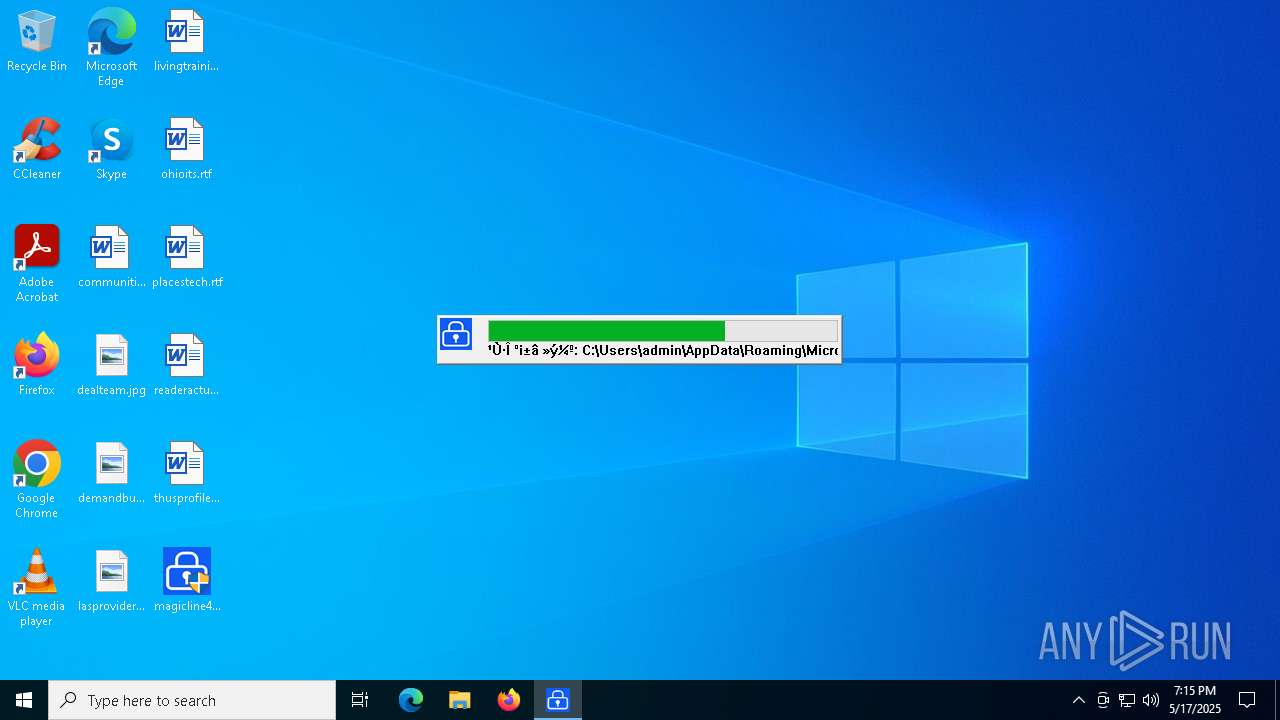
| File name: | magicline4nx_setup1.exe |
| Full analysis: | https://app.any.run/tasks/6b52dfb2-9097-4f37-8a4d-f13cbd272070 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 19:15:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | ED13F3278BBE177CF2F1D0B446ABD2C0 |
| SHA1: | A6D68DBE22BE66E6C3891DD9CC4A803B33AB34BE |
| SHA256: | 47314D936942E3BB71DD54AF9B3795D482BFAFC8AD5370F4B3EBD6A9FF9AC7A2 |
| SSDEEP: | 98304:OVFdn1DqYRtkXNufDYvAL2MlRws61Damcq2+LB/Z93t3ZV7or0+wPc35kRCCOf52:YV+7miVd4e5NGii8Trm1MHS7QjwW |
MALICIOUS
Accesses environment variables (SCRIPT)
- cscript.exe (PID: 5392)
- cscript.exe (PID: 4896)
Gets %appdata% folder path (SCRIPT)
- cscript.exe (PID: 5392)
- cscript.exe (PID: 4896)
Executing a file with an untrusted certificate
- MagicLine4NXServices.exe (PID: 7528)
- MagicLine4NXServices.exe (PID: 728)
Changes the autorun value in the registry
- magicline4nx_setup1.exe (PID: 7976)
SUSPICIOUS
Reads security settings of Internet Explorer
- magicline4nx_setup1.exe (PID: 7976)
Malware-specific behavior (creating "System.dll" in Temp)
- magicline4nx_setup1.exe (PID: 7976)
Stops a currently running service
- sc.exe (PID: 8184)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8024)
- cmd.exe (PID: 5364)
Windows service management via SC.EXE
- sc.exe (PID: 2320)
- sc.exe (PID: 7824)
Starts CMD.EXE for commands execution
- magicline4nx_setup1.exe (PID: 7976)
Process drops legitimate windows executable
- magicline4nx_setup1.exe (PID: 7976)
The process creates files with name similar to system file names
- magicline4nx_setup1.exe (PID: 7976)
Executable content was dropped or overwritten
- magicline4nx_setup1.exe (PID: 7976)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 5392)
- cscript.exe (PID: 4896)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 5392)
- cscript.exe (PID: 4896)
Runs shell command (SCRIPT)
- cscript.exe (PID: 5392)
- cscript.exe (PID: 4896)
Creates a software uninstall entry
- magicline4nx_setup1.exe (PID: 7976)
Adds/modifies Windows certificates
- certmgr.exe (PID: 7552)
Reads the BIOS version
- MagicLine4NX.exe (PID: 7476)
- MagicLine4NXServices.exe (PID: 7528)
- MagicLine4NXServices.exe (PID: 728)
- MagicLine4NX.exe (PID: 720)
The process executes VB scripts
- magicline4nx_setup1.exe (PID: 7976)
Executes as Windows Service
- MagicLine4NXServices.exe (PID: 728)
There is functionality for taking screenshot (YARA)
- MagicLine4NX.exe (PID: 7476)
INFO
Reads the computer name
- magicline4nx_setup1.exe (PID: 7976)
- certutil.exe (PID: 4408)
- certutil.exe (PID: 6712)
- certutil.exe (PID: 6040)
- certutil.exe (PID: 4424)
- MagicLine4NX.exe (PID: 7476)
- MagicLine4NXServices.exe (PID: 7528)
- MagicLine4NXServices.exe (PID: 728)
The sample compiled with korean language support
- magicline4nx_setup1.exe (PID: 7976)
Checks supported languages
- magicline4nx_setup1.exe (PID: 7976)
- certutil.exe (PID: 4408)
- certutil.exe (PID: 6712)
- certmgr.exe (PID: 7552)
- certutil.exe (PID: 4424)
- certutil.exe (PID: 6040)
- MagicLine4NX.exe (PID: 7476)
- MagicLine4NXServices.exe (PID: 7528)
- MagicLine4NXServices.exe (PID: 728)
- MagicLine4NX.exe (PID: 720)
Create files in a temporary directory
- magicline4nx_setup1.exe (PID: 7976)
Process checks computer location settings
- magicline4nx_setup1.exe (PID: 7976)
Creates files or folders in the user directory
- magicline4nx_setup1.exe (PID: 7976)
- certutil.exe (PID: 6040)
- certutil.exe (PID: 4424)
Reads security settings of Internet Explorer
- cscript.exe (PID: 5392)
- cscript.exe (PID: 4896)
The sample compiled with english language support
- magicline4nx_setup1.exe (PID: 7976)
Creates files in the program directory
- magicline4nx_setup1.exe (PID: 7976)
Manual execution by a user
- MagicLine4NX.exe (PID: 7476)
- MagicLine4NX.exe (PID: 720)
Themida protector has been detected
- MagicLine4NX.exe (PID: 7476)
- MagicLine4NXServices.exe (PID: 728)
Auto-launch of the file from Registry key
- magicline4nx_setup1.exe (PID: 7976)
Checks proxy server information
- slui.exe (PID: 7180)
Reads the software policy settings
- slui.exe (PID: 7180)
Reads the machine GUID from the registry
- MagicLine4NX.exe (PID: 7476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:26:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x310f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.32 |
| ProductVersionNumber: | 1.0.0.32 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| CompanyName: | Dreamsecurity, Inc. |
| FileDescription: | MagicLine4NX |
| FileVersion: | 1.0.0.32 |
| LegalCopyright: | Copyright (C) 2016 Dreamsecurity Co., Ltd. All rights reserved. |
| ProductName: | MagicLine4NX |
| ProductVersion: | MagicLine4Web |
Total processes
159
Monitored processes
34
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\DreamSecurity\MagicLine4NX\MagicLine4NX.exe" | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\MagicLine4NX.exe | — | explorer.exe | |||||||||||
User: admin Company: Dreamsecurity Integrity Level: MEDIUM Description: MagicLine4NX Exit code: 0 Version: 1.0.0.32 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\DreamSecurity\MagicLine4NX\MagicLine4NXServices.exe" | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\MagicLine4NXServices.exe | services.exe | ||||||||||||
User: SYSTEM Company: Dreamsecurity Integrity Level: SYSTEM Description: MagicLine4NXServices Version: 1.0.0.1 Modules
| |||||||||||||||
| 1676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | sc delete MagicLine4NXSVC | C:\Windows\SysWOW64\sc.exe | — | magicline4nx_setup1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | "C:\Program Files (x86)\DreamSecurity\MagicLine4NX\cert\certutil.exe" -L -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release" -n "Dreamsecurity ROOT CA" | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\cert\certutil.exe | — | cscript.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
| 4424 | "C:\Program Files (x86)\DreamSecurity\MagicLine4NX\cert\certutil.exe" -A -n "Dreamsecurity ROOT CA" -i "C:\Program Files (x86)\DreamSecurity\MagicLine4NX\cert\dreamsecurity-rootca.der" -t "CT,c,C" -d "C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\i17fj4h8.default" | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\cert\certutil.exe | — | cscript.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4756 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 442
Read events
7 420
Write events
18
Delete events
4
Modification events
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | NTSMagicLineNP |
Value: | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | MagicLine4NX |
Value: | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | DisplayName |
Value: MagicLine4NX | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.32 | |||
| (PID) Process: | (7552) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 0BAFEC00CC085C92F94FD1F2DECA2374C72EFFDA |
Value: | |||
| (PID) Process: | (7552) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\0BAFEC00CC085C92F94FD1F2DECA2374C72EFFDA |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000000BAFEC00CC085C92F94FD1F2DECA2374C72EFFDA200000000100000068030000308203643082024CA003020102020101300D06092A864886F70D01010B0500304A310B3009060355040613024B52311B3019060355040A1312447265616D736563757269747920496E632E311E301C06035504031315447265616D736563757269747920524F4F54204341301E170D3135303930333034313133345A170D3335303832393034313133345A304A310B3009060355040613024B52311B3019060355040A1312447265616D736563757269747920496E632E311E301C06035504031315447265616D736563757269747920524F4F5420434130820122300D06092A864886F70D01010105000382010F003082010A02820101009DA80827BDF5CF6AEF602D766C4BB961C246FFBB986A7F6F68F9D3DA62F8B11204EA0CFDC66329E238A4A1F477C7E29875A2567B870C8F1A37FCB798B55F7684BB06B81BF1479499B835877EBE79C1411AC22A88A304C275A56F6E3533BA564054E0CC7E1457D8D64A86C596AD797BA242E7DC584F258E8907ABB14AAB23FB5100B10A290AE63AEC24B128E8AE22F77620DF0CAD0DF37F6C71BA81105236E4A99B5E8708DD61441B52D33F610BB76D1918346107F9E2A653524E63FB45C2EF95E63774DB97C19388851887F867A3153664FD6EA3F42B7220DF106627EC309A8F361C953C7772937AEAE2ED6E6551292E8D5F86C2654FFD874092436F0C77A7290203010001A355305330120603551D130101FF040830060101FF020100301D0603551D0E0416041401CA541FACA7DBD3FEAF2327C5AF91273057E1D5300B0603551D0F040403020106301106096086480186F8420101040403020007300D06092A864886F70D01010B050003820101007BE5E98B4D75A4A6789BE6E9E3A499D6EC706BFA78AAD5EEDB6B234CD6439014567A306E10C06A51B1C75B5BFC45543DED522363D25B8562BD1D54662AB22D23093BBAF93AC9D71659048224C27A90BCCD4D6208F68364CFDB826CC1959D526CEEC3D8AA0B2E6EC0DEB0909CEA52394CBE06B4BA22677DDBC751CF8DE1B74314756B4C145727CF80F757496130FB241A3165246DE6361C5C9B6990B512AE627356FA2C665279F7DDE067F0438A2CE89344D6A9F936ADCA46EEF534085B200F5480DC1AA45530BF80FCF9E87DC525F1B7558FC7B9B226554D65CA52B51E32389C18667AFD0061234ED7D5B5892BBB2F5194A3D190AF2179B54349D3003AA09754 | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{D03745B1-EF05-4128-81FE-4EA062A6C468} |
| Operation: | write | Name: | AppName |
Value: MagicLine4NX.exe | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{D03745B1-EF05-4128-81FE-4EA062A6C468} |
| Operation: | write | Name: | AppPath |
Value: C:\Program Files (x86)\DreamSecurity\MagicLine4NX | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{D03745B1-EF05-4128-81FE-4EA062A6C468} |
| Operation: | write | Name: | Policy |
Value: 3 | |||
| (PID) Process: | (7976) magicline4nx_setup1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{D03745B1-EF05-4128-81FE-4EA062A6C468} |
| Operation: | write | Name: | AppName |
Value: MagicLine4NX.exe | |||
Executable files
30
Suspicious files
13
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7976 | magicline4nx_setup1.exe | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\CertManager.dll | executable | |
MD5:043F110E1C505BD8D567595983146160 | SHA256:0D40ACEF75C1C98E3E081A4E0E92609495F40BEC60A341F27CE8C7ADD5957F38 | |||
| 7976 | magicline4nx_setup1.exe | C:\Users\admin\AppData\Local\Temp\nsjCCE8.tmp\KillProcDLL.dll | executable | |
MD5:83142EAC84475F4CA889C73F10D9C179 | SHA256:AE2F1658656E554F37E6EAC896475A3862841A18FFC6FAD2754E2D3525770729 | |||
| 7976 | magicline4nx_setup1.exe | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\IssuerOid_Eng.conf | text | |
MD5:7015B31843A75675CBF45D0AFDB87976 | SHA256:FC6A79FA5C0B88C6BBEEBAD76E3BE275AD61F27F02F34DC8F81061755D0FEAAF | |||
| 7976 | magicline4nx_setup1.exe | C:\Users\admin\AppData\Local\Temp\nsjCCE8.tmp\nsProcess.dll | executable | |
MD5:FAA7F034B38E729A983965C04CC70FC1 | SHA256:579A034FF5AB9B732A318B1636C2902840F604E8E664F5B93C07A99253B3C9CF | |||
| 7976 | magicline4nx_setup1.exe | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\MagicCrypto32V22.dll | executable | |
MD5:6A3EB6617EF4CE8200DC2F9533D8F33B | SHA256:E82A1E934FC7195BFBF911FEC09CBA19A8DAD304B2BC9212A16EDD1D5E3CA8DF | |||
| 7976 | magicline4nx_setup1.exe | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\IssuerOid.conf | text | |
MD5:65B23B61966A87AE3D45FFA7C5A8985C | SHA256:2D803D60C49A5B43C504A5700905AA21750C6F913DC92F5315AC4DDA722D1073 | |||
| 7976 | magicline4nx_setup1.exe | C:\Program Files (x86)\DreamSecurity\MagicLine4NX\DSCToolkitV30-v3.4.2.25.dll | executable | |
MD5:C5E9763804798318723056B9D56BD1BB | SHA256:8D5763D6CF8A38D8D97F9F4265B245E8C3FB6D343E21919D2F4885A67834BD9E | |||
| 7976 | magicline4nx_setup1.exe | C:\Users\admin\AppData\Local\Temp\nsjCCE8.tmp\System.dll | executable | |
MD5:4D3B19A81BD51F8CE44B93643A4E3A99 | SHA256:FDA0018AB182AC6025D2FC9A2EFCCE3745D1DA21CE5141859F8286CF319A52CE | |||
| 7976 | magicline4nx_setup1.exe | C:\Users\admin\AppData\Local\Temp\nsjCCE8.tmp\nsExec.dll | executable | |
MD5:3EB4CD50DCB9F5981F5408578CB7FB70 | SHA256:1C2F19E57DC72587AA00800A498C5F581B7D6761DC13B24BCF287EA7BD5CA2BF | |||
| 7976 | magicline4nx_setup1.exe | C:\Users\admin\AppData\Local\Temp\nsjCCE8.tmp\NsisUtil.dll | executable | |
MD5:59541B9DA3C09F318A58BEF52C9FF131 | SHA256:74A542EF3BBE0673453286DFEB335C1D7BDE4E601C932A3D0D04C85EB098BB47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
40
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5400 | SIHClient.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7476 | MagicLine4NX.exe | 124.111.52.169:443 | www.dreamsecurity.com | SK Broadband Co Ltd | KR | unknown |
5400 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5400 | SIHClient.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5400 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5400 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.dreamsecurity.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MagicLine4NXServices.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|