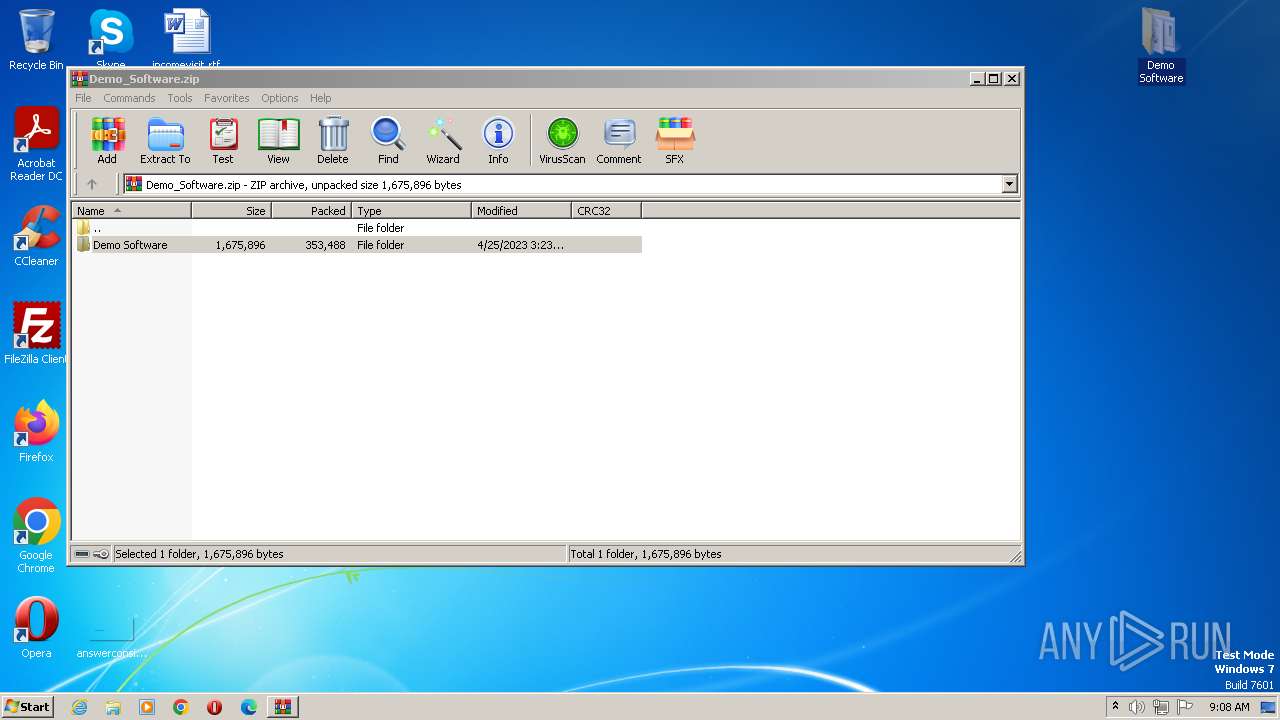
| File name: | Demo_Software.zip |
| Full analysis: | https://app.any.run/tasks/7880826a-1fde-448b-ae1e-1f0dcc307e89 |
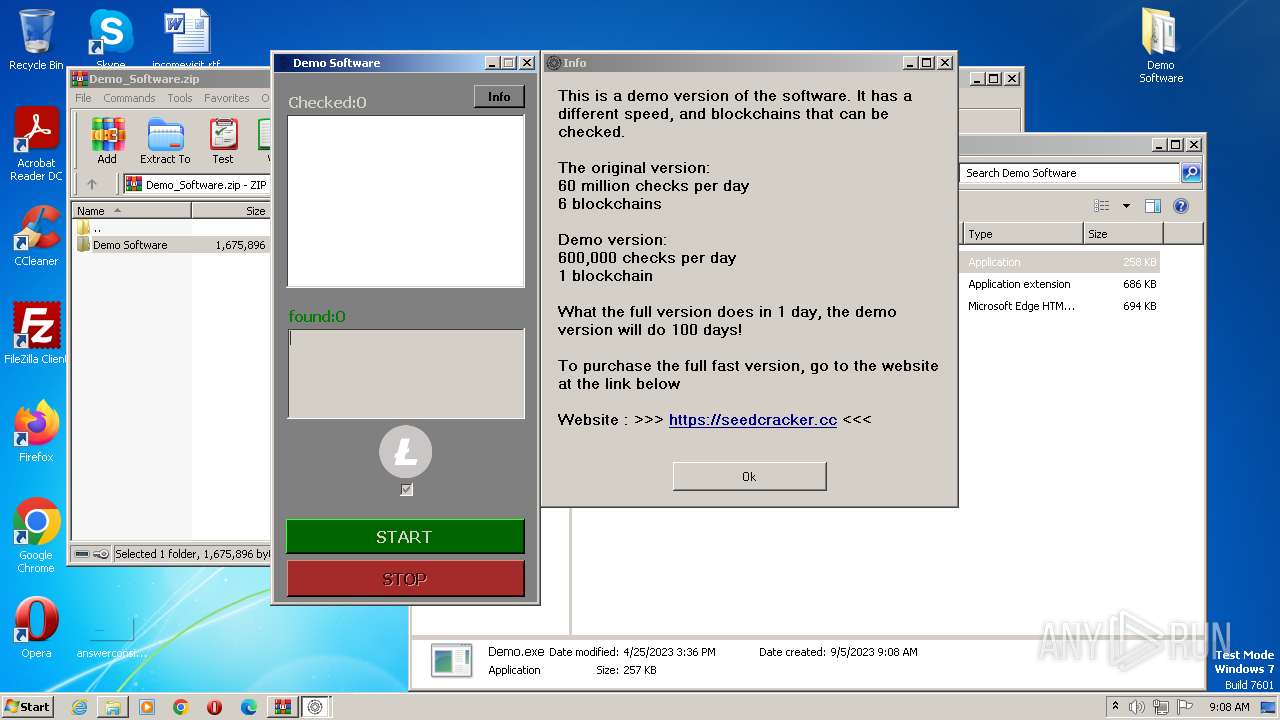
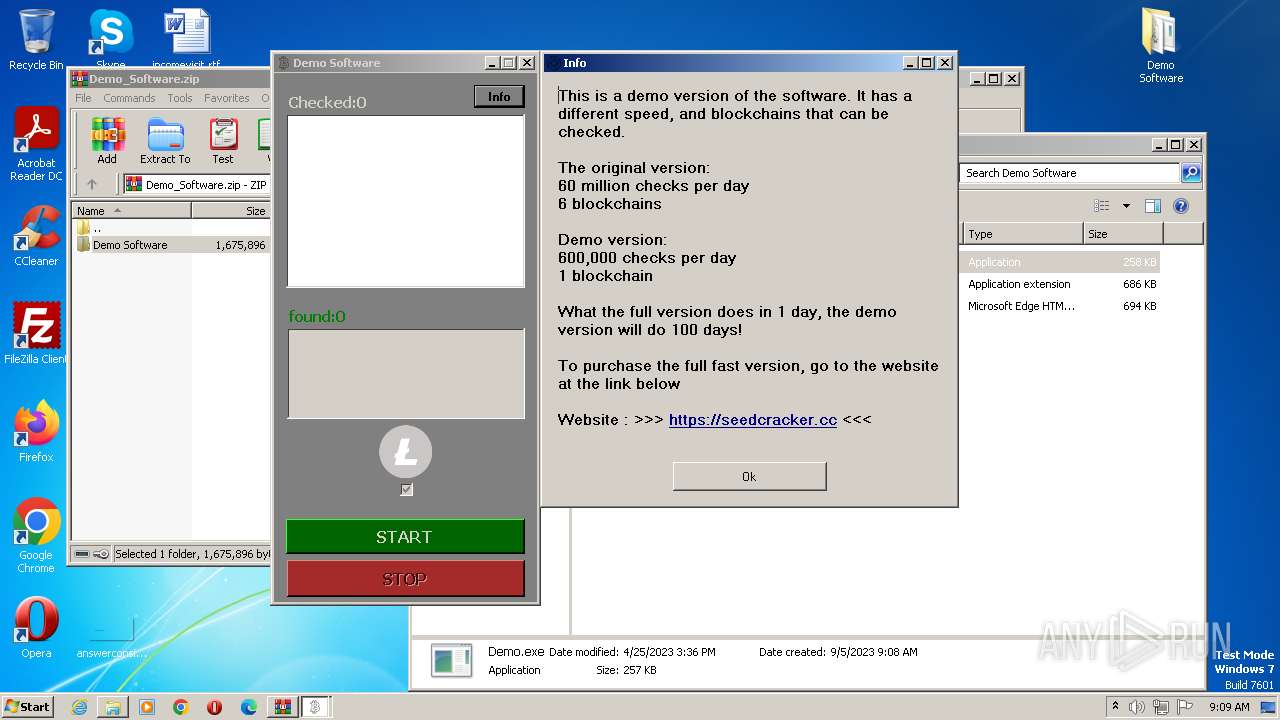
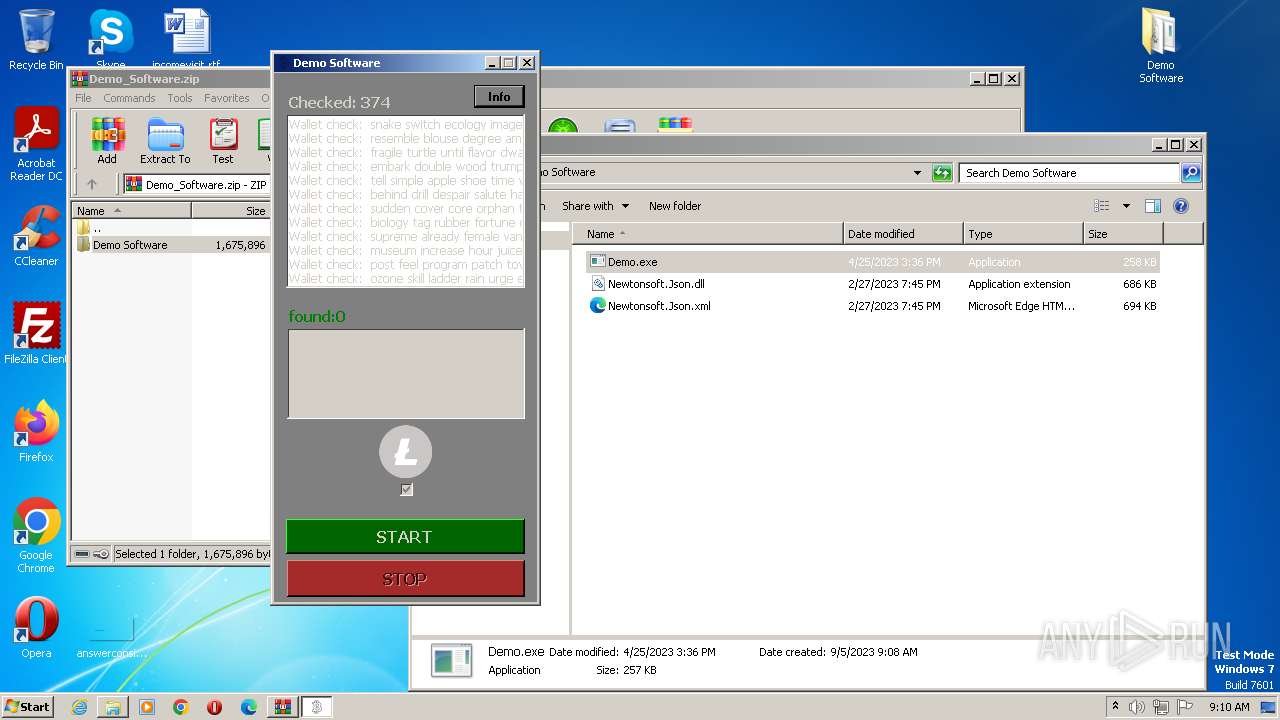
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2023, 08:08:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 159EF060C520DF93CB3E05C5F6B38BA9 |
| SHA1: | D7AEF97FFE331513AAD769D6F6CEF1E4930E3408 |
| SHA256: | 474DBD816C6C0182CD2EFC58F0DE524F64D7A27C35FBC6CBC4AF8FA2EBF80533 |
| SSDEEP: | 6144:fNi+i4aN95RE/LQt2pEm57PrwC7h7SjmH9r7mA2Kz233D3ZNXgPn18V/BUcO5jT:fmN9UlGyLuithz233D3v6n18Vpe5jT |
MALICIOUS
