| File name: | Clear-TemplateSearch.b5010.SK048.ed.exe |
| Full analysis: | https://app.any.run/tasks/b293378f-692e-4466-b568-100a48001d2e |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2024, 21:26:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4D01267756C208CA6ED1D5C10E29B874 |
| SHA1: | CF9750E26D2FF4A77B85BB27F325387DE2DA9A02 |
| SHA256: | 4735EAFE9826D48C494A6ED662F6BE40930A3F7234D10C526D2CCA5B42D2C46F |
| SSDEEP: | 98304:f+cD4dnAcuLHn+n+HuacjqW3Vz89dWG2d1WORyA3MCGm1Q2mYV5xH8HbOKJ+CxX5:f3X64 |
MALICIOUS
Drops the executable file immediately after the start
- Clear-TemplateSearch.b5010.SK048.ed.exe (PID: 3384)
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
SUSPICIOUS
Executable content was dropped or overwritten
- Clear-TemplateSearch.b5010.SK048.ed.exe (PID: 3384)
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
Reads the Windows owner or organization settings
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
INFO
Checks supported languages
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
- Clear-TemplateSearch.b5010.SK048.ed.exe (PID: 3384)
Create files in a temporary directory
- Clear-TemplateSearch.b5010.SK048.ed.exe (PID: 3384)
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
Reads the computer name
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
Reads Environment values
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
Reads the machine GUID from the registry
- Clear-TemplateSearch.b5010.SK048.ed.tmp (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:14 16:10:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 63488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.4.0 |
| ProductVersionNumber: | 1.1.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Clear.App |
| FileDescription: | Clear Setup |
| FileVersion: | 1.1.4.0 |
| LegalCopyright: | Clear.App |
| OriginalFileName: | |
| ProductName: | Clear |
| ProductVersion: | 1.1.4.0/Stub::1.1.4.0/7cef363/2024-03-28T14:31:35+ |
Total processes
40
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3384 | "C:\Users\admin\AppData\Local\Temp\Clear-TemplateSearch.b5010.SK048.ed.exe" | C:\Users\admin\AppData\Local\Temp\Clear-TemplateSearch.b5010.SK048.ed.exe | explorer.exe | ||||||||||||
User: admin Company: Clear.App Integrity Level: MEDIUM Description: Clear Setup Exit code: 3762504530 Version: 1.1.4.0 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\is-5839L.tmp\Clear-TemplateSearch.b5010.SK048.ed.tmp" /SL5="$7015A,4024649,806400,C:\Users\admin\AppData\Local\Temp\Clear-TemplateSearch.b5010.SK048.ed.exe" | C:\Users\admin\AppData\Local\Temp\is-5839L.tmp\Clear-TemplateSearch.b5010.SK048.ed.tmp | Clear-TemplateSearch.b5010.SK048.ed.exe | ||||||||||||
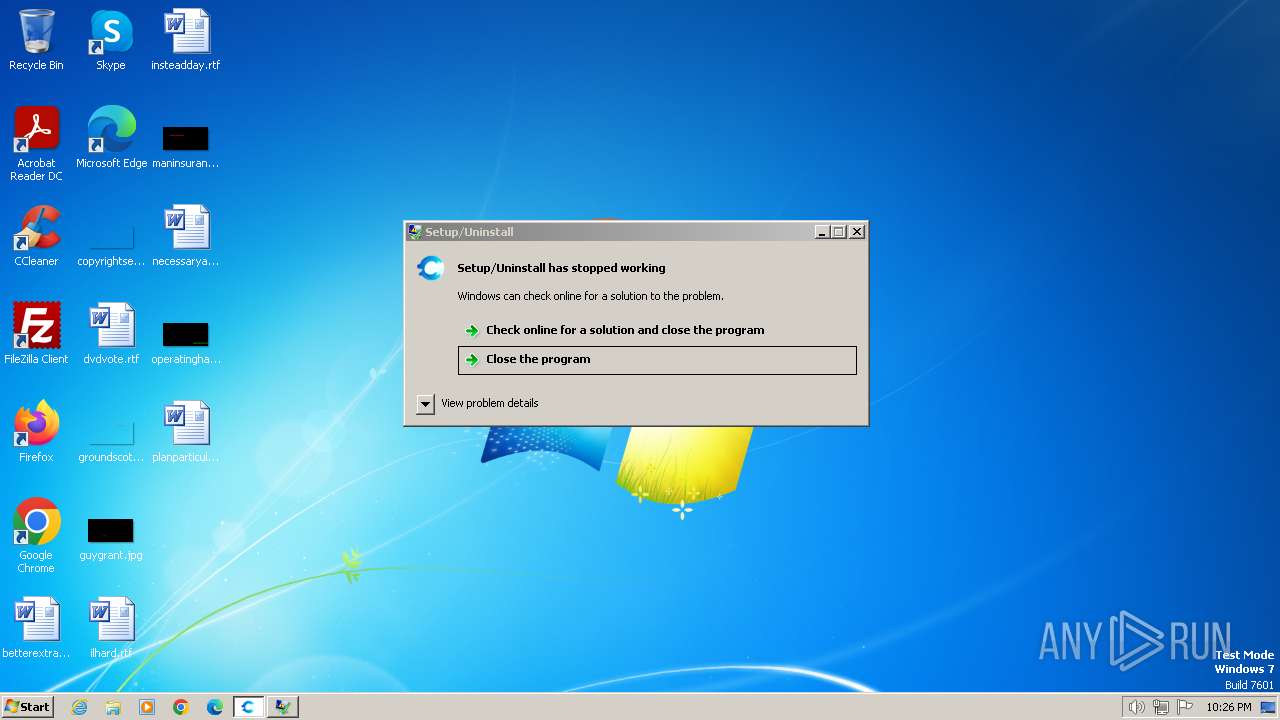
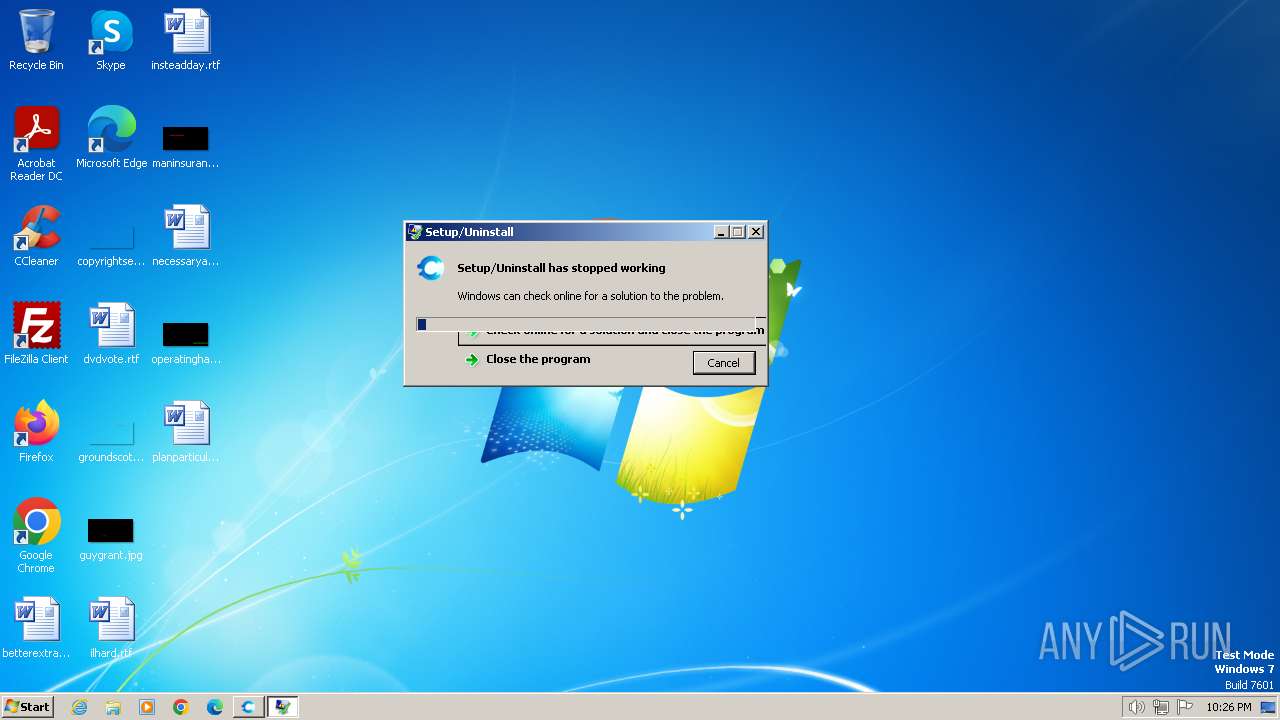
User: admin Company: Clear.App Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 3762504530 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
422
Read events
419
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3416) Clear-TemplateSearch.b5010.SK048.ed.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 580D00000C3575CAA1C9DA01 | |||
| (PID) Process: | (3416) Clear-TemplateSearch.b5010.SK048.ed.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 76239174A8AEB9F39F6D6F0B7C1DC66F6FB4B32C5CD7C0C25CA57E9AD3D7372C | |||
| (PID) Process: | (3416) Clear-TemplateSearch.b5010.SK048.ed.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\Profiles\profile_map.txt | text | |
MD5:6444764B2CF9F2B2C274787263A78CCB | SHA256:1AF45A6C76B8BAA3CC167690EB748D8C367D1B5E98FE3581B6D8975632FF07F7 | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\html\js\knockout.js | text | |
MD5:052E3CBD4009F65055D36541CE9CC91D | SHA256:7EB9DAB1C04D4ABCE6749AD9D94DDD0690E3C99C6890F979F07EFE4775EE1EAB | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\HtmlInstaller.dll | executable | |
MD5:B8146F1279AF9B9A6D4C7F377B1F93A1 | SHA256:C5A5F540914D46F93782DA9188EC16F75A7ED495512D8D3086BE9232EA8E7B8C | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\html\css\baseline.css | text | |
MD5:4C862C415540662AAB18410305790F9A | SHA256:085862D788D0DFE742617007AB076333D5C583AF4D179E73825F7718F2B8846D | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\Networking.dll | executable | |
MD5:6A1BE1A08C9A3839F2A4F5EC107C88A2 | SHA256:64DEC9190C5D290A11E37EC2933DDFA7ABE57153C71C2F49546EEC718A0B01ED | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\html\assets\templatesearch\background.jpg | image | |
MD5:934A2B6D13554796727B558AFB692641 | SHA256:6ED307710D2E815C16E3E15DB60EE6A02337EBCAB6D566DFC56BA4B09E45D6B2 | |||
| 3384 | Clear-TemplateSearch.b5010.SK048.ed.exe | C:\Users\admin\AppData\Local\Temp\is-5839L.tmp\Clear-TemplateSearch.b5010.SK048.ed.tmp | executable | |
MD5:BCFE6D377402B260F454902103B96183 | SHA256:EB9401BD3941D116DB155A444CE200BACC9E3A3465B723CA7F53C35E59ACC0ED | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\html\css\baseline-compliant.css | text | |
MD5:78D40BDAB40ED79853222569B9AC5BD9 | SHA256:E9B2E3C37C6463706FBE22925EB0B084AA785E78D49F65136608D9C15CA6C960 | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\html\css\baselinenew.css | text | |
MD5:4D9E4F45F1F8500EB7FE29AC4A34818D | SHA256:03ED977D9D2B9AEEE7912886185B69BABB7496DC9B45042190097F81153762DC | |||
| 3416 | Clear-TemplateSearch.b5010.SK048.ed.tmp | C:\Users\admin\AppData\Local\Temp\is-SUJBM.tmp\html\assets\common\browse_icon.png | image | |
MD5:9C26F5DD459C12F2F8A28CAFB7447520 | SHA256:3156AD4638AB7AE34E17E07A4BFC0E2509690B886506035DC92EF0EA8ADB0847 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.53.40.35:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.53.40.18:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 23.53.40.35:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
3172 | WerFault.exe | 104.208.16.93:443 | watson.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1060 | svchost.exe | 23.53.40.18:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.microsoft.com |
| whitelisted |