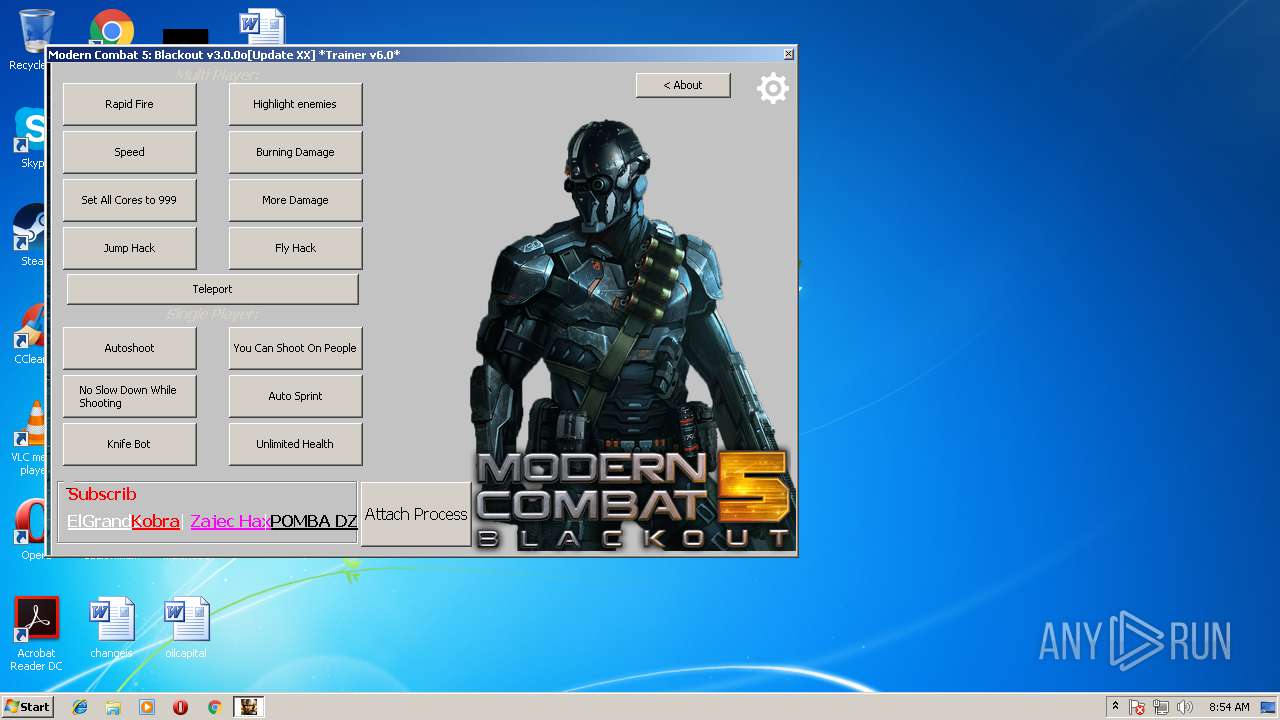
| File name: | MC5 Trainer v6.0.EXE |
| Full analysis: | https://app.any.run/tasks/69f7a64a-a0ef-4844-aa6c-8662d6c5294f |
| Verdict: | No threats detected |
| Analysis date: | July 23, 2018, 07:53:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 10D6293FB8C7F88ABBFB4AD631A120FD |
| SHA1: | AE66ADE4FA7306CDE0BCE7B3083174588486673D |
| SHA256: | 476F577334AD38C2A12A4AAA8878937960B0E517AD6F6057DE58BCB1F6D74FD3 |
| SSDEEP: | 196608:jJgXVfK50mq0+So4ldiZodmK/4/g3ek+wa+vyaCYzje/OH19nIzo6SeS6HldKZad:je+PdiZ6d3RpjeCRIzf9kVmUTK |
MALICIOUS
Application was dropped or rewritten from another process
- MC5 Trainer v6.0.EXE (PID: 700)
- MC5 Trainer v6.0.EXE (PID: 2896)
Loads dropped or rewritten executable
- MC5 Trainer v6.0.EXE (PID: 700)
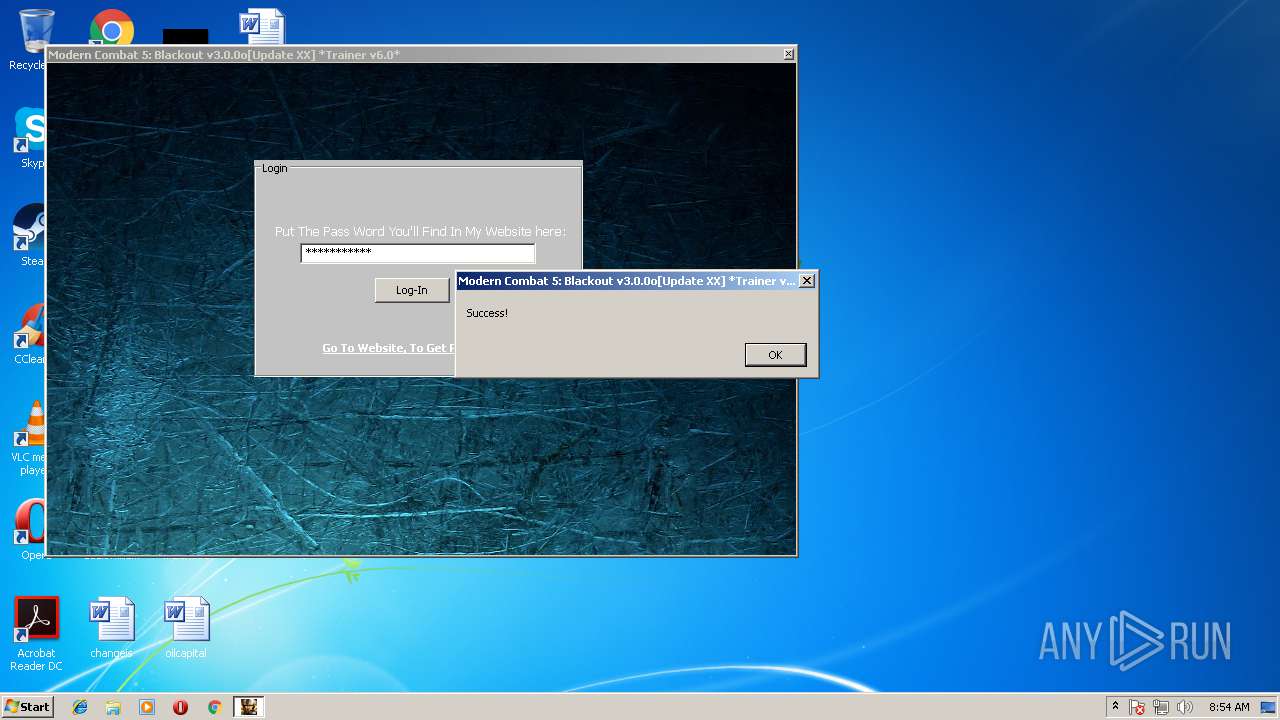
SUSPICIOUS
Executable content was dropped or overwritten
- MC5 Trainer v6.0.EXE (PID: 3508)
- MC5 Trainer v6.0.EXE (PID: 2896)
INFO
Dropped object may contain URL's
- MC5 Trainer v6.0.EXE (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:28 16:45:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 36352 |
| InitializedDataSize: | 10053120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x15eb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Jun-2013 14:45:44 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-Jun-2013 14:45:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008D54 | 0x00008E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56215 |
.rdata | 0x0000A000 | 0x00002114 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44357 |
.data | 0x0000D000 | 0x00002ADC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.1026 |
.rsrc | 0x00010000 | 0x00992314 | 0x00992400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99134 |
.reloc | 0x009A3000 | 0x00000EEA | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.32883 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77792 | 357 | Latin 1 / Western European | English - United States | RT_MANIFEST |
101 | 7.94197 | 4118 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
ARCHIVE | 7.99915 | 7642363 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DECOMPRESSOR | 6.11488 | 194048 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
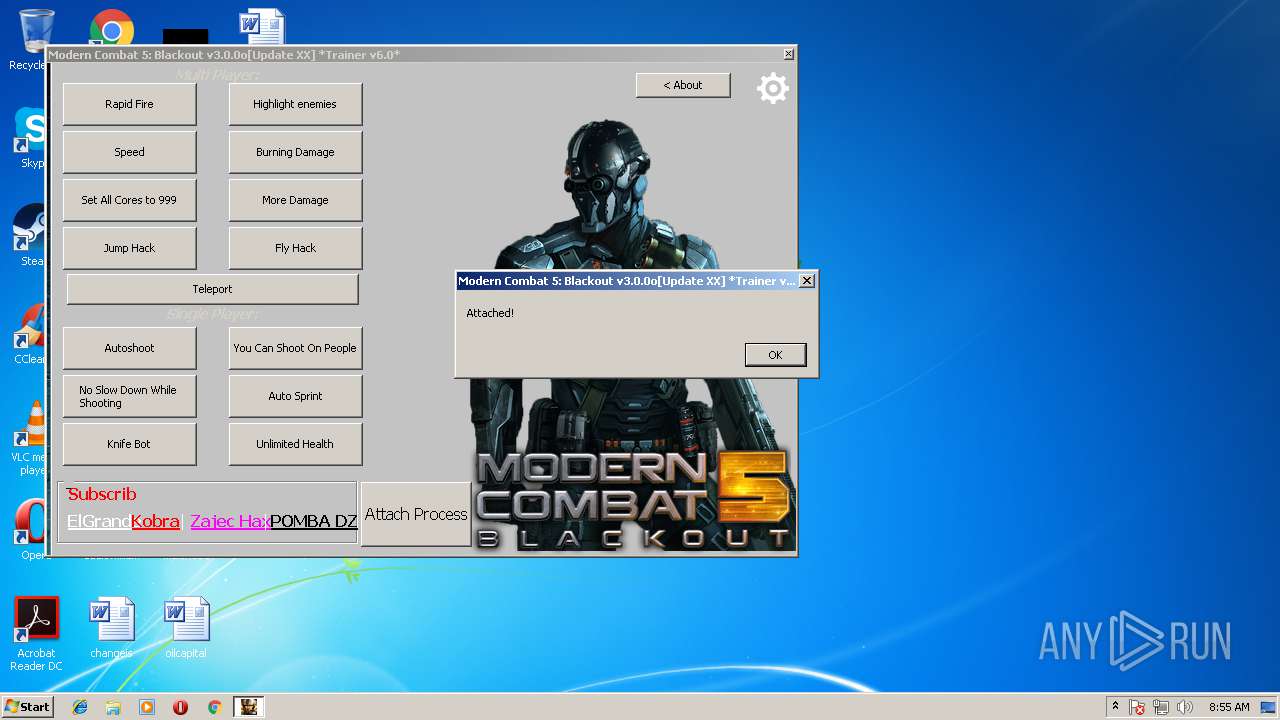
| 700 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\MC5 Trainer v6.0.EXE" "C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\CET_TRAINER.CETRAINER" "-ORIGIN:C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\MC5 Trainer v6.0.EXE | MC5 Trainer v6.0.EXE | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 6.7.0.5198 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\MC5 Trainer v6.0.EXE" -ORIGIN:"C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\MC5 Trainer v6.0.EXE | MC5 Trainer v6.0.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
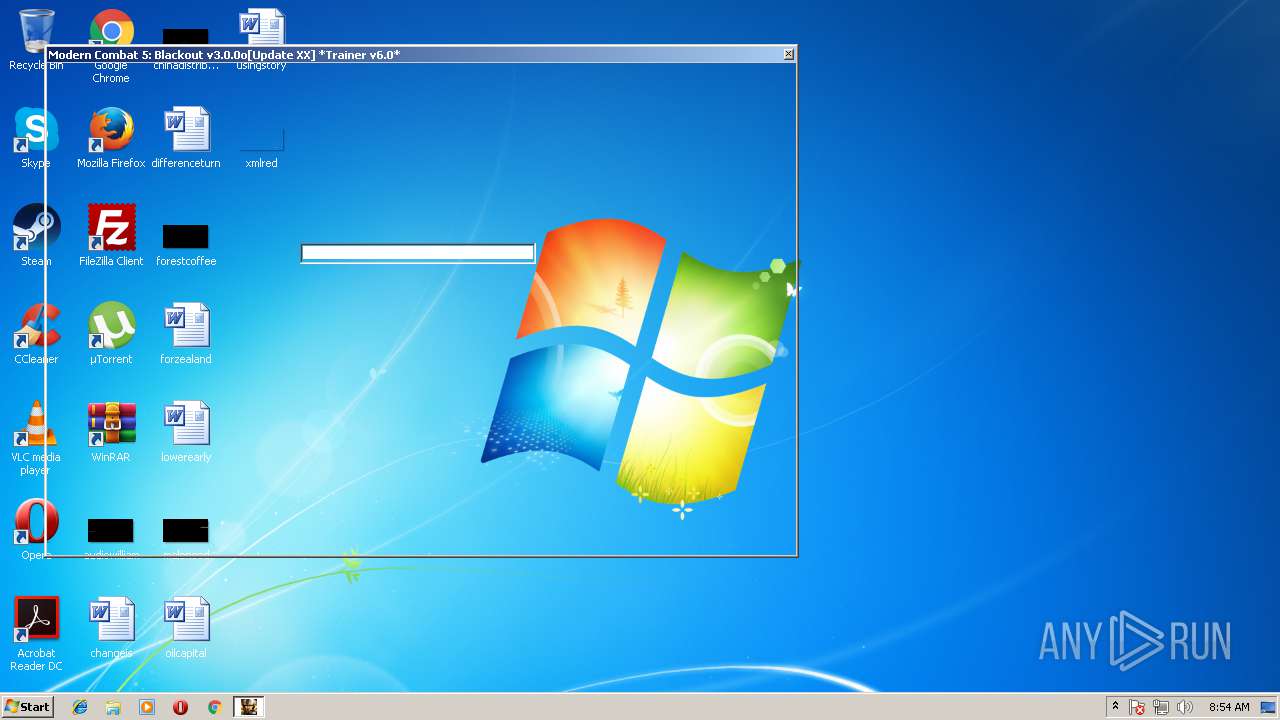
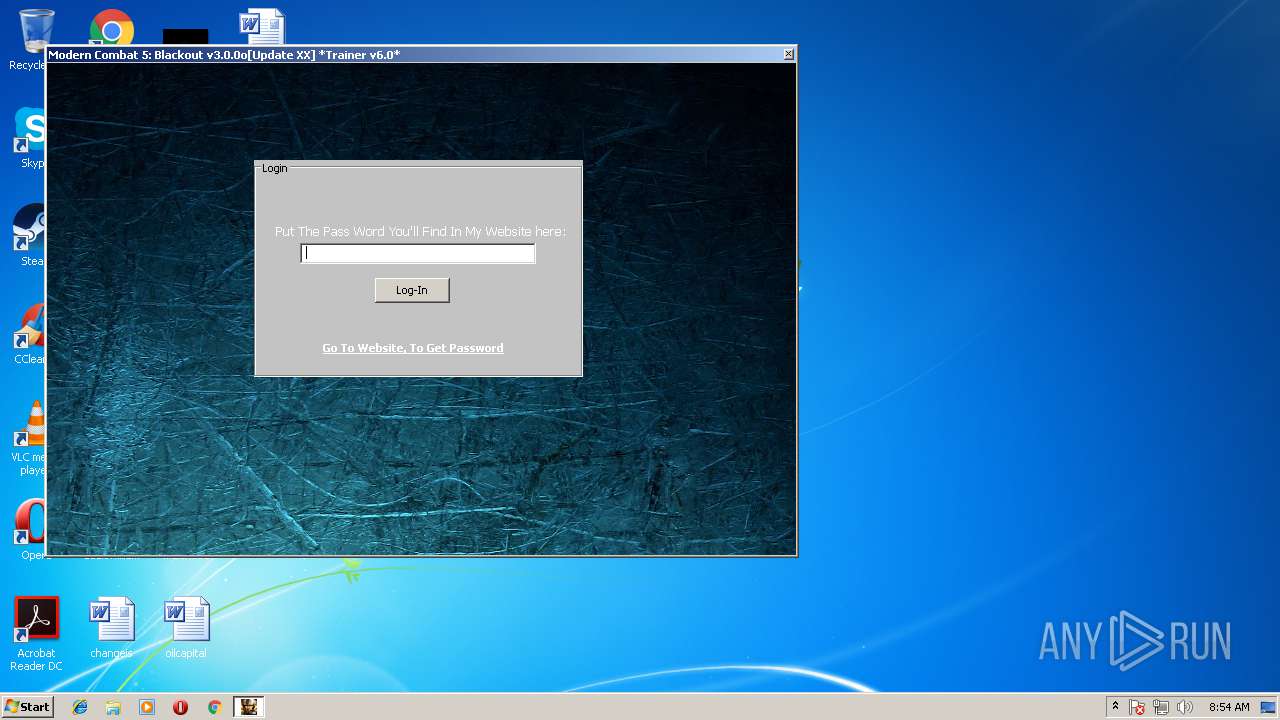