Application was dropped or rewritten from another process
- Demo.exe (PID: 1348)
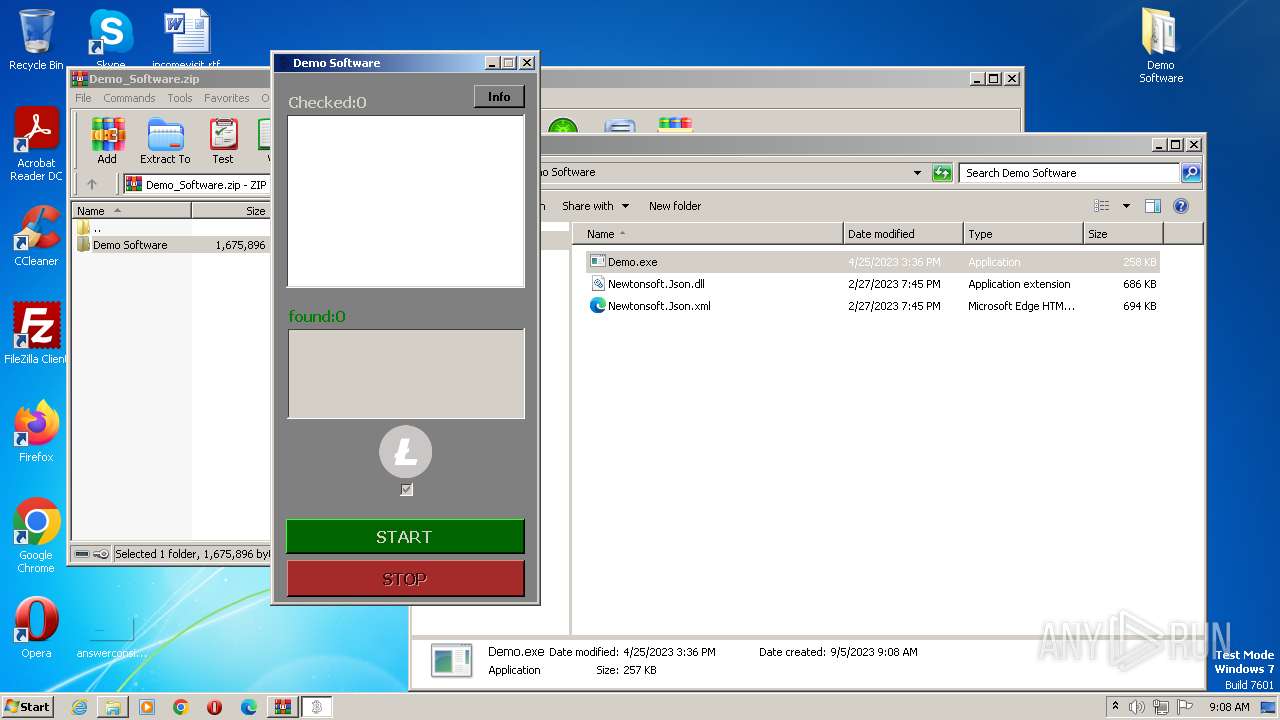
SUSPICIOUS
Reads the Internet Settings
- Demo.exe (PID: 1348)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 124)
Checks supported languages
- Demo.exe (PID: 1348)
Reads the computer name
- Demo.exe (PID: 1348)
Reads the machine GUID from the registry
- Demo.exe (PID: 1348)
Reads Environment values
- Demo.exe (PID: 1348)
Manual execution by a user
- Demo.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Demo Software/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2023:04:25 15:24:00 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
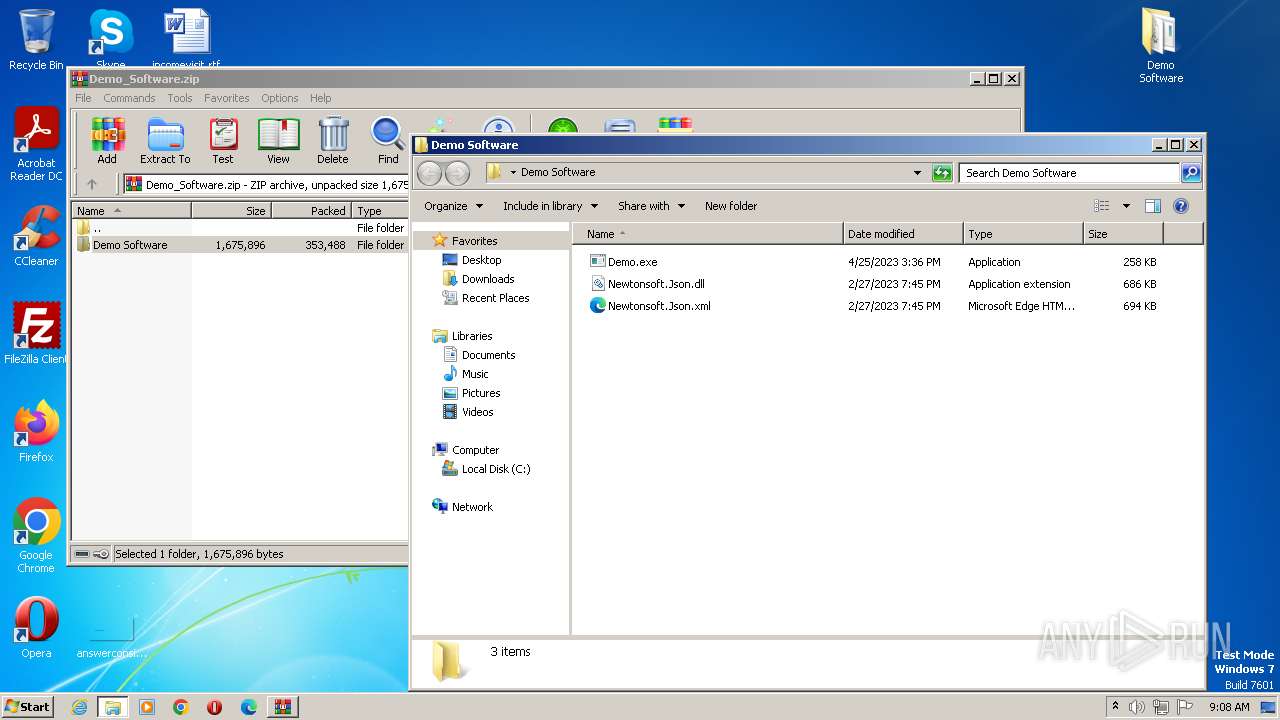
| 124 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Demo_Software.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
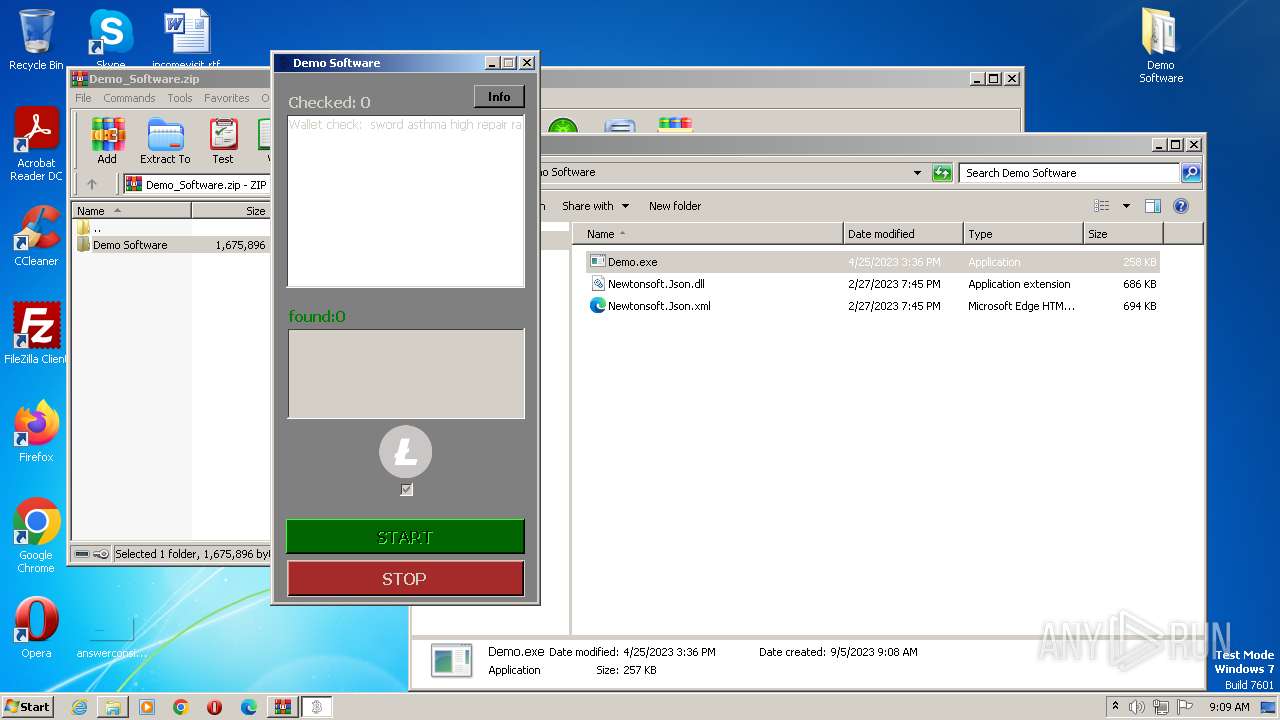
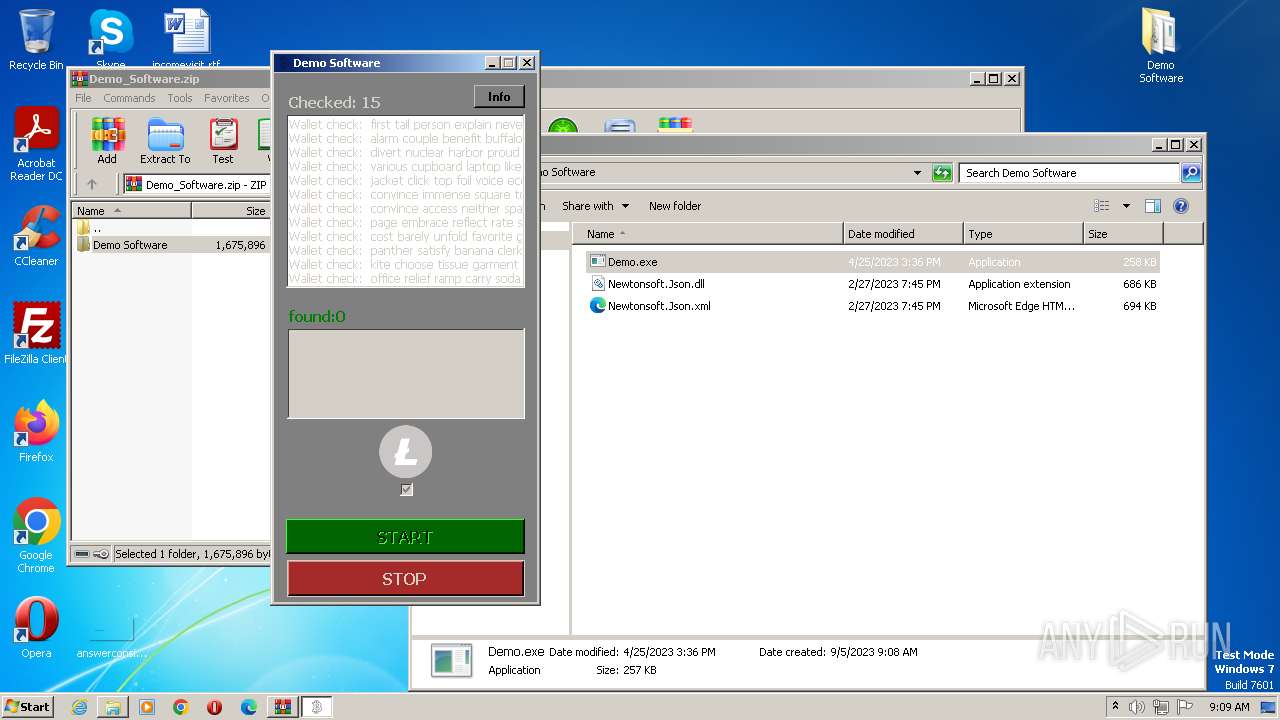
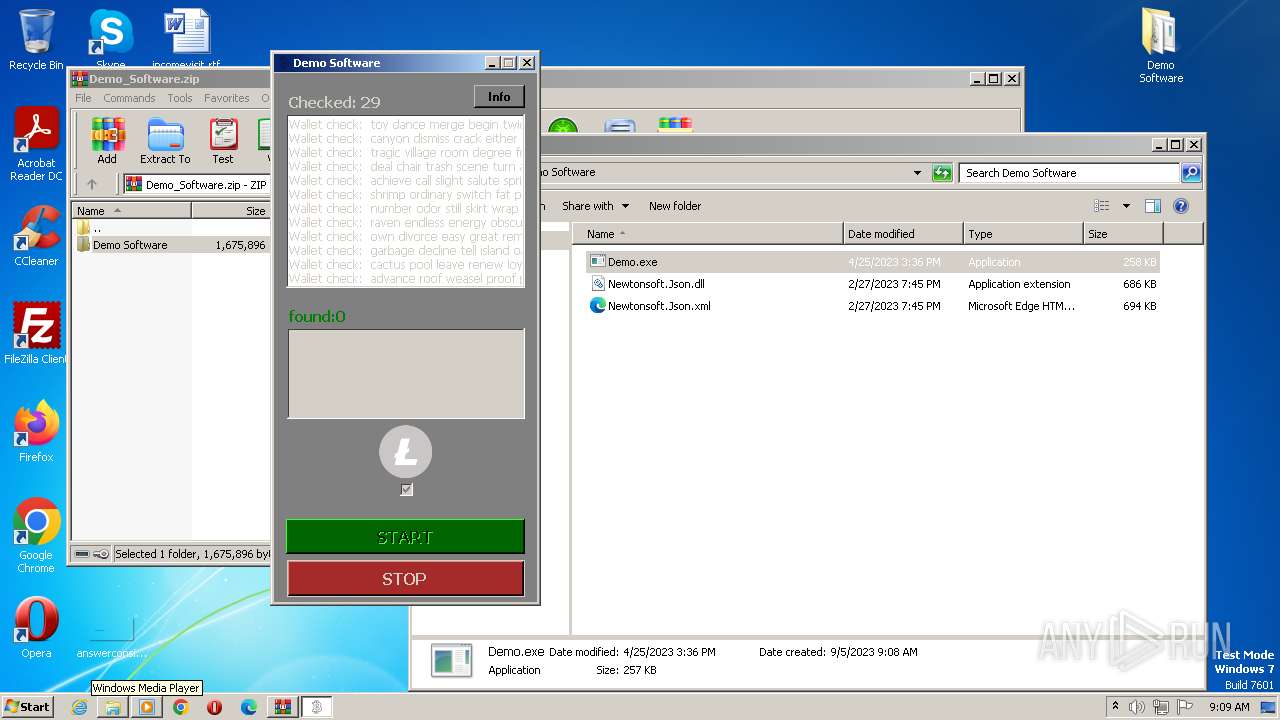
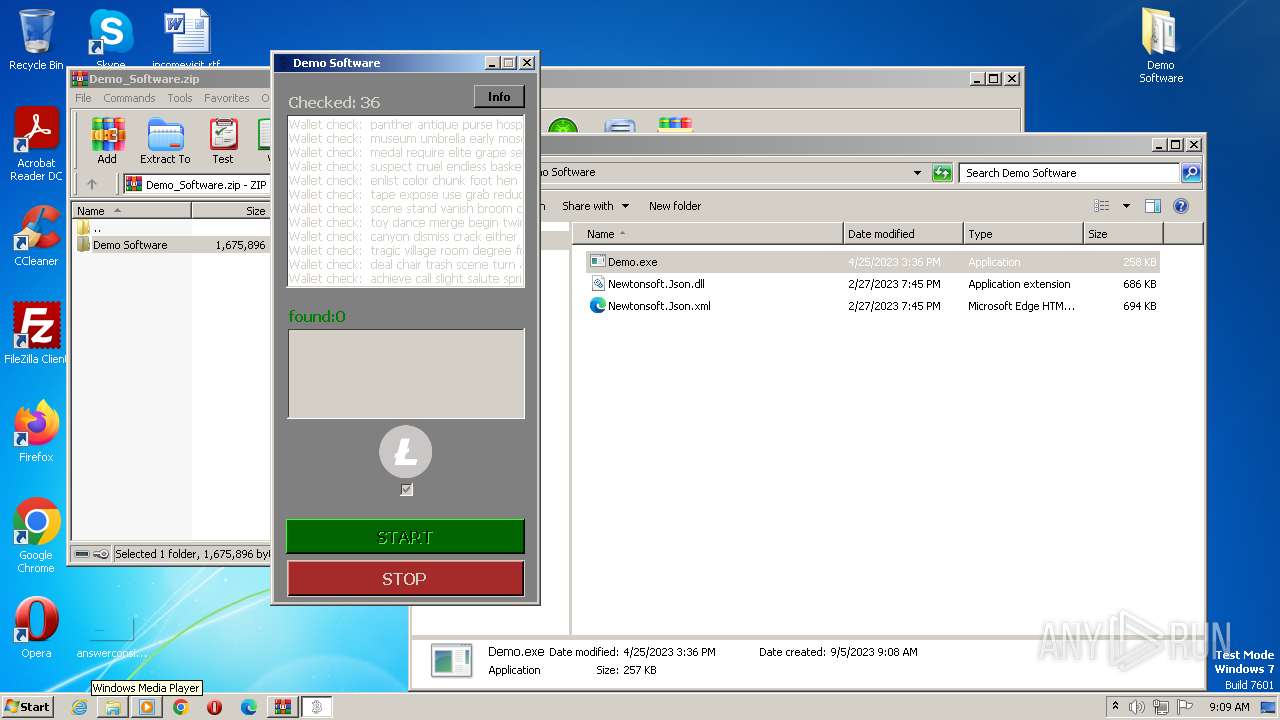
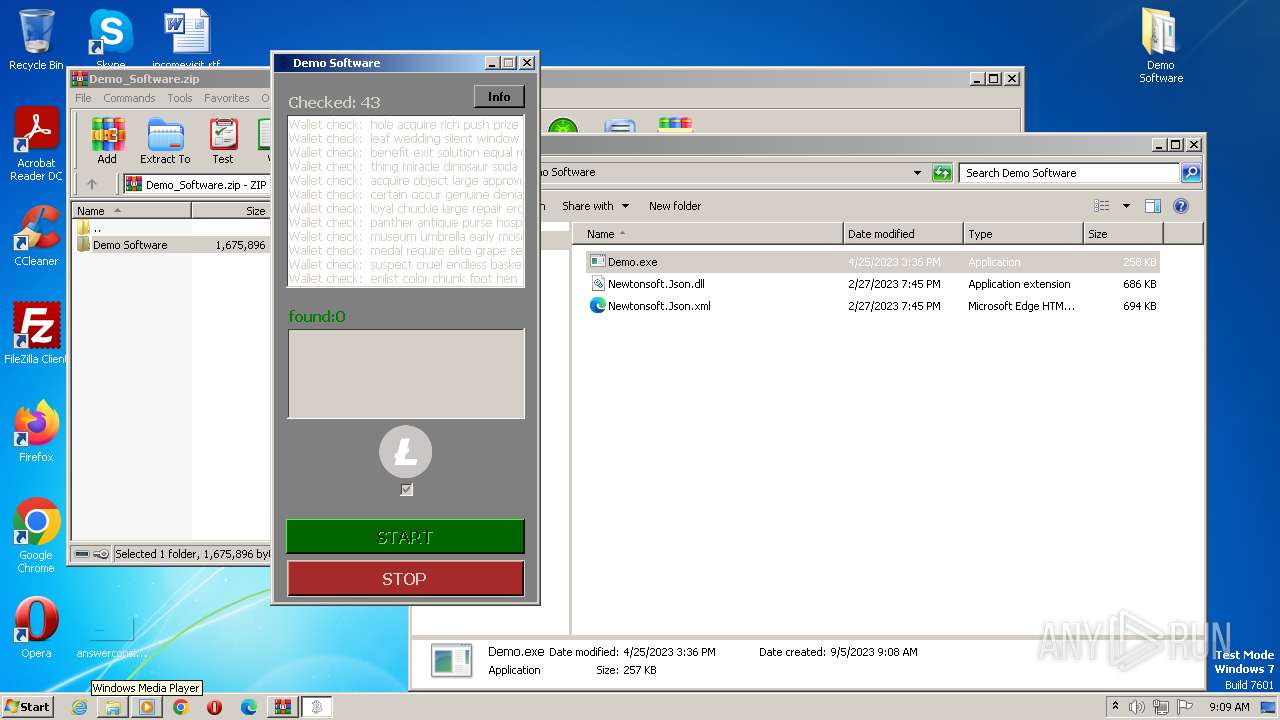
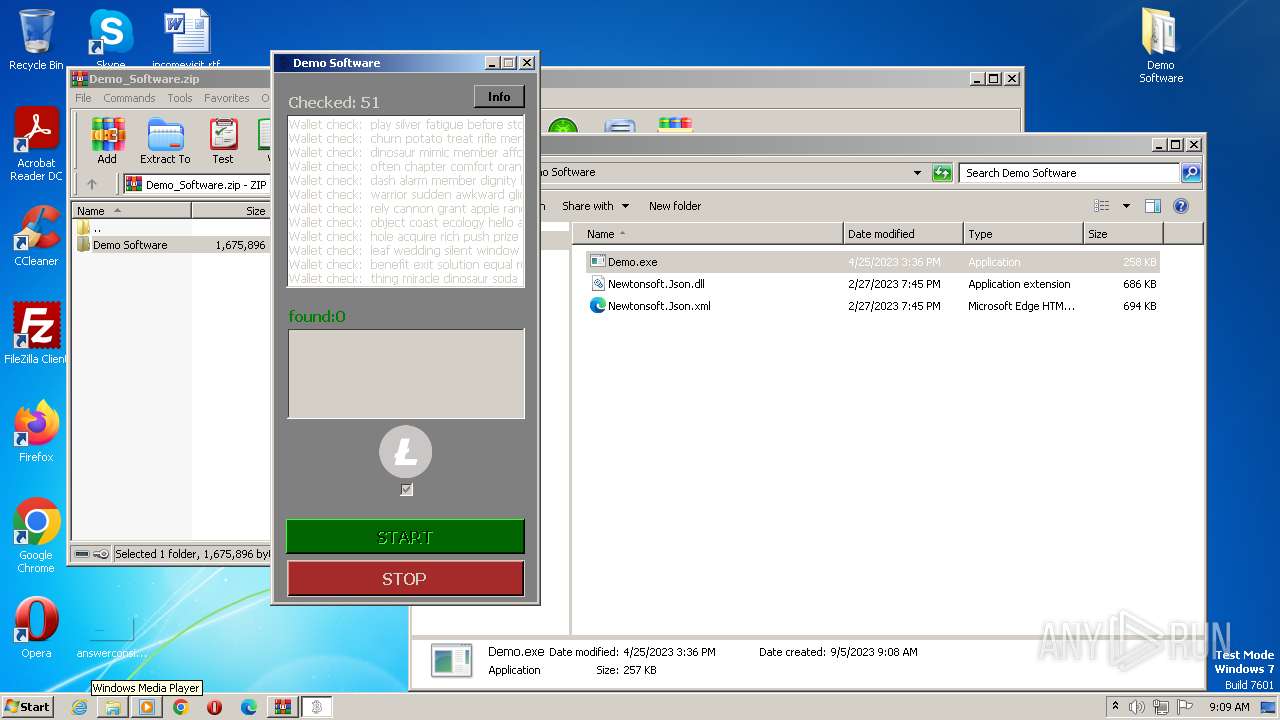
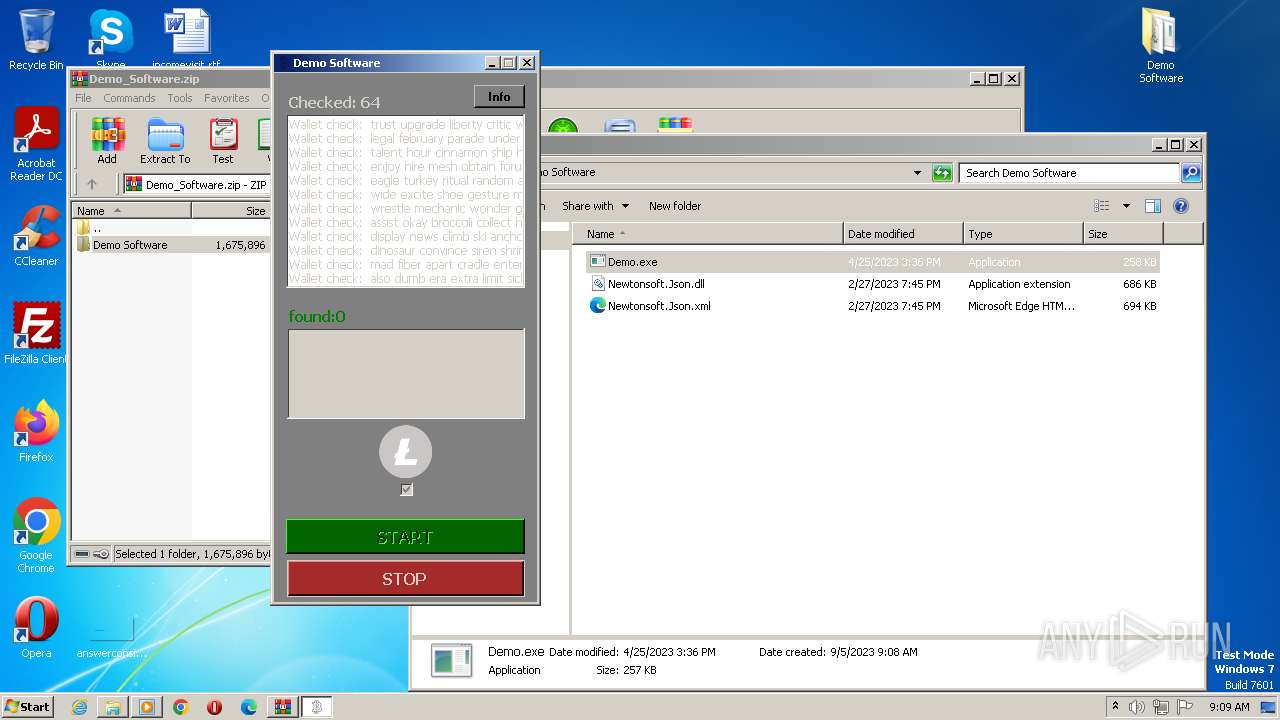
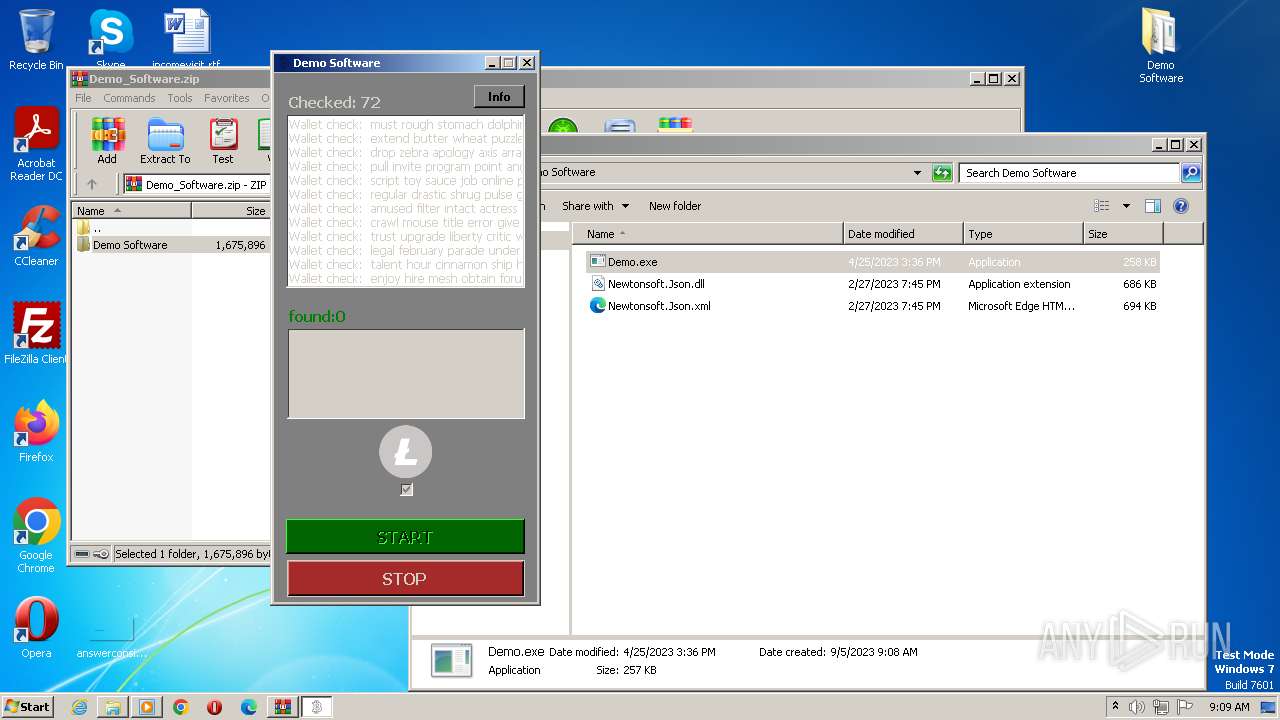
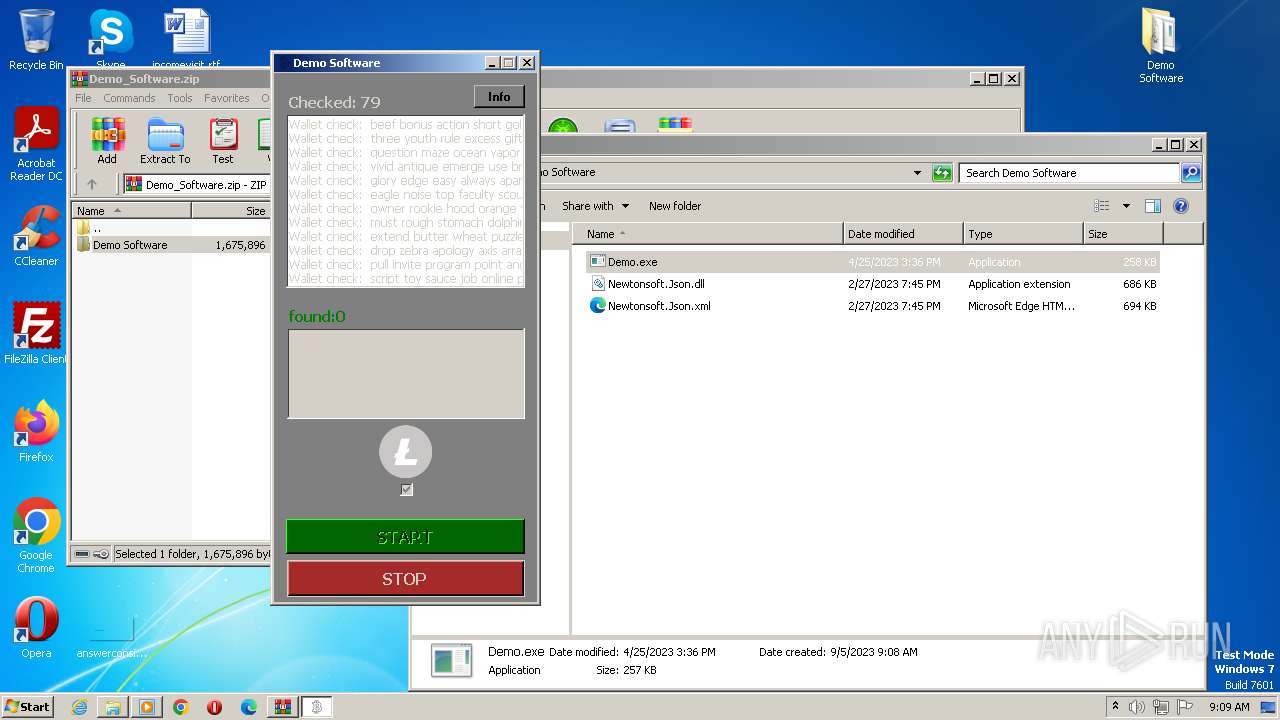
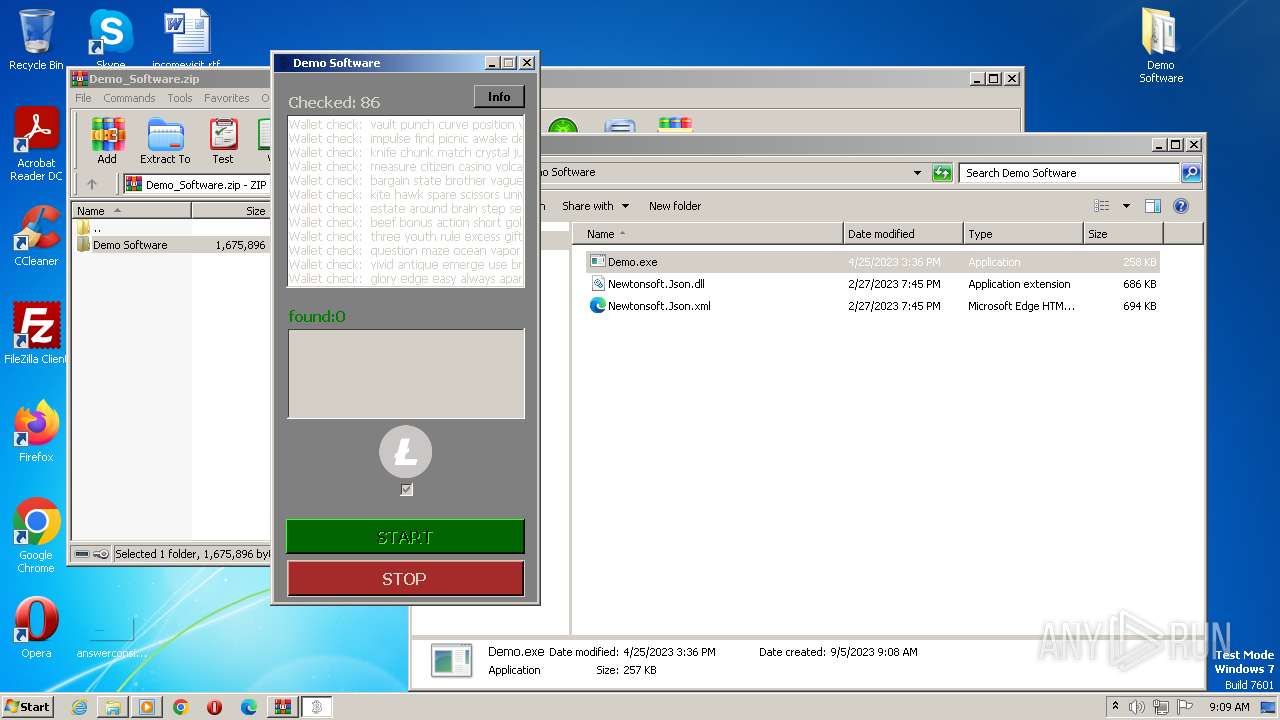
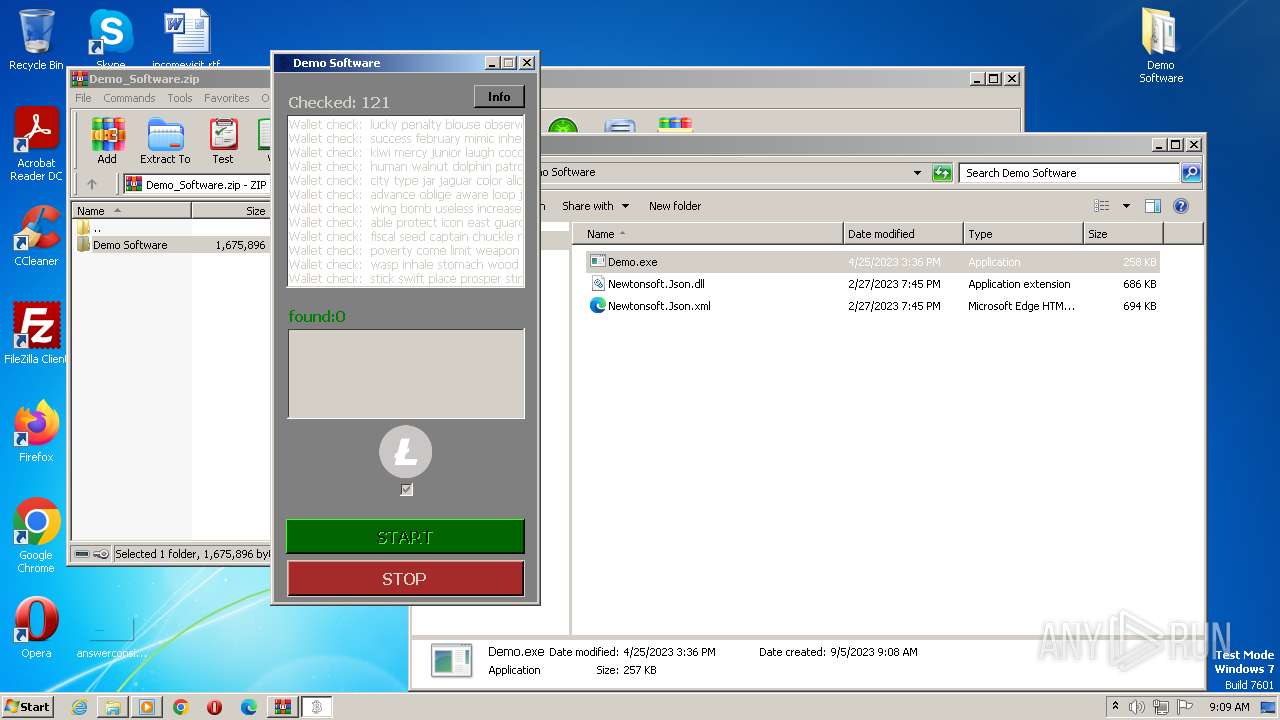
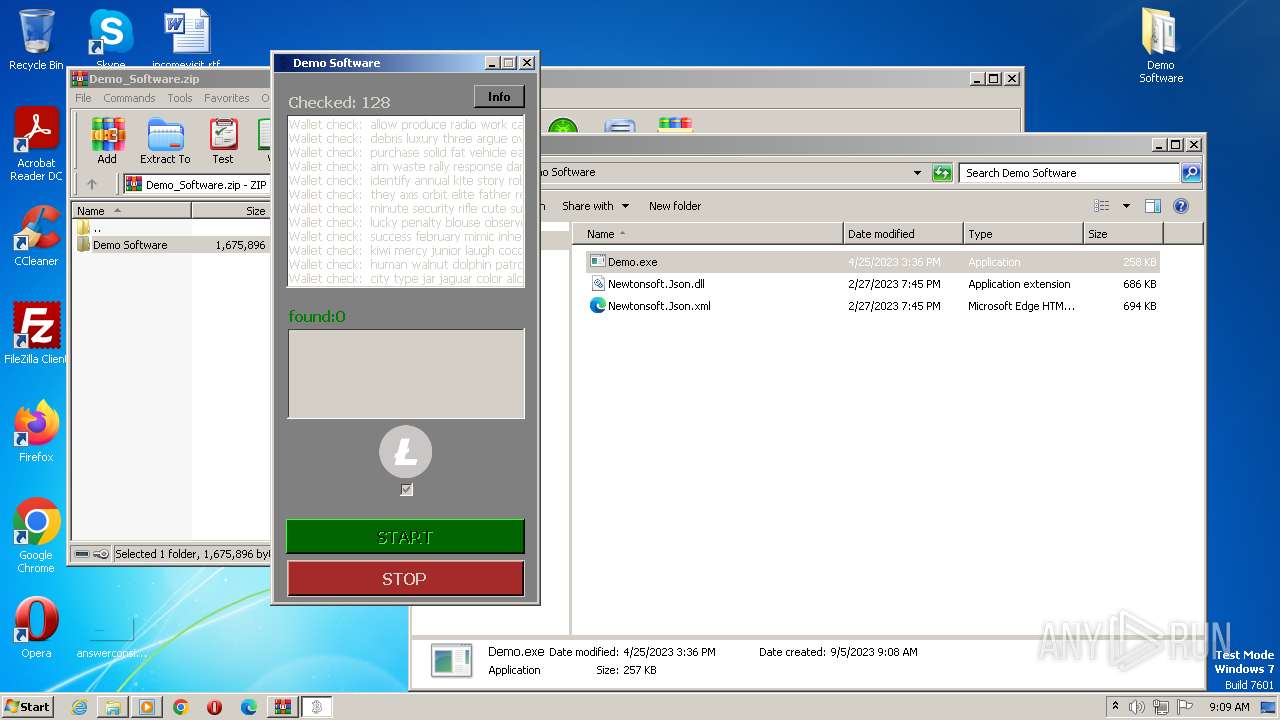
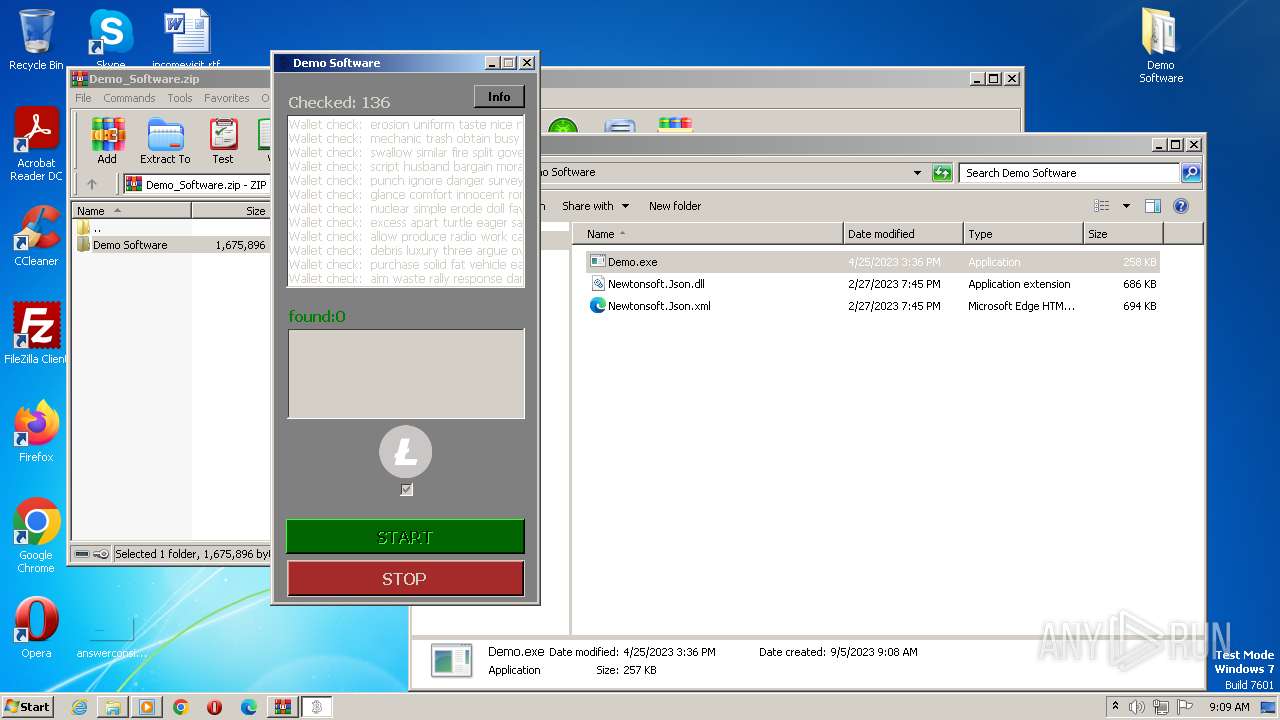
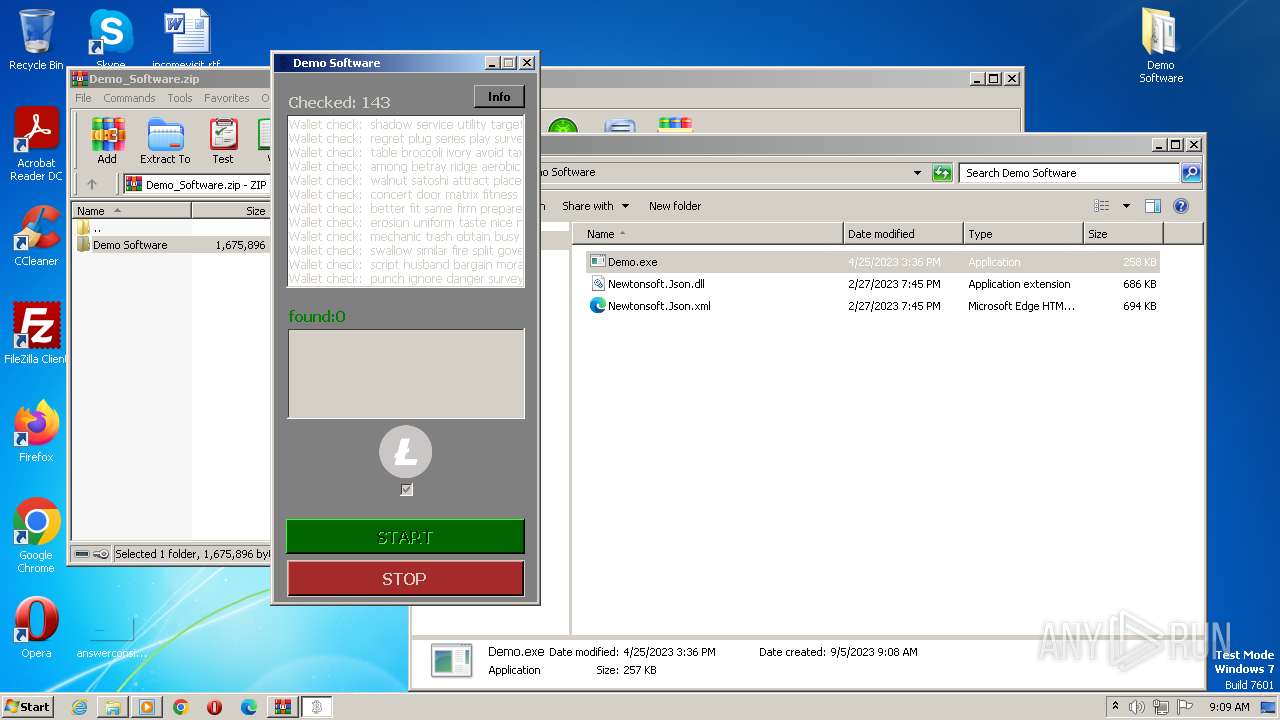
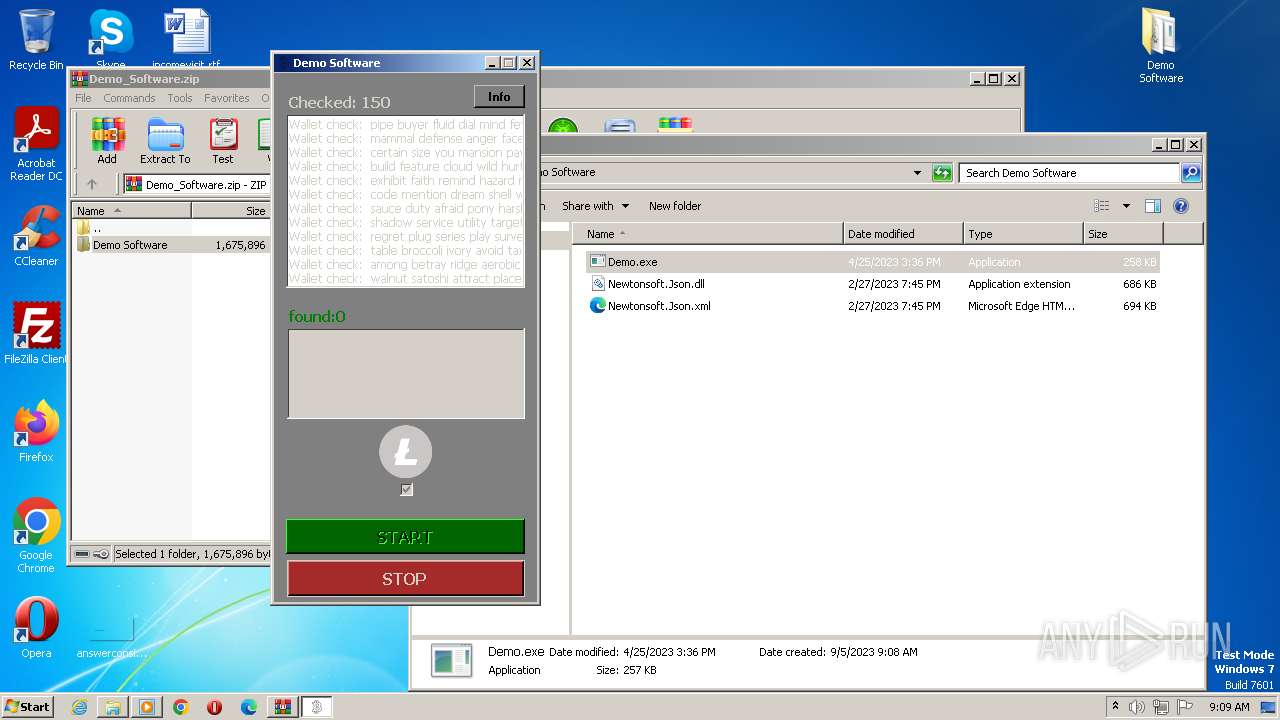
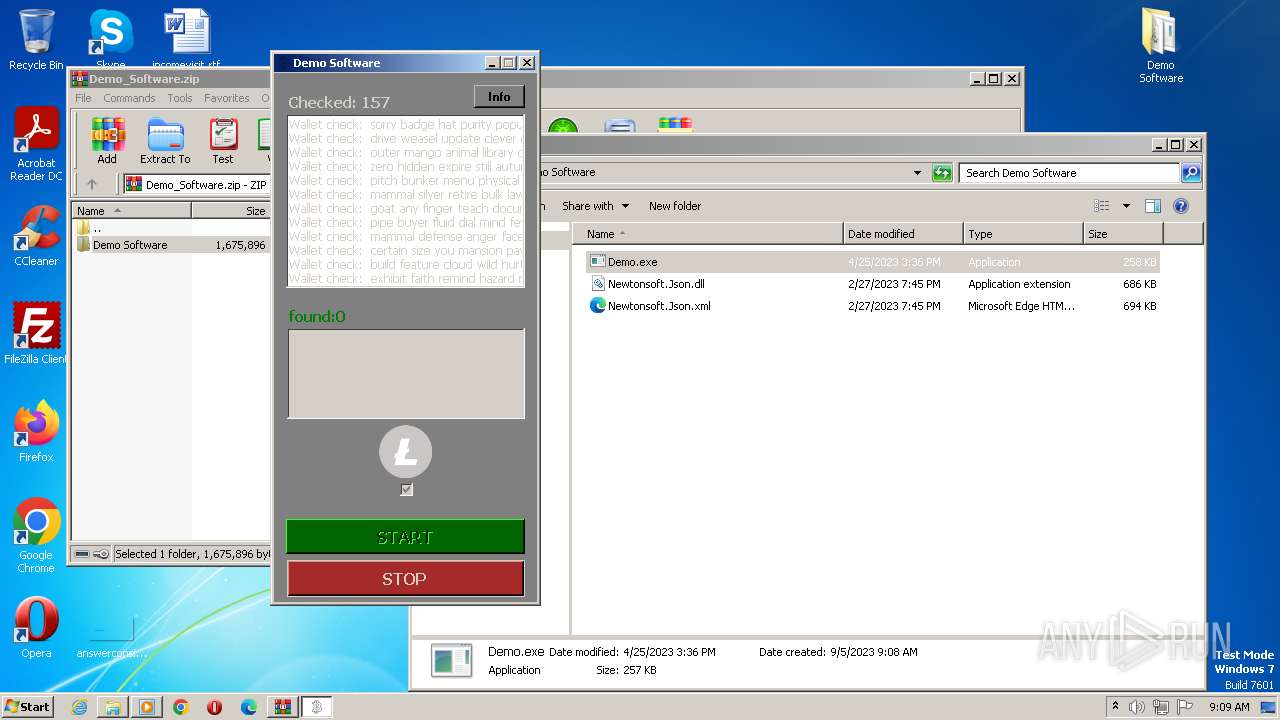
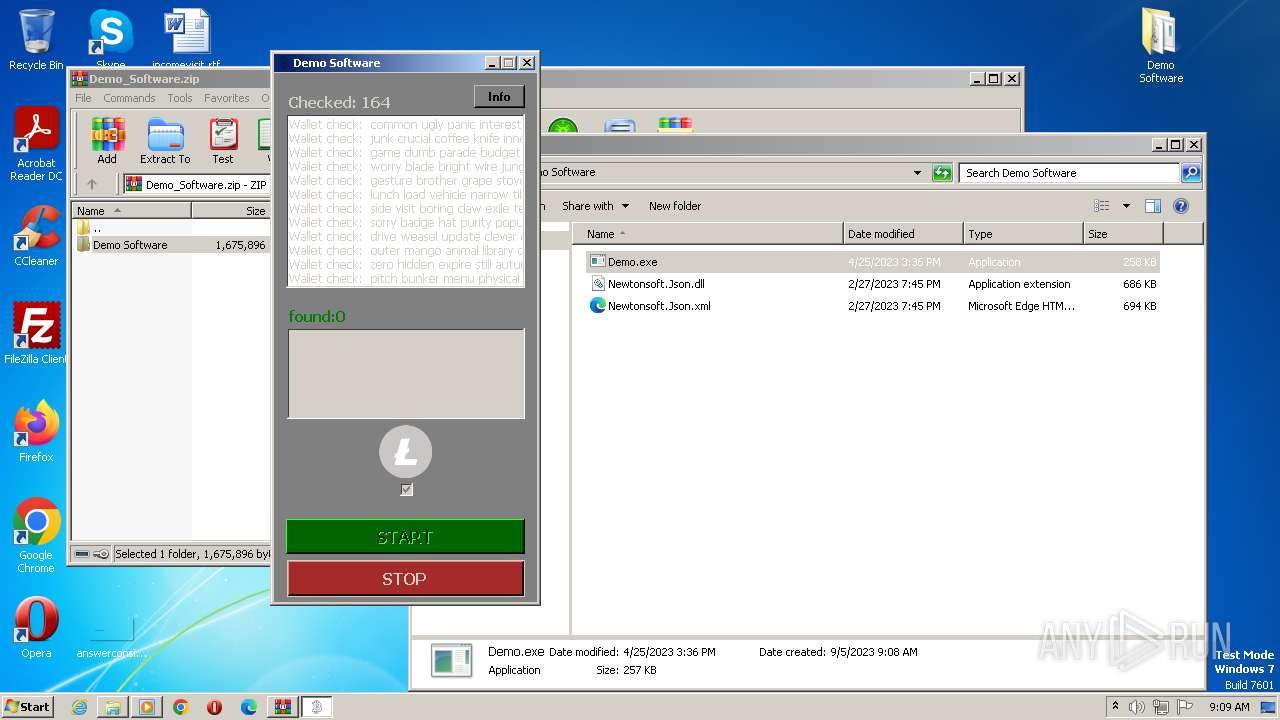
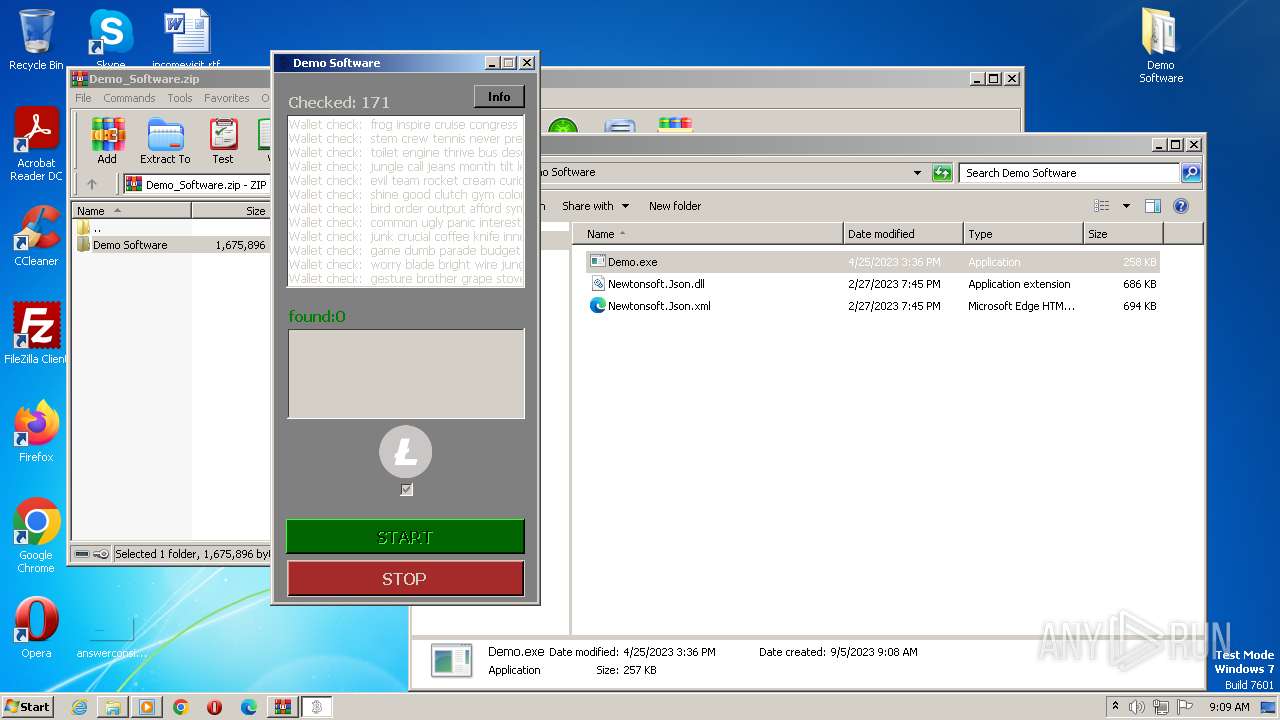
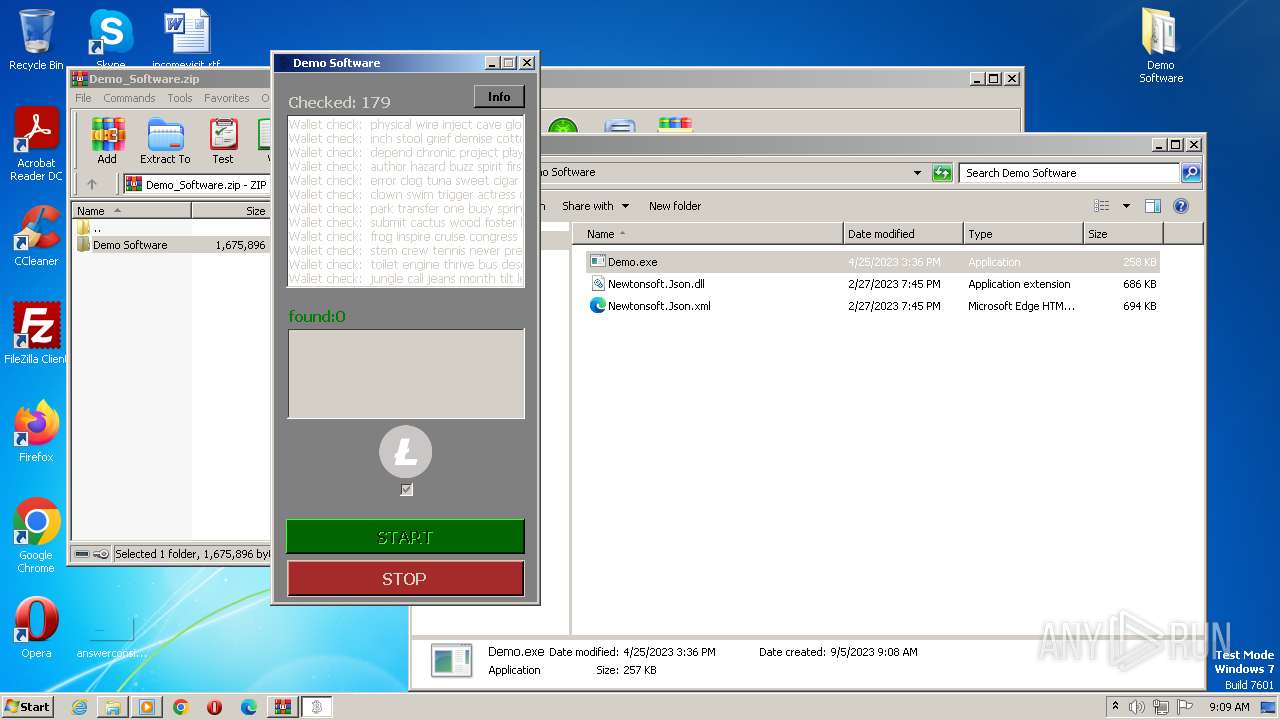
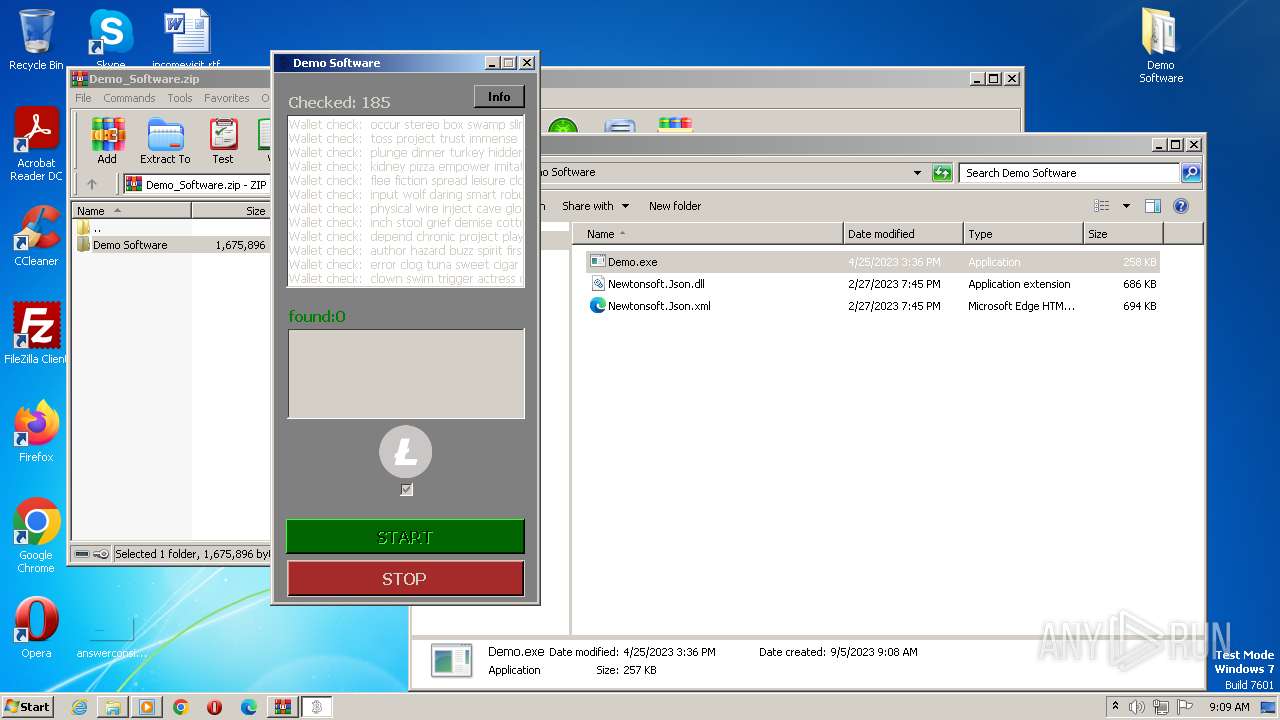
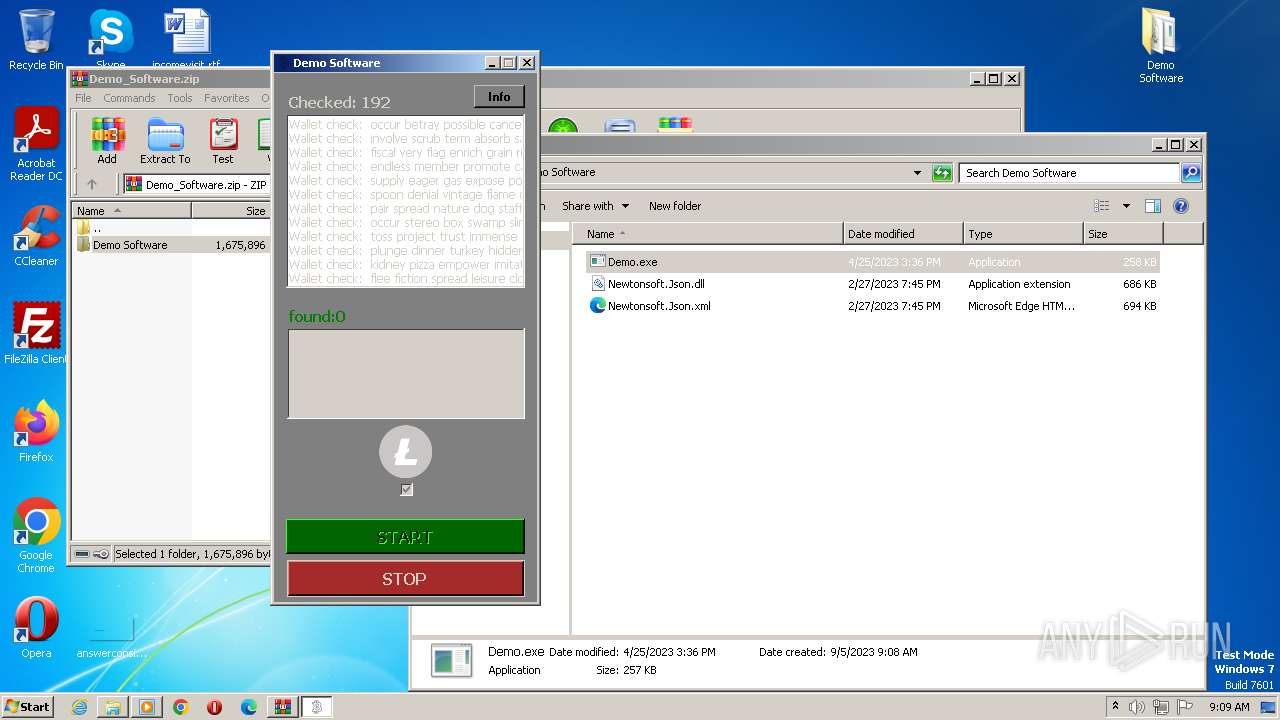
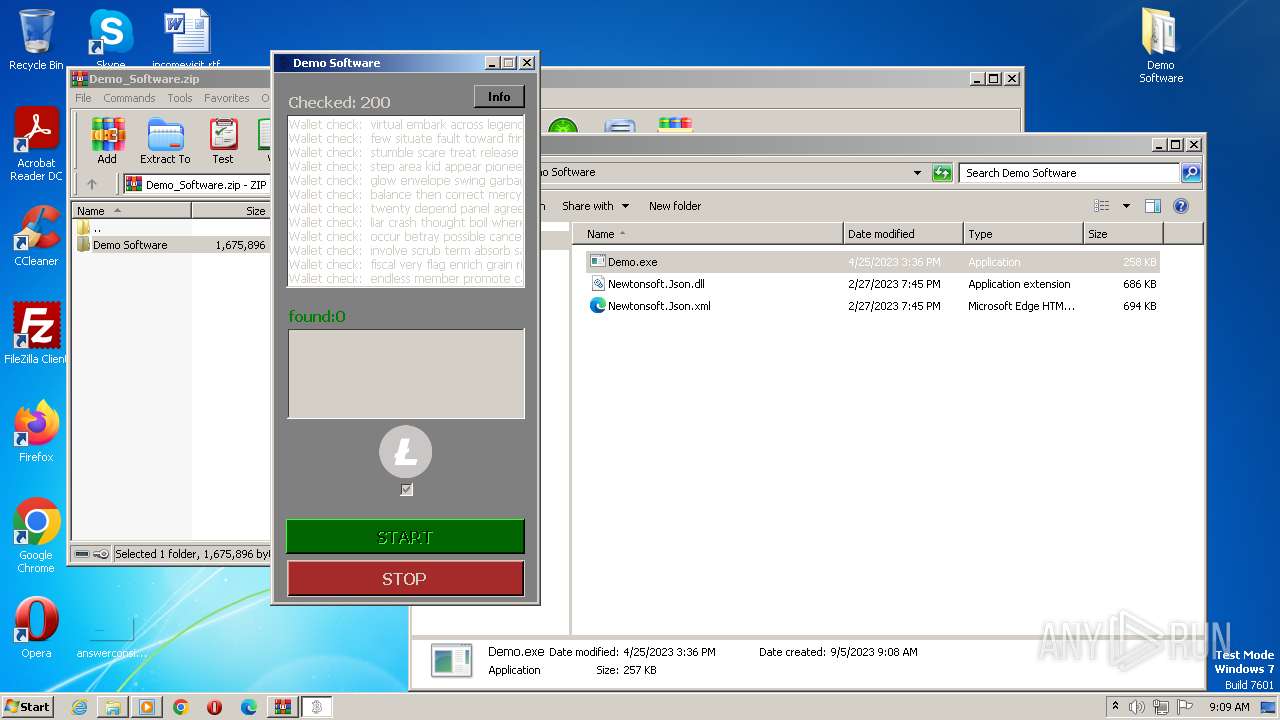
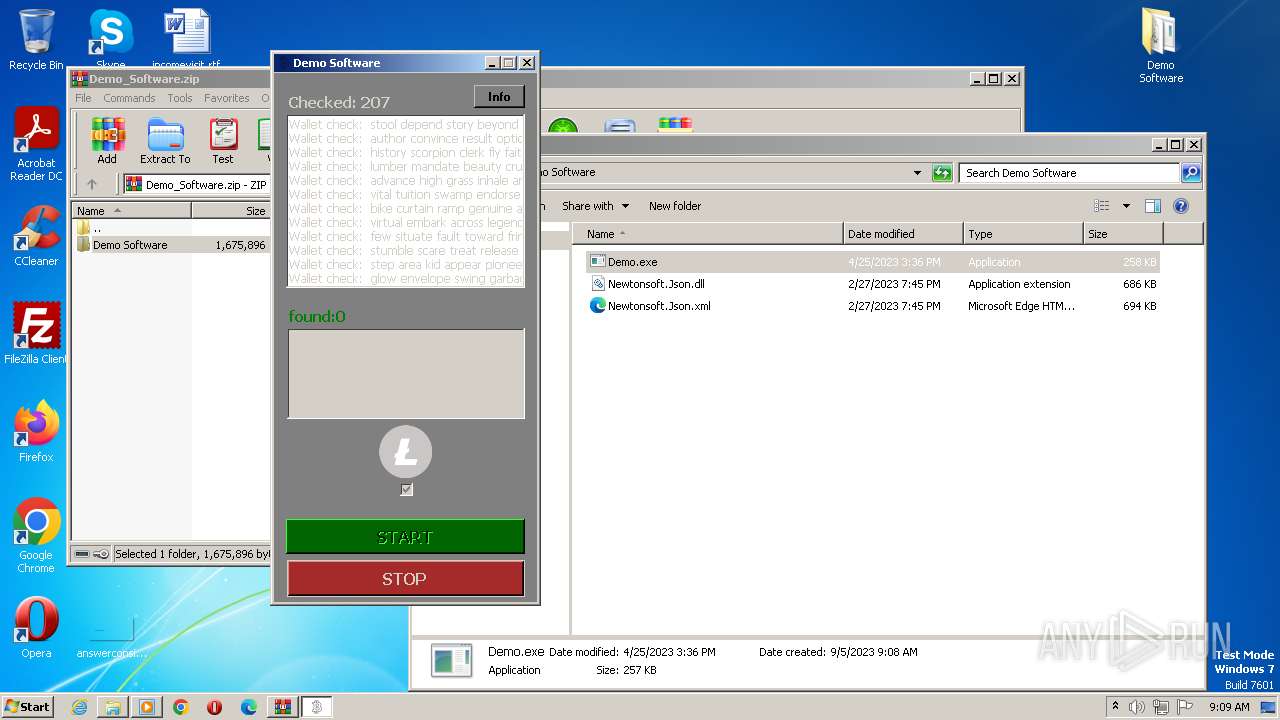
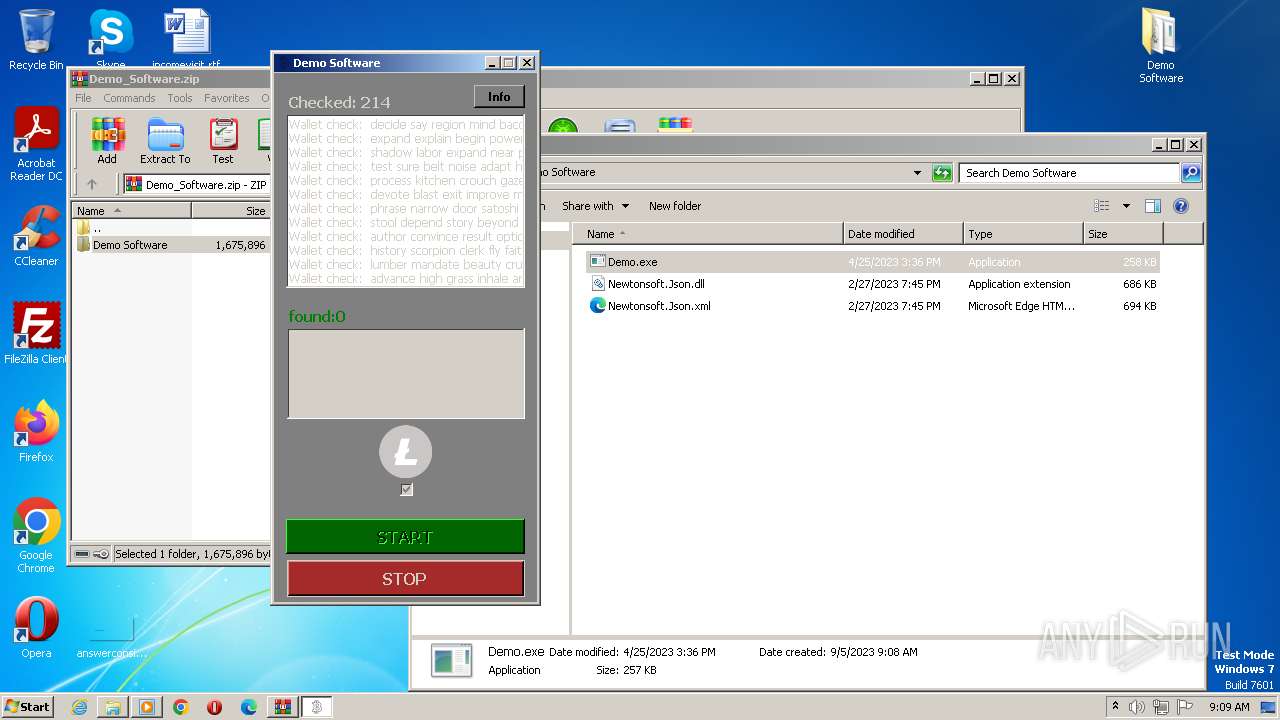
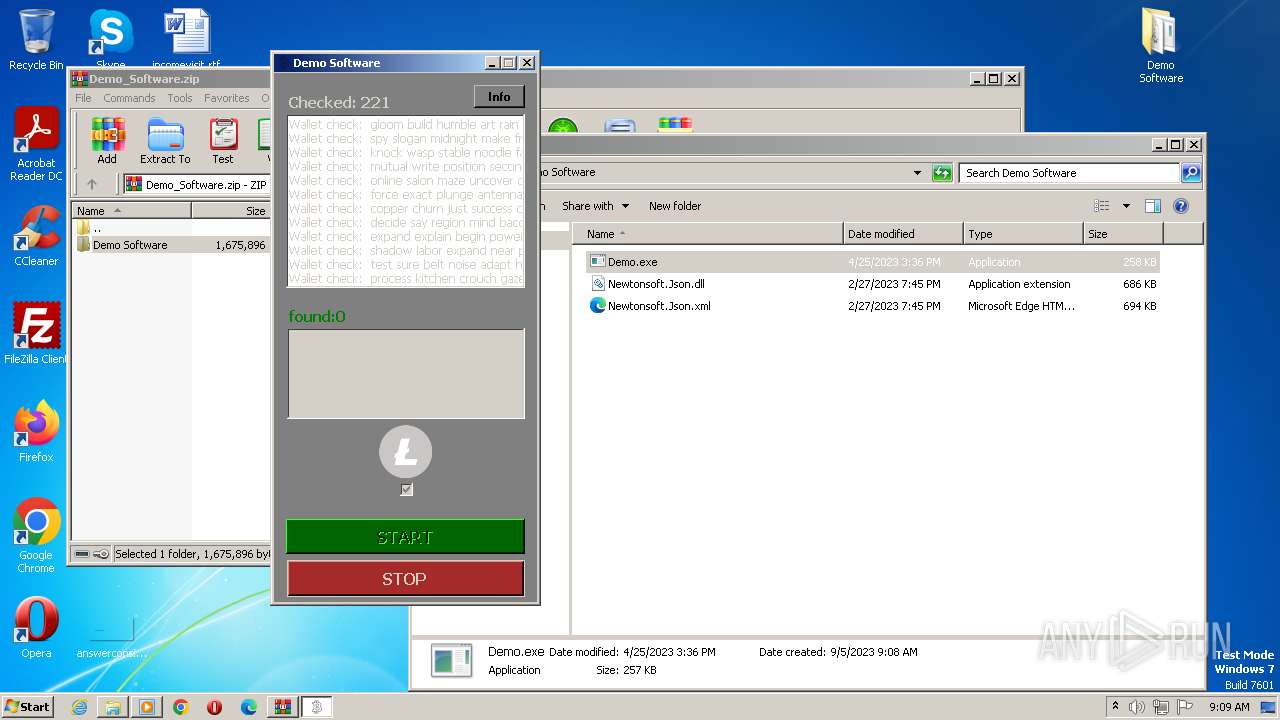
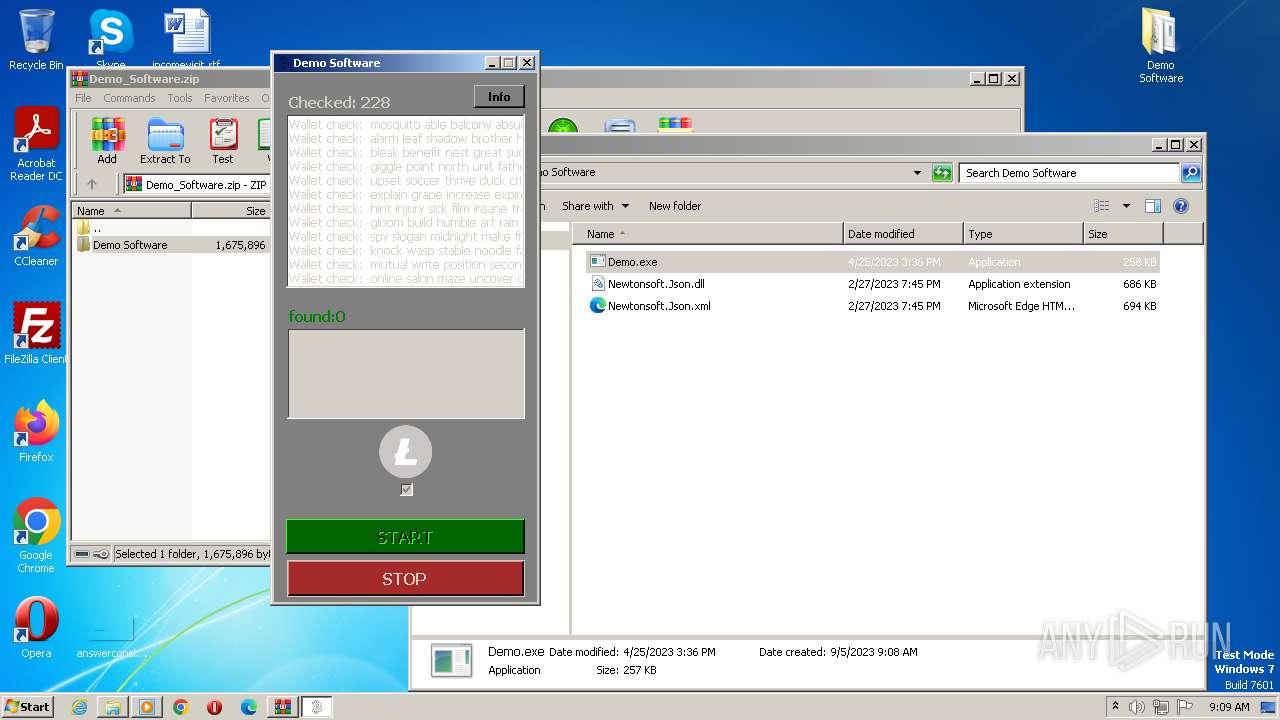
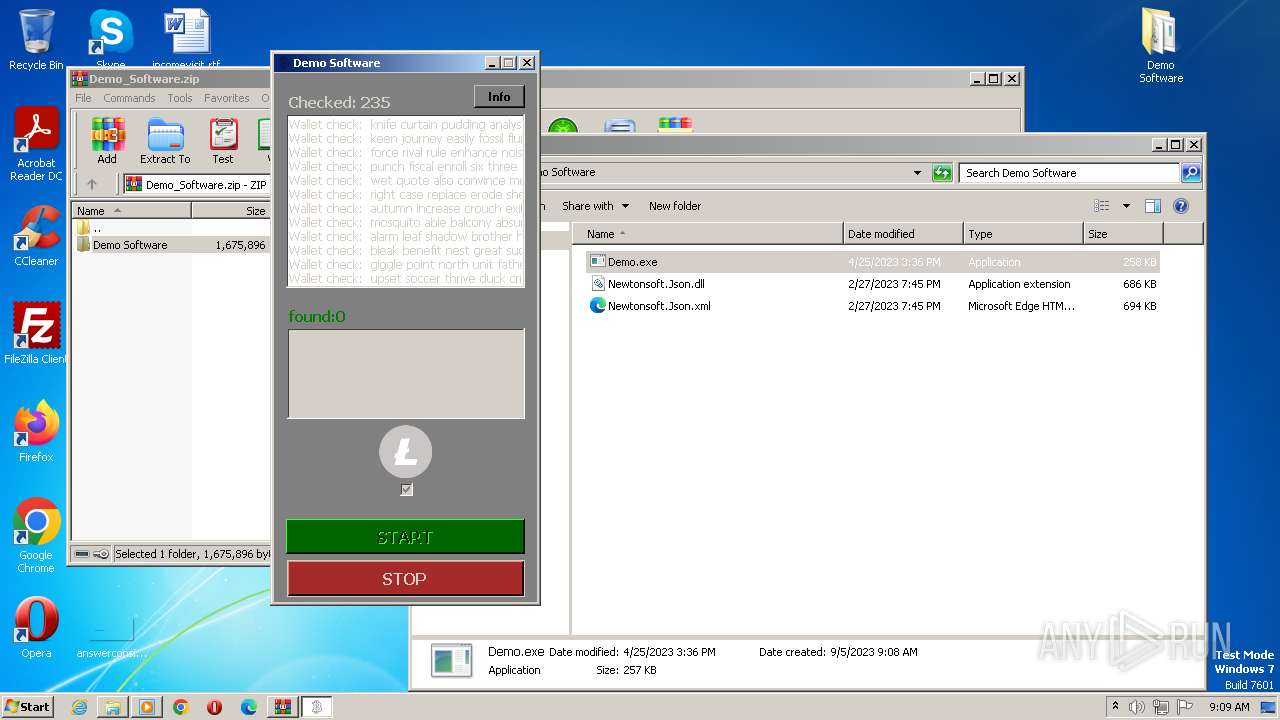
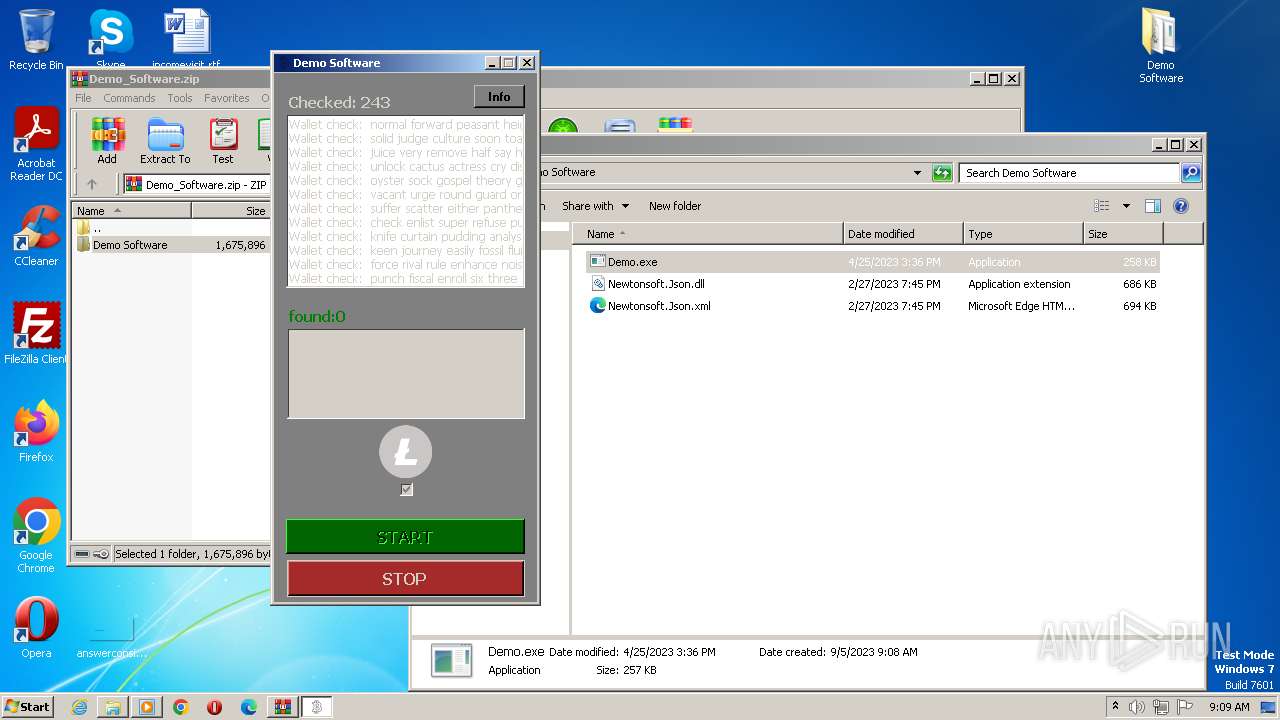
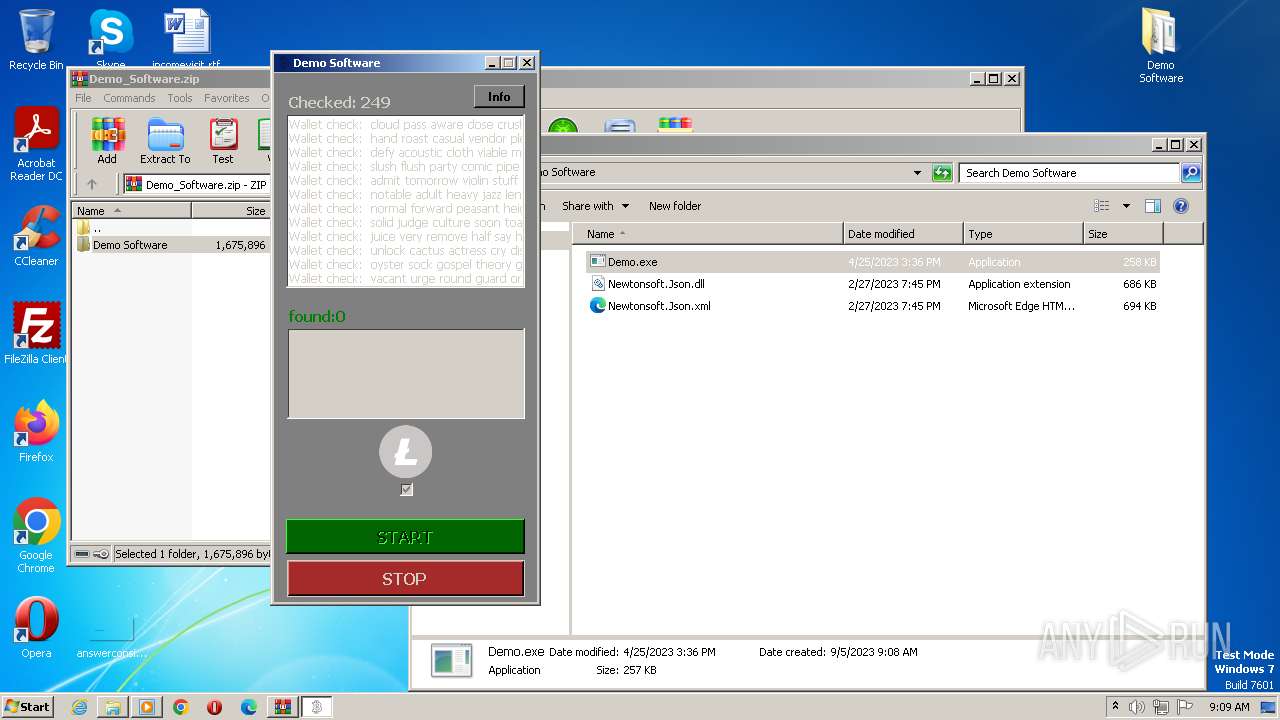
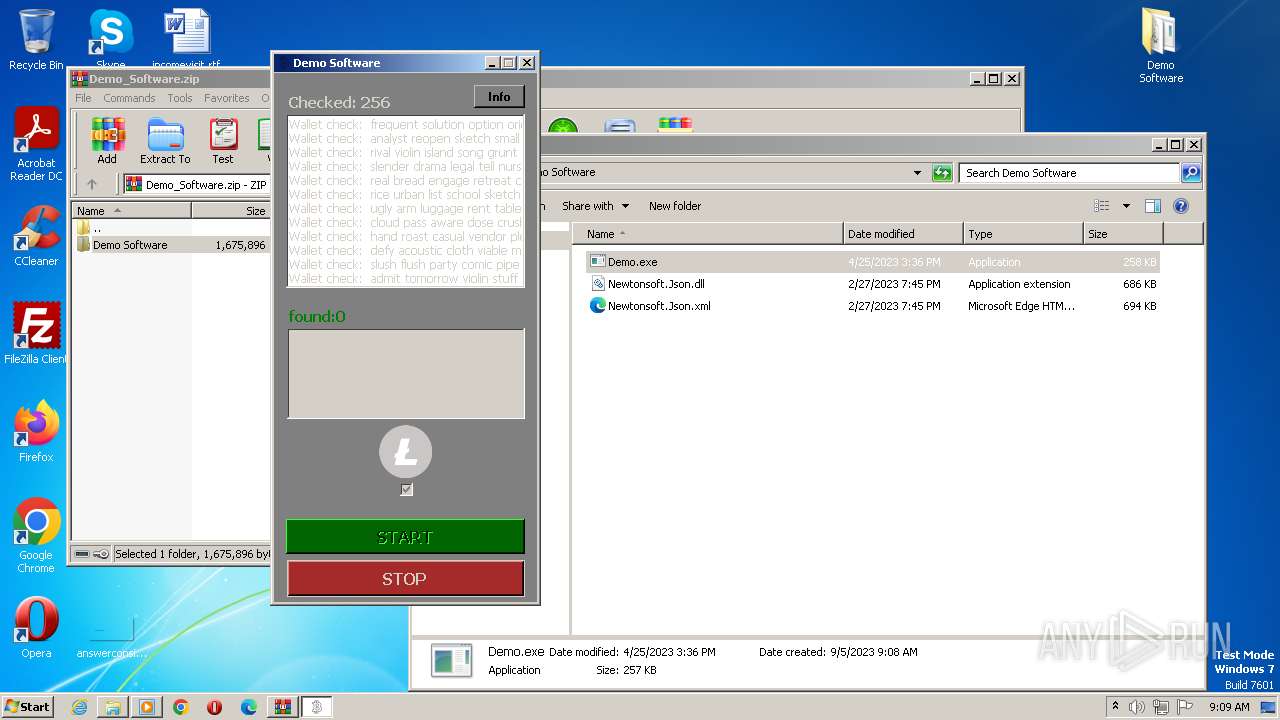
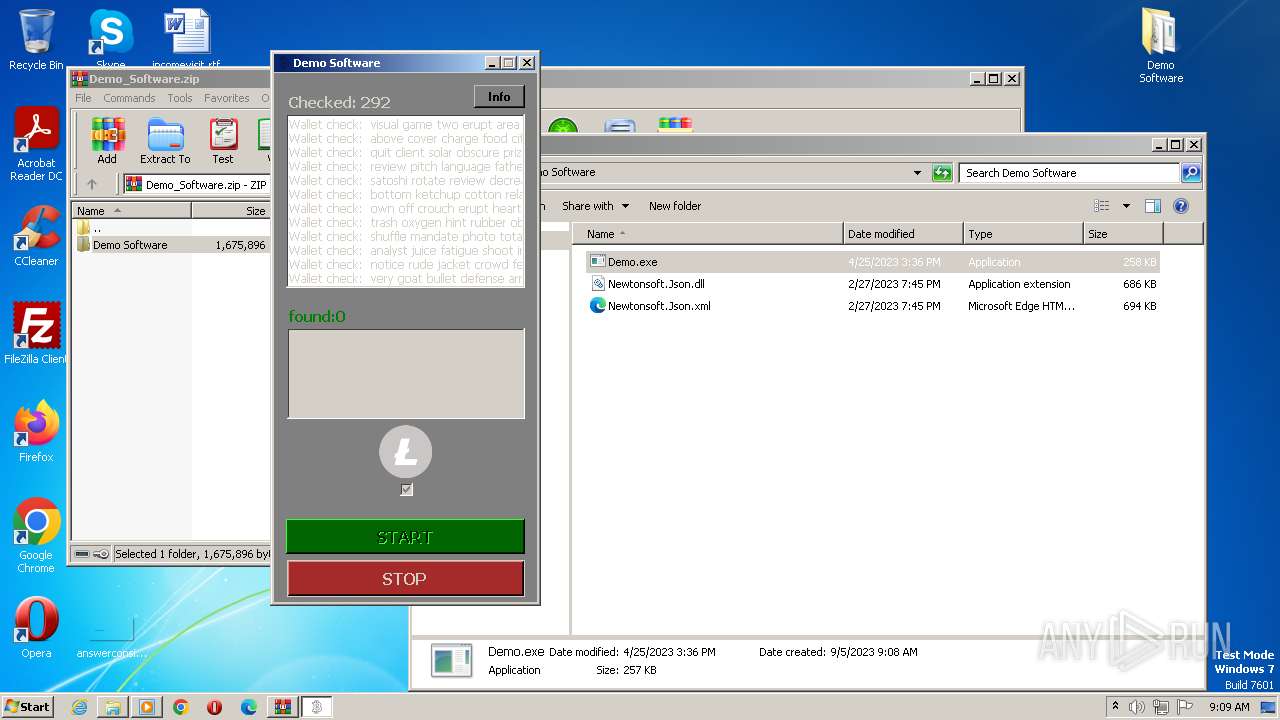
