| File name: | Microsoft.exe |
| Full analysis: | https://app.any.run/tasks/21c31903-7e5f-45e0-9106-2ef3cd606b75 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2020, 19:45:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9F055E60E6ACB1A50BC542E0DBAE34FC |
| SHA1: | 33486338927E5F5736DE4B4ED491A85D1F630094 |
| SHA256: | 46CF0D598EAD968845E7D17CFBA1B30ECCB7A66FA639763BA99335B3CE4D8F65 |
| SSDEEP: | 12288:lqMxF2J56BIPTd/mI5F/OyPJkVCB1pNV0vpvQc:lmiV8zCvJt |
MALICIOUS
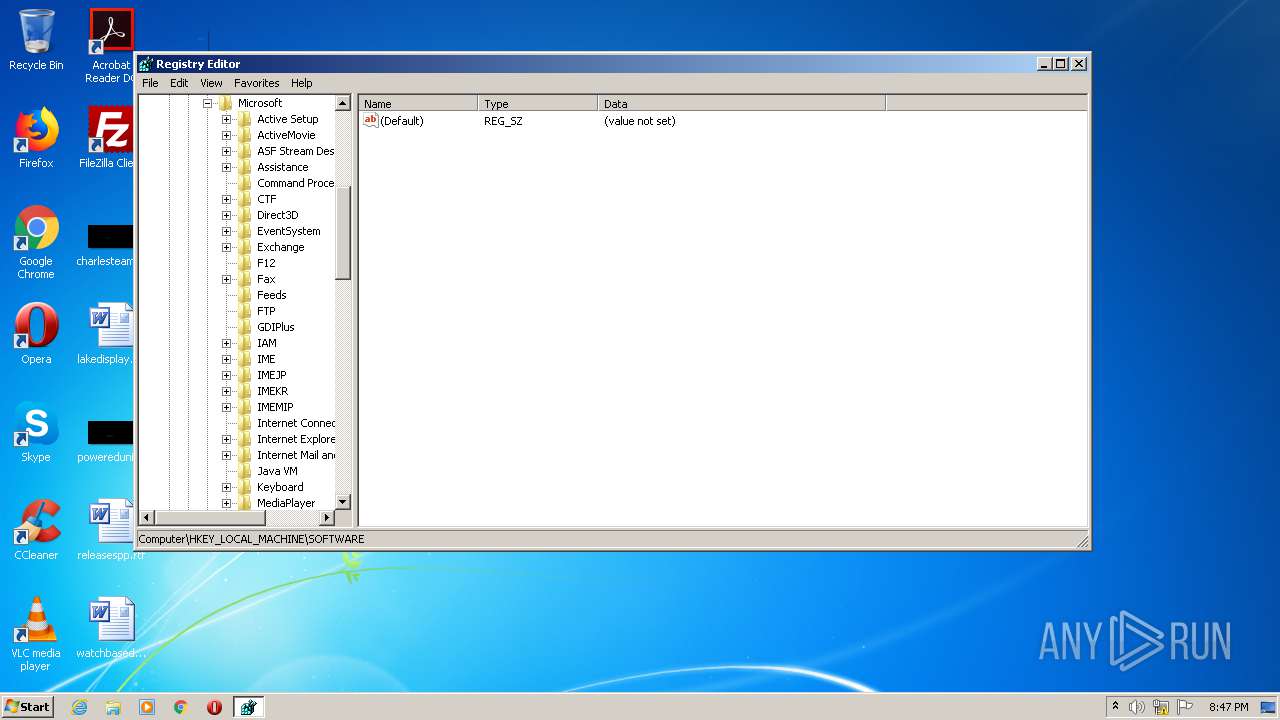
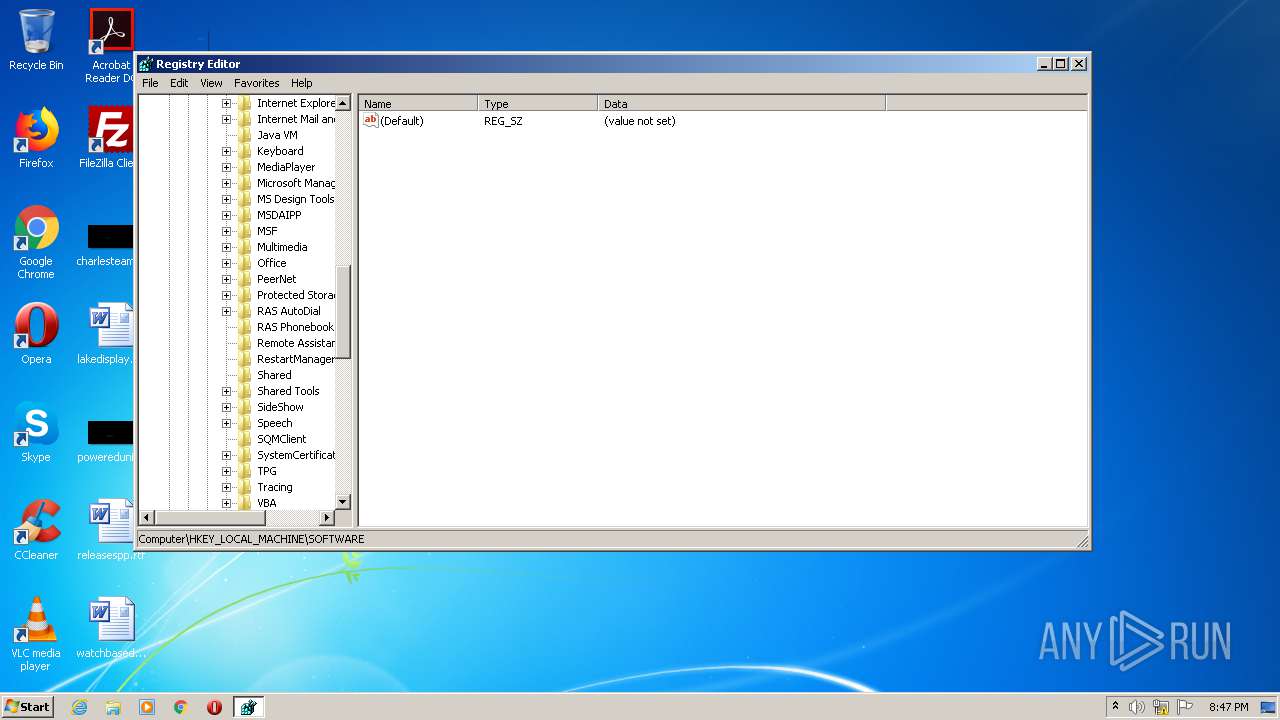
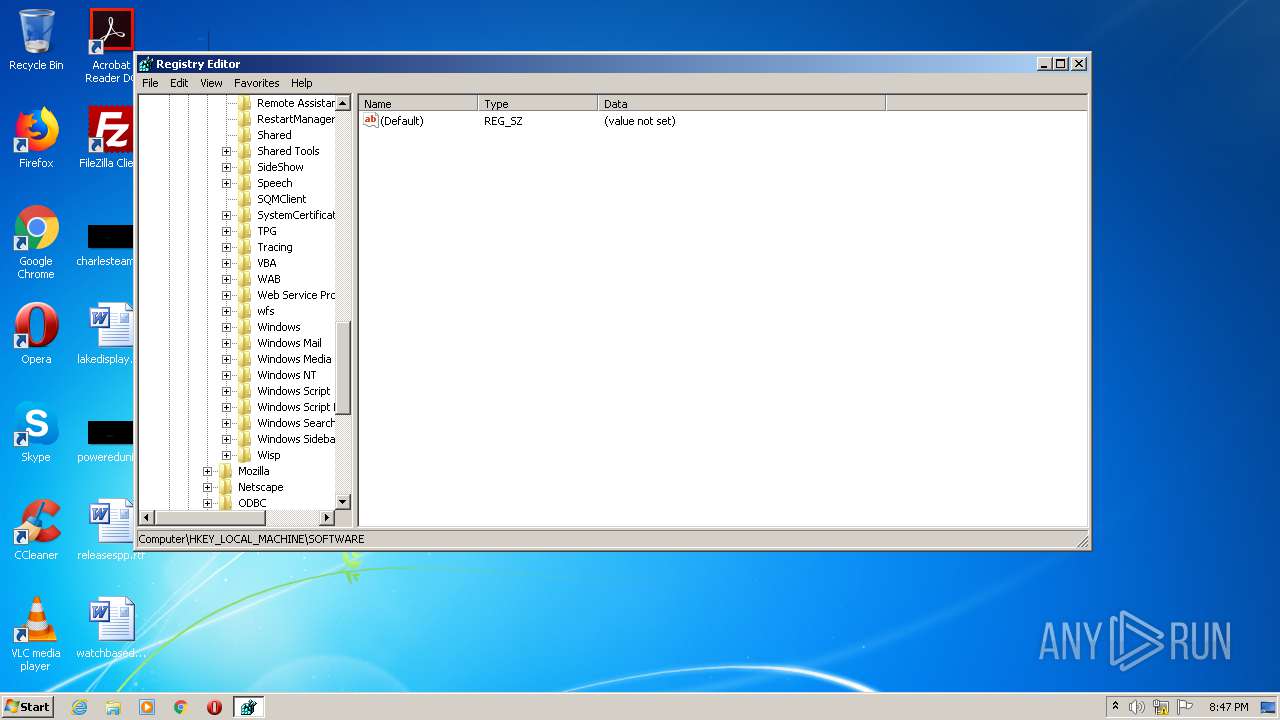
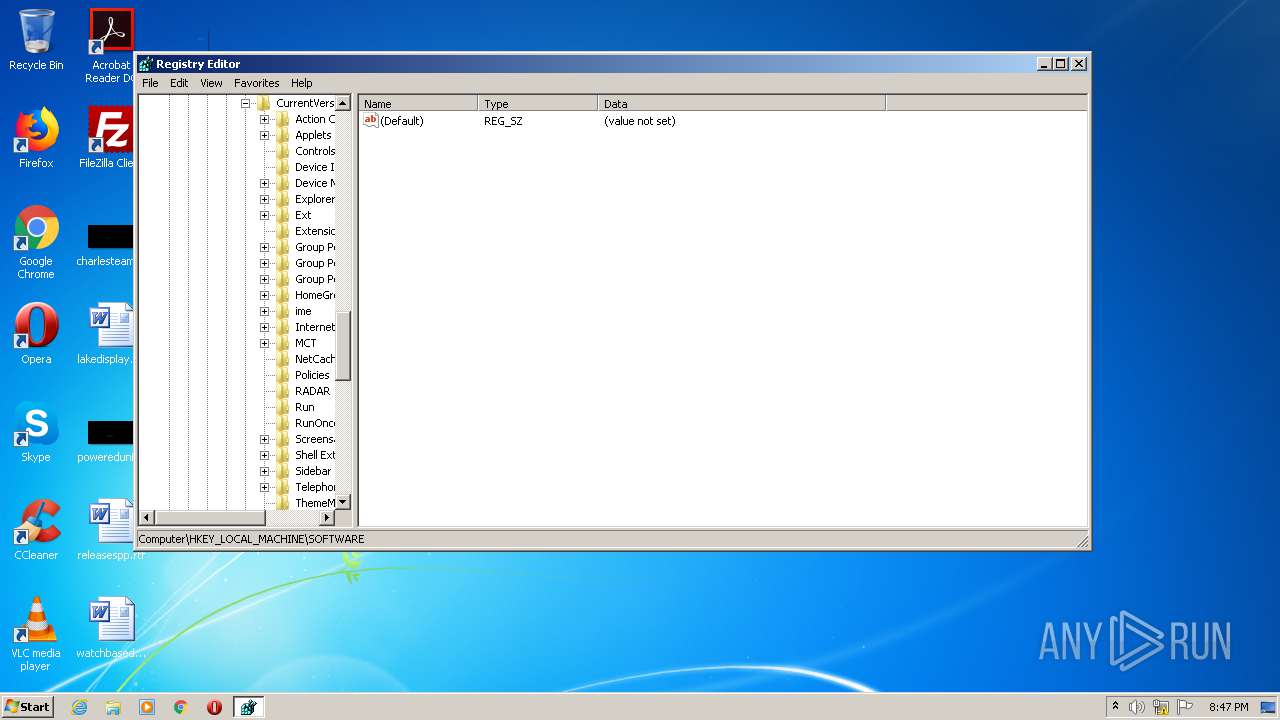
Changes the autorun value in the registry
- reg.exe (PID: 2240)
- AddInProcess32.exe (PID: 372)
Application was dropped or rewritten from another process
- AddInProcess32.exe (PID: 372)
Actions looks like stealing of personal data
- AddInProcess32.exe (PID: 372)
SUSPICIOUS
Executable content was dropped or overwritten
- Microsoft.exe (PID: 2768)
- AddInProcess32.exe (PID: 372)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3704)
Starts CMD.EXE for commands execution
- Microsoft.exe (PID: 2768)
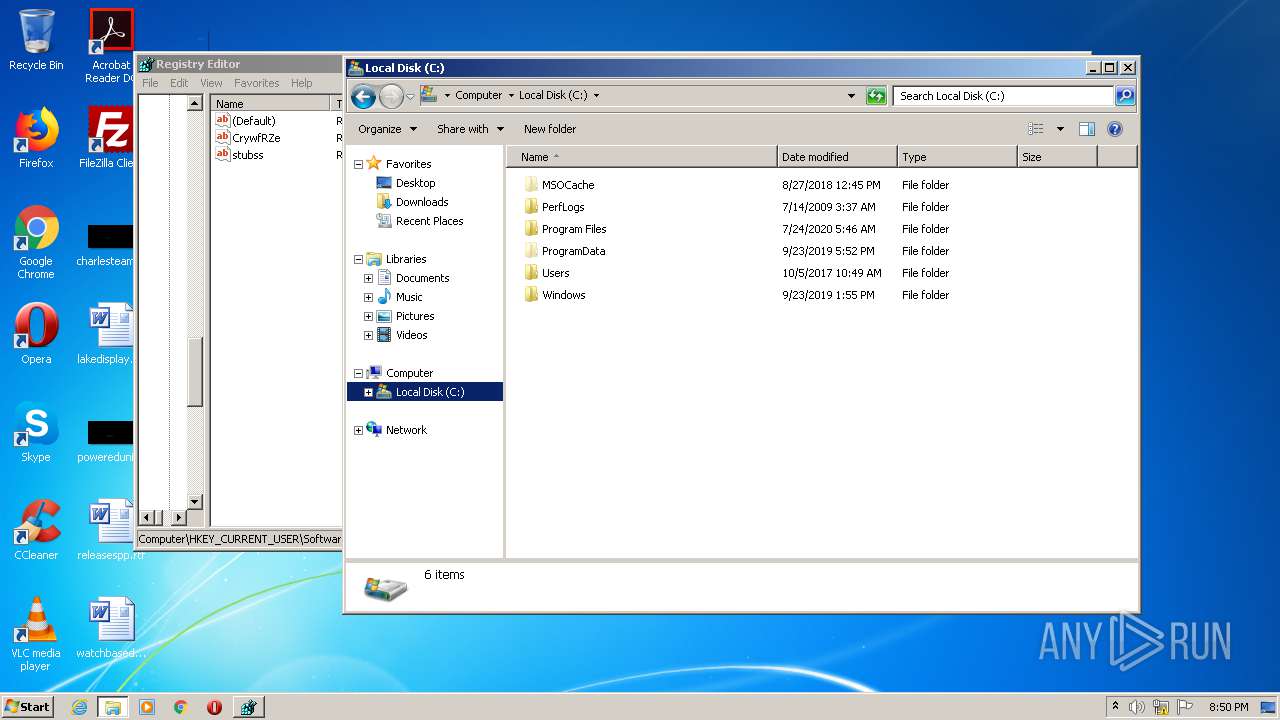
Creates files in the user directory
- Microsoft.exe (PID: 2768)
- AddInProcess32.exe (PID: 372)
Starts itself from another location
- Microsoft.exe (PID: 2768)
Reads the cookies of Google Chrome
- AddInProcess32.exe (PID: 372)
Reads Environment values
- AddInProcess32.exe (PID: 372)
Reads the cookies of Mozilla Firefox
- AddInProcess32.exe (PID: 372)
INFO
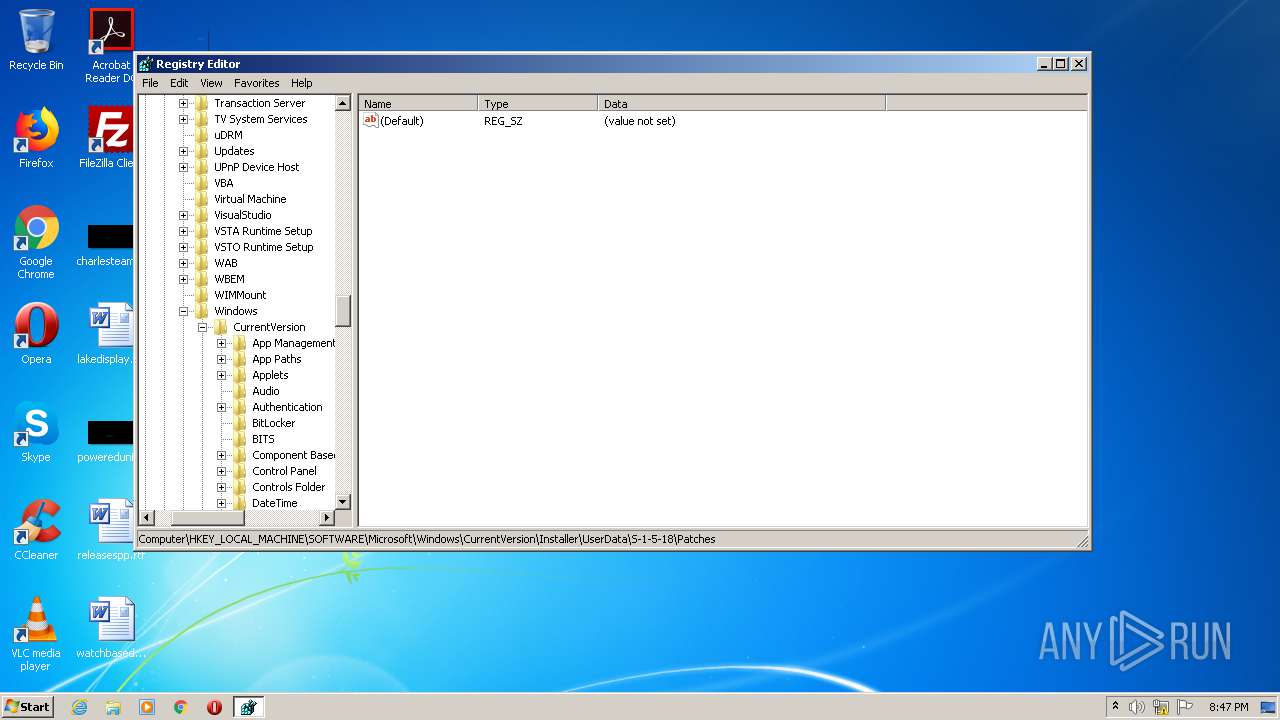
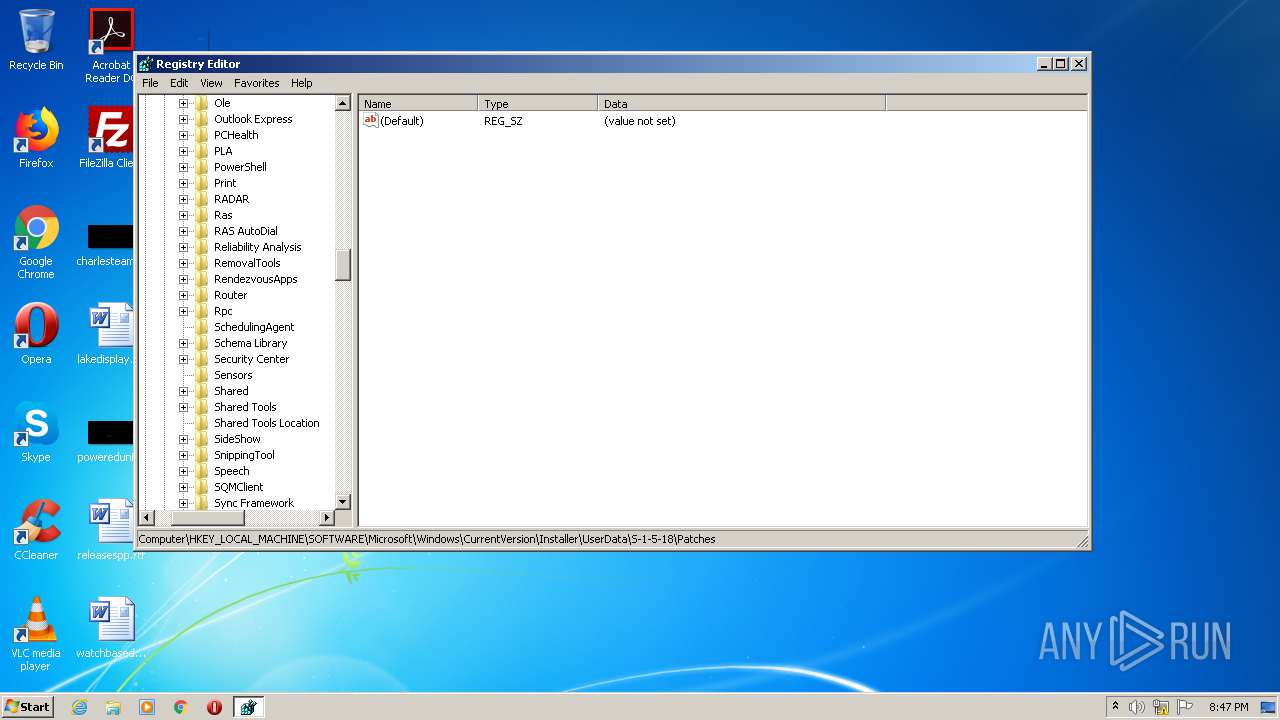
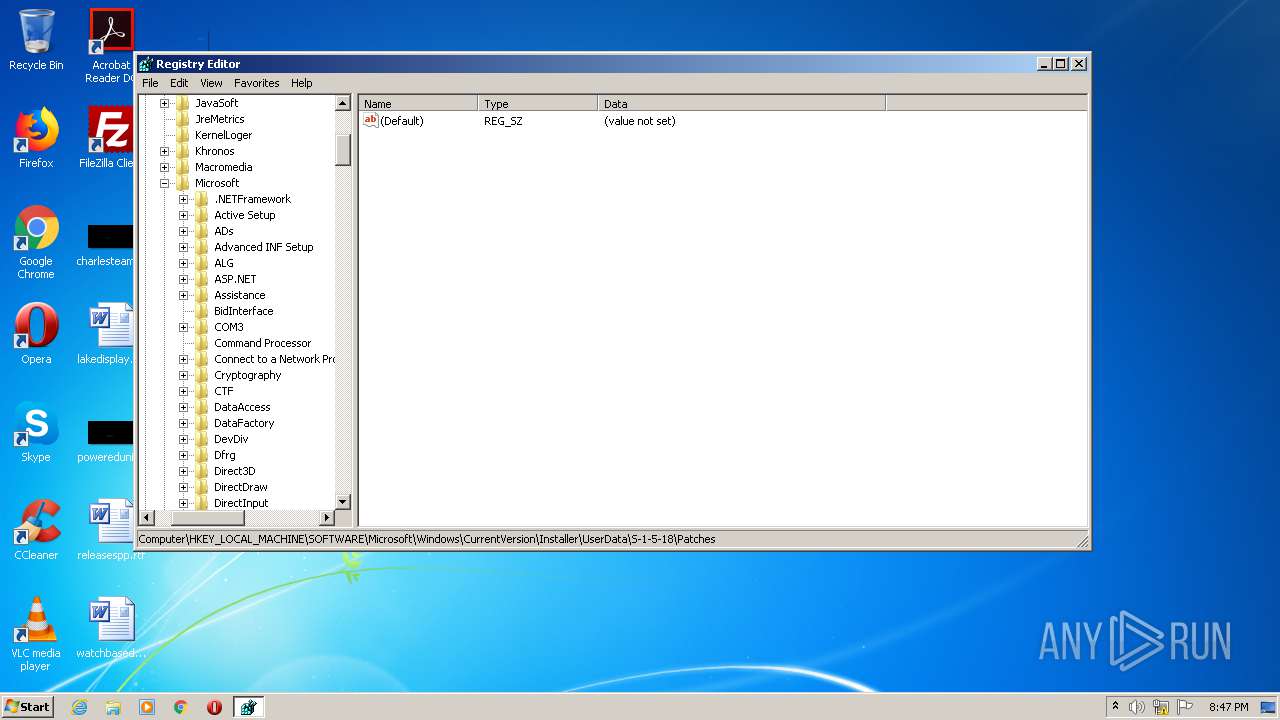
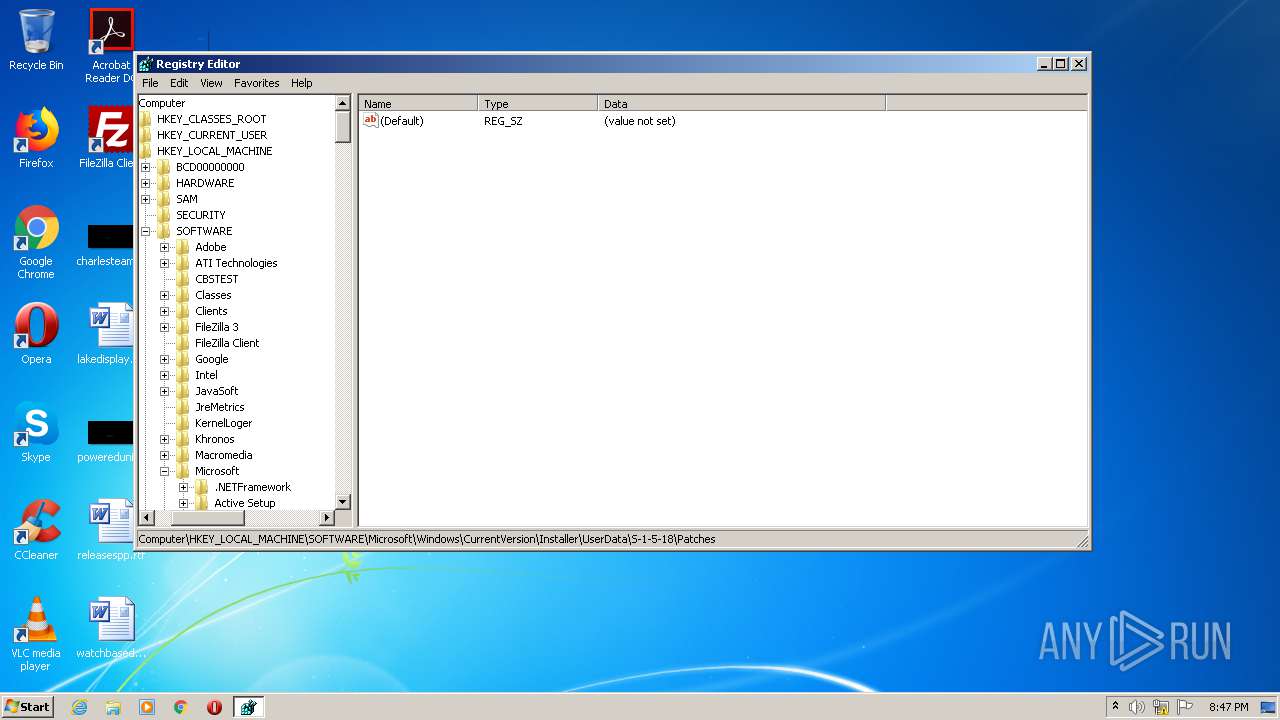
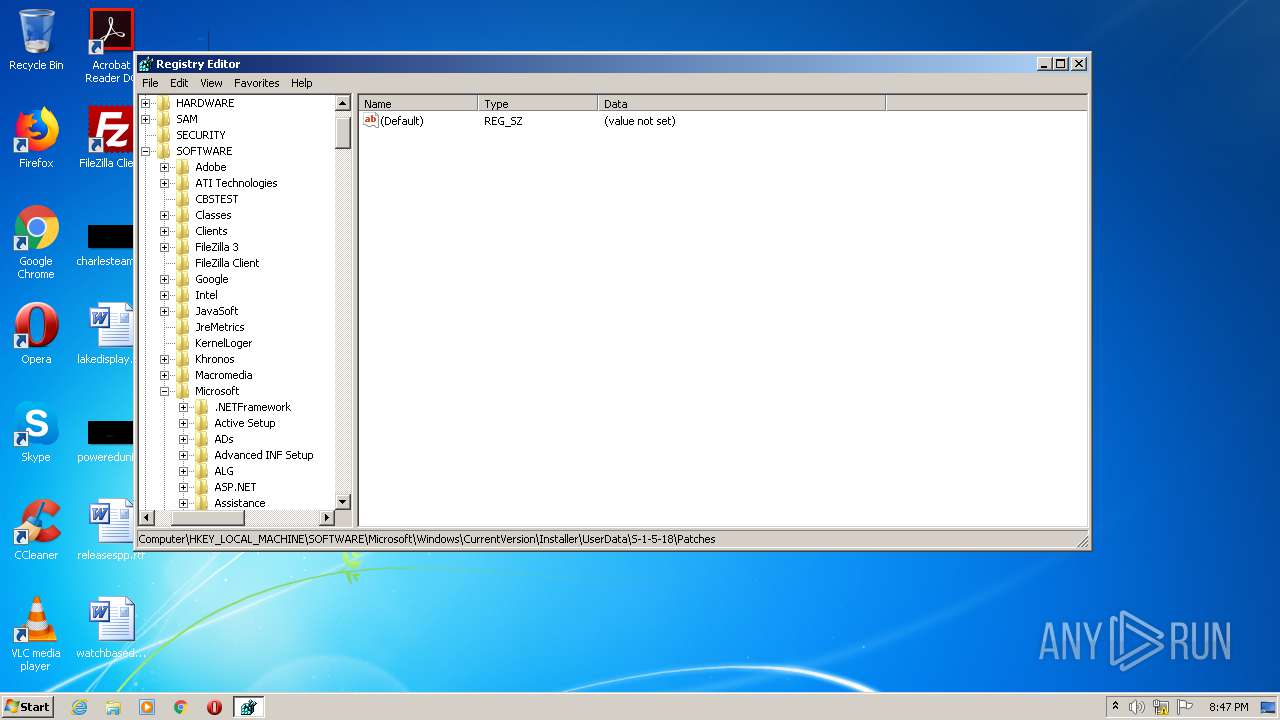
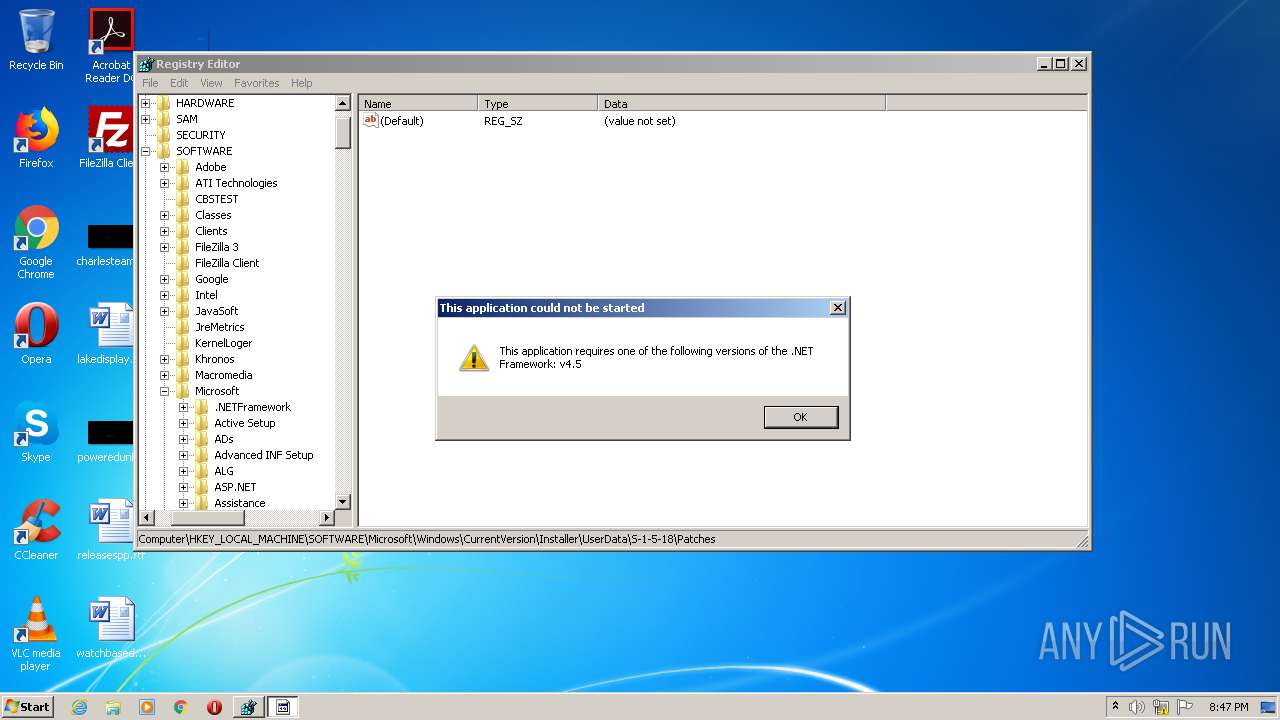
Manual execution by user
- regedit.exe (PID: 3240)
- regedit.exe (PID: 440)
- explorer.exe (PID: 180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:03 16:07:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 637952 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9da7e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.14.19.24 |
| ProductVersionNumber: | 9.14.19.24 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | D)k25L*po(4H$ |
| CompanyName: | mY~5Q4g@!fE27B(q |
| FileDescription: | i!8E3oR$k|6XJw/ |
| FileVersion: | 9.14.19.24 |
| InternalName: | Microsoft.exe |
| LegalCopyright: | Copyright © 2018 - 2019 |
| OriginalFileName: | Microsoft.exe |
| ProductName: | i!8E3oR$k|6XJw/ |
| ProductVersion: | 9.14.19.24 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Oct-2019 14:07:27 |
| Comments: | D)k25L*po(4H$ |
| CompanyName: | mY~5Q4g@!fE27B(q |
| FileDescription: | i!8E3oR$k|6XJw/ |
| FileVersion: | 9.14.19.24 |
| InternalName: | Microsoft.exe |
| LegalCopyright: | Copyright © 2018 - 2019 |
| OriginalFilename: | Microsoft.exe |
| ProductName: | i!8E3oR$k|6XJw/ |
| ProductVersion: | 9.14.19.24 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 03-Oct-2019 14:07:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0009BA84 | 0x0009BC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.22462 |
.rsrc | 0x0009E000 | 0x00027FFE | 0x00028000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.96894 |
.reloc | 0x000C6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.03309 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 6.00948 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.82749 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.10367 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.00794 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.26919 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 6.1021 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
51
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
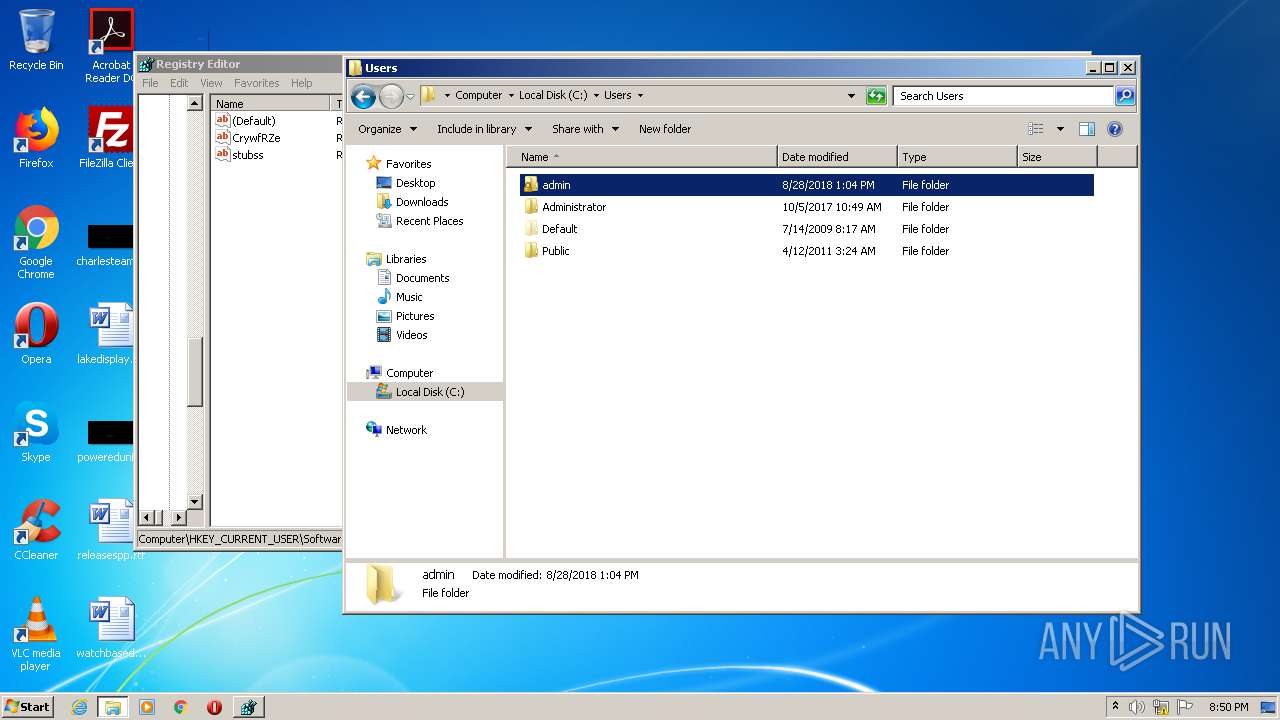
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
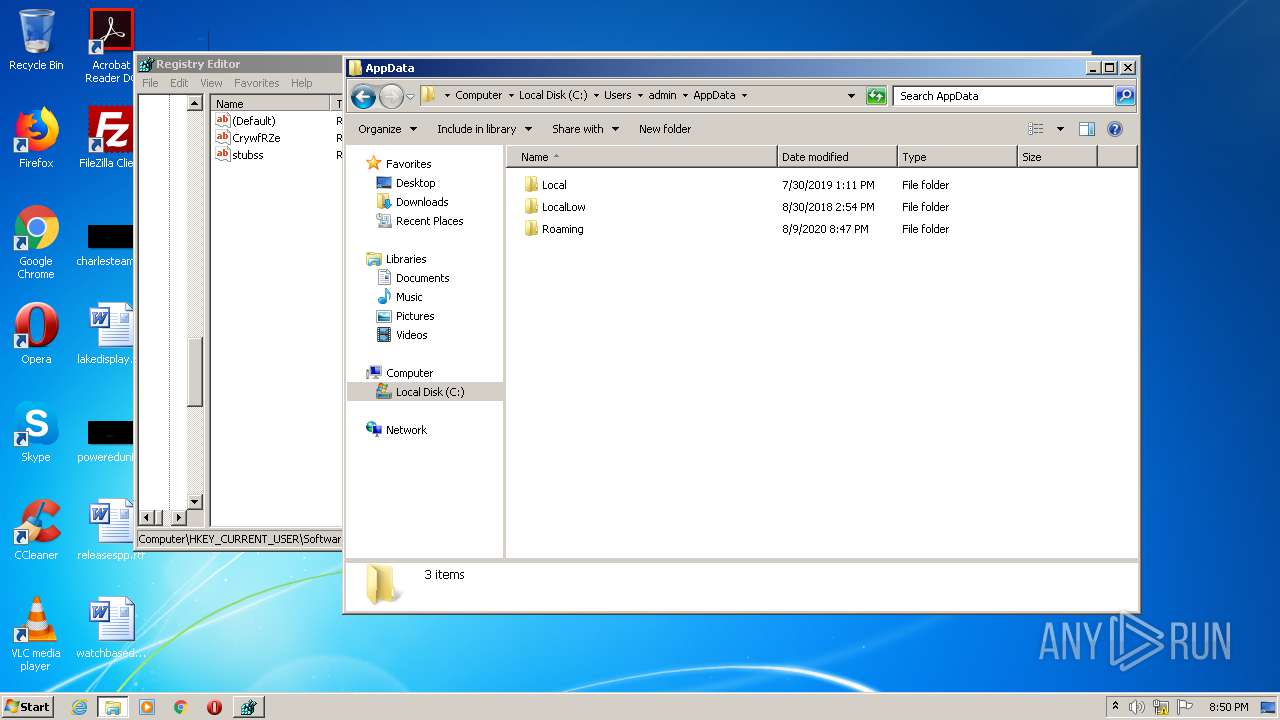
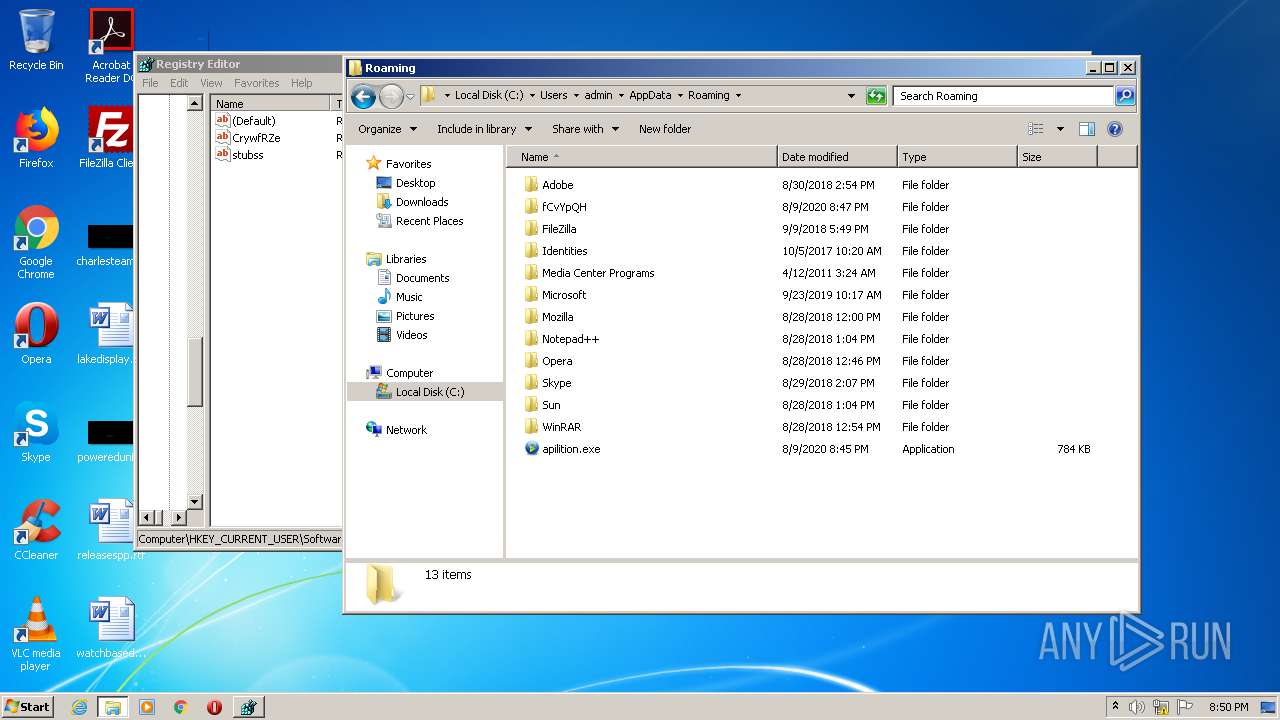
| 372 | "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | apilition.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 440 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
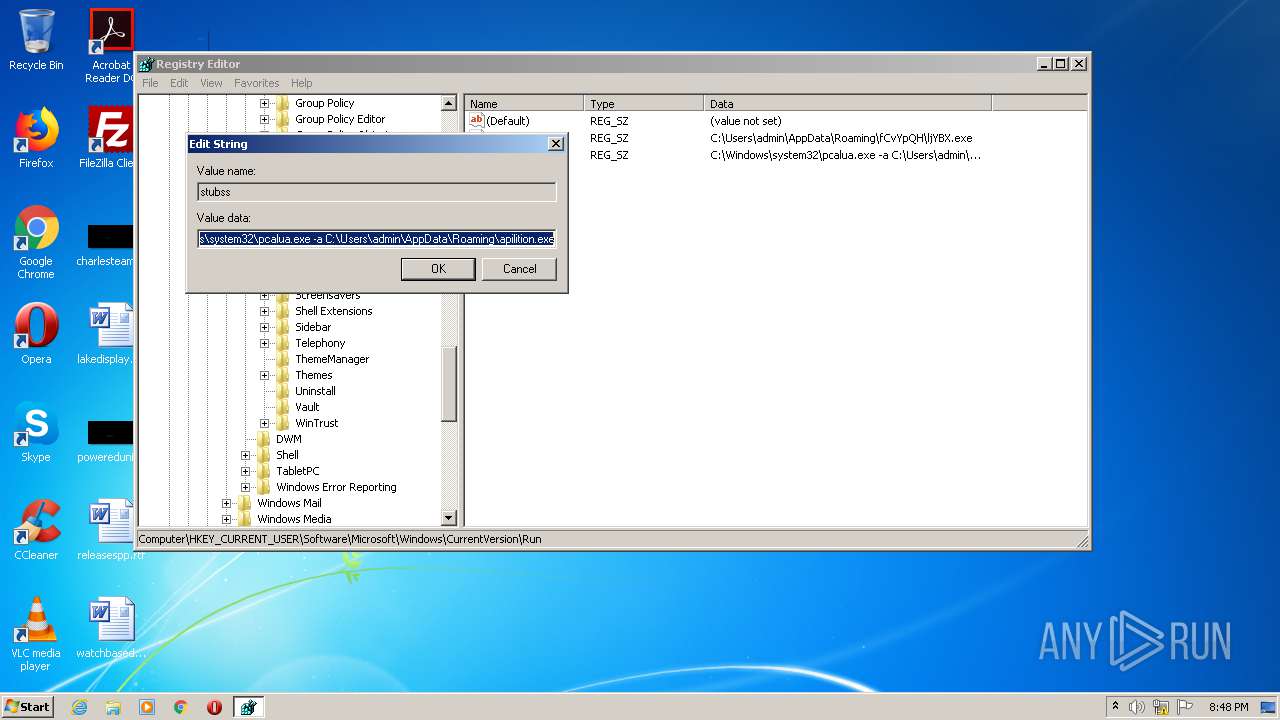
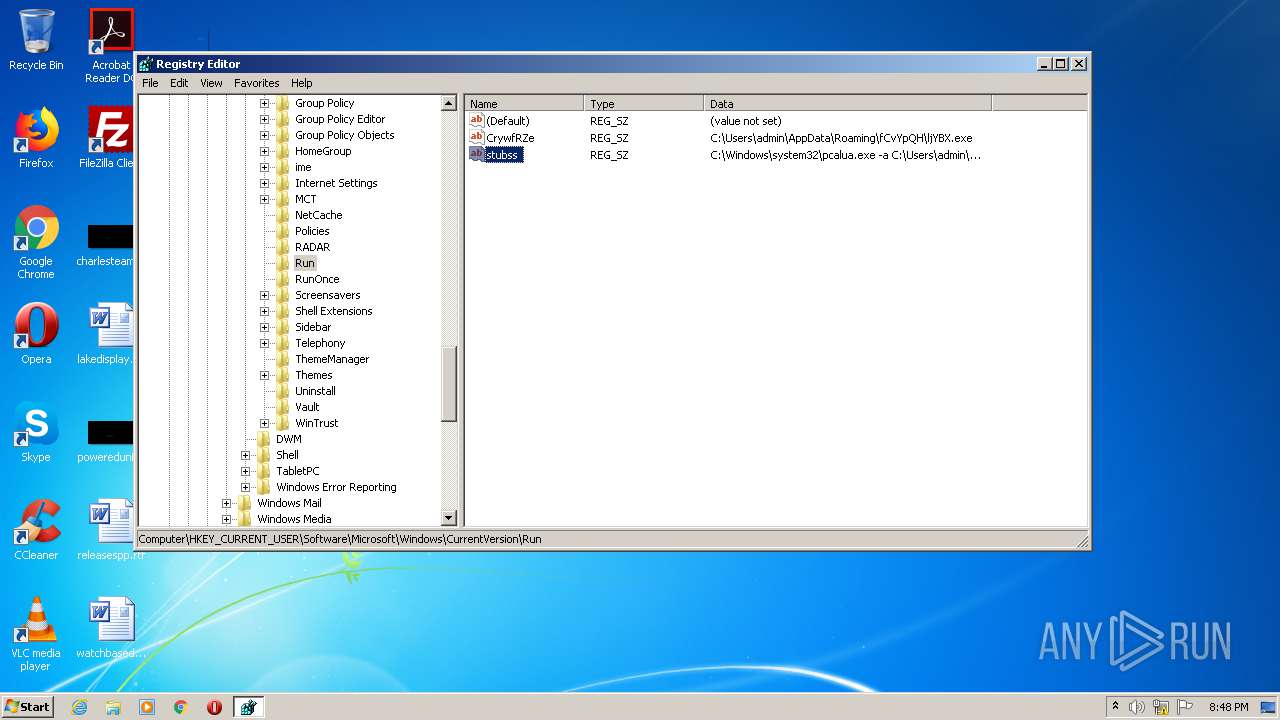
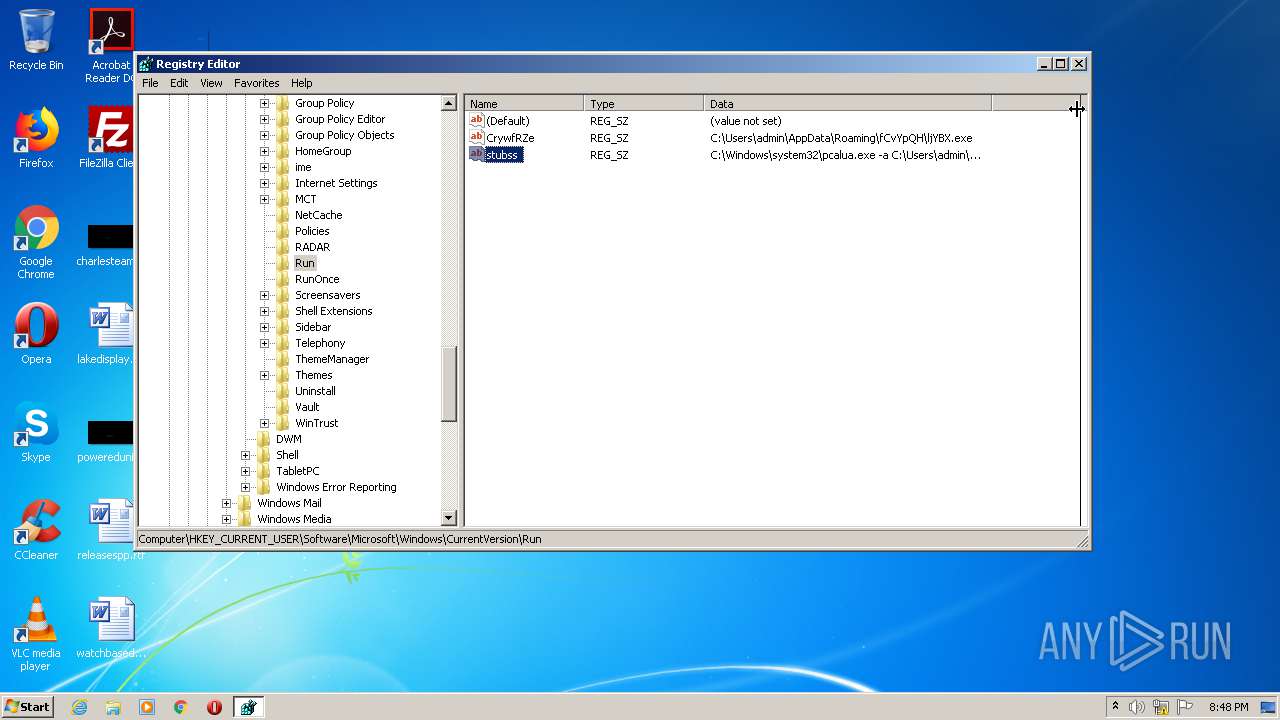
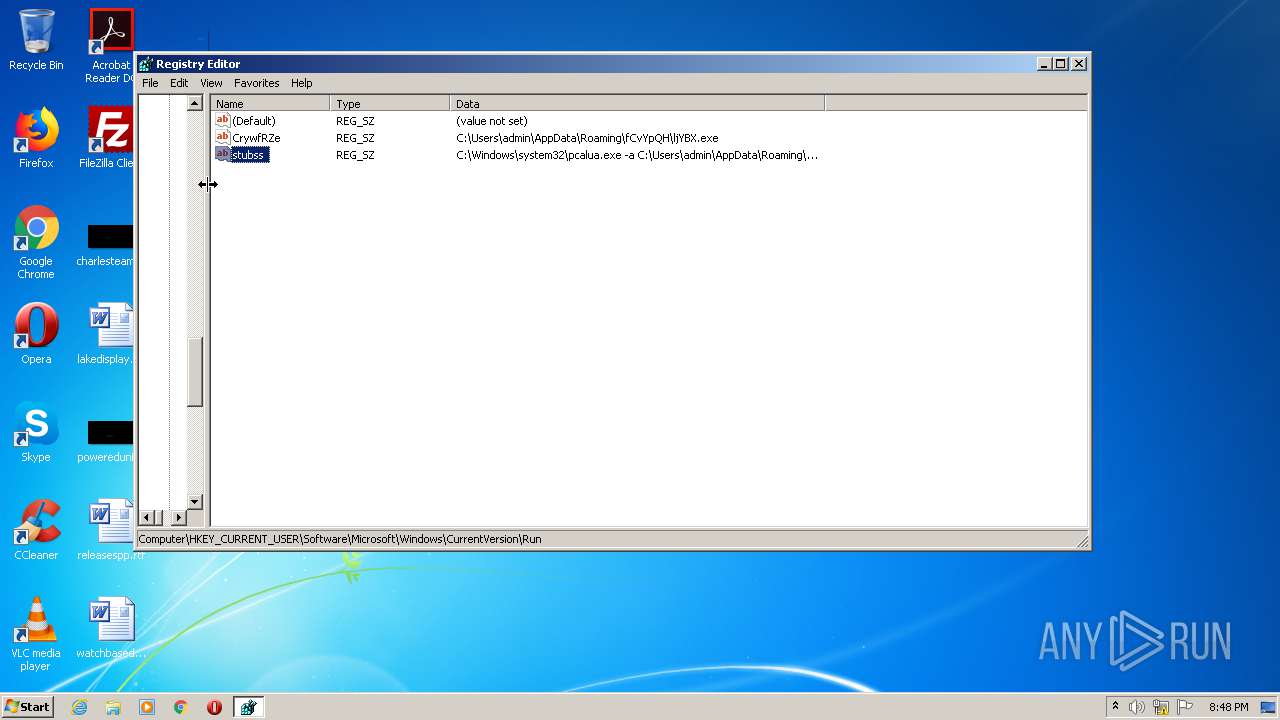
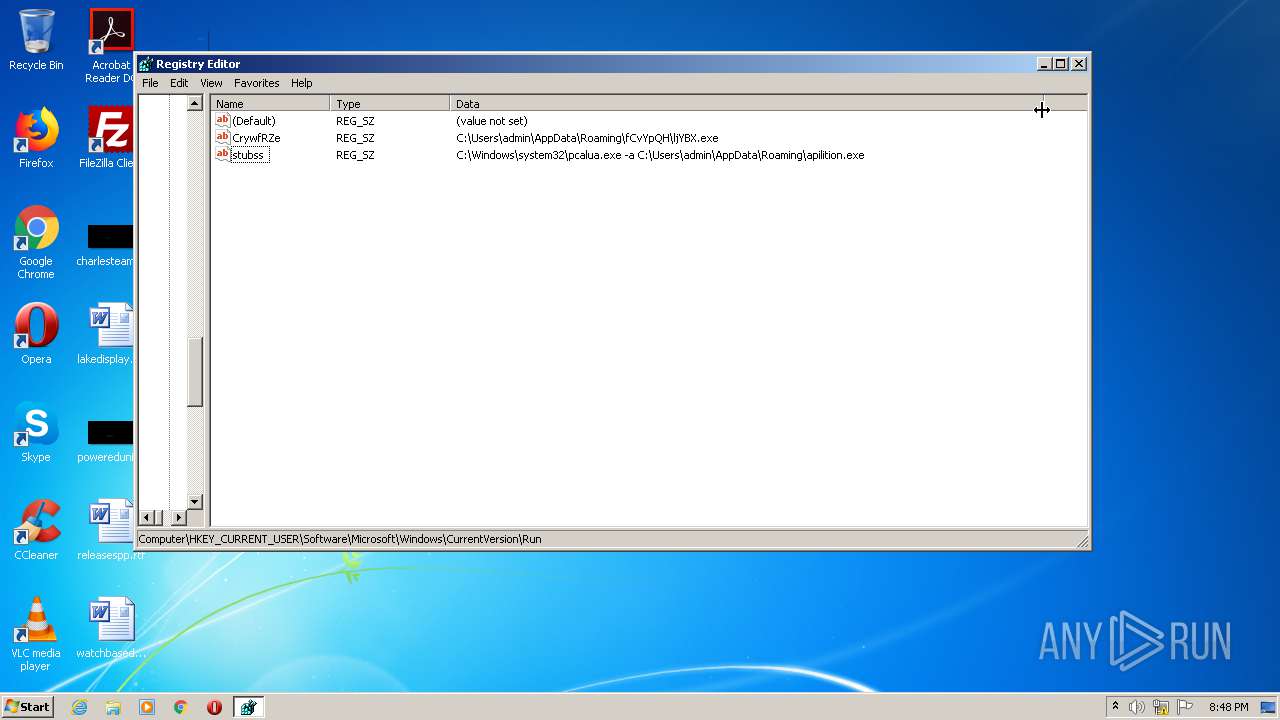
| 2240 | REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /f /v stubss /t REG_SZ /d C:\Windows\system32\pcalua.exe" -a C:\Users\admin\AppData\Roaming\apilition.exe" | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\Microsoft.exe" | C:\Users\admin\AppData\Local\Temp\Microsoft.exe | explorer.exe | ||||||||||||
User: admin Company: mY~5Q4g@!fE27B(q Integrity Level: MEDIUM Description: i!8E3oR$k|6XJw/ Exit code: 0 Version: 9.14.19.24 Modules
| |||||||||||||||
| 3240 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3704 | "C:\Windows\System32\cmd.exe" /c REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /f /v stubss /t REG_SZ /d C:\Windows\system32\pcalua.exe" -a C:\Users\admin\AppData\Roaming\apilition.exe" | C:\Windows\System32\cmd.exe | — | Microsoft.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4028 | "C:\Users\admin\AppData\Roaming\apilition.exe" | C:\Users\admin\AppData\Roaming\apilition.exe | — | Microsoft.exe | |||||||||||
User: admin Company: mY~5Q4g@!fE27B(q Integrity Level: MEDIUM Description: i!8E3oR$k|6XJw/ Exit code: 0 Version: 9.14.19.24 Modules
| |||||||||||||||
Total events
496
Read events
480
Write events
16
Delete events
0
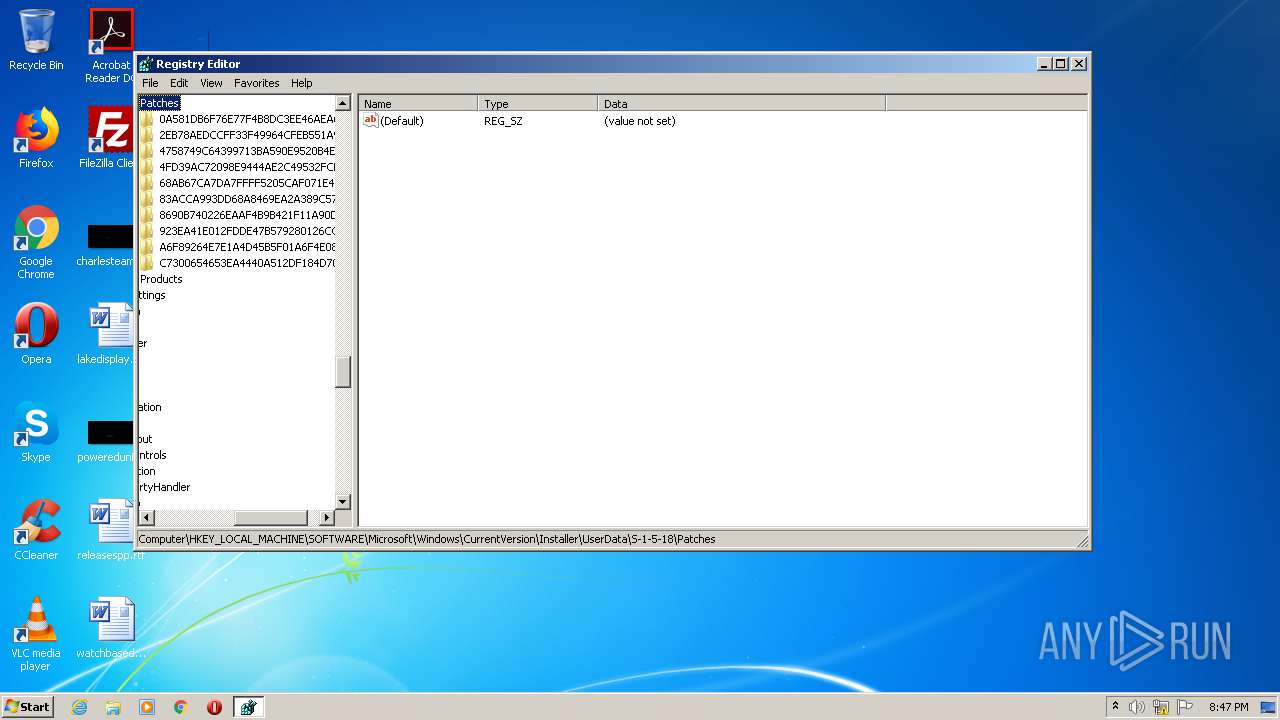
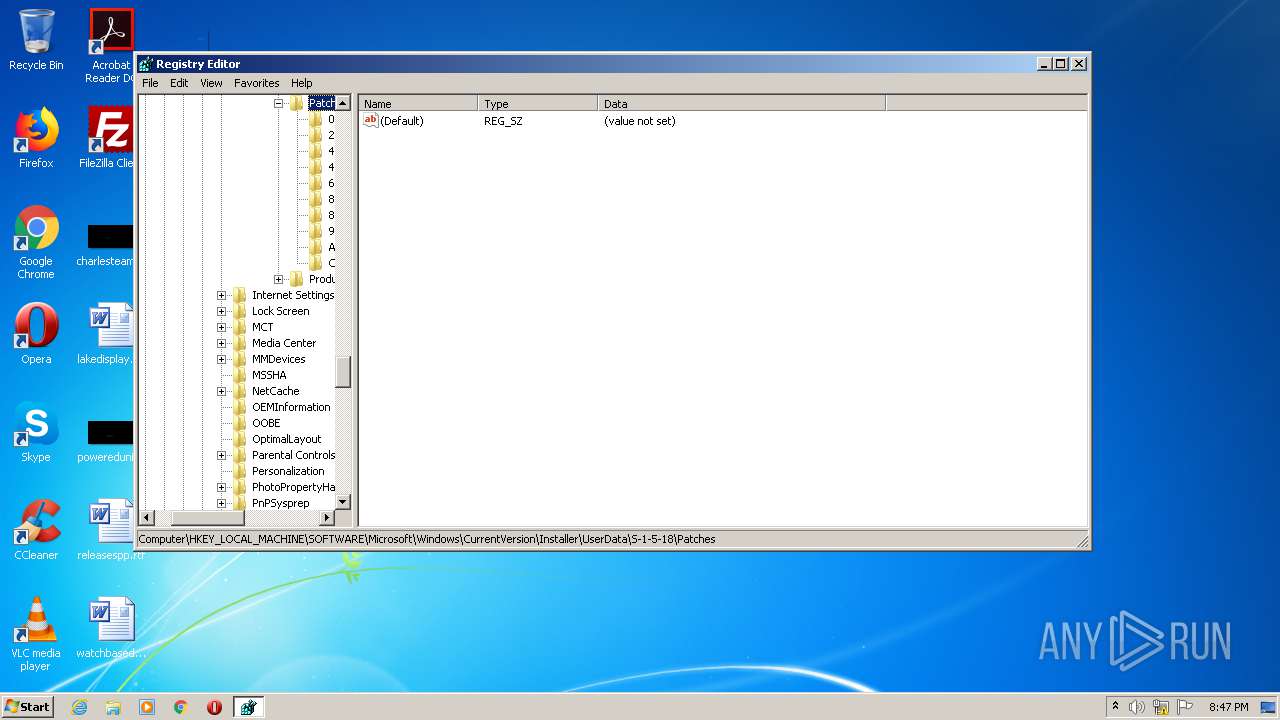
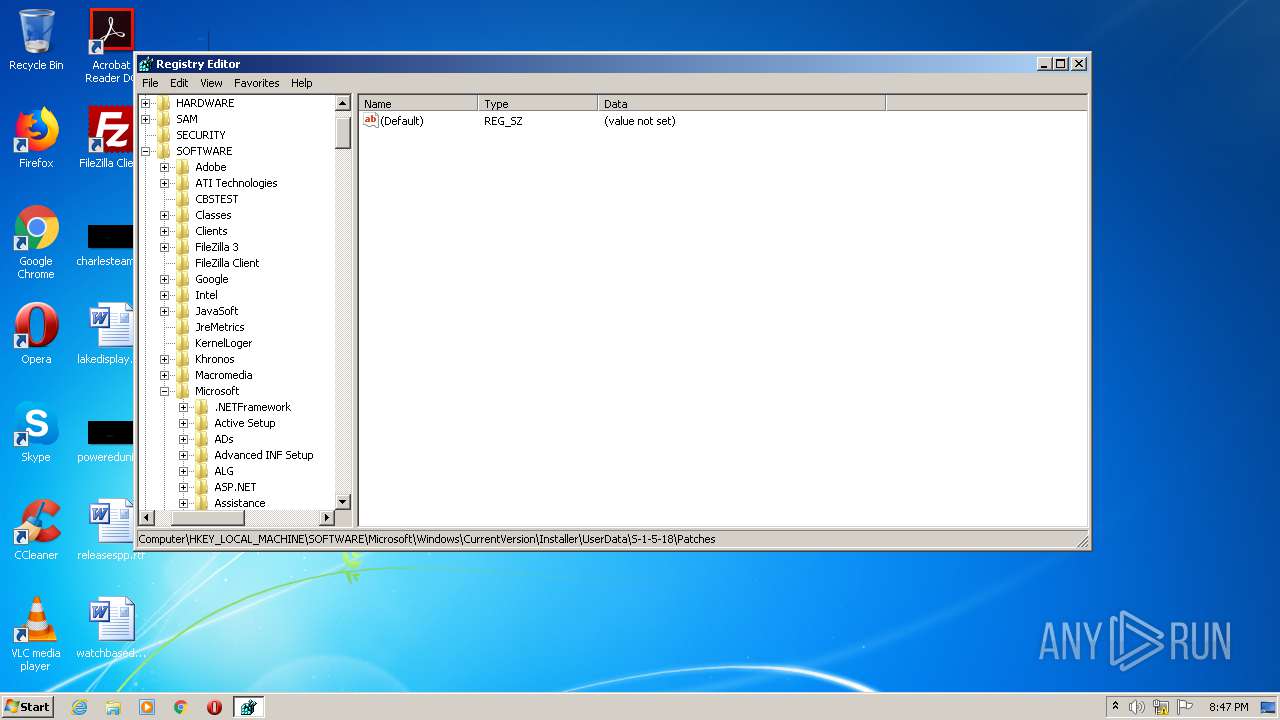
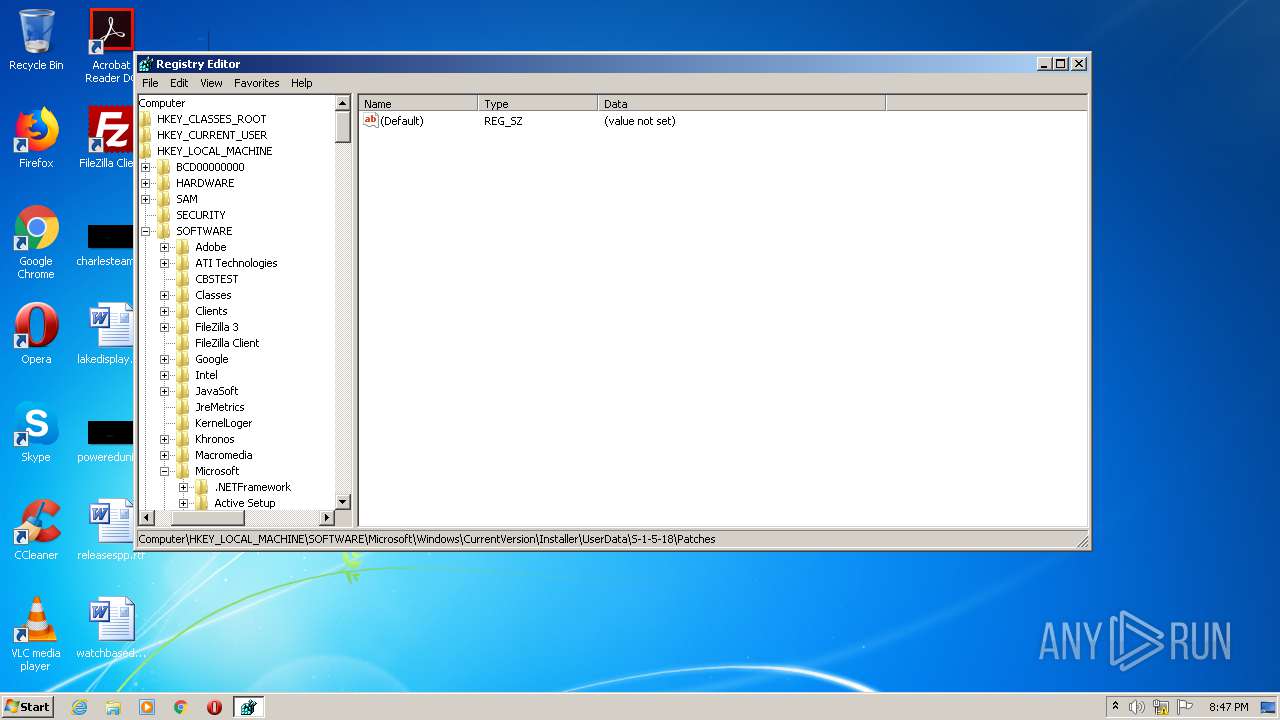
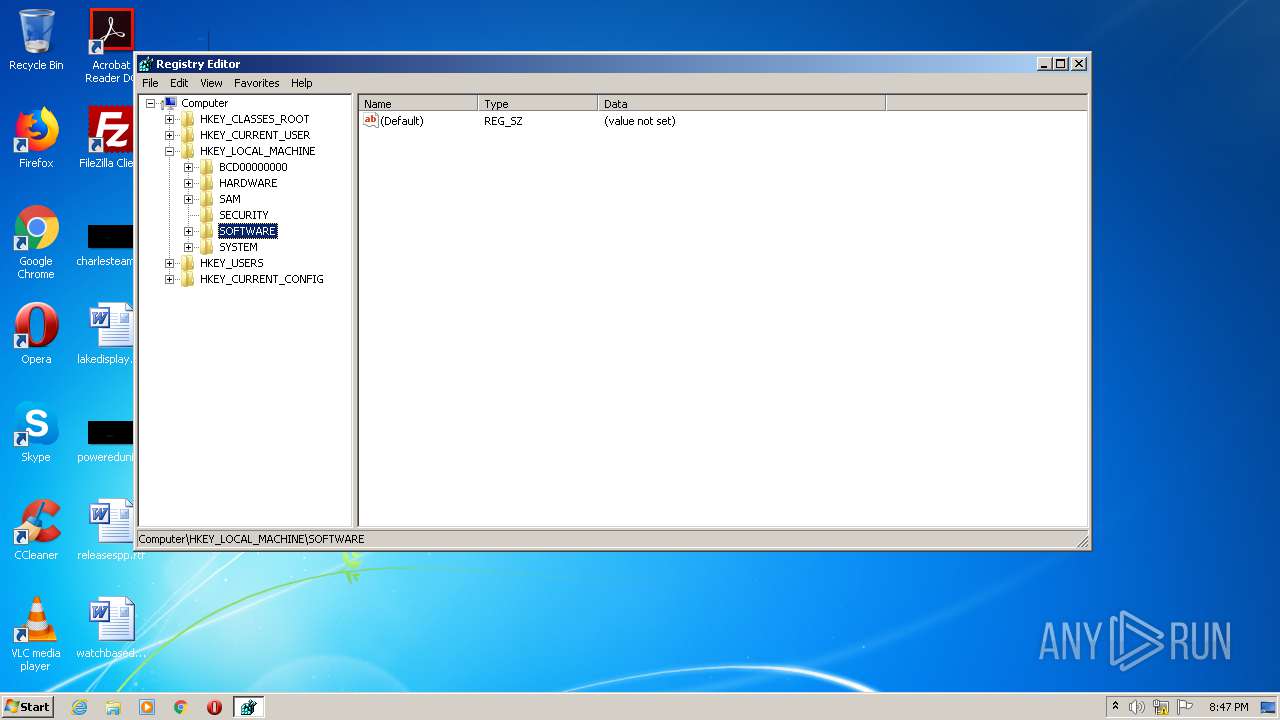
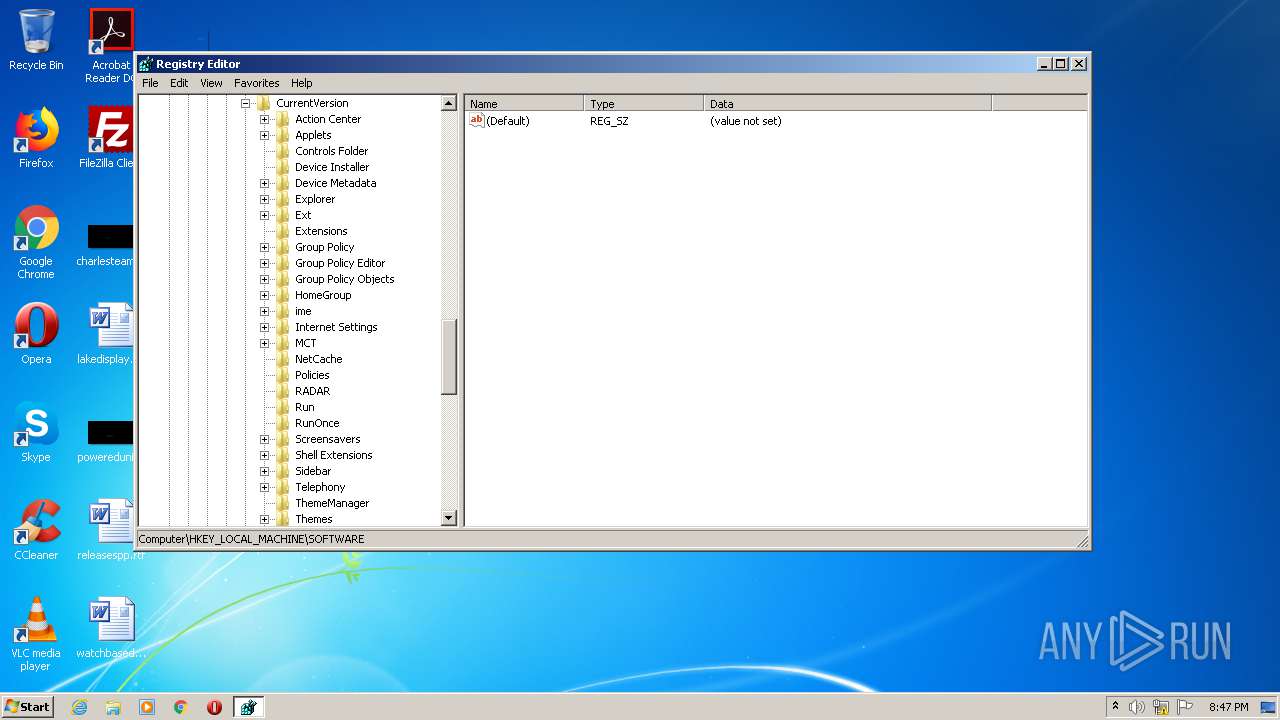
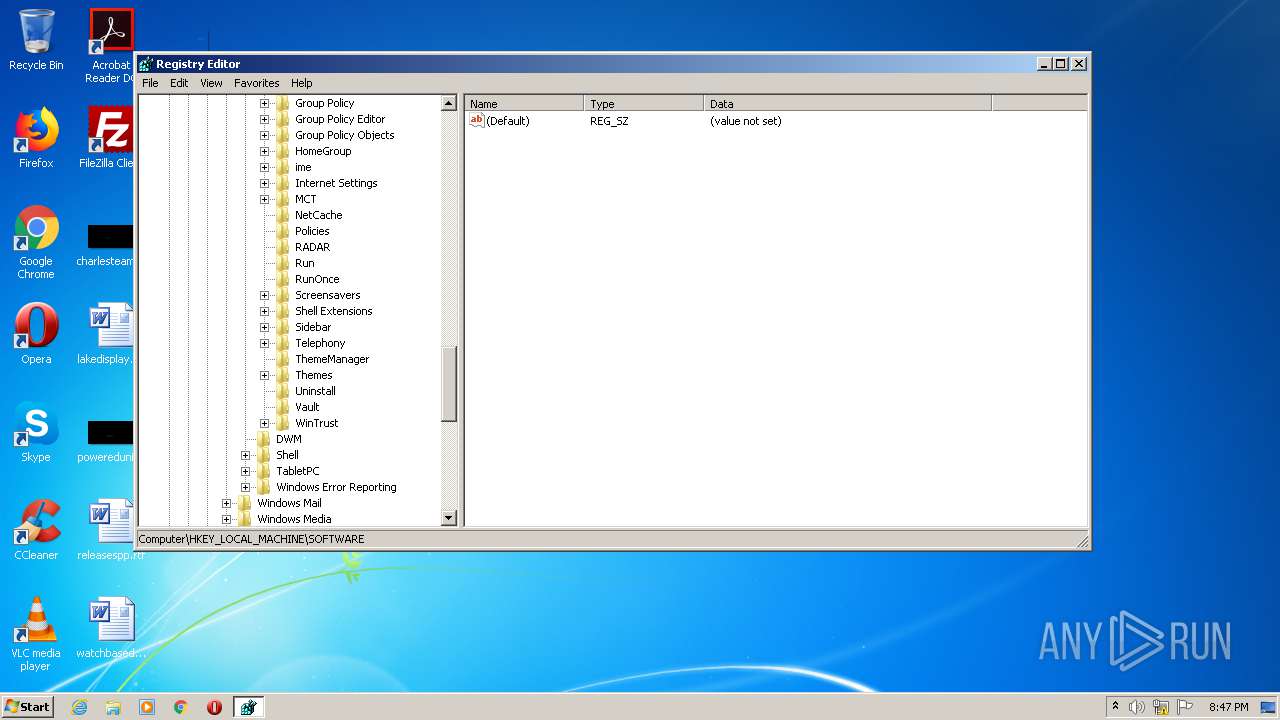
Modification events
| (PID) Process: | (2240) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | stubss |
Value: C:\Windows\system32\pcalua.exe -a C:\Users\admin\AppData\Roaming\apilition.exe | |||
| (PID) Process: | (2768) Microsoft.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2768) Microsoft.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
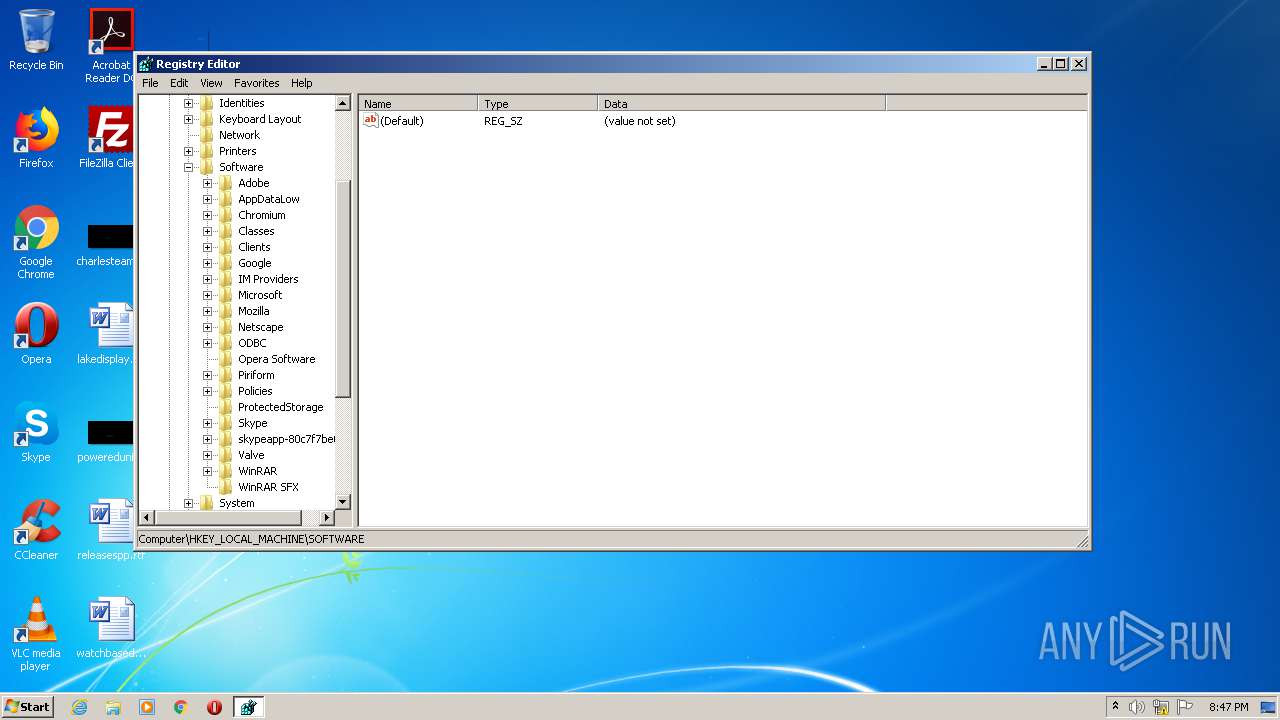
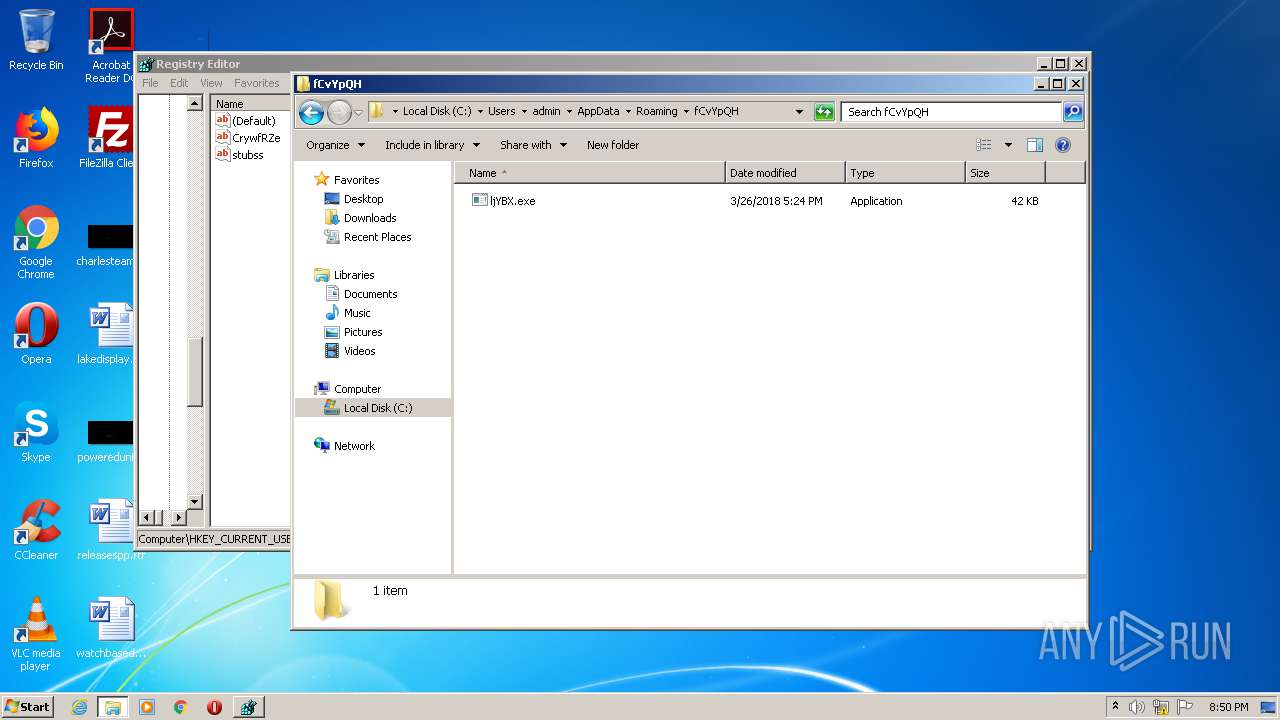
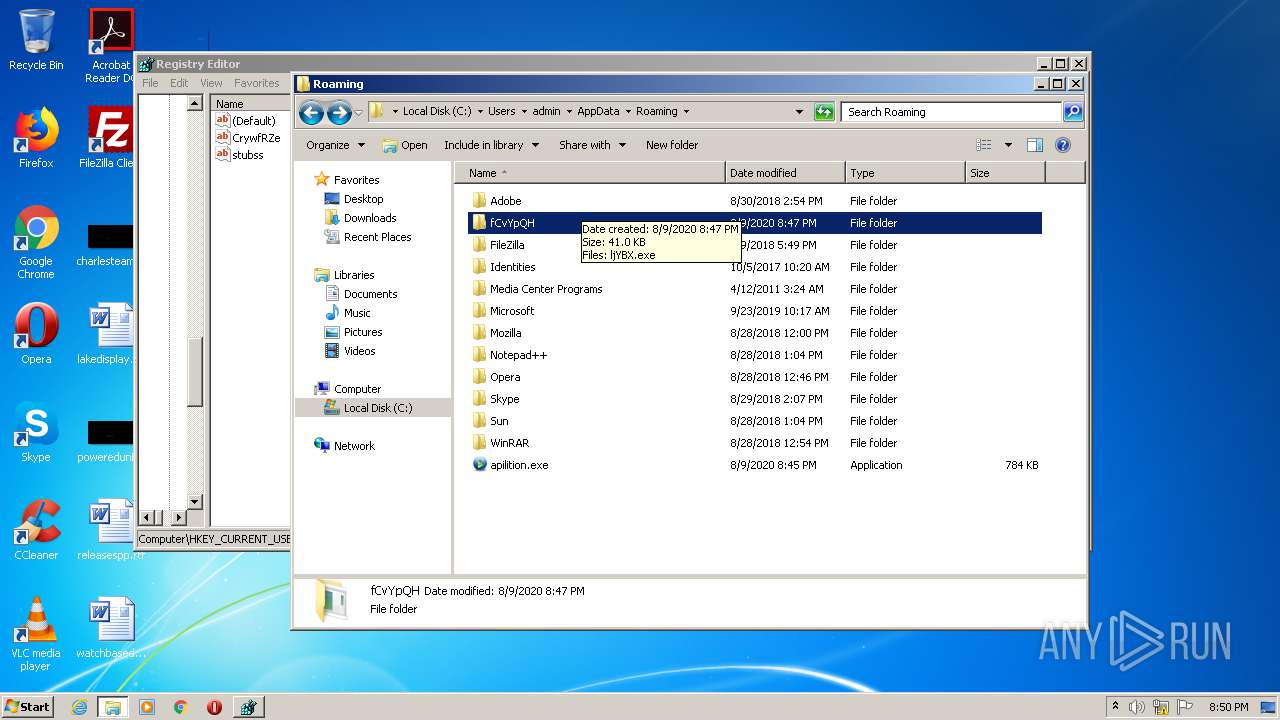
| (PID) Process: | (372) AddInProcess32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CrywfRZe |
Value: C:\Users\admin\AppData\Roaming\fCvYpQH\ljYBX.exe | |||
| (PID) Process: | (372) AddInProcess32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\wtzw4u0l.xvc\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 2768 | Microsoft.exe | C:\Users\admin\AppData\Roaming\apilition.exe | executable | |
MD5:— | SHA256:— | |||
| 372 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\wtzw4u0l.xvc\Chrome\Default\Cookies | sqlite | |
MD5:— | SHA256:— | |||
| 372 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\wtzw4u0l.xvc.zip | compressed | |
MD5:— | SHA256:— | |||
| 372 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\fCvYpQH\ljYBX.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
| 2768 | Microsoft.exe | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
372 | AddInProcess32.exe | 66.102.1.109:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
smtp.gmail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
372 | AddInProcess32.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
372 | AddInProcess32.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |