| File name: | suf_launch.exe |
| Full analysis: | https://app.any.run/tasks/9976d5b8-3a08-492e-a15a-8b75fc846953 |
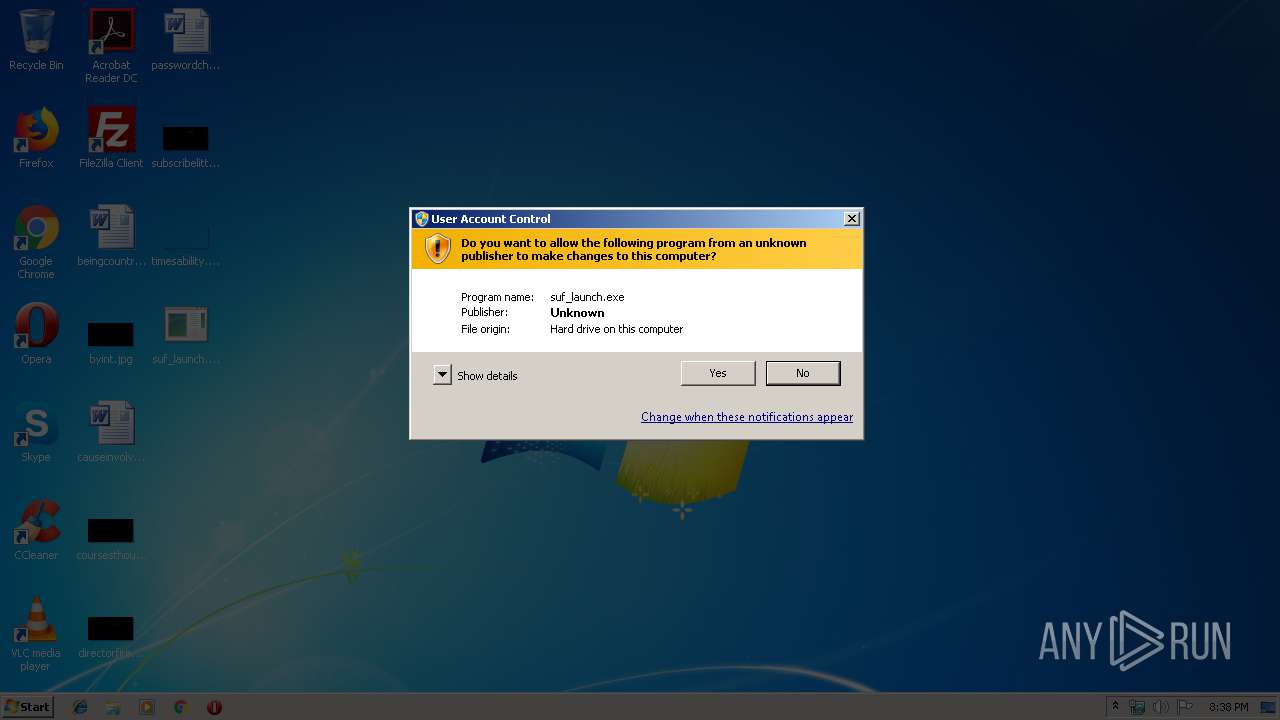
| Verdict: | Suspicious activity |
| Analysis date: | October 03, 2019, 19:38:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A454B78F52609AAB042F943A266C099B |
| SHA1: | 6BF0586BA79347E2172E237150FB5B4820462D46 |
| SHA256: | 46FC04DF059E804388AE01B0C821FE287B125D292F2F87B513021DDB92AE4903 |
| SSDEEP: | 98304:lIW02lqngV40/8ECCY6Y+iCcVSOqwEf6ZaLnUFtsOWV5CsQ88xKhp2OmuhNkze:lf1V40/8EyaiCgDEfKabisznpQBxKhPp |
MALICIOUS
Loads dropped or rewritten executable
- irsetup.exe (PID: 2832)
Application was dropped or rewritten from another process
- irsetup.exe (PID: 2832)
SUSPICIOUS
Executable content was dropped or overwritten
- suf_launch.exe (PID: 3552)
- irsetup.exe (PID: 2832)
Creates files in the program directory
- irsetup.exe (PID: 2832)
INFO
Dropped object may contain Bitcoin addresses
- irsetup.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:03 20:13:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 23552 |
| InitializedDataSize: | 48128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ce1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Created by PK2 |
| CompanyName: | packing case |
| FileDescription: | PATCH Application |
| FileVersion: | 3.0.0.0 |
| InternalName: | sf_rt |
| LegalCopyright: | pk2 |
| LegalTrademarks: | none |
| OriginalFileName: | suf_launch.exe |
| ProductName: | SetupRuntime |
| ProductVersion: | 3.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jan-2019 19:13:08 |
| Detected languages: |
|
| Comments: | Created by PK2 |
| CompanyName: | packing case |
| FileDescription: | PATCH Application |
| FileVersion: | 3.0.0.0 |
| InternalName: | sf_rt |
| LegalCopyright: | pk2 |
| LegalTrademarks: | none |
| OriginalFilename: | suf_launch.exe |
| ProductName: | SetupRuntime |
| ProductVersion: | 3.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jan-2019 19:13:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A18 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40733 |
.rdata | 0x00007000 | 0x00002F54 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05968 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59807 |
.rsrc | 0x0000C000 | 0x00006DC0 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.84528 |
.reloc | 0x00013000 | 0x000010D0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.81847 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3701 | 1425 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.31421 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.9477 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.78233 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.14953 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.83714 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.64397 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.84115 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.41049 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.89097 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2832 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1798178 "__IRAFN:C:\Users\admin\Desktop\suf_launch.exe" "__IRCT:3" "__IRTSS:0" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | suf_launch.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.3.0 Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\Desktop\suf_launch.exe" | C:\Users\admin\Desktop\suf_launch.exe | explorer.exe | ||||||||||||
User: admin Company: packing case Integrity Level: HIGH Description: PATCH Application Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3864 | "C:\Users\admin\Desktop\suf_launch.exe" | C:\Users\admin\Desktop\suf_launch.exe | — | explorer.exe | |||||||||||
User: admin Company: packing case Integrity Level: MEDIUM Description: PATCH Application Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
437
Read events
433
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3552) suf_launch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3552) suf_launch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
22
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 3552 | suf_launch.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:75835693ADEA59A592A81D0A899C2C1B | SHA256:566A66E5A5A02AD894D13C48FE0B46AFF92BC92BD892CBA30E1DDB149BE5E8BA | |||
| 2832 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\Labcenter Electronics Setup Log.txt | text | |
MD5:— | SHA256:— | |||
| 3552 | suf_launch.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\lua5.1.dll | executable | |
MD5:80D93D38BADECDD2B134FE4699721223 | SHA256:C572A6103AF1526F97E708A229A532FD02100A52B949F721052107F1F55E0C59 | |||
| 2832 | irsetup.exe | C:\Program Files\Labcenter Electronics\Proteus 8 Professional\BIN\LICENCE.DLL | executable | |
MD5:24B57D06E2004223DBE7B0572BCEBB5C | SHA256:DB3685A08BFF1BFCB4B0E9431957463439B341B69D0C7A8BC9A1813126C01B17 | |||
| 2832 | irsetup.exe | C:\Program Files\Labcenter Electronics\Proteus 8 Professional\BIN\PROSPICE.DLL | executable | |
MD5:51F82516677FBAAF736FF862C055CA41 | SHA256:688F70D824B102AB54B9E82C99DB466AA81B33259B435EB77679D78AD5CAE349 | |||
| 2832 | irsetup.exe | C:\Program Files\Labcenter Electronics\Proteus 8 Professional\MODELS\LEDMPX.DLL | executable | |
MD5:FBA4C9D8FDADD245BC3EF95054A55C18 | SHA256:078A3A26C48656C9636462E1998B8897E9E71FCAB0740E6FB24961672458F0BC | |||
| 2832 | irsetup.exe | C:\Program Files\Labcenter Electronics\Proteus 8 Professional\BIN\ISIS.DLL | executable | |
MD5:F9BDCDCA6E524D0696B11AB1261135E8 | SHA256:FBB54560E891C4A606C51DBCA8EC01A93582B018BEE8C6A3FD4F10D657ECD911 | |||
| 2832 | irsetup.exe | C:\Program Files\Labcenter Electronics\Proteus 8 Professional\MODELS\i8086.DLL | executable | |
MD5:BC4C36C05AAAB34C3E6B7C1C2F343C50 | SHA256:581A2081B6072D11232A7C01AF151CE1E1EE1A273AA5A36540B8FBB231F7CD39 | |||
| 2832 | irsetup.exe | C:\Program Files\Labcenter Electronics\Proteus 8 Professional\MODELS\LCDALPHA.DLL | executable | |
MD5:6D92BA7958426C9C1878413B5641B369 | SHA256:BA8A830B7DF9C1D3AE2F88FCD4E003C91570B438545ED64B8D6E0156312B9C76 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report