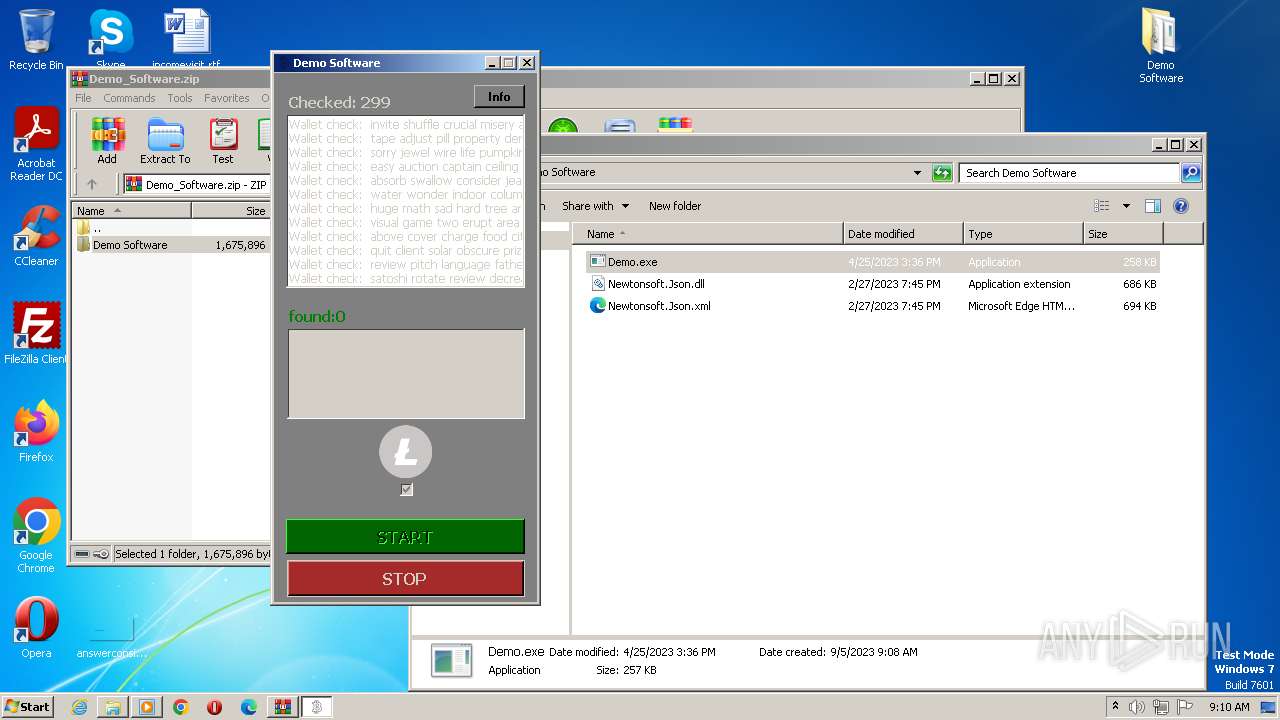
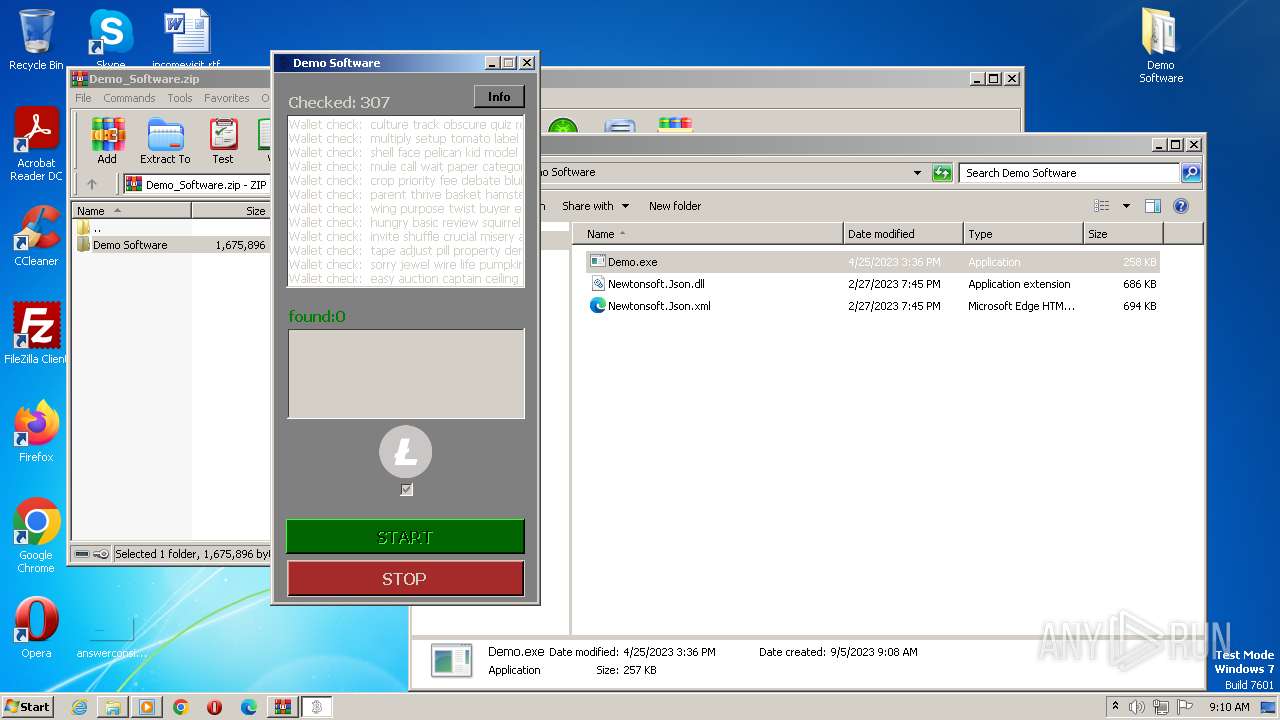
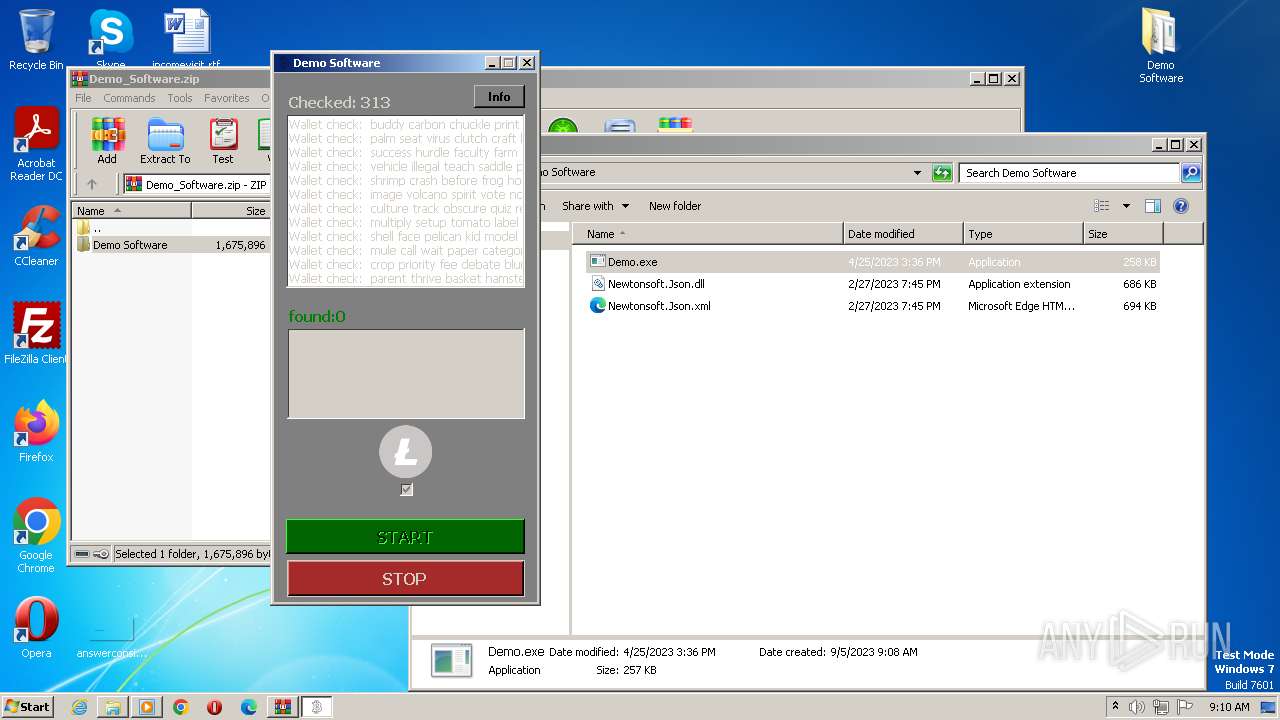
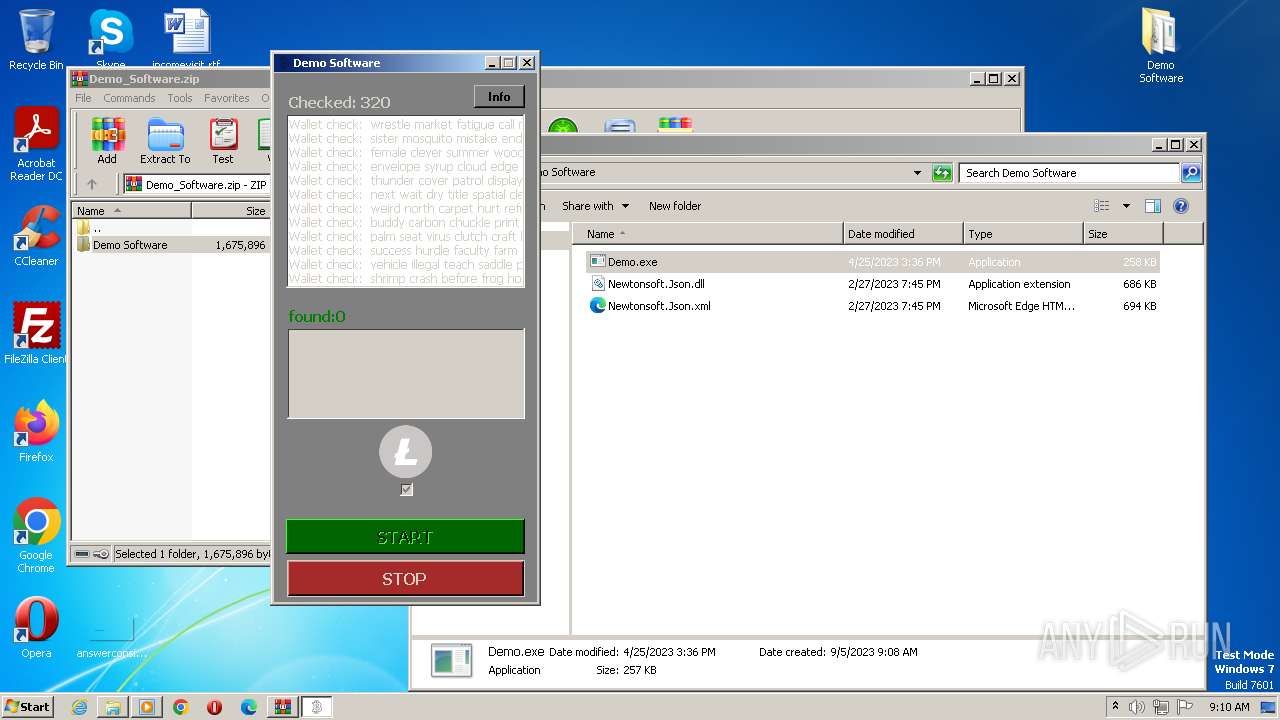
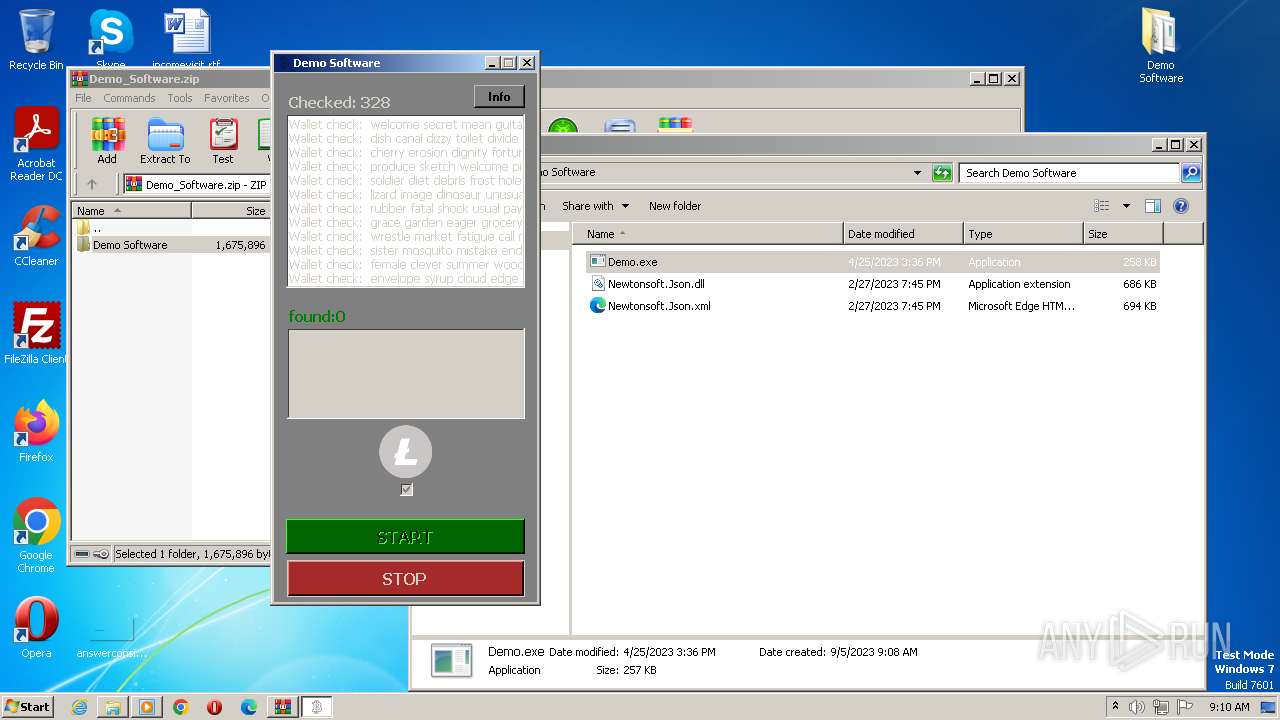
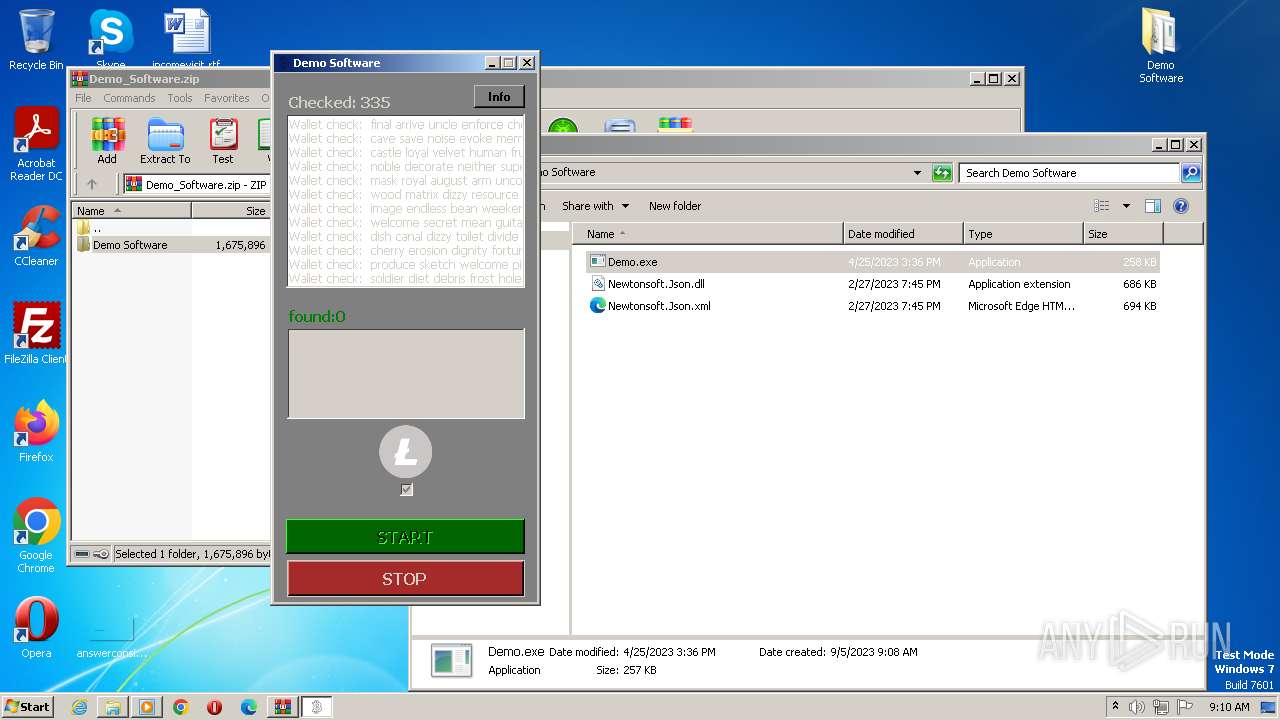
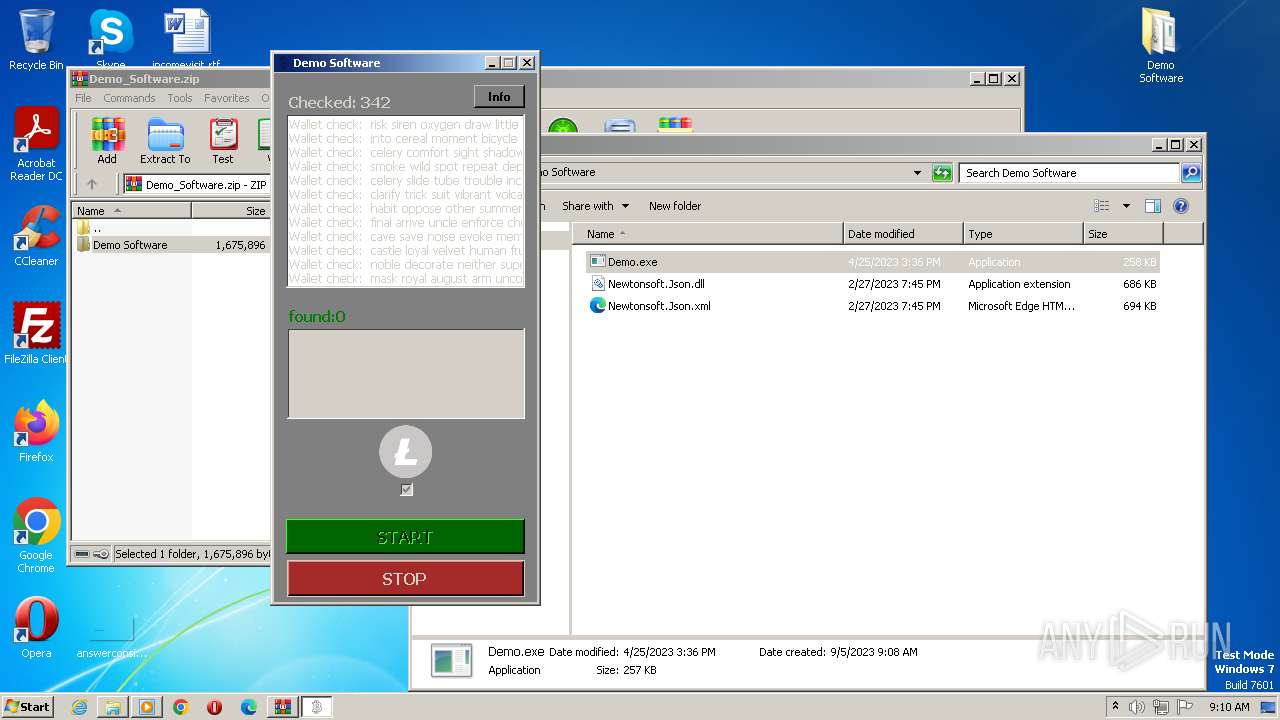
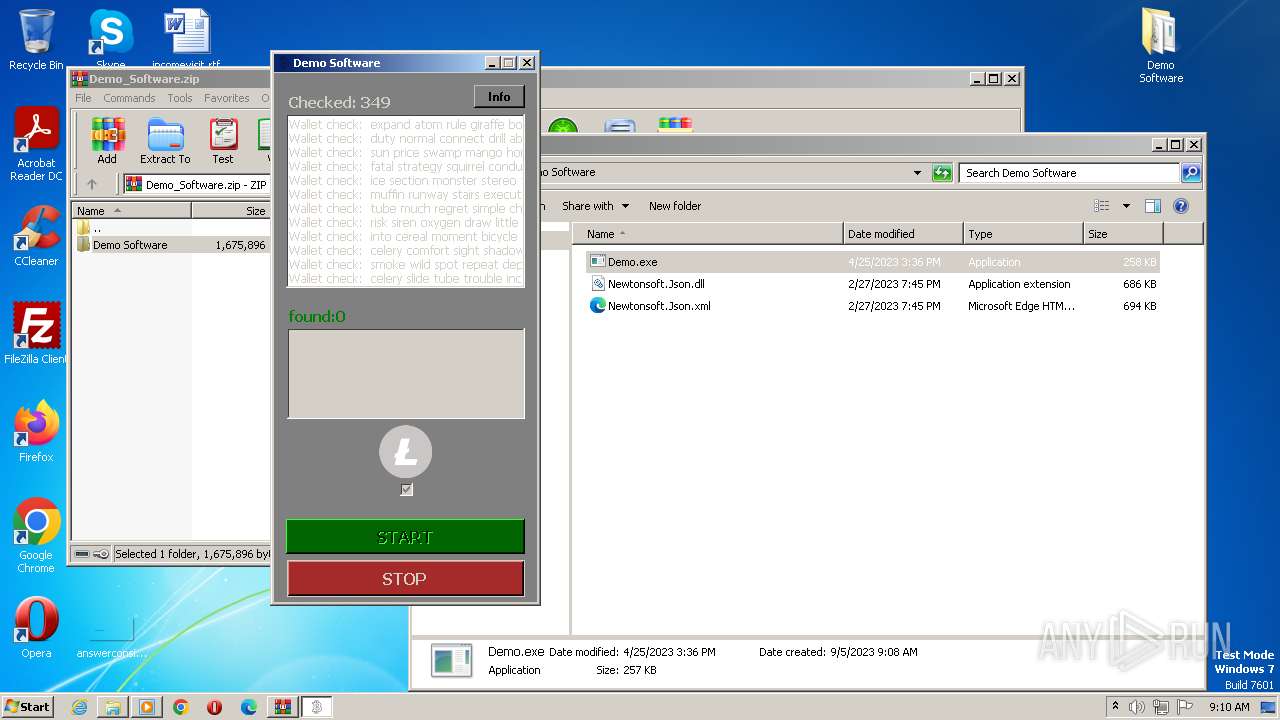
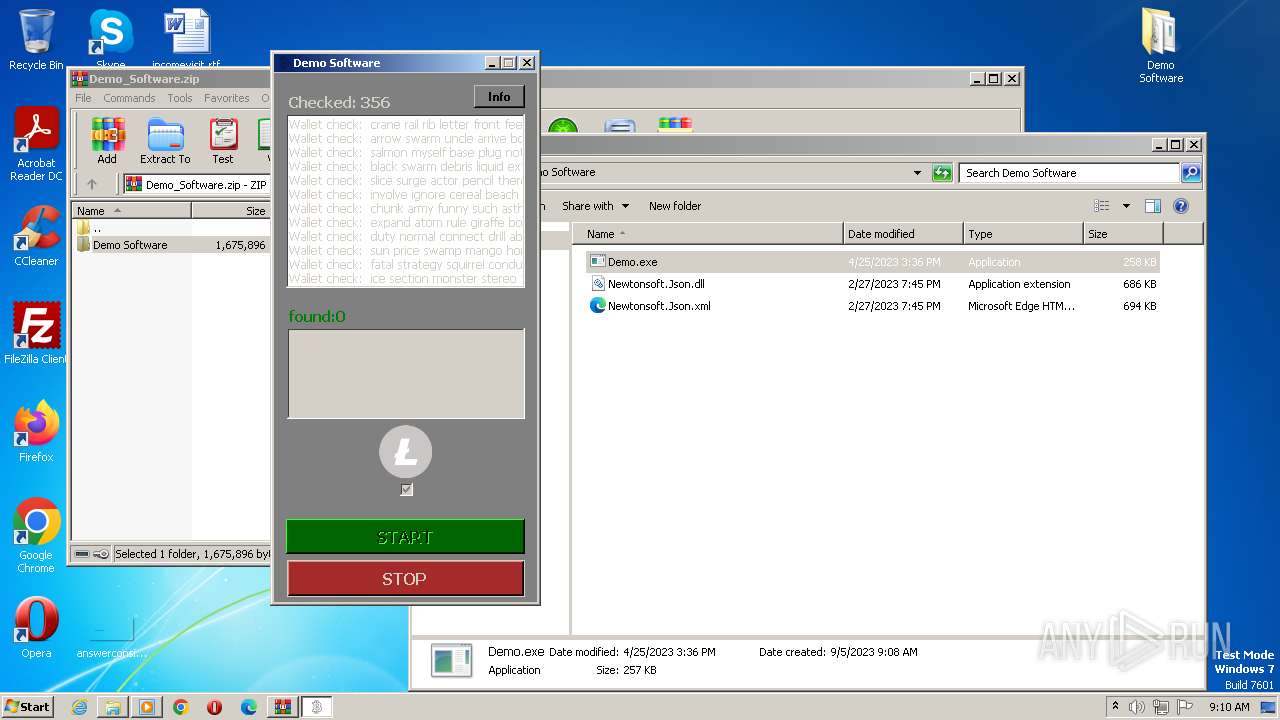
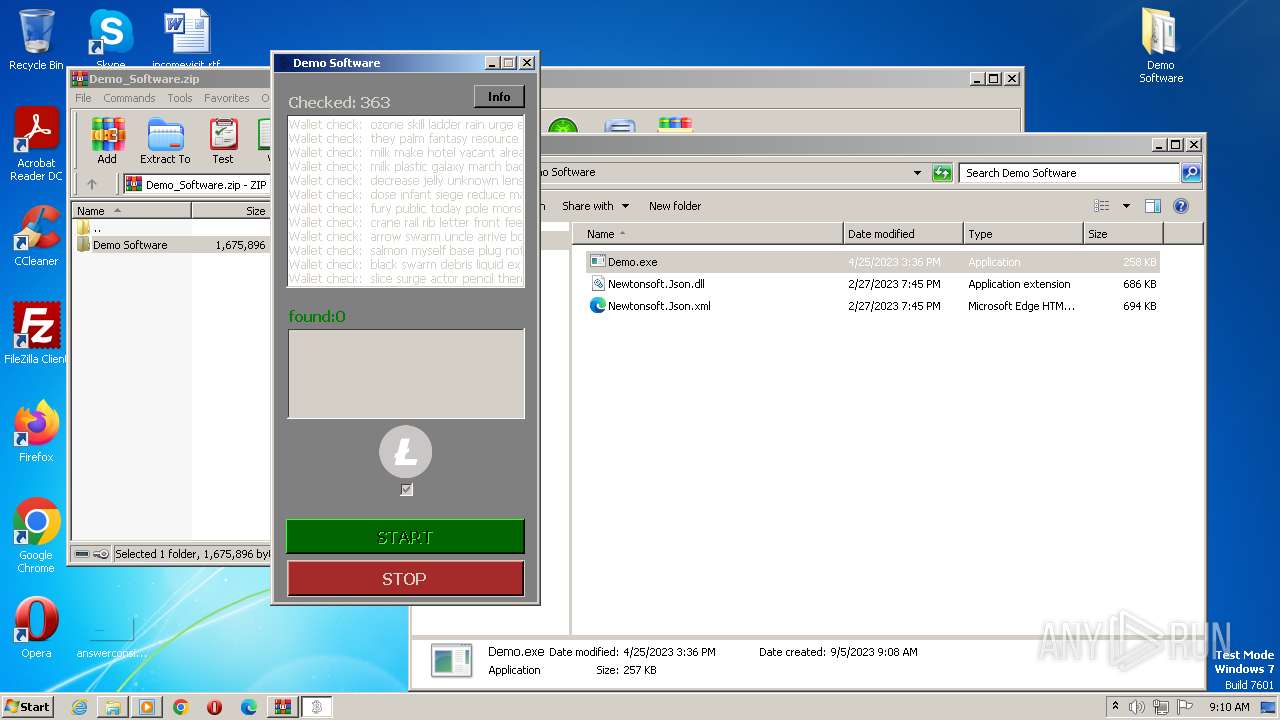
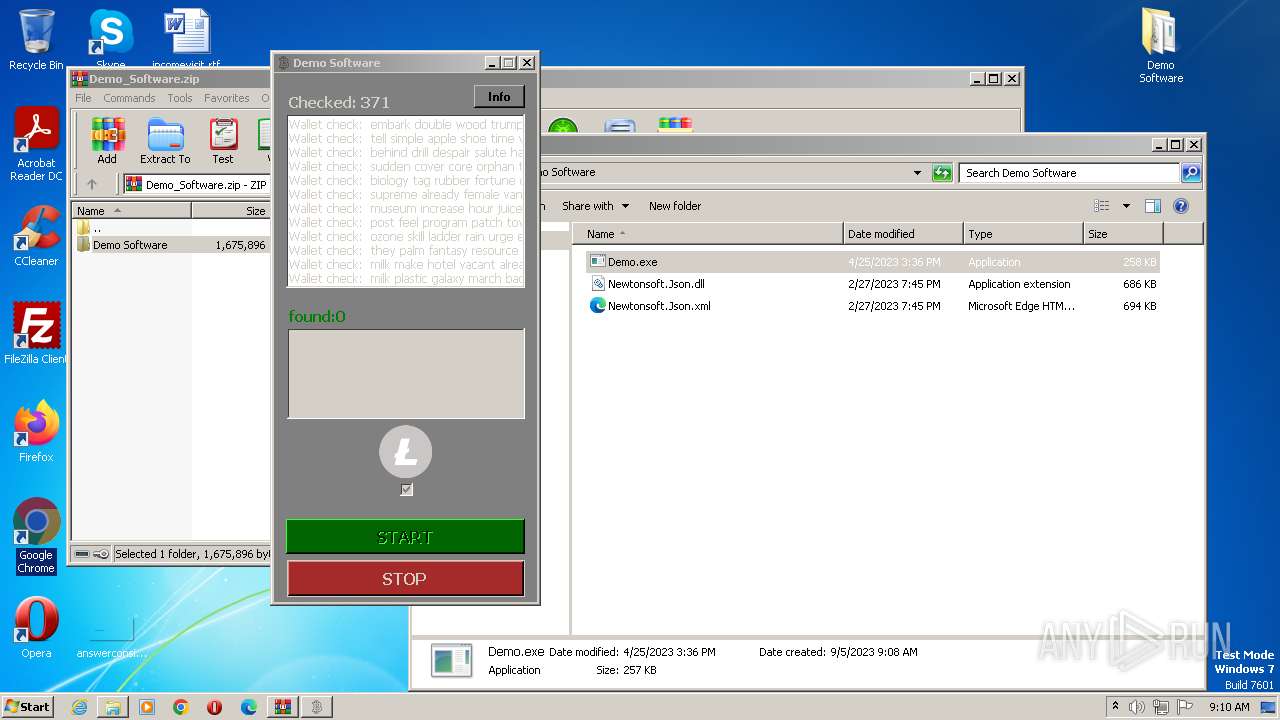
| 1348 | "C:\Users\admin\Desktop\Demo Software\Demo.exe" | C:\Users\admin\Desktop\Demo Software\Demo.exe | explorer.exe | ||||||||||||
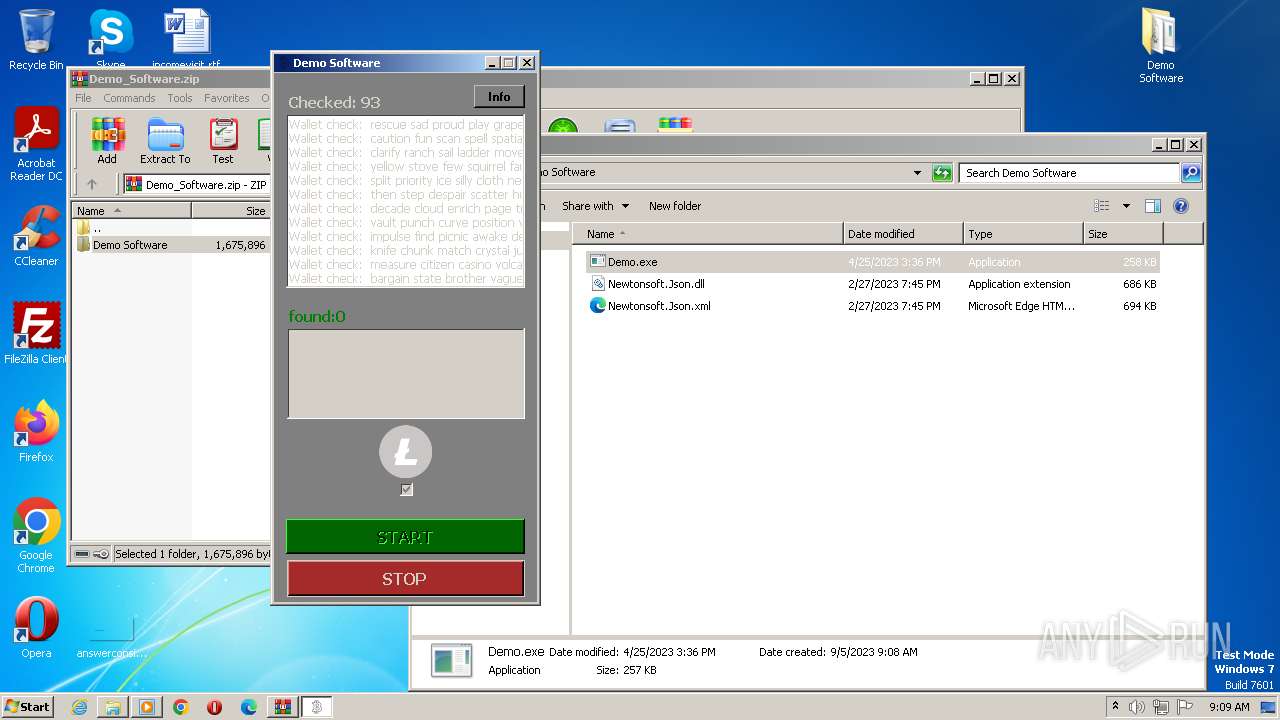
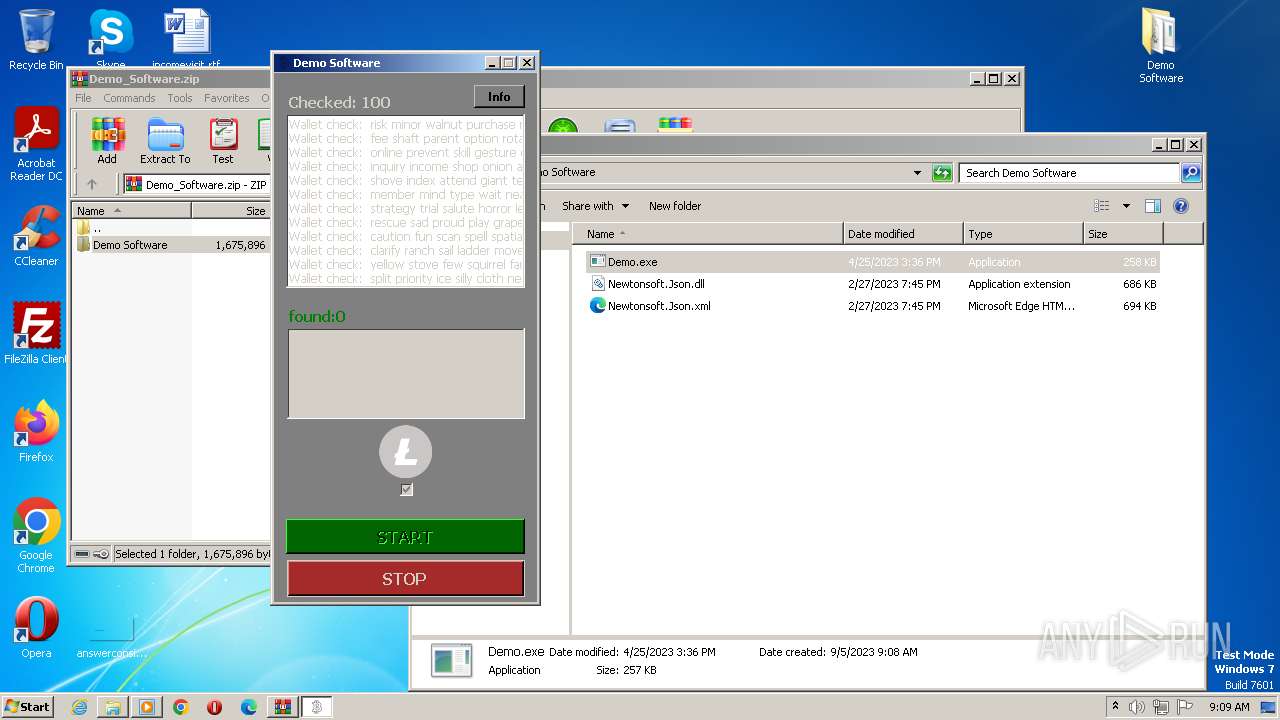
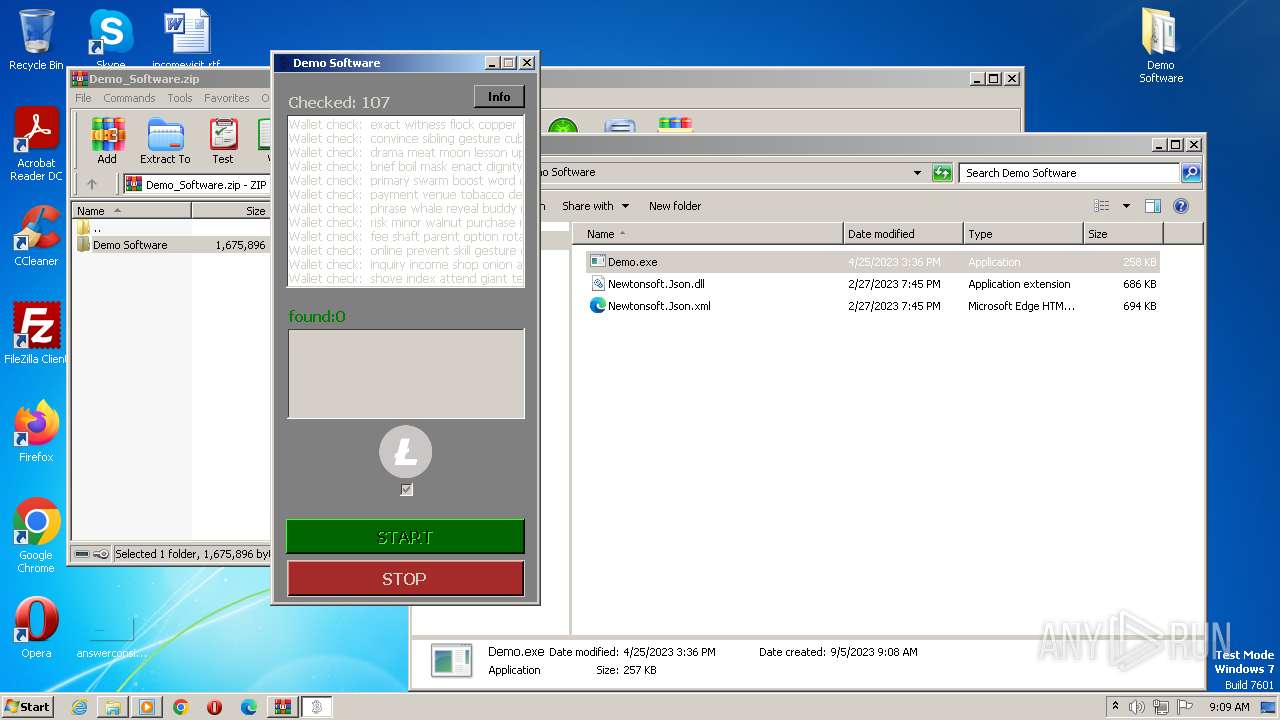
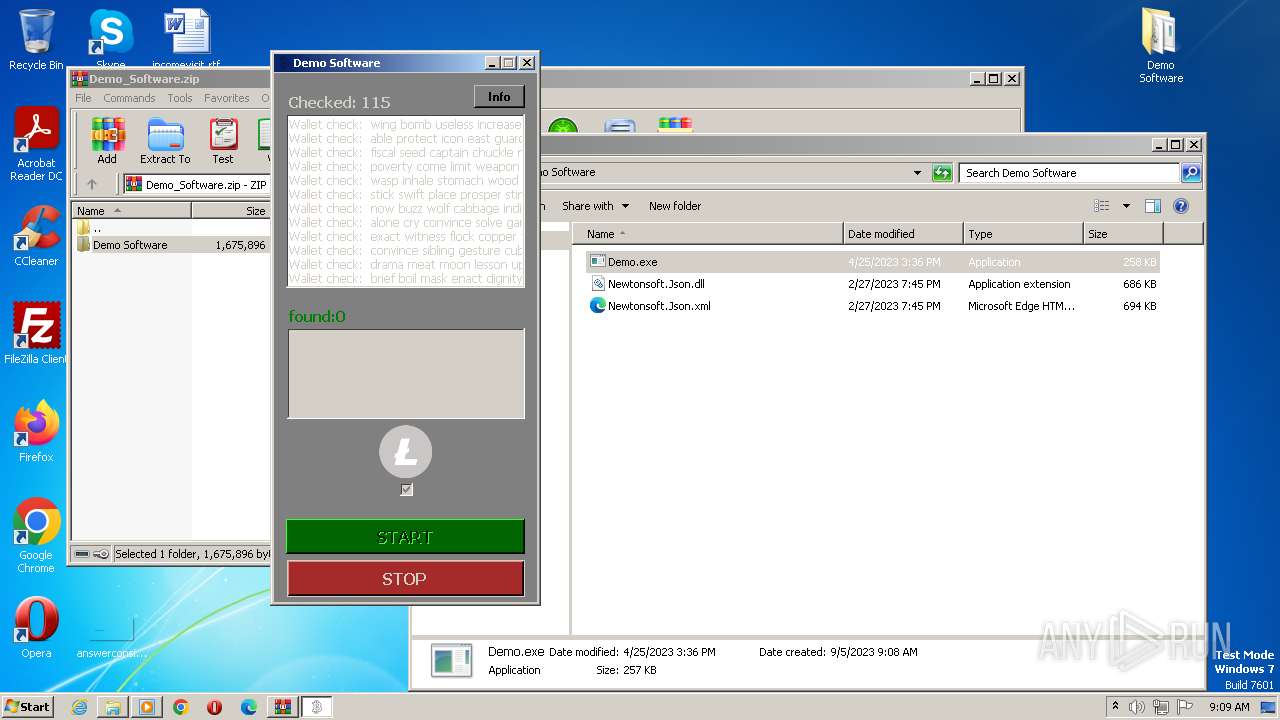
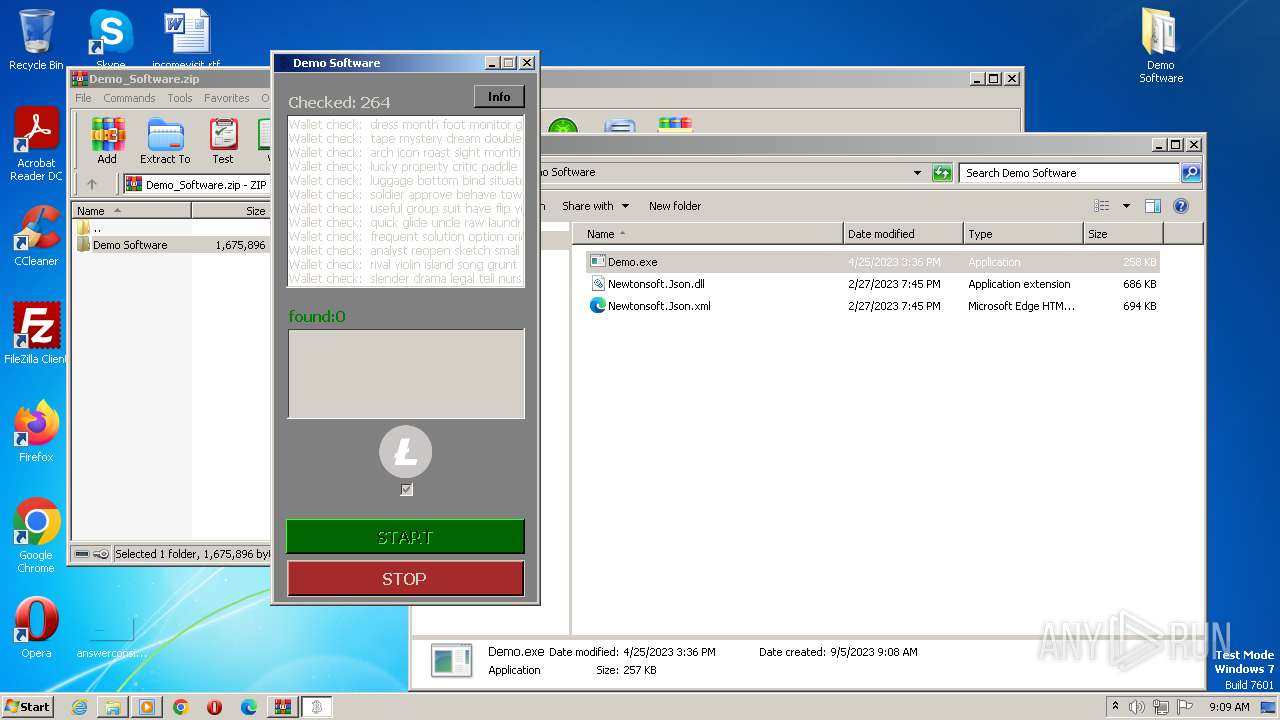
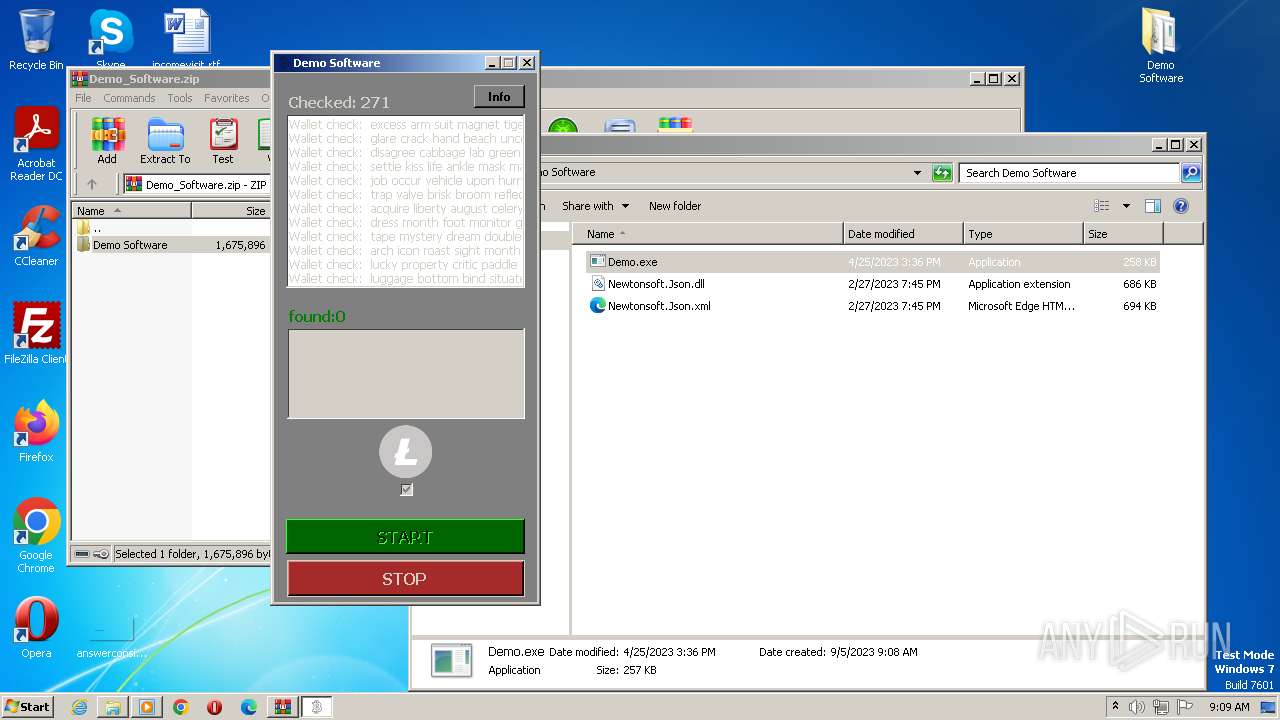
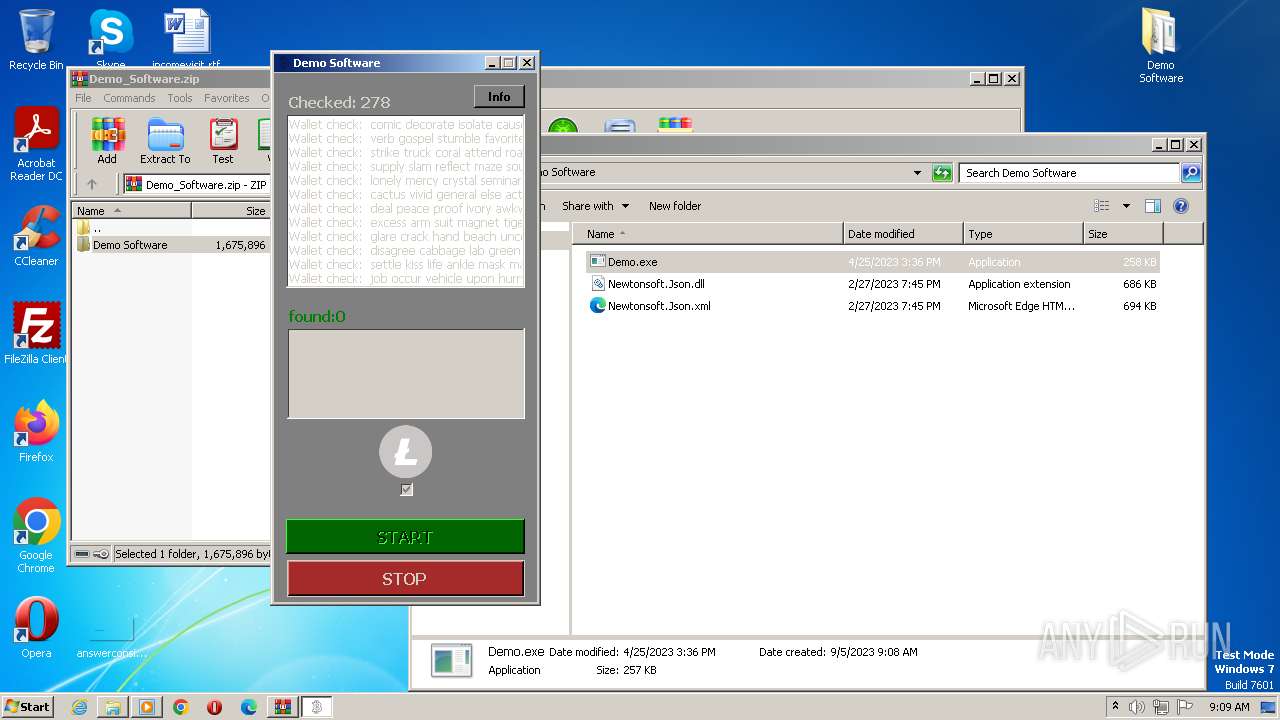
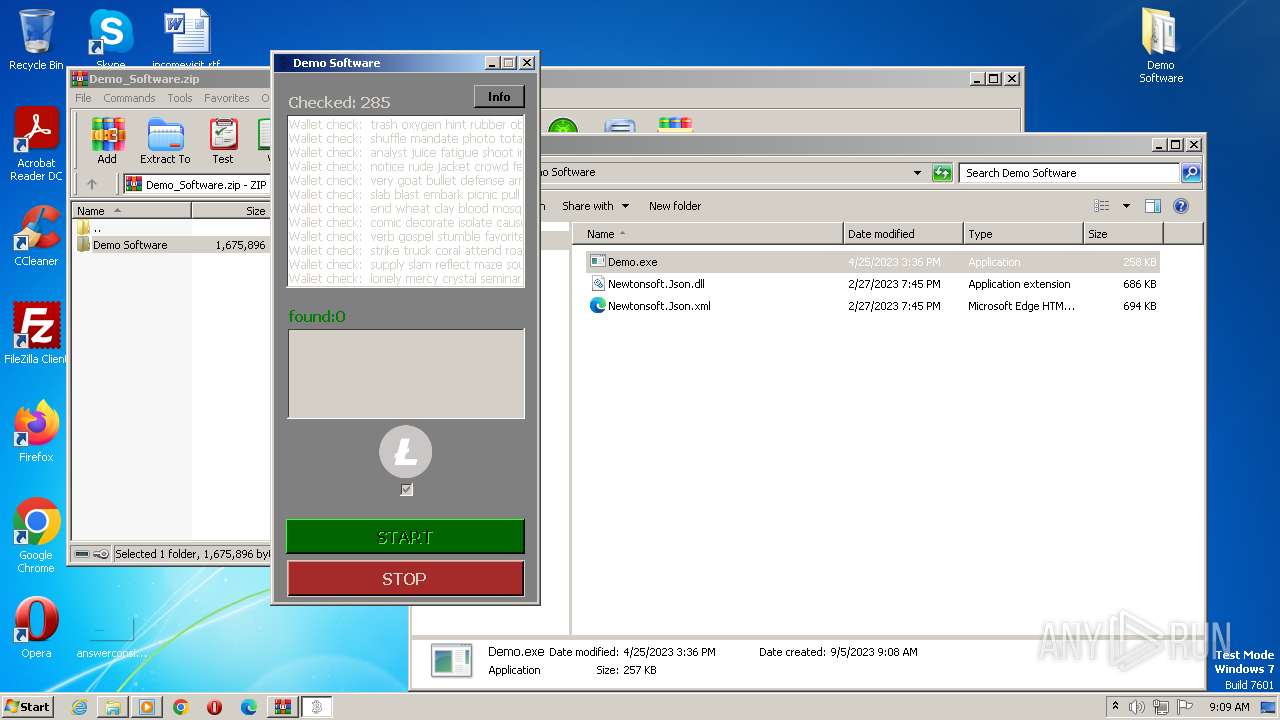
User: admin Company: Microsoft Integrity Level: MEDIUM Description: SeedBrutoforce Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
2 069
Read events
2 060
Write events
9
Delete events
0
Modification events
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2552) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 124 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa124.30716\Demo Software\Demo.exe | executable | |
MD5:C9B935CF870DF4BF84034B93C8B1326C | SHA256:C1CE030F64A91E4EA6729CD438BDD6663C0131252CAA08A544E62D8FBD0C3A8A | |||
| 124 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa124.30716\Demo Software\Newtonsoft.Json.dll | executable | |
MD5:081D9558BBB7ADCE142DA153B2D5577A | SHA256:B624949DF8B0E3A6153FDFB730A7C6F4990B6592EE0D922E1788433D276610F3 | |||
| 124 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa124.30716\Demo Software\Newtonsoft.Json.xml | xml | |
MD5:F414B3F68FE7C4F094B8FE8382F858C9 | SHA256:2D46B37B086D6848AF5F021D2D7A40581CE78AADD8EE39D309AEE4771A0EECCF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
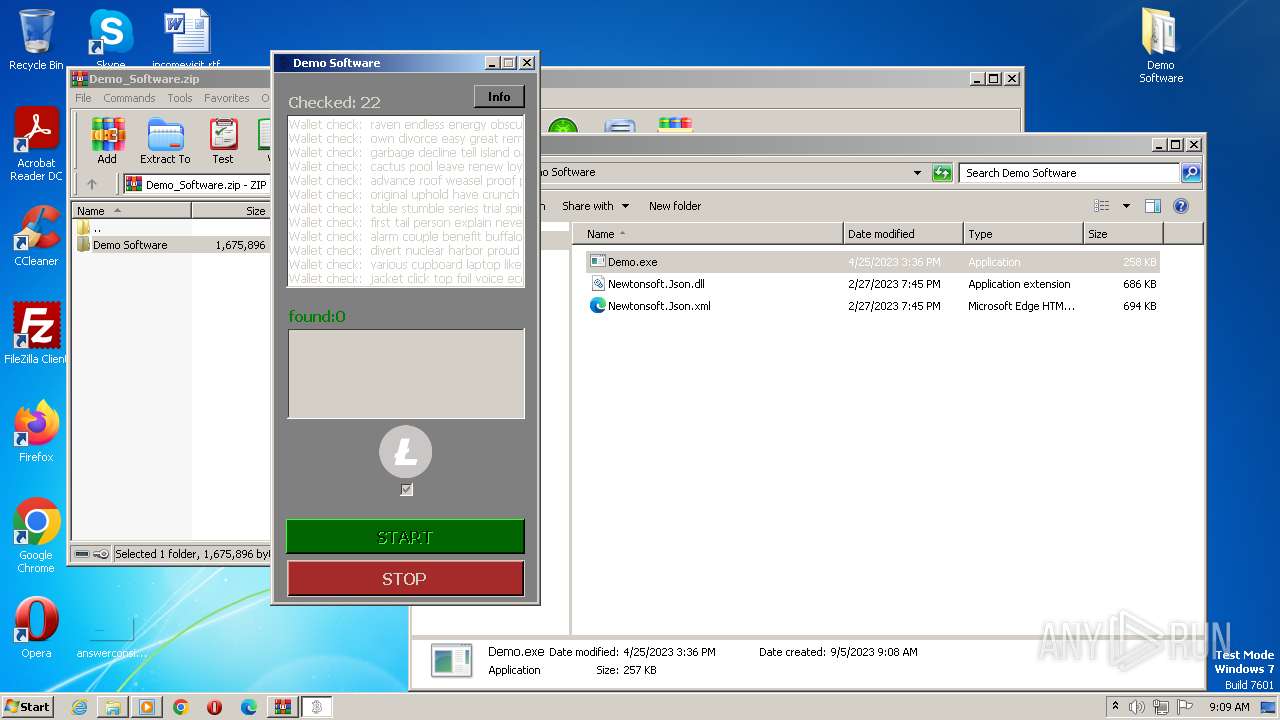
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1348 | Demo.exe | GET | 200 | 2.21.20.155:80 | http://www.msftncsi.com/ncsi.txt | unknown | text | 14 b | suspicious |
1348 | Demo.exe | GET | 200 | 2.21.20.155:80 | http://www.msftncsi.com/ncsi.txt | unknown | text | 14 b | suspicious |
1348 | Demo.exe | GET | 200 | 2.21.20.155:80 | http://www.msftncsi.com/ncsi.txt | unknown | text | 14 b | suspicious |
1348 | Demo.exe | GET | 200 | 2.21.20.155:80 | http://www.msftncsi.com/ncsi.txt | unknown | text | 14 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1348 | Demo.exe | 2.21.20.155:80 | www.msftncsi.com | Akamai International B.V. | DE | suspicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
www.msftncsi.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report