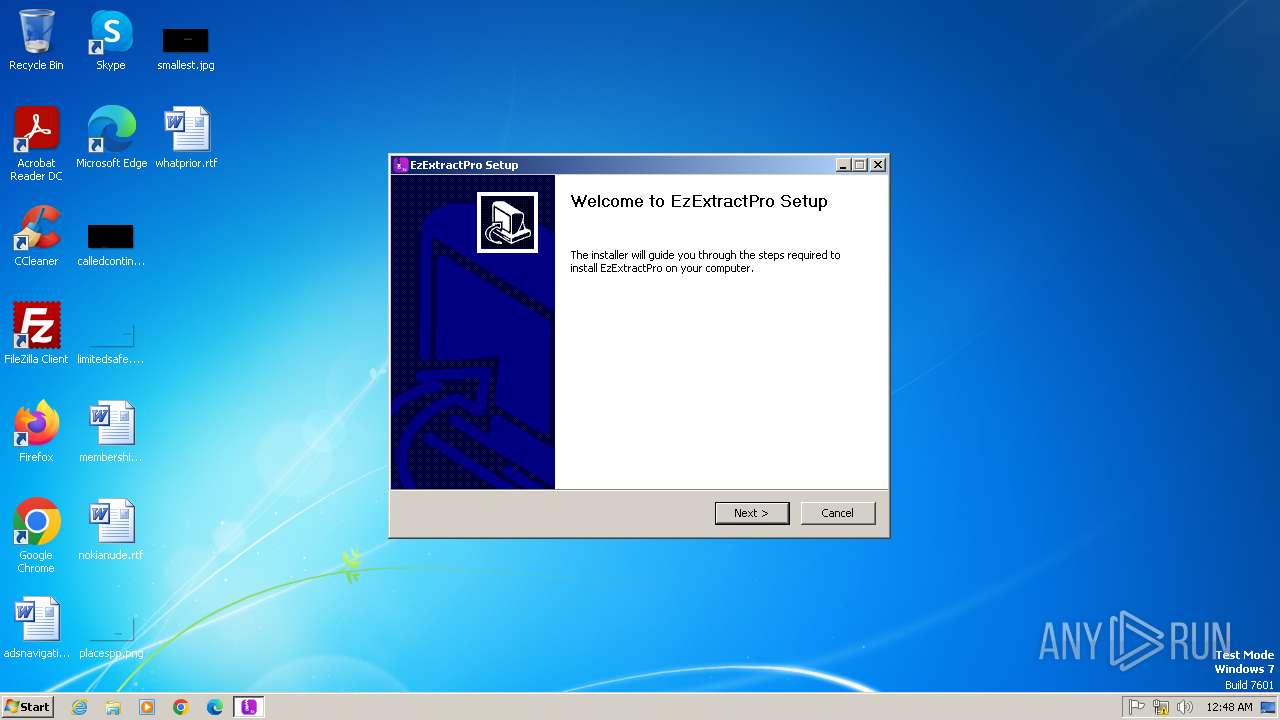
| File name: | EzExtractSetup.exe |
| Full analysis: | https://app.any.run/tasks/87479bfc-73bf-4679-bd19-a9a22ba93852 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 00:47:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 7399EBE1E1B9C99F3CB4A2521D424384 |
| SHA1: | 7A560782421FEB72B1E84F162CF0ABD0809FDA28 |
| SHA256: | 4704846C5605552A2573AEB62F176630FD2BA5498457420C3FB36A27CAE6800F |
| SSDEEP: | 98304:QBXfMTSPotXjLlZa6XloPaUP0KsdzGP5shhrLAvKxKEczZRNNYyWs0CbXnoGAyvp:QioCUm5m |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- EzExtractSetup.exe (PID: 2568)
Reads the Internet Settings
- EzExtractSetup.exe (PID: 2568)
Reads security settings of Internet Explorer
- EzExtractSetup.exe (PID: 2568)
Reads settings of System Certificates
- EzExtractSetup.exe (PID: 2568)
The process creates files with name similar to system file names
- EzExtractSetup.exe (PID: 2568)
Malware-specific behavior (creating "System.dll" in Temp)
- EzExtractSetup.exe (PID: 2568)
Adds/modifies Windows certificates
- EzExtractSetup.exe (PID: 2568)
There is functionality for taking screenshot (YARA)
- EzExtractSetup.exe (PID: 2568)
INFO
The sample compiled with english language support
- EzExtractSetup.exe (PID: 2568)
Reads the computer name
- EzExtractSetup.exe (PID: 2568)
Checks supported languages
- EzExtractSetup.exe (PID: 2568)
Create files in a temporary directory
- EzExtractSetup.exe (PID: 2568)
Reads the machine GUID from the registry
- EzExtractSetup.exe (PID: 2568)
Checks proxy server information
- EzExtractSetup.exe (PID: 2568)
Reads the software policy settings
- EzExtractSetup.exe (PID: 2568)
Creates files or folders in the user directory
- EzExtractSetup.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:58:45+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3665 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Empire Security Services Inc |
| FileDescription: | EzExtractPro |
| FileVersion: | 1.0.0.1 |
| LegalCopyright: | Copyright © Empire Security Services Inc 2024 |
| ProductName: | EzExtractPro |
| ProductVersion: | 1.0.0.1 |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | "C:\Users\admin\AppData\Local\Temp\EzExtractSetup.exe" | C:\Users\admin\AppData\Local\Temp\EzExtractSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: HIGH Description: EzExtractPro Version: 1.0.0.1 Modules
| |||||||||||||||
| 2812 | "C:\Users\admin\AppData\Local\Temp\EzExtractSetup.exe" | C:\Users\admin\AppData\Local\Temp\EzExtractSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: MEDIUM Description: EzExtractPro Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
5 042
Read events
4 998
Write events
36
Delete events
8
Modification events
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2568) EzExtractSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
Executable files
4
Suspicious files
6
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:1DE4F3BD4535ECB70B20056F8DAD96BC | SHA256:087557CE8722F7590D493E2696874FC14DE93C4969F90641A44D84251B3EA47D | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\Local\Temp\nsm1FAA.tmp\INetC.dll | executable | |
MD5:40D7ECA32B2F4D29DB98715DD45BFAC5 | SHA256:85E03805F90F72257DD41BFDAA186237218BBB0EC410AD3B6576A88EA11DCCB9 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:971C514F84BBA0785F80AA1C23EDFD79 | SHA256:F157ED17FCAF8837FA82F8B69973848C9B10A02636848F995698212A08F31895 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:C9BE626E9715952E9B70F92F912B9787 | SHA256:C13E8D22800C200915F87F71C31185053E4E60CA25DE2E41E160E09CD2D815D4 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:E7C4B5152A734AE17D25B6DFC5C697B4 | SHA256:8800232D1F4020BFDAF6D7FDE2BF6170F4A8426DF2146E0FDC262F1B53E267DB | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\Local\Temp\nsm1FAA.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\Local\Temp\nsm1FAA.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\Local\Temp\nsm1FAA.tmp\NsisPlugin.dll | executable | |
MD5:1D0E98E6817A35237509731E1398B47A | SHA256:23ABC9395B36419700F31B507F13A189EC2EEB70C7E1A1FE9406C2B9E0728298 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 2568 | EzExtractSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EDAE10D6B052B658231BEAB6EC8CE2C5 | SHA256:9076AFF4F12547AC79CF8411DD44F5F6CF4E6917BE82889DCBDABA1E7AB5F431 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | EzExtractSetup.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
2568 | EzExtractSetup.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?62ef0279b4e2d3c9 | unknown | — | — | whitelisted |
2568 | EzExtractSetup.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2568 | EzExtractSetup.exe | 104.21.32.2:443 | ezextractinstaller.com | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2568 | EzExtractSetup.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2568 | EzExtractSetup.exe | 142.250.186.35:80 | c.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ezextractinstaller.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
c.pki.goog |
| whitelisted |