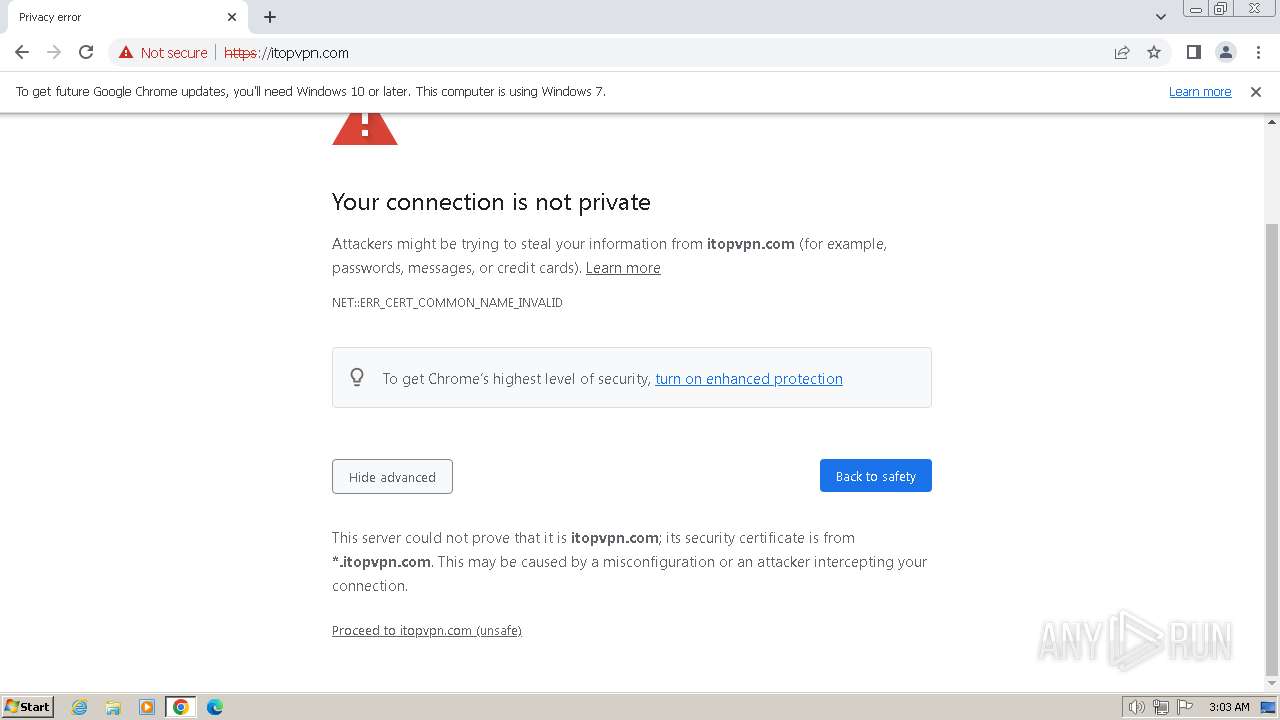
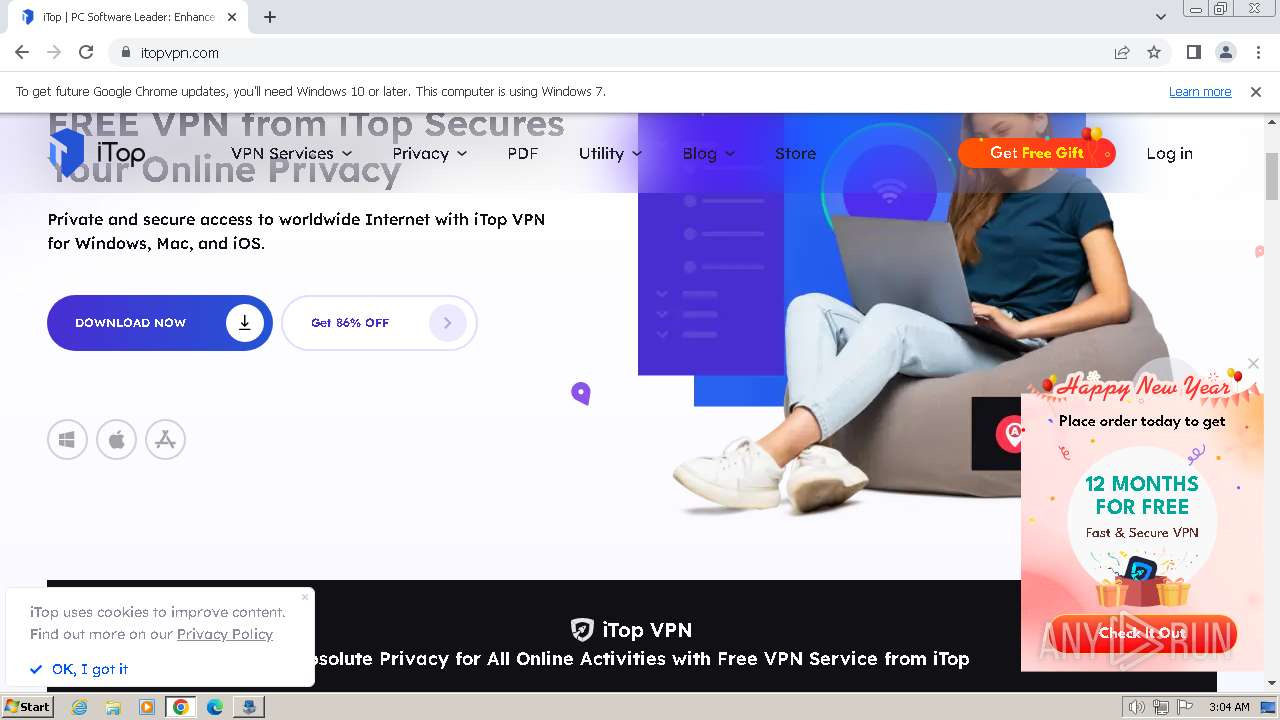
| URL: | https://stats.itopvpn.com |
| Full analysis: | https://app.any.run/tasks/be98df74-28ce-4f77-8248-d8fa7d0134e8 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 10, 2024, 03:03:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E6633D8FFD0A3BE6D93840E195671E28 |
| SHA1: | DA8C589C62F058D96370F2BBD3E0ACC222BE2243 |
| SHA256: | 470EA417B9920105F35438CCF90751EB8D9F55F5F944D53CE662F5ABA3426447 |
| SSDEEP: | 3:N8cvMRKLSn:2cvMRK+ |
MALICIOUS
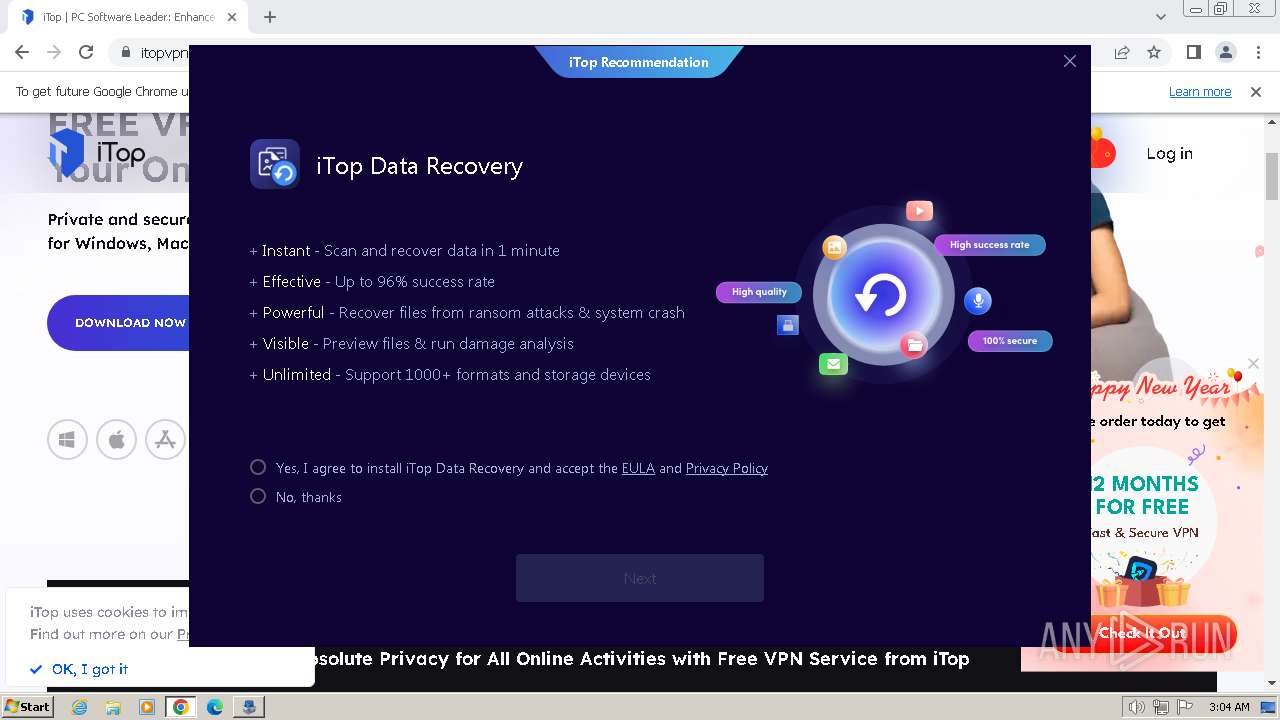
Runs injected code in another process
- icop32.exe (PID: 3944)
- ICONPIN32.exe (PID: 572)
Steals credentials from Web Browsers
- iTopVPN.exe (PID: 2520)
Actions looks like stealing of personal data
- iTopVPN.exe (PID: 2520)
SUSPICIOUS
Reads the Windows owner or organization settings
- iTopVPN_setup_Free.tmp (PID: 3696)
- iTopVPN_setup_Free.tmp (PID: 4036)
- iTopDataRecovery.tmp (PID: 3088)
Reads the Internet Settings
- iTopVPN_setup_Free.tmp (PID: 3696)
- iTopVPN_setup_Free.tmp (PID: 4036)
- ugin.exe (PID: 1572)
- Setup.exe (PID: 3824)
- iTopVPN.exe (PID: 2520)
- iTopDataRecovery.tmp (PID: 3088)
- iTopDownloader.exe (PID: 1088)
- IdrInit.exe (PID: 3696)
- iTopDataRecovery.exe (PID: 2568)
Uses TASKKILL.EXE to kill process
- iTopVPN_setup_Free.tmp (PID: 4036)
Drops a system driver (possible attempt to evade defenses)
- iTopVPN_setup_Free.tmp (PID: 4036)
- ugin.exe (PID: 1572)
Starts CMD.EXE for commands execution
- ugin.exe (PID: 1572)
- iTopVPN.exe (PID: 2520)
- iTopDataRecovery.tmp (PID: 3088)
Starts SC.EXE for service management
- cmd.exe (PID: 2208)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 1540)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 2636)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 1888)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 1384)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 876)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 3720)
- cmd.exe (PID: 3168)
Searches for installed software
- iTopVPN.exe (PID: 2520)
The process verifies whether the antivirus software is installed
- iTopVPN.exe (PID: 2520)
INFO
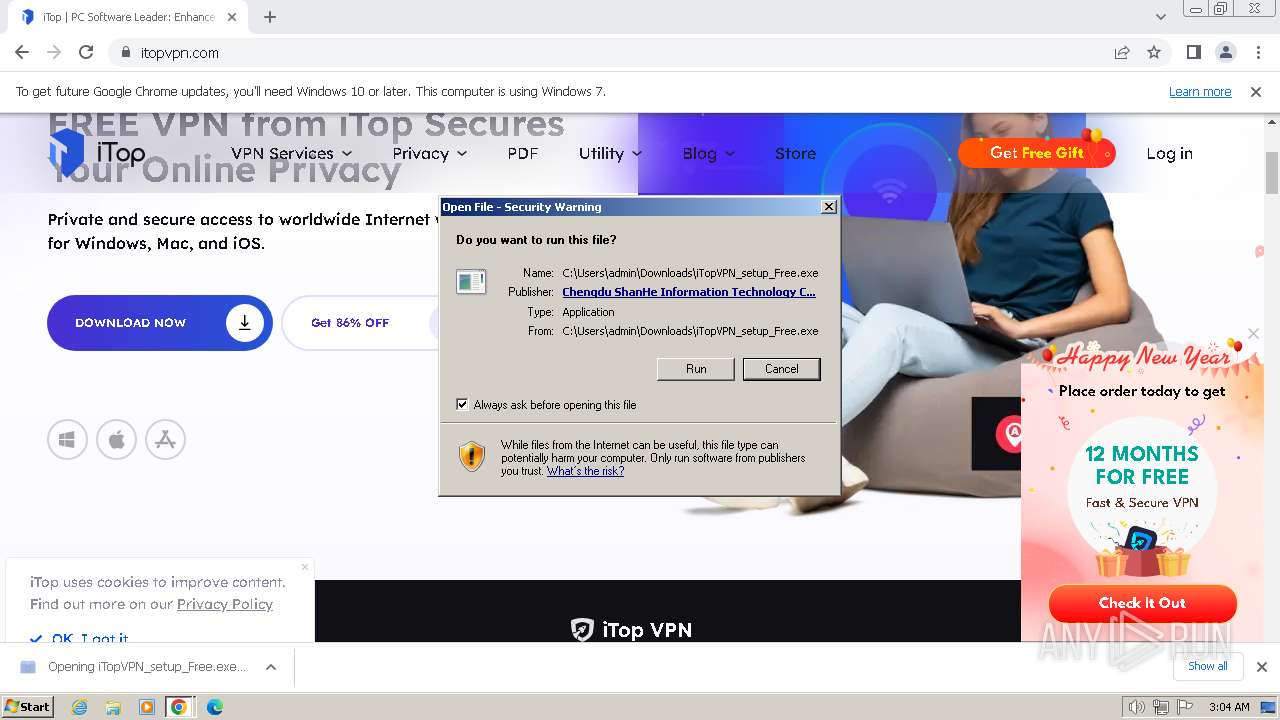
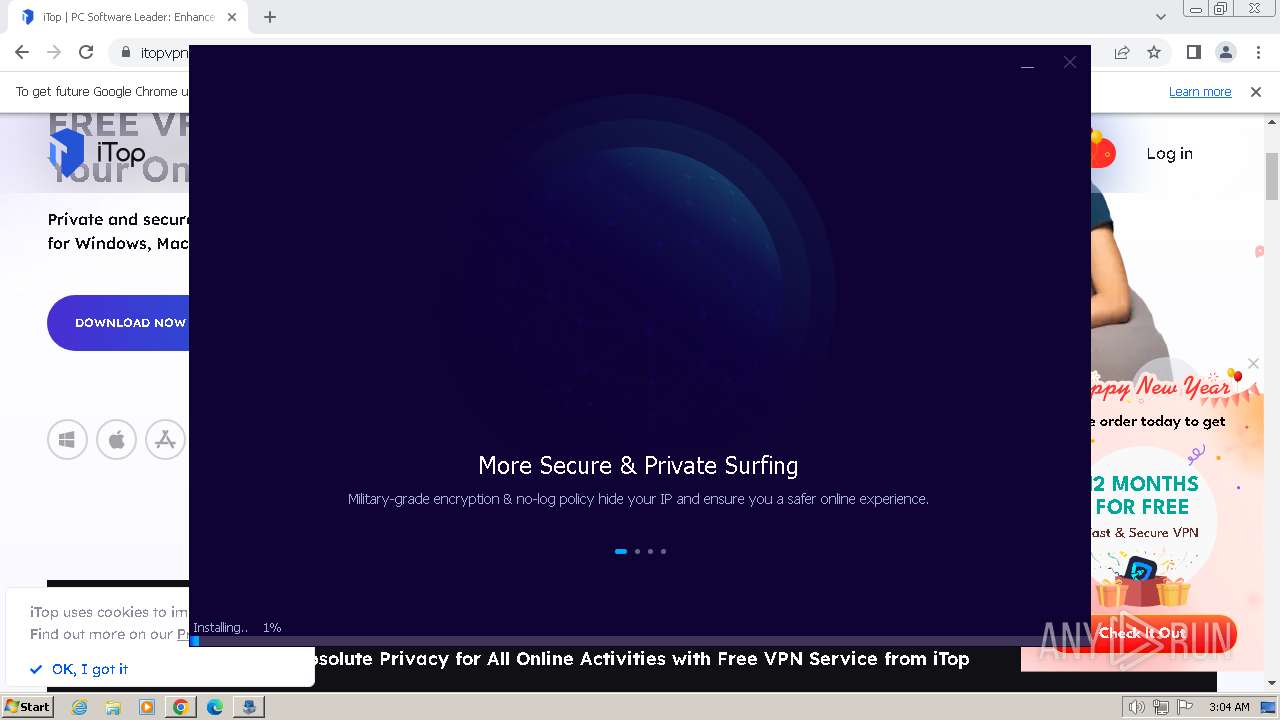
Drops the executable file immediately after the start
- chrome.exe (PID: 2184)
- iTopVPN_setup_Free.tmp (PID: 3696)
- iTopVPN_setup_Free.exe (PID: 3320)
- iTopVPN_setup_Free.exe (PID: 3744)
- iTopVPN_setup_Free.exe (PID: 4056)
- iTopVPN_setup_Free.tmp (PID: 4036)
- ugin.exe (PID: 1572)
- iTopDownloader.exe (PID: 1088)
- iTopDataRecovery.tmp (PID: 3088)
- iTopDataRecovery.exe (PID: 1644)
- chrome.exe (PID: 2148)
Checks supported languages
- iTopVPN_setup_Free.exe (PID: 3320)
- ugin.exe (PID: 3380)
- iTopVPN_setup_Free.tmp (PID: 2812)
- iTopVPN_setup_Free.exe (PID: 3744)
- iTopVPN_setup_Free.tmp (PID: 3696)
- iTopVPN_setup_Free.exe (PID: 4056)
- iTopVPN_setup_Free.tmp (PID: 4036)
- Setup.exe (PID: 3824)
- ugin.exe (PID: 120)
- ullc.exe (PID: 2172)
- iTopVPN.exe (PID: 1904)
- ugin.exe (PID: 1572)
- ugin.exe (PID: 148)
- icop32.exe (PID: 3944)
- ugin.exe (PID: 2300)
- ugin.exe (PID: 4080)
- ugin.exe (PID: 3564)
- unpr.exe (PID: 2540)
- ugin.exe (PID: 1192)
- iTopVPN.exe (PID: 2520)
- iTopDownloader.exe (PID: 1088)
- atud.exe (PID: 3012)
- aud.exe (PID: 3032)
- aud.exe (PID: 2796)
- iTopVPNMini.exe (PID: 3288)
- iTopDataRecovery.exe (PID: 1644)
- iTopDataRecovery.tmp (PID: 3088)
- LocalLang.exe (PID: 3688)
- iTopInsur.exe (PID: 3896)
- iTopInsur.exe (PID: 3856)
- IdrInit.exe (PID: 3696)
- IDRService.exe (PID: 2208)
- ICONPIN32.exe (PID: 572)
- UninstallInfo.exe (PID: 3876)
- Autoupdate.exe (PID: 2640)
- iTopDataRecovery.exe (PID: 2568)
- AUpdate.exe (PID: 920)
- AUpdate.exe (PID: 3980)
- Newfts.exe (PID: 2832)
- aud.exe (PID: 2152)
- iTopVPN.exe (PID: 2516)
Reads the computer name
- iTopVPN_setup_Free.tmp (PID: 2812)
- iTopVPN_setup_Free.tmp (PID: 3696)
- ugin.exe (PID: 3380)
- Setup.exe (PID: 3824)
- iTopVPN_setup_Free.tmp (PID: 4036)
- ugin.exe (PID: 120)
- ugin.exe (PID: 148)
- ugin.exe (PID: 1572)
- iTopVPN.exe (PID: 1904)
- ugin.exe (PID: 2300)
- ugin.exe (PID: 4080)
- ugin.exe (PID: 3564)
- unpr.exe (PID: 2540)
- ugin.exe (PID: 1192)
- iTopDownloader.exe (PID: 1088)
- iTopVPN.exe (PID: 2516)
- iTopVPN.exe (PID: 2520)
- aud.exe (PID: 2796)
- atud.exe (PID: 3012)
- aud.exe (PID: 3032)
- iTopVPNMini.exe (PID: 3288)
- iTopDataRecovery.tmp (PID: 3088)
- iTopInsur.exe (PID: 3896)
- IdrInit.exe (PID: 3696)
- iTopInsur.exe (PID: 3856)
- UninstallInfo.exe (PID: 3876)
- IDRService.exe (PID: 2208)
- iTopDataRecovery.exe (PID: 2568)
- Autoupdate.exe (PID: 2640)
- AUpdate.exe (PID: 3980)
- Newfts.exe (PID: 2832)
- aud.exe (PID: 2152)
- AUpdate.exe (PID: 920)
Create files in a temporary directory
- iTopVPN_setup_Free.exe (PID: 3744)
- iTopVPN_setup_Free.exe (PID: 3320)
- iTopVPN_setup_Free.tmp (PID: 3696)
- Setup.exe (PID: 3824)
- iTopVPN_setup_Free.exe (PID: 4056)
- iTopVPN_setup_Free.tmp (PID: 4036)
- icop32.exe (PID: 3944)
- explorer.exe (PID: 1164)
- iTopDataRecovery.tmp (PID: 3088)
- iTopDataRecovery.exe (PID: 1644)
- SecEdit.exe (PID: 2656)
- SecEdit.exe (PID: 3652)
- iTopVPN.exe (PID: 2520)
- ICONPIN32.exe (PID: 572)
The process uses the downloaded file
- chrome.exe (PID: 3148)
- chrome.exe (PID: 2184)
Process drops legitimate windows executable
- iTopVPN_setup_Free.tmp (PID: 3696)
- iTopVPN_setup_Free.tmp (PID: 4036)
- iTopDataRecovery.tmp (PID: 3088)
Application launched itself
- chrome.exe (PID: 2184)
- ugin.exe (PID: 1572)
Reads the machine GUID from the registry
- ugin.exe (PID: 3380)
- Setup.exe (PID: 3824)
- ugin.exe (PID: 1572)
- unpr.exe (PID: 2540)
- icop32.exe (PID: 3944)
- iTopVPN.exe (PID: 2520)
- iTopDownloader.exe (PID: 1088)
- aud.exe (PID: 2796)
- atud.exe (PID: 3012)
- aud.exe (PID: 3032)
- iTopVPNMini.exe (PID: 3288)
- ICONPIN32.exe (PID: 572)
- AUpdate.exe (PID: 3980)
- AUpdate.exe (PID: 920)
- aud.exe (PID: 2152)
Creates files or folders in the user directory
- ugin.exe (PID: 3380)
- iTopVPN_setup_Free.tmp (PID: 4036)
- iTopVPN.exe (PID: 1904)
- explorer.exe (PID: 1164)
- iTopVPN.exe (PID: 2520)
- atud.exe (PID: 3012)
- iTopVPNMini.exe (PID: 3288)
- iTopInsur.exe (PID: 3896)
- iTopDataRecovery.tmp (PID: 3088)
- Autoupdate.exe (PID: 2640)
Checks for external IP
- ugin.exe (PID: 3380)
- Setup.exe (PID: 3824)
- unpr.exe (PID: 2540)
- UninstallInfo.exe (PID: 3876)
Creates files in the program directory
- Setup.exe (PID: 3824)
- ugin.exe (PID: 3380)
- iTopVPN_setup_Free.tmp (PID: 4036)
- iTopVPN.exe (PID: 1904)
- ugin.exe (PID: 1572)
- unpr.exe (PID: 2540)
- ugin.exe (PID: 1192)
- iTopDownloader.exe (PID: 1088)
- iTopVPN.exe (PID: 2520)
- atud.exe (PID: 3012)
- iTopDataRecovery.tmp (PID: 3088)
- iTopInsur.exe (PID: 3896)
- UninstallInfo.exe (PID: 3876)
- iTopDataRecovery.exe (PID: 2568)
- AUpdate.exe (PID: 3980)
- Autoupdate.exe (PID: 2640)
- IDRService.exe (PID: 2208)
- Newfts.exe (PID: 2832)
Process drops SQLite DLL files
- iTopVPN_setup_Free.tmp (PID: 4036)
- iTopDataRecovery.tmp (PID: 3088)
Application was injected by another process
- explorer.exe (PID: 1164)
Process requests binary or script from the Internet
- iTopDownloader.exe (PID: 1088)
Connects to unusual port
- iTopVPN.exe (PID: 2520)
Process checks Internet Explorer phishing filters
- iTopVPN.exe (PID: 2520)
Process checks are UAC notifies on
- iTopVPN.exe (PID: 2520)
Executes as Windows Service
- IDRService.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
162
Monitored processes
103
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\AppData\Local\Temp\is-K0SPS.tmp\ugin.exe" /kill /UPGRADE | C:\Users\admin\AppData\Local\Temp\is-K0SPS.tmp\ugin.exe | — | iTopVPN_setup_Free.tmp | |||||||||||
User: admin Company: iTop Inc. Integrity Level: HIGH Description: iTop VPN Exit code: 0 Version: 5.0.0.5029 Modules
| |||||||||||||||
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e558b38,0x6e558b48,0x6e558b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 148 | "C:\Program Files\iTop VPN\ugin.exe" /kill /updagrade | C:\Program Files\iTop VPN\ugin.exe | — | iTopVPN_setup_Free.tmp | |||||||||||
User: admin Company: iTop Inc. Integrity Level: HIGH Description: iTop VPN Exit code: 0 Version: 5.0.0.5029 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1340 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 572 | "C:\Program Files\iTop Data Recovery\ICONPIN32.exe" Pin "C:\Program Files\iTop Data Recovery\iTopDataRecovery.exe" | C:\Program Files\iTop Data Recovery\ICONPIN32.exe | iTopDataRecovery.tmp | ||||||||||||
User: admin Company: iTop Inc. Integrity Level: HIGH Description: Icon Pin Exit code: 0 Version: 1.0.0.22 Modules
| |||||||||||||||
| 584 | sc start iTopDataRecoveryService4 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1512 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 876 | "C:\Windows\System32\cmd.exe" /c sc start iTopDataRecoveryService4 | C:\Windows\System32\cmd.exe | — | iTopDataRecovery.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 920 | "C:\Program Files\iTop Data Recovery\AUpdate.exe" /idr /dayactive | C:\Program Files\iTop Data Recovery\AUpdate.exe | iTopDataRecovery.exe | ||||||||||||
User: admin Company: iTop Inc. Integrity Level: HIGH Description: Common Component Exit code: 0 Version: 4.1.0.619 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\iTop VPN\iTopDownloader.exe" "/Config=https://update.itopvpn.com/infofiles/itop/freeware.upt" /product=ITOP3 "iTop Data Recovery Installer" | C:\Program Files\iTop VPN\iTopDownloader.exe | Setup.exe | ||||||||||||
User: admin Company: iTop Inc. Integrity Level: HIGH Description: iTop Downloader Exit code: 0 Version: 5.0.0.4754 Modules
| |||||||||||||||
Total events
47 092
Read events
46 718
Write events
348
Delete events
26
Modification events
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000DBDD10622BD67741A42163F361389C4700000000020000000000106600000001000020000000714C0B985B0540658F4A2080B484A48FEA0193B4945278E76DEADC9EF300F178000000000E80000000020000200000002B477AD6A48910EDA2BF44A8E4FAAFB7E2EDF3EE6F87B8965B303D8016BD90EA30000000CB02147CAA96DADF9F5A3BD08AC8A954F632048A3EC443FAA534C64E43A96953CAB4A202A2BC0443ADBC5B693897DBB44000000078BCD17E1DCD91E99A86D38616C049FA8C5E2A7C07BB269B76B0709DC8A01ABF25866BF6638D5C4422D1151CE173748901F5A2433E1BD07914E254B07BB130FD | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
273
Suspicious files
221
Text files
384
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe1009.TMP | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe18c3.TMP | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe13d2.TMP | text | |
MD5:8593E82FF8753DC10267243C51E8A91B | SHA256:FE9EE2D77D9EB5CBA707EDBCB7F1ABAA83418CDB66D66835B4B9A1B6CC5CC34F | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFe25c3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
522
DNS requests
71
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
548 | chrome.exe | GET | 204 | 142.250.186.99:80 | http://www.gstatic.com/generate_204 | unknown | — | — | unknown |
3824 | Setup.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | binary | 313 b | unknown |
— | — | GET | 200 | 152.199.20.140:80 | http://update.iobit.com/dl/img/inst/img_screenshot_idr.png | unknown | image | 75.7 Kb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | binary | 136 Kb | unknown |
3824 | Setup.exe | GET | 200 | 152.199.20.140:80 | http://update.iobit.com/infofiles/ac/appver-ac.upt | unknown | text | 848 b | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | binary | 6.14 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | binary | 9.84 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | binary | 9.87 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | binary | 9.82 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2184 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
548 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
548 | chrome.exe | 34.230.143.180:443 | stats.itopvpn.com | AMAZON-AES | US | unknown |
548 | chrome.exe | 142.250.181.228:443 | www.google.com | GOOGLE | US | whitelisted |
2184 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
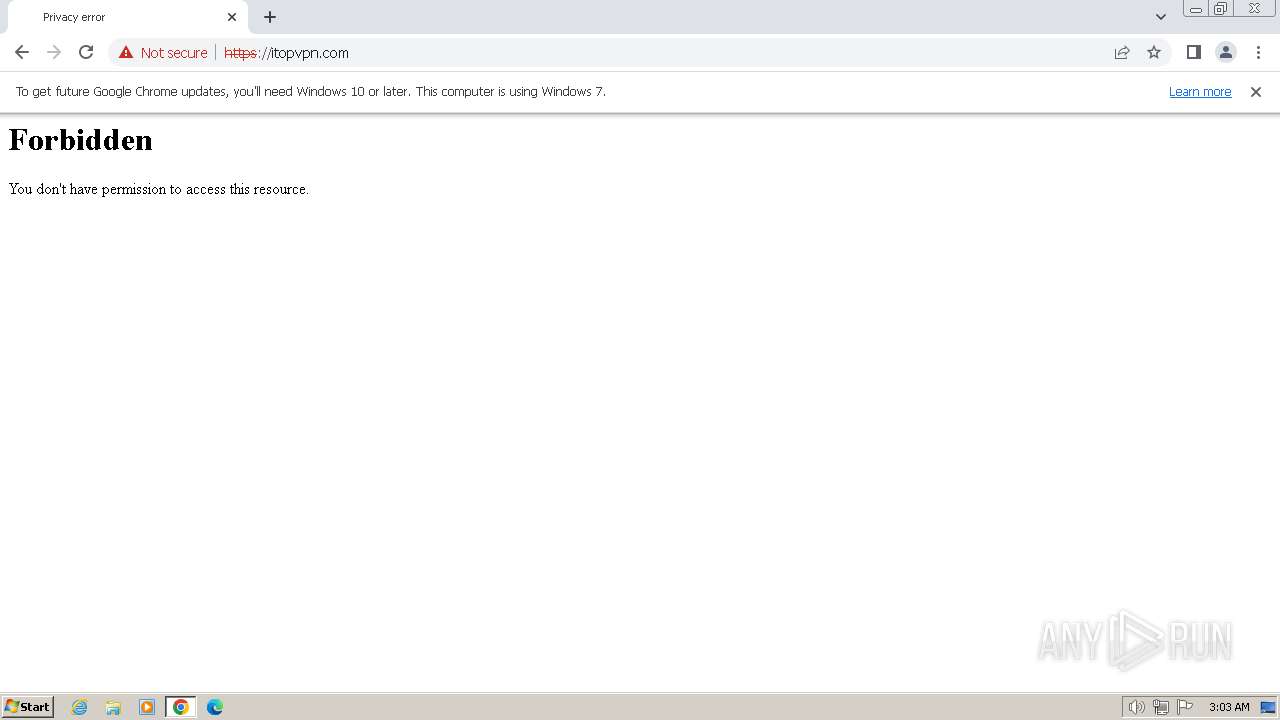
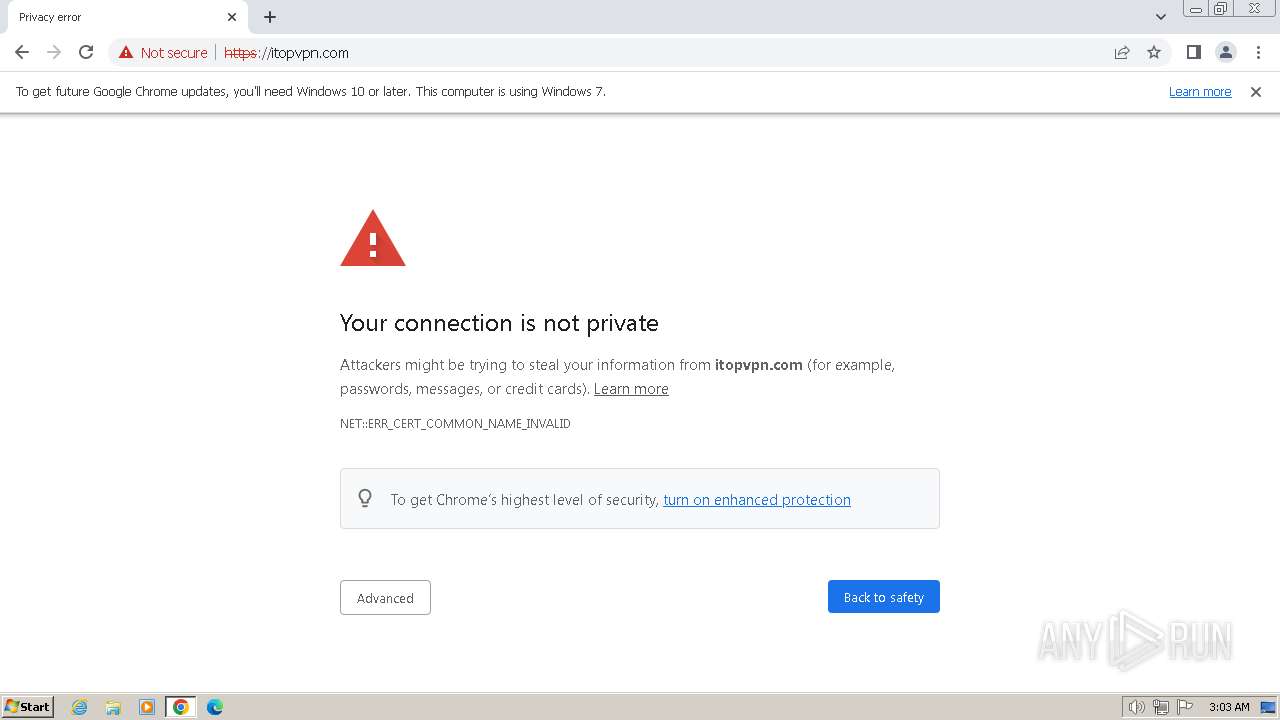
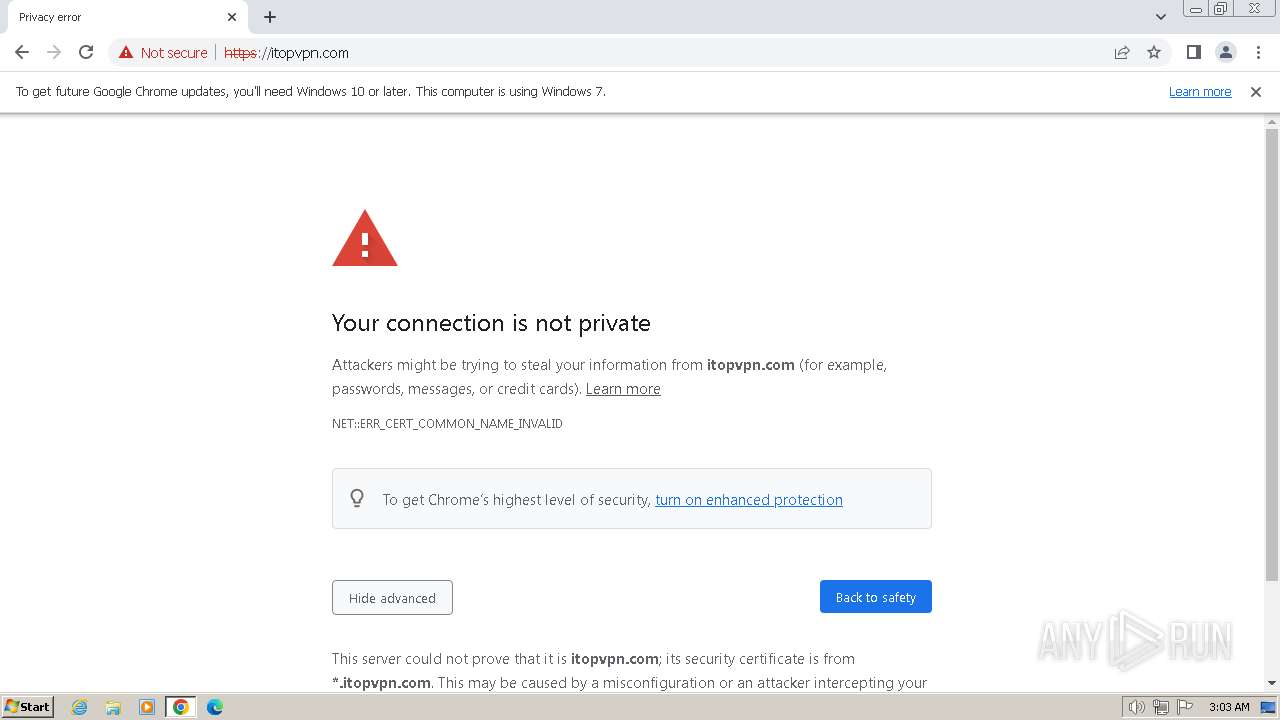
548 | chrome.exe | 54.204.76.172:443 | itopvpn.com | AMAZON-AES | US | unknown |
548 | chrome.exe | 142.250.186.99:80 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
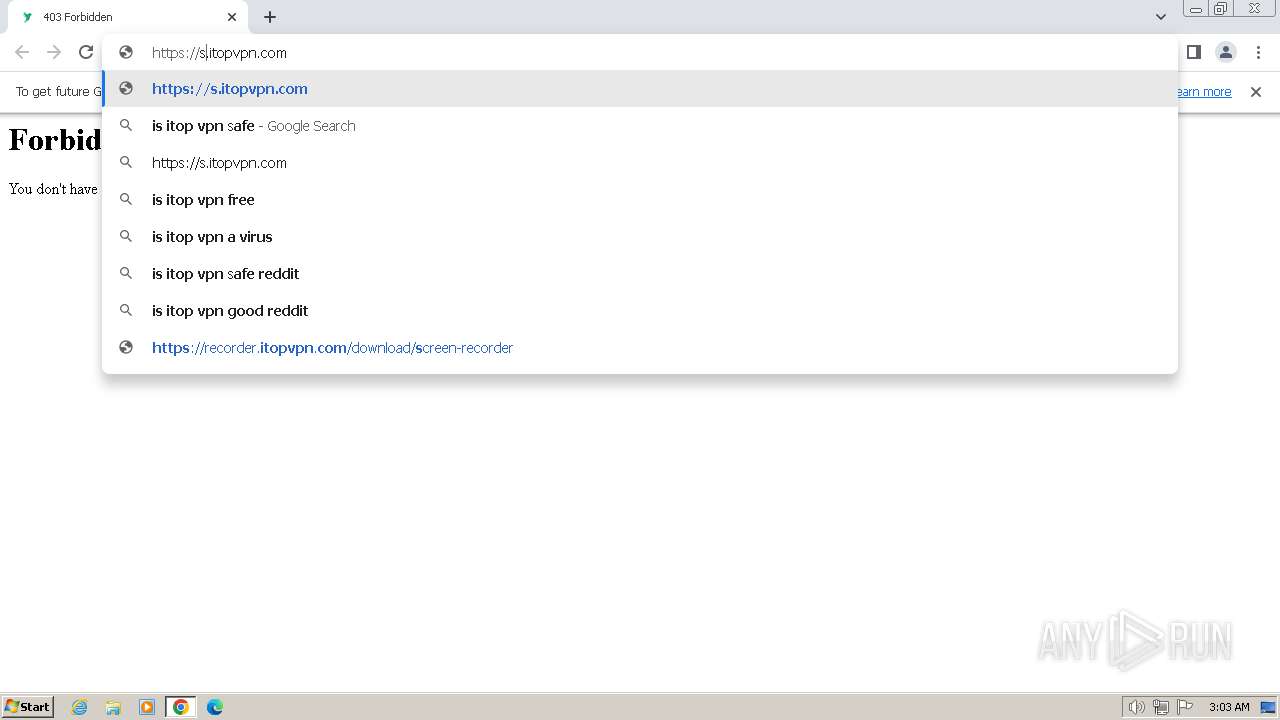
stats.itopvpn.com |
| unknown |
www.google.com |
| whitelisted |
itopvpn.com |
| malicious |
www.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
www.itopvpn.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | ugin.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3380 | ugin.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3380 | ugin.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3824 | Setup.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3824 | Setup.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3824 | Setup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3824 | Setup.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3824 | Setup.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
3824 | Setup.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
2540 | unpr.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
Process | Message |
|---|---|
Setup.exe | time1 |
Setup.exe | doFinshedEvent_Freeware 0 |
Setup.exe | time3 |
Setup.exe | Order: isr |
Setup.exe | chk_os_ver 110;100;63;62;61 |
Setup.exe | CheckLicense |
Setup.exe | Chk_ver_min |
Setup.exe | WinVer 61 |
Setup.exe | chk_arch |
Setup.exe | ProductVersion: 5.2.0.5033 |