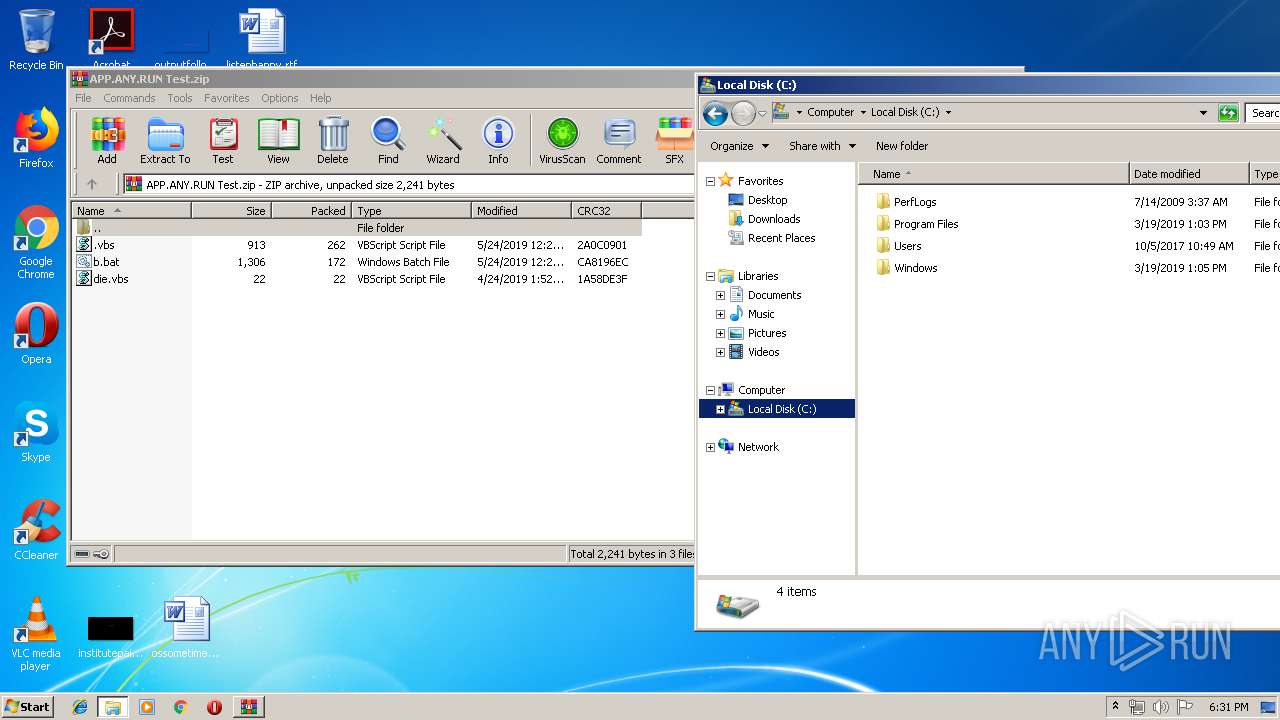
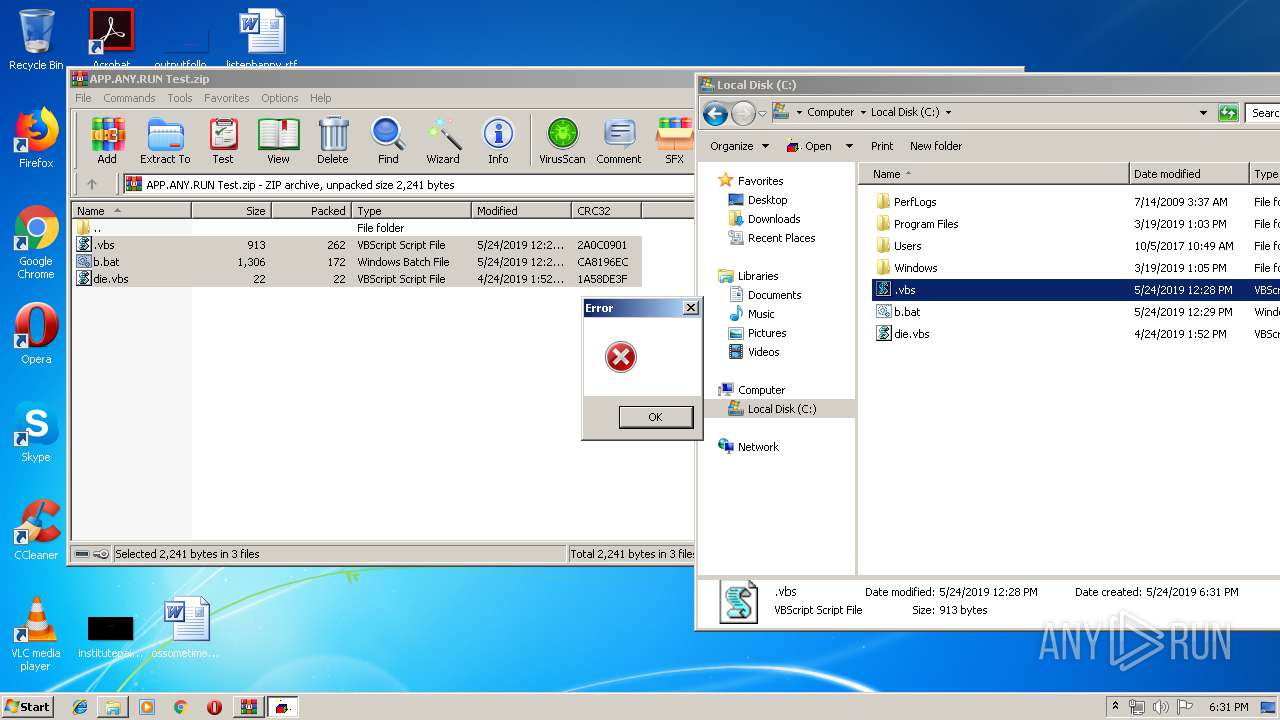
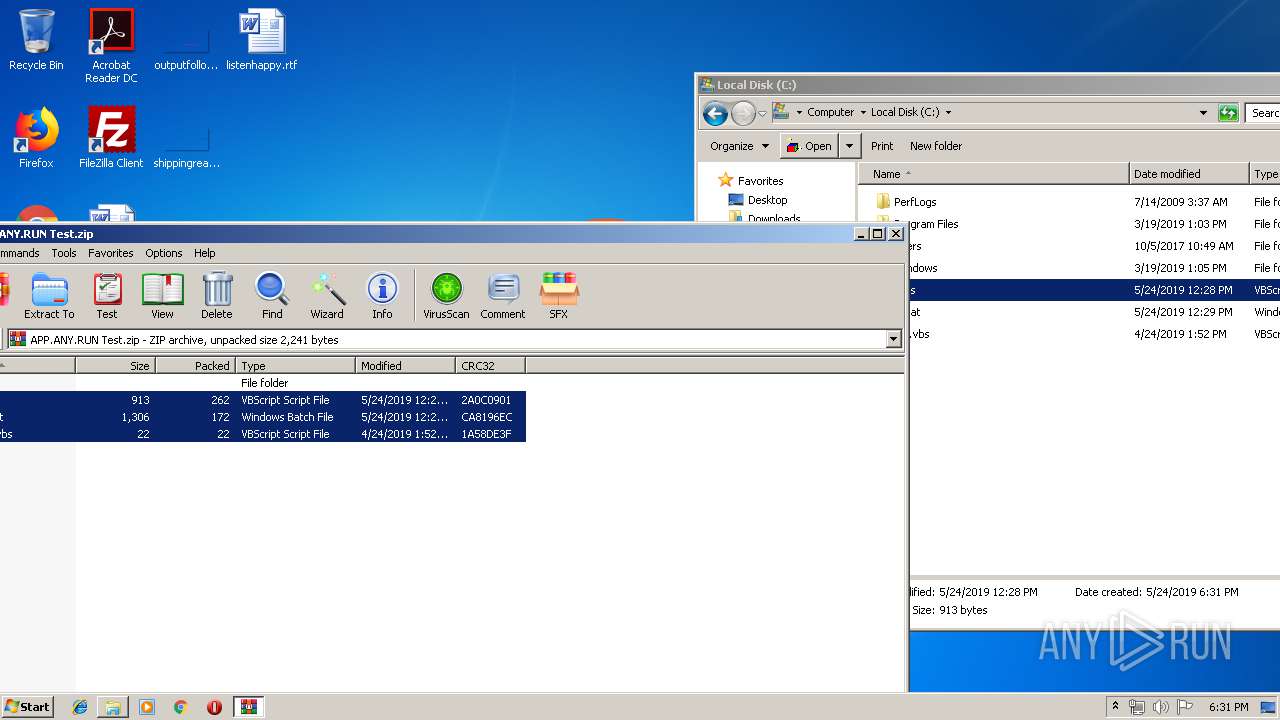
| File name: | APP.ANY.RUN Test.zip |
| Full analysis: | https://app.any.run/tasks/5f91939e-a938-4817-b7b7-043570a8ddba |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 17:31:06 |
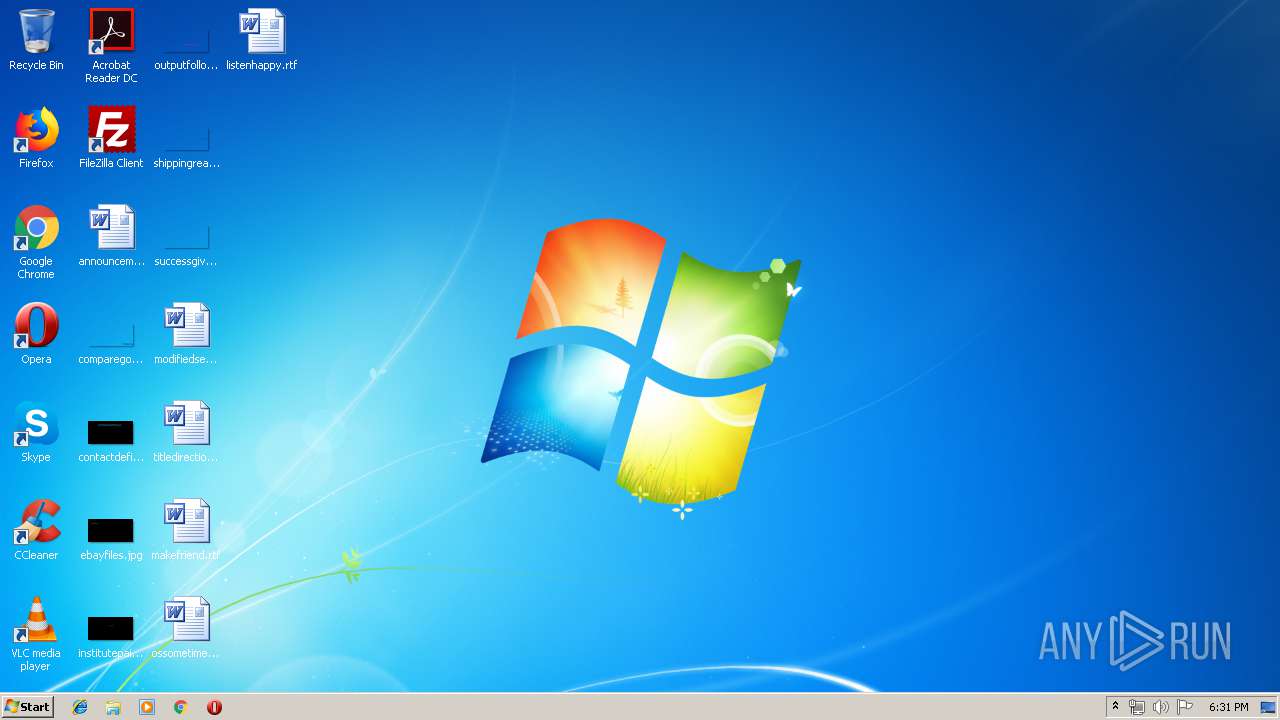
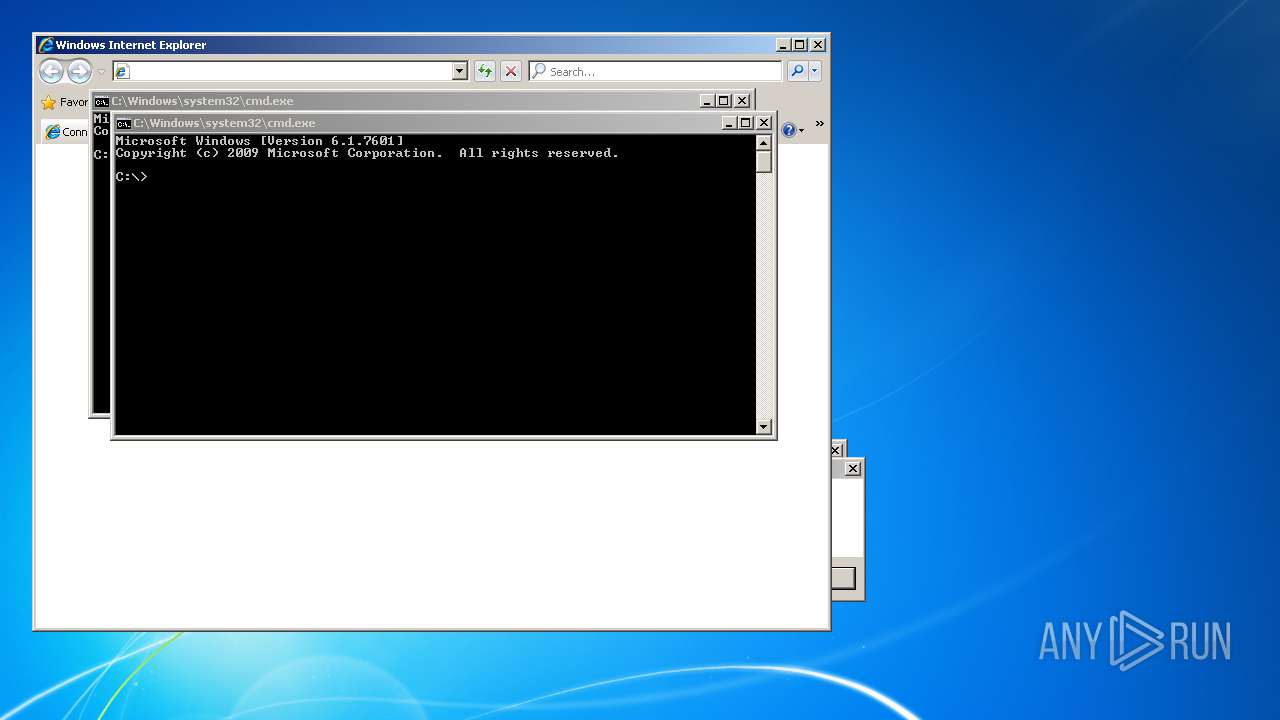
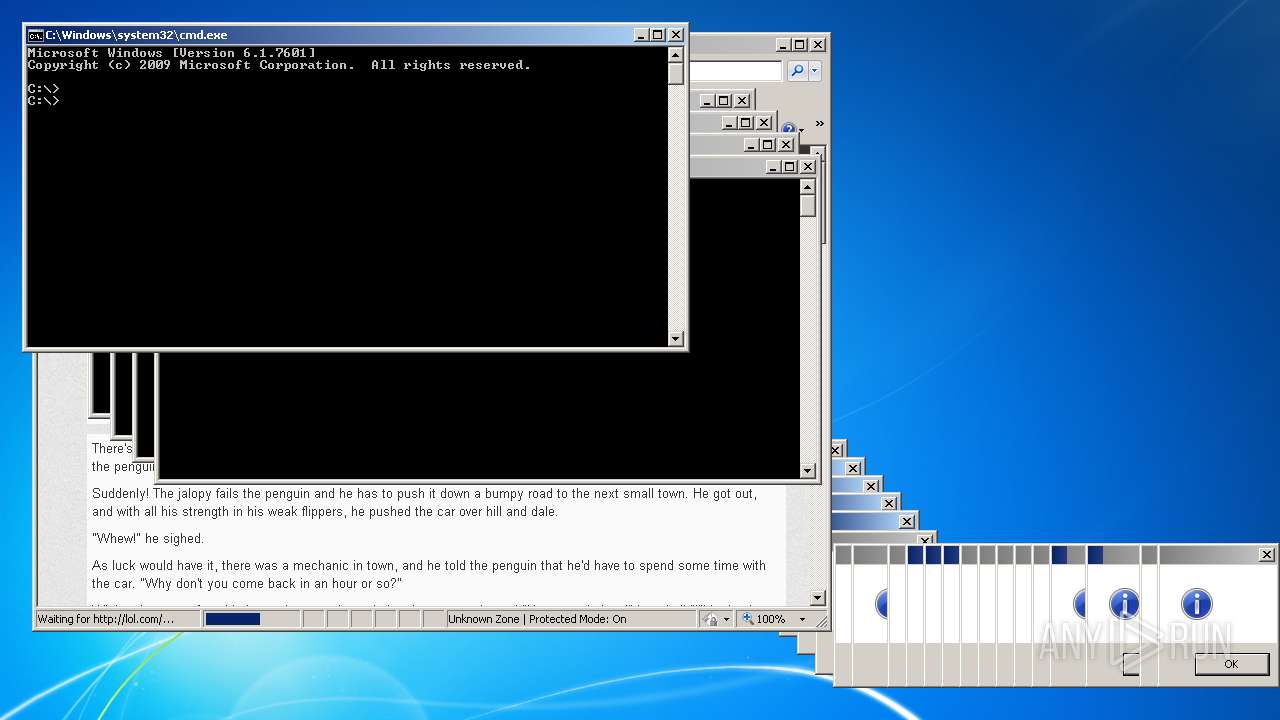
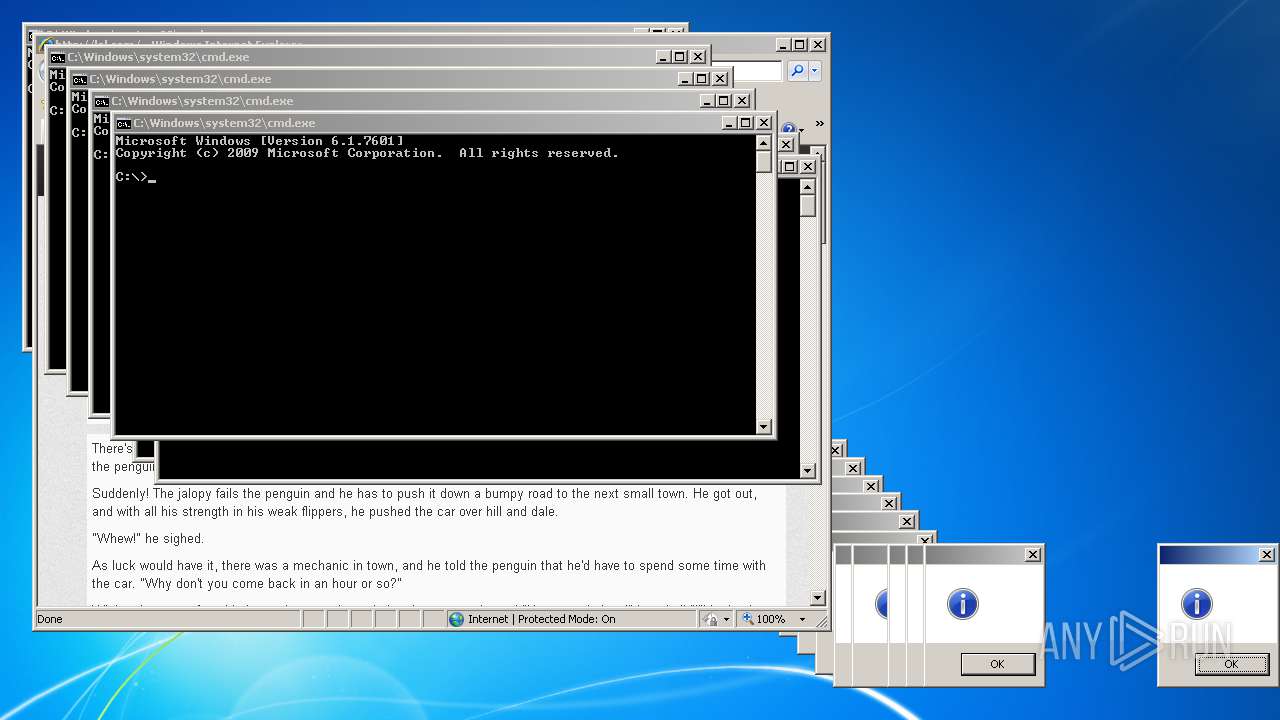
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8D24859688089DB488D67D652C276E34 |
| SHA1: | 90E2507808CCD11C8067723F933E2E2777A4D1D4 |
| SHA256: | 476ACD30DCA6EE0071359357FD6A771E293A2B0B9DE52648B78699A647C76D9F |
| SSDEEP: | 12:5jxZiZmnowd6J58RoXNZGwRAqi5NrPJEFz2q44UJ2KEy9nDUlDzIMaxrZixnEF+x:9rigJS8yN8wRAqi5NrRER2q44UJ2KVn2 |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1856)
Runs app for hidden code execution
- cmd.exe (PID: 1856)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2508)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4348)
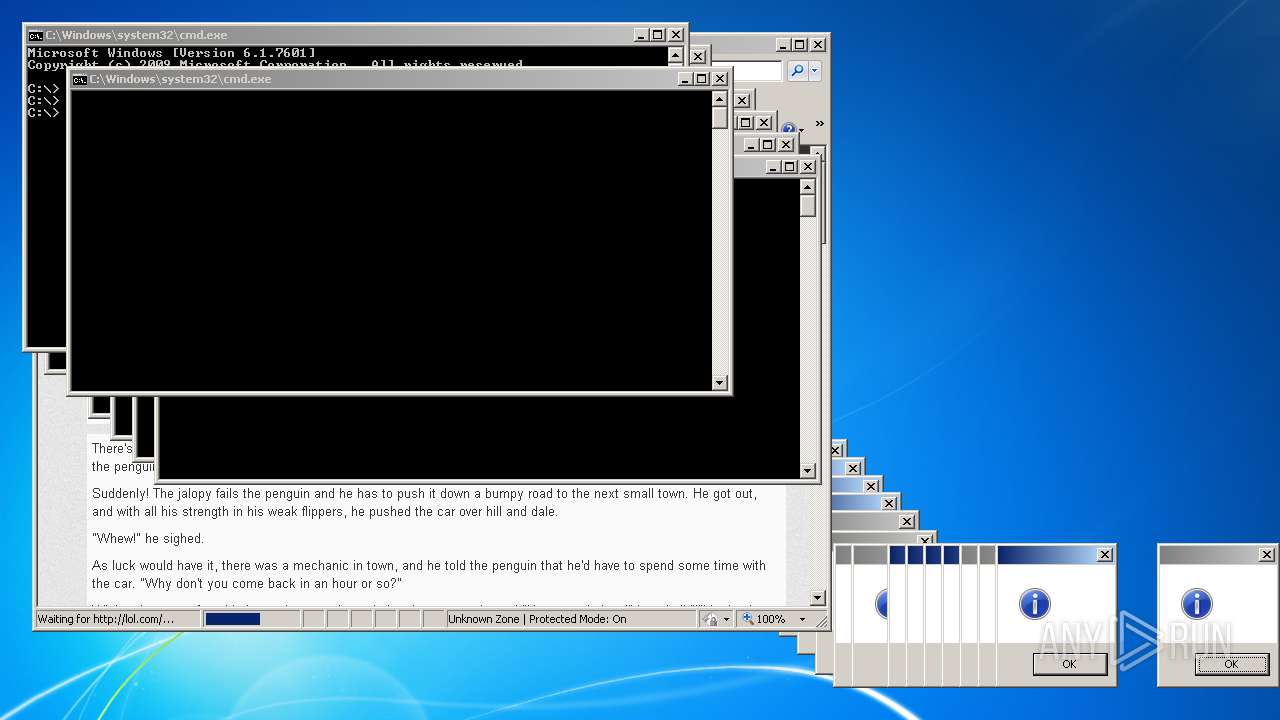
Application launched itself
- cmd.exe (PID: 1856)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1856)
- WScript.exe (PID: 2748)
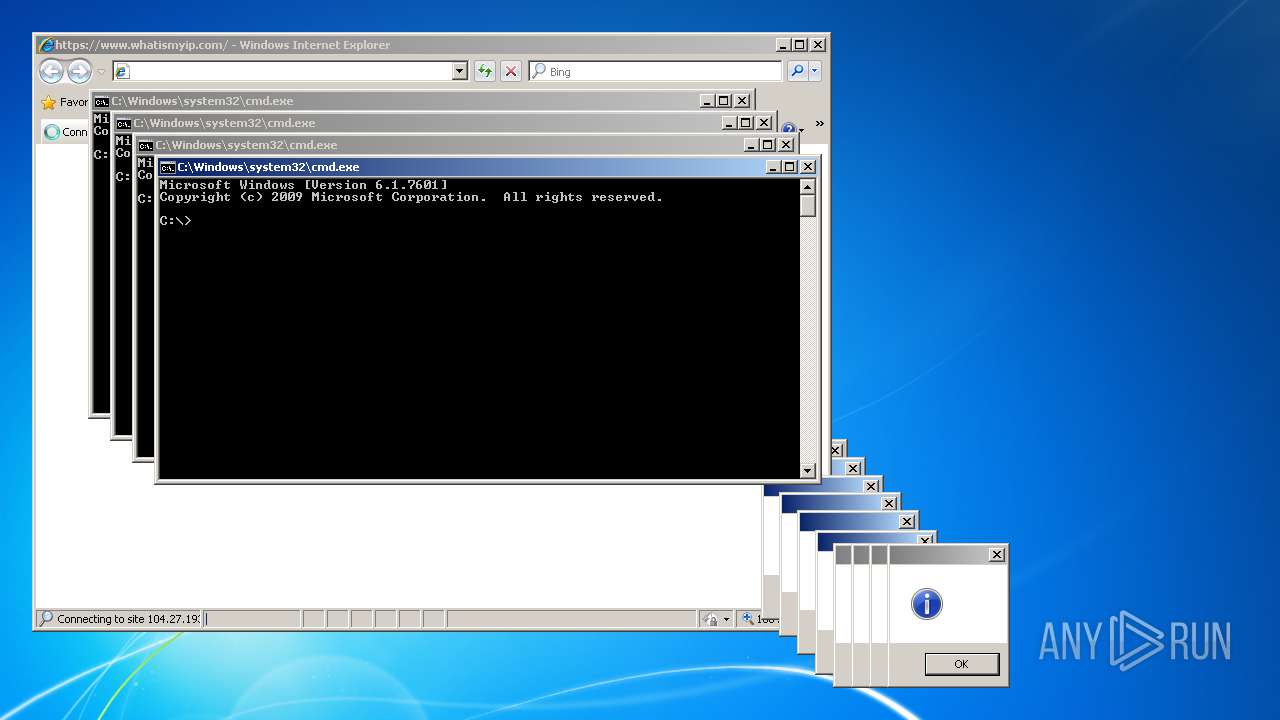
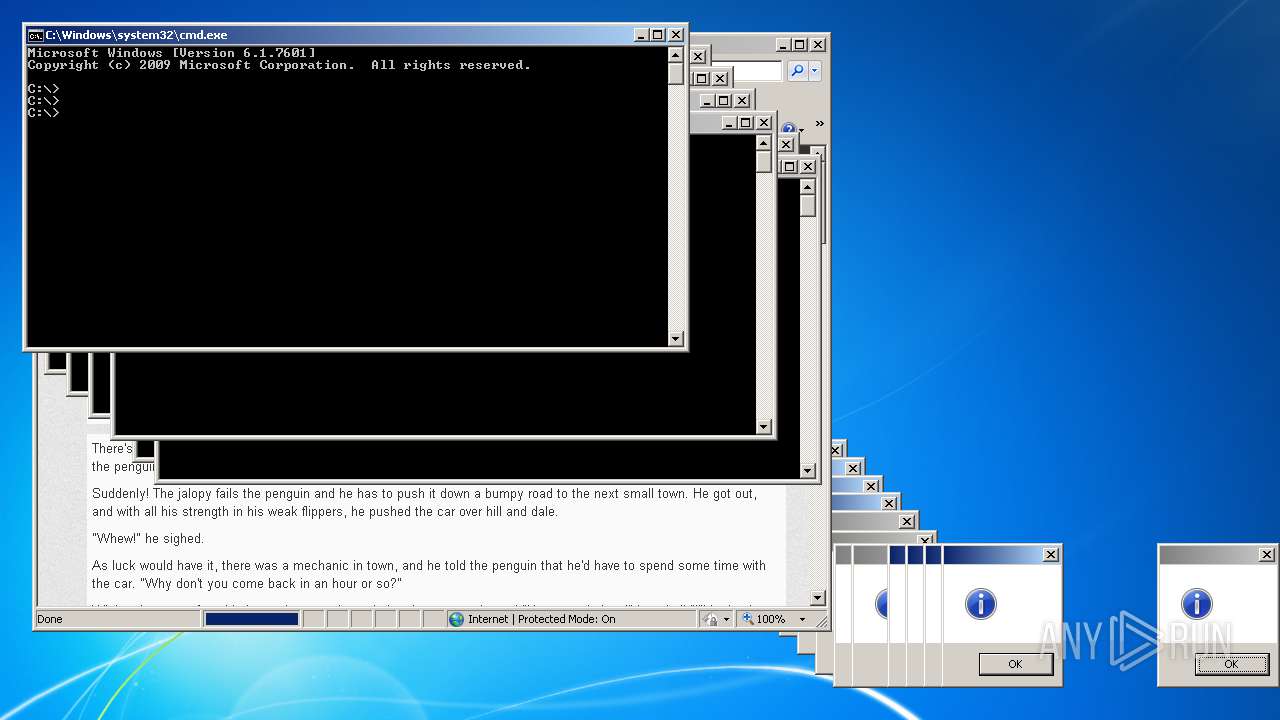
Checks for external IP
- iexplore.exe (PID: 804)
Executes scripts
- cmd.exe (PID: 1856)
Starts Internet Explorer
- cmd.exe (PID: 1856)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1856)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 1856)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 804)