| 3256 | "C:\Users\admin\AppData\Local\Temp\MC5 Trainer v6.0.EXE" | C:\Users\admin\AppData\Local\Temp\MC5 Trainer v6.0.EXE | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\Temp\MC5 Trainer v6.0.EXE" | C:\Users\admin\AppData\Local\Temp\MC5 Trainer v6.0.EXE | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
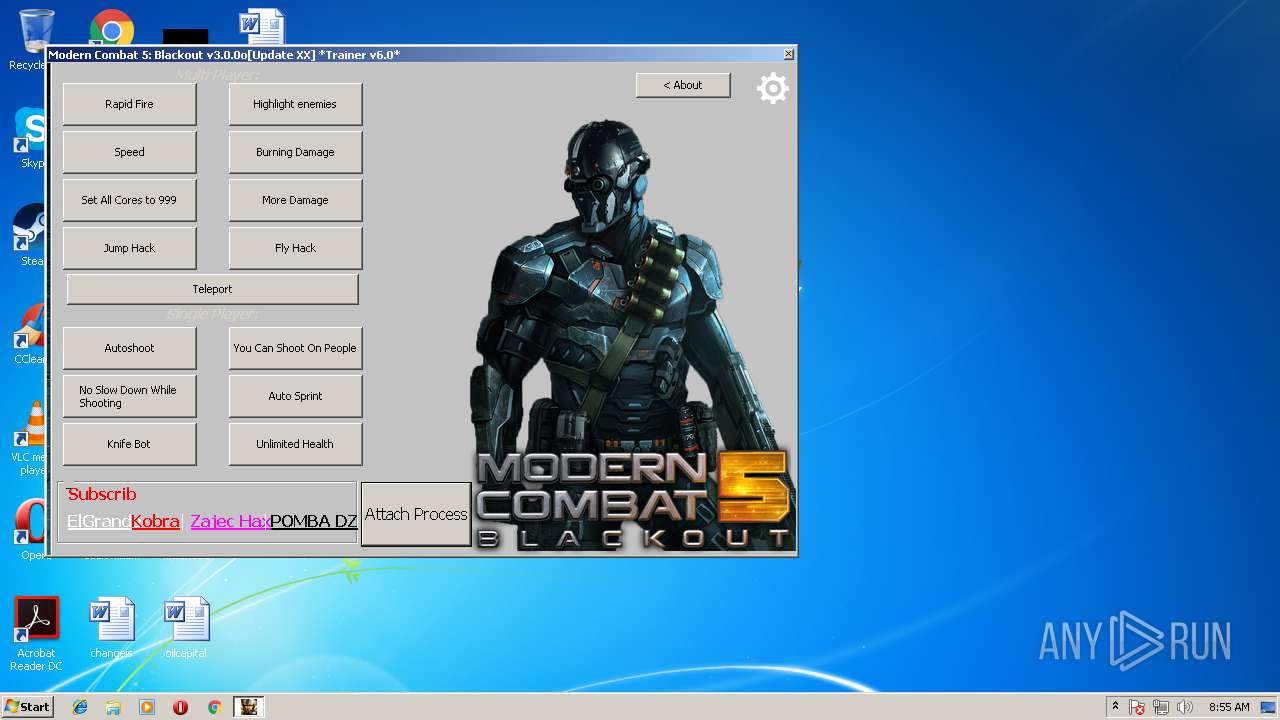
Total events
32
Read events
30
Write events
2
Delete events
0
Modification events
| (PID) Process: | (700) MC5 Trainer v6.0.EXE | Key: | HKEY_CURRENT_USER\Software\Cheat Engine\Window Positions 96 |
| Operation: | write | Name: | AdvancedOptions Position |
Value: C0000000000100003B0200002F010000 | |||
| (PID) Process: | (700) MC5 Trainer v6.0.EXE | Key: | HKEY_CURRENT_USER\Software\Cheat Engine\Window Positions 96 |
| Operation: | write | Name: | frmAutoInject Position |
Value: AE010000E5020000AF0100004B010000 | |||
Executable files
6
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\CET_Archive.dat | — | |
MD5:— | SHA256:— | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\CET_TRAINER.CETRAINER | binary | |
MD5:— | SHA256:— | |||
| 3508 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\MC5 Trainer v6.0.EXE | executable | |
MD5:A65C29111A4CF5A7FDD5A9D79F77BCAB | SHA256:DAB3003436B6861AE220CC5FDCB97970FC05AFDF114C2F91E46EED627CE3D6AF | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\DotNetDataCollector32.exe | executable | |
MD5:667C6978388F40406438A0ACA762B3BF | SHA256:E40EF87EDAD9321657B7770C926534481031726CC37C20C898A4C1F15F94058E | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\DotNetDataCollector64.exe | executable | |
MD5:8D59B498EB8311EDD5C29F3930F4789B | SHA256:D26EA9B41F172C146633D2E4FAC8C50A4B0C6BB343A37CF5FB3C17598BB49971 | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\MC5 Trainer v6.0.EXE | executable | |
MD5:CAA9D29F5B5751A94A179328AAF7CC6F | SHA256:76892D1A377BF7A010D77E3C7B26E42369BA12AD066C3DB71F05E361343E9AED | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\defines.lua | text | |
MD5:AF18263191D6F3FE55AF8BD455A947BD | SHA256:A71D5867A2C1A25DFE7649549449024128DD5540A492DA76856E150FDBE07FEB | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\lua53-32.dll | executable | |
MD5:9B8D650FFC6FFF2CFE67A7E5C020CCFB | SHA256:59B9F3FA57C1B7FDD3312F864C20EAEE76BA9FCB7BB8D2542060D3533CED12C2 | |||
| 2896 | MC5 Trainer v6.0.EXE | C:\Users\admin\AppData\Local\Temp\cetrainers\CET9B73.tmp\extracted\win32\dbghelp.dll | executable | |
MD5:9139604740814E53298A5E8428BA29D7 | SHA256:150782FCA5E188762A41603E2D5C7AAD6B6419926BCADF350EBF84328E50948F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
MC5 Trainer v6.0.EXE | sizeof fxstate = 512 |
MC5 Trainer v6.0.EXE | sizeof fxstate = 512 |
MC5 Trainer v6.0.EXE | TSymhandler.create > |
MC5 Trainer v6.0.EXE | TSymhandler.create 1 |
MC5 Trainer v6.0.EXE | TSymhandler.create 2 |
MC5 Trainer v6.0.EXE | TSymhandler.create 3 |
MC5 Trainer v6.0.EXE | TSymbolListHandler.create 2 |
MC5 Trainer v6.0.EXE | TSymbolListHandler.create 2 |
MC5 Trainer v6.0.EXE | TSymbolListHandler.create exit |
MC5 Trainer v6.0.EXE | TSymhandler.create exit |