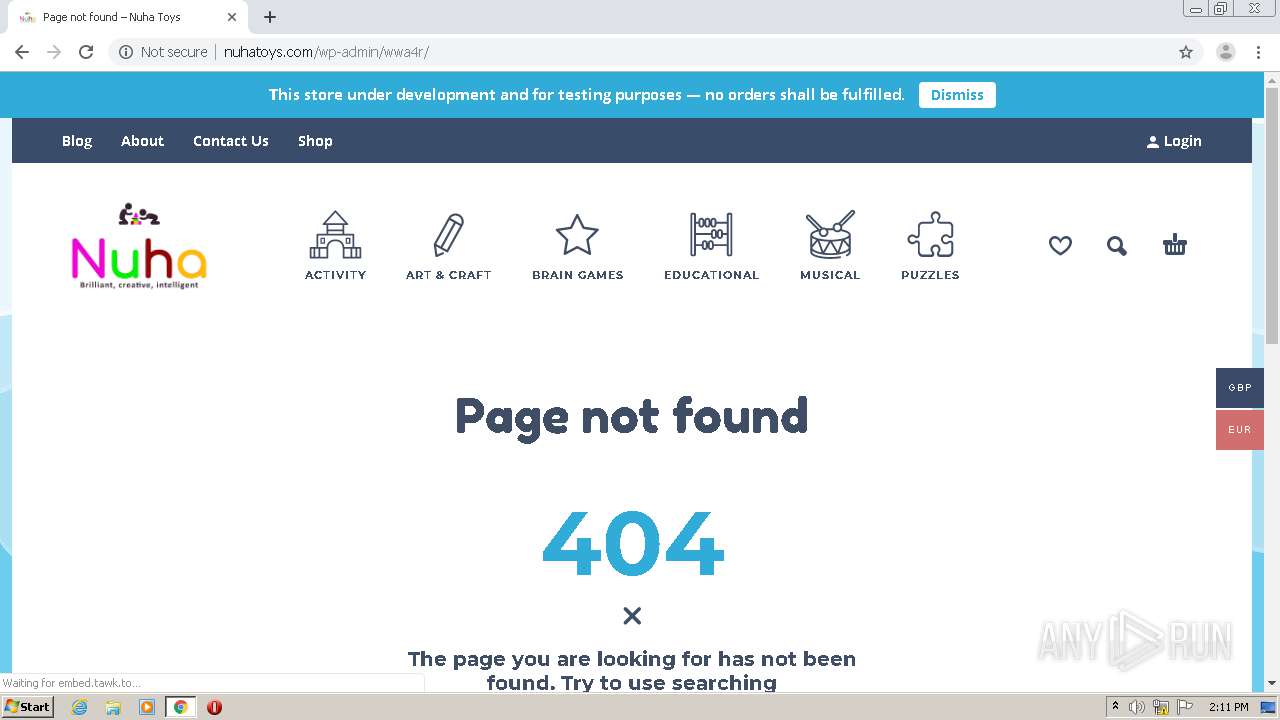
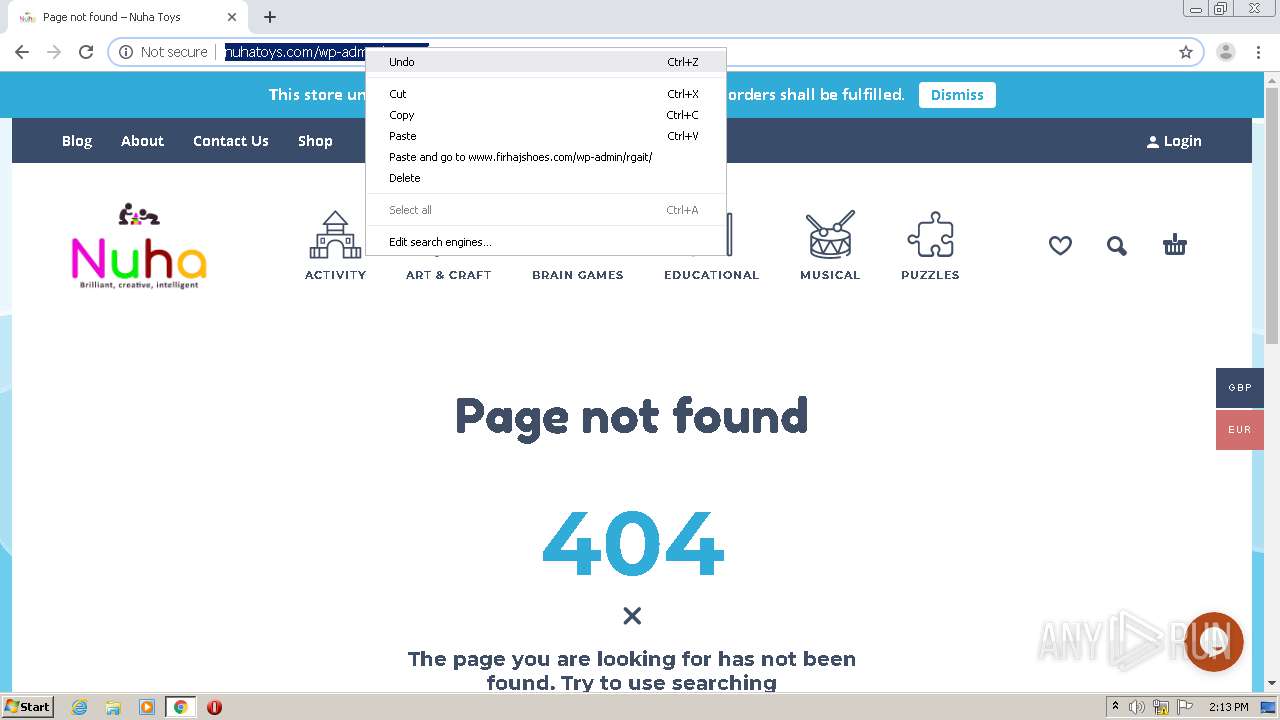
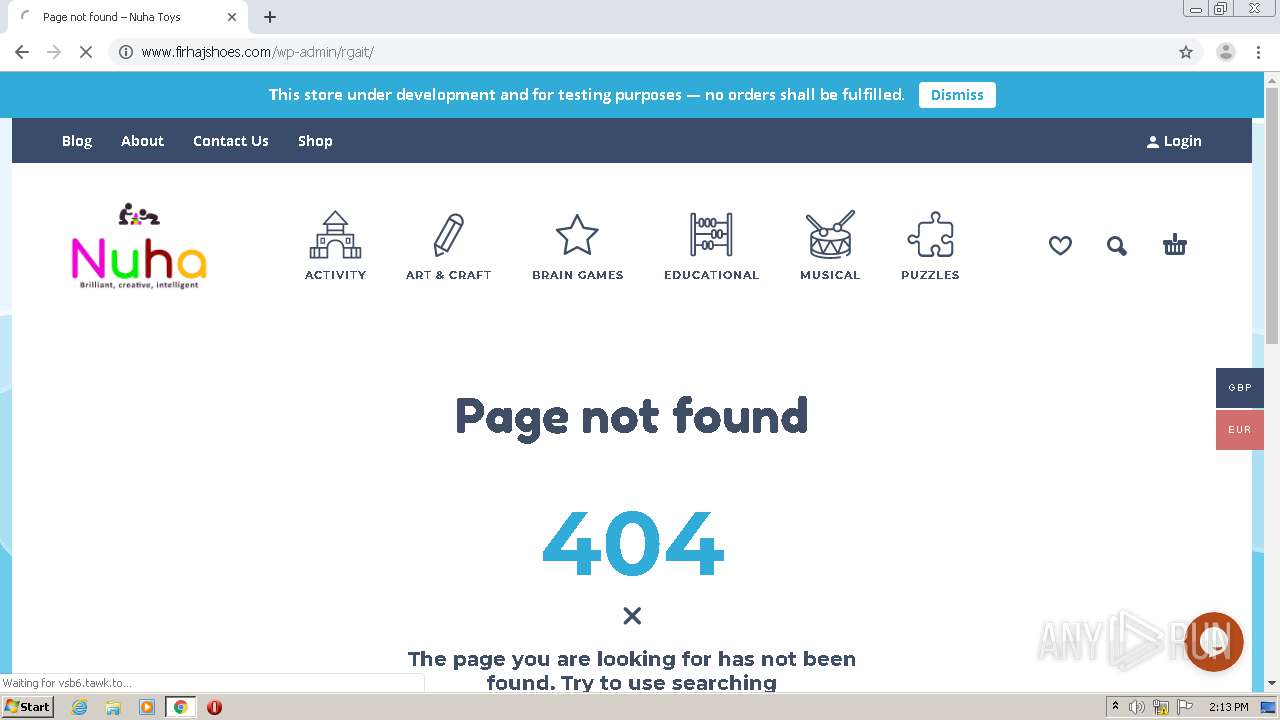
| URL: | http://blueskysol.com/sys-cache/2rk/liste/ |
| Full analysis: | https://app.any.run/tasks/54b9beab-2ac0-4c90-adef-7306d9bdb379 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 13:08:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1B4CDDF4AEA92533075B4AAF639A9FD1 |
| SHA1: | 35C852CA47F513CE0161D571B0FBF0E22AD9B5AD |
| SHA256: | 46CA5940D7D336EF56049721C52B868D459D5BA4A1039A16EDB16538A448AC18 |
| SSDEEP: | 3:N1KcxcN8BcW7VAMZ:CcxceBxAs |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 2748)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 532)
Reads the hosts file
- chrome.exe (PID: 532)
- chrome.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://blueskysol.com/sys-cache/2rk/liste/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10855037672851748858 --mojo-platform-channel-handle=2968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16363210928314242562 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14790991664254464648 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7187689792079038954 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9829228905620947899 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2942862094629932508 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16055410100577203154 --mojo-platform-channel-handle=1576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14696074939852962923 --mojo-platform-channel-handle=2636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15844517705449432231,18415623979724748624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11073756083424940481 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
591
Read events
522
Write events
65
Delete events
4
Modification events
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 532-13245944934750750 |
Value: 259 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 532-13245944934750750 |
Value: 259 | |||
Executable files
0
Suspicious files
117
Text files
100
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F748367-214.pma | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3b74d3.TMP | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6cdb6590-c8fd-48a0-be83-9d995dd71725.tmp | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3b74b4.TMP | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF3b7550.TMP | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
115
TCP/UDP connections
59
DNS requests
44
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
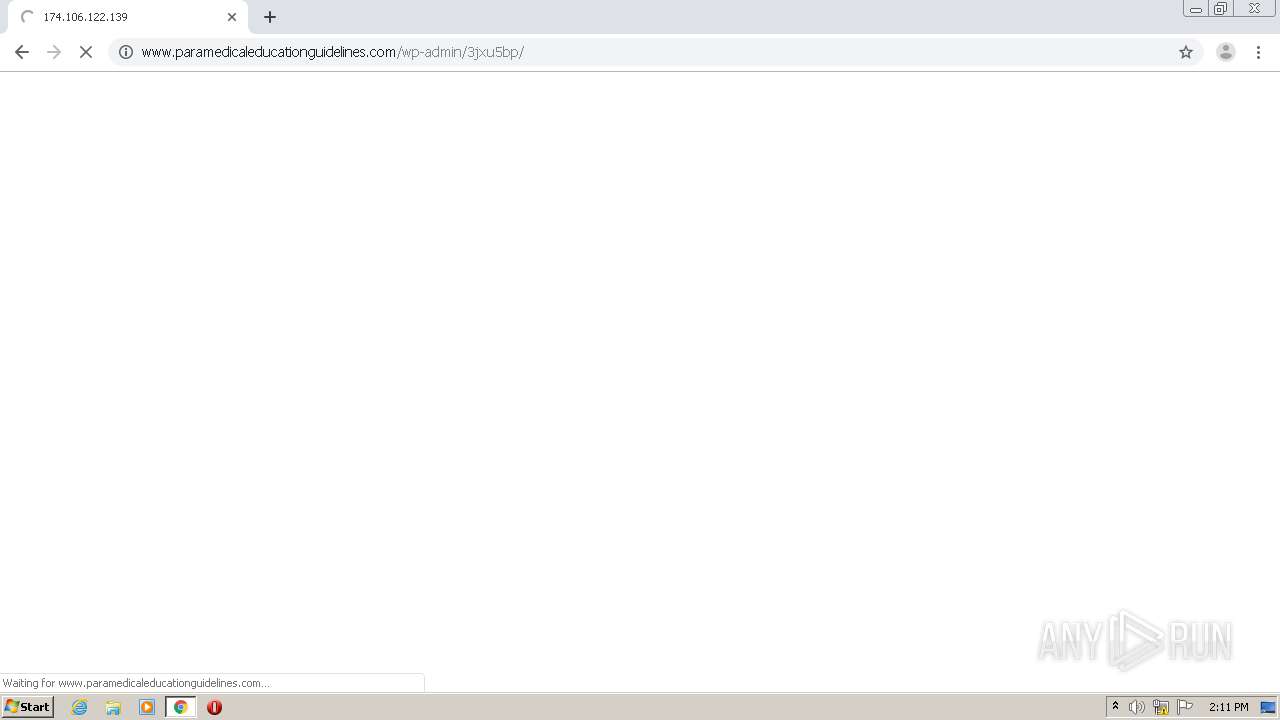
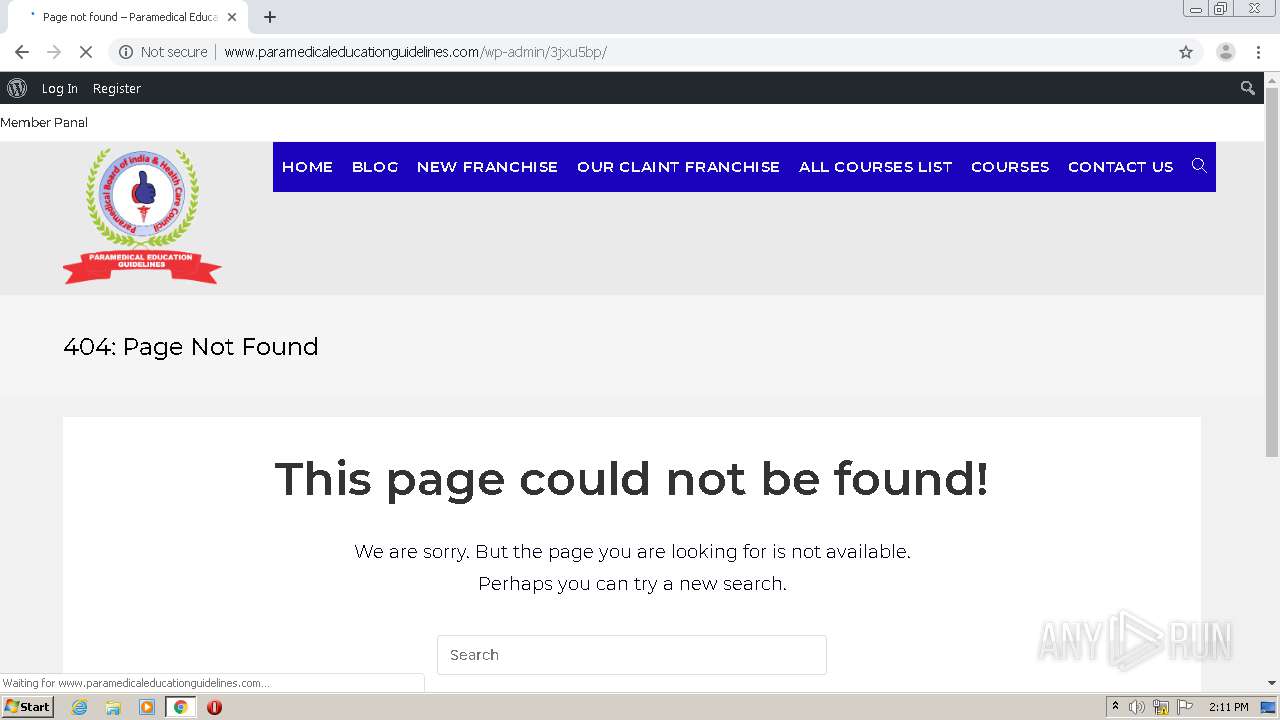
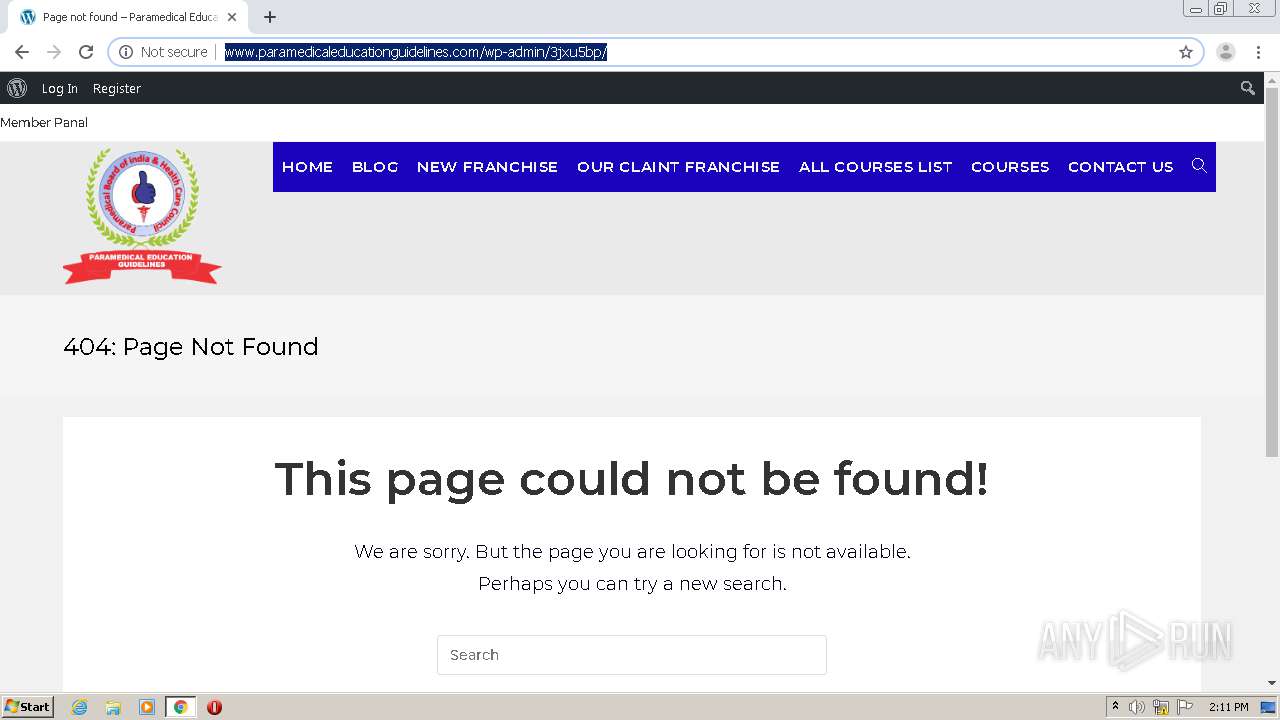
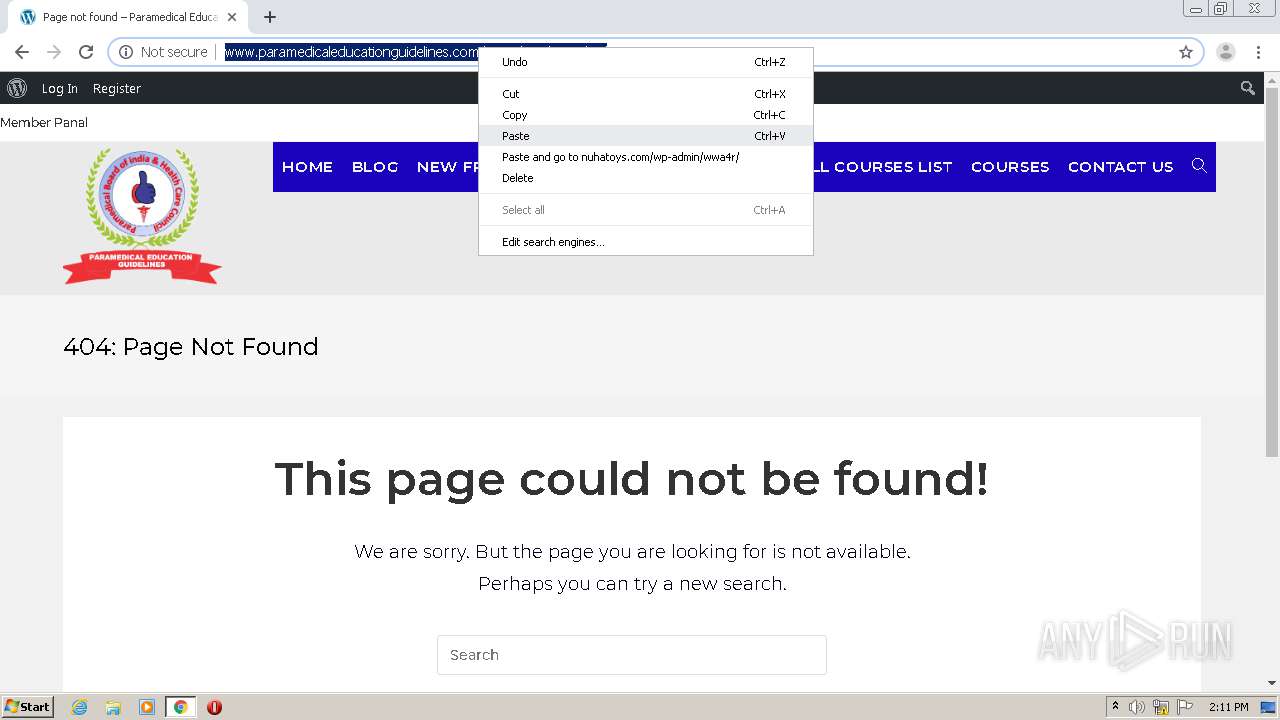
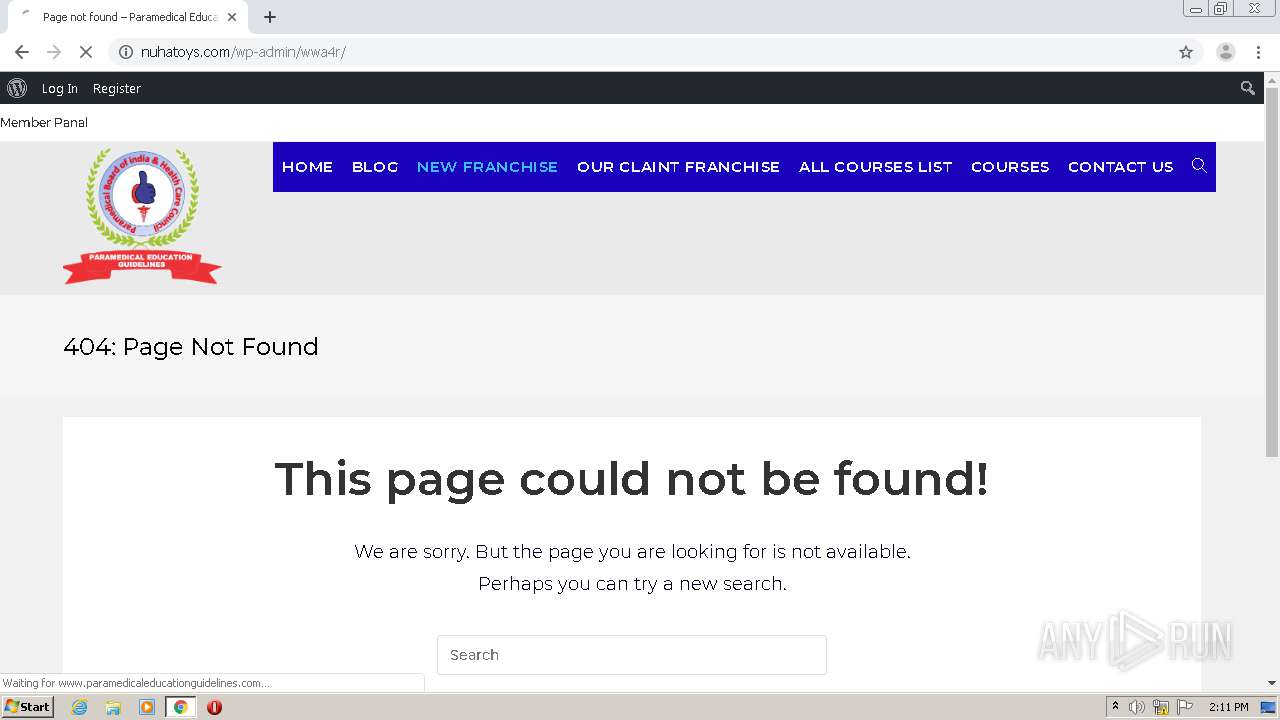
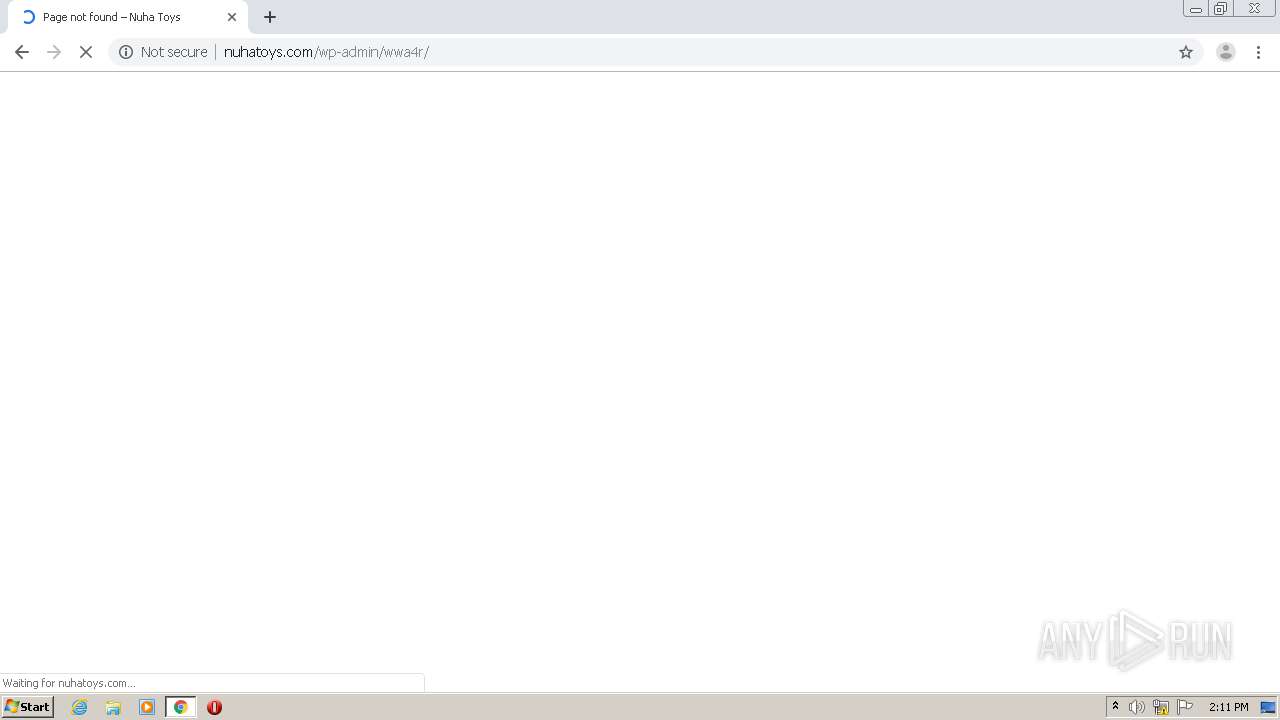
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-includes/css/admin-bar.min.css?ver=5.5.1 | US | text | 5.58 Kb | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-content/plugins/affiliate-coupons/public/css/styles.min.css?ver=1.5.6 | US | text | 3.44 Kb | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-includes/css/dist/block-library/style.min.css?ver=5.5.1 | US | text | 10.2 Kb | malicious |
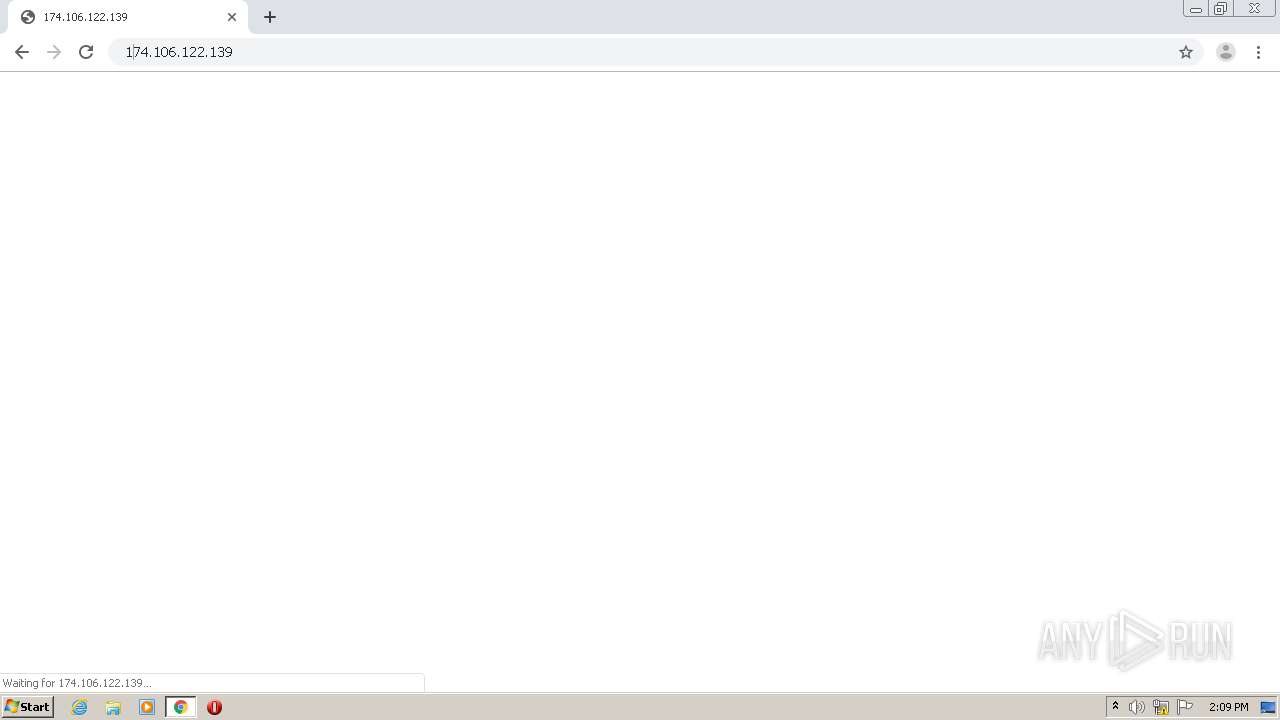
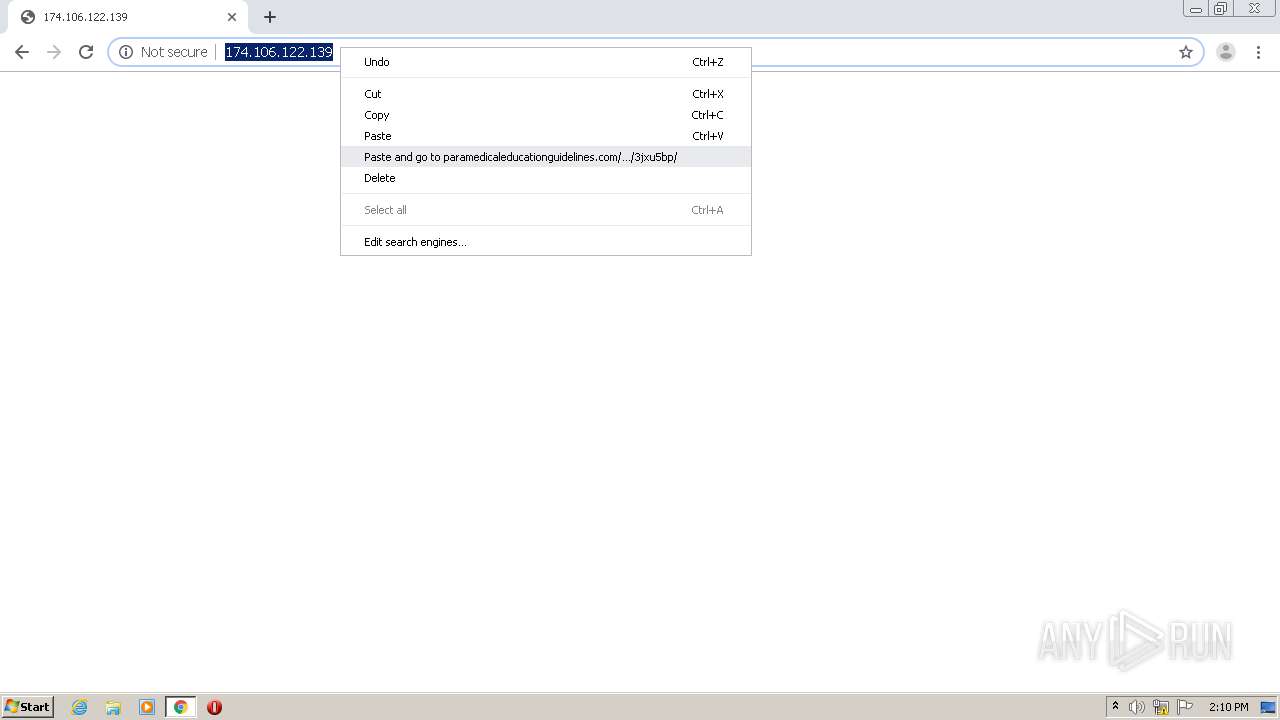
2748 | chrome.exe | GET | 200 | 174.106.122.139:80 | http://174.106.122.139/ | US | binary | 20 b | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-includes/css/dashicons.min.css?ver=5.5.1 | US | text | 34.7 Kb | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-content/plugins/buddypress/bp-members/css/blocks/member.min.css?ver=6.3.0 | US | text | 553 b | malicious |
2748 | chrome.exe | GET | 200 | 174.106.122.139:80 | http://174.106.122.139/favicon.ico | US | binary | 20 b | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-includes/css/dist/block-library/theme.min.css?ver=5.5.1 | US | text | 790 b | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-content/plugins/import-spreadsheets-from-microsoft-excel/css/custom_plugin.css?ver=5.5.1 | US | text | 401 b | malicious |
2748 | chrome.exe | GET | 200 | 162.241.148.206:80 | http://www.paramedicaleducationguidelines.com/wp-content/plugins/buddypress/bp-core/css/admin-bar.min.css?ver=6.3.0 | US | text | 433 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 142.250.74.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 174.106.122.139:80 | — | Time Warner Cable Internet LLC | US | malicious |
2748 | chrome.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 162.241.148.206:443 | www.paramedicaleducationguidelines.com | CyrusOne LLC | US | malicious |
2748 | chrome.exe | 162.241.148.206:80 | www.paramedicaleducationguidelines.com | CyrusOne LLC | US | malicious |
2748 | chrome.exe | 216.58.206.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
blueskysol.com |
| suspicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.paramedicaleducationguidelines.com |
| malicious |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2748 | chrome.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |