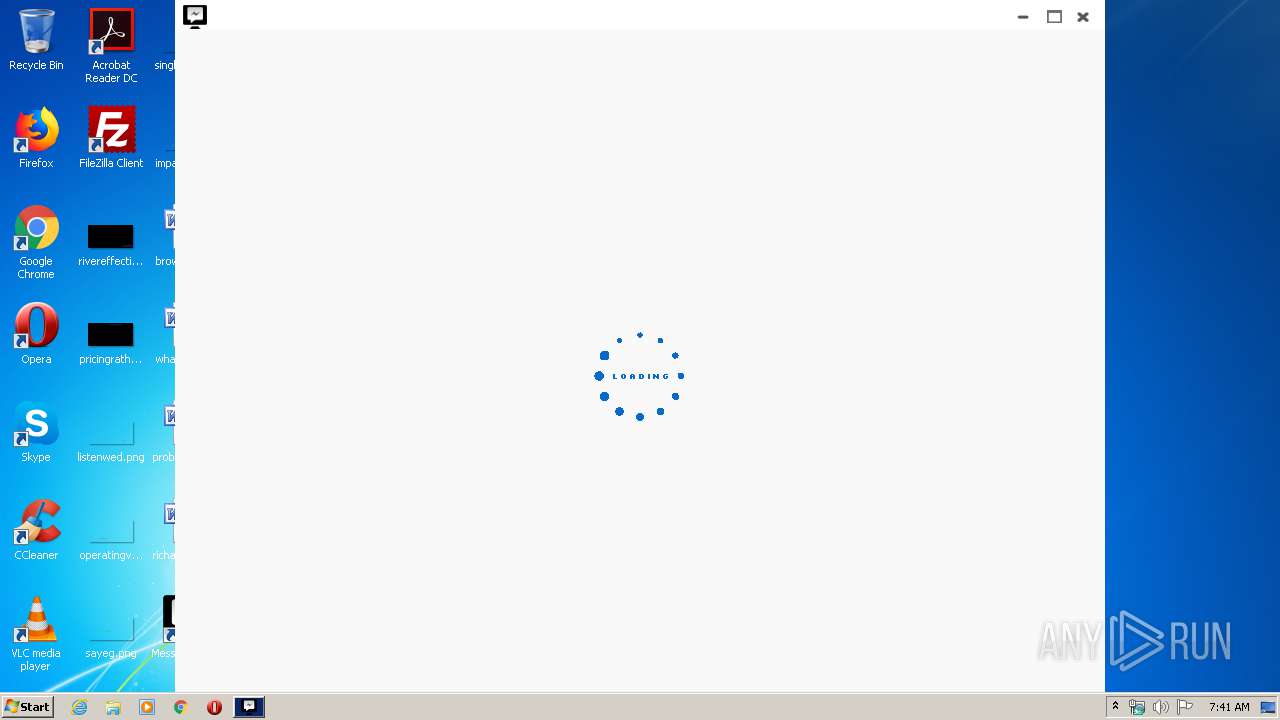
Application launched itself
- MessengerLite.exe (PID: 2648)
Adds / modifies Windows certificates
- paml.exe (PID: 3340)
INFO
Reads settings of System Certificates
- paml.exe (PID: 3340)
- MessengerLite.exe (PID: 2648)
Reads the hosts file
- MessengerLite.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:07:06 16:31:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 26624 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3415 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 15.1907.1.0 |
| ProductVersionNumber: | 15.1907.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | MessengerLite |
| FileVersion: | 15.1907.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jul-2011 14:31:20 |
| Detected languages: |
|
| CompanyName: | MessengerLite |
| FileVersion: | 15.1907.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jul-2011 14:31:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000671C | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50461 |
.rdata | 0x00008000 | 0x000019D6 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02684 |
.data | 0x0000A000 | 0x0007139C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.73601 |
.ndata | 0x0007C000 | 0x00191000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0020D000 | 0x0005B318 | 0x0005B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.14923 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21684 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.13391 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.22633 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 3.27074 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.35839 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 3.5506 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.55883 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
54
Monitored processes
12
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | driverquery /FO list /v | C:\Windows\system32\driverquery.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Queries the drivers on a system Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 628 | "C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe" --type=renderer --js-flags=--expose-gc --no-sandbox --enable-deferred-image-decoding --lang=en-US --extension-process --nodejs --working-directory="C:\Users\admin\AppData\Local\Temp\nw2648_19734" --device-scale-factor=1 --font-cache-shared-mem-suffix=2648 --enable-pinch-virtual-viewport --enable-delegated-renderer --num-raster-threads=2 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2648.1.1571037024\974776538" /prefetch:673131151 | C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe | — | MessengerLite.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 816 | C:\Windows\system32\cmd.exe /C "sc QUERY NPF | FIND /C "RUNNING"" | C:\Windows\system32\cmd.exe | — | paml.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2092 | "C:\Windows\explorer.exe" C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe | C:\Windows\explorer.exe | — | paml.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe" | C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe" --type=renderer --js-flags=--expose-gc --no-sandbox --enable-deferred-image-decoding --lang=en-US --extension-process --nodejs --working-directory="C:\Users\admin\AppData\Local\Temp\nw2648_19734" --device-scale-factor=1 --font-cache-shared-mem-suffix=2648 --enable-pinch-virtual-viewport --enable-delegated-renderer --num-raster-threads=2 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2648.0.1876437883\1522909533" /prefetch:673131151 | C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe | MessengerLite.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3160 | C:\Windows\system32\cmd.exe /s /c "driverquery /FO list /v" | C:\Windows\system32\cmd.exe | — | MessengerLite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3340 | "C:\Users\admin\AppData\Local\Temp\paml.exe" | C:\Users\admin\AppData\Local\Temp\paml.exe | explorer.exe | ||||||||||||
User: admin Company: MessengerLite Integrity Level: HIGH Exit code: 0 Version: 15.1907.1.0 Modules
| |||||||||||||||
| 3456 | FIND /C "RUNNING" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | sc QUERY NPF | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 722
Read events
504
Write events
1 218
Delete events
0
Modification events
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MessengerLite |
| Operation: | write | Name: | DisplayName |
