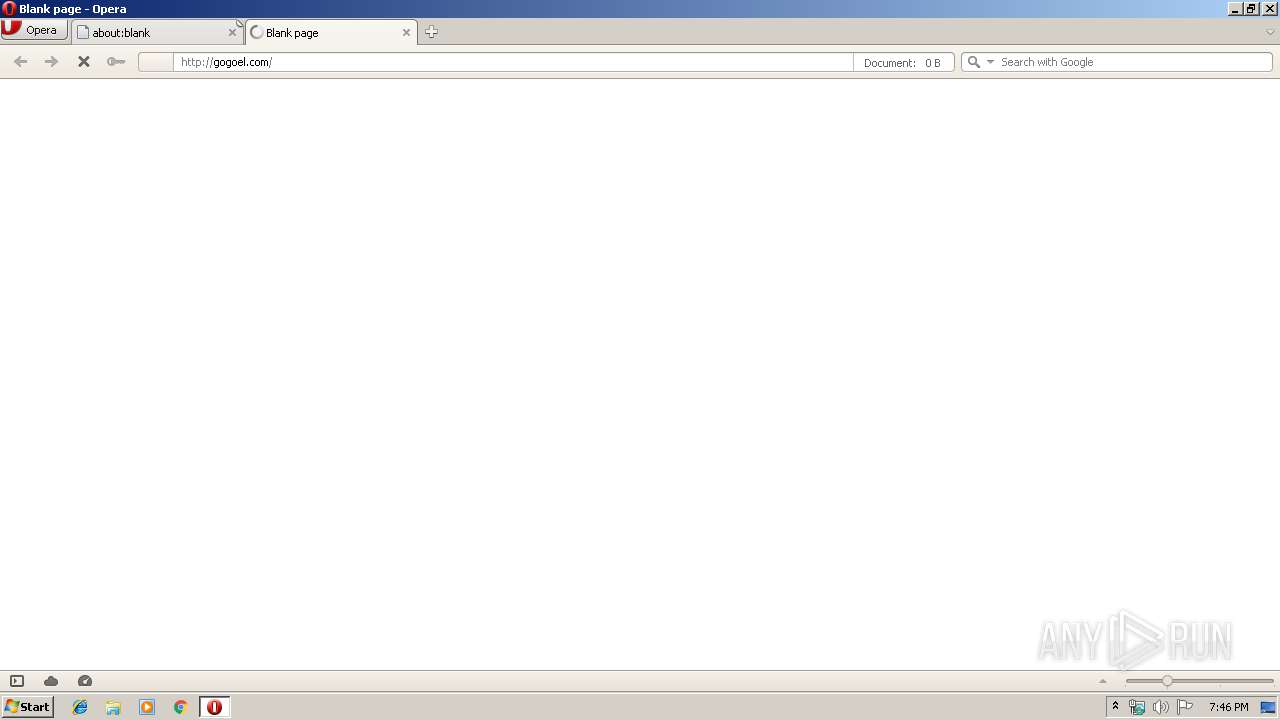
| URL: | http://gogoel.com |
| Full analysis: | https://app.any.run/tasks/f7582669-9641-4b05-9b07-09712daa88de |
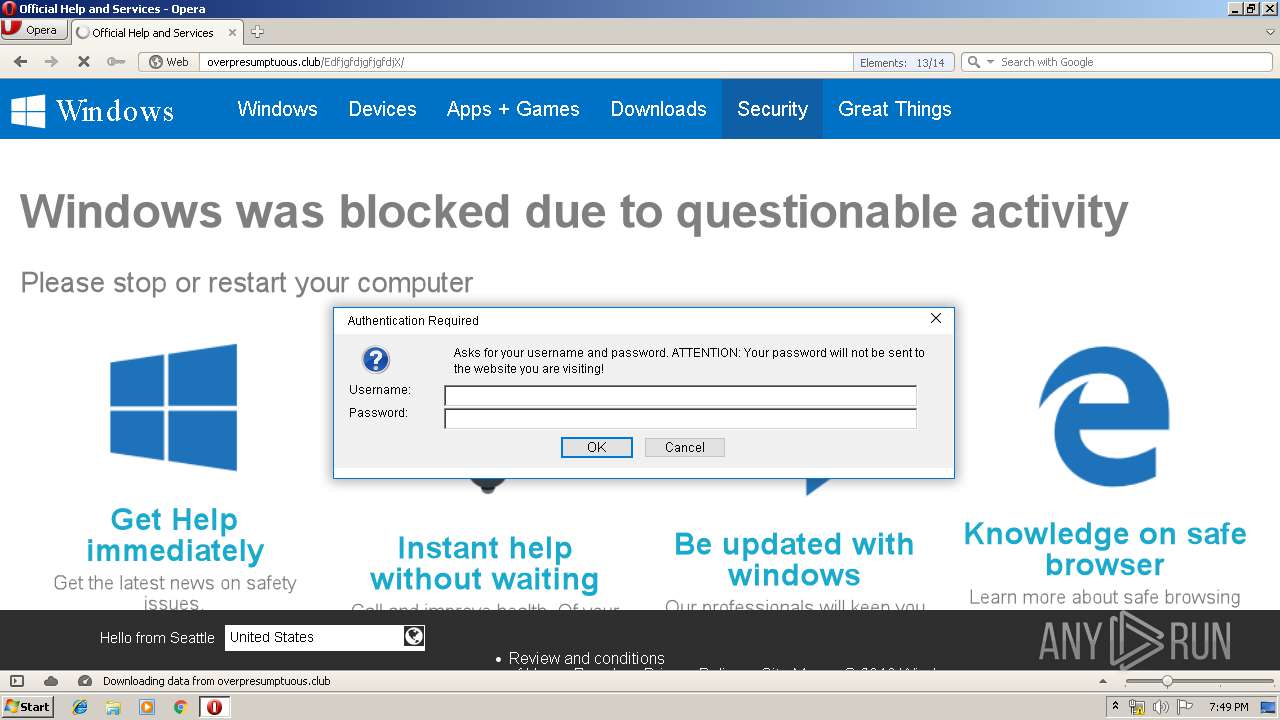
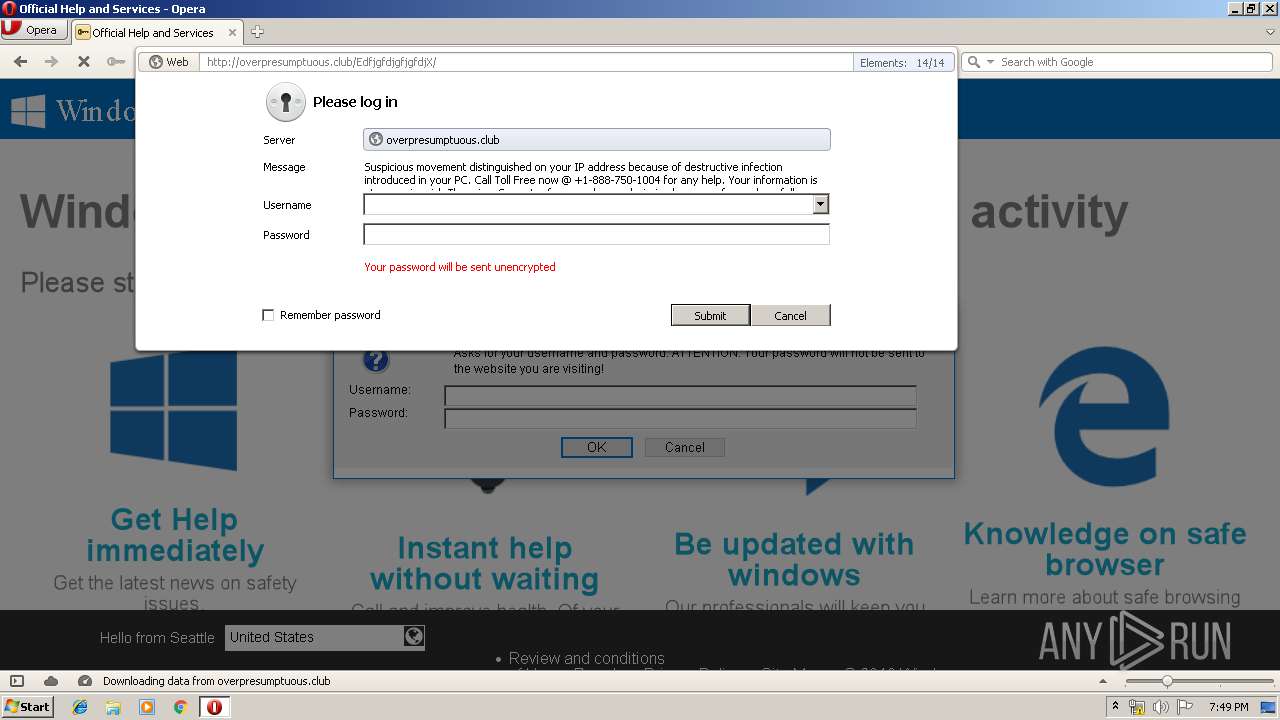
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2019, 18:46:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5300D2CAAE6BFD59B60E378B2E1BAB82 |
| SHA1: | 54638CF0A1B8C8D1BF6FE1082F062A546AE1FAFF |
| SHA256: | 46DECE07444062271032A2B2E9D5FCEFC9689C1C3145915AE14E0C5216FD0AD4 |
| SSDEEP: | 3:N1KZKDn:C0Dn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 4048)
- chrome.exe (PID: 964)
Application launched itself
- chrome.exe (PID: 4048)
Manual execution by user
- chrome.exe (PID: 4048)
Creates files in the user directory
- opera.exe (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8409550613068163289 --mojo-platform-channel-handle=3280 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11171336538571649533 --mojo-platform-channel-handle=1564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5107405163145125484 --mojo-platform-channel-handle=2476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1352050684018012798 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x67ffa9d0,0x67ffa9e0,0x67ffa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Opera\opera.exe" "http://gogoel.com" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5909239256257479632 --mojo-platform-channel-handle=2944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4864456662681767369 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5542281864279770265 --mojo-platform-channel-handle=1100 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,849931790201354233,1093460541434413396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5619825962862760446 --mojo-platform-channel-handle=3124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
889
Read events
753
Write events
132
Delete events
4
Modification events
| (PID) Process: | (2416) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "http://gogoel.com" | |||
| (PID) Process: | (2416) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4048-13216243813914093 |
Value: 259 | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
0
Suspicious files
82
Text files
108
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
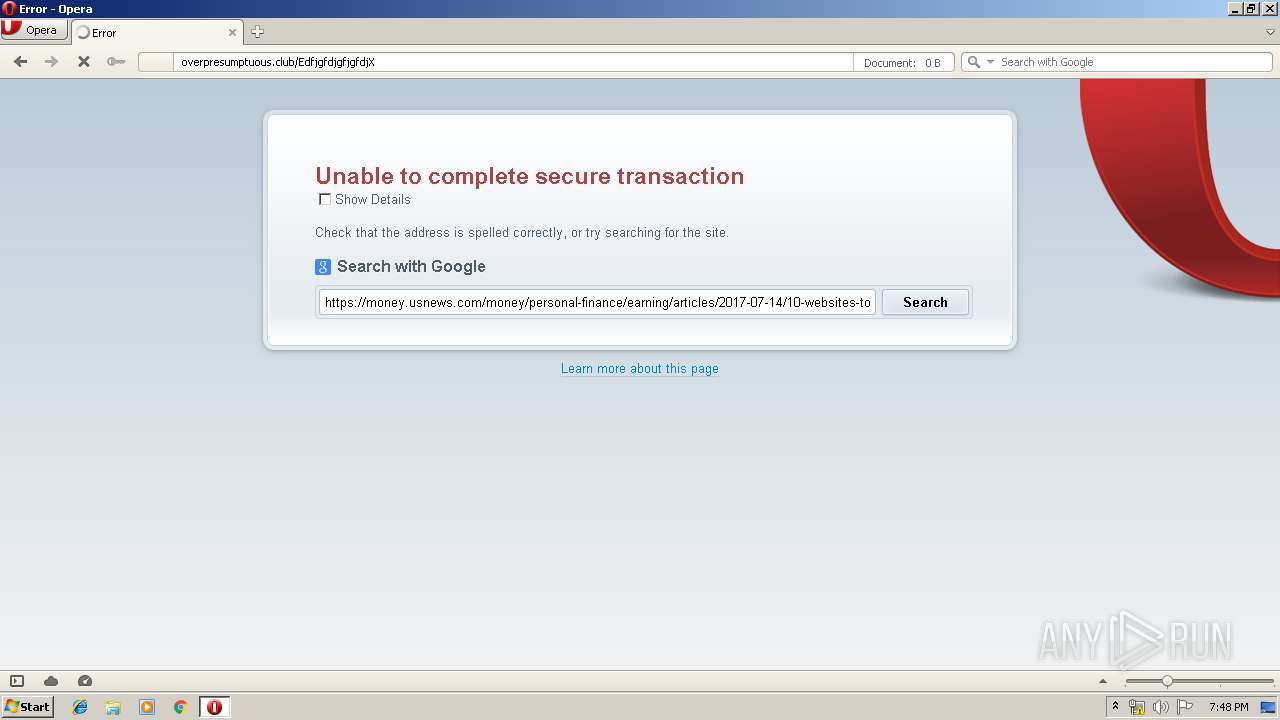
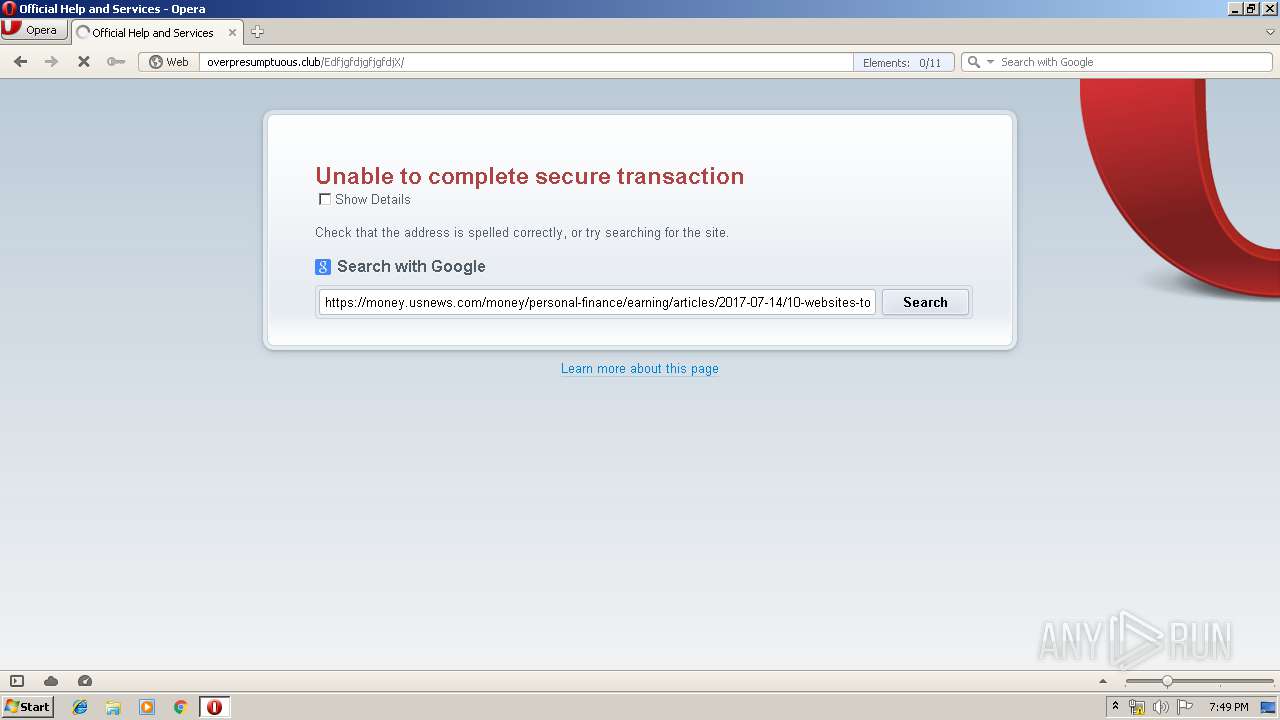
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprAAB2.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprAAC2.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprAB02.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1SSXMZP02XV3PCL0KY6F.temp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprC08E.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00002.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF39b64a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
97
DNS requests
95
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2416 | opera.exe | GET | — | 13.224.217.158:80 | http://crl.rootg2.amazontrust.com/rootg2.crl | US | — | — | whitelisted |
2416 | opera.exe | GET | 200 | 192.16.58.8:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
2416 | opera.exe | GET | 200 | 172.217.19.196:80 | http://www.google.com/adsense/domains/caf.js | US | text | 55.0 Kb | malicious |
2416 | opera.exe | GET | 200 | 172.217.17.131:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 950 b | whitelisted |
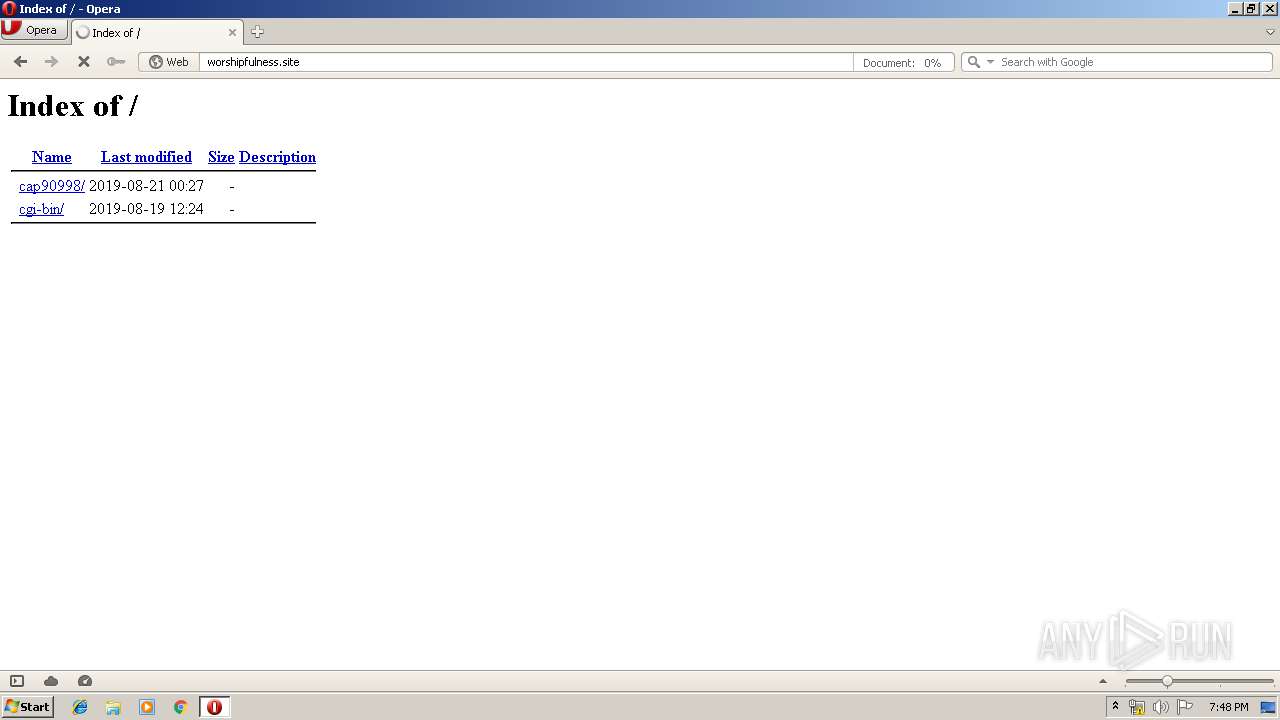
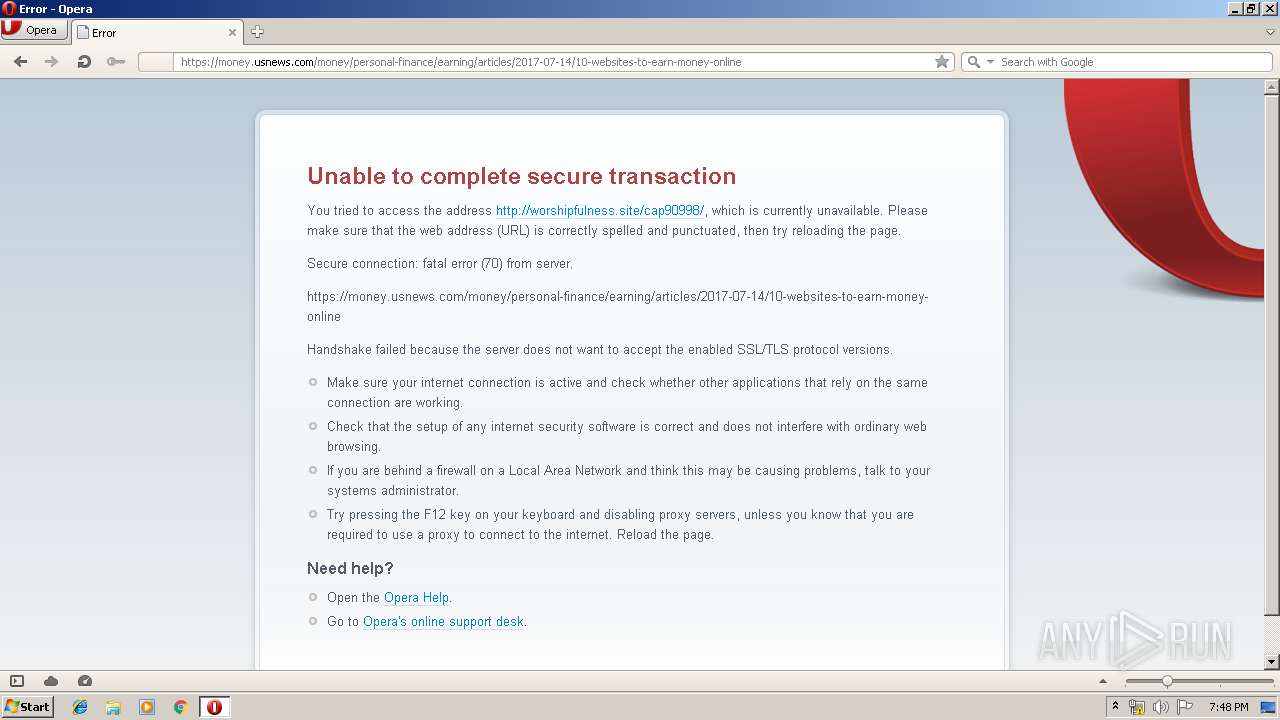
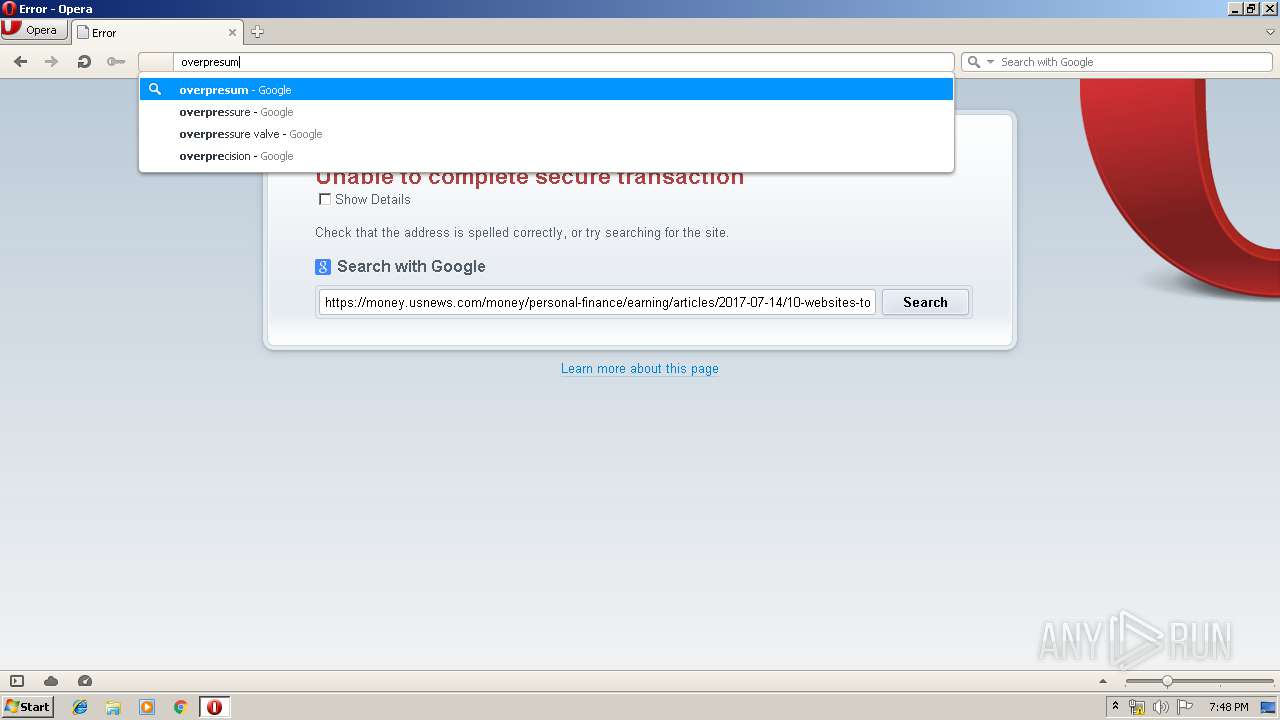
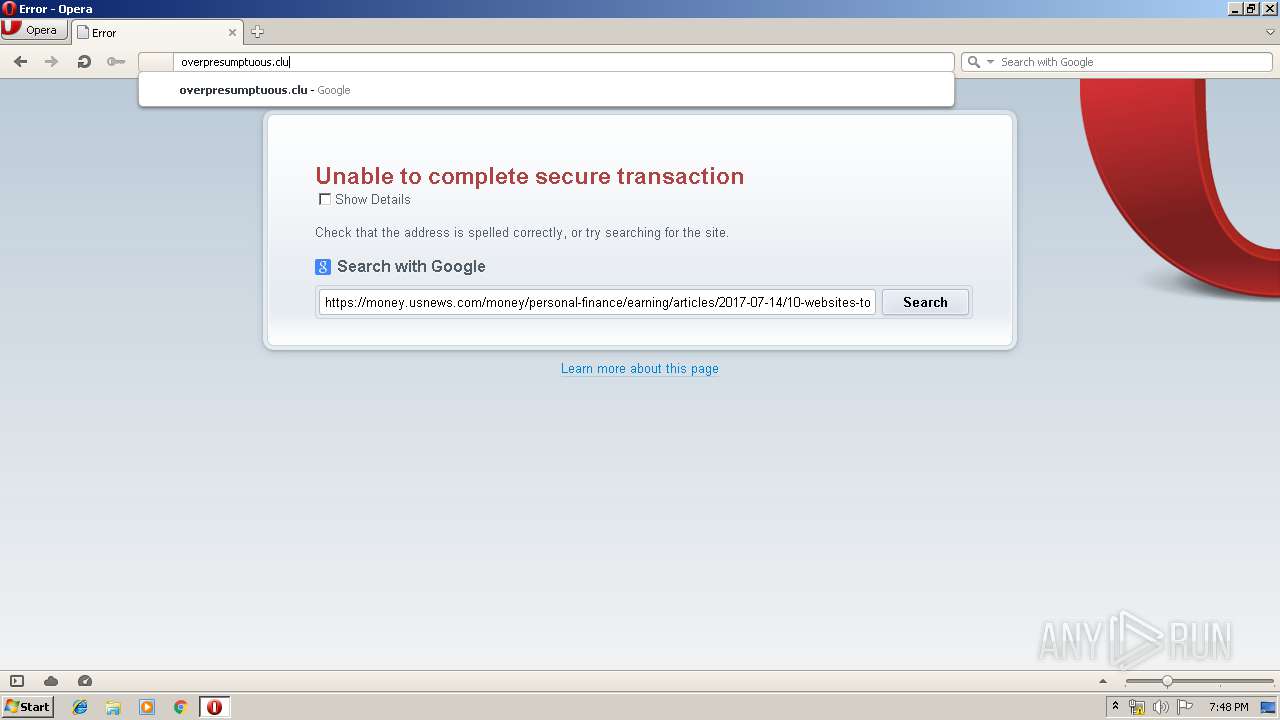
2416 | opera.exe | GET | 200 | 209.126.123.12:80 | http://gogoel.com/ | US | html | 466 b | malicious |
2416 | opera.exe | POST | 200 | 199.59.242.153:80 | http://ww1.gogoel.com/gzb | US | text | 224 b | malicious |
2416 | opera.exe | GET | 200 | 13.224.244.161:80 | http://crl.rootca1.amazontrust.com/rootca1.crl | US | der | 439 b | whitelisted |
2416 | opera.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gogoel.com/glp?r=http%3A%2F%2Fgogoel.com%2F&u=http%3A%2F%2Fww1.gogoel.com%2F&rw=1280&rh=720&ww=1280&wh=591 | US | text | 8.49 Kb | malicious |
2416 | opera.exe | GET | 200 | 172.217.17.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDlcREEFHaVywIAAAAARtCU | US | der | 472 b | whitelisted |
2416 | opera.exe | GET | 302 | 209.126.123.12:80 | http://gogoel.com/?js=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJhdWQiOiJKb2tlbiIsImV4cCI6MTU3MTc3NzE4MywiaWF0IjoxNTcxNzY5OTgzLCJpc3MiOiJKb2tlbiIsImpzIjoxLCJqdGkiOiIybjgwb3U4NDJlMnQ5cTdpMGcwMmF0MG4iLCJuYmYiOjE1NzE3Njk5ODMsInRzIjoxNTcxNzY5OTgzODUxMjMxfQ.01SohYS6dMU9XAiM16sNCT3c_Nd_jadehxQl5dkh_YU&sid=3f0fd66c-f4fc-11e9-aae0-b576a4e9b17c | US | text | 11 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
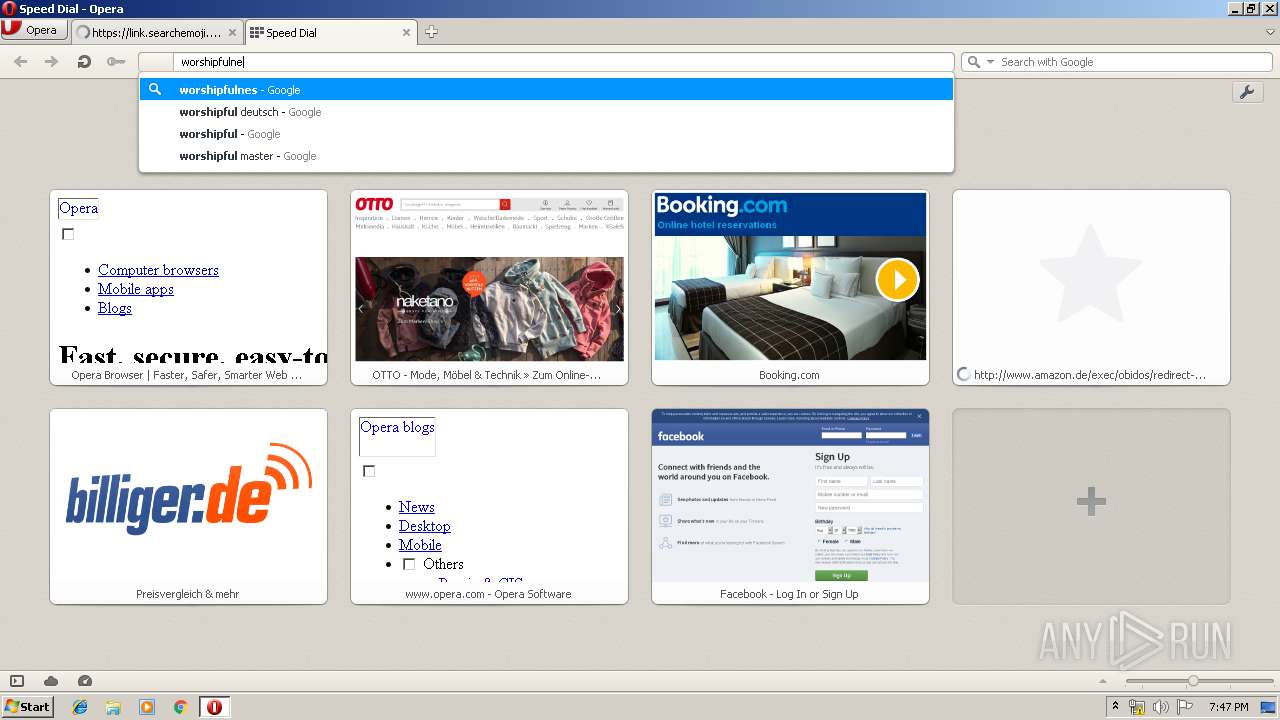
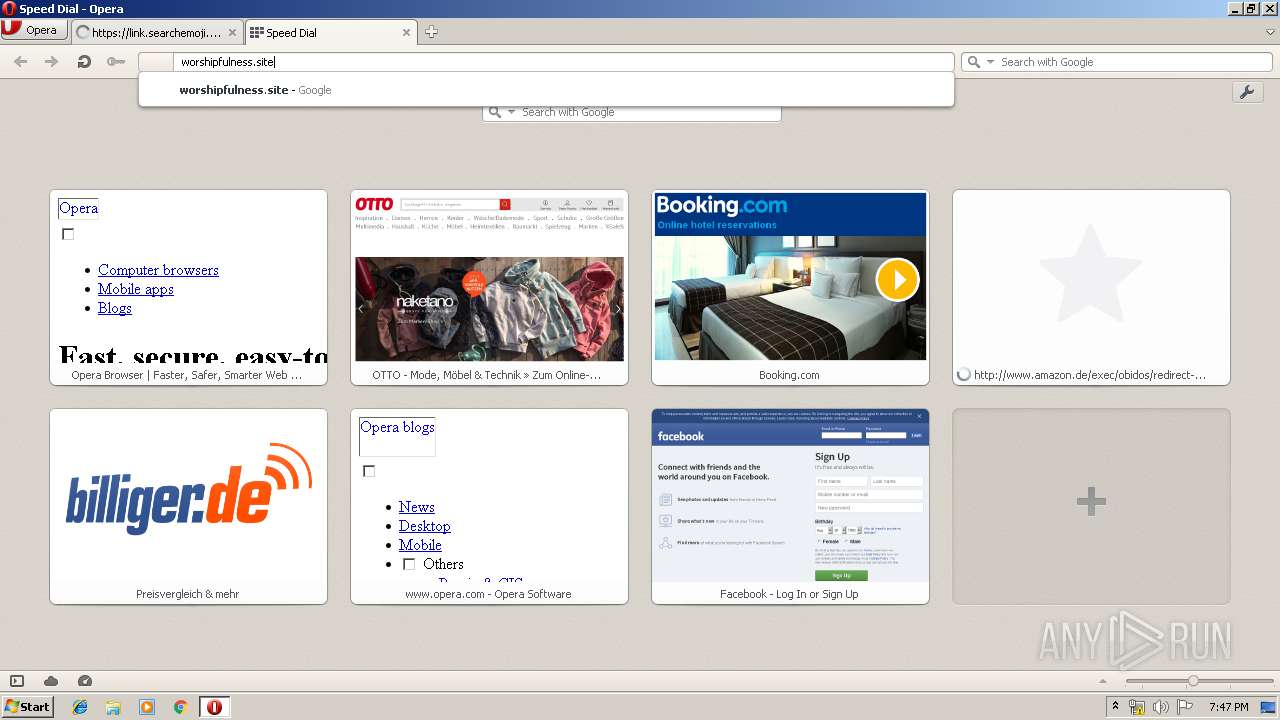
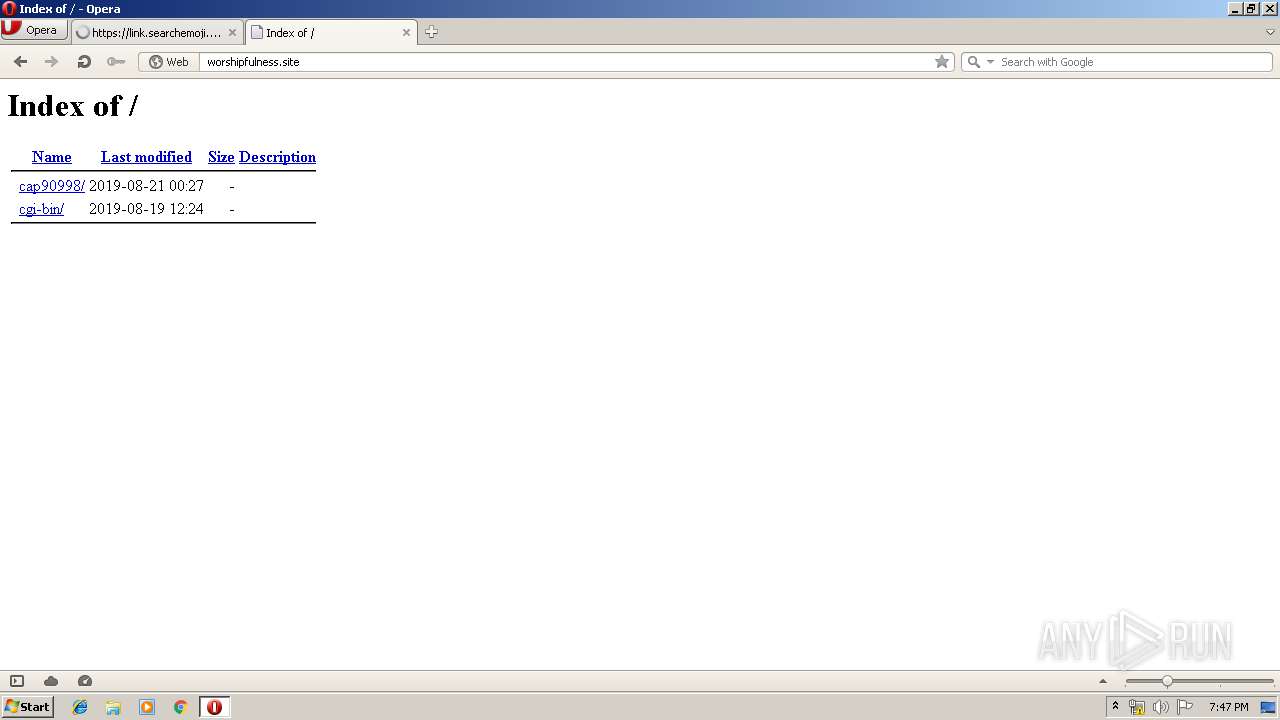
2416 | opera.exe | 13.224.227.9:443 | link.searchemoji.global | — | US | unknown |
2416 | opera.exe | 13.224.217.158:80 | crl.rootg2.amazontrust.com | — | US | whitelisted |
2416 | opera.exe | 13.224.244.161:80 | crl.rootca1.amazontrust.com | — | US | whitelisted |
2416 | opera.exe | 209.126.123.12:80 | gogoel.com | server4you Inc. | US | suspicious |
2416 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2416 | opera.exe | 185.26.182.93:80 | certs.opera.com | Opera Software AS | — | whitelisted |
2416 | opera.exe | 199.59.242.153:80 | ww1.gogoel.com | Bodis, LLC | US | malicious |
2416 | opera.exe | 185.26.182.110:80 | redir.opera.com | Opera Software AS | — | unknown |
2416 | opera.exe | 99.86.114.226:80 | www.amazon.com | AT&T Services, Inc. | US | unknown |
2416 | opera.exe | 172.217.17.46:80 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
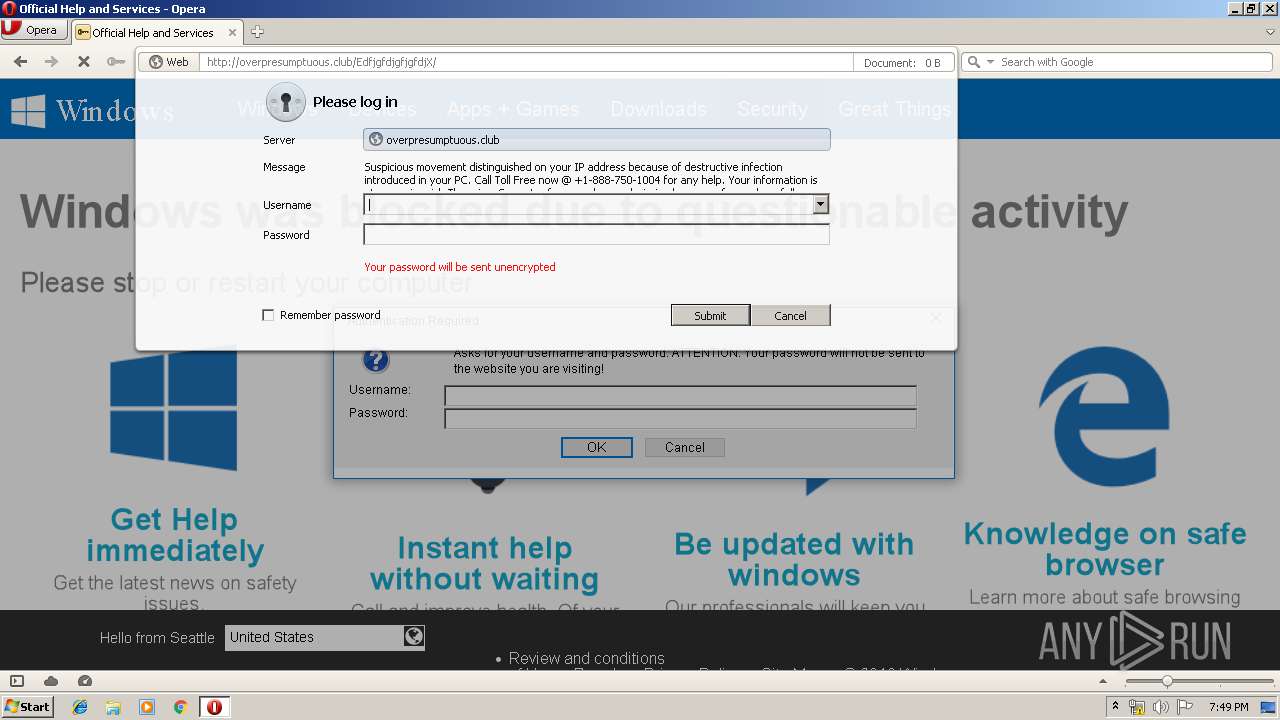
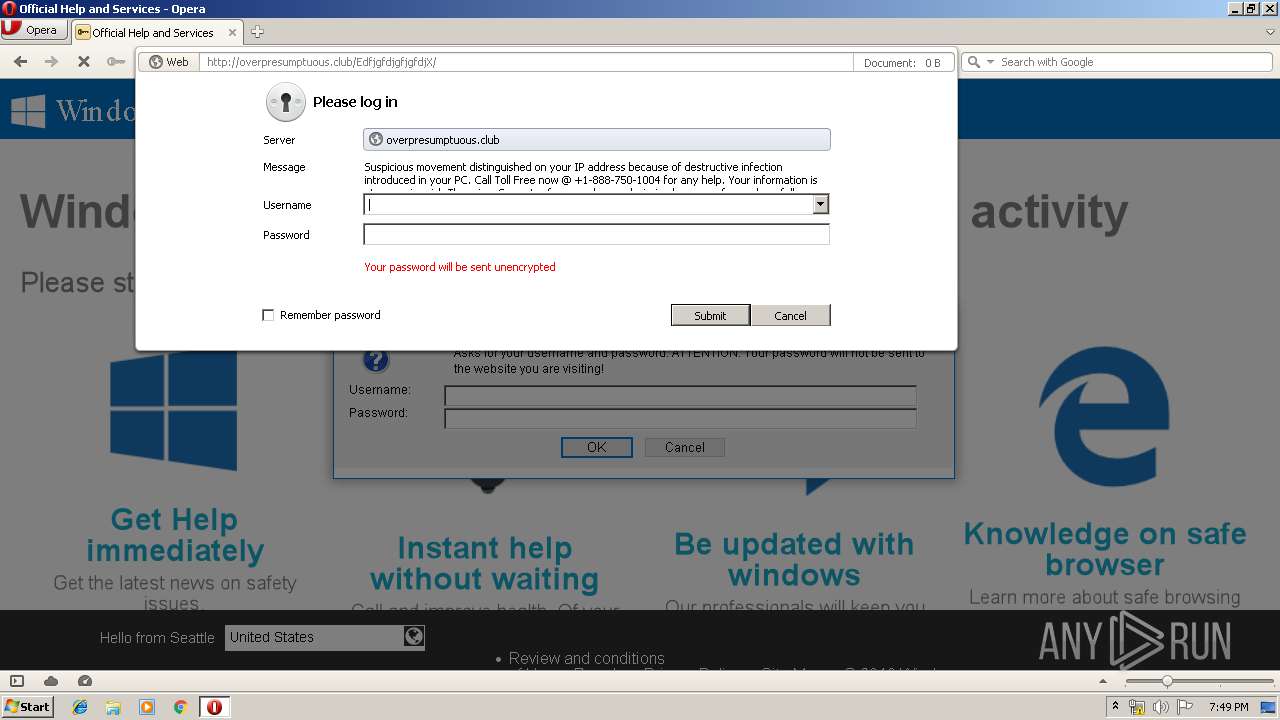
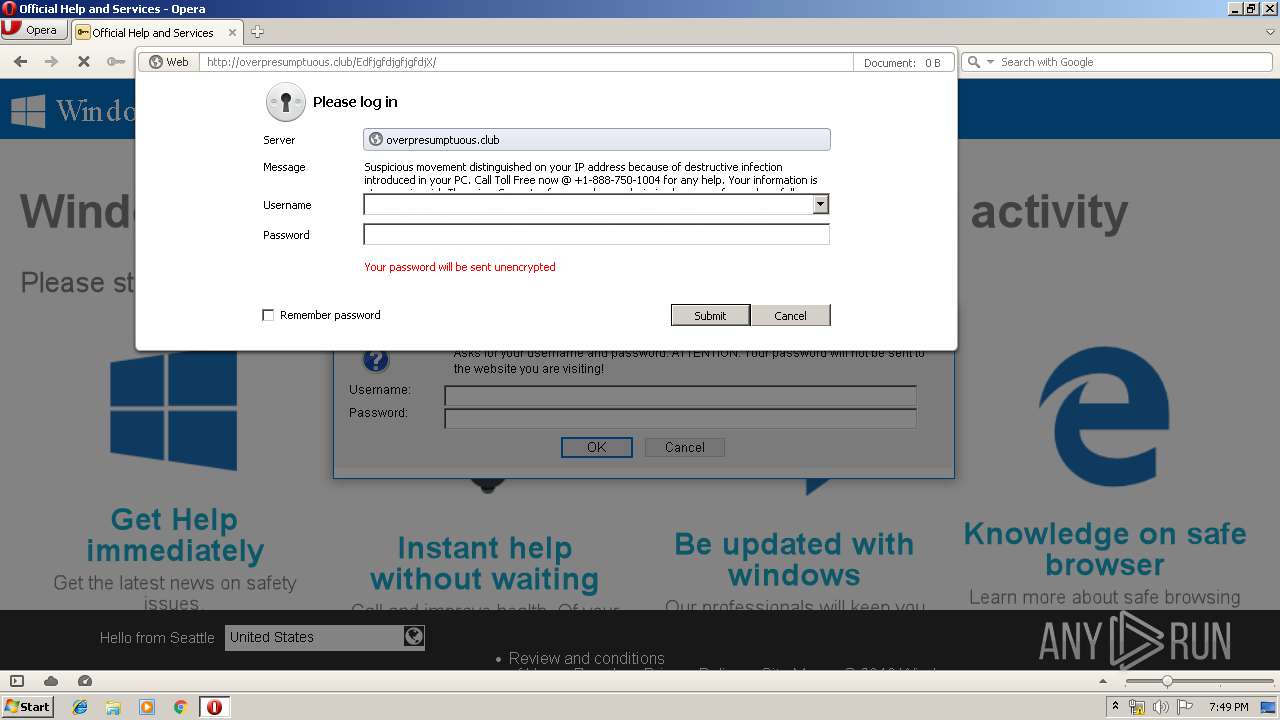
gogoel.com |
| malicious |
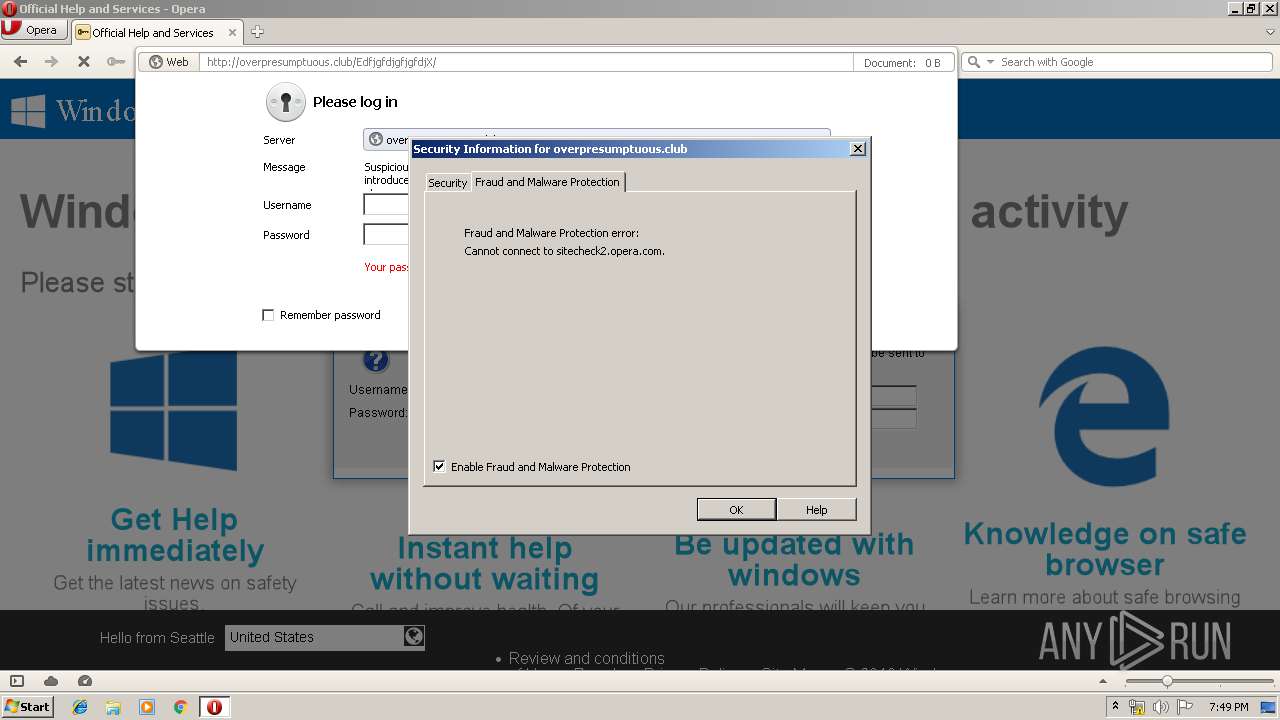
certs.opera.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
ww1.gogoel.com |
| malicious |
crl4.digicert.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
link.searchemoji.global |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
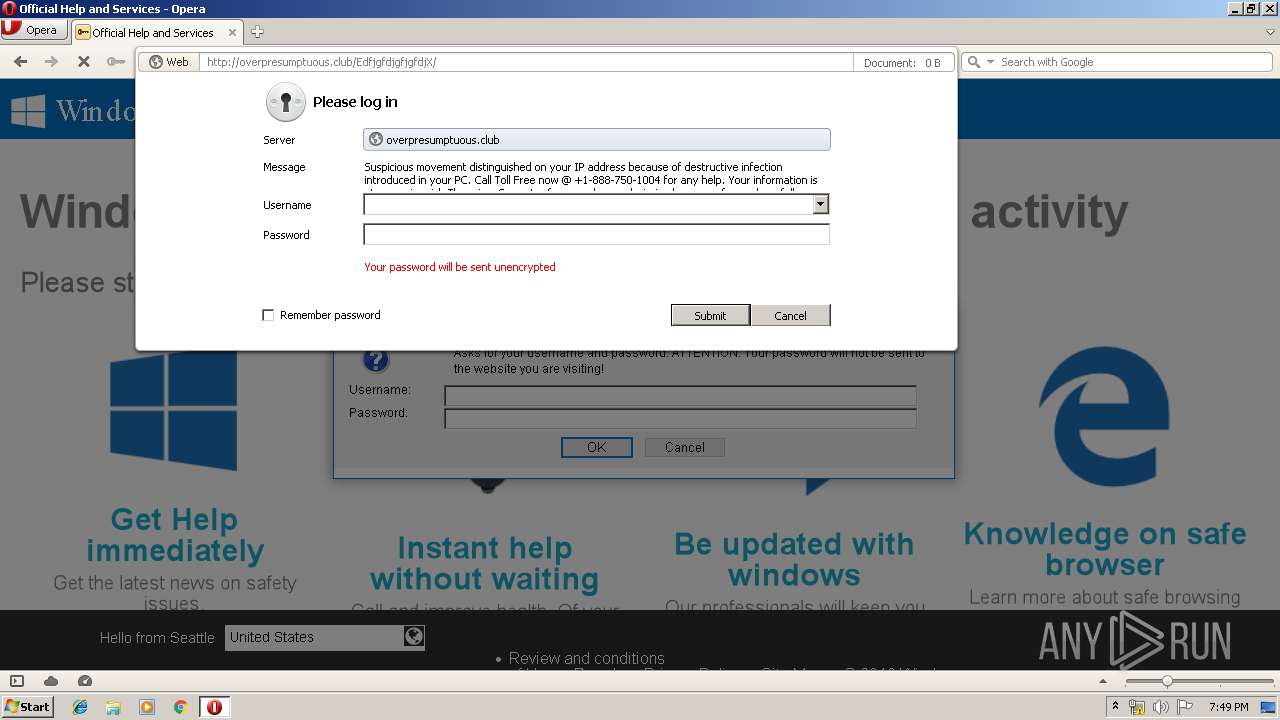
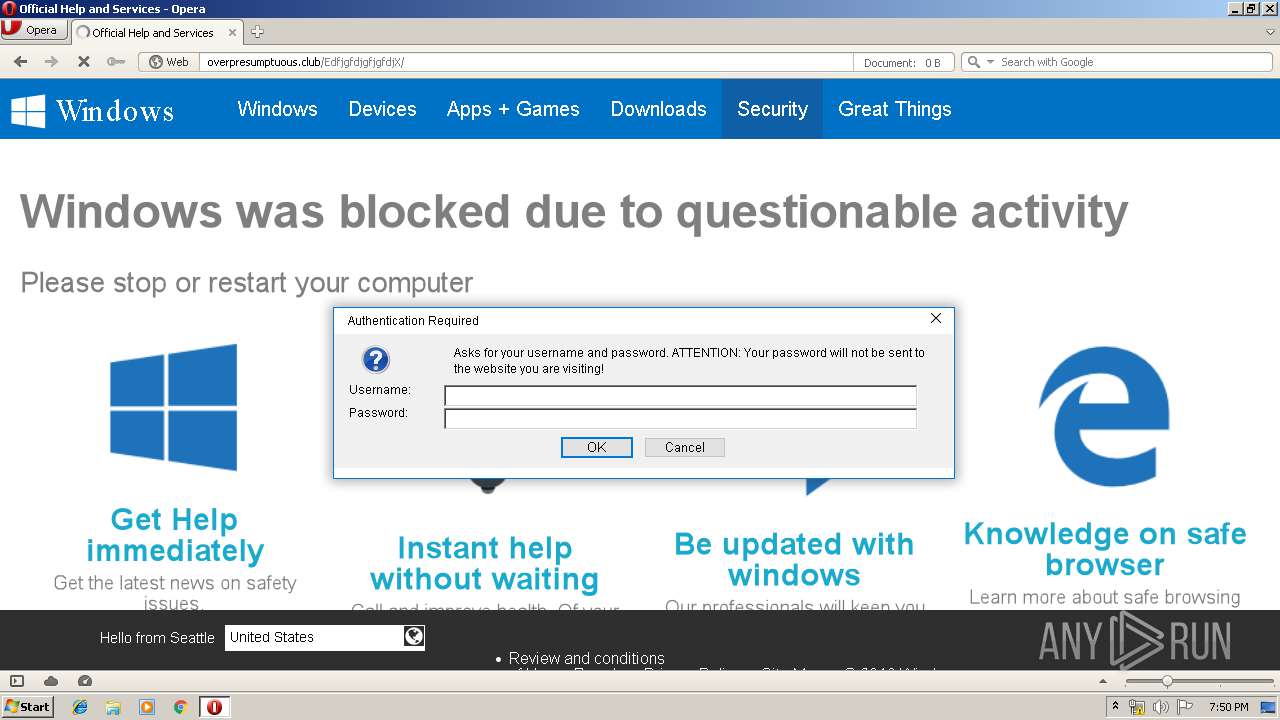
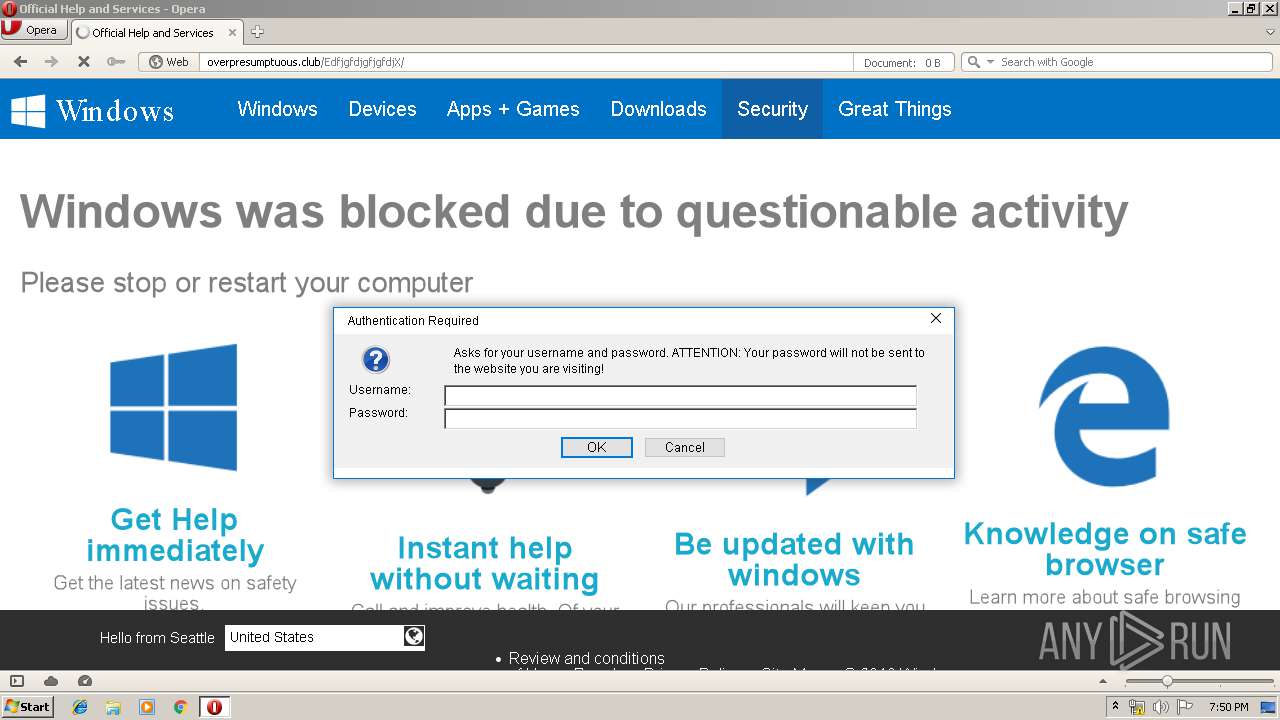
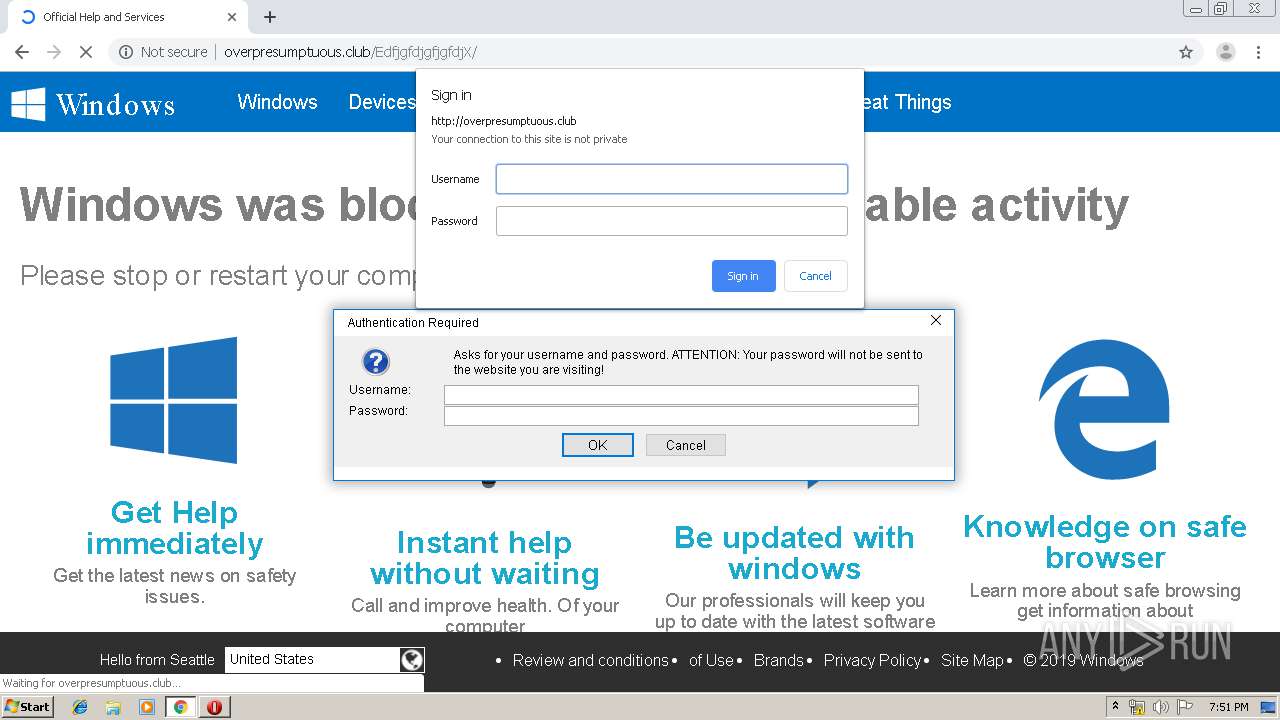
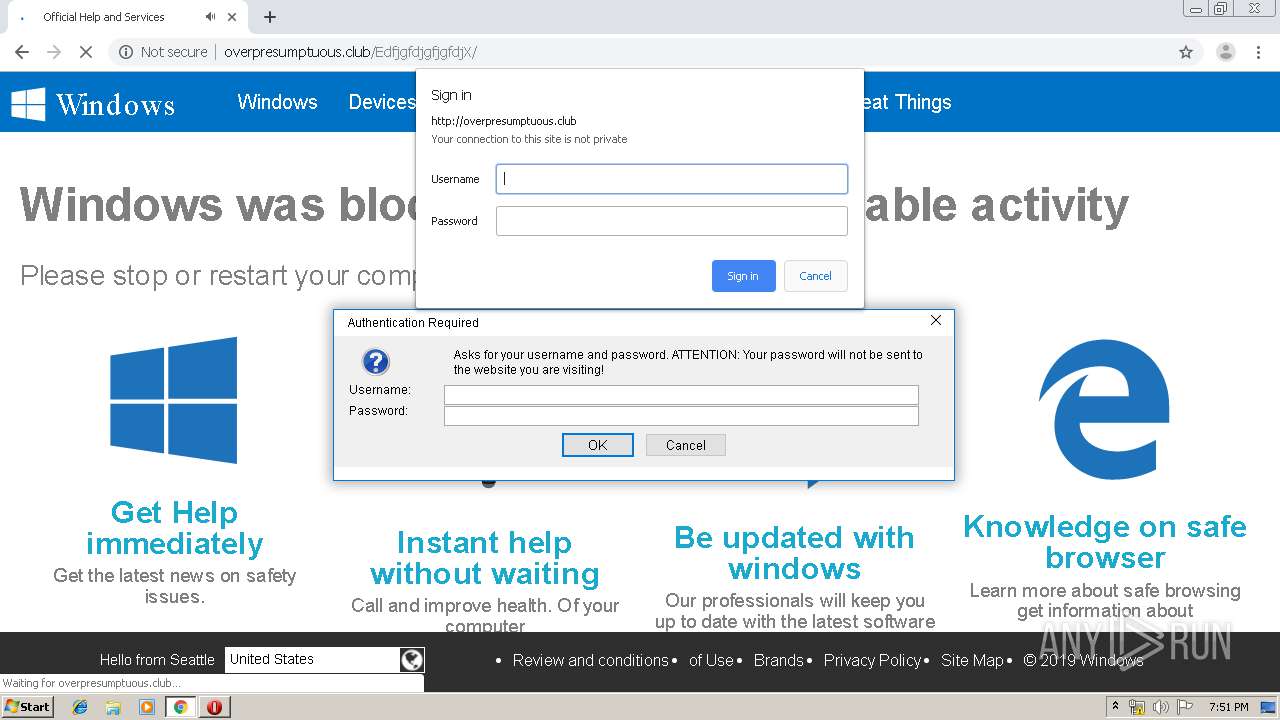
2416 | opera.exe | Potential Corporate Privacy Violation | ET POLICY Outgoing Basic Auth Base64 HTTP Password detected unencrypted |
Process | Message |
|---|---|
opera.exe | core libvlc debug: VLC media player - 2.2.6 Umbrella
|
opera.exe | core libvlc debug: revision 2.2.6-0-g1aae789
|
opera.exe | core libvlc debug: revision 2.2.6-0-g1aae789
|
opera.exe | core libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-twolame' '--enable-quicktime' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-x264' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--disable-sdl' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' 'host_alias=i686-w64-mingw32'
|
opera.exe | core libvlc debug: using multimedia timers as clock source
|
opera.exe | core libvlc debug: min period: 1 ms, max period: 1000000 ms
|
opera.exe | core libvlc debug: searching plug-in modules
|
opera.exe | core libvlc debug: ignoring plugins cache file
|
opera.exe | core libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
opera.exe | core libvlc debug: plug-ins loaded: 419 modules
|