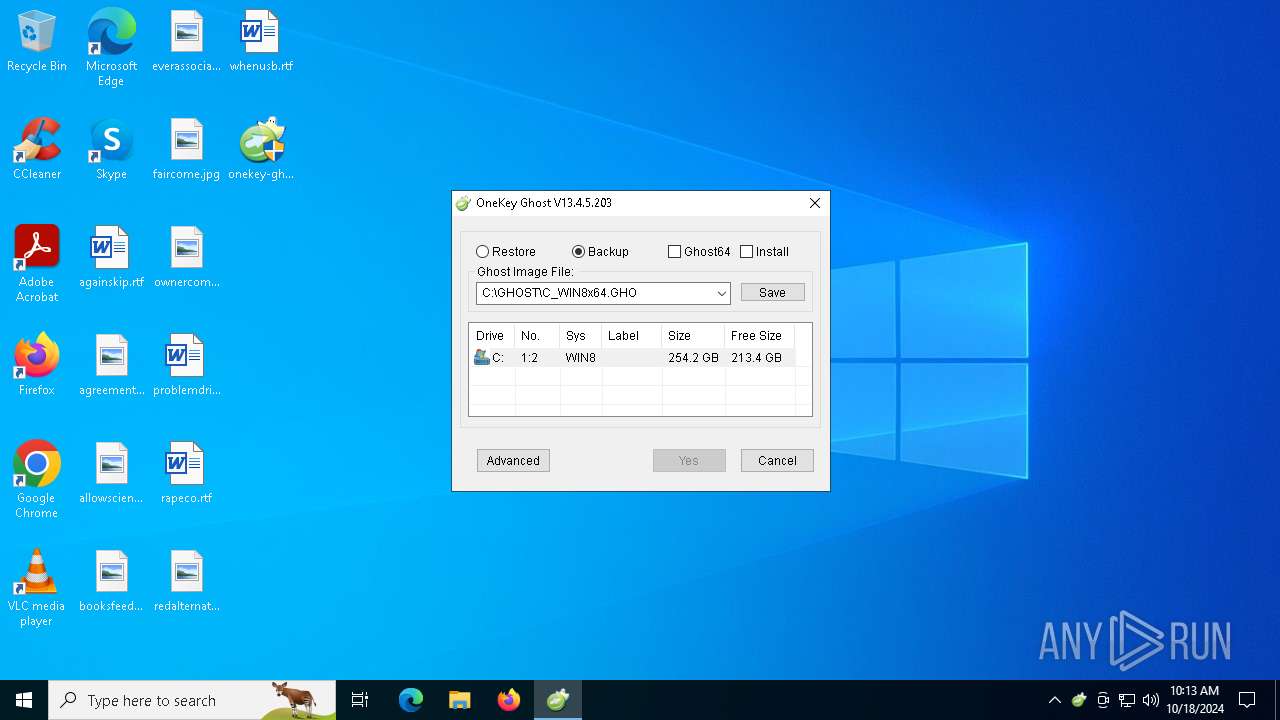
| File name: | onekey-ghost_setup.exe |
| Full analysis: | https://app.any.run/tasks/6c8095fc-1b19-47a7-acba-e3308abc0bc0 |
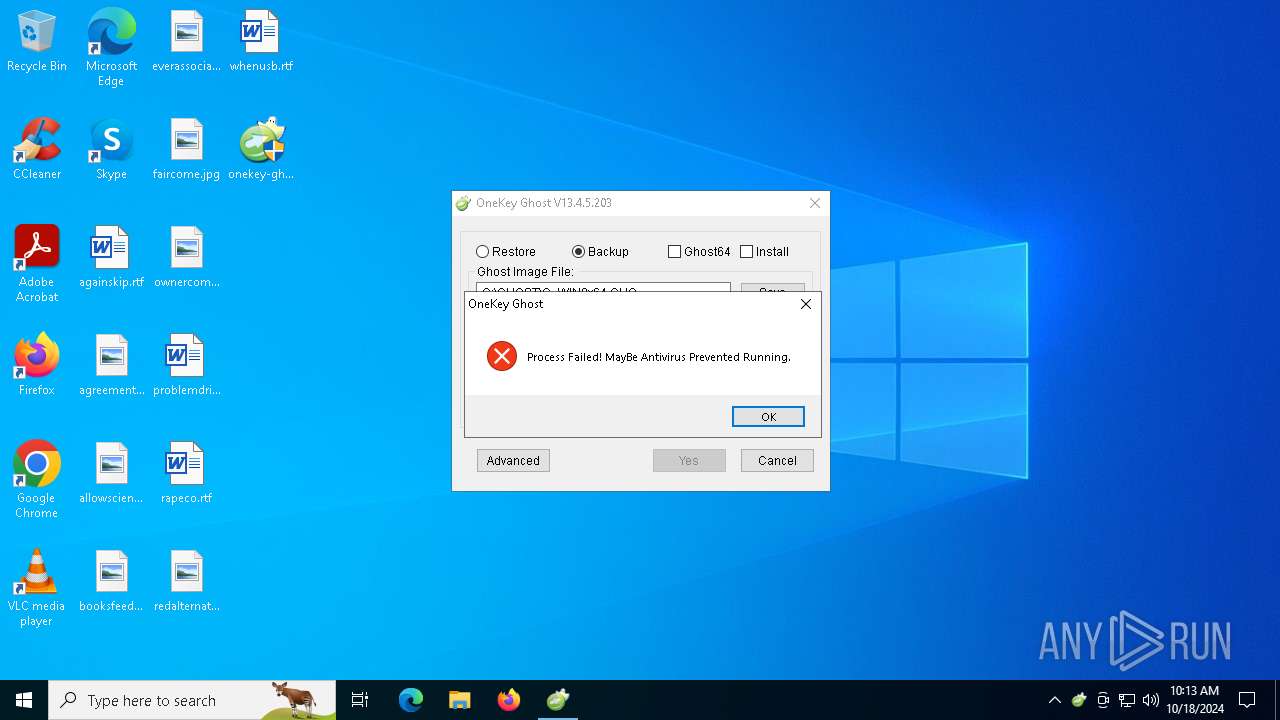
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2024, 10:13:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | A64E374945845AAEC6AD063E8BE450DB |
| SHA1: | 765C30DCFE127CB9C7C246FFA5EBB35040E1EE82 |
| SHA256: | 46D0413084564B4DE78218AB73CAC481743D6C5756B13FD4FFEC7C897B8F75D8 |
| SSDEEP: | 98304:eP16n8ejh+trbU0tgfPGzpOV7JQQoKb0KigDuiKeZTZGmYKivHlKnGundOn2fSsy:kEEJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Read disk information to detect sandboxing environments
- onekey-ghost_setup.exe (PID: 5512)
The executable file from the user directory is run by the CMD process
- Getptw.dl_ (PID: 920)
- ISODrv.dll (PID: 1576)
- grubinst.exe (PID: 4868)
- ShowDrive.exe (PID: 5496)
The process creates files with name similar to system file names
- onekey-ghost_setup.exe (PID: 5512)
Process drops legitimate windows executable
- onekey-ghost_setup.exe (PID: 5512)
Drops a system driver (possible attempt to evade defenses)
- onekey-ghost_setup.exe (PID: 5512)
Starts application with an unusual extension
- cmd.exe (PID: 1112)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 6596)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 6152)
Executable content was dropped or overwritten
- onekey-ghost_setup.exe (PID: 5512)
Reads security settings of Internet Explorer
- onekey-ghost_setup.exe (PID: 5512)
Potential Corporate Privacy Violation
- onekey-ghost_setup.exe (PID: 5512)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1584)
Starts CMD.EXE for commands execution
- onekey-ghost_setup.exe (PID: 5512)
INFO
Reads mouse settings
- onekey-ghost_setup.exe (PID: 5512)
Checks supported languages
- onekey-ghost_setup.exe (PID: 5512)
- ShowDrive.exe (PID: 5496)
- grubinst.exe (PID: 4868)
- ISODrv.dll (PID: 1576)
- Getptw.dl_ (PID: 920)
Reads the computer name
- onekey-ghost_setup.exe (PID: 5512)
Create files in a temporary directory
- onekey-ghost_setup.exe (PID: 5512)
Checks proxy server information
- onekey-ghost_setup.exe (PID: 5512)
Creates files or folders in the user directory
- onekey-ghost_setup.exe (PID: 5512)
The process uses AutoIt
- onekey-ghost_setup.exe (PID: 5512)
UPX packer has been detected
- onekey-ghost_setup.exe (PID: 5512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:04:10 00:11:21+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 286720 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 524288 |
| EntryPoint: | 0xc5990 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
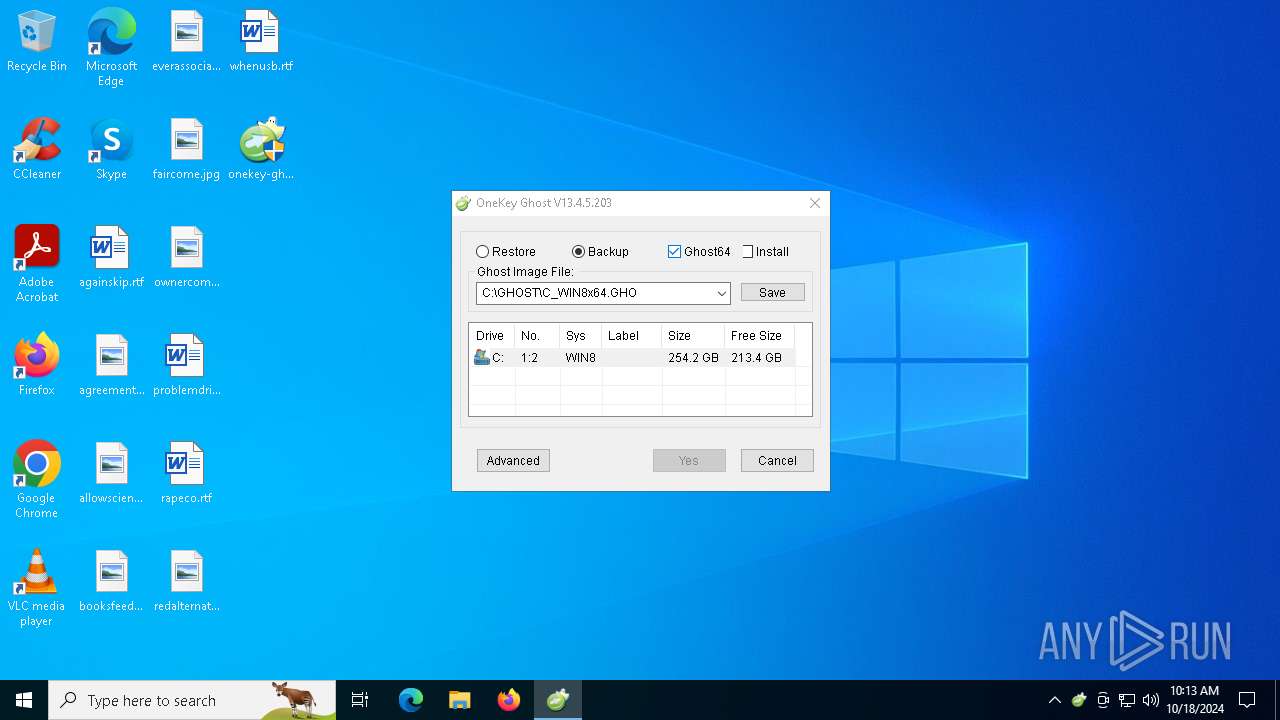
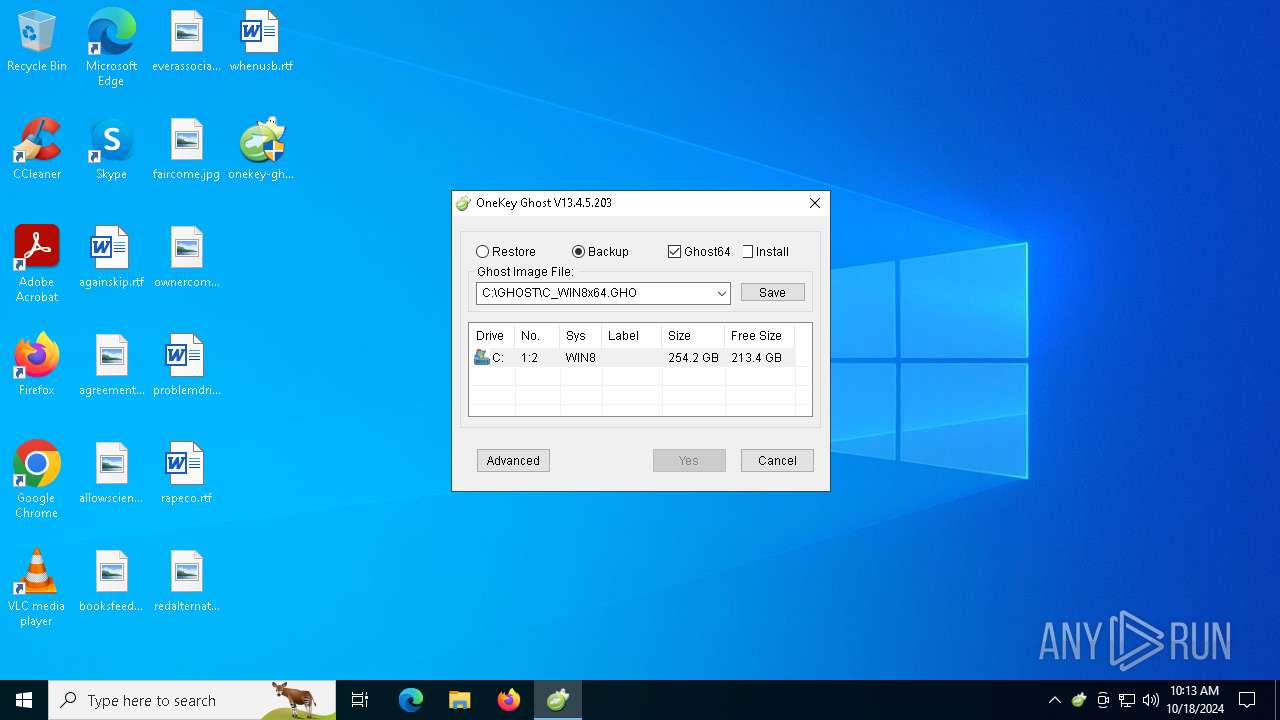
| FileVersionNumber: | 13.4.5.203 |
| ProductVersionNumber: | 10853.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 13.4.5.203 |
| FileDescription: | 一键还原 |
| LegalCopyright: | Copyright (C) 2005-2013 OneKey.Cc |
| ProductVersion: | 20130405 |
| Compiler: | 2013-4-5 00:16:50 |
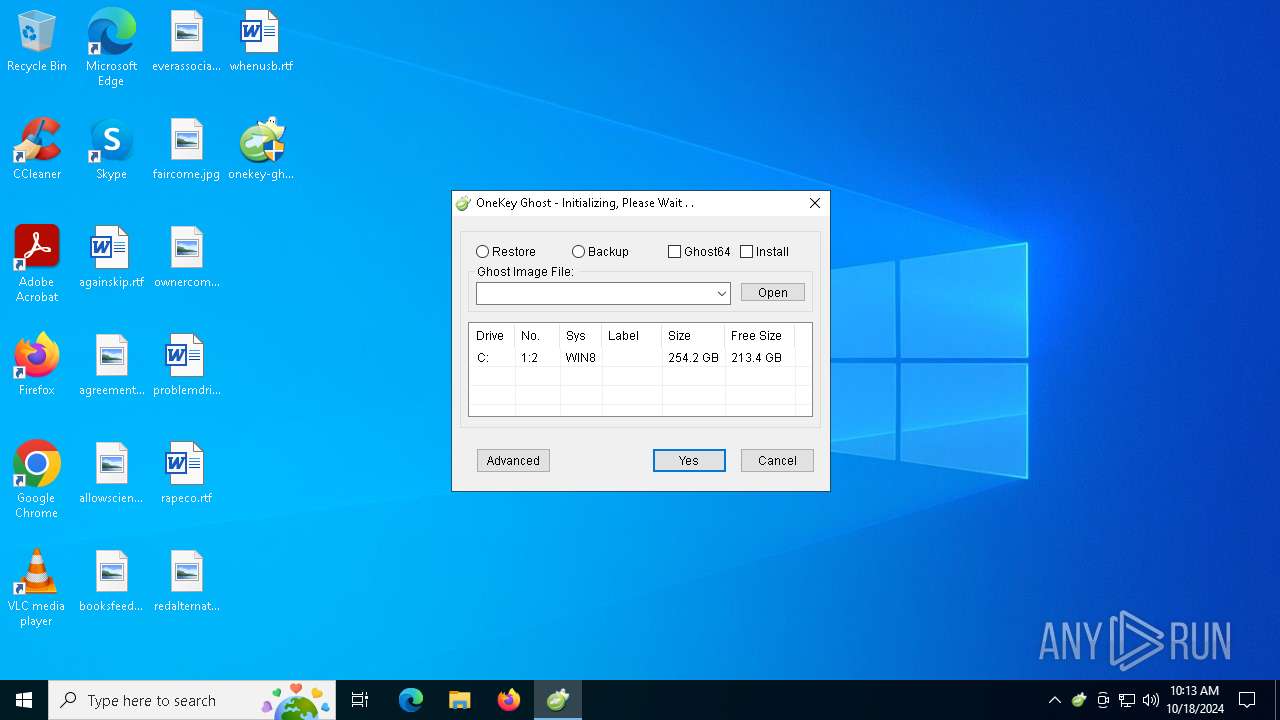
| ProductName: | OneKey Ghost |
| LegalTrademarks: | OneKey Ghost |
| CompanyName: | OneKey.Cc |
| OriginalFileName: | OneKeyGhost.exe |
Total processes
164
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | C:\Users\admin\AppData\Local\Temp\Getptw.dl_ -a/part | C:\Users\admin\AppData\Local\Temp\Getptw.dl_ | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1112 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\ISODrv.dll -Print | C:\Windows\SysWOW64\cmd.exe | — | onekey-ghost_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\Bcdedit.dll /create {b5d09b58-5bdc-5b57-a096-7b7c6bde08f1} /d "OneKey Ghost V13.4" /application bootsector | C:\Windows\SysWOW64\cmd.exe | — | onekey-ghost_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | C:\Users\admin\AppData\Local\Temp\ISODrv.dll -Print | C:\Users\admin\AppData\Local\Temp\ISODrv.dll | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1584 | C:\WINDOWS\system32\cmd.exe /c reg unload HKLM\BCD00000000 | C:\Windows\SysWOW64\cmd.exe | — | onekey-ghost_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\Bcdedit.dll /delete {b5d09b58-5bdc-5b57-a096-7b7c6bde08f1} | C:\Windows\Bcdedit.dll | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | C:\WINDOWS\Bcdedit.dll /delete {b5d09b48-5bdc-4b57-a096-7b7c6bde08f1} | C:\Windows\Bcdedit.dll | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3728 | C:\WINDOWS\system32\cmd.exe /c grubinst.exe --read-only --save=MBR.tmp (hd-1) | C:\Windows\SysWOW64\cmd.exe | — | onekey-ghost_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3772 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 010
Read events
3 970
Write events
39
Delete events
1
Modification events
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000030000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 010000000000000004000000050000000200000003000000FFFFFFFF | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
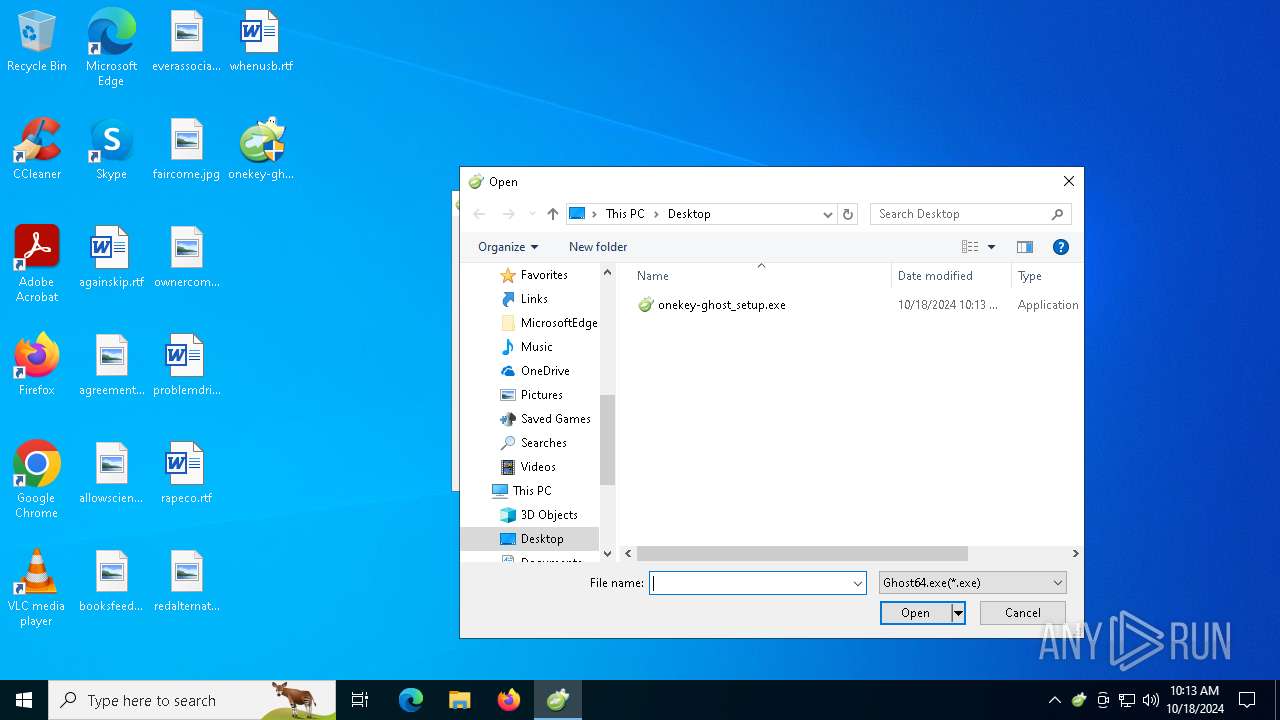
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | write | Name: | 2 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E803ACCBFB42CDB4C42B0297FE99A87C6417A00320018C43C005259AC5120004F4E454B45597E312E45584500005E0009000400EFBE5259AC515259AC512E0000001704000000000D0000000000000000000000000000008C0AF3006F006E0065006B00650079002D00670068006F00730074005F00730065007400750070002E0065007800650000001C000000 | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (5512) onekey-ghost_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | 7 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E803ACCBFB42CDB4C42B0297FE99A87C6417A00320018C43C005259AC5120004F4E454B45597E312E45584500005E0009000400EFBE5259AC515259AC512E0000001704000000000D0000000000000000000000000000008C0AF3006F006E0065006B00650079002D00670068006F00730074005F00730065007400750070002E0065007800650000001C000000 | |||
Executable files
7
Suspicious files
8
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\autBA43.tmp | binary | |
MD5:798B5E4C5F9B9821884723E8FAF0C632 | SHA256:1E3F3AFCE826A1C5E48D78F48A31096EADEAD43516D84DD5D322C842B66280A6 | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\autB994.tmp | binary | |
MD5:1B502265D33CA5F3524E8D2E64C0E697 | SHA256:42F2F0A1AFBB00E35470D79EFE0C671C4CDA68376900DD455E829D0AA894C8F1 | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\haupgdy | text | |
MD5:F55BB6EA75EA01ACBEA4C6CE71523665 | SHA256:19419491028916E99D705C13F3EB87425D9E49D890820D7563CFCDECF48F3F9C | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\ISODrv64.sys | executable | |
MD5:9C6F3F69163133FB8E56AC4A6E163452 | SHA256:BD6CAB093B5451B4CC85B4528DC0251C97A3D11CB3C1493D25F37B06F8CD2238 | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\Getptw.dl_ | executable | |
MD5:94D297CCB80B1F7940EA98FFDFC25257 | SHA256:DD4694E89AE067E49E4F9581782A277EB0FAB052AA1539717FECF8449A872F75 | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\ShowDrive.exe | executable | |
MD5:63F0697283A67DB3F50B440F142044ED | SHA256:09C07DB40DACD999E726786FC9A8F5E37688D94997F2692DA63746F417851F0F | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\grubinst.exe | executable | |
MD5:EC6ECFE076C6367BD4E3CAEC6DC869F3 | SHA256:EF3F1DD34AEA7E6EAA44F57E3A0B117D995786373585E635A8554625BD7C3F3B | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\DataIcon.dl_ | executable | |
MD5:79BA9C235207324C83802758FFDC1C97 | SHA256:F6C39B01FB2E10D192C1C400313F7D56CBFED9D8C4A8DDB0239BE9F959371749 | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\autBD93.tmp | binary | |
MD5:E3999F49BE03CC4B28B313AB88DF746B | SHA256:9274E7EDFDD8BF7446A75F79DA271EB3E05DDF6EB5276290757CC64355B20559 | |||
| 5512 | onekey-ghost_setup.exe | C:\Users\admin\AppData\Local\Temp\autBD15.tmp | binary | |
MD5:72F2B80941A61903F787D8B26A9AA38B | SHA256:345B4D1074EDA61B00AF9BC16092C5BC6317781C3C0EA5225B2793C1BF5DFEBE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
60
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5512 | onekey-ghost_setup.exe | GET | 200 | 47.244.112.164:80 | http://ghost.onekey.cc/OKinfo/OKinfo.asp | unknown | — | — | malicious |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5948 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1752 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5512 | onekey-ghost_setup.exe | 47.244.112.164:80 | ghost.onekey.cc | Alibaba US Technology Co., Ltd. | HK | suspicious |
2364 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2364 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ghost.onekey.cc |
| unknown |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5512 | onekey-ghost_setup.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |