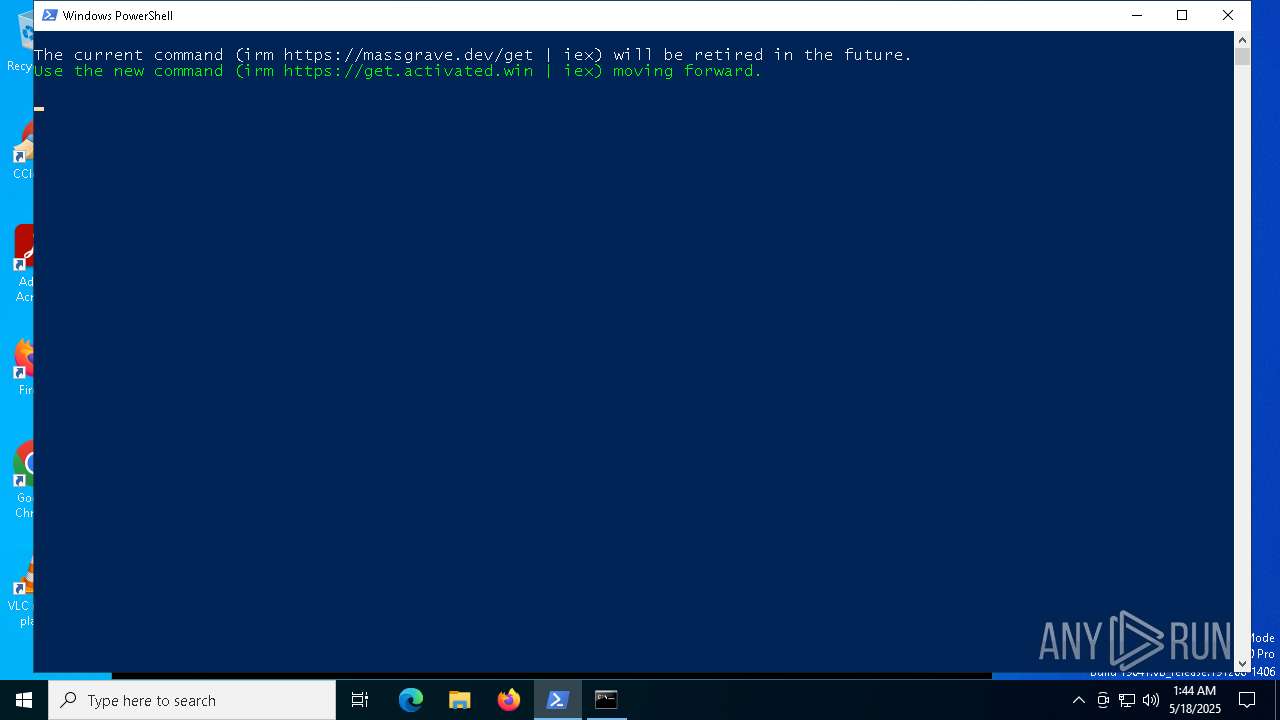
| download: | /get |
| Full analysis: | https://app.any.run/tasks/ce635eed-c841-4056-b79a-6b8b78f4ad9a |
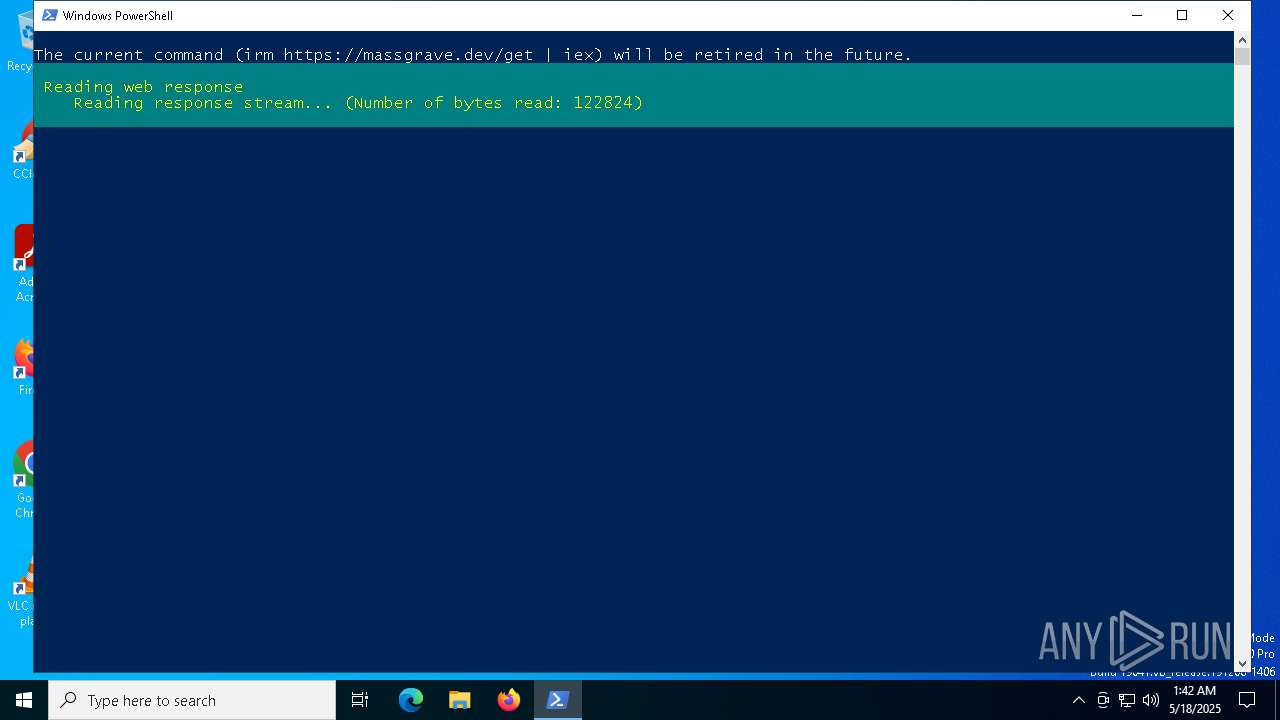
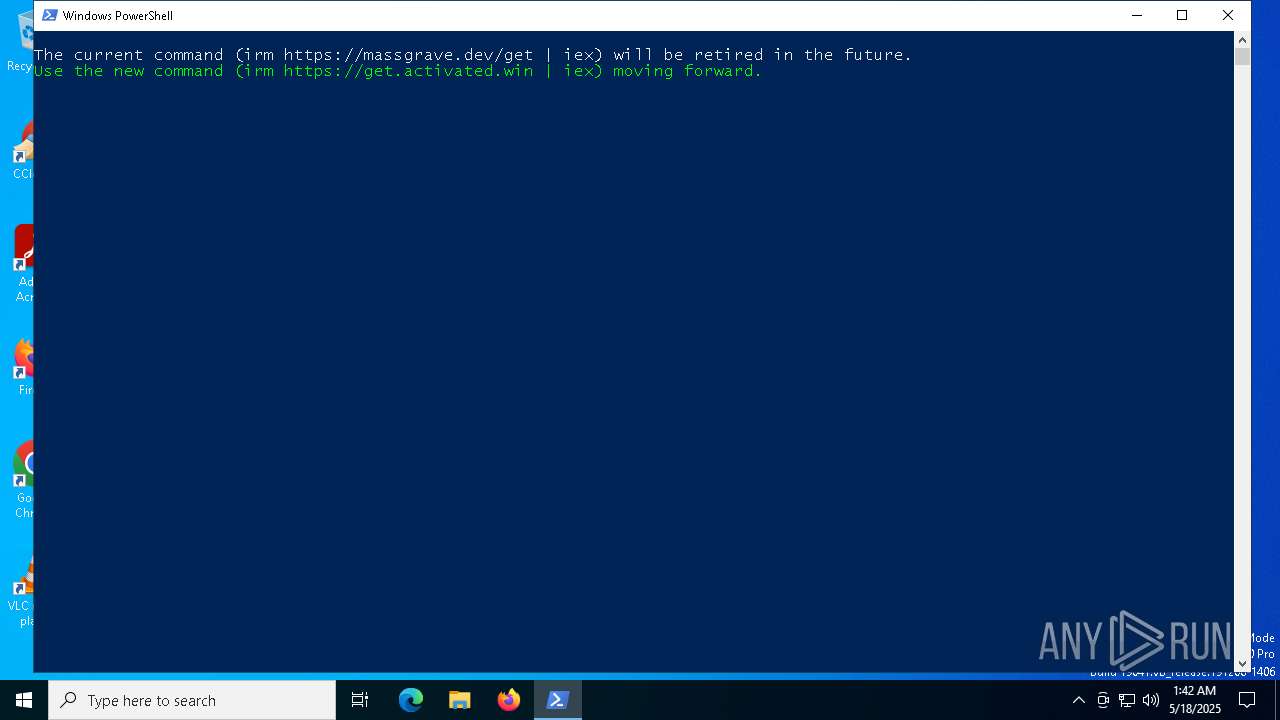
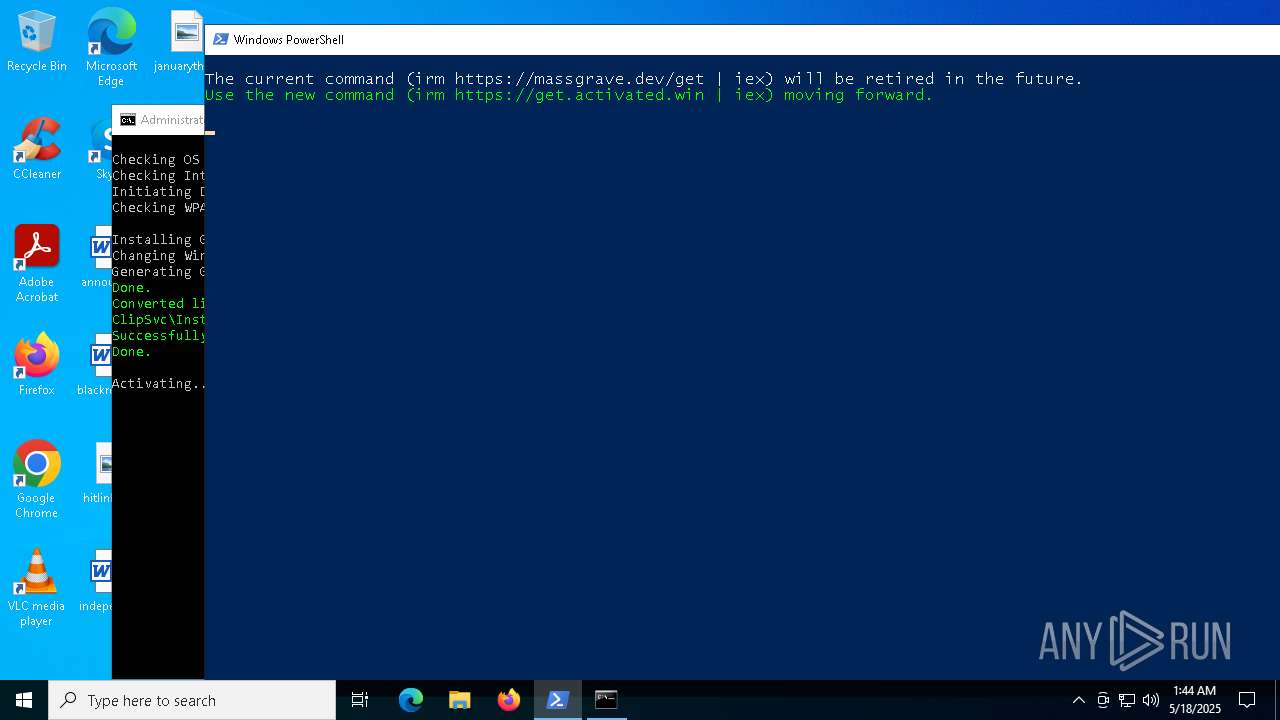
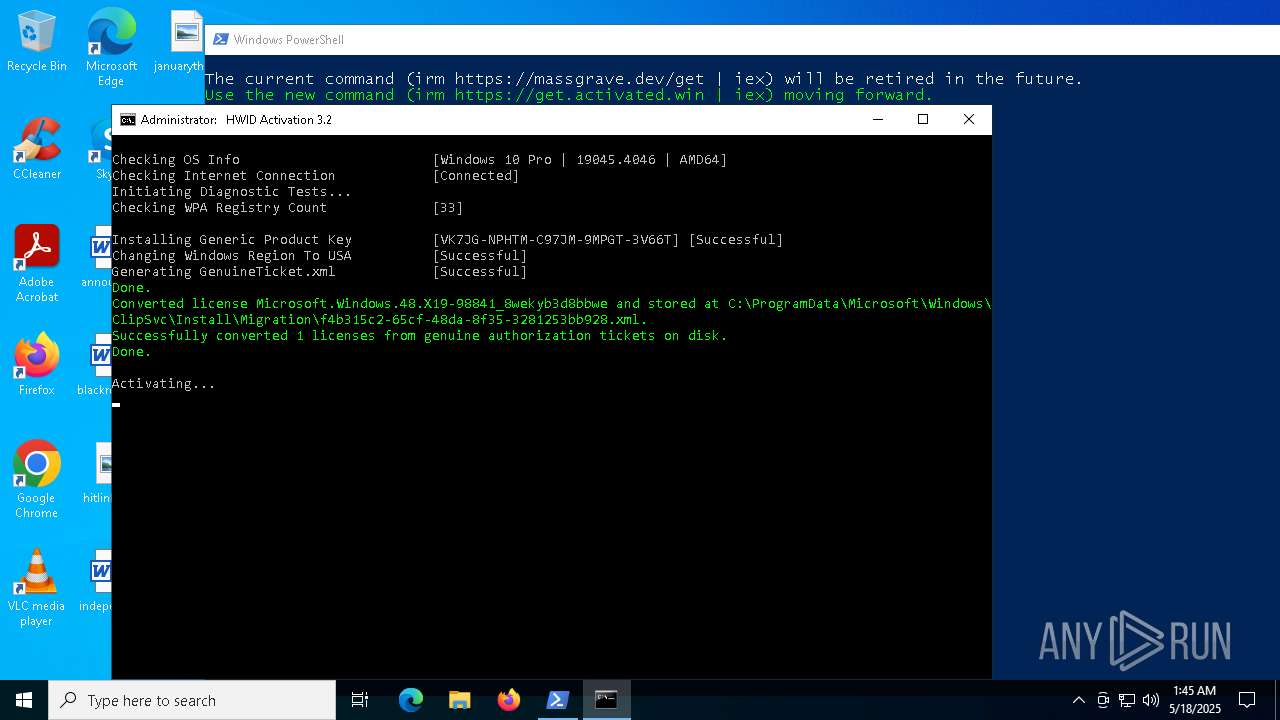
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 01:42:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | F2CB50260986DACDE7DBF1CDE1BFA3FE |
| SHA1: | 14A78EBB8718FD99D9EE9085EAF77F7BFFFA23D2 |
| SHA256: | 474DDFF93C0E1FE4C9F882E394E79342B42C5807732584446166AF11FB1E1227 |
| SSDEEP: | 96:HKFUuBVkDx+uy6OphNHOSjlSSSra4SoTAByjNlkXeQo6CGefWrG/a:qFUOVk1+uyp/jMzratoTAByZlkO7BGZ |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6004)
SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6004)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1188)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 1096)
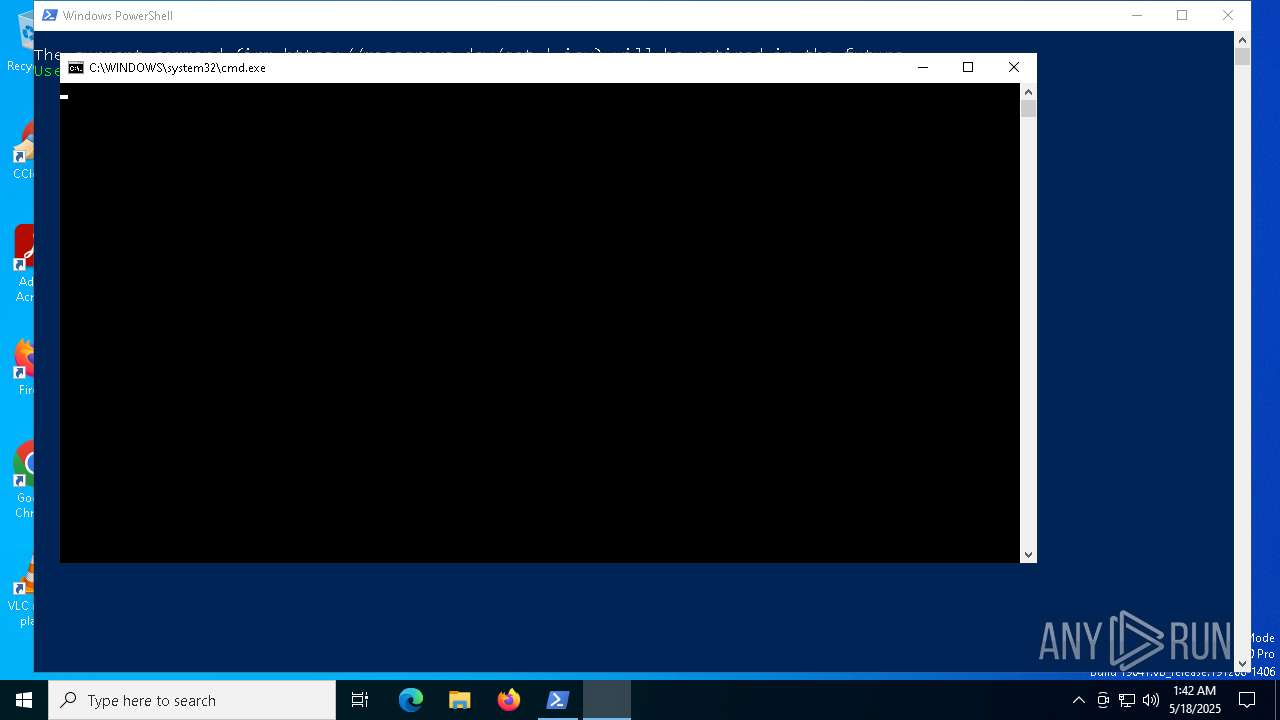
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6640)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 2984)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 736)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 1188)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3032)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3032)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3032)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6004)
Application launched itself
- cmd.exe (PID: 6640)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 736)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 1188)
- powershell.exe (PID: 1012)
- ClipUp.exe (PID: 3796)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 5936)
Executing commands from ".cmd" file
- cmd.exe (PID: 1188)
- powershell.exe (PID: 2984)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 1096)
- powershell.exe (PID: 6004)
Executes script without checking the security policy
- powershell.exe (PID: 2984)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 6676)
- powershell.exe (PID: 1012)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 5408)
- powershell.exe (PID: 2616)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6876)
- powershell.exe (PID: 1760)
- powershell.exe (PID: 3896)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 2084)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 616)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 5936)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1188)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 5384)
- powershell.exe (PID: 1012)
- cmd.exe (PID: 536)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 4268)
- powershell.exe (PID: 2420)
- cmd.exe (PID: 1328)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 5936)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1188)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 5384)
- powershell.exe (PID: 1012)
- cmd.exe (PID: 536)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 1328)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 5936)
Windows service management via SC.EXE
- sc.exe (PID: 3956)
- sc.exe (PID: 4608)
- sc.exe (PID: 4932)
- sc.exe (PID: 5024)
- sc.exe (PID: 4448)
- sc.exe (PID: 3268)
- sc.exe (PID: 3968)
- sc.exe (PID: 4868)
- sc.exe (PID: 5156)
- sc.exe (PID: 6960)
- sc.exe (PID: 6768)
- sc.exe (PID: 4436)
- sc.exe (PID: 3008)
- sc.exe (PID: 5512)
- sc.exe (PID: 680)
- sc.exe (PID: 4284)
- sc.exe (PID: 3156)
- sc.exe (PID: 5200)
- sc.exe (PID: 5260)
- sc.exe (PID: 2800)
- sc.exe (PID: 4932)
- sc.exe (PID: 5800)
- sc.exe (PID: 3896)
- sc.exe (PID: 5304)
- sc.exe (PID: 3300)
- sc.exe (PID: 4188)
- sc.exe (PID: 5740)
- sc.exe (PID: 4488)
- sc.exe (PID: 3300)
- sc.exe (PID: 4688)
- sc.exe (PID: 2344)
- sc.exe (PID: 5864)
- sc.exe (PID: 6656)
- sc.exe (PID: 5136)
- sc.exe (PID: 5156)
- sc.exe (PID: 7144)
- sc.exe (PID: 1132)
Starts SC.EXE for service management
- cmd.exe (PID: 6652)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 1188)
Hides command output
- cmd.exe (PID: 1764)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 536)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 1128)
- cmd.exe (PID: 3032)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1764)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 536)
- cmd.exe (PID: 1328)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1764)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 536)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6652)
- cmd.exe (PID: 1096)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4188)
- cmd.exe (PID: 1096)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 1132)
Probably file/command deobfuscation
- cmd.exe (PID: 5384)
- cmd.exe (PID: 1328)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 1012)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 5936)
- powershell.exe (PID: 2420)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1096)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 3024)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 1096)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1096)
INFO
Disables trace logs
- powershell.exe (PID: 6004)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3032)
Checks proxy server information
- powershell.exe (PID: 6004)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3032)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 736)
- powershell.exe (PID: 728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3032)
Checks operating system version
- cmd.exe (PID: 6652)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 1188)
Checks supported languages
- mode.com (PID: 2772)
- mode.com (PID: 2384)
- mode.com (PID: 680)
- mode.com (PID: 1184)
Starts MODE.COM to configure console settings
- mode.com (PID: 2772)
- mode.com (PID: 1184)
- mode.com (PID: 680)
- mode.com (PID: 2384)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2644)
- WMIC.exe (PID: 1568)
- WMIC.exe (PID: 5596)
- WMIC.exe (PID: 2616)
- WMIC.exe (PID: 2420)
- WMIC.exe (PID: 1568)
- WMIC.exe (PID: 668)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
436
Monitored processes
298
Malicious processes
11
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | reg query HKLM\SYSTEM\CurrentControlSet\Services\LicenseManager /v DependOnService | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | wmic path SoftwareLicensingService where __CLASS='SoftwareLicensingService' call InstallProductKey ProductKey="VK7JG-NPHTM-C97JM-9MPGT-3V66T" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\cmd.exe /c C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_0fce9650-17a0-440e-8872-8c79131a1dd9.cmd') -split ':wpatest\:.*';iex ($f[1])" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | wmic path SoftwareLicensingService where __CLASS='SoftwareLicensingService' call RefreshLicenseStatus | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | wmic path SoftwareLicensingProduct where (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f') get ID /VALUE | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "Start-Job { Restart-Service wlidsvc } | Wait-Job -Timeout 20 | Out-Null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
132 451
Read events
132 442
Write events
2
Delete events
7
Modification events
| (PID) Process: | (3896) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
| (PID) Process: | (3896) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Nation |
Value: 244 | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\ExtendedProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Property |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token\{D6D5A677-0872-4AB0-9442-BB792FCE85C5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6208) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
6
Text files
58
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6004 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FWCVEHTRYH6ADAHFGM1V.temp | binary | |
MD5:D0C7BEC983CE423E29EB909F964EBBAB | SHA256:17D7A90CA829CE29C5FD62DDB3D7656D3D1418643ABDA73CB87A618B91CC6D23 | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3vu4xqa5.zn2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gc1enxia.tyt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:D0C7BEC983CE423E29EB909F964EBBAB | SHA256:17D7A90CA829CE29C5FD62DDB3D7656D3D1418643ABDA73CB87A618B91CC6D23 | |||
| 736 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bczbaodz.jpg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rzarqstw.jvi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B4BABA0B04414D29F33886BB520C3B6D | SHA256:C3C8FD0BE1B1BABED2F62B70AD1843BA86C74A7BC7284DCC8B14AC20F8E141E4 | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2vcwfgon.a00.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_chej54qp.hkx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 736 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5xh4gfa4.a0i.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1240 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1240 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6004 | powershell.exe | 13.107.42.20:443 | dev.azure.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
dev.azure.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
activated.win |
| unknown |
updatecheck32.activated.win |
| unknown |