| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/f1a5737c-f126-4431-9f97-b7c7fd15db48 |
| Verdict: | Malicious activity |
| Analysis date: | September 01, 2024, 10:20:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 23ABC43BA1CF8C1B721681A3314C3722 |
| SHA1: | 4D5746D41E91AA39963E531C8EBD5D2C17DCD082 |
| SHA256: | 46E5AFB96A092307725EB4503480ED4C894168884474DF01B5A679BDAE7E3E5E |
| SSDEEP: | 98304:t+cD4dn6oCsC5qTfrZl0Cd/WwgVL1yfbIxVQHJdebCxKjme14QLDAaDepVVQ3OSr:gRp9YN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- setup.exe (PID: 5720)
- setup.exe (PID: 252)
- setup.tmp (PID: 2580)
Reads security settings of Internet Explorer
- setup.tmp (PID: 5548)
- StartMenuExperienceHost.exe (PID: 2132)
Reads the date of Windows installation
- setup.tmp (PID: 5548)
- StartMenuExperienceHost.exe (PID: 2132)
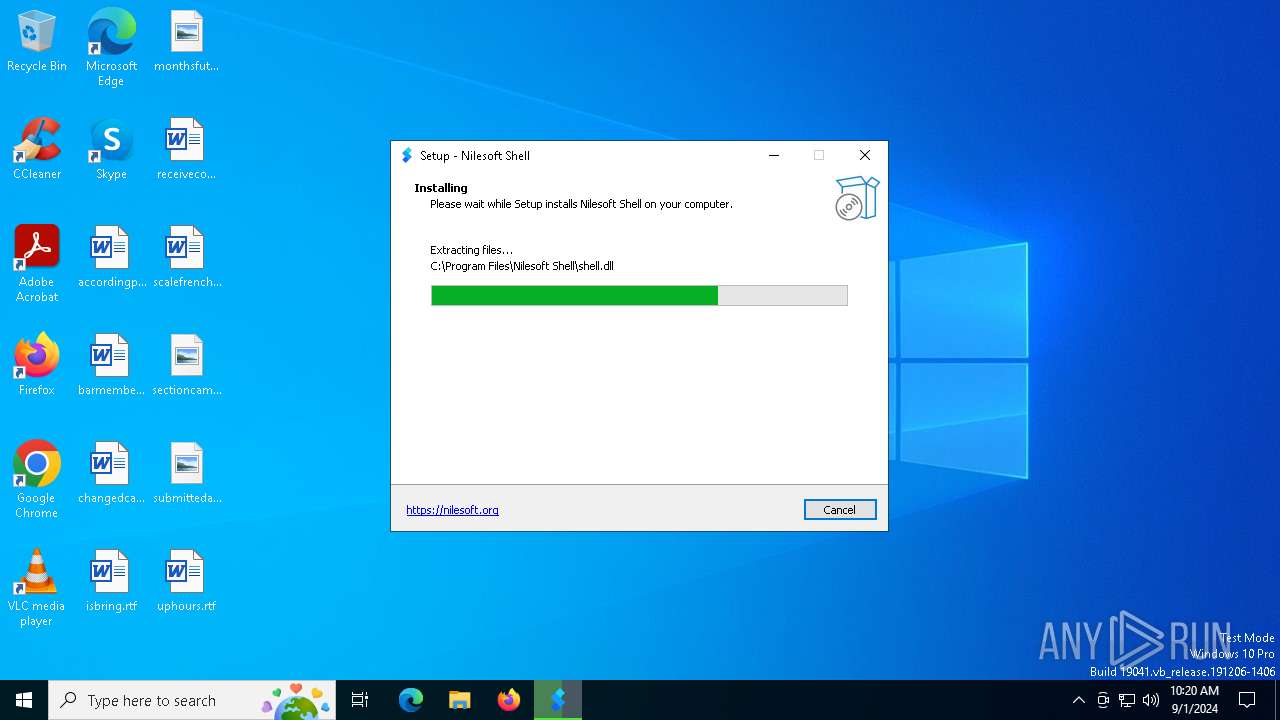
Executable content was dropped or overwritten
- setup.exe (PID: 5720)
- setup.exe (PID: 252)
- setup.tmp (PID: 2580)
Reads the Windows owner or organization settings
- setup.tmp (PID: 2580)
Creates/Modifies COM task schedule object
- shell.exe (PID: 7144)
INFO
Create files in a temporary directory
- setup.exe (PID: 5720)
- setup.exe (PID: 252)
- setup.tmp (PID: 2580)
Checks supported languages
- setup.tmp (PID: 5548)
- setup.exe (PID: 5720)
- setup.exe (PID: 252)
- setup.tmp (PID: 2580)
- _setup64.tmp (PID: 7016)
- TextInputHost.exe (PID: 2224)
- shell.exe (PID: 7144)
- StartMenuExperienceHost.exe (PID: 2132)
- SearchApp.exe (PID: 2268)
Process checks computer location settings
- setup.tmp (PID: 5548)
- StartMenuExperienceHost.exe (PID: 2132)
- SearchApp.exe (PID: 2268)
Reads the computer name
- setup.tmp (PID: 5548)
- setup.tmp (PID: 2580)
- TextInputHost.exe (PID: 2224)
- StartMenuExperienceHost.exe (PID: 2132)
- SearchApp.exe (PID: 2268)
Creates files in the program directory
- setup.tmp (PID: 2580)
- shell.exe (PID: 7144)
Creates a software uninstall entry
- setup.tmp (PID: 2580)
The process uses the downloaded file
- setup.tmp (PID: 5548)
Reads product name
- shell.exe (PID: 7144)
Reads Environment values
- shell.exe (PID: 7144)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 2268)
Reads the software policy settings
- SearchApp.exe (PID: 2268)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 2268)
Checks proxy server information
- SearchApp.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.9.15.0 |
| ProductVersionNumber: | 1.9.15.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Nilesoft |
| FileDescription: | Nilesoft Shell Setup |
| FileVersion: | 1.9.15 |
| LegalCopyright: | 2024 © Nilesoft Ltd. |
| OriginalFileName: | nilesoft-shell.exe |
