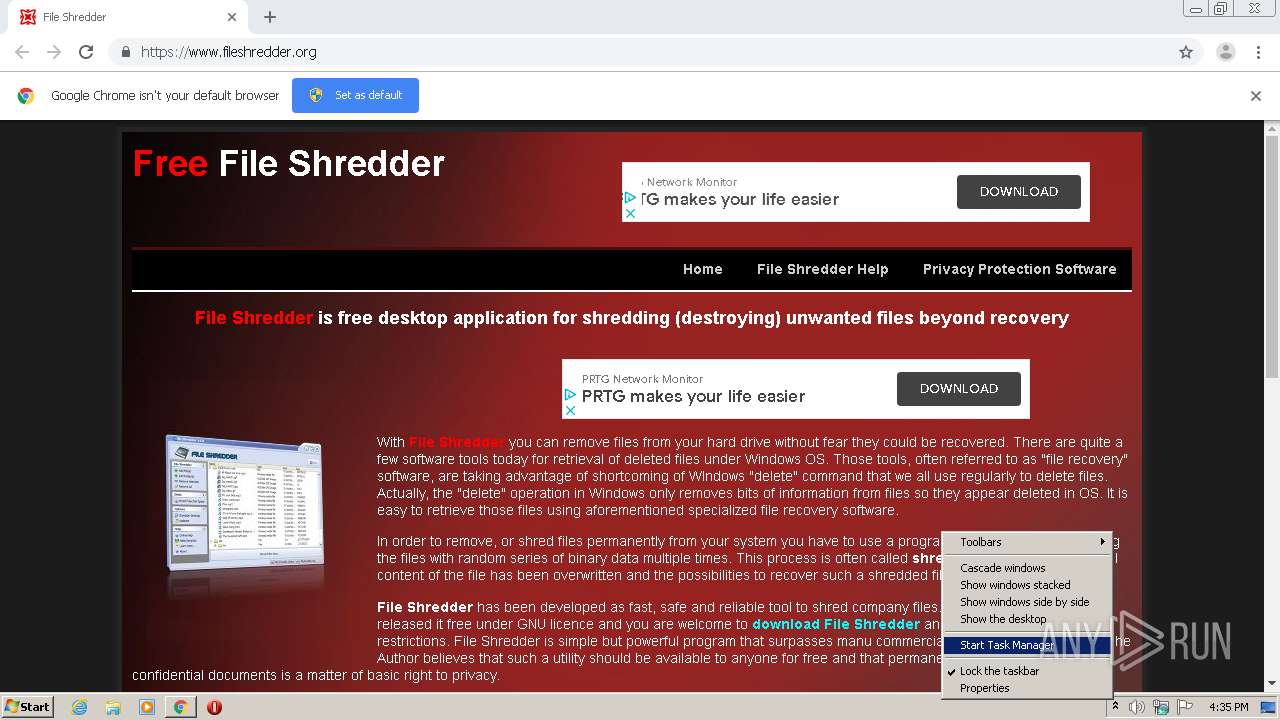
| URL: | https://www.fileshredder.org/ |
| Full analysis: | https://app.any.run/tasks/b29e32bd-e531-473d-8b26-9c3db6bd210f |
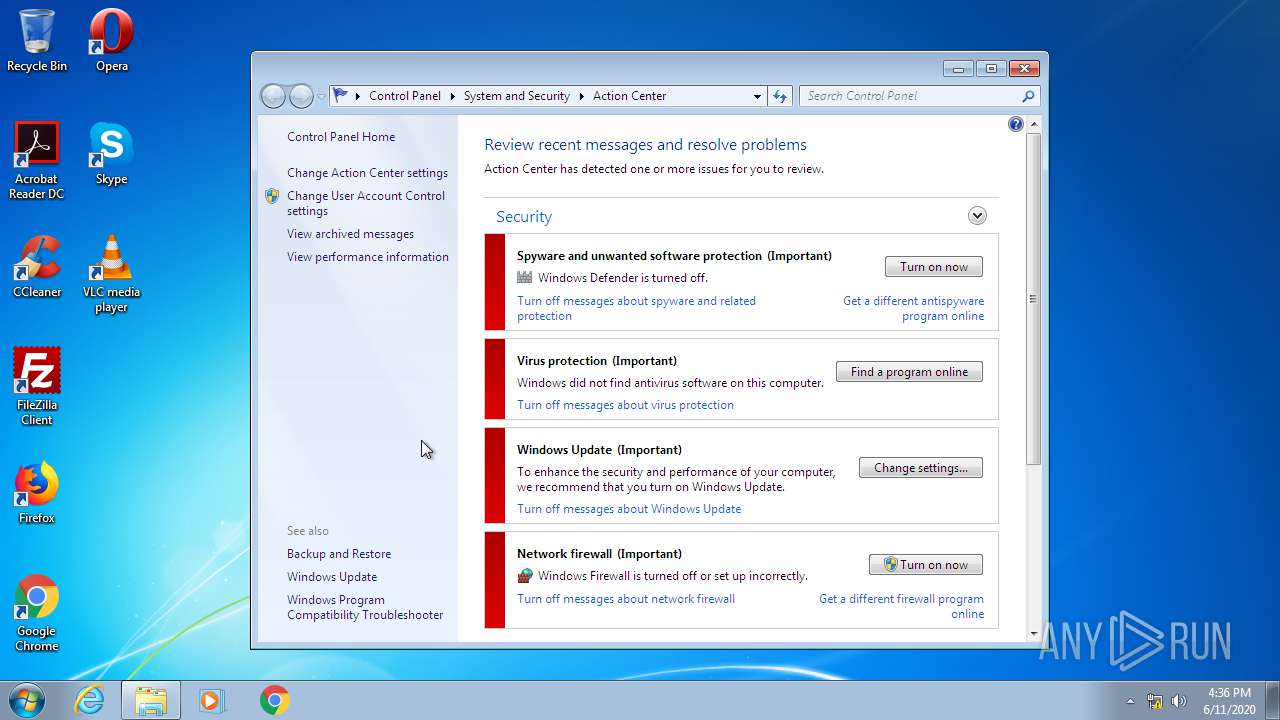
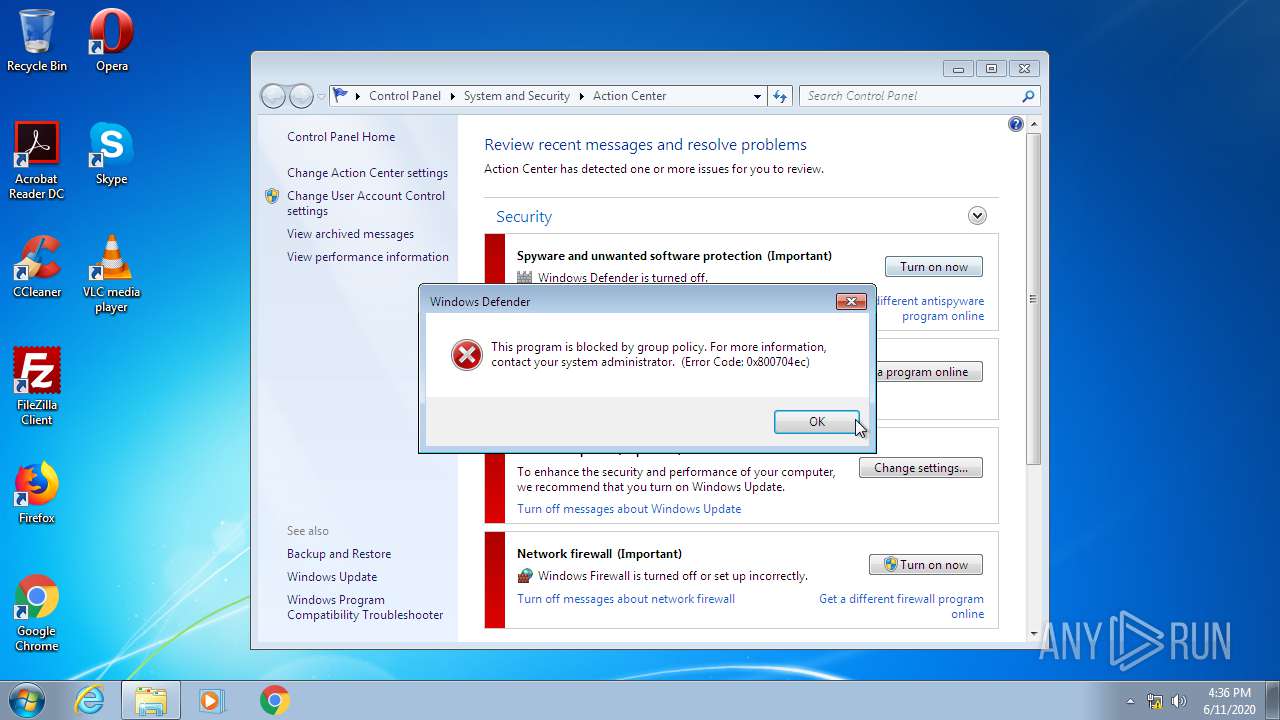
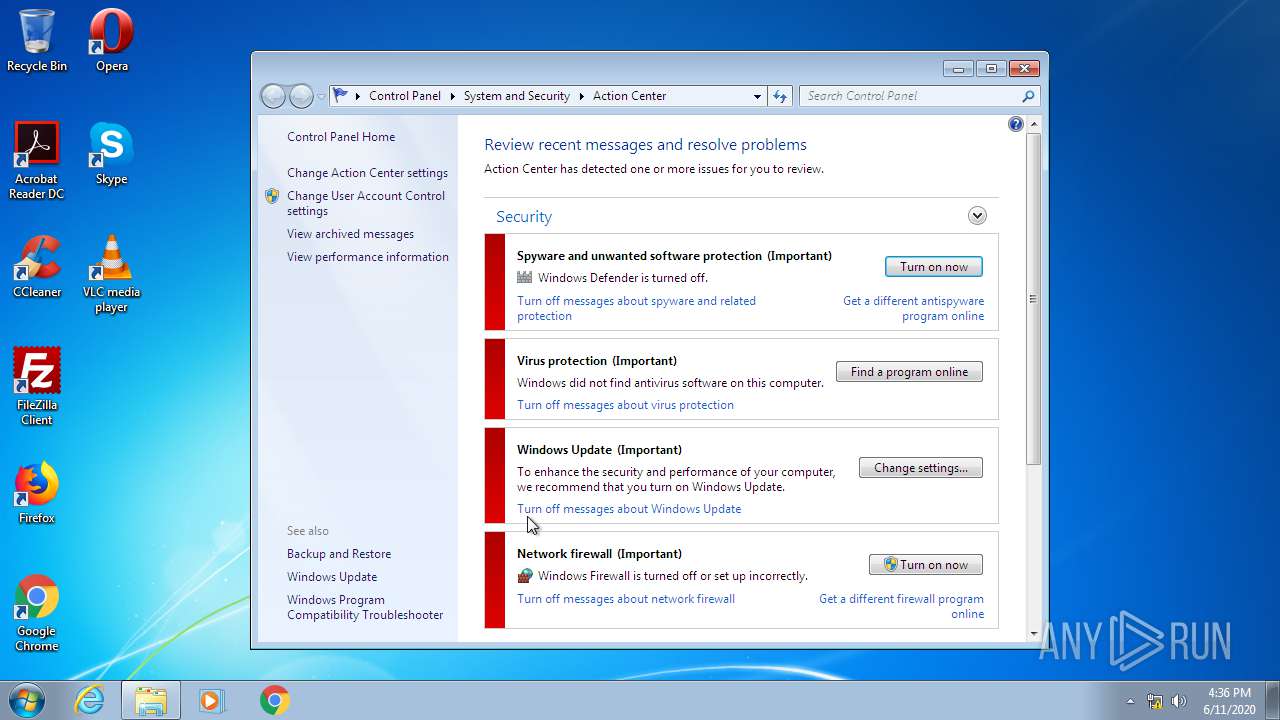
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2020, 15:35:20 |
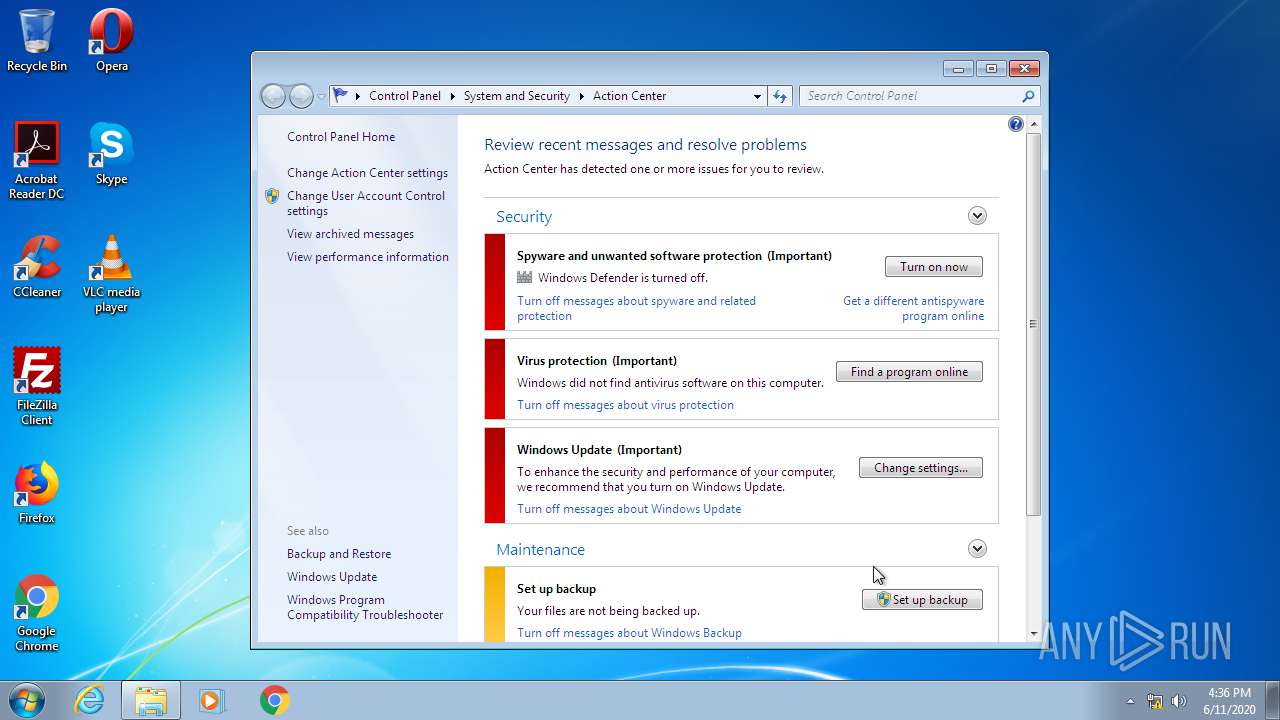
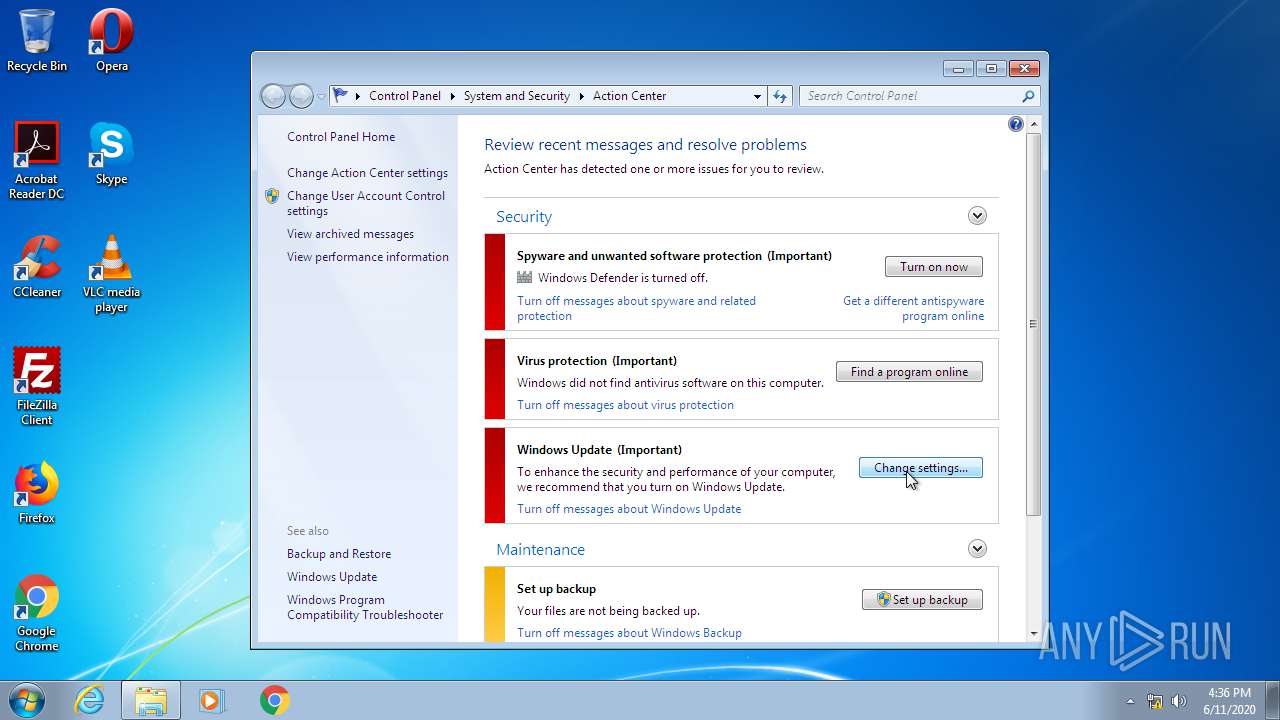
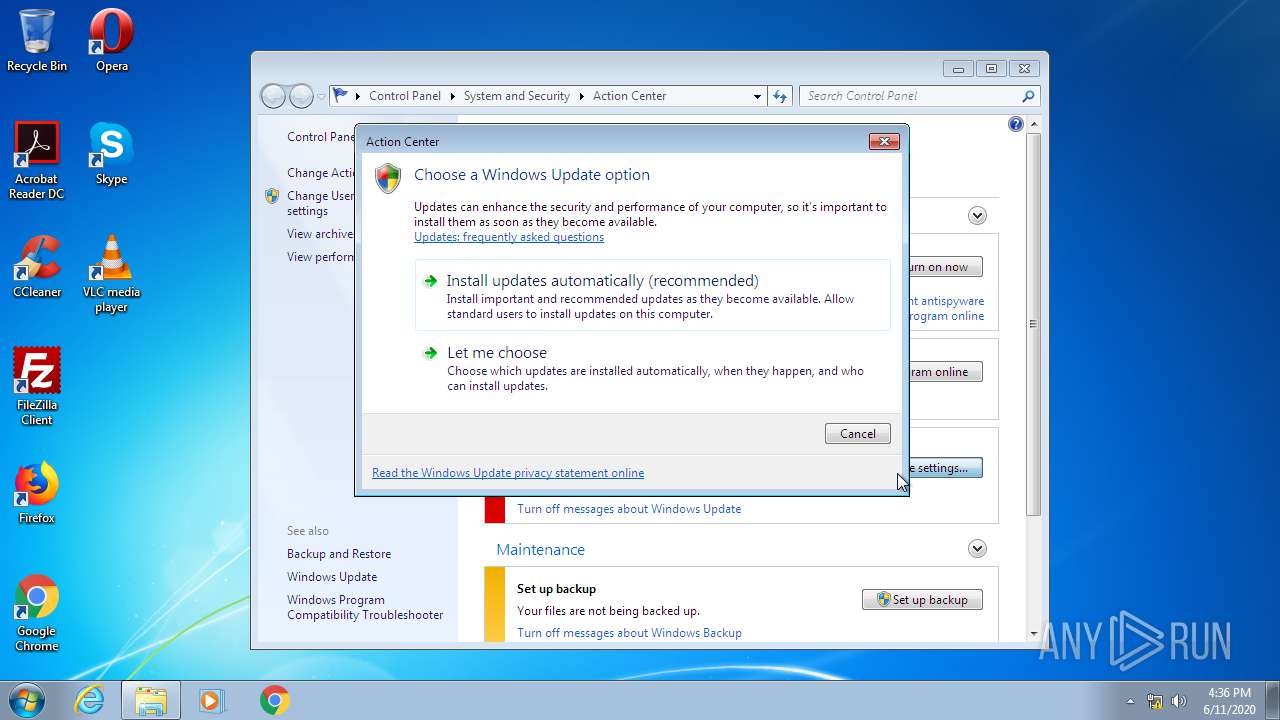
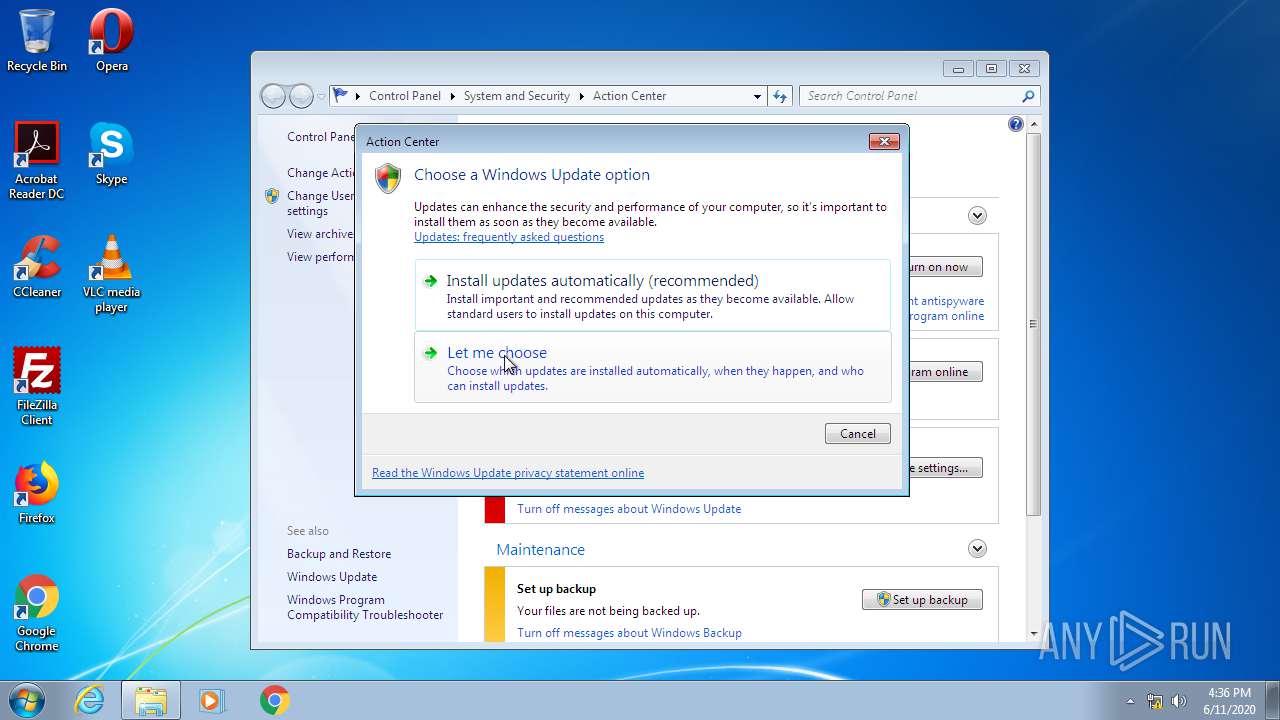
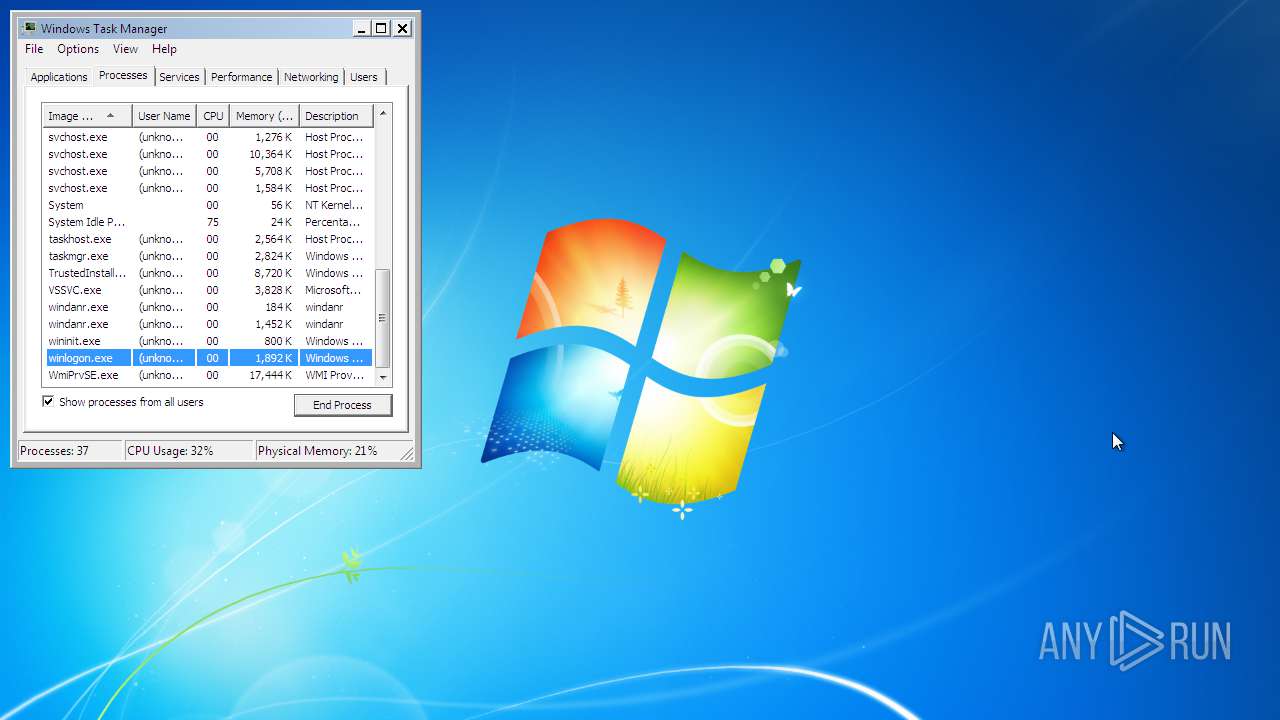
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FC732F3D468584A94C5F860F6709BAD1 |
| SHA1: | CB5494BF02820407E18975204D0275EB40BA61F3 |
| SHA256: | 473462E88DC24FE8365810CAF3156C437D6AB3F22950773F58782D15B41E9F43 |
| SSDEEP: | 3:N8DSLQ5NXABwfKn:2OLQ5Nlin |
MALICIOUS
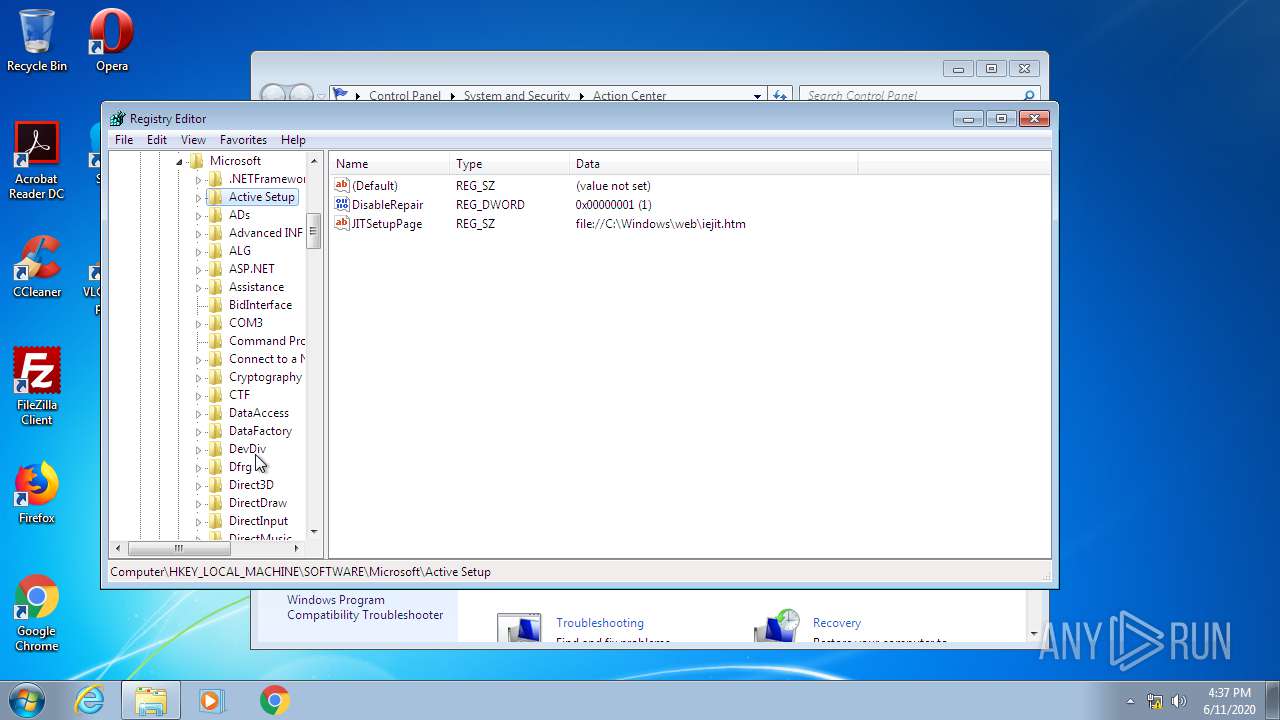
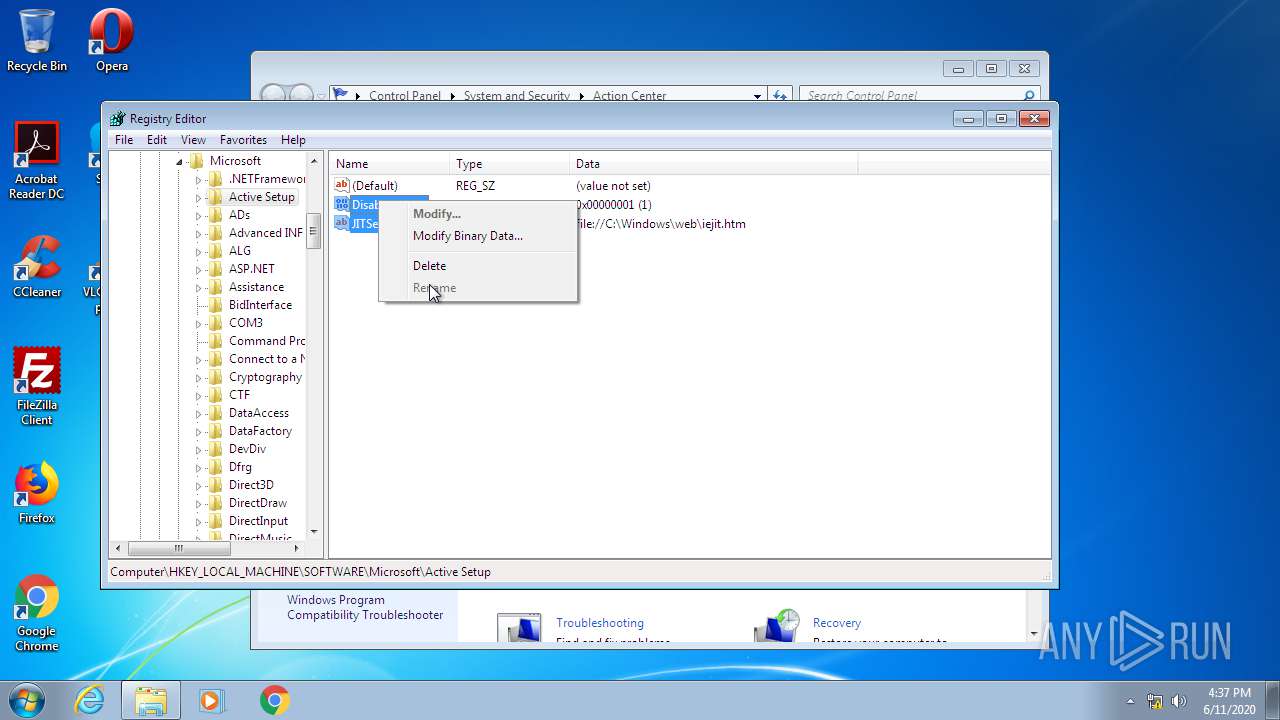
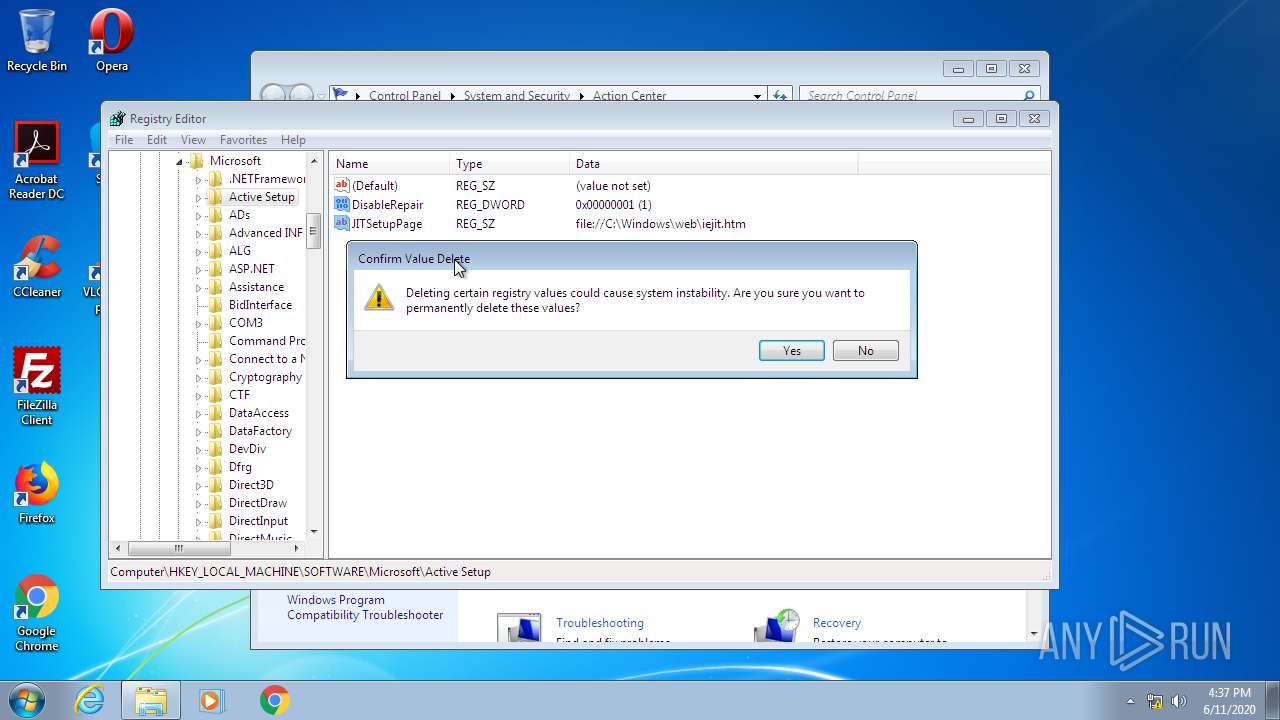
Changes internet zones settings
- ie4uinit.exe (PID: 2708)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 1992)
Application was dropped or rewritten from another process
- WuSetupV.exe (PID: 2396)
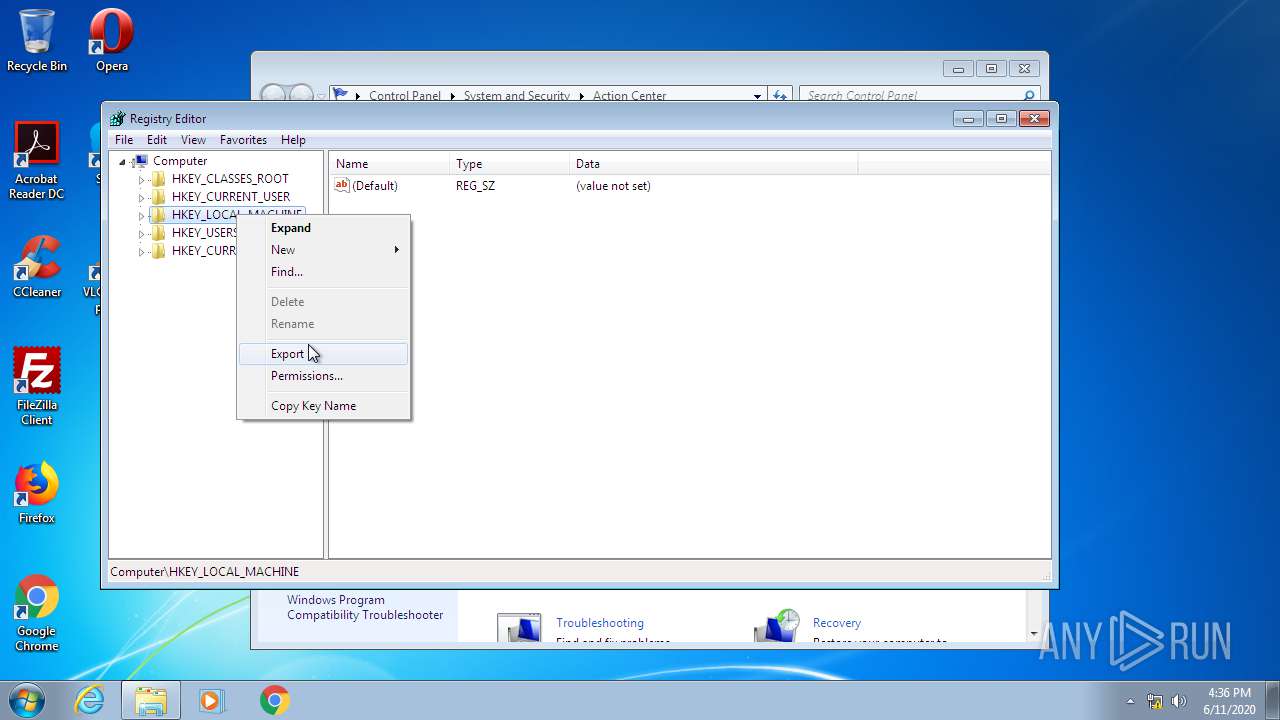
Changes settings of System certificates
- WuSetupV.exe (PID: 2396)
SUSPICIOUS
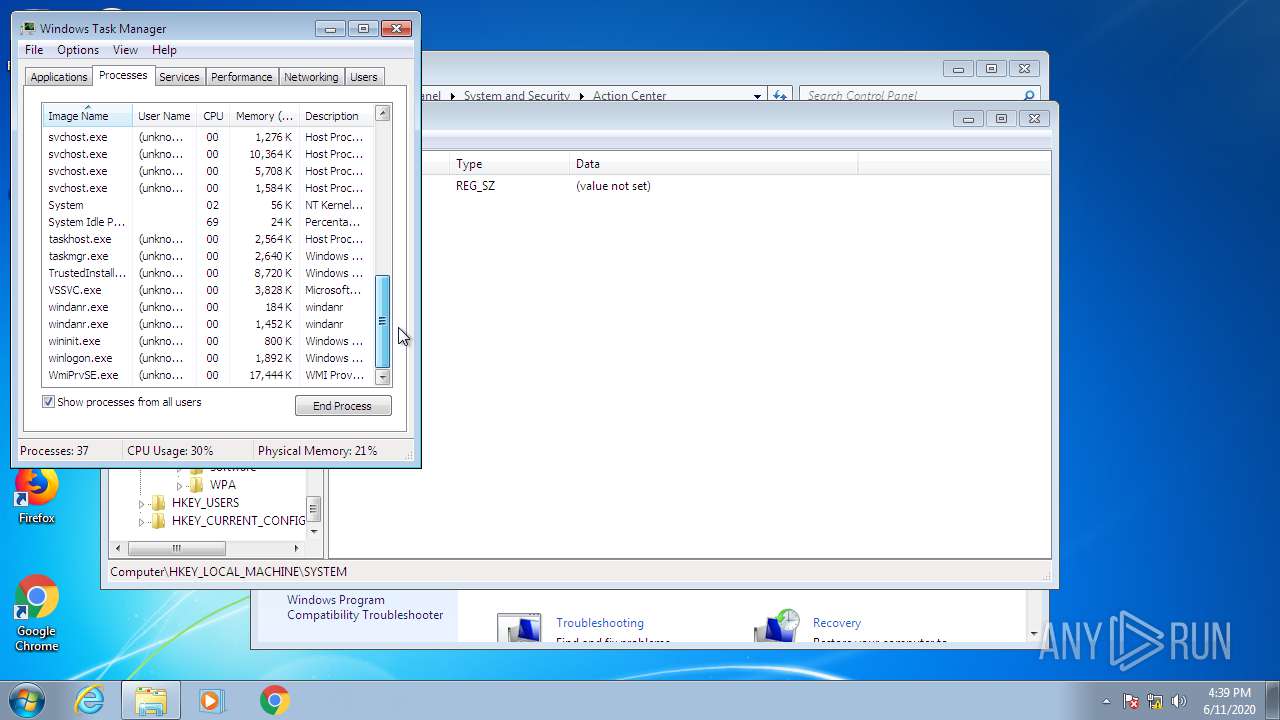
Executed as Windows Service
- taskhost.exe (PID: 3384)
- vssvc.exe (PID: 2452)
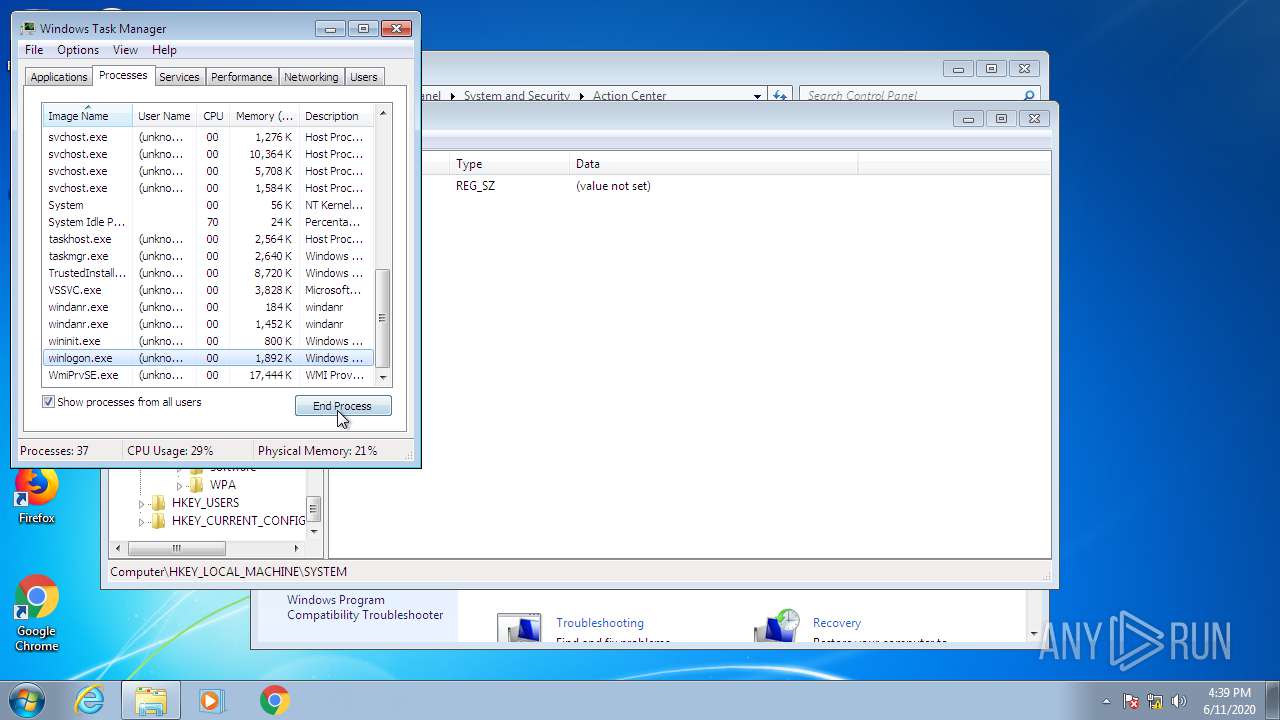
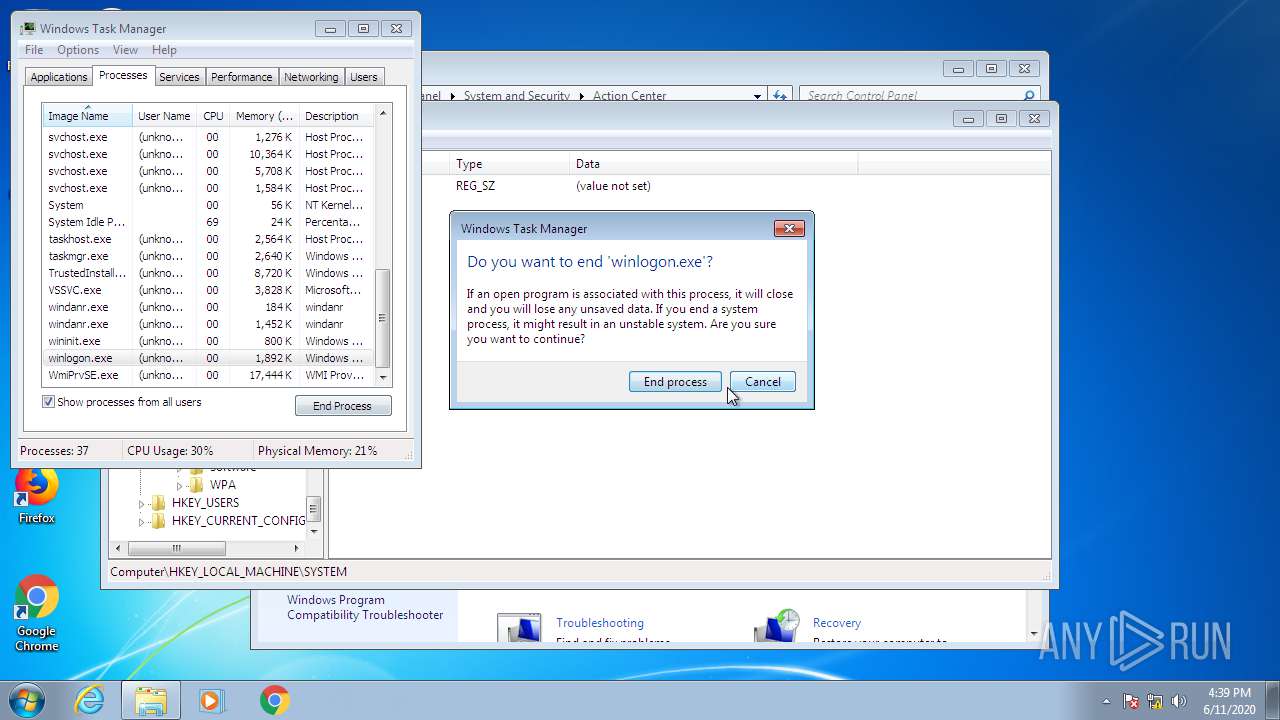
Application launched itself
- ie4uinit.exe (PID: 2708)
- taskmgr.exe (PID: 3124)
- rundll32.exe (PID: 1992)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 2708)
- rundll32.exe (PID: 1992)
Reads Internet Cache Settings
- taskhost.exe (PID: 3384)
Creates files in the program directory
- ie4uinit.exe (PID: 2708)
- chrmstp.exe (PID: 1760)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 2708)
INFO
Application launched itself
- chrome.exe (PID: 2124)
Reads the hosts file
- chrome.exe (PID: 2124)
- chrome.exe (PID: 1976)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2124)
- chrome.exe (PID: 1976)
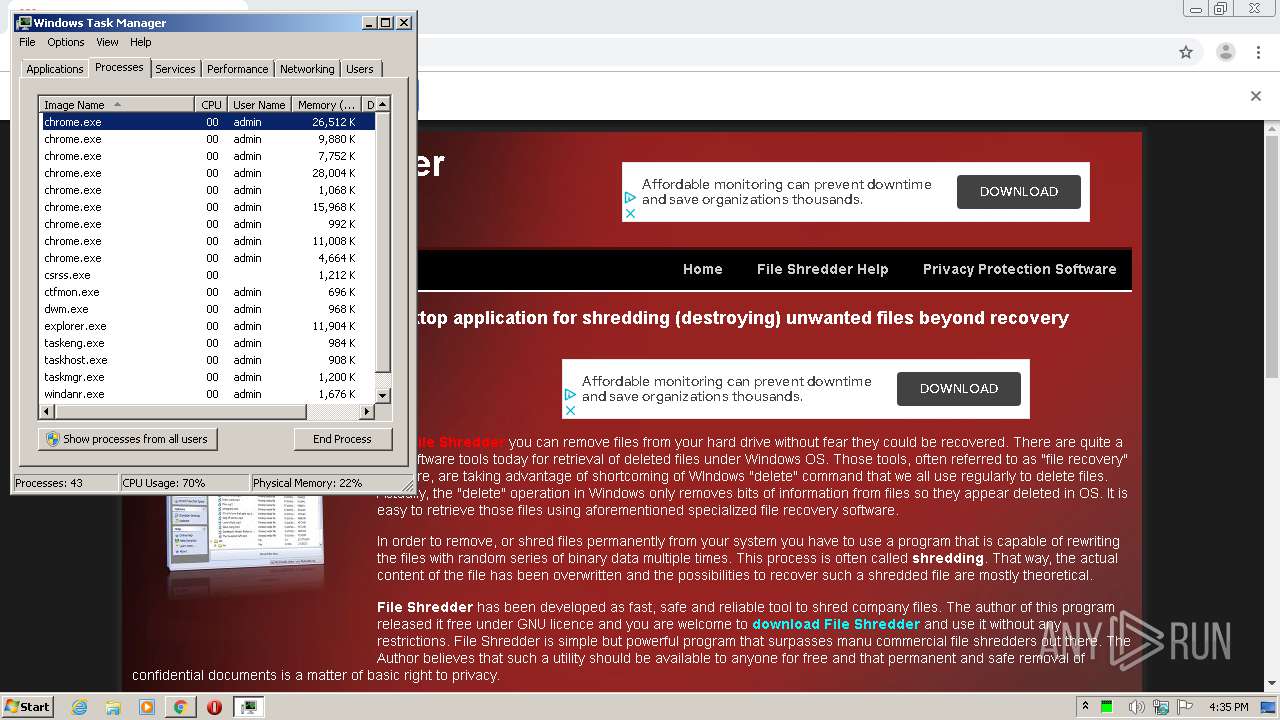
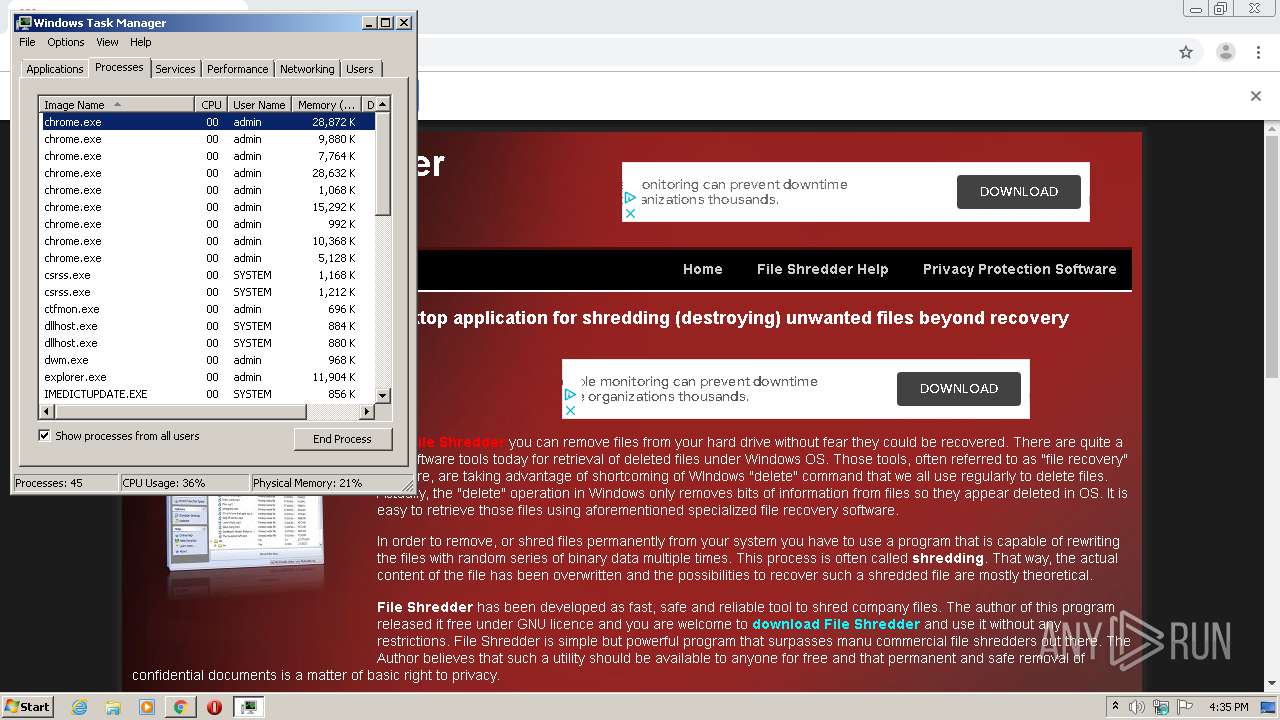
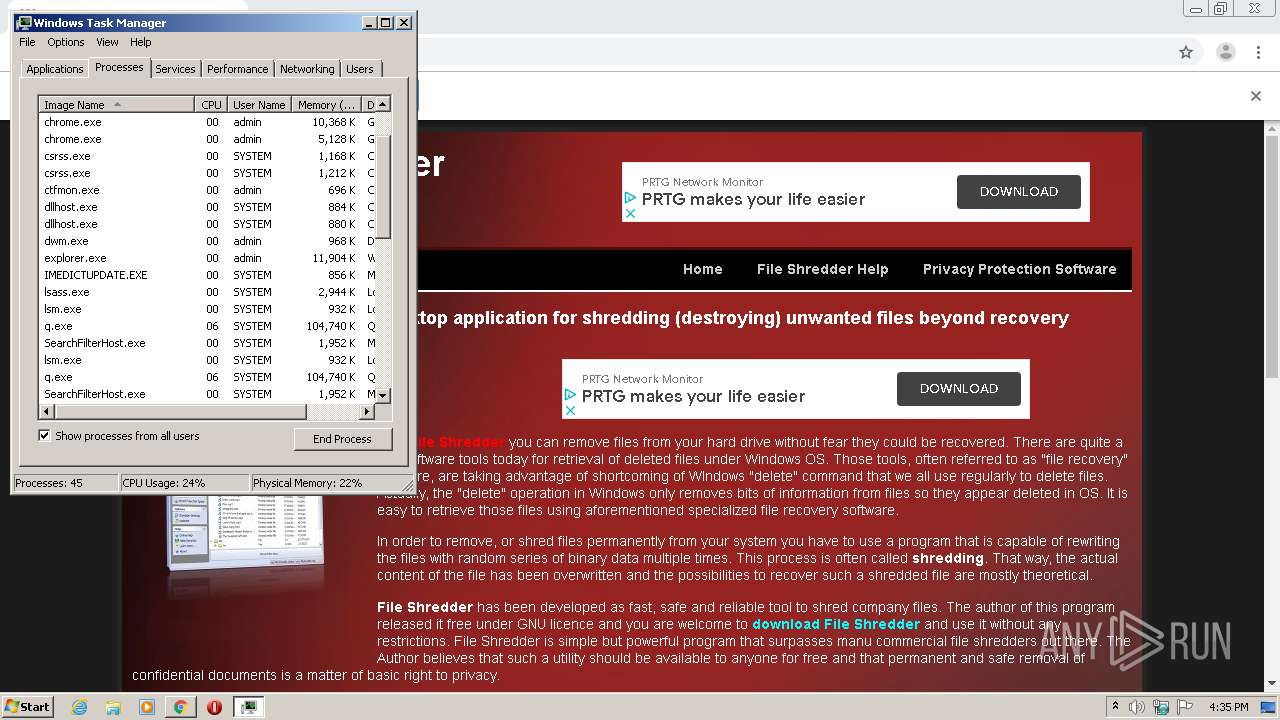
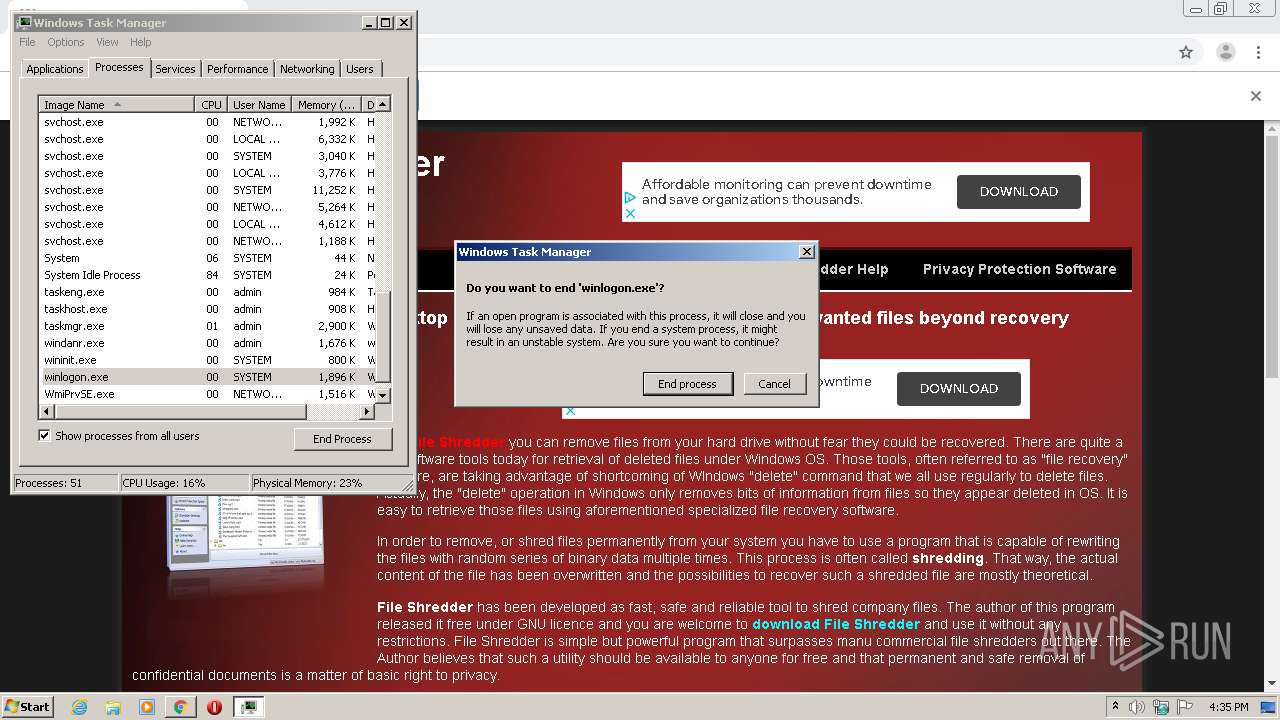
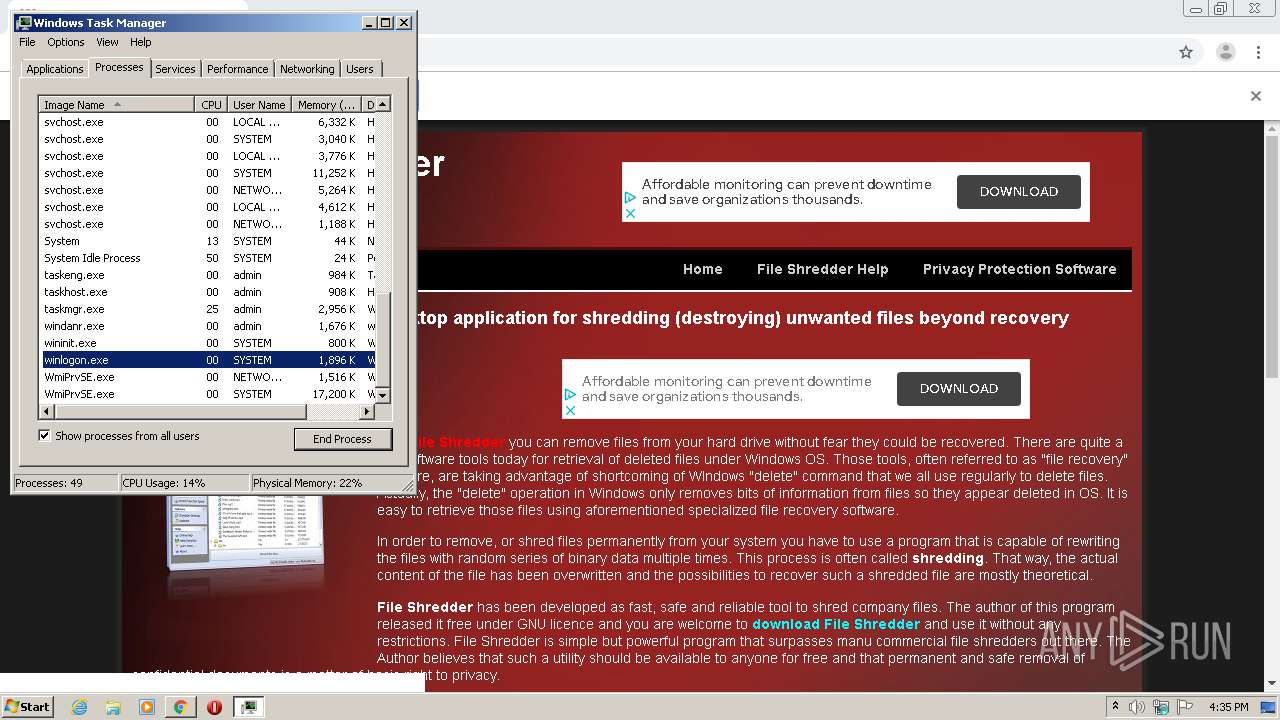
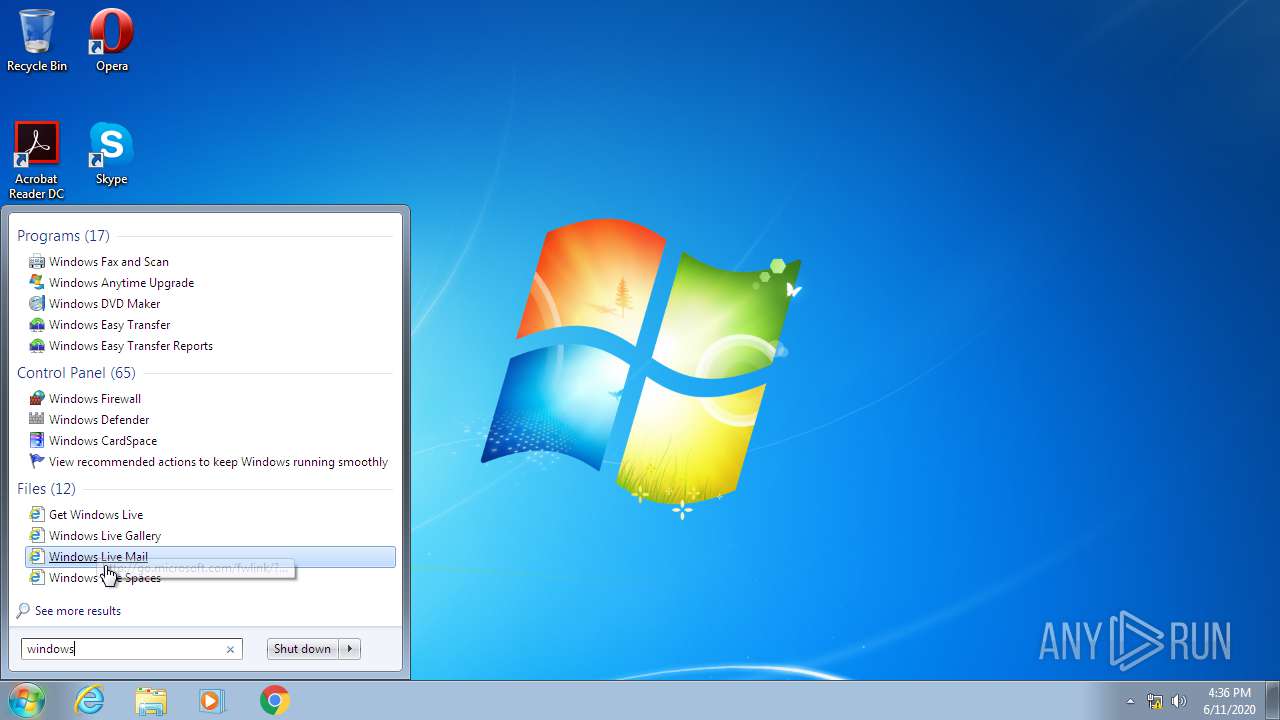
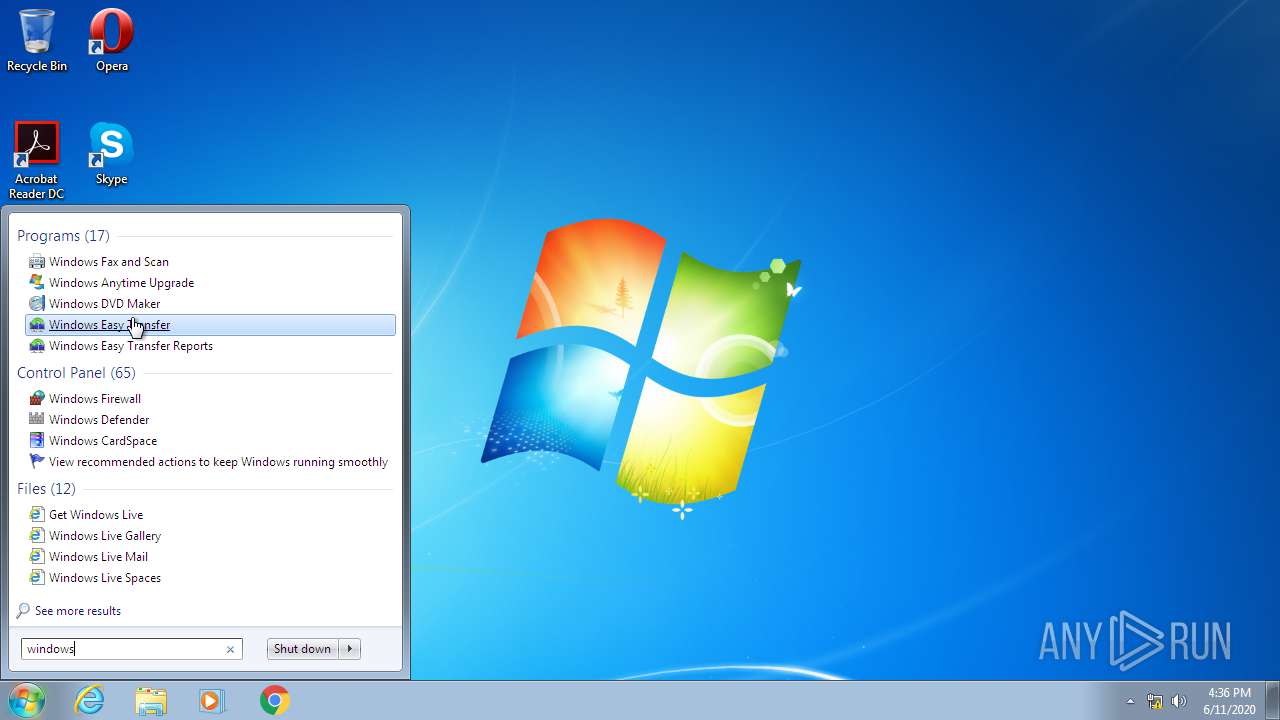
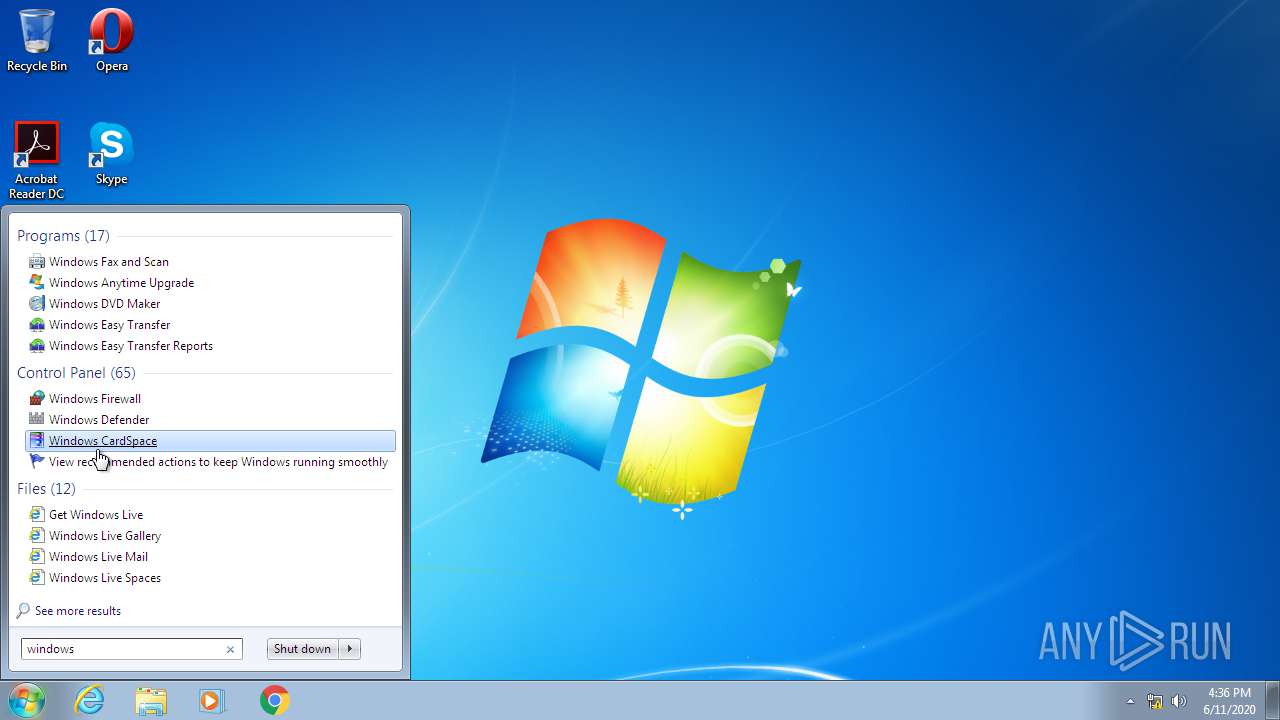
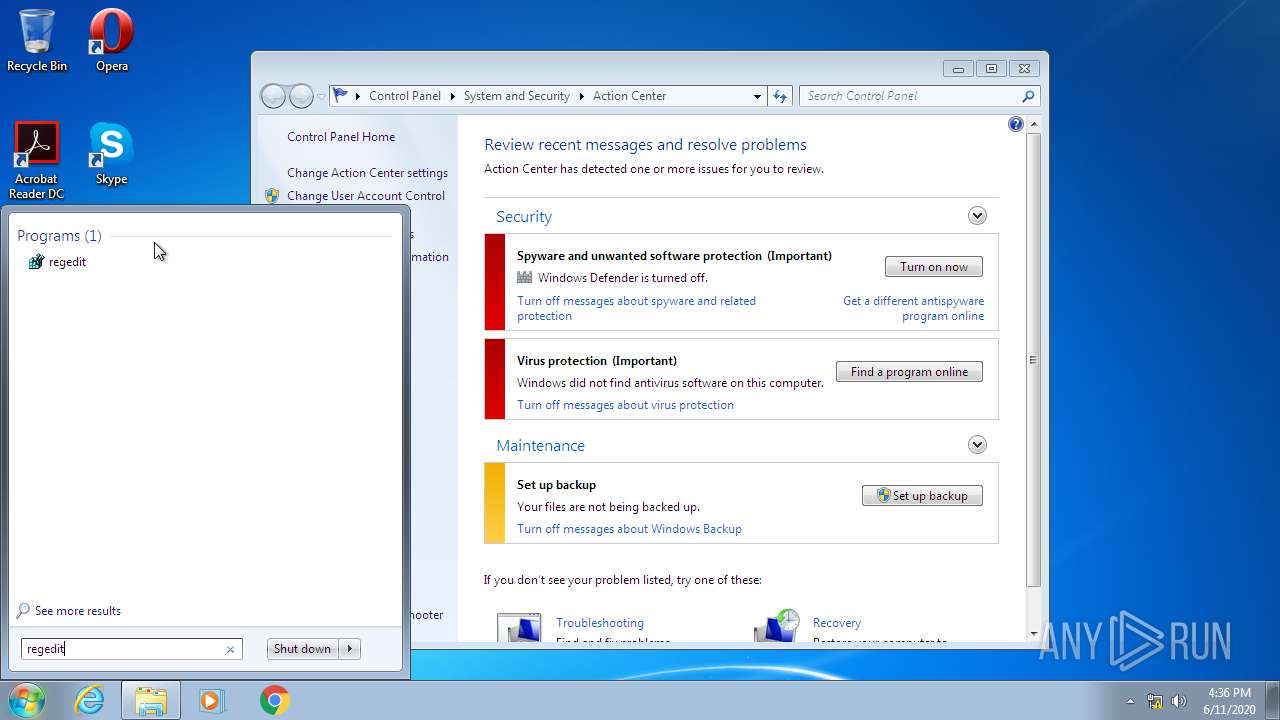
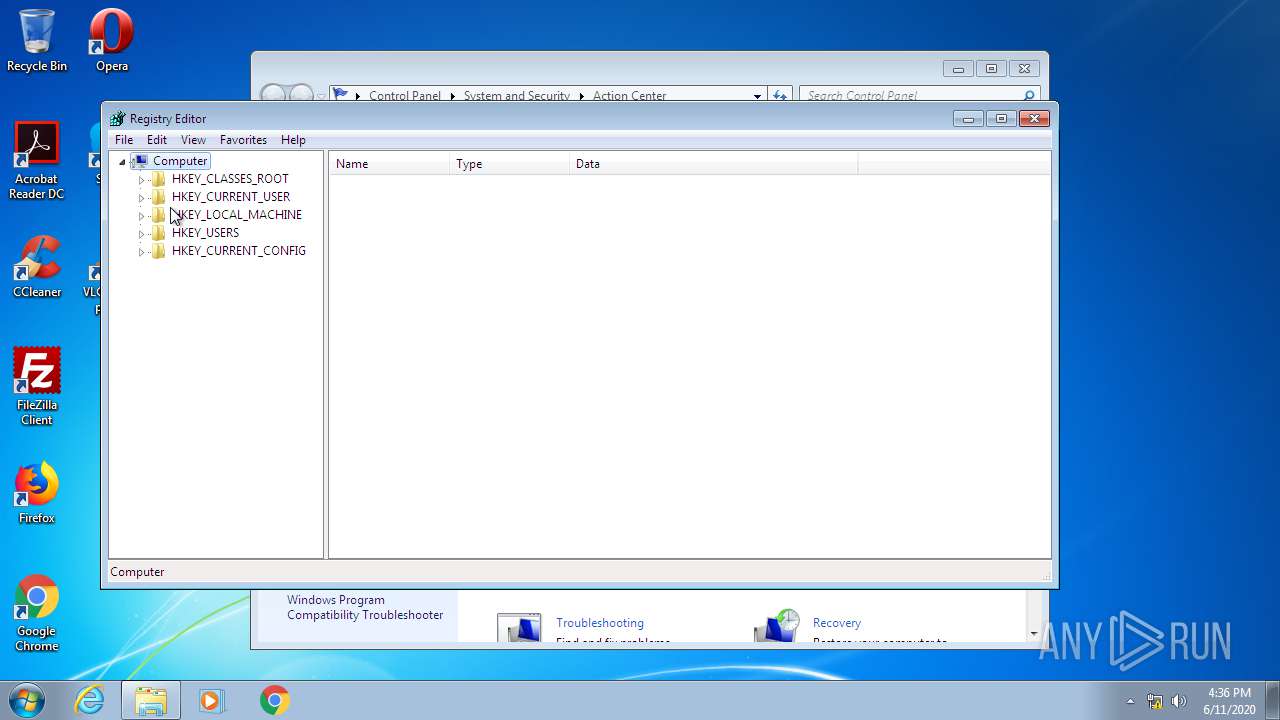
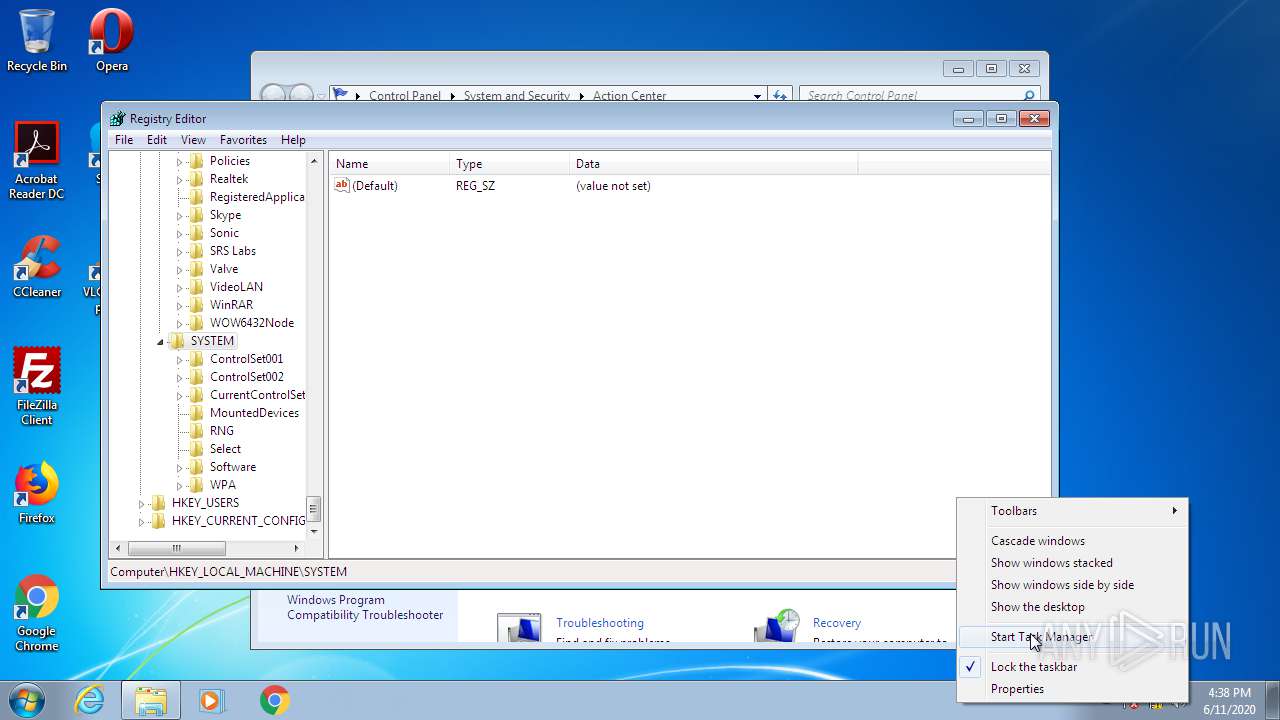
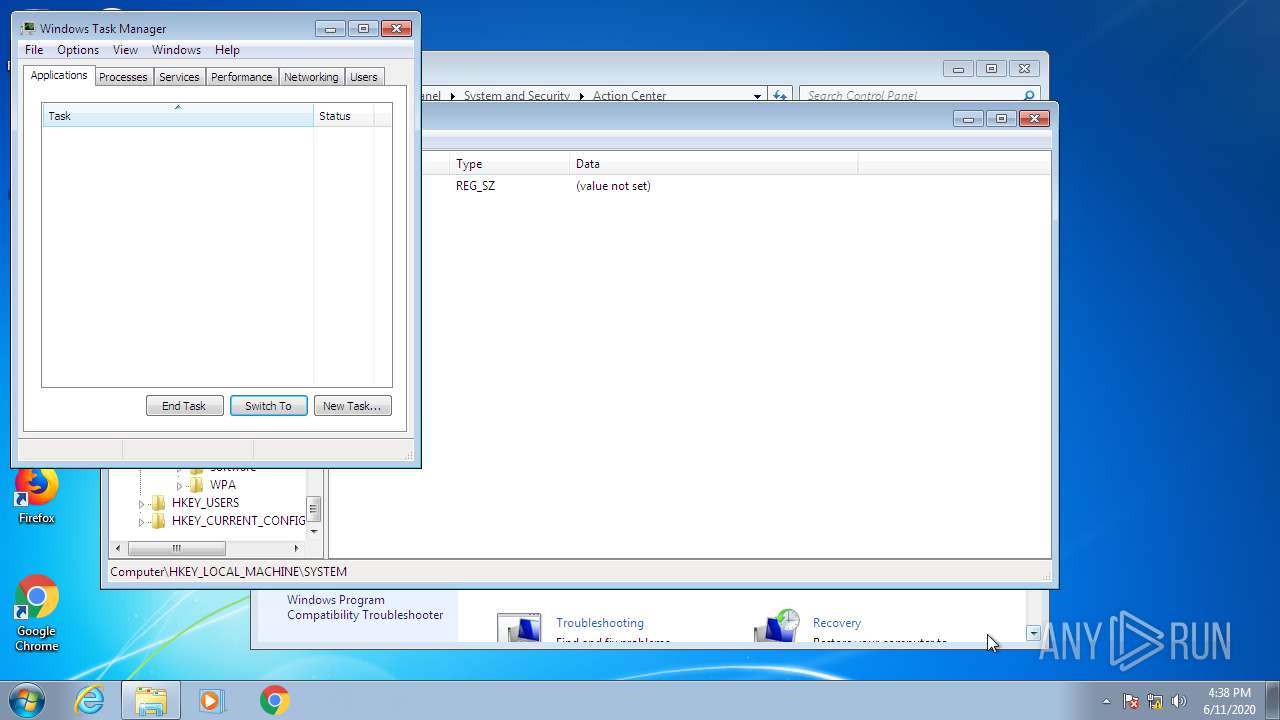
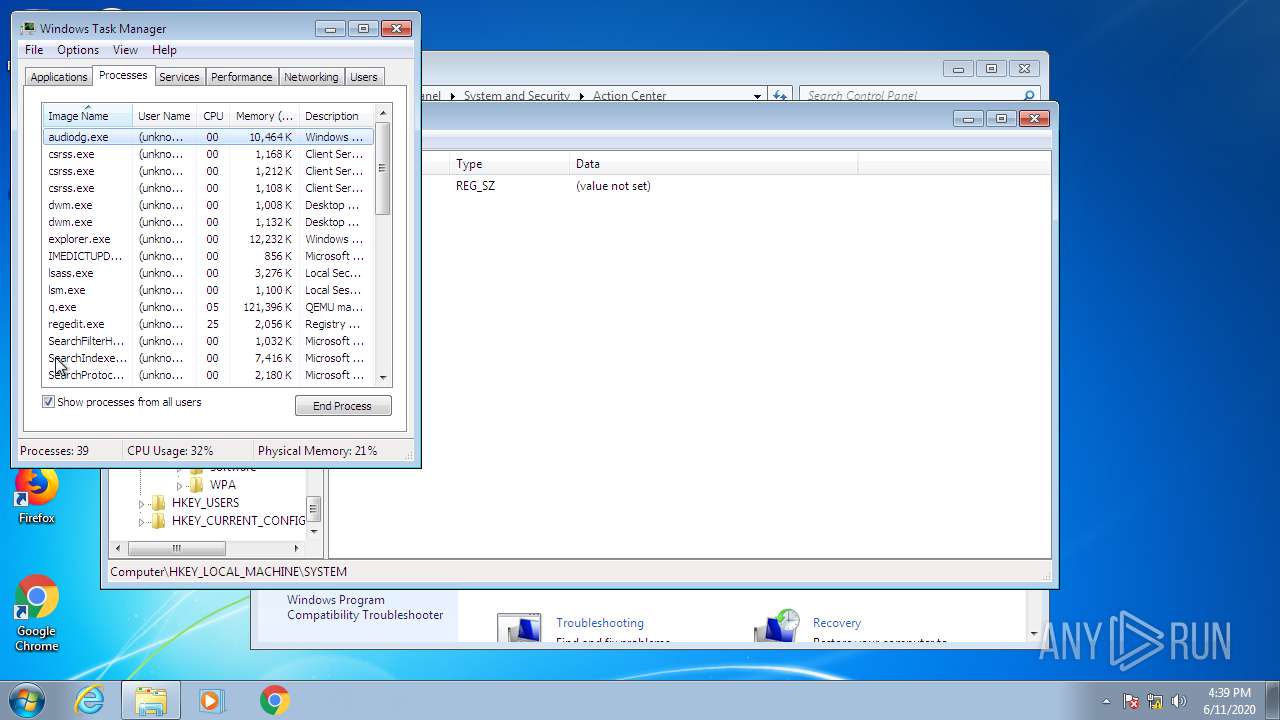
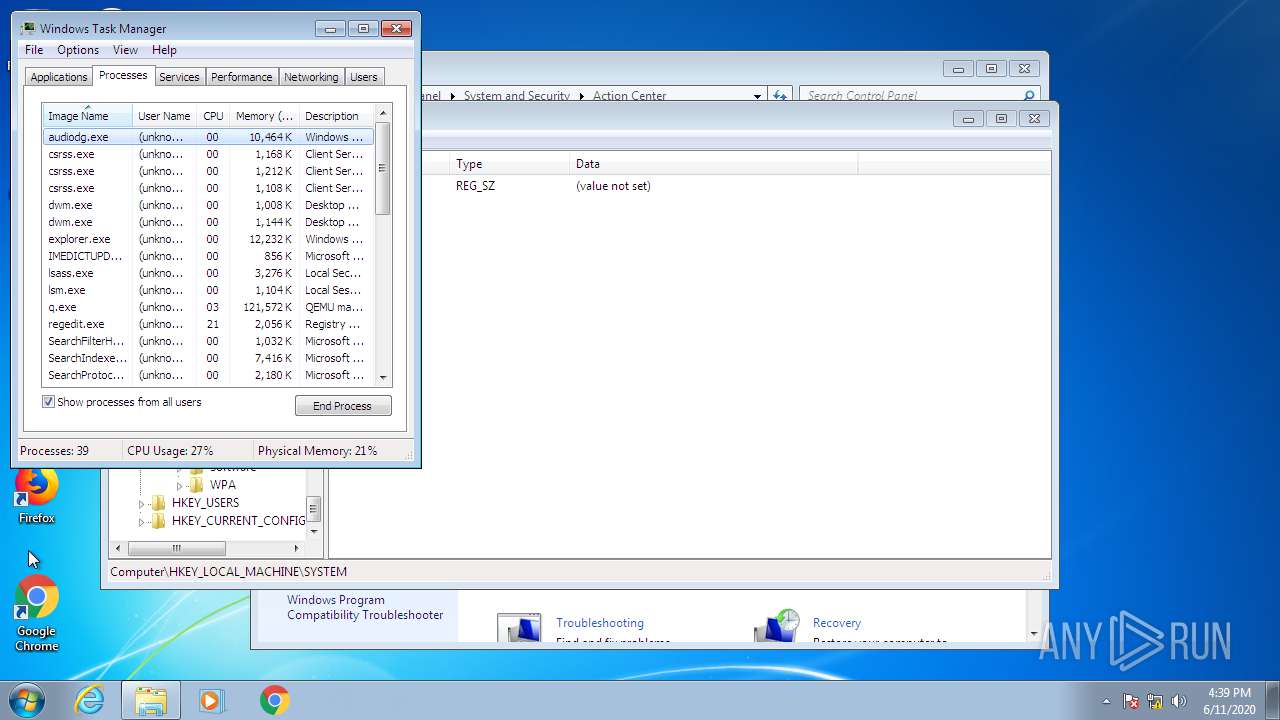
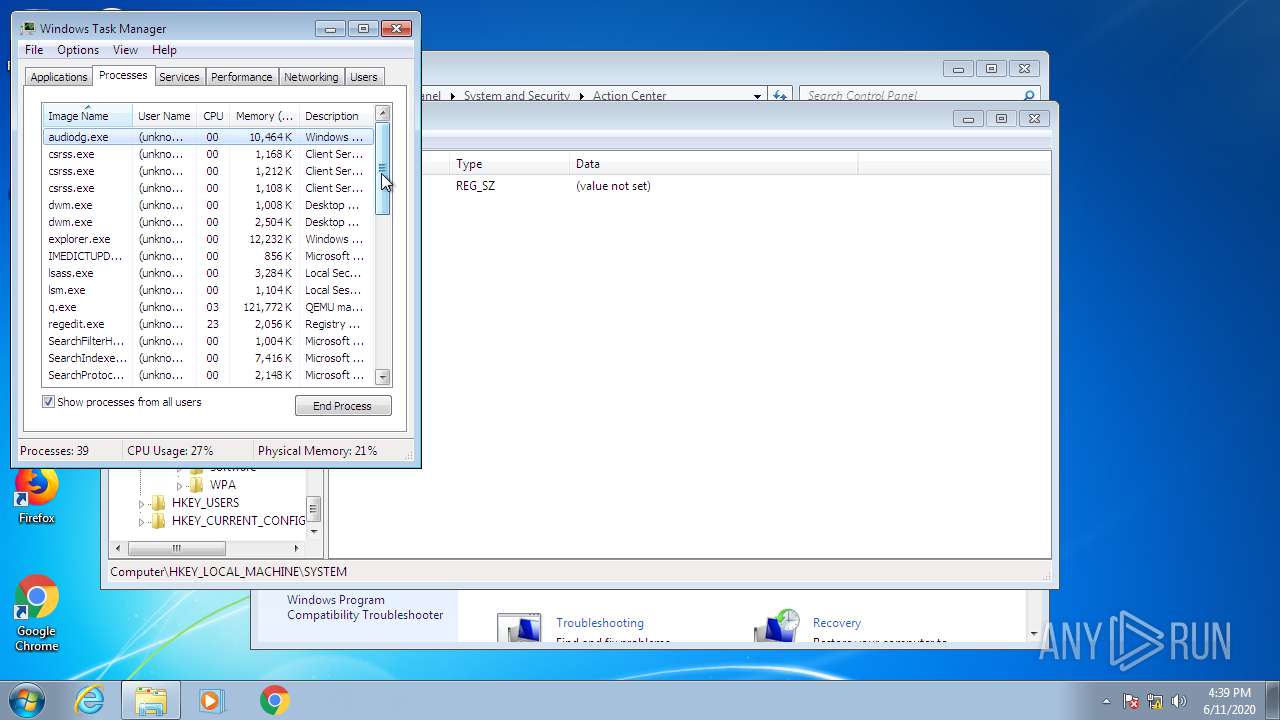
Manual execution by user
- taskmgr.exe (PID: 3124)
- ie4uinit.exe (PID: 2708)
- chrmstp.exe (PID: 1760)
- ie4uinit.exe (PID: 3348)
- verclsid.exe (PID: 2564)
- taskmgr.exe (PID: 2608)
- MSASCui.exe (PID: 2620)
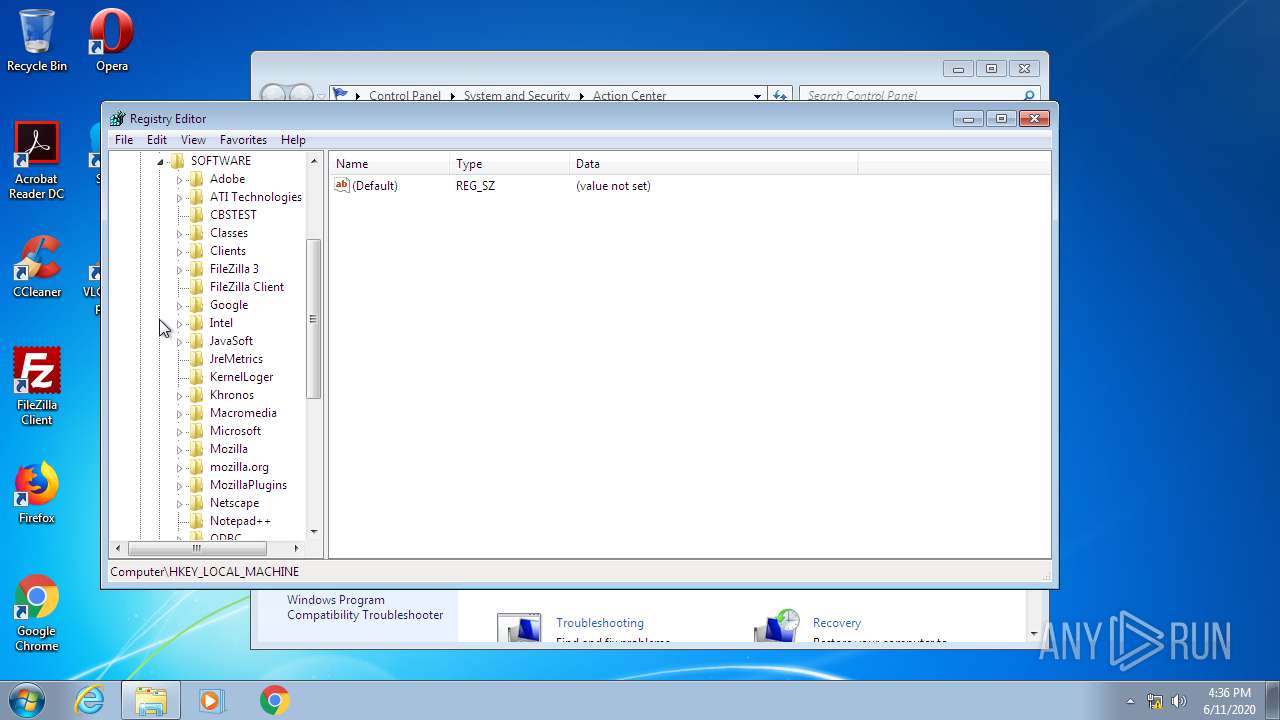
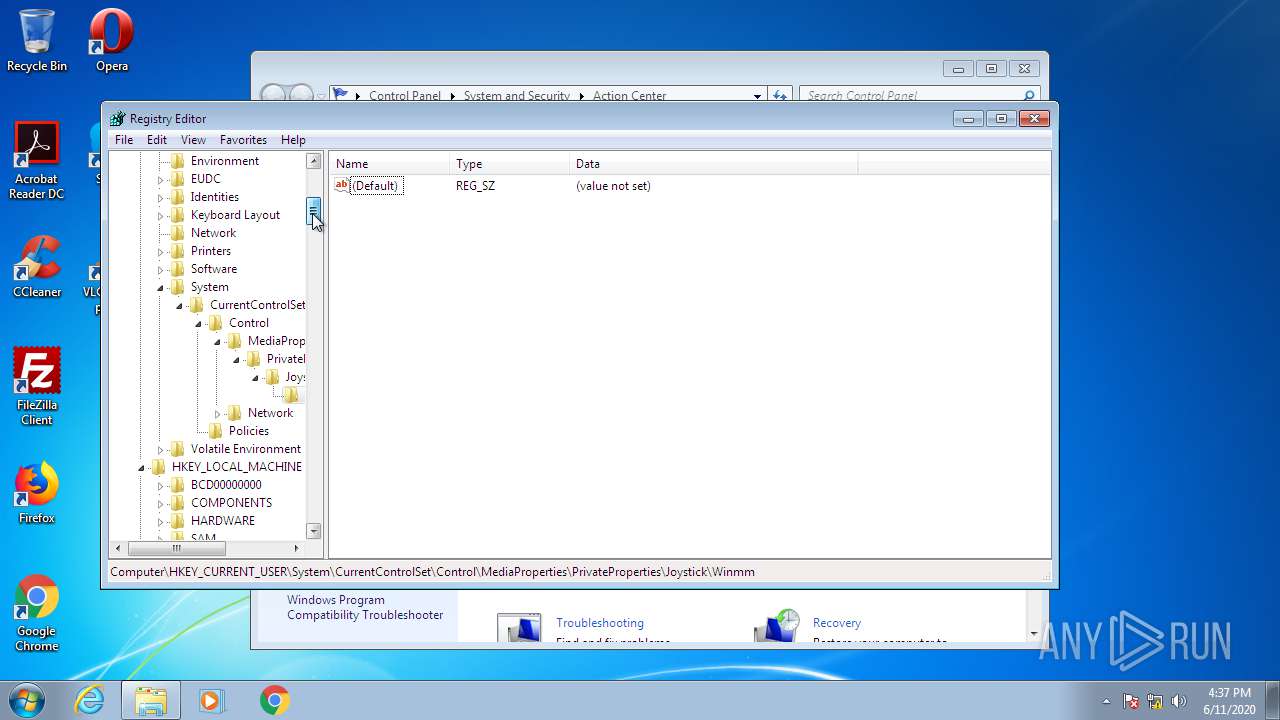
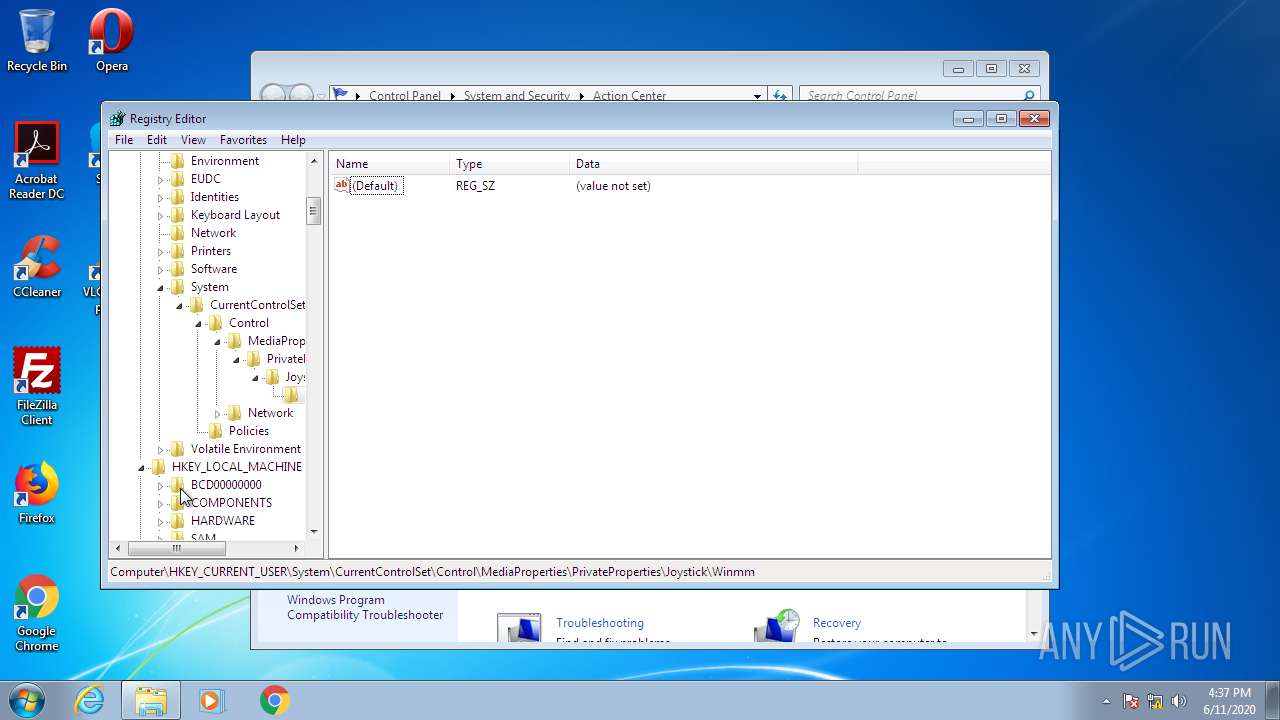
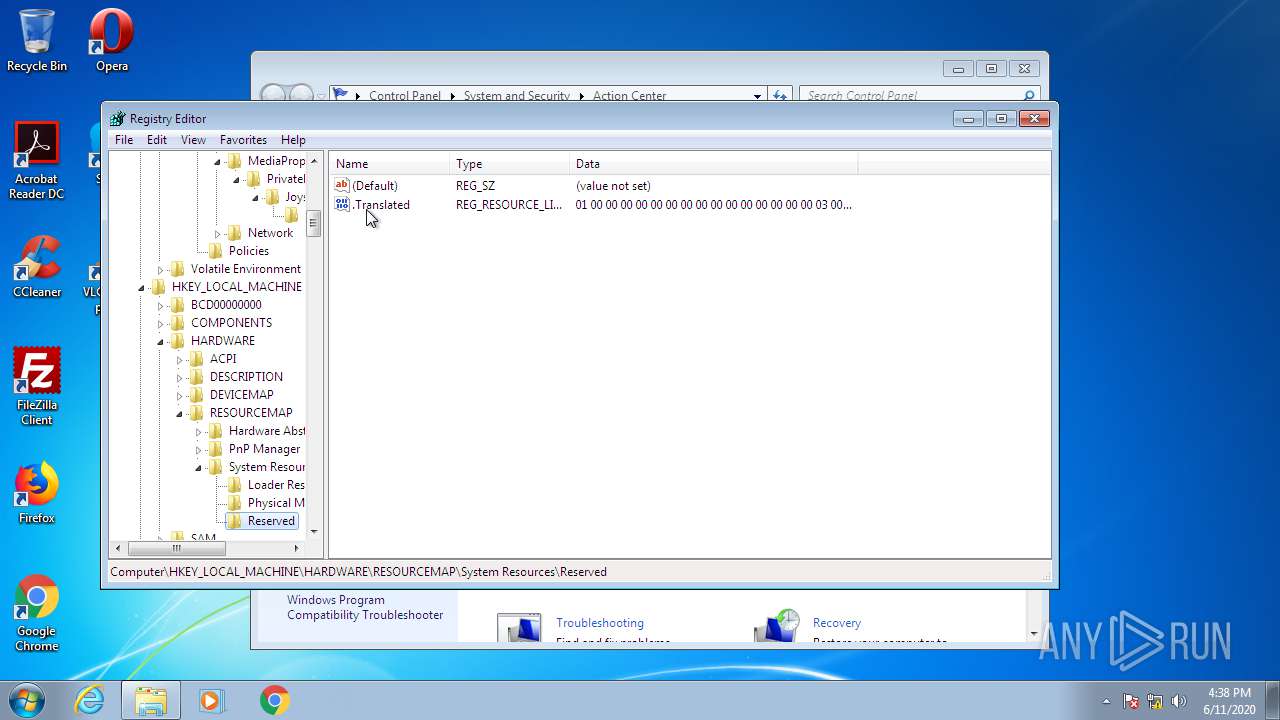
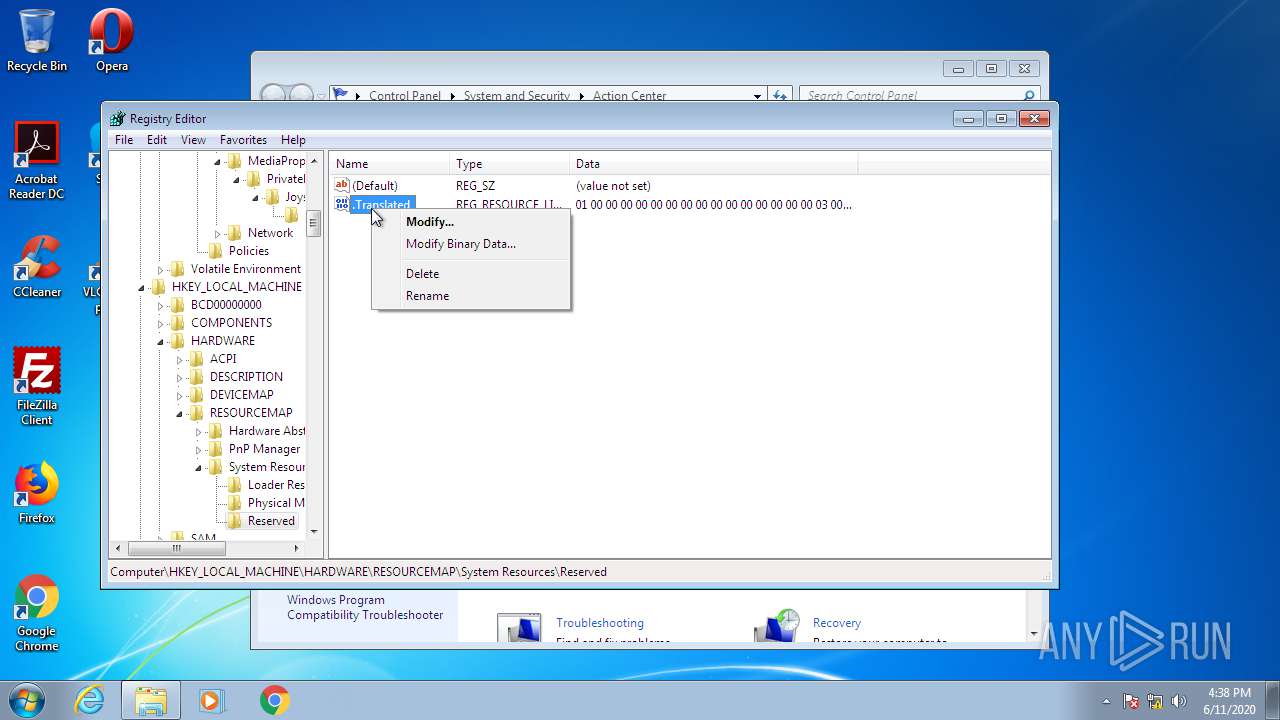
- regedit.exe (PID: 2724)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
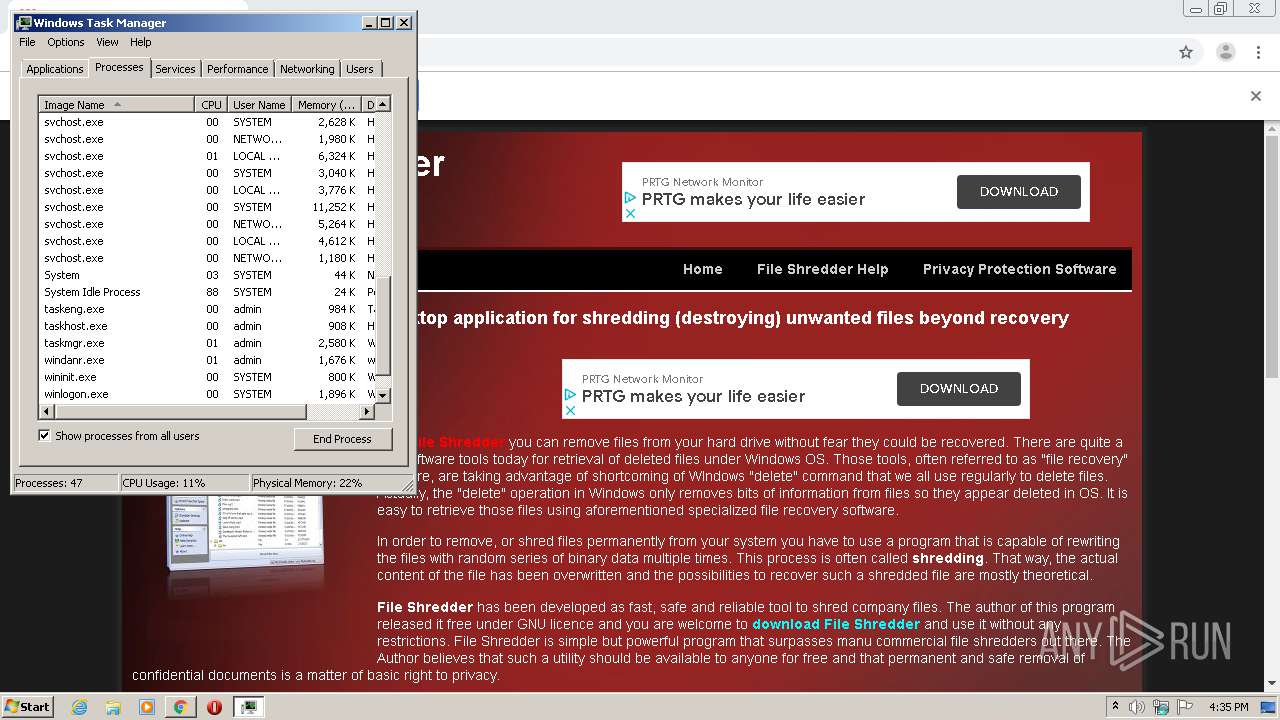
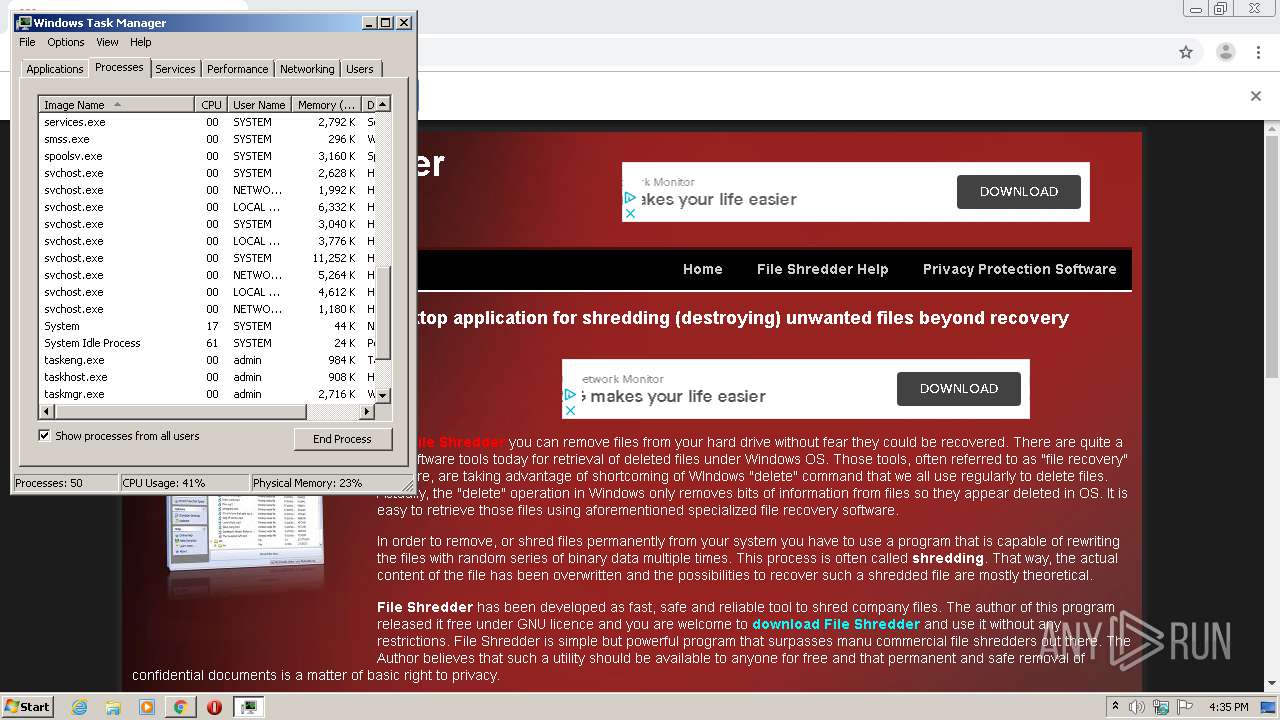
Total processes
457
Monitored processes
44
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | "C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Windows\TEMP\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0xd0,0xd8,0xdc,0xcc,0xe0,0xa42238,0xa42248,0xa42254 | C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8196501587452587329,12207504692816976757,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11483338179714365615 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8196501587452587329,12207504692816976757,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16360763823602382087 --mojo-platform-channel-handle=4516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | C:\Windows\System32\ie4uinit.exe -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,8196501587452587329,12207504692816976757,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12084131923370791760 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe" --configure-user-settings --verbose-logging --system-level | C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8196501587452587329,12207504692816976757,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16221157366602027239 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8196501587452587329,12207504692816976757,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4793015101286442401 --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1992 | C:\Windows\System32\rundll32 C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m | C:\Windows\System32\rundll32.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.fileshredder.org/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
9 564
Read events
587
Write events
501
Delete events
8 476
Modification events
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2124-13236363333793750 |
Value: 259 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
69
Text files
196
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EE24F46-84C.pma | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\80fa83d5-7030-45c7-9aa7-b28367b0e538.tmp | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10736d.TMP | text | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF107570.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
40
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 2.17.46.176:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?2006111536 | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/wsus3setup.cab?2006111536 | US | — | — | whitelisted |
1976 | chrome.exe | GET | 200 | 173.194.150.231:80 | http://r1---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.76.9.72&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1591889656&mv=m&mvi=0&pl=27&shardbypass=yes | US | crx | 823 Kb | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/WuSetupHandler.cab?2006111536 | US | compressed | 32.9 Kb | whitelisted |
— | — | GET | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/WUClient-SelfUpdate-ActiveX~31bf3856ad364e35~x86~~7.6.7600.320.cab?2006111536 | US | compressed | 116 Kb | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/WUClient-SelfUpdate-Aux-TopLevel~31bf3856ad364e35~x86~~7.6.7600.320.cab?2006111536 | US | compressed | 116 Kb | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/WUClient-SelfUpdate-Core-TopLevel~31bf3856ad364e35~x86~~7.6.7600.320.cab?2006111536 | US | compressed | 458 Kb | whitelisted |
— | — | GET | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/WUClient-SelfUpdate-Aux-TopLevel~31bf3856ad364e35~x86~~7.6.7600.320.cab?2006111536 | US | compressed | 458 Kb | whitelisted |
1976 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
1976 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1976 | chrome.exe | 104.31.85.241:443 | www.fileshredder.org | Cloudflare Inc | US | unknown |
1976 | chrome.exe | 216.58.210.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1976 | chrome.exe | 104.111.228.123:443 | www.paypalobjects.com | Akamai International B.V. | NL | unknown |
1976 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1976 | chrome.exe | 172.217.18.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
1976 | chrome.exe | 172.217.16.162:443 | adservice.google.se | Google Inc. | US | whitelisted |
1976 | chrome.exe | 172.217.22.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
1976 | chrome.exe | 172.217.21.194:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
1976 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1976 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.fileshredder.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
adservice.google.se |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
www.googletagservices.com |
| whitelisted |