Application launched itself
- iexplore.exe (PID: 2956)
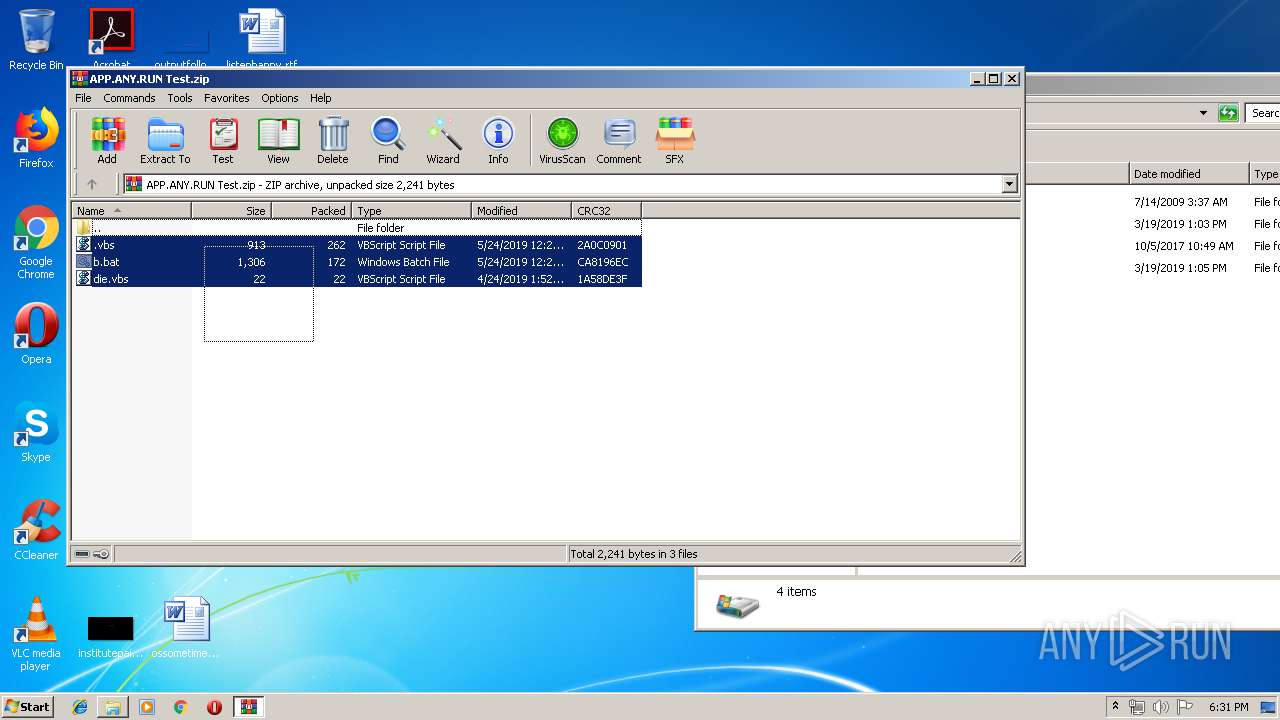
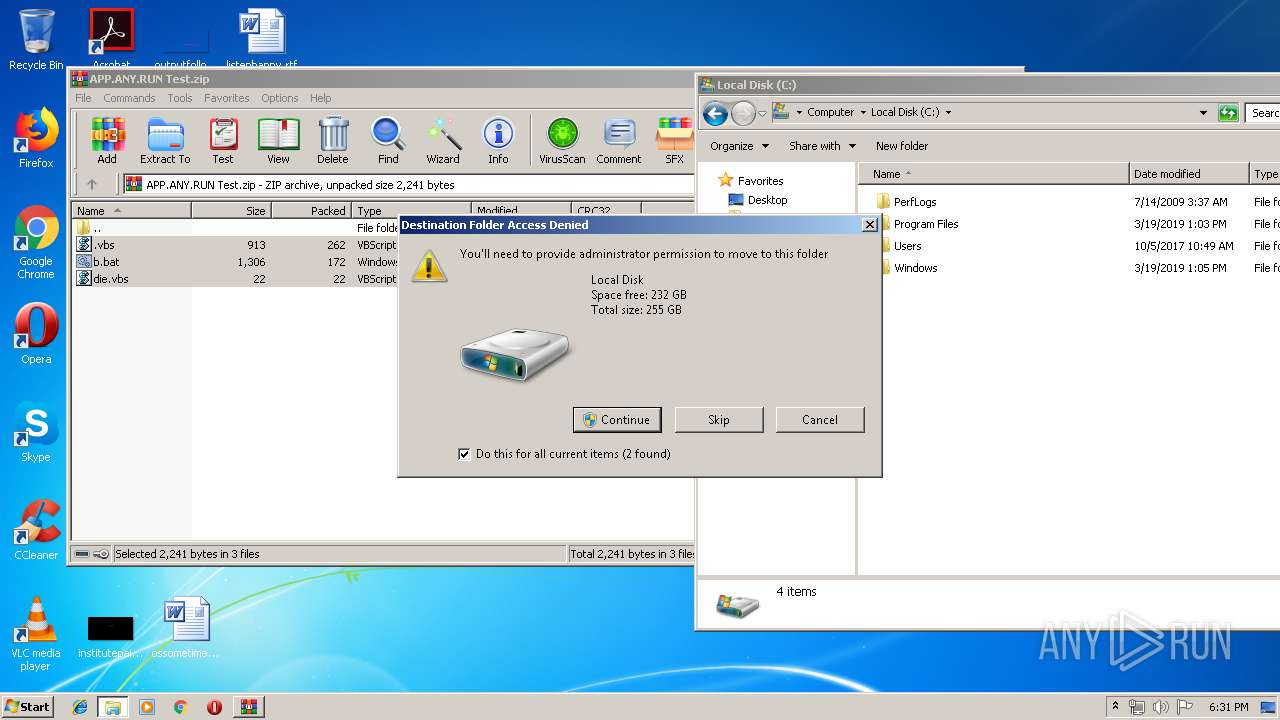
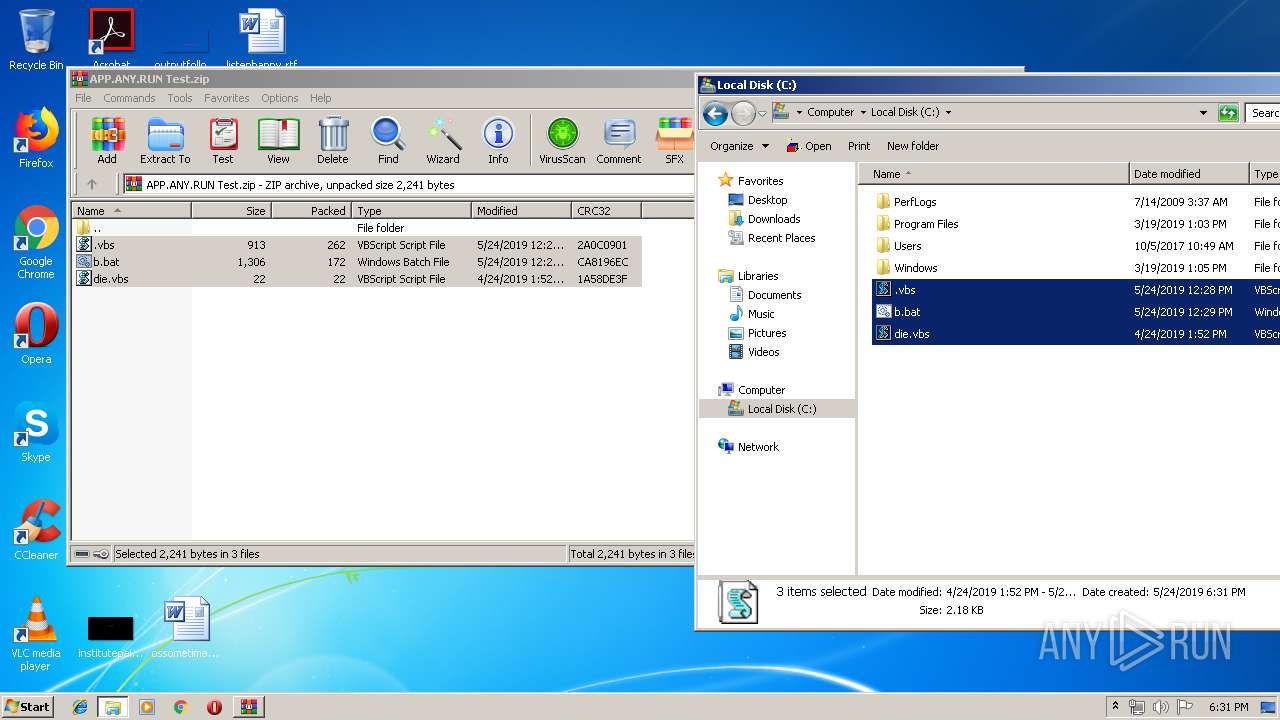
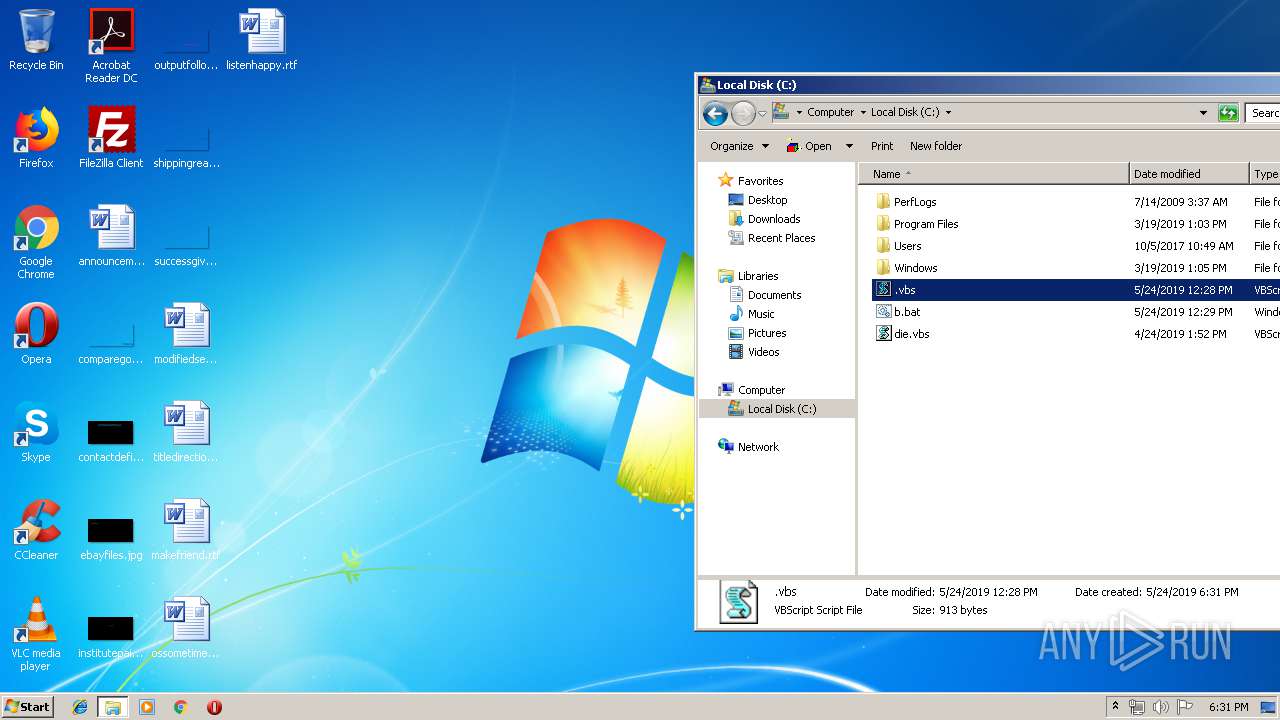
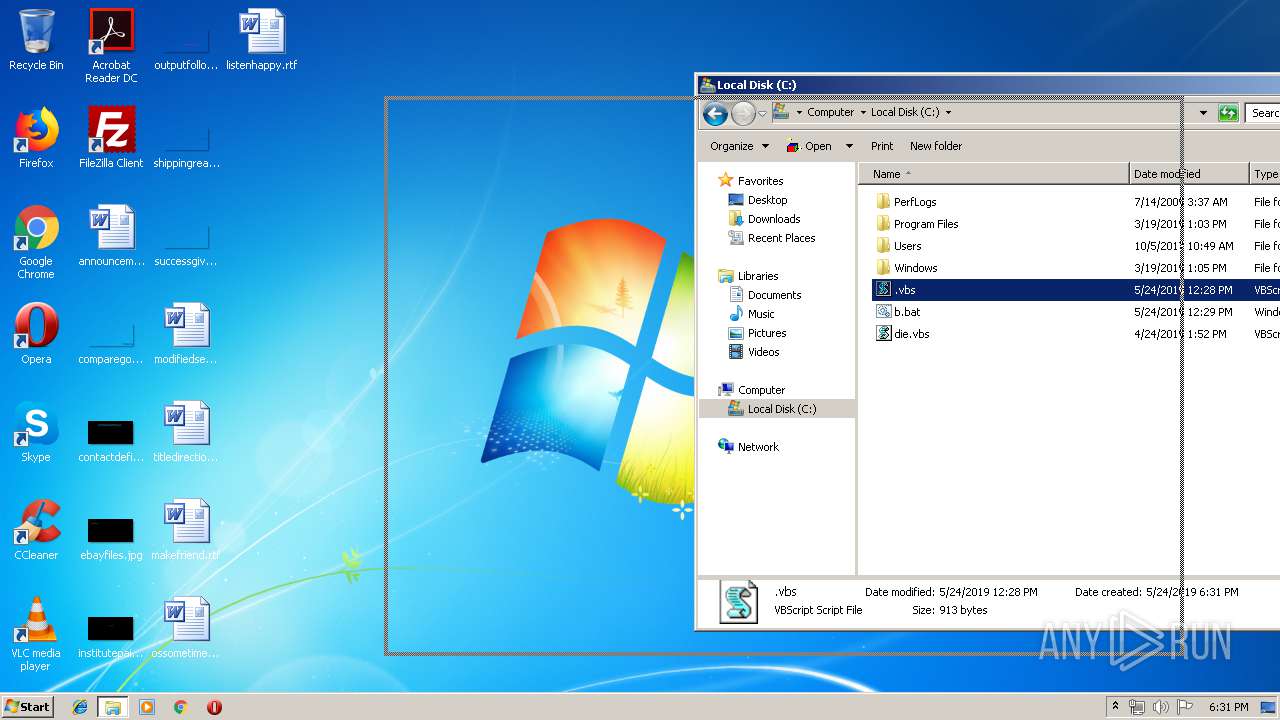
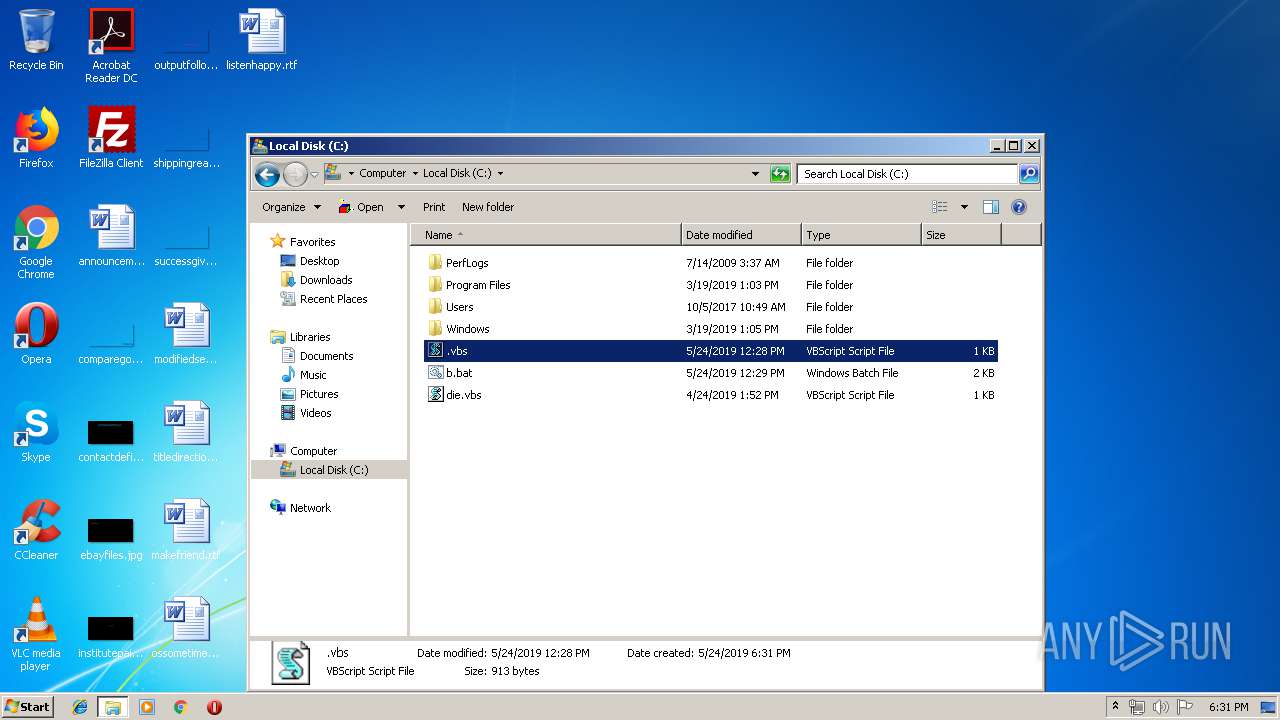
Manual execution by user
- explorer.exe (PID: 1300)
- WScript.exe (PID: 2748)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4348)
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 804)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:24 12:28:29 |
| ZipCRC: | 0x2a0c0901 |
| ZipCompressedSize: | 262 |
| ZipUncompressedSize: | 913 |
| ZipFileName: | .vbs |
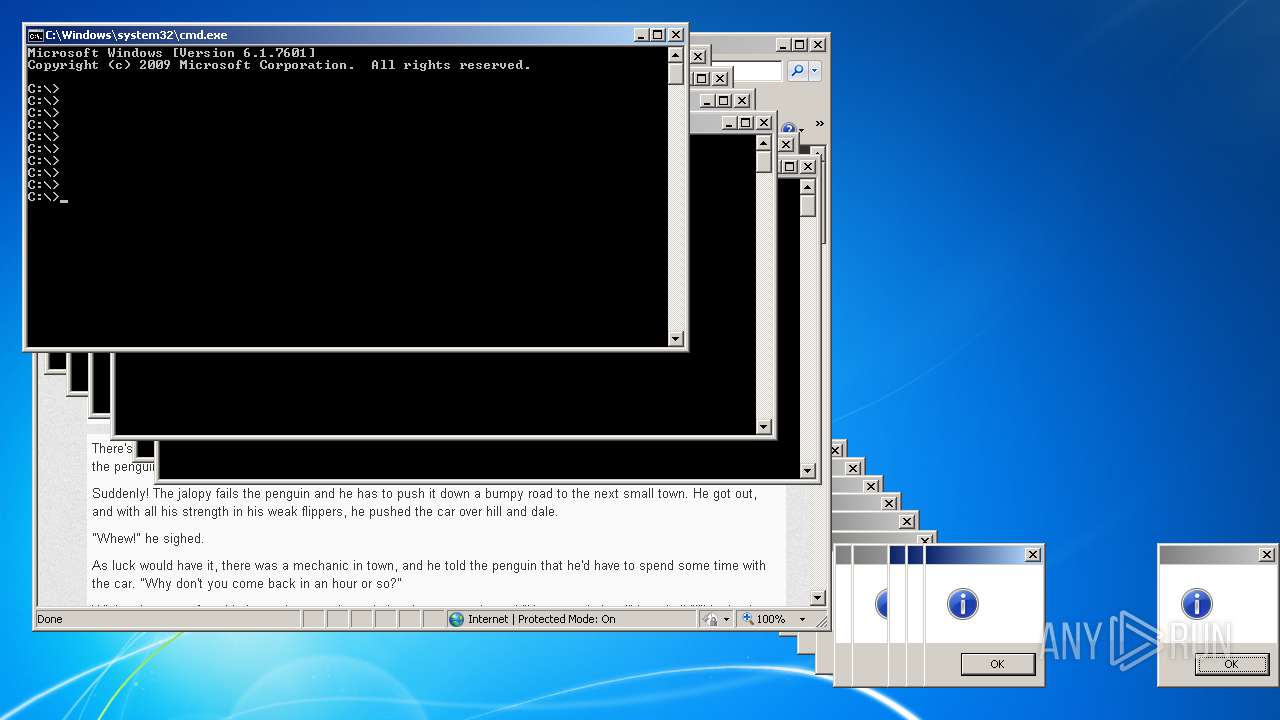
Total processes
144
Monitored processes
87
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Windows\System32\WScript.exe" "C:\die.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 580 | "C:\Windows\System32\WScript.exe" "C:\die.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 672 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | "C:\Windows\System32\WScript.exe" "C:\die.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 900 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1048 | "C:\Windows\System32\WScript.exe" "C:\die.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1156 | "C:\Windows\System32\WScript.exe" "C:\die.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1216 | "C:\Windows\System32\WScript.exe" "C:\die.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
2 200
Read events
2 096
Write events
103
Delete events
1
Modification events
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\APP.ANY.RUN Test.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
Executable files
0
Suspicious files
0
Text files
39
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2152.9891\b.bat | text | |
MD5:— | SHA256:— | |||
| 804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\CZE2S8F5\lol_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2508 | DllHost.exe | C:\die.vbs | text | |
MD5:— | SHA256:— | |||
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2152.9891\.vbs | text | |
MD5:— | SHA256:— | |||
| 2508 | DllHost.exe | C:\.vbs | text | |
MD5:— | SHA256:— | |||
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2152.9891\die.vbs | text | |
MD5:— | SHA256:— | |||
| 2508 | DllHost.exe | C:\b.bat | text | |
MD5:— | SHA256:— | |||
| 804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
14
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
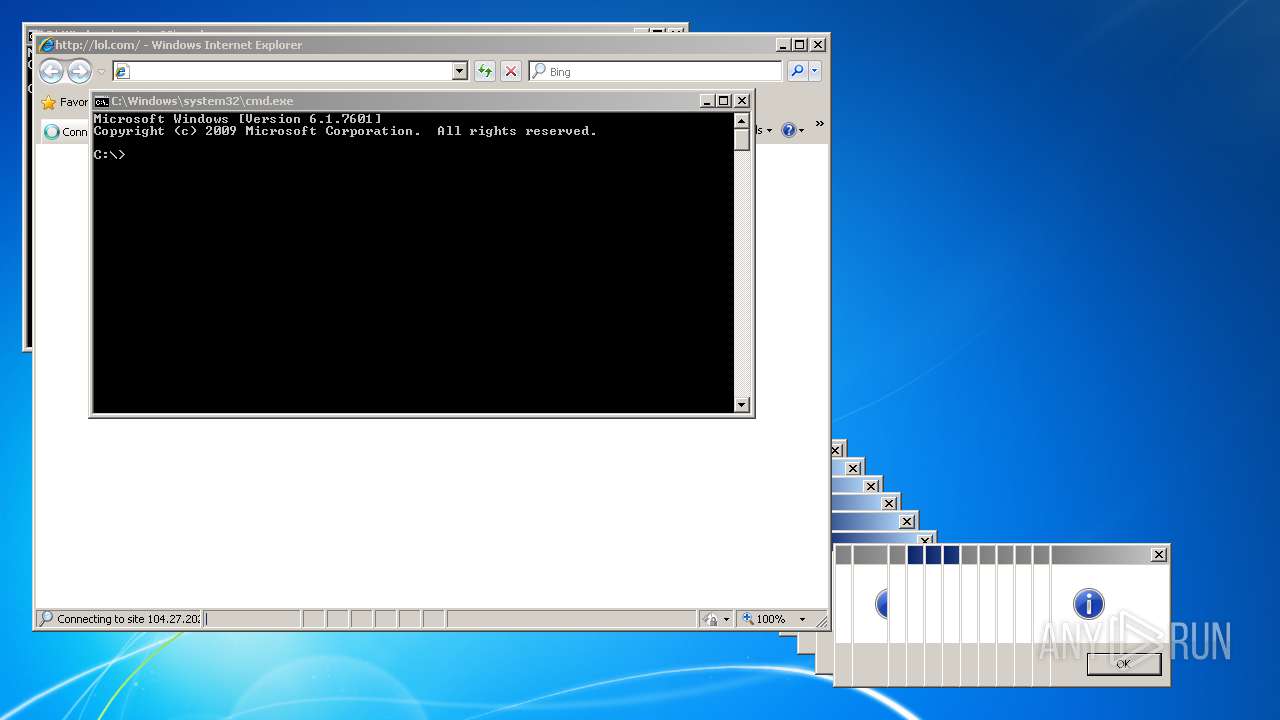
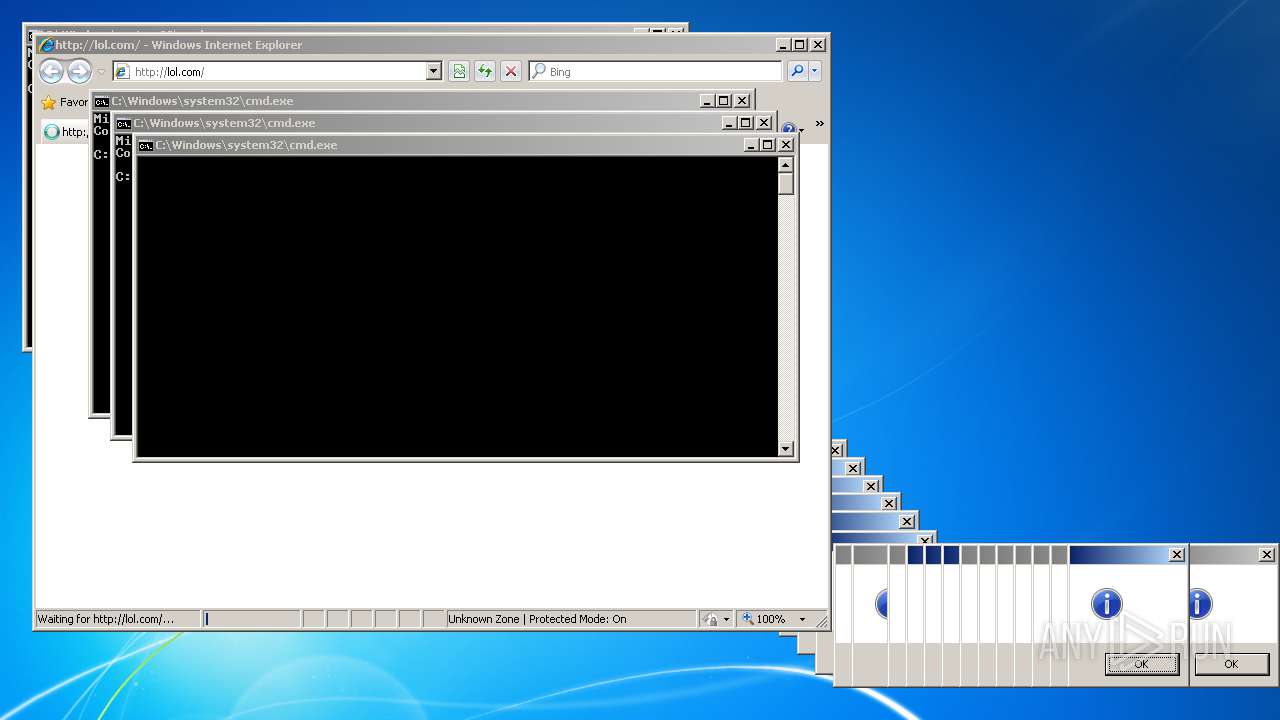
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/css/style.css | US | text | 338 b | malicious |
804 | iexplore.exe | GET | 200 | 172.217.18.162:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 23.4 Kb | whitelisted |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/css/bootstrap.css | US | text | 12.2 Kb | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/ | US | html | 4.69 Kb | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/js/libs/bootstrap/collapse.js | US | text | 1.43 Kb | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/css/bootstrap-responsive.css | US | text | 2.21 Kb | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/js/libs/bootstrap/transition.js | US | text | 775 b | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/js/libs/modernizr-2.5.3-respond-1.1.0.min.js | US | html | 7.67 Kb | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/js/script.js | US | text | 39 b | malicious |
804 | iexplore.exe | GET | 200 | 104.27.202.92:80 | http://lol.com/cdn-cgi/scripts/5c5dd728/cloudflare-static/email-decode.min.js | US | html | 655 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 104.27.193.92:80 | www.whatismyip.com | Cloudflare Inc | US | shared |
804 | iexplore.exe | 104.27.193.92:443 | www.whatismyip.com | Cloudflare Inc | US | shared |
804 | iexplore.exe | 104.27.203.92:80 | www.lol.com | Cloudflare Inc | US | shared |
804 | iexplore.exe | 104.27.202.92:80 | www.lol.com | Cloudflare Inc | US | shared |
804 | iexplore.exe | 172.217.16.202:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
804 | iexplore.exe | 172.217.18.162:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
804 | iexplore.exe | 172.217.16.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2956 | iexplore.exe | 104.27.202.92:80 | www.lol.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.whatismyip.com |
| shared |
www.lol.com |
| malicious |
lol.com |
| malicious |
pagead2.googlesyndication.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
804 | iexplore.exe | Attempted Information Leak | ET POLICY IP Check Domain (whatismyip in HTTP Host) |