Value: MessengerLite - Facebook Messenger for Desktop | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MessengerLite |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Roaming\MessengerLite\Uninstall.exe" | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MessengerLite |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Users\admin\AppData\Roaming\MessengerLite\Uninstall.exe" | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MessengerLite |
| Operation: | write | Name: | Publisher |
Value: MessengerLite | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MessengerLite |
| Operation: | write | Name: | DisplayVersion |
Value: 15.1907.1paml | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MessengerLite |
| Operation: | write | Name: | EstimatedSize |
Value: 67965 | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MessengerLite |
Value: C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe su | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\MessengerLite |
| Operation: | write | Name: | uid |
Value: EA59C7C4-CCD8-449D-962C-88927E22550D | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3340) paml.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
108
Text files
492
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\MessengerLite.exe | — | |
MD5:— | SHA256:— | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\nw.pak | — | |
MD5:— | SHA256:— | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Local\Temp\nsz9F56.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\locales\ar.pak | binary | |
MD5:7C321056F805AABD5A503821FA1994CD | SHA256:261E6AAD3AD0A5F608B5694919EE39026C4C3EB4256540068F7C1AA46BE9315A | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Local\Temp\nsz9F56.tmp\nsDialogs.dll | executable | |
MD5:635E0750D89A69FCFCA2EFAE8B65C0F2 | SHA256:7F7AF08E55E792805930C9090147085A047FBD8FD820BA72DF3783B8FDF26F87 | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\ffmpegsumo.dll | executable | |
MD5:— | SHA256:— | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Local\Temp\nsz9F56.tmp\System.dll | executable | |
MD5:5CCDE6CBE28A74C393F2B7B6F5CC7458 | SHA256:2C2DB6B7CA5781A34C30C42C18EC1ECE1284B8D500FD0251FA383FD7B1EEB6E0 | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\locales\es.pak | binary | |
MD5:7C321056F805AABD5A503821FA1994CD | SHA256:261E6AAD3AD0A5F608B5694919EE39026C4C3EB4256540068F7C1AA46BE9315A | |||
| 3340 | paml.exe | C:\Users\admin\AppData\Roaming\MessengerLite\locales\es-419.pak | binary | |
MD5:7C321056F805AABD5A503821FA1994CD | SHA256:261E6AAD3AD0A5F608B5694919EE39026C4C3EB4256540068F7C1AA46BE9315A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3340 | paml.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3340 | paml.exe | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgO0poT3hl3id1qmUtN9n73Iaw%3D%3D | unknown | der | 527 b | whitelisted |
3104 | MessengerLite.exe | POST | 200 | 172.217.22.78:80 | http://172.217.22.78:80/collect | US | image | 35 b | whitelisted |
3104 | MessengerLite.exe | POST | 200 | 172.217.22.78:80 | http://172.217.22.78:80/collect | US | image | 35 b | whitelisted |
3104 | MessengerLite.exe | POST | 200 | 172.217.22.78:80 | http://172.217.22.78:80/collect | US | image | 35 b | whitelisted |
3340 | paml.exe | POST | 200 | 172.217.22.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3104 | MessengerLite.exe | GET | 200 | 34.192.68.110:80 | http://34.192.68.110:80/update_manager/messengerlite/15.1907.2002?au_version=11 | US | text | 49 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3340 | paml.exe | 52.73.195.55:443 | track.fourtiz.com | Amazon.com, Inc. | US | unknown |
3340 | paml.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3340 | paml.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3340 | paml.exe | 172.217.22.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3104 | MessengerLite.exe | 52.4.202.19:443 | tools.fourtiz.com | Amazon.com, Inc. | US | unknown |
3104 | MessengerLite.exe | 172.217.22.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2648 | MessengerLite.exe | 31.13.92.10:443 | www.messenger.com | Facebook, Inc. | IE | whitelisted |
2648 | MessengerLite.exe | 31.13.92.14:443 | static.xx.fbcdn.net | Facebook, Inc. | IE | whitelisted |
3104 | MessengerLite.exe | 35.168.165.30:443 | info.wikitextbooks.info | Amazon.com, Inc. | US | unknown |
2648 | MessengerLite.exe | 87.245.208.81:443 | scontent.frix7-1.fna.fbcdn.net | RETN Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
track.fourtiz.com |
| shared |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
www.google-analytics.com |
| whitelisted |
tools.fourtiz.com |
| shared |
www.messenger.com |
| suspicious |
info.wikitextbooks.info |
| malicious |
static.xx.fbcdn.net |
| whitelisted |
scontent.frix7-1.fna.fbcdn.net |
| unknown |
connect.facebook.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3340 | paml.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |