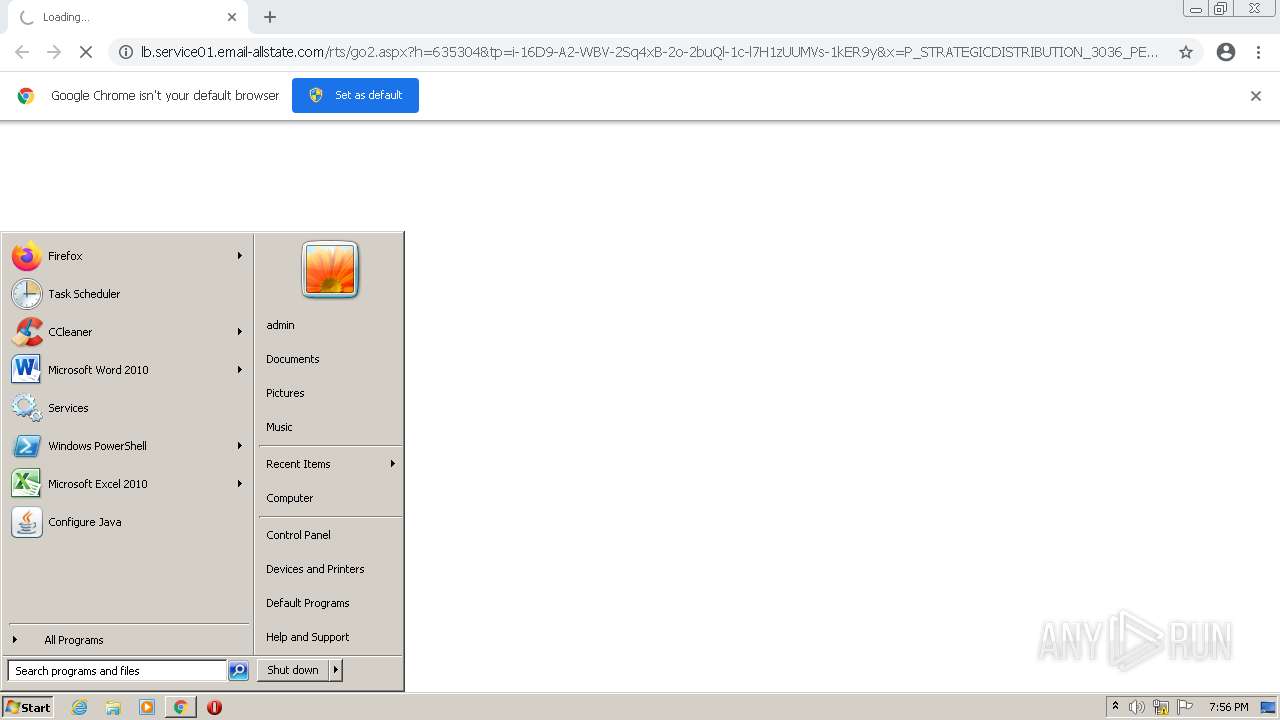
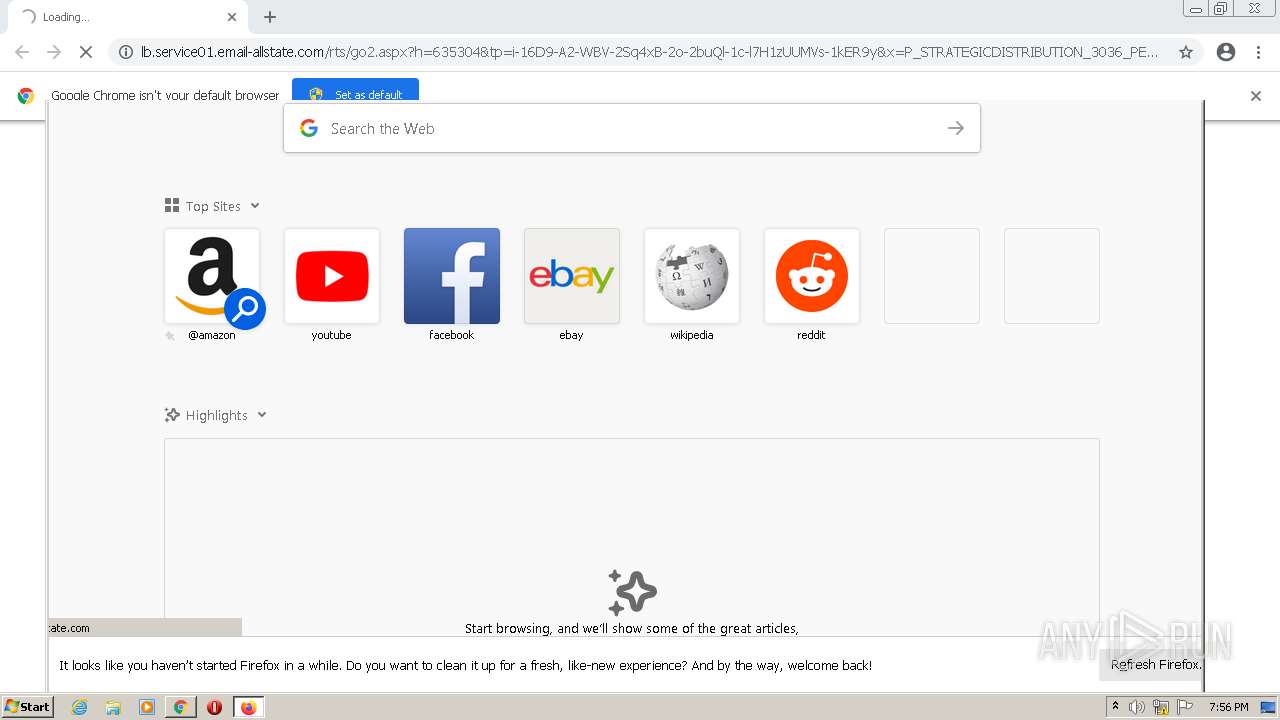
| URL: | http://lb.service01.email-allstate.com/rts/go2.aspx?h=635304&tp=i-16D9-A2-WBV-2Sq4xB-2o-2buQl-1c-l7H1zUUMVs-1kER9y&x=P_STRATEGICDISTRIBUTION_3036_PERSONALIZEDONBOARDINGEXPERIANCEWELCOME_T%7c20210325%7c:EN |
| Full analysis: | https://app.any.run/tasks/3c98d18c-ec91-422a-b32e-5ac728259cf8 |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2022, 19:56:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6AA127224580F29F9D3CCD3D534C96F6 |
| SHA1: | 00D2941C03513F38E7EC3B70B6E5C0BE029EADED |
| SHA256: | 4714D749087AD11BA27BD1D094DF45E9C4A0E2322ABDA980003156970A9CC9A0 |
| SSDEEP: | 3:N1KSHLWANLtt2HKKbEWqKTw0aToLNDjfIUErjCc3tUGmIQr6WC+qrgeyd1gcacqk:CSHLHZtKgWtaEbE6c9u6WZQRwAcbCgZn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 624)
- chrome.exe (PID: 480)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2620)
- firefox.exe (PID: 2788)
- firefox.exe (PID: 348)
- firefox.exe (PID: 3132)
- chrome.exe (PID: 1360)
- firefox.exe (PID: 2568)
- firefox.exe (PID: 3796)
- chrome.exe (PID: 2356)
- firefox.exe (PID: 3636)
- firefox.exe (PID: 2768)
- firefox.exe (PID: 1596)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 404)
Reads the computer name
- chrome.exe (PID: 3020)
- chrome.exe (PID: 480)
- chrome.exe (PID: 624)
- chrome.exe (PID: 2620)
- firefox.exe (PID: 348)
- firefox.exe (PID: 2768)
- firefox.exe (PID: 1596)
- firefox.exe (PID: 2568)
- firefox.exe (PID: 3636)
- firefox.exe (PID: 3796)
- firefox.exe (PID: 3132)
- chrome.exe (PID: 404)
Reads settings of System Certificates
- chrome.exe (PID: 624)
Reads the hosts file
- chrome.exe (PID: 624)
- chrome.exe (PID: 3020)
Manual execution by user
- firefox.exe (PID: 2788)
Application launched itself
- chrome.exe (PID: 3020)
- firefox.exe (PID: 2788)
- firefox.exe (PID: 348)
Creates files in the program directory
- firefox.exe (PID: 348)
Creates files in the user directory
- firefox.exe (PID: 348)
Reads CPU info
- firefox.exe (PID: 348)
Reads the date of Windows installation
- chrome.exe (PID: 404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3036 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1228 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="348.34.1194314042\393292419" -childID 5 -isForBrowser -prefsHandle 4056 -prefMapHandle 3320 -prefsLen 7857 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 348 "\\.\pipe\gecko-crash-server-pipe.348" 4060 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="348.6.607091110\1512279050" -childID 1 -isForBrowser -prefsHandle 2656 -prefMapHandle 2652 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 348 "\\.\pipe\gecko-crash-server-pipe.348" 2668 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2672 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
17 712
Read events
17 644
Write events
68
Delete events
0
Modification events
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
119
Text files
72
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62339256-BCC.pma | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\27ad141d-6657-4ffa-9e47-238f9e2d8a9e.tmp | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11505f.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1151b7.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
152
DNS requests
184
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
348 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
348 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
348 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
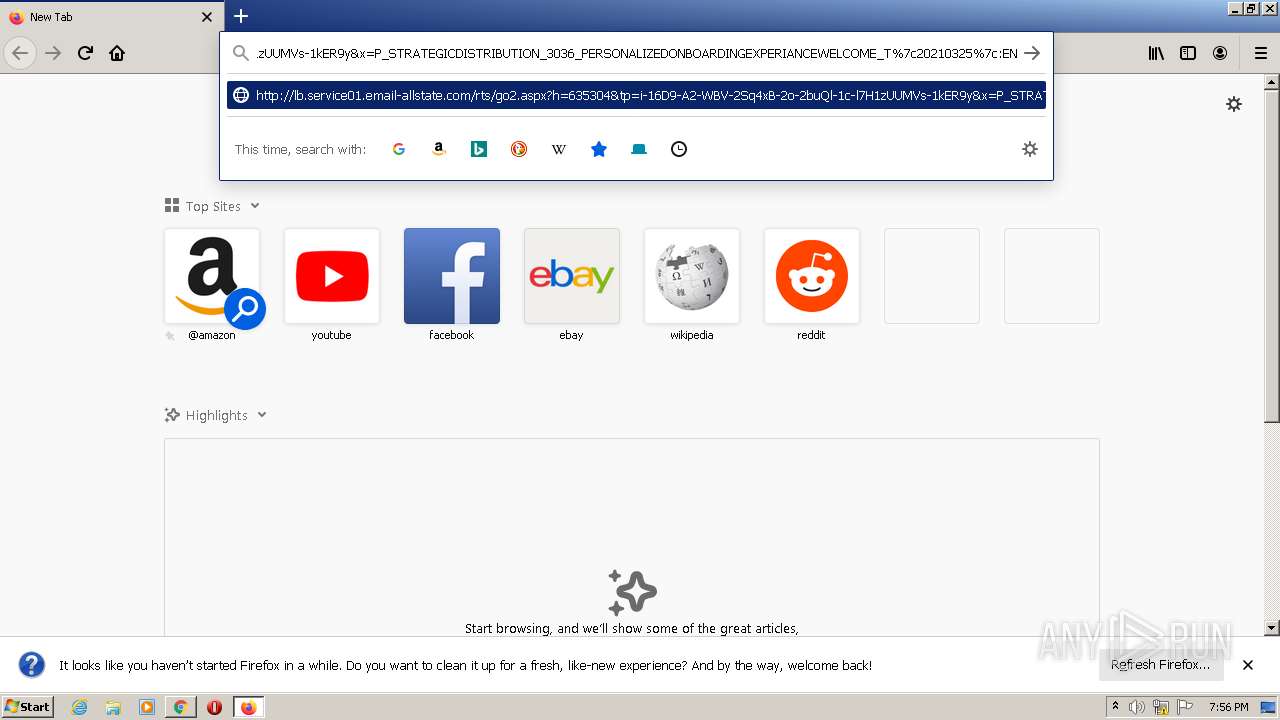
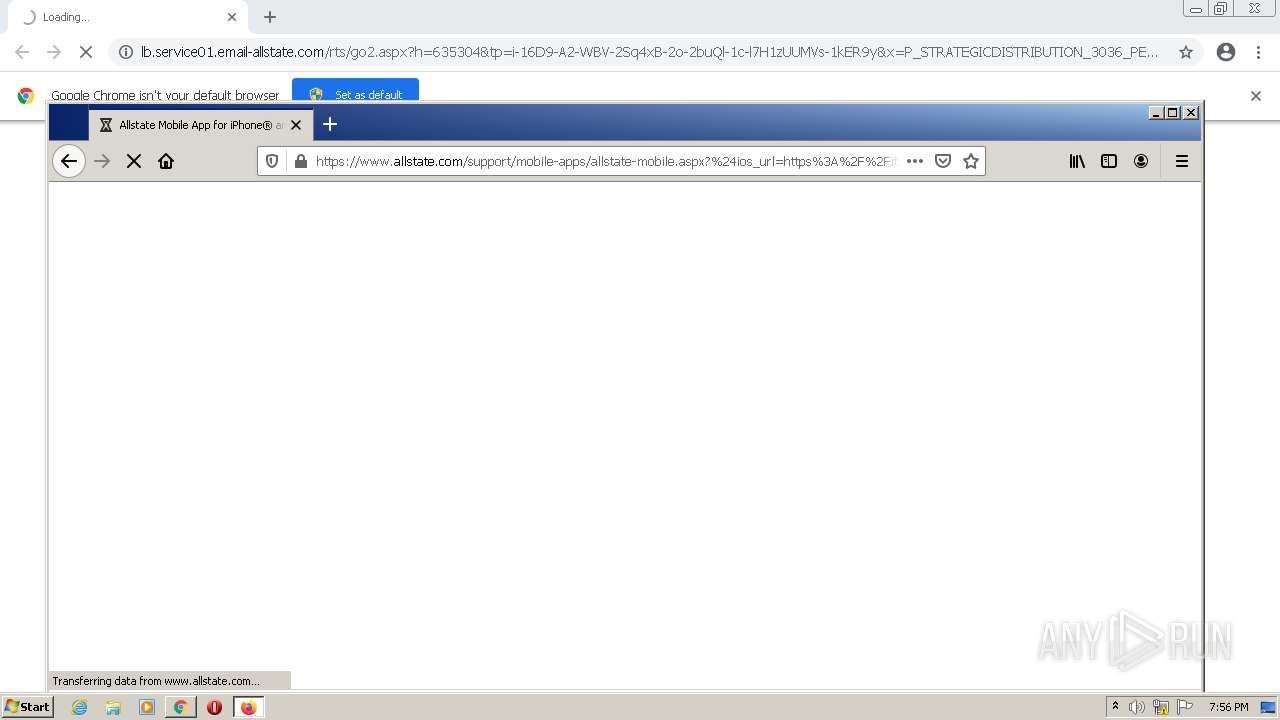
348 | firefox.exe | GET | 302 | 54.193.140.103:80 | http://lb.service01.email-allstate.com/rts/go2.aspx?h=635304&tp=i-16D9-A2-WBV-2Sq4xB-2o-2buQl-1c-l7H1zUUMVs-1kER9y&x=P_STRATEGICDISTRIBUTION_3036_PERSONALIZEDONBOARDINGEXPERIANCEWELCOME_T%7c20210325%7c:EN | US | html | 635 b | suspicious |
348 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
348 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
348 | firefox.exe | POST | 200 | 23.45.103.152:80 | http://ocsp.entrust.net/ | NL | der | 1.55 Kb | whitelisted |
348 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
348 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
348 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
624 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 54.177.1.87:80 | lb.service01.email-allstate.com | Amazon.com, Inc. | US | unknown |
624 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
348 | firefox.exe | 54.193.140.103:80 | lb.service01.email-allstate.com | Amazon.com, Inc. | US | suspicious |
348 | firefox.exe | 13.32.22.114:443 | content-signature-2.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
348 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
348 | firefox.exe | 143.204.215.92:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | malicious |
348 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
348 | firefox.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
348 | firefox.exe | 23.45.108.129:443 | www.allstate.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
lb.service01.email-allstate.com |
| suspicious |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
348 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
348 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |