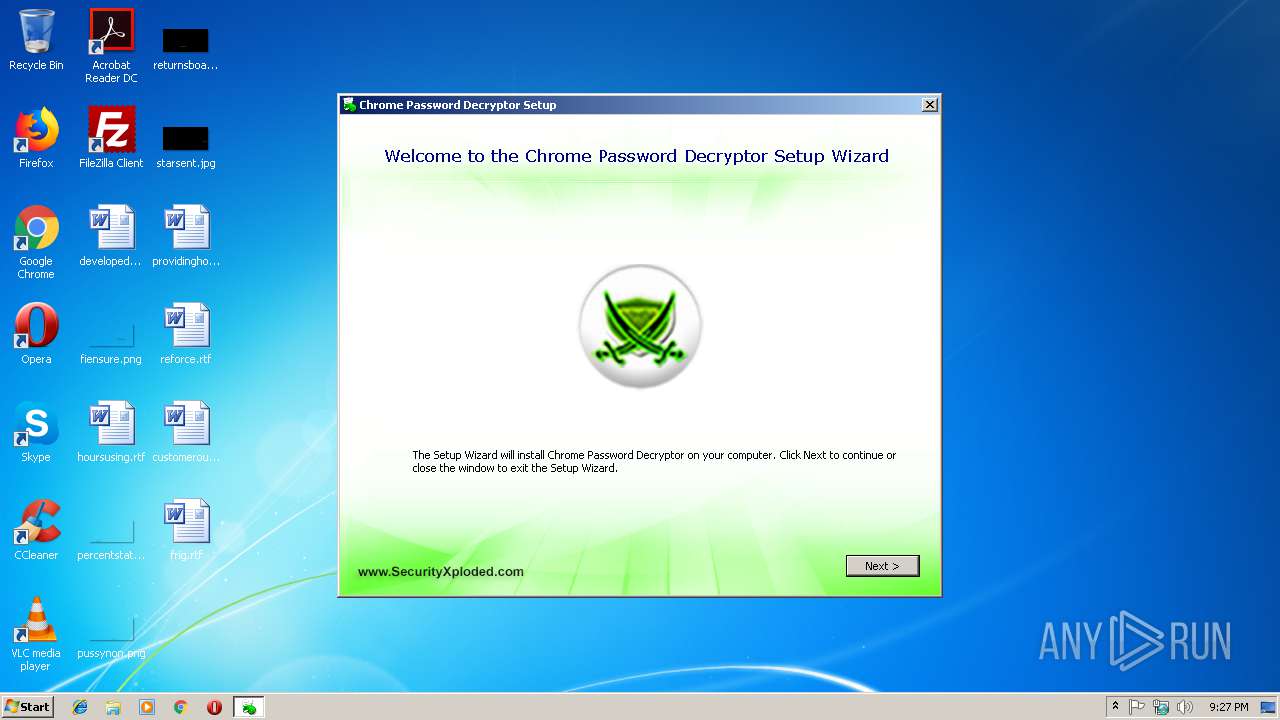
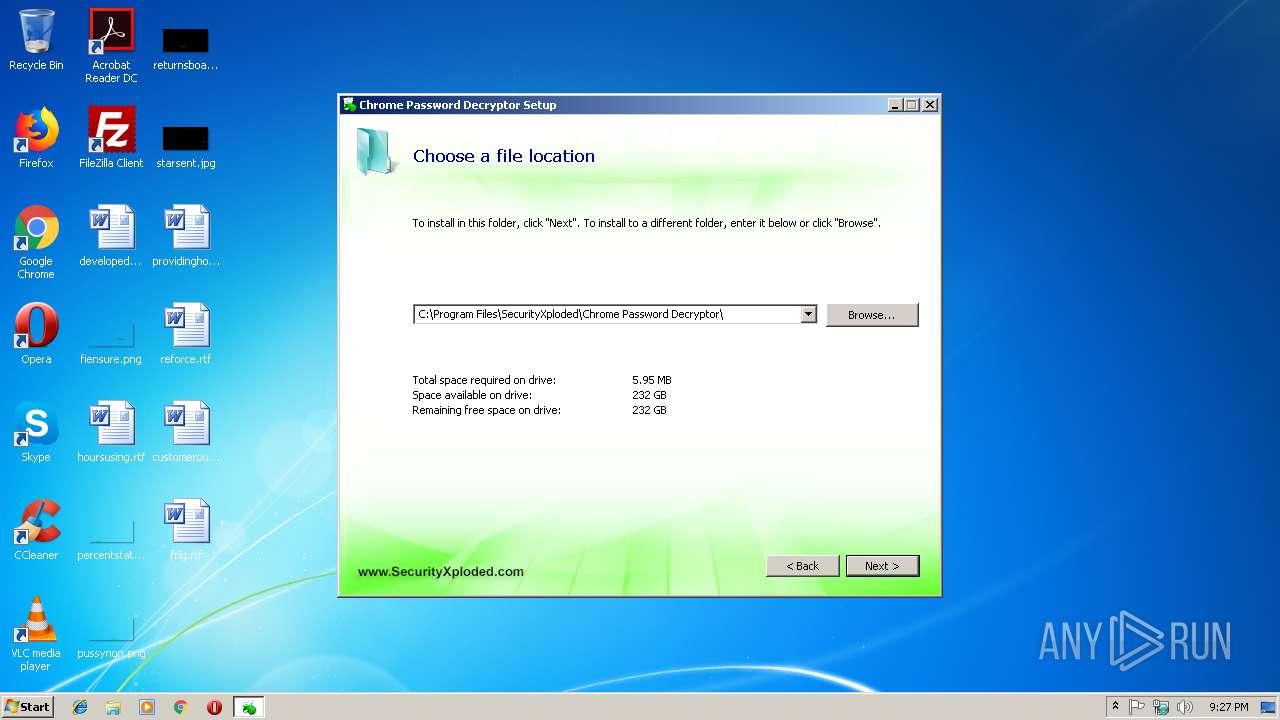
| File name: | Setup_ChromePasswordDecryptor.exe |
| Full analysis: | https://app.any.run/tasks/b83f5fc2-08ac-4cc1-9eb6-0c5a61eefeda |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 21:26:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BE33145C0A67E0180475B32503979EC5 |
| SHA1: | A20833C98A89096CBC625497F982BB3F9A0733A4 |
| SHA256: | 47139B4258787F484960B9405F1F9DA09763063871F603C61DD6F2919BD5E29A |
| SSDEEP: | 98304:kH23QMy3hLASfWDNH23QMy3hLASvWDKtqZNtECTVACnD9w66nI0n7CnlKnwlt:o23Axm23AxR0ECpA8Kwlt |
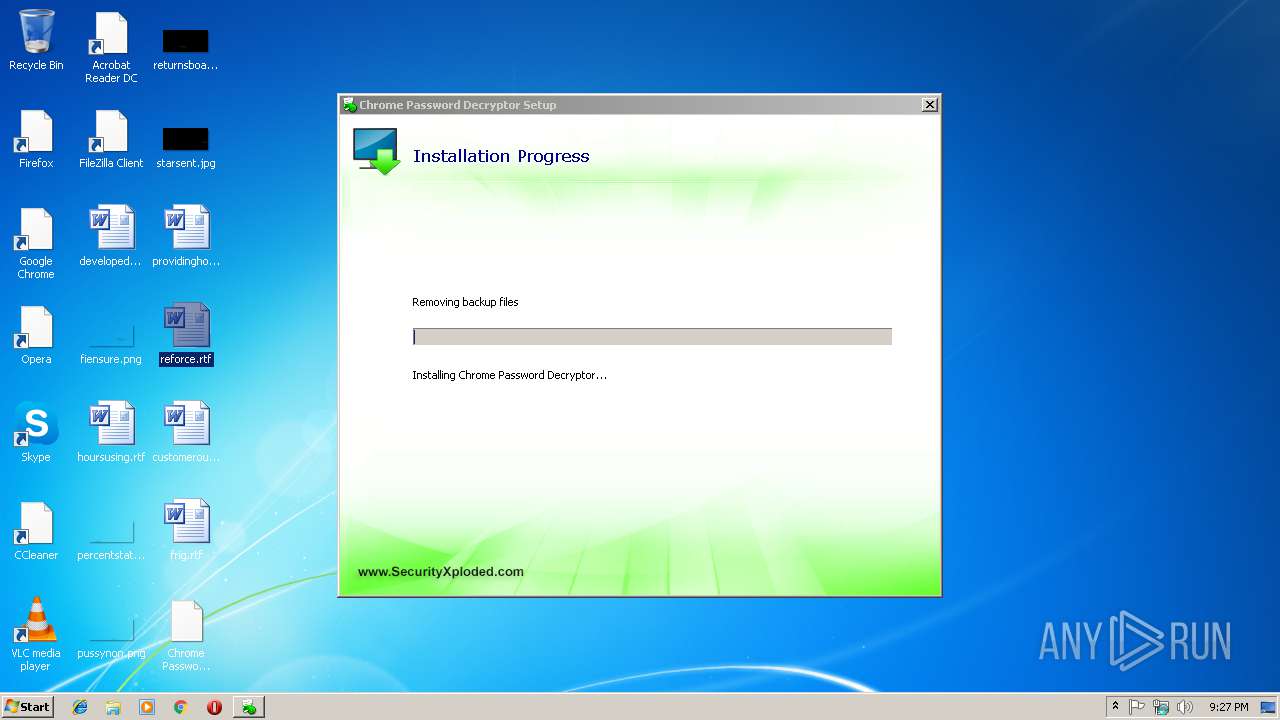
MALICIOUS
Application was dropped or rewritten from another process
- MSI2B1D.tmp (PID: 3040)
- ChromePasswordDecryptor.exe (PID: 1748)
- MSI2B1C.tmp (PID: 3048)
Loads the Task Scheduler DLL interface
- Setup_ChromePasswordDecryptor.exe (PID: 3272)
SUSPICIOUS
Creates files in the user directory
- Setup_ChromePasswordDecryptor.exe (PID: 3272)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3208)
- Setup_ChromePasswordDecryptor.exe (PID: 3272)
- Setup_ChromePasswordDecryptor.exe (PID: 3096)
Application launched itself
- Setup_ChromePasswordDecryptor.exe (PID: 3272)
- cmd.exe (PID: 2652)
- cmd.exe (PID: 1820)
Creates files in the program directory
- Setup_ChromePasswordDecryptor.exe (PID: 3096)
Starts application with an unusual extension
- Setup_ChromePasswordDecryptor.exe (PID: 3272)
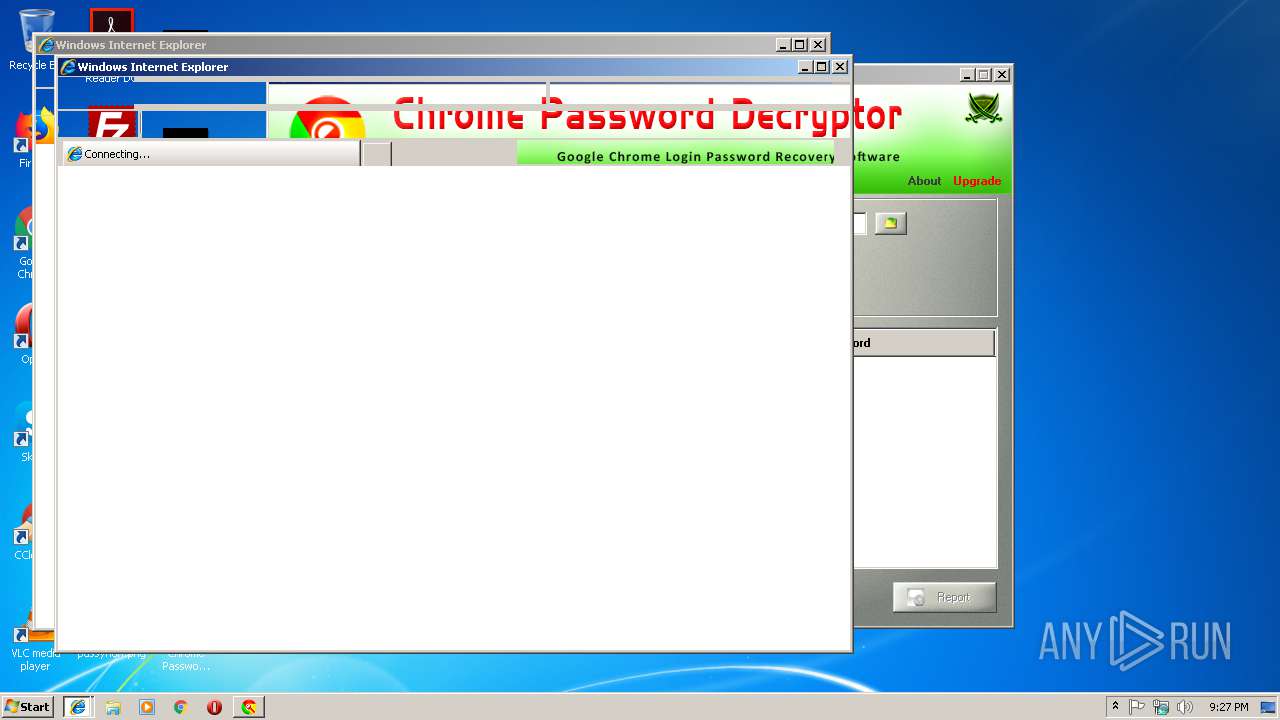
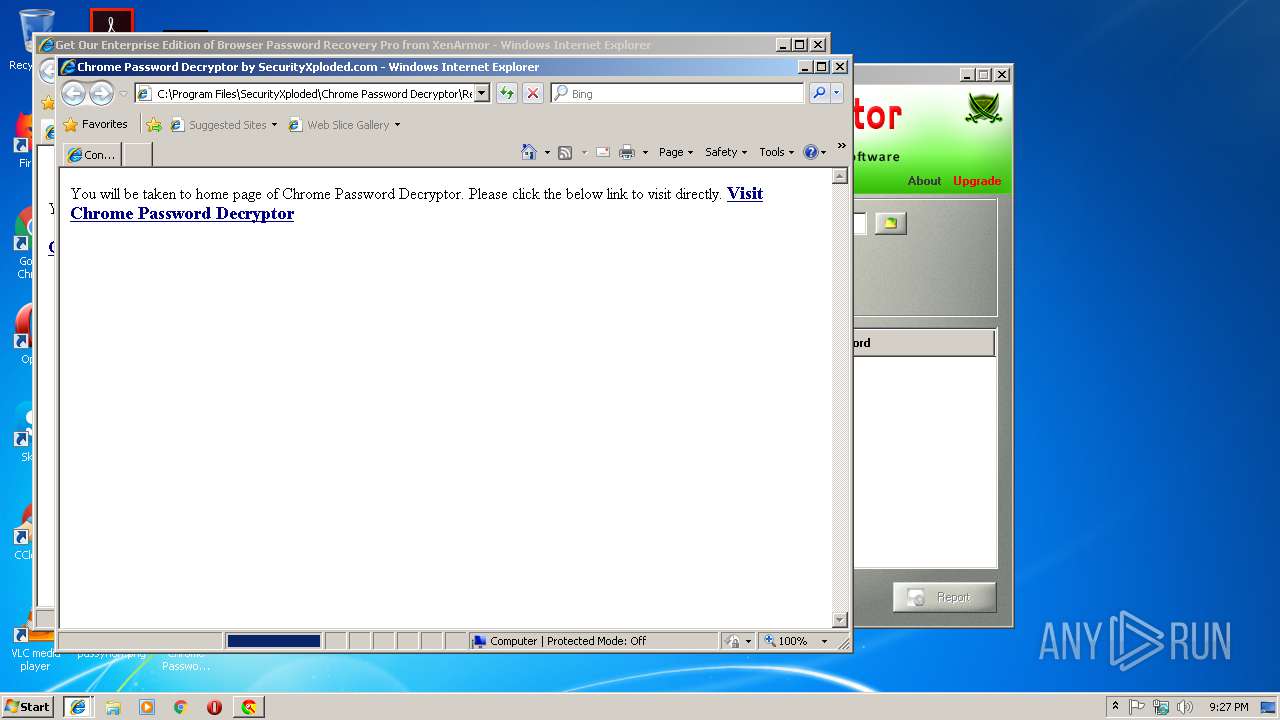
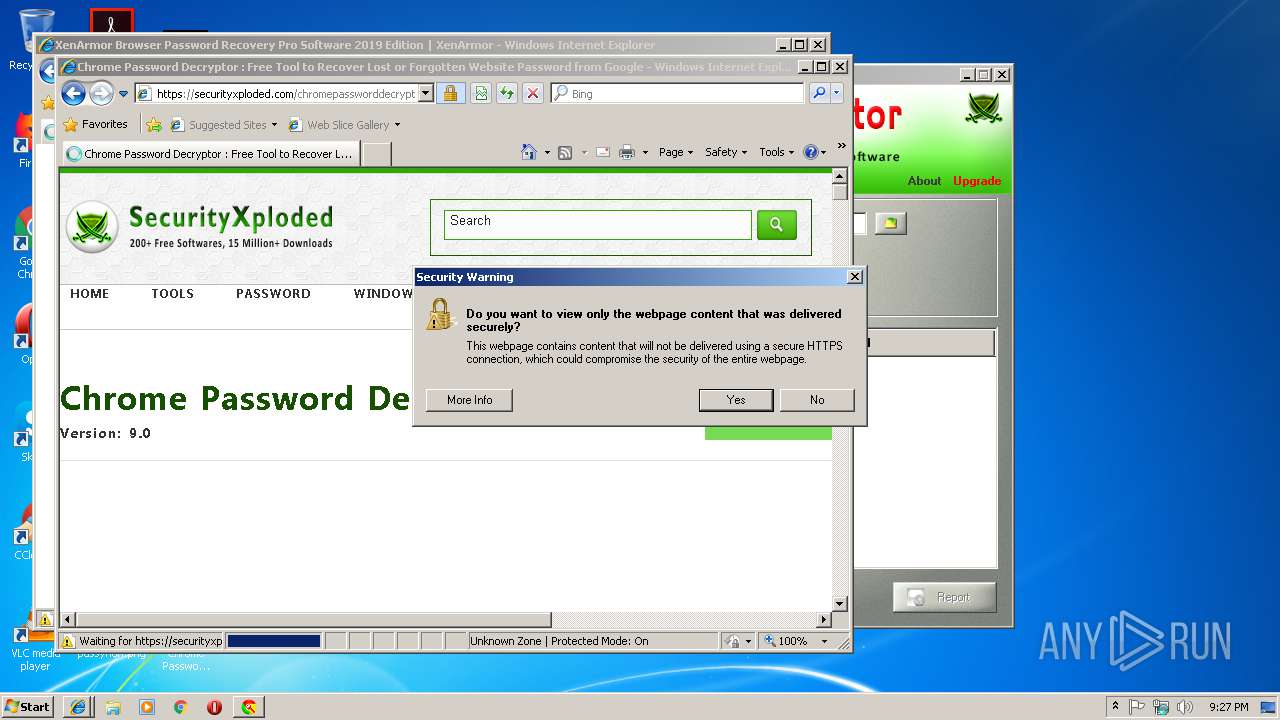
Starts Internet Explorer
- MSI2B1D.tmp (PID: 3040)
- MSI2B1C.tmp (PID: 3048)
Starts CMD.EXE for commands execution
- Setup_ChromePasswordDecryptor.exe (PID: 3272)
- cmd.exe (PID: 1820)
- cmd.exe (PID: 2652)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1820)
- cmd.exe (PID: 2652)
INFO
Application launched itself
- msiexec.exe (PID: 3208)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3388)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2972)
- MsiExec.exe (PID: 3368)
Creates files in the program directory
- msiexec.exe (PID: 3208)
Creates a software uninstall entry
- msiexec.exe (PID: 3208)
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 3388)
Changes internet zones settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3388)
Reads Internet Cache Settings
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3388)
Reads internet explorer settings
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 2532)
Reads settings of System Certificates
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3388)
Changes settings of System certificates
- iexplore.exe (PID: 3632)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3632)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3356)
- iexplore.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:23 10:36:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1132032 |
| InitializedDataSize: | 648192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd2ba3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
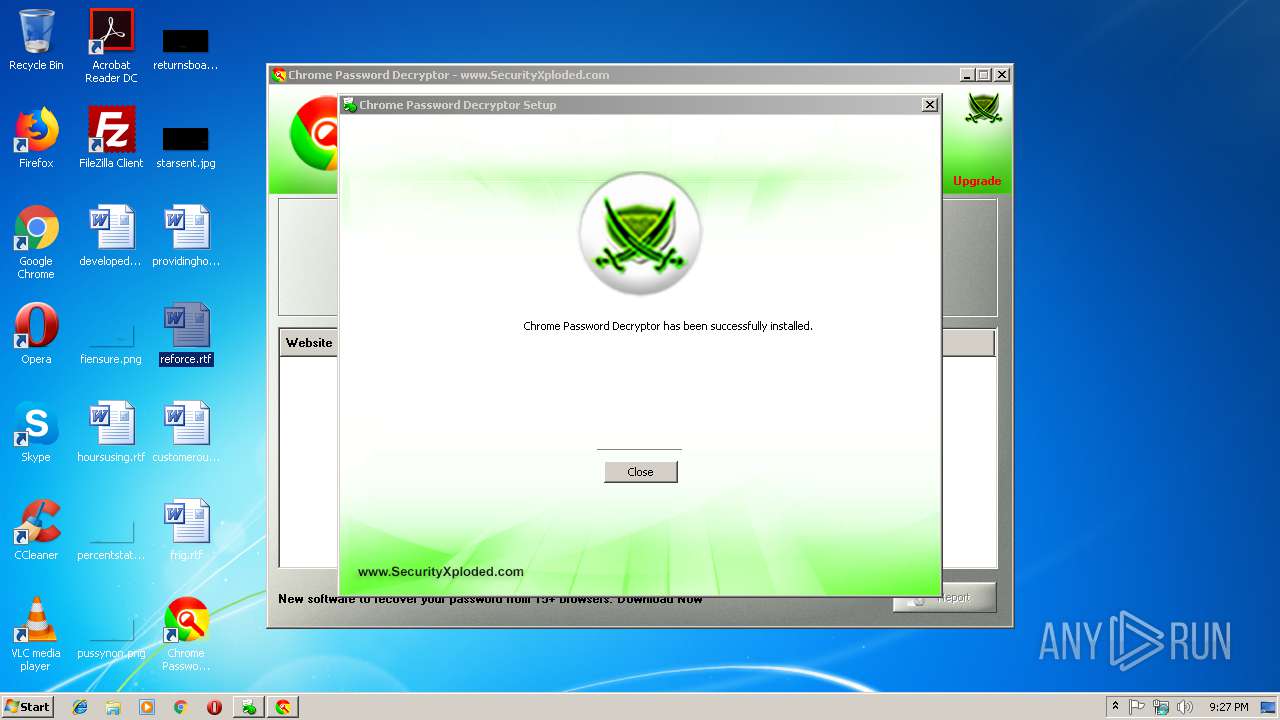
| CompanyName: | SecurityXploded |
| FileDescription: | This installer database contains the logic and data required to install Chrome Password Decryptor. |
| FileVersion: | 9 |
| InternalName: | Setup_ChromePasswordDecryptor |
| LegalCopyright: | Copyright (C) 2018 SecurityXploded |
| OriginalFileName: | Setup_ChromePasswordDecryptor.exe |
| ProductName: | Chrome Password Decryptor |
| ProductVersion: | 9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Mar-2016 09:36:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | SecurityXploded |
| FileDescription: | This installer database contains the logic and data required to install Chrome Password Decryptor. |
| FileVersion: | 9.0 |
| InternalName: | Setup_ChromePasswordDecryptor |
| LegalCopyright: | Copyright (C) 2018 SecurityXploded |
| OriginalFileName: | Setup_ChromePasswordDecryptor.exe |
| ProductName: | Chrome Password Decryptor |
| ProductVersion: | 9.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 23-Mar-2016 09:36:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001144A0 | 0x00114600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63578 |
.rdata | 0x00116000 | 0x0004E26A | 0x0004E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42801 |
.data | 0x00165000 | 0x000075EC | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.14531 |
.gfids | 0x0016D000 | 0x000003E8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.91254 |
.tls | 0x0016E000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0016F000 | 0x00035BB0 | 0x00035C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53497 |
.reloc | 0x001A5000 | 0x00014758 | 0x00014800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60442 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.57558 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.82278 | 26600 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.84142 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.1433 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.07235 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.30616 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.09197 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
62
Monitored processes
25
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
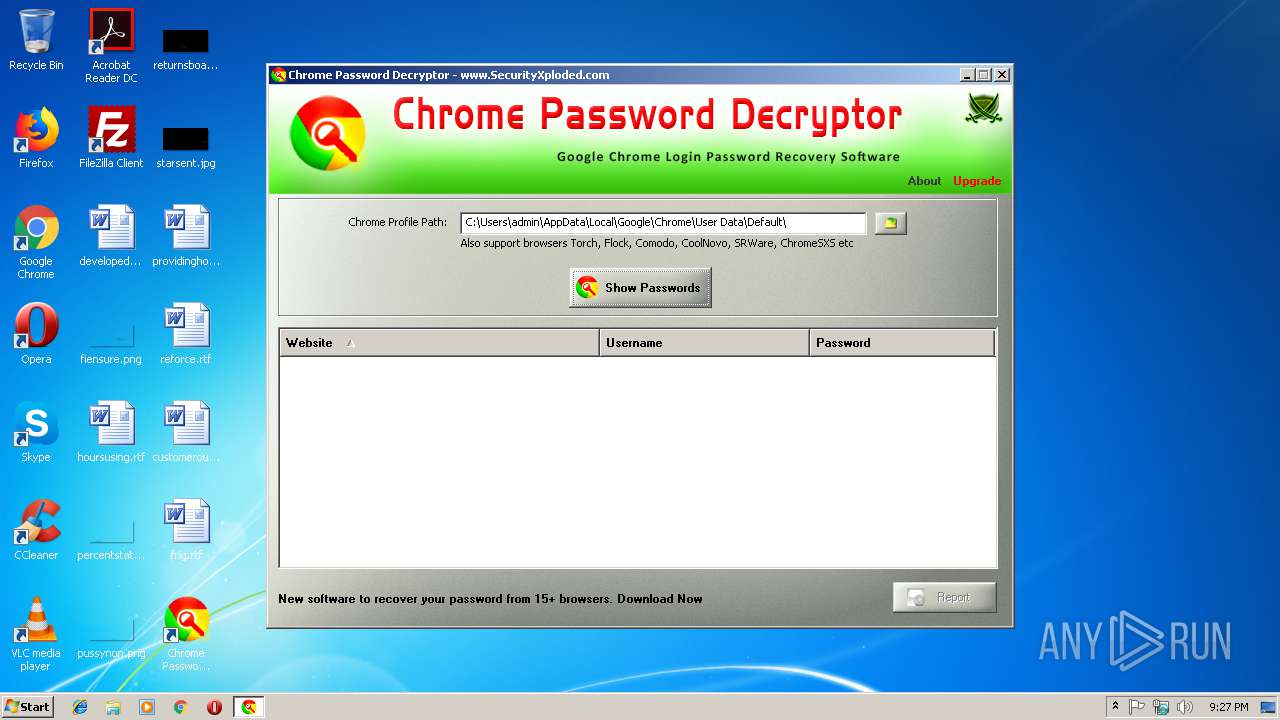
| 1748 | "C:\Program Files\SecurityXploded\Chrome Password Decryptor\ChromePasswordDecryptor.exe" | C:\Program Files\SecurityXploded\Chrome Password Decryptor\ChromePasswordDecryptor.exe | Setup_ChromePasswordDecryptor.exe | ||||||||||||
User: admin Company: SecurityXploded Integrity Level: MEDIUM Description: Chrome Password Decryptor Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 1820 | cmd /c ""C:\Users\admin\AppData\Local\Temp\EXE3223.tmp.bat" " | C:\Windows\system32\cmd.exe | — | Setup_ChromePasswordDecryptor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2124 | C:\Windows\system32\cmd.exe /S /D /c" cls" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2304 | ATTRIB -r "\\?\C:\Users\admin\AppData\Roaming\SECURI~1\CHROME~1.0\install\CHROME~1.MSI" | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | ATTRIB -r "C:\Users\admin\AppData\Local\Temp\EXE32A1.tmp.bat" | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3632 CREDAT:14337 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3632 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2652 | cmd /c ""C:\Users\admin\AppData\Local\Temp\EXE32A1.tmp.bat" " | C:\Windows\system32\cmd.exe | — | Setup_ChromePasswordDecryptor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3388 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3388 CREDAT:14337 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 258
Read events
1 910
Write events
331
Delete events
17
Modification events
| (PID) Process: | (3272) Setup_ChromePasswordDecryptor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3272) Setup_ChromePasswordDecryptor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 880C0000C85B573599B2D401 | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A5981E360E6A619FA5B59F63F5C4F27F7891902EEA706952892C75DE854BAE9F | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\1a0dfc.ipi | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1a0dfd.rbs |
Value: 30716569 | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1a0dfd.rbsLow |
Value: 1202882576 | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\D567225B335A7B34CB41B116ADE039F8 |
| Operation: | write | Name: | 0116752B824B6F942840CE469058B7AD |
Value: C:\Program Files\SecurityXploded\Chrome Password Decryptor\ChromePasswordDecryptor.exe | |||
| (PID) Process: | (3208) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\6B25AEDF8ED16B14D862B02E64FE4DC7 |
| Operation: | write | Name: | 0116752B824B6F942840CE469058B7AD |
Value: 02:\Software\SecurityXploded\Chrome Password Decryptor\Version | |||
Executable files
16
Suspicious files
11
Text files
138
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\MSI9C37.tmp | — | |
MD5:— | SHA256:— | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Roaming\SecurityXploded\Chrome Password Decryptor 9.0\install\holder0.aiph | gmc | |
MD5:— | SHA256:— | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Roaming\SecurityXploded\Chrome Password Decryptor 9.0\install\ChromePasswordDecryptor.msi | executable | |
MD5:— | SHA256:— | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\tabback | image | |
MD5:4C3DDA35E23D44E273D82F7F4C38470A | SHA256:E728F79439E07DF1AFBCF03E8788FA0B8B08CF459DB31FC8568BC511BF799537 | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\installlogoicon | image | |
MD5:2D030BB775A8D74CC5D39910601FA7D6 | SHA256:FA387D12AEF97734A3B8A079B462447FB977ABEEF5987D5EE5B4217F1057CC2D | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\printico | image | |
MD5:BDC280616F9670F41C57C16BF08E8387 | SHA256:6E5C2E9E923569F943E9F8A86EE5023034B3DB1F6434118A0D95F429F90FFBE7 | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\info | image | |
MD5:FD535E63F539EACB3F11D03B52B39A80 | SHA256:0086BC01150989F553A0A4AE0E14926C6E247CEDDA312E1F946AE35D575742AB | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\sx_logo_icon.ico | image | |
MD5:87360088F68F5FF62AE038C9E6856C07 | SHA256:6FC308D85B50C8F8903317E00924AAB7CB2C07CFA3F7E0C1A181E01E3162B8E3 | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\folderlogoicon | image | |
MD5:17780B507A253C687F744FD9B2627864 | SHA256:451331950FF77FC77E7E58C8F1AC8A099268C75A872DFAE3B7B475F33F9A5E70 | |||
| 3272 | Setup_ChromePasswordDecryptor.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_3272\removico | image | |
MD5:F39938F40CE3BD5CF79F3C155C11F775 | SHA256:DE53FD967F039D2CAF4D21D149B607EC7015884A870A877C5039A0F1888D97EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
46
DNS requests
9
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
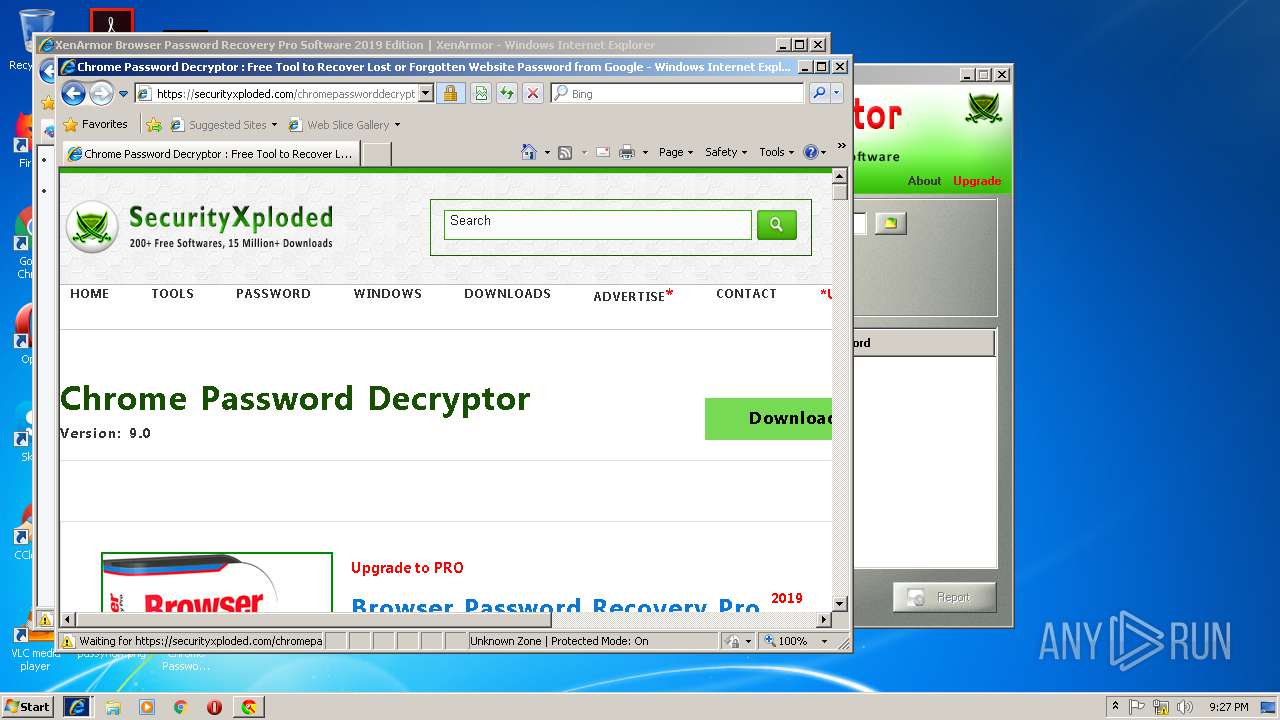
2848 | iexplore.exe | GET | 301 | 172.217.21.206:80 | http://www.youtube.com/v/yQg9GY9qEa8?fs=1&hl=en_US&rel=0&color1=0x3a3a3a&color2=0x999999&border=1 | US | — | — | whitelisted |
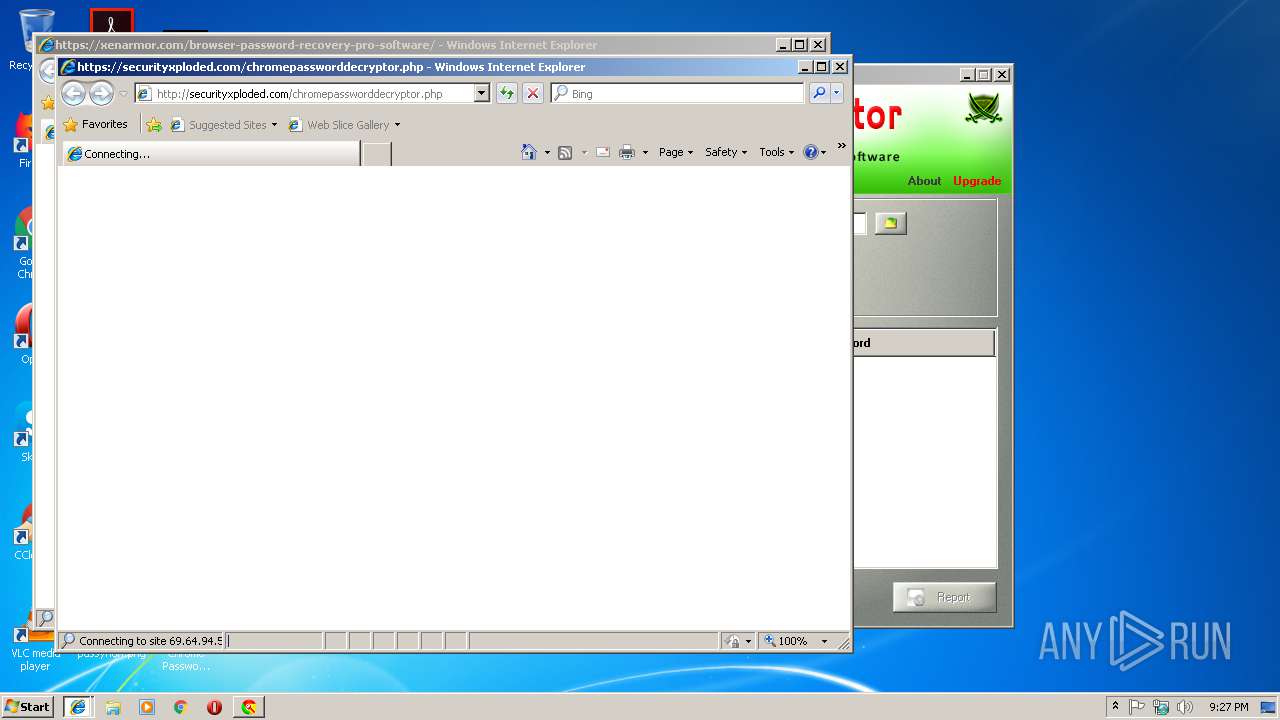
2848 | iexplore.exe | GET | 301 | 69.64.94.55:80 | http://securityxploded.com/chromepassworddecryptor.php | US | html | 178 b | whitelisted |
3632 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
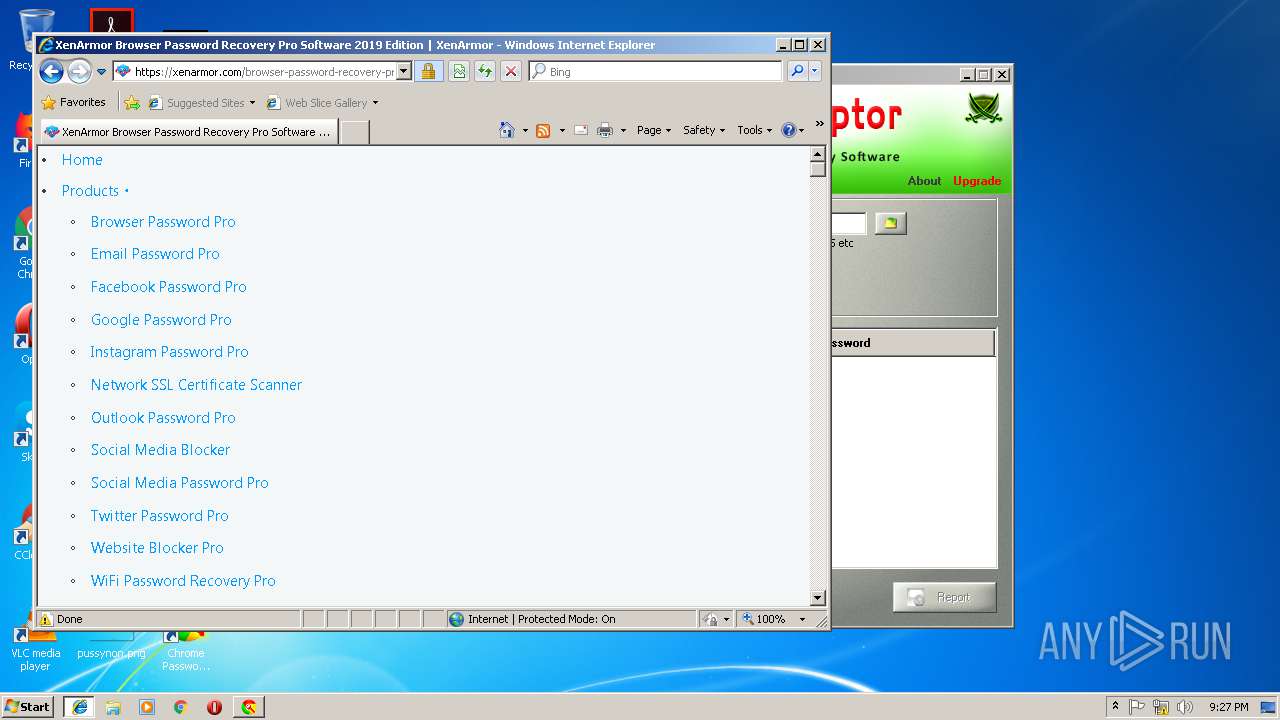
2532 | iexplore.exe | GET | 301 | 69.64.94.128:80 | http://xenarmor.com/browser-password-recovery-pro-software/ | US | html | 178 b | suspicious |
1748 | ChromePasswordDecryptor.exe | GET | 301 | 69.64.94.55:80 | http://www.securityxploded.com/product_versions.xml | US | html | 178 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | iexplore.exe | 69.64.94.55:443 | www.securityxploded.com | Codero | US | malicious |
2532 | iexplore.exe | 69.64.94.128:443 | xenarmor.com | Codero | US | suspicious |
2848 | iexplore.exe | 151.139.128.10:443 | cdn.securityxploded.com | Highwinds Network Group, Inc. | US | malicious |
2532 | iexplore.exe | 151.139.128.10:443 | cdn.securityxploded.com | Highwinds Network Group, Inc. | US | malicious |
3632 | iexplore.exe | 151.139.128.10:443 | cdn.securityxploded.com | Highwinds Network Group, Inc. | US | malicious |
2532 | iexplore.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2848 | iexplore.exe | 172.217.21.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
2848 | iexplore.exe | 172.217.21.206:80 | www.youtube.com | Google Inc. | US | whitelisted |
3388 | iexplore.exe | 69.64.94.55:443 | www.securityxploded.com | Codero | US | malicious |
1748 | ChromePasswordDecryptor.exe | 69.64.94.55:80 | www.securityxploded.com | Codero | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.securityxploded.com |
| whitelisted |
securityxploded.com |
| whitelisted |
www.bing.com |
| whitelisted |
xenarmor.com |
| suspicious |
cdn.securityxploded.com |
| suspicious |
cdn.xenarmor.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
cdn.subscribers.com |
| whitelisted |
www.youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
2 ETPRO signatures available at the full report