| File name: | SUPORTE MARCOS.exe |
| Full analysis: | https://app.any.run/tasks/670bb0f1-50d3-49a2-966b-af9fedcd7892 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2021, 18:01:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 190785B2BB664324334C1B5231B5C4B0 |
| SHA1: | 07539ABB2623FE24B9A05E240F675FA2D15268CB |
| SHA256: | 4731517B198414342891553881913565819509086B8154214462788C740B34C9 |
| SSDEEP: | 12288:8YdNctvsfu2LVBfKf057C9lRt3i5olGJsxhzagH:HdNikfu2hBfK8ilRty5olGJsxNH |
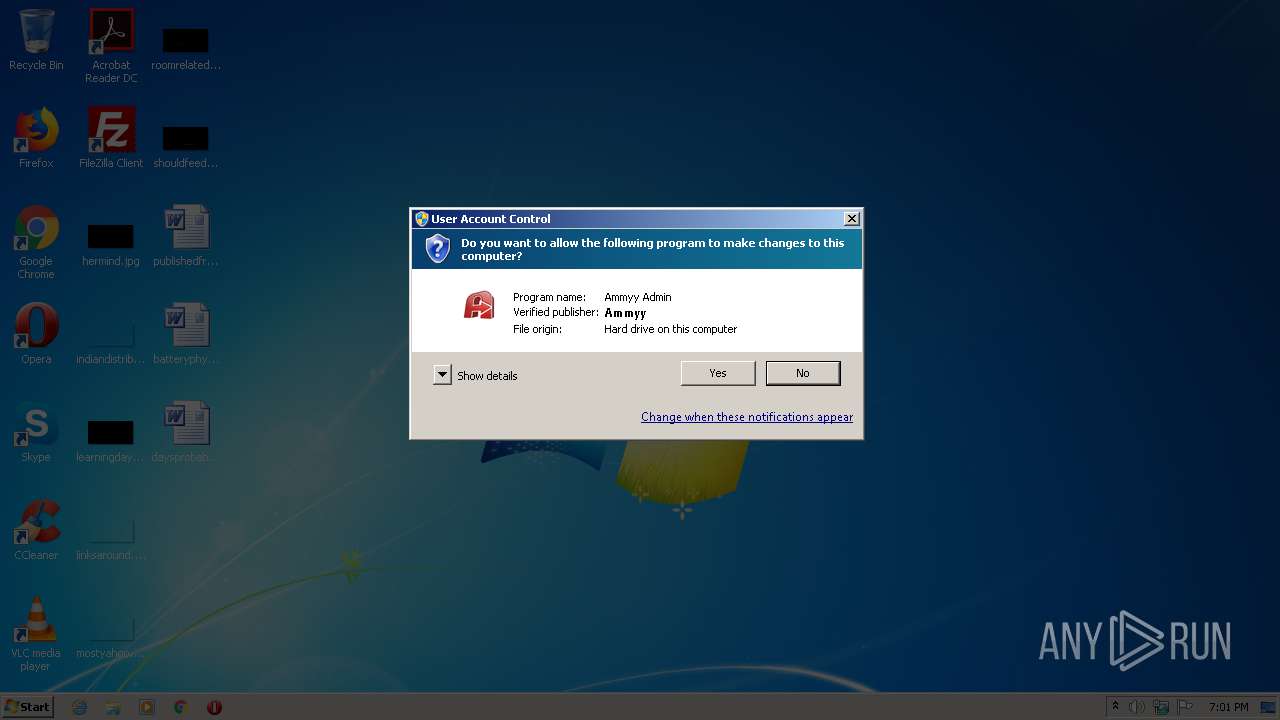
MALICIOUS
Deletes the SafeBoot registry key
- SUPORTE MARCOS.exe (PID: 2576)
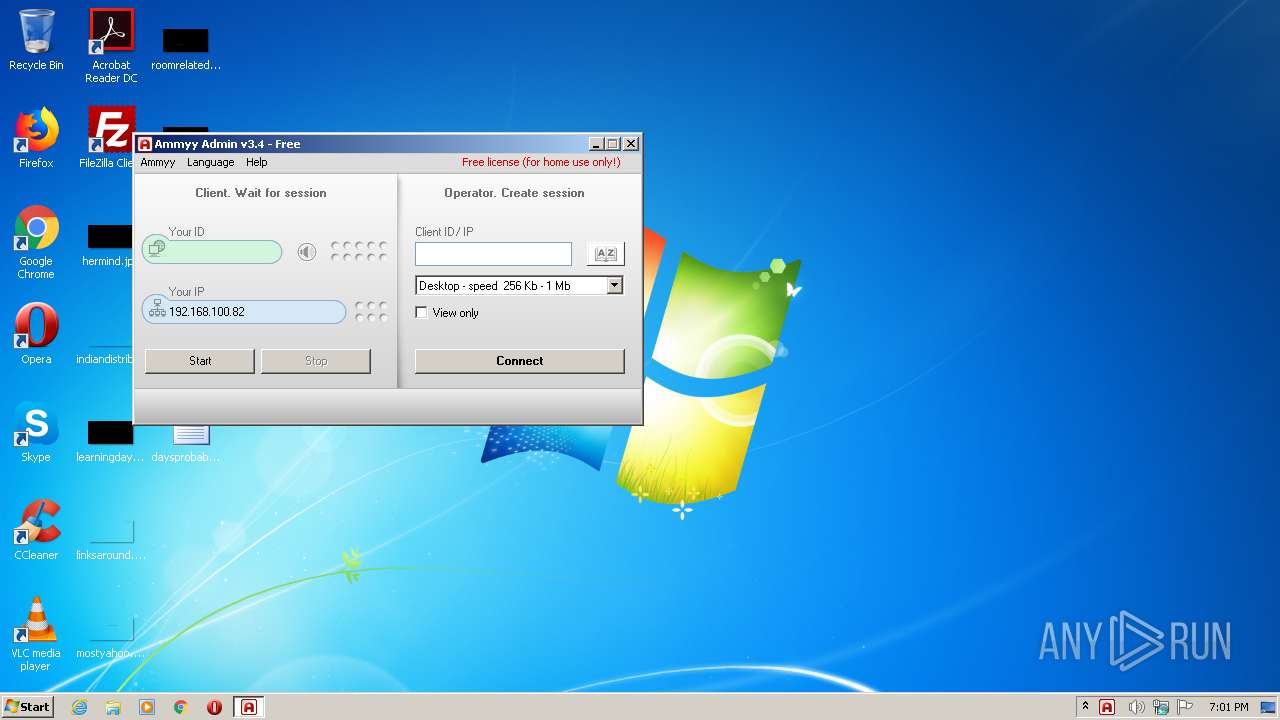
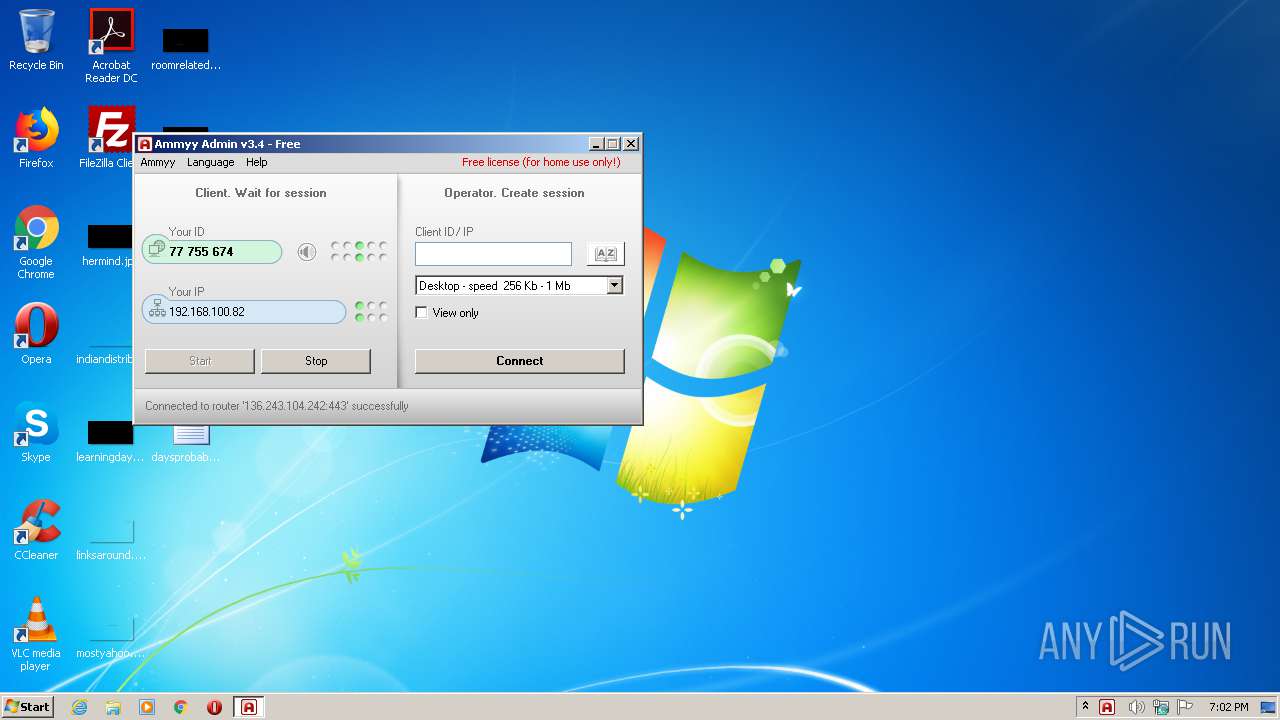
AMMYY was detected
- SUPORTE MARCOS.exe (PID: 2180)
Connects to CnC server
- SUPORTE MARCOS.exe (PID: 2180)
SUSPICIOUS
Application launched itself
- SUPORTE MARCOS.exe (PID: 1960)
- SUPORTE MARCOS.exe (PID: 2900)
Creates files in the program directory
- SUPORTE MARCOS.exe (PID: 2900)
Executed as Windows Service
- SUPORTE MARCOS.exe (PID: 1960)
Checks for external IP
- SUPORTE MARCOS.exe (PID: 2180)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| SpecialBuild: | - |
|---|---|
| ProductVersion: | 3.4 |
| ProductName: | Ammyy Admin |
| PrivateBuild: | - |
| OriginalFileName: | - |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Ammyy Admin |
| FileVersion: | 3.4 |
| FileDescription: | Ammyy Admin |
| CompanyName: | Ammyy LLC |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.4.0.0 |
| FileVersionNumber: | 3.4.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x79afe |
| UninitializedDataSize: | - |
| InitializedDataSize: | 241664 |
| CodeSize: | 520192 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2014:01:14 21:25:26+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jan-2014 20:25:26 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.4 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.4 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-Jan-2014 20:25:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0007EE5A | 0x0007F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6938 |
.rdata | 0x00080000 | 0x0001089A | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53052 |
.data | 0x00091000 | 0x0001EDE8 | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.95173 |
.rsrc | 0x000B0000 | 0x0000AE68 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.5768 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.841 | 637 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.72434 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.13946 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 1.65331 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 1.19249 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 1.34234 | 308 | UNKNOWN | English - United States | RT_CURSOR |
100 | 3.59063 | 366 | UNKNOWN | UNKNOWN | RT_DIALOG |
103 | 5.72337 | 1768 | UNKNOWN | Russian - Russia | RT_BITMAP |
104 | 3.07153 | 174 | UNKNOWN | Russian - Russia | RT_DIALOG |
105 | 5.94736 | 1768 | UNKNOWN | Russian - Russia | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
DSOUND.dll |
GDI32.dll |
KERNEL32.dll |
MSVCP60.dll |
MSVCRT.dll |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
43
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1960 | "C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe" -service -lunch | C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.4 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe" -elevated | C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe | SUPORTE MARCOS.exe | ||||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.4 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe" -elevated | C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe | SUPORTE MARCOS.exe | ||||||||||||
User: admin Company: Ammyy LLC Integrity Level: HIGH Description: Ammyy Admin Exit code: 0 Version: 3.4 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe" | C:\Users\admin\AppData\Local\Temp\SUPORTE MARCOS.exe | — | explorer.exe | |||||||||||
User: admin Company: Ammyy LLC Integrity Level: MEDIUM Description: Ammyy Admin Exit code: 0 Version: 3.4 Modules
| |||||||||||||||
Total events
370
Read events
354
Write events
15
Delete events
1
Modification events
| (PID) Process: | (2900) SUPORTE MARCOS.exe | Key: | HKEY_CURRENT_USER\Software\Ammyy\Admin |
| Operation: | write | Name: | hr |
Value: 537D56736631FC7019EB7660B652 | |||
| (PID) Process: | (2900) SUPORTE MARCOS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr |
Value: 537D56736631FC7019EB7660B652 | |||
| (PID) Process: | (2900) SUPORTE MARCOS.exe | Key: | HKEY_CURRENT_USER\Software\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 95FC12B912B89140A7A4A884E2EDD7428650328FCD52E950FFEA7C001F15BC7AA8853867AFEF445A7C35621E8A992DBCB65EEF2A951ED12E5CA2C6F9 | |||
| (PID) Process: | (2900) SUPORTE MARCOS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 95FC12B912B89140A7A4A884E2EDD7428650328FCD52E950FFEA7C001F15BC7AA8853867AFEF445A7C35621E8A992DBCB65EEF2A951ED12E5CA2C6F9 | |||
| (PID) Process: | (2900) SUPORTE MARCOS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2900) SUPORTE MARCOS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2576) SUPORTE MARCOS.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_A10 |
| Operation: | write | Name: | (default) |
Value: Service | |||
| (PID) Process: | (2576) SUPORTE MARCOS.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_A10 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2180) SUPORTE MARCOS.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2180) SUPORTE MARCOS.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2180 | SUPORTE MARCOS.exe | C:\ProgramData\AMMYY\hr | binary | |
MD5:— | SHA256:— | |||
| 2900 | SUPORTE MARCOS.exe | C:\ProgramData\AMMYY\hr | binary | |
MD5:— | SHA256:— | |||
| 2900 | SUPORTE MARCOS.exe | C:\ProgramData\AMMYY\hr3 | flc | |
MD5:— | SHA256:— | |||
| 2180 | SUPORTE MARCOS.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:— | SHA256:— | |||
| 2900 | SUPORTE MARCOS.exe | C:\ProgramData\AMMYY\settings3.bin | binary | |
MD5:4CB889E527B0D0781A17F6C2DD968129 | SHA256:2658CD46DD49335E739CAFA31FF2EC63F3315B65ECC171A0F7612713D3AC702B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2180 | SUPORTE MARCOS.exe | 188.42.129.148:80 | rl.ammyy.com | Servers.com, Inc. | NL | malicious |
— | — | 136.243.104.242:443 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rl.ammyy.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2180 | SUPORTE MARCOS.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
2 ETPRO signatures available at the full report