| File name: | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe |
| Full analysis: | https://app.any.run/tasks/1ed7eefb-85b0-4a0a-ad9e-d947223f0742 |
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2025, 12:15:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 869721AB903879B396B1415850AC925A |
| SHA1: | 6C4378B8DDB2123206BF7CFECD3A40517C07F05D |
| SHA256: | 46CC6FB420B3A29E077F05DCD18D18CF03B381B71DCC850157F40520D2C937E7 |
| SSDEEP: | 98304:HZJEiDzP7sSaCtbDv8c2QIfVxKXOuWQ/uQ5KQz856DN/aItLXxBSKZrtqiTtalls:TD/ydO5kEvCeAc |
MALICIOUS
Executing a file with an untrusted certificate
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
- MiniThunderPlatform.exe (PID: 8168)
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7608)
- XLBugReport.exe (PID: 8136)
Changes settings of System certificates
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- XLBugReport.exe (PID: 8136)
Executable content was dropped or overwritten
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Drops 7-zip archiver for unpacking
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Adds/modifies Windows certificates
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
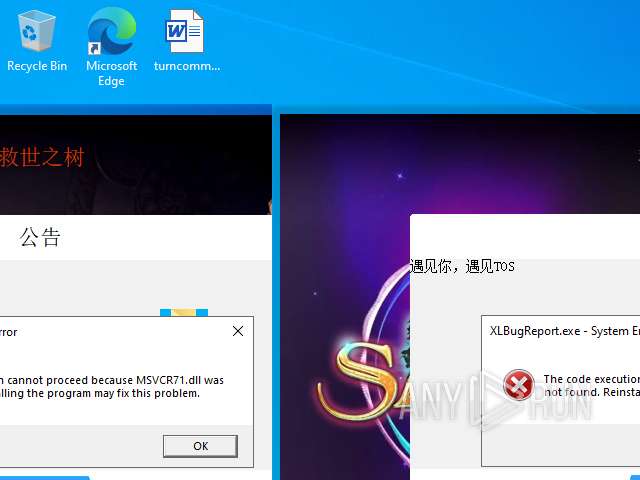
The process drops C-runtime libraries
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Process drops legitimate windows executable
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
INFO
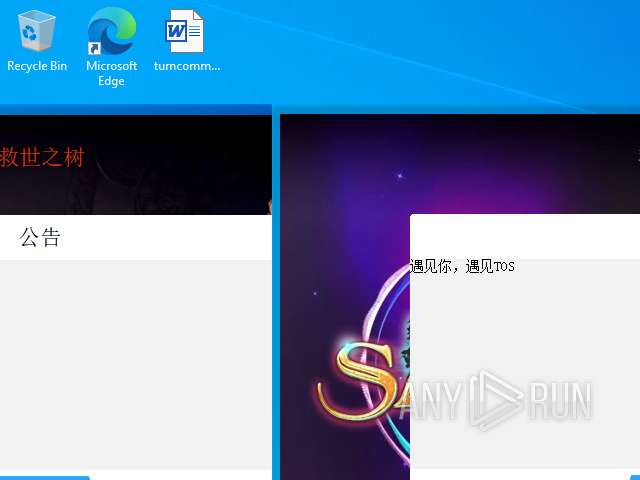
The sample compiled with chinese language support
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Checks supported languages
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
- Lzx_aria2c.exe (PID: 7328)
Reads the computer name
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Creates files or folders in the user directory
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Checks proxy server information
- slui.exe (PID: 3568)
Reads the software policy settings
- slui.exe (PID: 3568)
The sample compiled with english language support
- 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe (PID: 7796)
Manual execution by a user
- XLBugReport.exe (PID: 8136)
- Lzx_aria2c.exe (PID: 7328)
- MiniThunderPlatform.exe (PID: 8168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:09:06 05:07:26+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1359360 |
| InitializedDataSize: | 8631808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xff32f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | 专业版Ver0.1.7 (729888) |
| FileVersion: | 1.0.0.1 |
| InternalName: | ConsoleA.exe |
| LegalCopyright: | Copyright (C) 2024 |
| OriginalFileName: | Pro |
| ProductName: | Downloader |
| ProductVersion: | 1.0.0.1 |
Total processes
151
Monitored processes
7
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3568 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Lzx_aria2c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7328 | "C:\Users\admin\Desktop\Downloader_Por\Lzx_aria2c.exe" | C:\Users\admin\Desktop\Downloader_Por\Lzx_aria2c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7608 | "C:\Users\admin\Desktop\46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe" | C:\Users\admin\Desktop\46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 专业版Ver0.1.7 (729888) Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 7796 | "C:\Users\admin\Desktop\46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe" | C:\Users\admin\Desktop\46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 专业版Ver0.1.7 (729888) Version: 1.0.0.1 Modules
| |||||||||||||||
| 8136 | "C:\Users\admin\Desktop\Downloader_Por\download\XLBugReport.exe" | C:\Users\admin\Desktop\Downloader_Por\download\XLBugReport.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 迅雷错误报告 Version: 2, 2, 0, 12 Modules
| |||||||||||||||
| 8168 | "C:\Users\admin\Desktop\Downloader_Por\download\MiniThunderPlatform.exe" | C:\Users\admin\Desktop\Downloader_Por\download\MiniThunderPlatform.exe | — | explorer.exe | |||||||||||
User: admin Company: 深圳市迅雷网络技术有限公司 Integrity Level: MEDIUM Description: 迅雷云加速开放平台 Version: 3.2.1.36 Modules
| |||||||||||||||
Total events
7 454
Read events
7 452
Write events
1
Delete events
1
Modification events
| (PID) Process: | (7796) 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | CC1C64DFEE39E07D053AC69522B1089D1C39749D |
Value: | |||
| (PID) Process: | (7796) 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\CC1C64DFEE39E07D053AC69522B1089D1C39749D |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000CC1C64DFEE39E07D053AC69522B1089D1C39749D2000000001000000FA020000308202F6308201E2A00302010202103F5BA01C60CBF1B2447D05F57975A021300906052B0E03021D050030153113301106035504031E0A4E134E1A4E0B8F7D5668301E170D3235303133303134343632375A170D3339313233313233353935395A30153113301106035504031E0A4E134E1A4E0B8F7D566830820122300D06092A864886F70D01010105000382010F003082010A0282010100D873B5208726FBF05B8CB6FD97393716300F9A4B787C20A516C4FE3A5A287947DD7FC65D5E7BF00D8864083D659A693CD0FB04159B7885846CECB46F7C743F2EB5880475E747C65548E3CAE7E823C7B856C640FE7C6AFAC6DDBD9B4CF5B25A27F414861C215093E0712A4E390FB59BAB81EDD129C9CEFAA183B4D0ABD6249B100095898E9F5D06990B58AED0C543A8F569B609FE99FD15288C702DF556F4C6BAF3AC4AF8E2732ADD63FE0B63EF02C4D640760A7C9F3D2CAC1E41451DD763494F26F5F2718F5E716D5F3FBC0A49E000A78516713450C44176DB44E373E344B4EFAFCE7496D9F0CE13F08499A2199A2778ECC0B7B85AA7A7AB54249D5C1BE2286D0203010001A34A304830460603551D01043F303D8010E1479FA279483823D8A9575BFE1C6863A11730153113301106035504031E0A4E134E1A4E0B8F7D566882103F5BA01C60CBF1B2447D05F57975A021300906052B0E03021D05000382010100BF07FE18F3E099C052A73A4F86AFD745E43206FB9FE76CC5352187DA37E43B6BAC4C5D1B721117B27EA27DF7E6C6F940A55163E5986EE1DCC44B02298D87C858CBFAF21B95A63FDB83C6A739AD2E575D03EE1DD1D661291ABDE70D8772133E19060FE179096997E71A6A338A403D31742AC998E251D4C5CF8C28D11D12440E85068EE8C811F07674AC3F1DE44382A00C91ECF3F16BE450CCC54CF9FC0E0E6B28DDD73D7FF3DB801BF1DC998757F0D8E13A35959BE0B85EC65CC357F124560016707703FC435F697471D189AEA5EE6F4F29F5CB7DCBDD16465C563EB9BDF442878DE1966419DD7BBE8A6FBE003A34DC25FF48E660CD698E94E1DA49FB4D0493FE | |||
Executable files
13
Suspicious files
4
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\download\atl71.dll | executable | |
MD5:79CB6457C81ADA9EB7F2087CE799AAA7 | SHA256:A68E1297FAE2BCF854B47FFA444F490353028DE1FA2CA713B6CF6CC5AA22B88A | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\aria2.conf | text | |
MD5:C048DDD7E003849AE9DF1C5F5FCDA3AE | SHA256:30D9ABDBCB13554237A754A9679F29A8CEB7ECE575DF93A742F41F3E03E2F026 | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Temp.zip | compressed | |
MD5:DACCB8279E7C774459CEB7A29029F8D6 | SHA256:FAA149503FD0FE0A8E3C936BFB511FE4A9435CDFF9DCBCEE1CE17AE6505AC257 | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\L7z.dll | executable | |
MD5:96B4C1D0683DCE22BD3223E1E40689C1 | SHA256:51075AF59F6696D5DC5446BA39FABFD0022628CDCFA41C80E7CB66E3BF4EE55D | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\download\MiniThunderPlatform.exe | executable | |
MD5:9F1D3DFAC55080C712C0281FB2EEEB47 | SHA256:A5622E2BF46CC2EC90C4DCA70372F051BFB5BF55DA3788B5DFCA9429529D285B | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\download\msvcp71.dll | executable | |
MD5:A94DC60A90EFD7A35C36D971E3EE7470 | SHA256:6C483CBE349863C7DCF6F8CB7334E7D28C299E7D5AA063297EA2F62352F6BDD9 | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\download\download_engine.dll | executable | |
MD5:E164D5CC3D566708CAF1AA2C0E842347 | SHA256:3245995A4D7417A8DFFFF27F416F8C2F8AE15EB9D8A57A6CD371F366F2C9B808 | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\download\XLBugHandler.dll | executable | |
MD5:92154E720998ACB6FA0F7BAD63309470 | SHA256:1845DF41DA539BCA264F59365BF7453B686B9098CC94CD0E2B9A20C74A561096 | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\download\XLBugReport.exe | executable | |
MD5:67C767470D0893C4A2E46BE84C9AFCBB | SHA256:64F8D68CC1CFC5B9CC182DF3BECF704AF93D0F1CC93EE59DBF682C75B6D4FFC0 | |||
| 7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | C:\Users\admin\AppData\Roaming\Downloader_Por\Lzx_aria2c.exe | executable | |
MD5:61DDCBD0DB832F7B2546CFEF93250E3D | SHA256:4CAE645245700F04C8FADE534A3432C1542AAC8F7349D67B5B6BB3D278800220 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
37
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5596 | MoUsoCoreWorker.exe | GET | 200 | 95.101.35.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6752 | svchost.exe | GET | 200 | 95.101.35.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 95.101.35.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7796 | 46cc6fb420b3a29e077f05dcd18d18cf03b381b71dcc850157f40520d2c937e7.exe | POST | 200 | 43.159.98.26:80 | http://aria2c.vip/vc/SelectListOne.php | SG | binary | 2.46 Kb | unknown |
— | — | POST | 200 | 40.126.31.3:443 | https://login.live.com/RST2.srf | US | xml | 11.0 Kb | unknown |
— | — | POST | 200 | 40.126.31.0:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | unknown |
— | — | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | compressed | 29.1 Kb | unknown |
4528 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | ZA | binary | 813 b | whitelisted |
4528 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | ZA | binary | 814 b | whitelisted |
4528 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | ZA | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6752 | svchost.exe | 95.101.35.35:80 | crl.microsoft.com | Orange | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 95.101.35.35:80 | crl.microsoft.com | Orange | NL | whitelisted |
— | — | 95.101.35.35:80 | crl.microsoft.com | Orange | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6752 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5524 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
aria2c.vip |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
www.microsoft.com |
| whitelisted |