| ProductName: | Nilesoft Shell |
| ProductVersion: | 1.9.15 |
Total processes
141
Monitored processes
12
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Users\admin\AppData\Local\Temp\setup.exe" /SPAWNWND=$604DA /NOTIFYWND=$8039A | C:\Users\admin\AppData\Local\Temp\setup.exe | setup.tmp | ||||||||||||
User: admin Company: Nilesoft Integrity Level: HIGH Description: Nilesoft Shell Setup Exit code: 0 Version: 1.9.15 Modules
| |||||||||||||||
| 2132 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2224 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2268 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\is-U8CI1.tmp\setup.tmp" /SL5="$1504DE,2893195,815616,C:\Users\admin\AppData\Local\Temp\setup.exe" /SPAWNWND=$604DA /NOTIFYWND=$8039A | C:\Users\admin\AppData\Local\Temp\is-U8CI1.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Company: Nilesoft Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 4820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _setup64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "C:\Users\admin\AppData\Local\Temp\is-IT6D0.tmp\setup.tmp" /SL5="$8039A,2893195,815616,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-IT6D0.tmp\setup.tmp | — | setup.exe | |||||||||||
User: admin Company: Nilesoft Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 5720 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Nilesoft Integrity Level: MEDIUM Description: Nilesoft Shell Setup Exit code: 0 Version: 1.9.15 Modules
| |||||||||||||||
| 6248 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6764 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 917
Read events
22 817
Write events
87
Delete events
13
Modification events
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 140A0000251A3A8A58FCDA01 | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2472926F8F0A36AAB32F3797CF6193C020F5D224972AA8D3DF6AFCEE168B5E47 | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Nilesoft Shell\shell.dll | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 29F2B809A9F8D57E3AF2EEE4A72440290548D835F8B759FC23FDA9832AD82AB4 | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A5E0BCAC-2748-424B-81E8-4481FF33F479}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A5E0BCAC-2748-424B-81E8-4481FF33F479}_is1 |
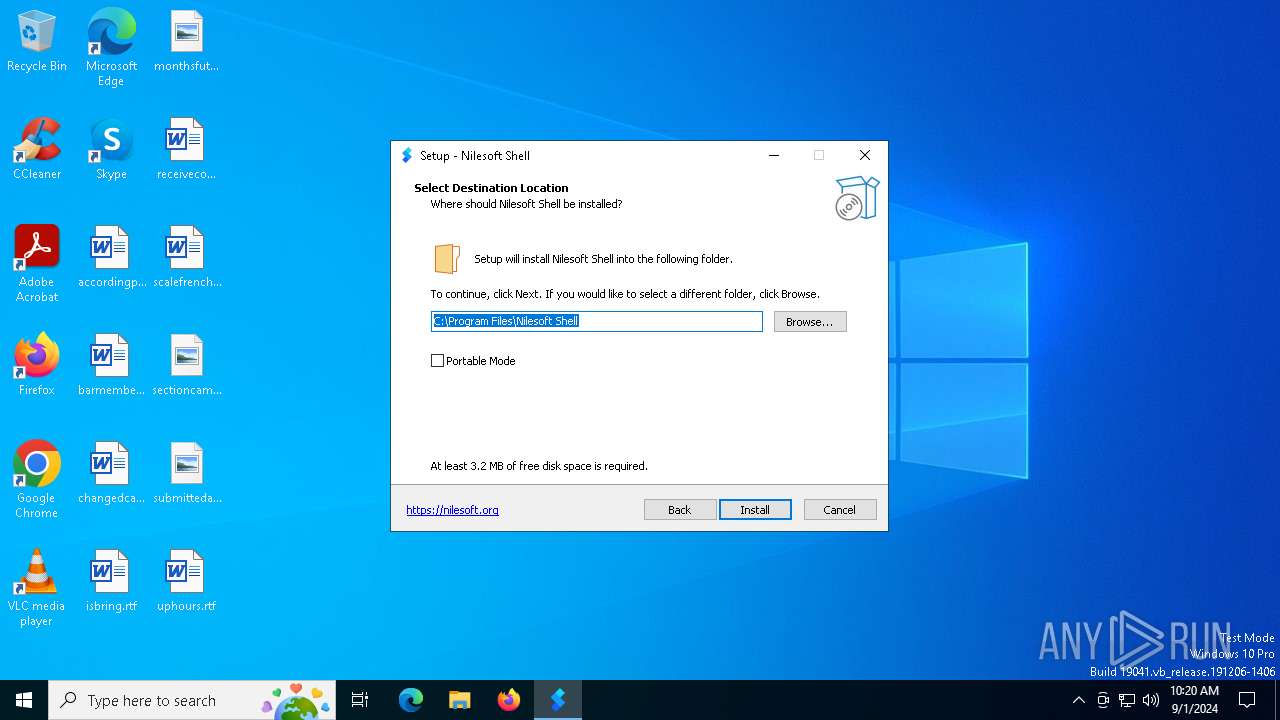
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Nilesoft Shell | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A5E0BCAC-2748-424B-81E8-4481FF33F479}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Nilesoft Shell\ | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A5E0BCAC-2748-424B-81E8-4481FF33F479}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (2580) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A5E0BCAC-2748-424B-81E8-4481FF33F479}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
10
Suspicious files
63
Text files
212
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 252 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-U8CI1.tmp\setup.tmp | executable | |
MD5:E5E62F35D7DE252D0970DE6798B3288D | SHA256:09BA3AE548980417E18D01603F055FFE2EF769EAACA2BECA1B33A73AD5D041A4 | |||
| 2580 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GA99B.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\imports\is-3Q5CB.tmp | text | |
MD5:64071E0ADE07C9476AFB2ECF8F2FB4D7 | SHA256:CE2C52D60B517834453E7D9C0AE17C9AF0FA52E05BC6DBBF22E699135DFF3D58 | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\unins000.exe | executable | |
MD5:41CF42C9C010C315F32AB252A2F2C471 | SHA256:FA6DC4295B9996C6FDE83E45B4E33EB29CC7642ADB843FA242AC4A21D3084E98 | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\shell.exe | executable | |
MD5:FCA624D8AF2D9364398CAA0942D8E8EB | SHA256:BA90226F2FBDC36B96ACE0BCB4C9A430D7F04CC99F543044D27F75C63B9214A5 | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\is-467QR.tmp | executable | |
MD5:FCA624D8AF2D9364398CAA0942D8E8EB | SHA256:BA90226F2FBDC36B96ACE0BCB4C9A430D7F04CC99F543044D27F75C63B9214A5 | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\is-G43UJ.tmp | executable | |
MD5:DA93AC965678492D790D9DCF378B96FC | SHA256:D101213256583C6730F9F4FDFD7C9E43EB73C6A1317B5522E2178C79E0FE0A60 | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\is-DPFOC.tmp | text | |
MD5:DF1AC2C455F3874D10470D5A49B12057 | SHA256:B7BA000E80F1F40991884CA63C9305E05D1EA5EFABBDEBC524D1E0779B84C2CF | |||
| 2580 | setup.tmp | C:\Program Files\Nilesoft Shell\imports\develop.nss | text | |
MD5:64071E0ADE07C9476AFB2ECF8F2FB4D7 | SHA256:CE2C52D60B517834453E7D9C0AE17C9AF0FA52E05BC6DBBF22E699135DFF3D58 | |||
| 5720 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-IT6D0.tmp\setup.tmp | executable | |
MD5:E5E62F35D7DE252D0970DE6798B3288D | SHA256:09BA3AE548980417E18D01603F055FFE2EF769EAACA2BECA1B33A73AD5D041A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
34
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7056 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7056 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2268 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6160 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2032 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4324 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6160 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |