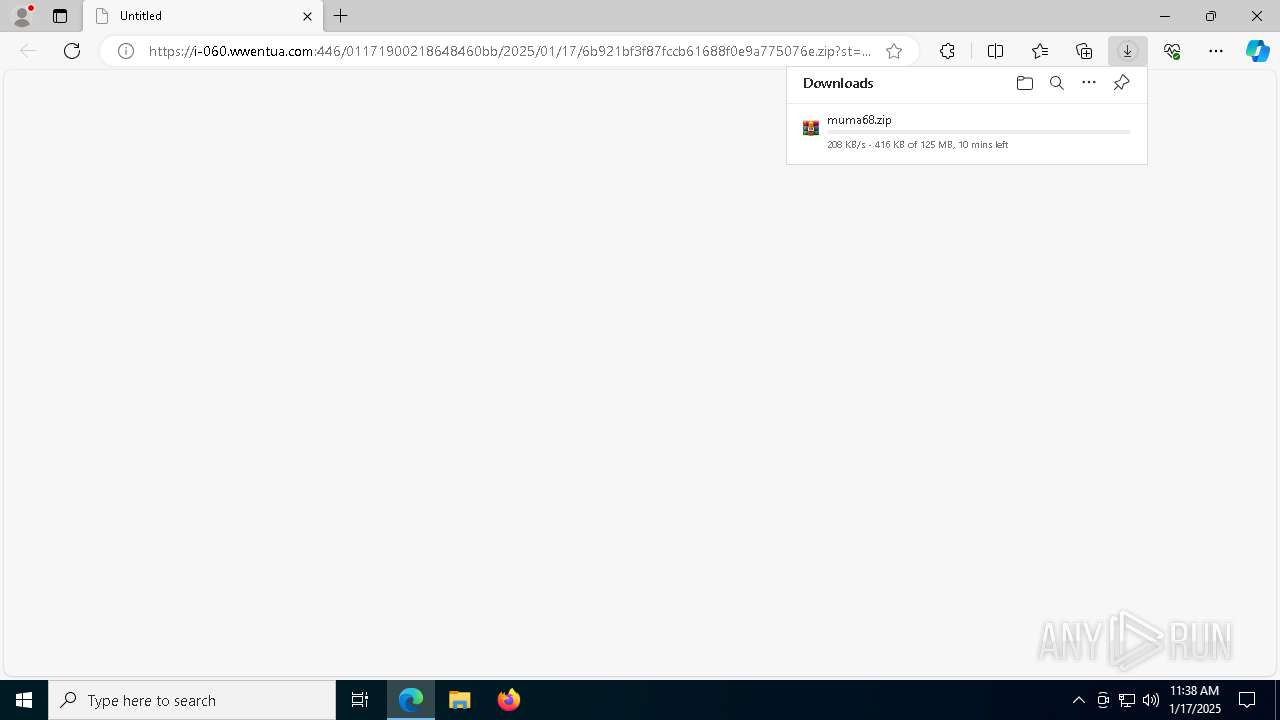
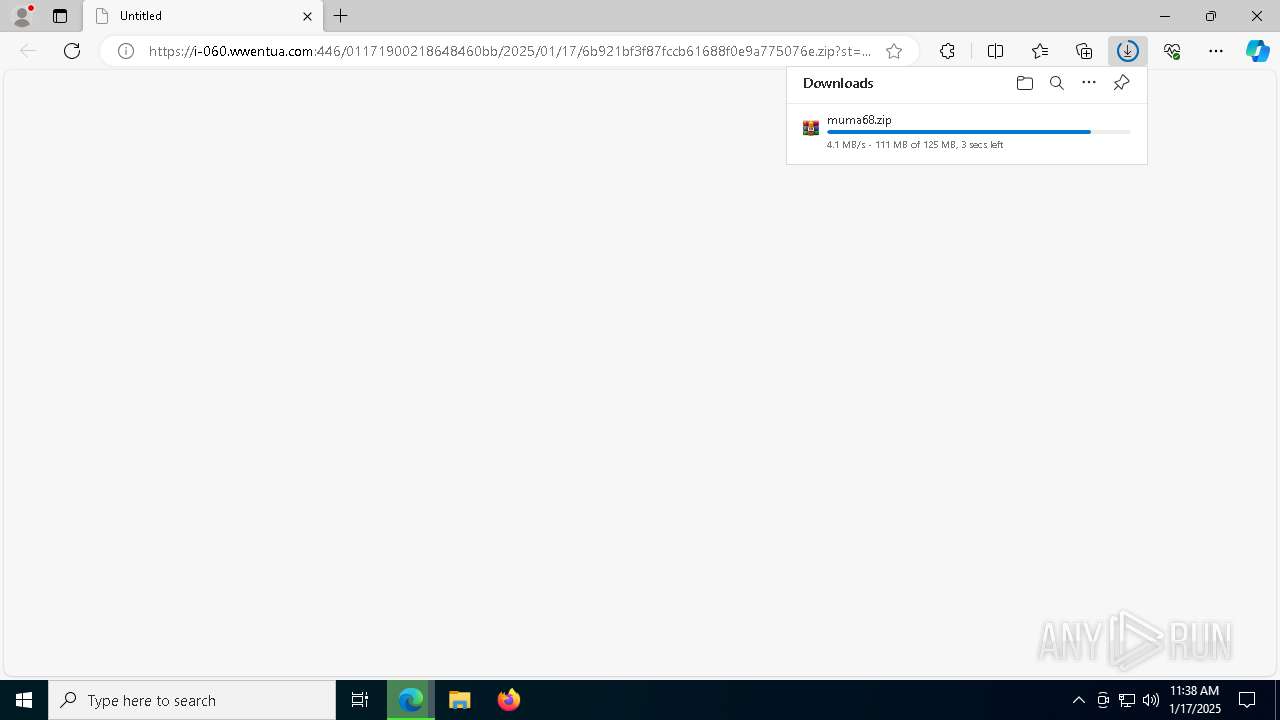
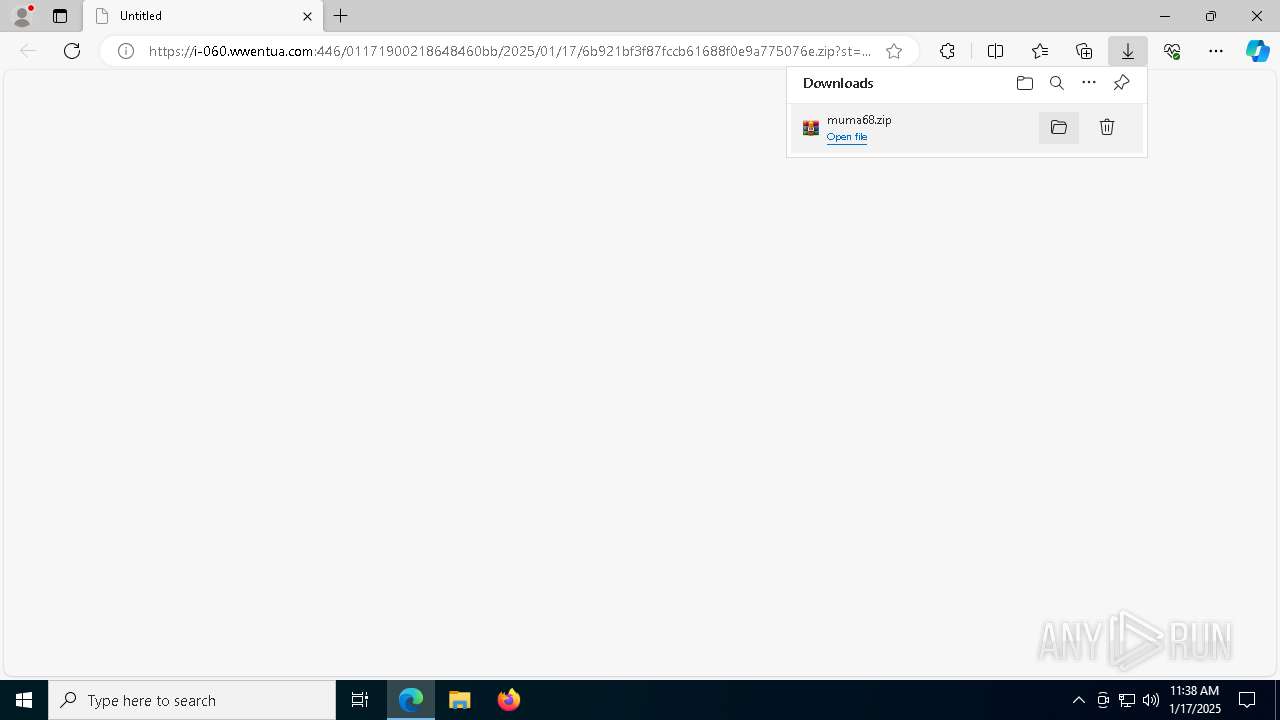
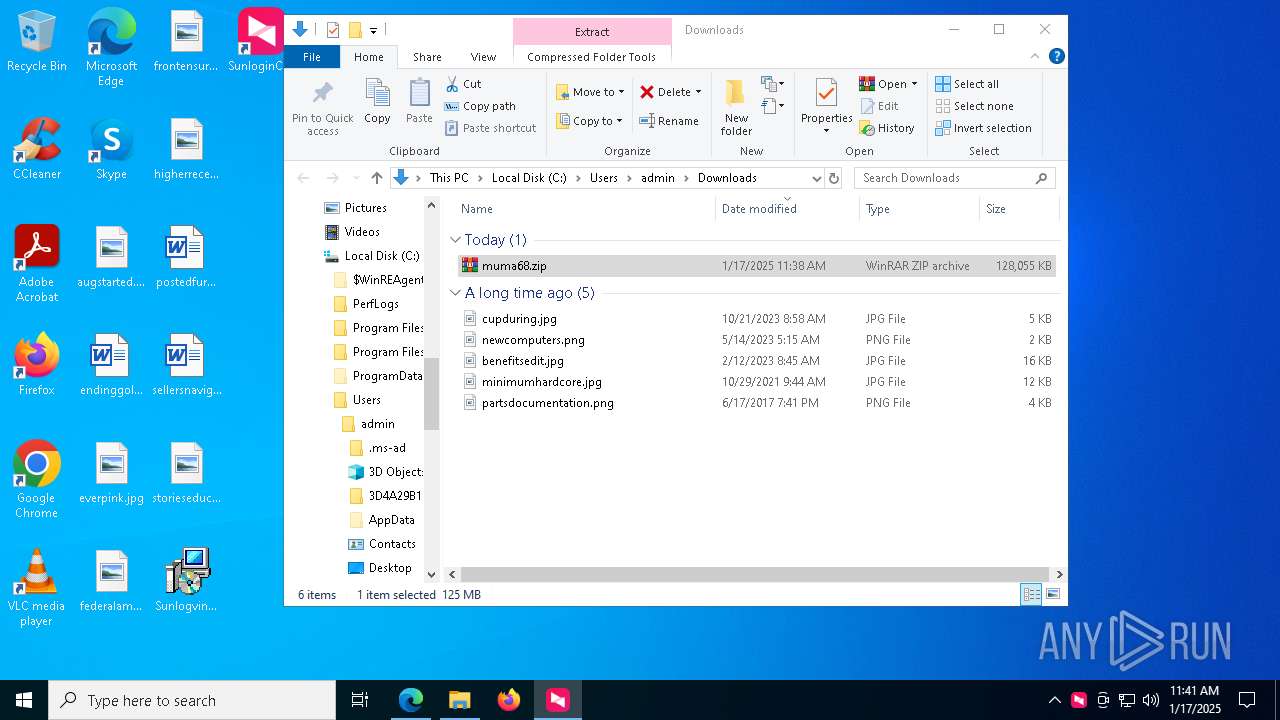
| URL: | https://i-060.wwentua.com:446/01171900218648460bb/2025/01/17/6b921bf3f87fccb61688f0e9a775076e.zip?st=Tzlus4fvpTEqjGXblVeNsQ&e=1737115695&b=Aj0JfFU4UTVZOgdpVihQLlRoWnY_c&fi=218648460&pid=1-63-148-50&up=2&mp=0&co=0 |
| Full analysis: | https://app.any.run/tasks/bab978a7-7c88-46e4-8bbc-4c779cb57191 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2025, 11:38:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
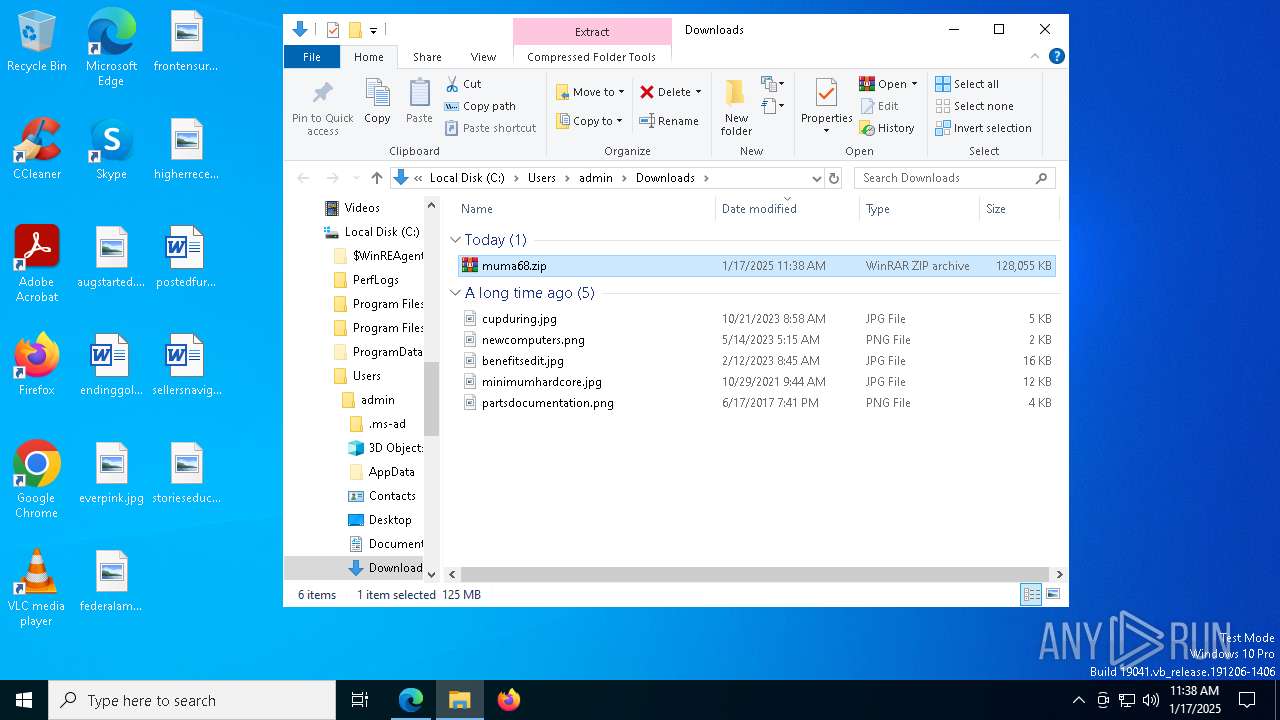
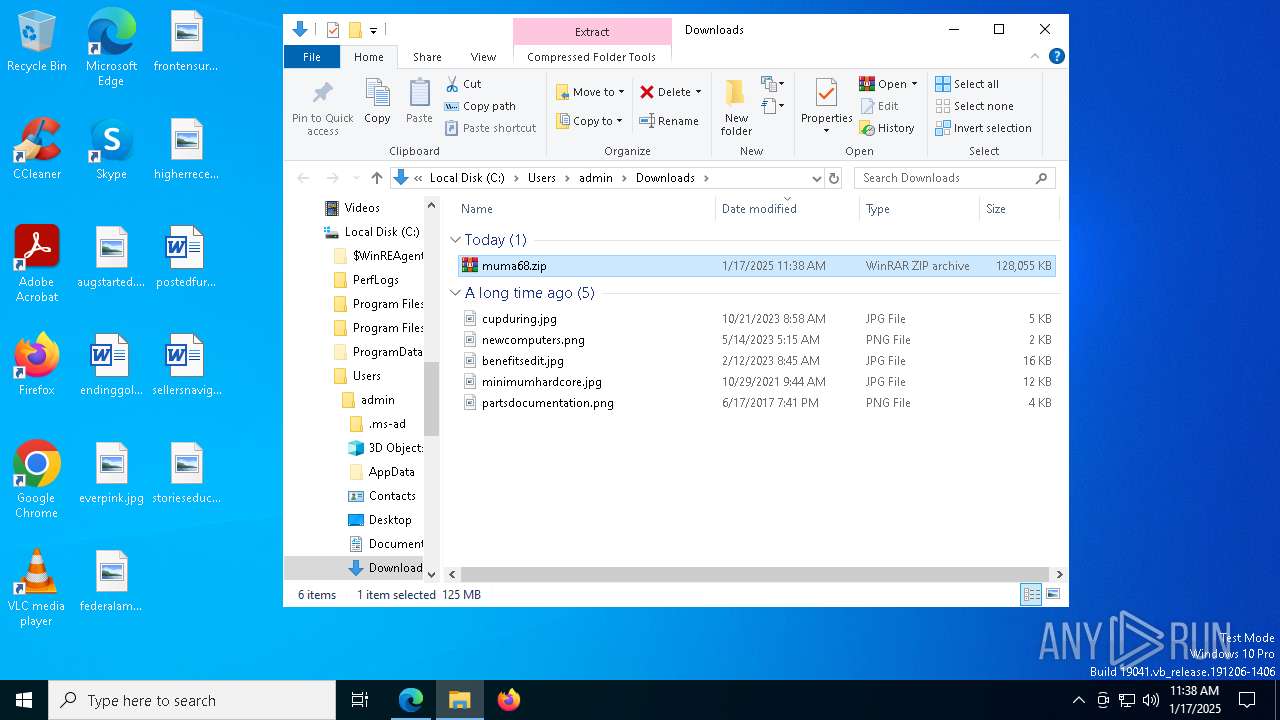
| MD5: | D891B33932C98402B5626F142C4004C0 |
| SHA1: | 02B356699FE004590A43EDA8A72922C27BE1DC81 |
| SHA256: | 46C8F3228EF04FF85BFDBA0C6EB6021174C2920129F184710E5420B55A22E0F5 |
| SSDEEP: | 3:N8lES8yTrKVULv2vA+q6jjVUTr7jeQMVKDJQ9pzAJrLGaWxTfyeURxQY0N8P/Lqr:2y2rOUrPHCZViJvGaWh2zQYlHLmV |
MALICIOUS
No malicious indicators.SUSPICIOUS
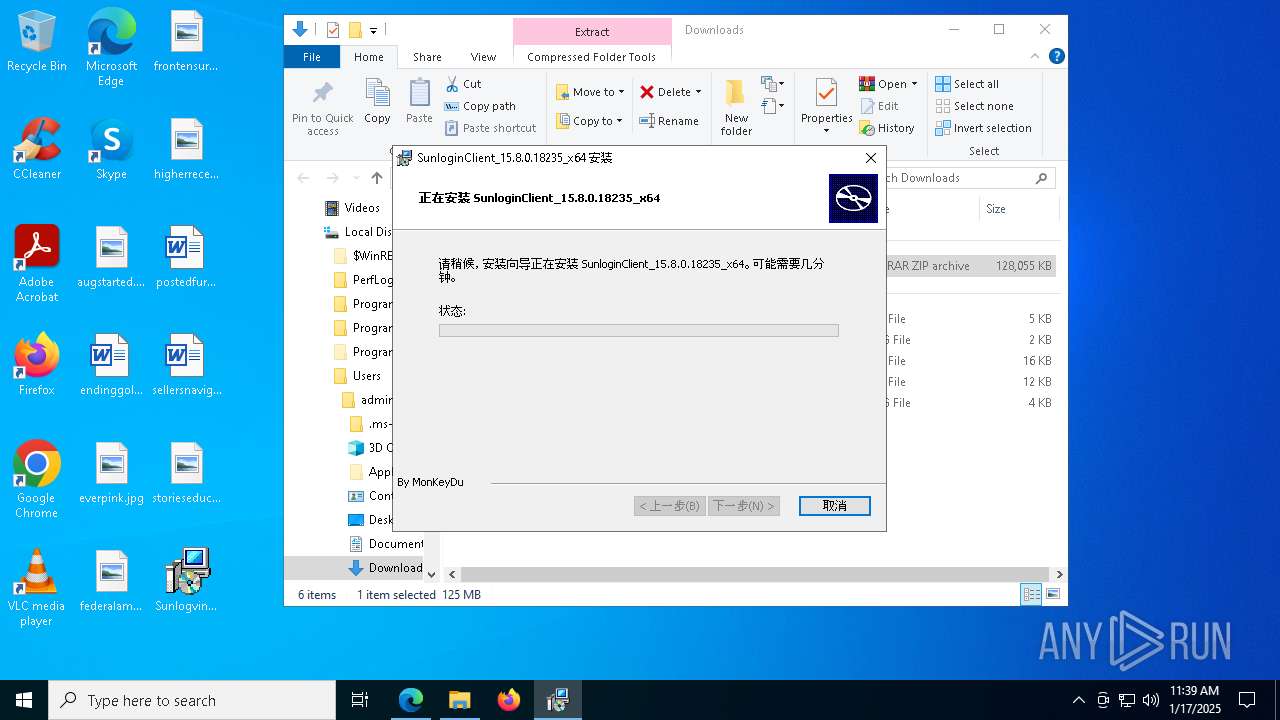
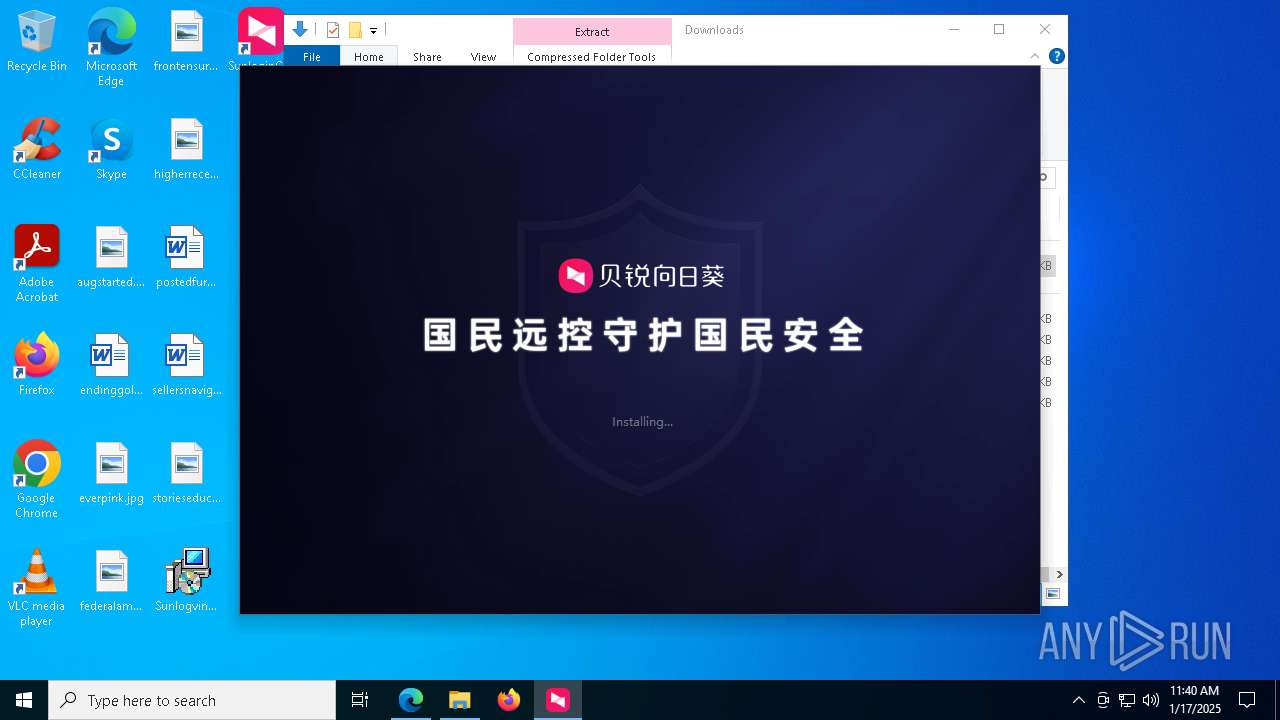
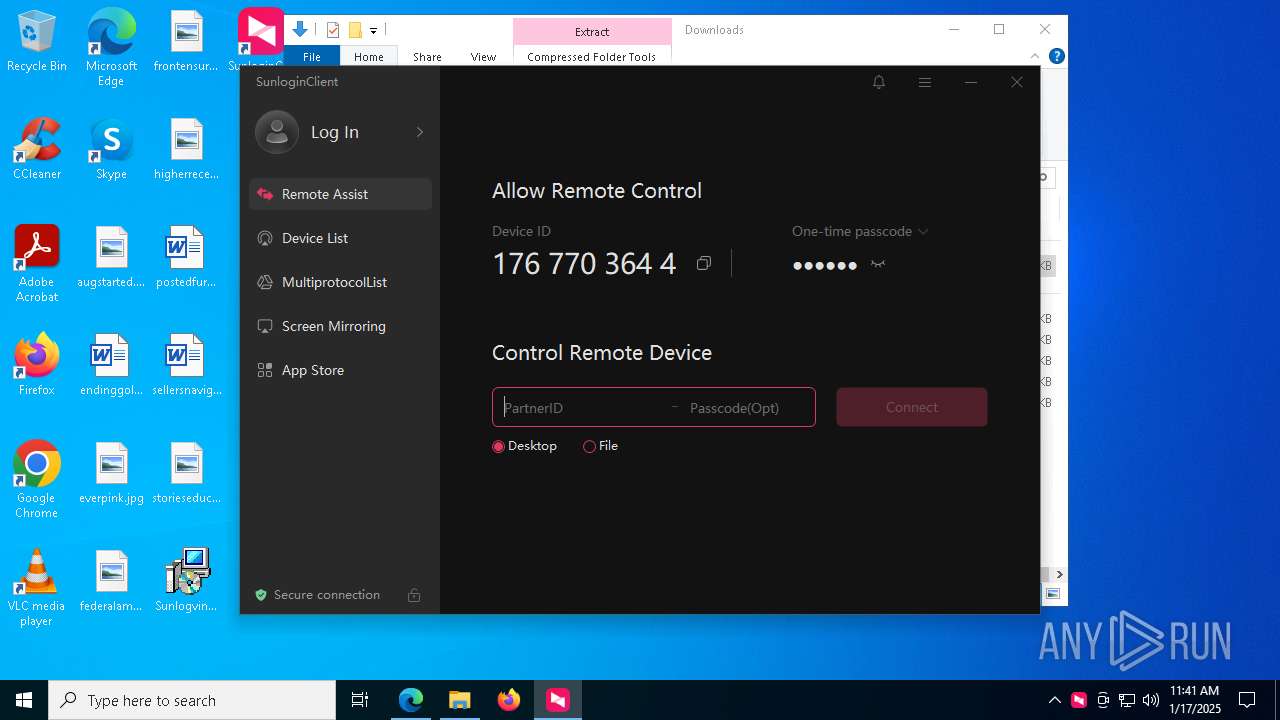
Executes as Windows Service
- VSSVC.exe (PID: 4976)
- WUDFHost.exe (PID: 1868)
- SunloginClient.exe (PID: 5556)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5472)
Process drops legitimate windows executable
- msiexec.exe (PID: 8112)
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
The process drops C-runtime libraries
- msiexec.exe (PID: 8112)
Executes application which crashes
- Microsoft_Xtools.exe (PID: 5776)
Reads the date of Windows installation
- SunloginClient_15.8.0.18235_x64.exe (PID: 8016)
- SunloginClient.exe (PID: 7792)
Application launched itself
- SunloginClient_15.8.0.18235_x64.exe (PID: 8016)
- cmd.exe (PID: 7896)
- SunloginClient.exe (PID: 5556)
- SunloginClient.exe (PID: 8008)
Executable content was dropped or overwritten
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- devcon.exe (PID: 4996)
- SunloginClient.exe (PID: 2736)
- devcon.exe (PID: 2092)
- drvinst.exe (PID: 7304)
- drvinst.exe (PID: 7972)
- drvinst.exe (PID: 7188)
- drvinst.exe (PID: 7948)
- SunloginClient.exe (PID: 5556)
Drops a system driver (possible attempt to evade defenses)
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- devcon.exe (PID: 4996)
- drvinst.exe (PID: 7972)
- SunloginClient.exe (PID: 2736)
- drvinst.exe (PID: 7188)
- drvinst.exe (PID: 7948)
Starts itself from another location
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
Starts CMD.EXE for commands execution
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- cmd.exe (PID: 7896)
Executing commands from a ".bat" file
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 7272)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7140)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 968)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 3920)
- cmd.exe (PID: 7804)
- cmd.exe (PID: 5580)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 4704)
- cmd.exe (PID: 7824)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 512)
- cmd.exe (PID: 7864)
Reads security settings of Internet Explorer
- SunloginClient.exe (PID: 7792)
- SunloginClient.exe (PID: 8072)
- devcon.exe (PID: 4996)
Checks Windows Trust Settings
- devcon.exe (PID: 4996)
Creates files in the driver directory
- drvinst.exe (PID: 7188)
- drvinst.exe (PID: 7304)
Creates a software uninstall entry
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
Searches for installed software
- SunloginClient.exe (PID: 8008)
Process uses ARP to discover network configuration
- SunloginClient.exe (PID: 8008)
Uses TASKKILL.EXE to kill process
- SunloginClient.exe (PID: 8008)
Checks for external IP
- svchost.exe (PID: 2192)
- SunloginClient.exe (PID: 8008)
INFO
Checks supported languages
- identity_helper.exe (PID: 7672)
- msiexec.exe (PID: 5472)
- msiexec.exe (PID: 1296)
- msiexec.exe (PID: 8076)
- msiexec.exe (PID: 8112)
- SunloginClient_15.8.0.18235_x64.exe (PID: 8016)
- SunloginClient.exe (PID: 2012)
- devcon.exe (PID: 4996)
- SunloginClient.exe (PID: 7792)
- SunloginClient.exe (PID: 8072)
- devcon.exe (PID: 2092)
- drvinst.exe (PID: 7364)
- drvinst.exe (PID: 7948)
- SunloginClient.exe (PID: 1596)
Reads the computer name
- identity_helper.exe (PID: 7672)
- msiexec.exe (PID: 5472)
- msiexec.exe (PID: 8112)
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- SunloginClient.exe (PID: 2012)
- SunloginClient.exe (PID: 7792)
- drvinst.exe (PID: 7364)
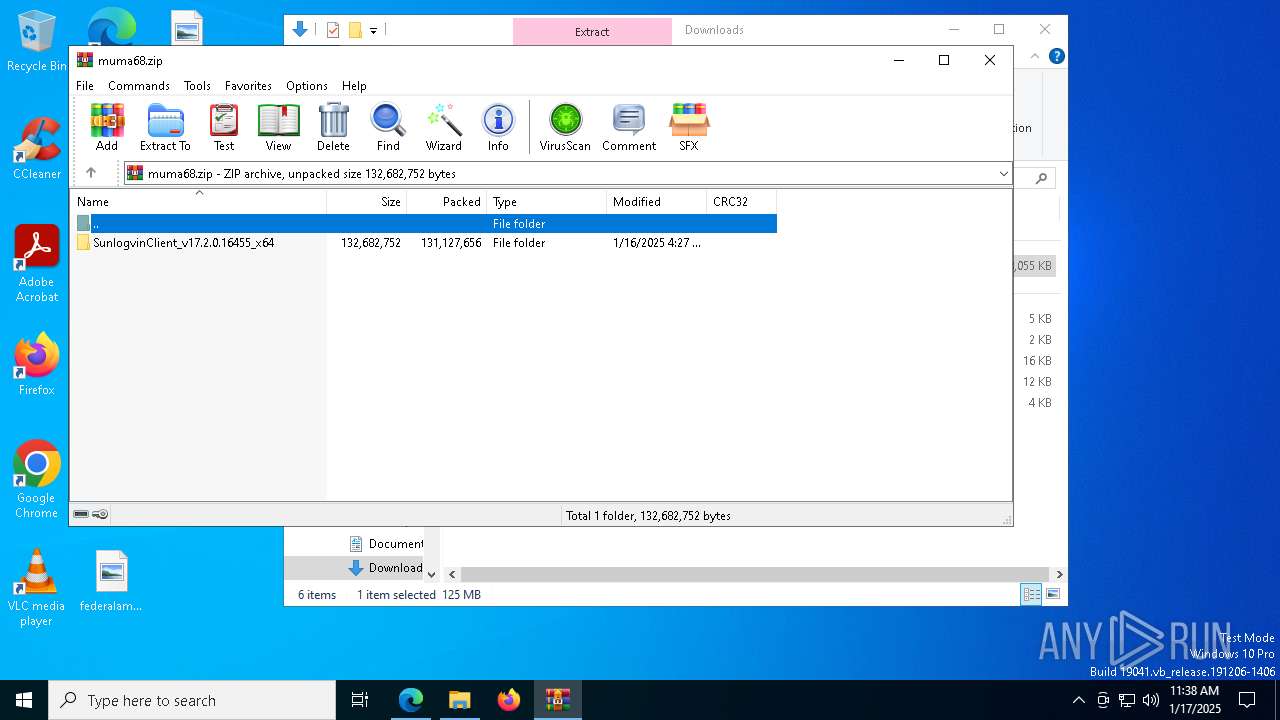
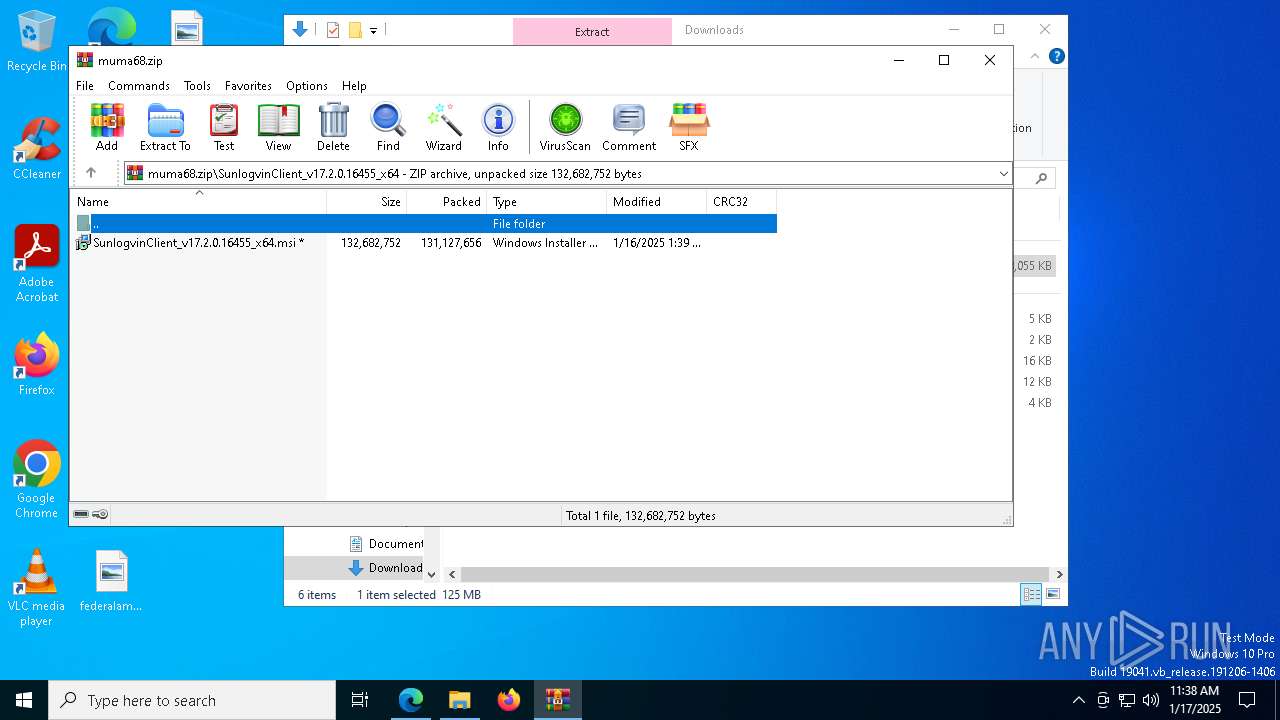
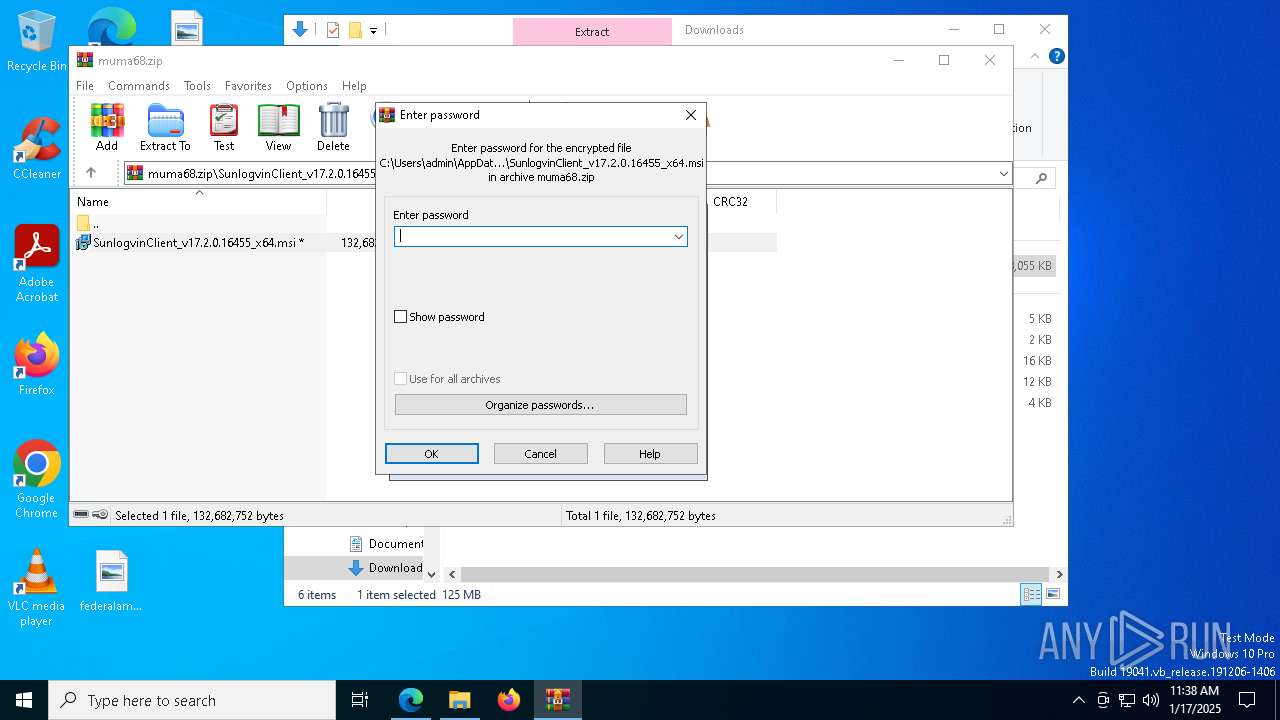
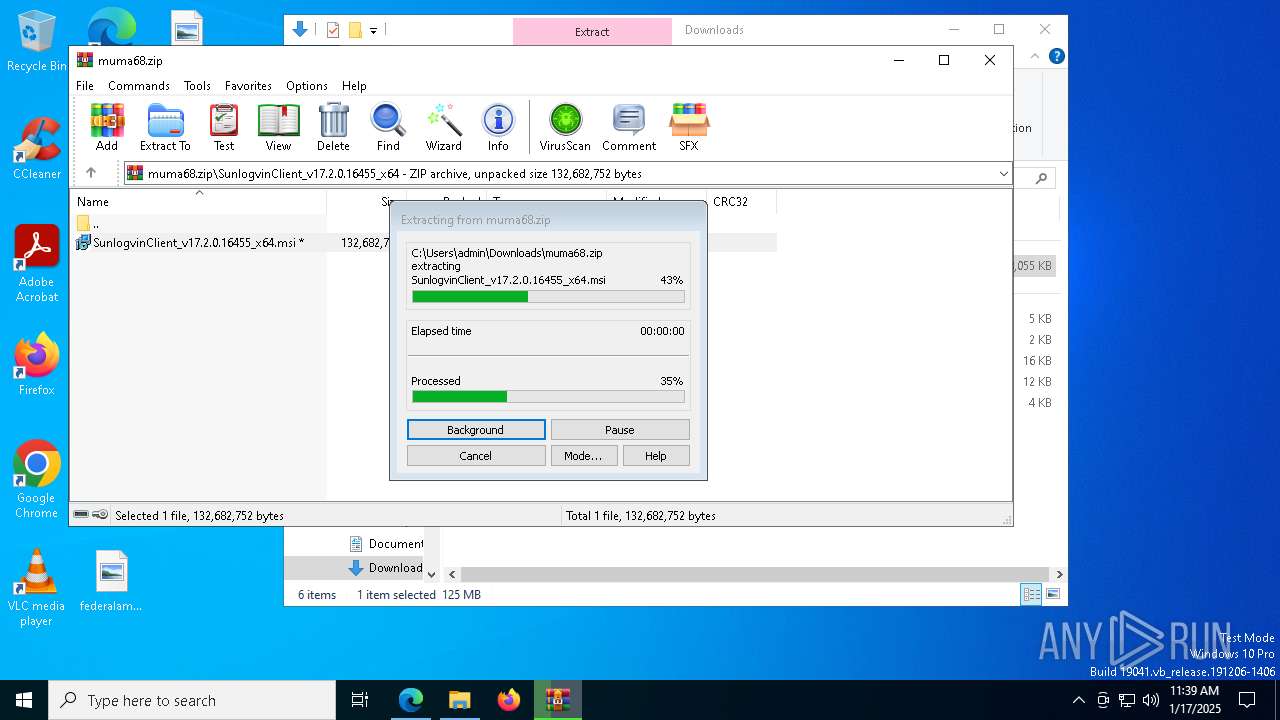
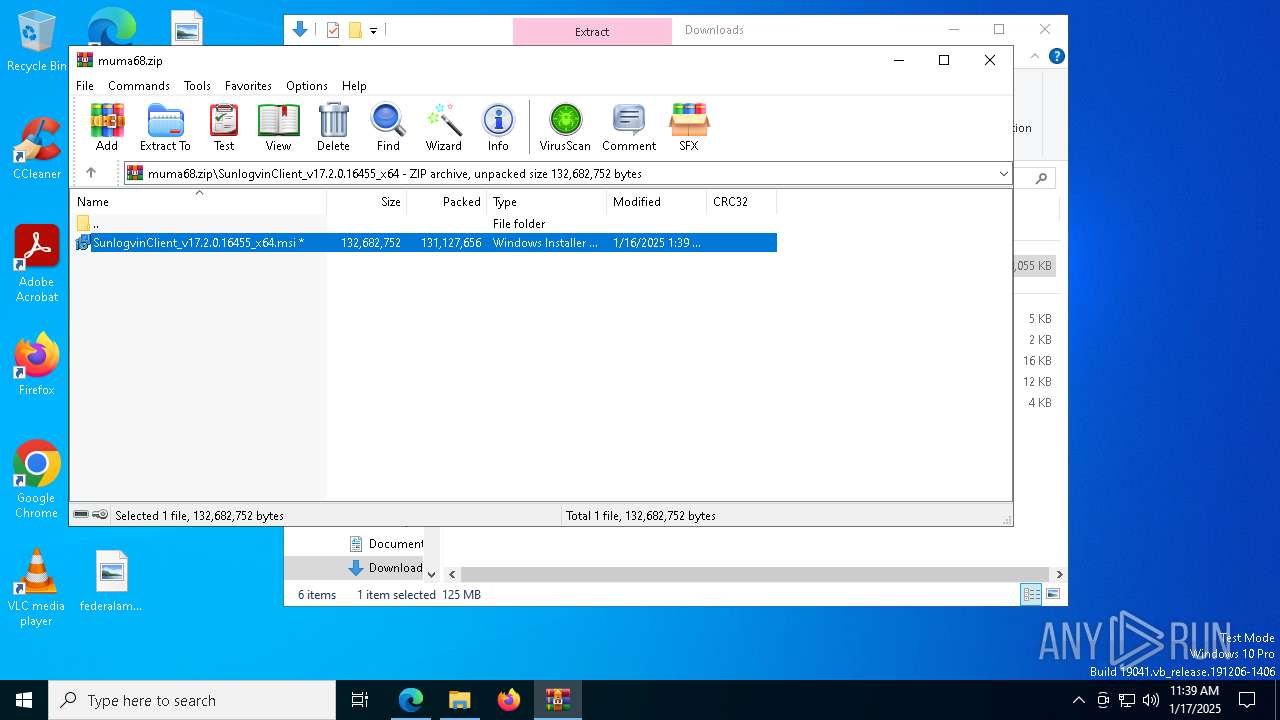
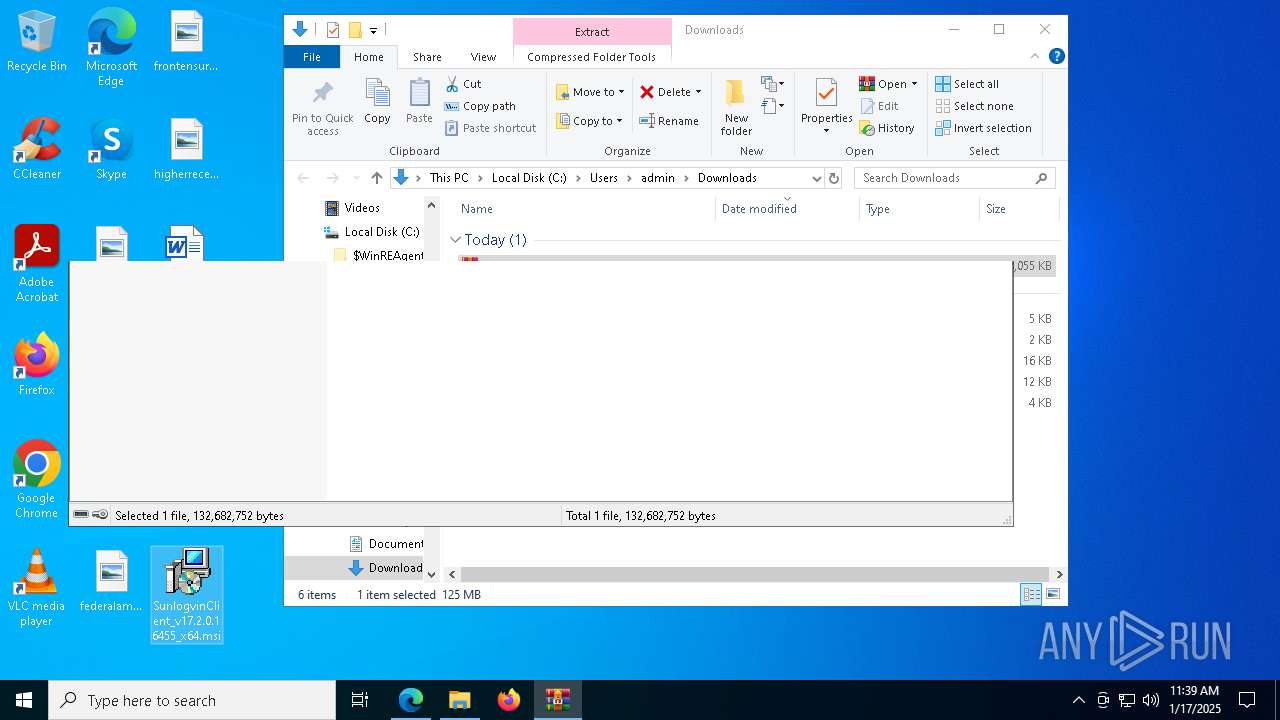
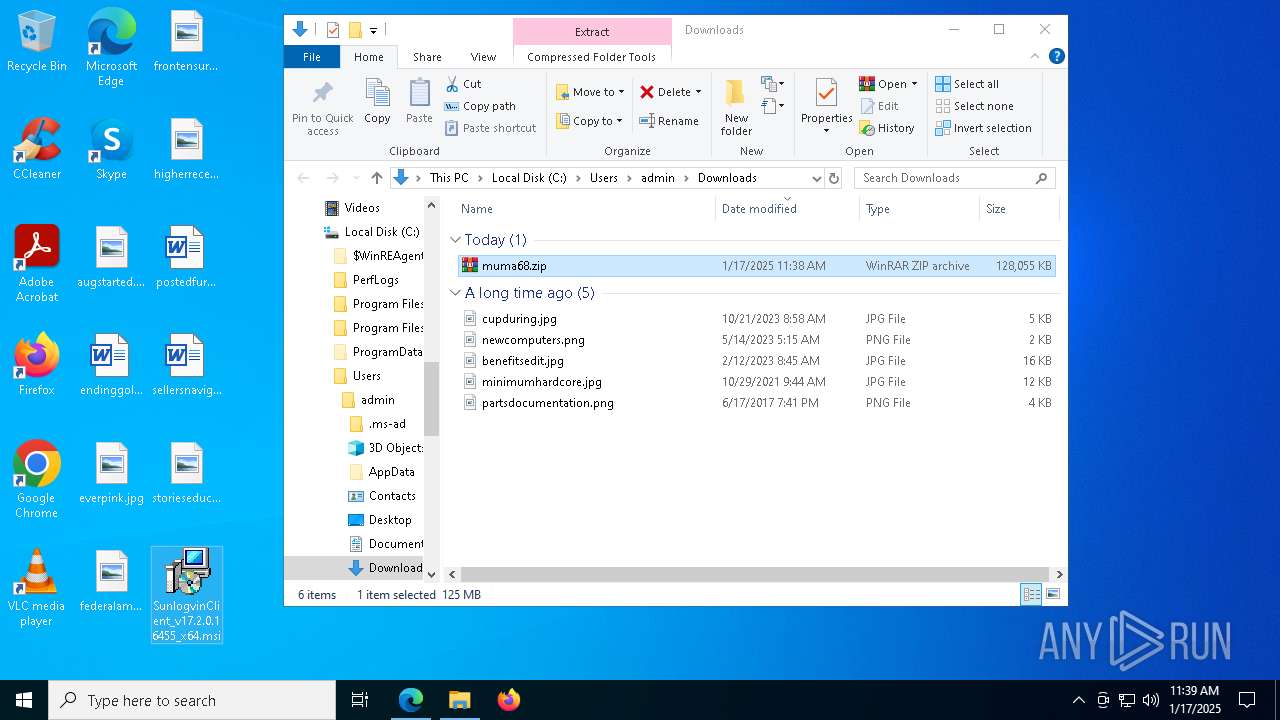
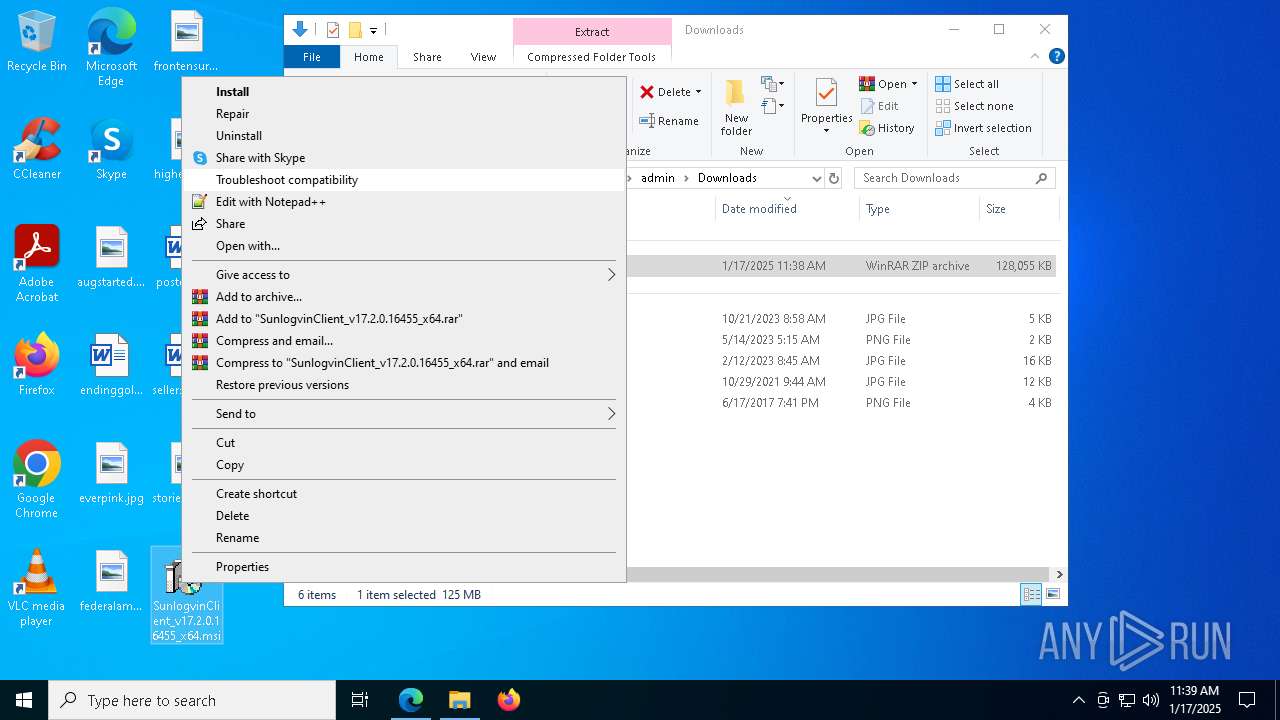
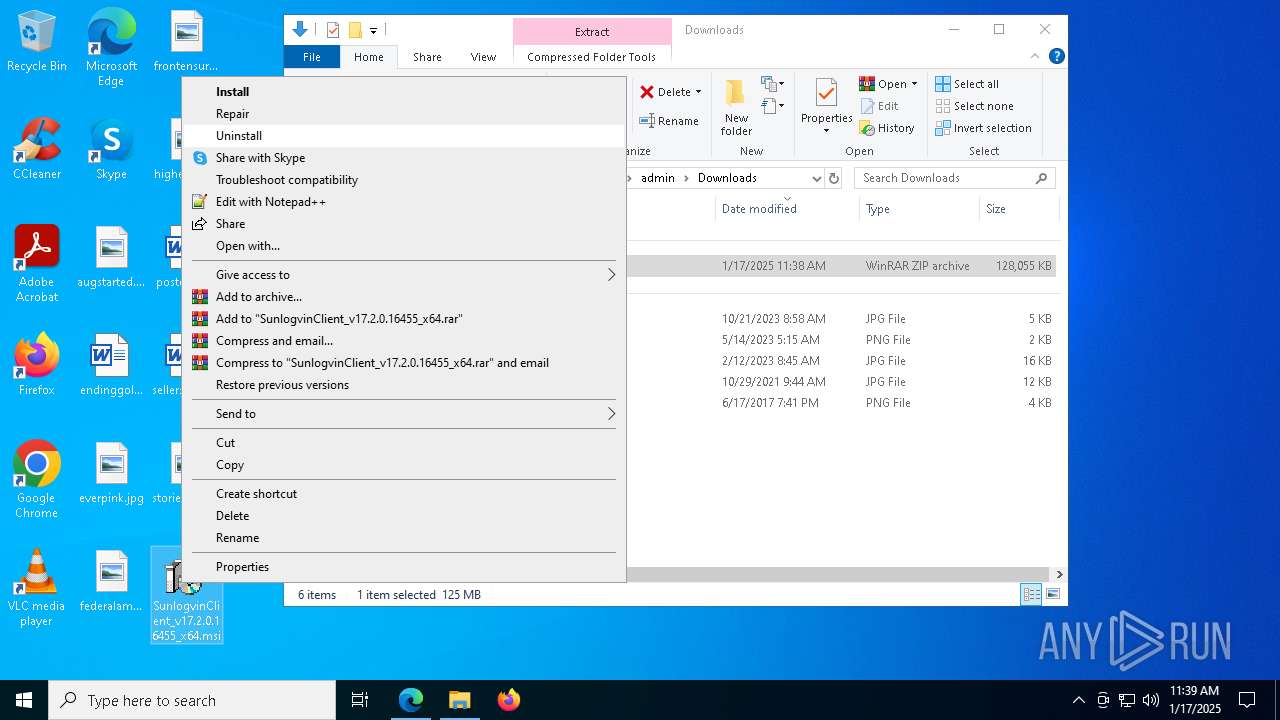
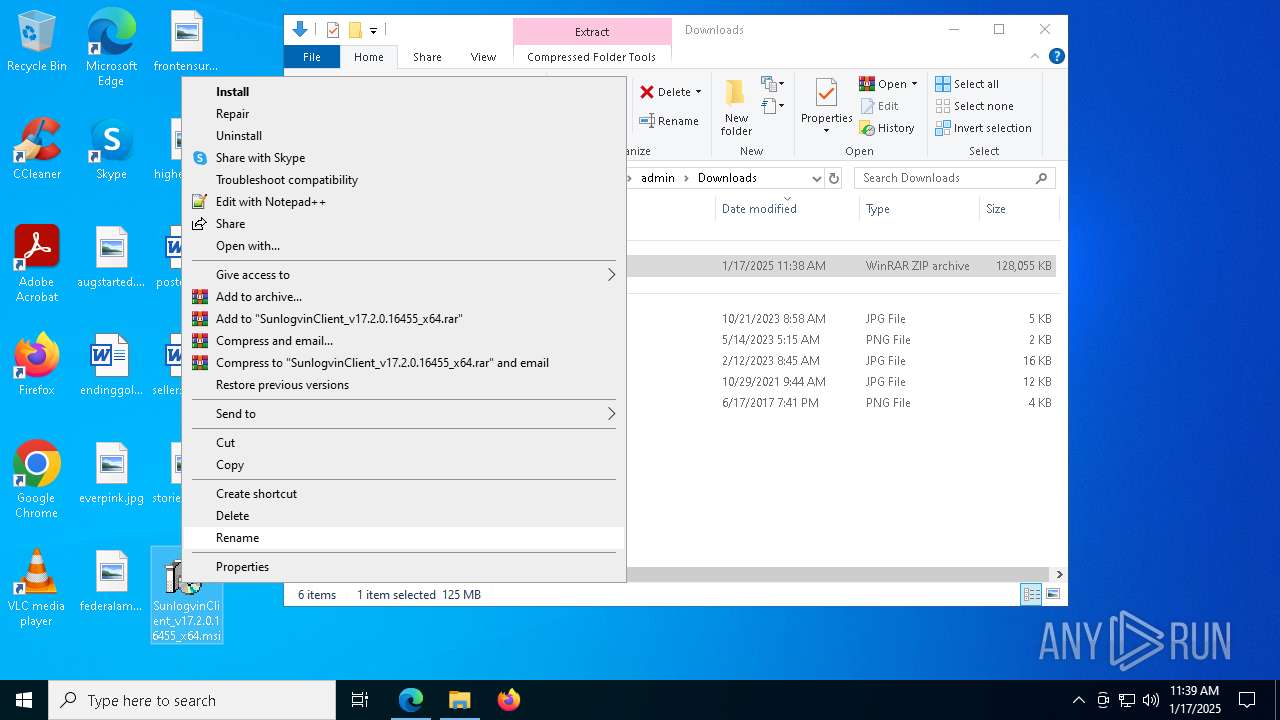
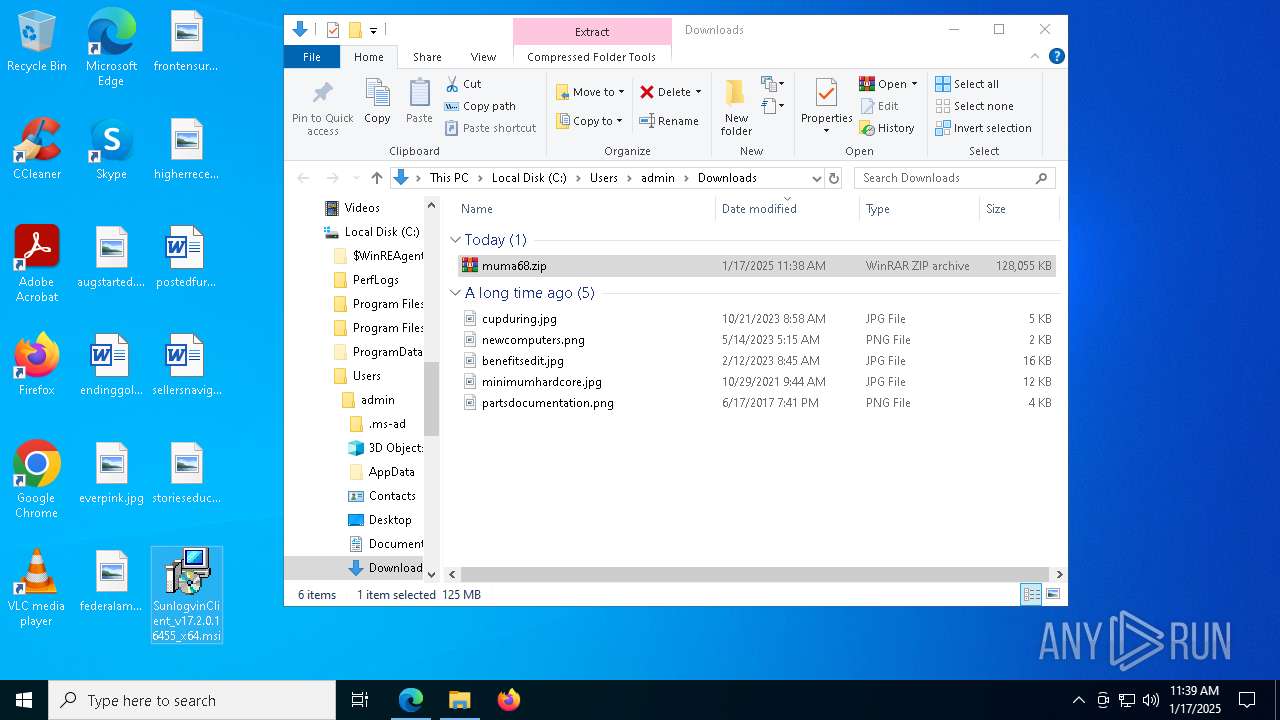
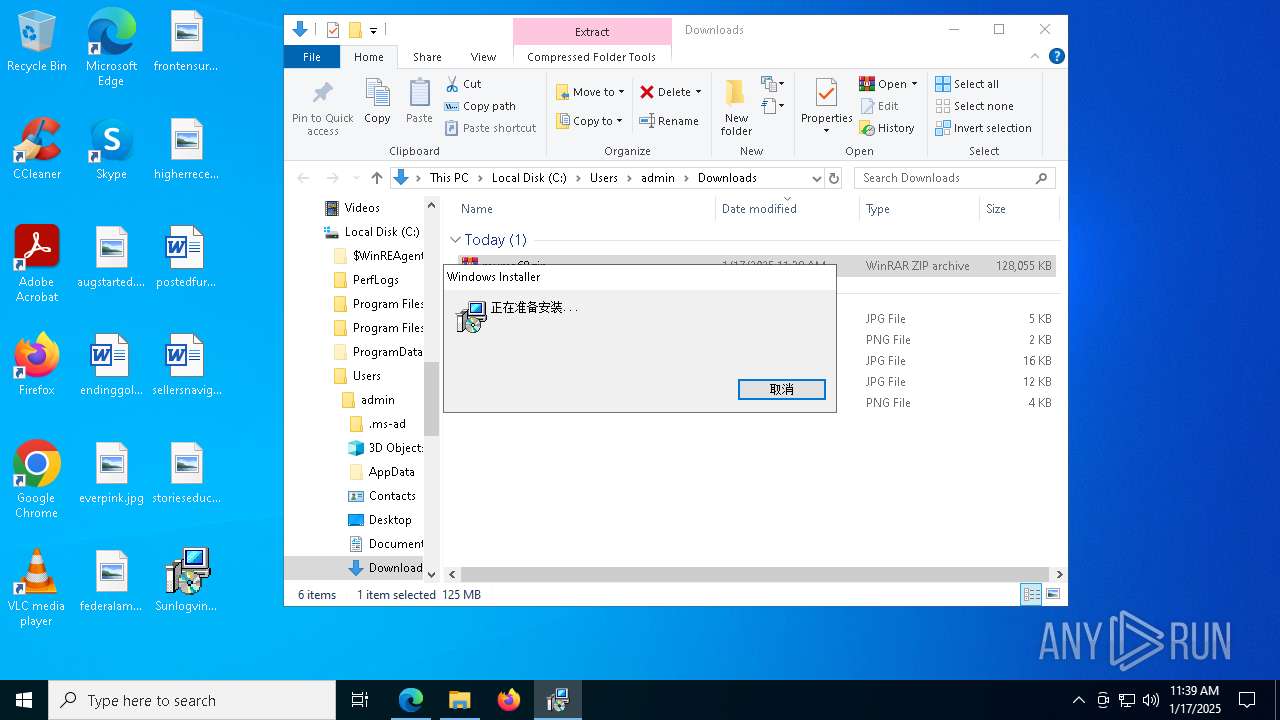
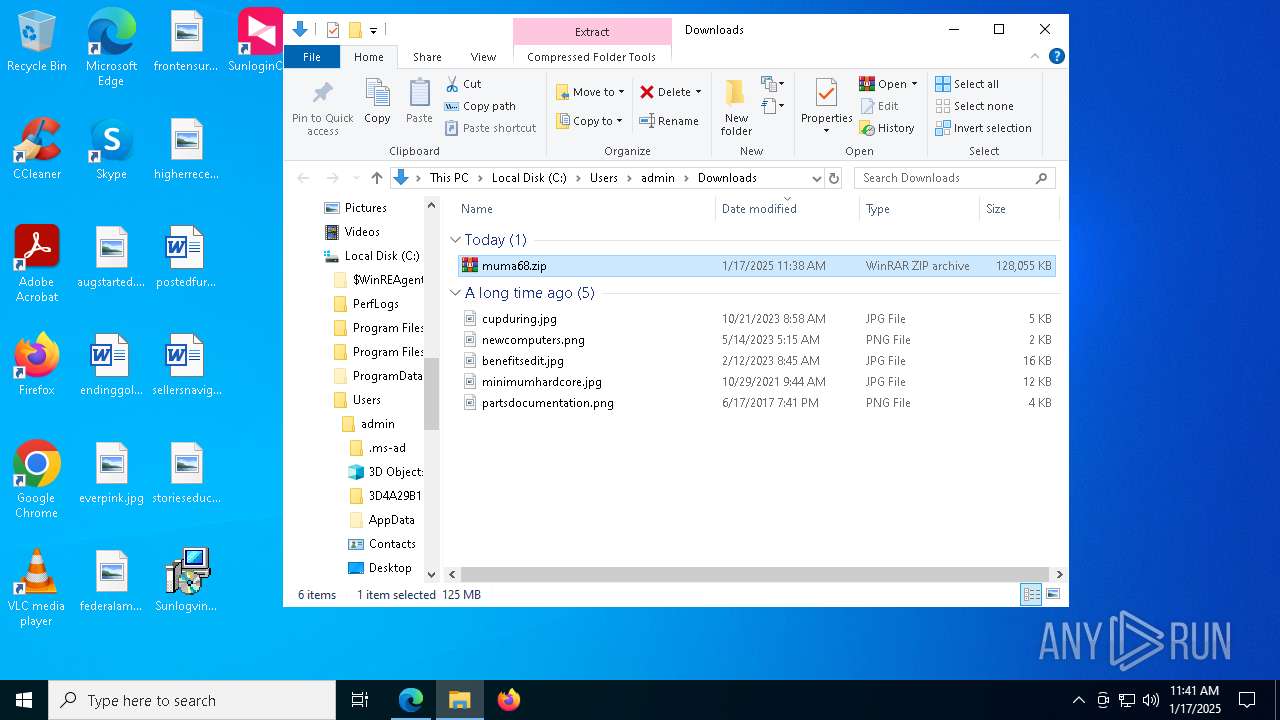
Manual execution by a user
- WinRAR.exe (PID: 7856)
- msiexec.exe (PID: 4980)
Reads Environment values
- identity_helper.exe (PID: 7672)
- msiexec.exe (PID: 1296)
- msiexec.exe (PID: 8076)
Connects to unusual port
- msedge.exe (PID: 6544)
The sample compiled with english language support
- msiexec.exe (PID: 4980)
- msiexec.exe (PID: 5472)
- msiexec.exe (PID: 8112)
- msedge.exe (PID: 5556)
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- devcon.exe (PID: 4996)
- devcon.exe (PID: 2092)
- drvinst.exe (PID: 7304)
- drvinst.exe (PID: 7972)
- SunloginClient.exe (PID: 2736)
- drvinst.exe (PID: 7948)
- drvinst.exe (PID: 7188)
Manages system restore points
- SrTasks.exe (PID: 7308)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4980)
- msiexec.exe (PID: 5472)
- msiexec.exe (PID: 8112)
- msedge.exe (PID: 5556)
Application launched itself
- msedge.exe (PID: 4444)
- msiexec.exe (PID: 5472)
The sample compiled with korean language support
- msiexec.exe (PID: 8112)
Checks proxy server information
- WerFault.exe (PID: 236)
- SunloginClient.exe (PID: 8008)
Sends debugging messages
- SunloginClient_15.8.0.18235_x64.exe (PID: 8016)
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- SunloginClient.exe (PID: 2012)
- SunloginClient.exe (PID: 7792)
- SunloginClient.exe (PID: 8072)
- SunloginClient.exe (PID: 2736)
- SunloginClient.exe (PID: 5556)
- SunloginClient.exe (PID: 3620)
- SunloginClient.exe (PID: 8008)
- SunloginClient.exe (PID: 2452)
The process uses the downloaded file
- msiexec.exe (PID: 1296)
- SunloginClient_15.8.0.18235_x64.exe (PID: 8016)
- SunloginClient.exe (PID: 7792)
- SunloginClient.exe (PID: 8072)
- SunloginClient.exe (PID: 8008)
Process checks computer location settings
- SunloginClient_15.8.0.18235_x64.exe (PID: 8016)
- SunloginClient.exe (PID: 7792)
Creates files in the program directory
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- SunloginClient.exe (PID: 5556)
- SunloginClient.exe (PID: 8008)
The sample compiled with chinese language support
- SunloginClient_15.8.0.18235_x64.exe (PID: 1228)
- SunloginClient.exe (PID: 5556)
Checks operating system version
- cmd.exe (PID: 7896)
Reads the machine GUID from the registry
- SunloginClient.exe (PID: 7792)
- SunloginClient.exe (PID: 8072)
- devcon.exe (PID: 4996)
- drvinst.exe (PID: 7304)
- SunloginClient.exe (PID: 3620)
- SunloginClient.exe (PID: 1596)
Reads the software policy settings
- devcon.exe (PID: 4996)
Create files in a temporary directory
- devcon.exe (PID: 2092)
- SunloginClient.exe (PID: 2736)
- SunloginClient.exe (PID: 8008)
Creates files or folders in the user directory
- SunloginClient.exe (PID: 8008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
146
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\WINDOWS\system32\WerFault.exe -u -p 5776 -s 592 | C:\Windows\System32\WerFault.exe | Microsoft_Xtools.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | arp -a | C:\Windows\System32\ARP.EXE | — | SunloginClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Arp Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | cmd /c netsh advfirewall firewall delete rule name="SunloginClient" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=tcp enable=yes profile=public | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6920 --field-trial-handle=2312,i,18264979821435792423,5895278453648083818,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 880 | netsh advfirewall firewall add rule name="SunloginDesktopAgent" dir=out action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\agent\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | taskkill /IM OrayAI.exe /F | C:\Windows\System32\taskkill.exe | — | SunloginClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | cmd /c netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Oray\SunLogin\SunloginClient\Driver\Idd64\devcon.exe" remove Root\OrayIddDriver | C:\Program Files\Oray\SunLogin\SunloginClient\driver\Idd64\devcon.exe | — | SunloginClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\SunloginClient_15.8.0.18235_x64\SunloginClient_15.8.0.18235_x64\SunloginClient_15.8.0.18235_x64.exe" --mod=install --admin=1 | C:\Program Files (x86)\SunloginClient_15.8.0.18235_x64\SunloginClient_15.8.0.18235_x64\SunloginClient_15.8.0.18235_x64.exe | SunloginClient_15.8.0.18235_x64.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: HIGH Description: SunloginClient 64 bit Exit code: 0 Version: 15.8.0.18235 Modules
| |||||||||||||||
Total events
51 367
Read events
50 771
Write events
550
Delete events
46
Modification events
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5D92B4A07B8A2F00 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E5E5BCA07B8A2F00 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328448 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6F9F5CFF-0586-492E-9BFB-6BD26D1F814C} | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328448 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0B6FD1CB-05C8-4952-B253-626A21FE25B3} | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2496F2A07B8A2F00 | |||
| (PID) Process: | (4444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
109
Suspicious files
417
Text files
77
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135603.TMP | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135603.TMP | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135603.TMP | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135612.TMP | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135612.TMP | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
93
DNS requests
81
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8180 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1737475195&P2=404&P3=2&P4=VBwjmK7Jt3UIBcKPg%2fozowAIY4Ib%2bkxwGyG8y%2fIyDe2dgvONAdzfZIlCSBKiKfPmkIYE%2fAz88zFUJjgD6G9ZTw%3d%3d | unknown | — | — | whitelisted |
6284 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1737475195&P2=404&P3=2&P4=VBwjmK7Jt3UIBcKPg%2fozowAIY4Ib%2bkxwGyG8y%2fIyDe2dgvONAdzfZIlCSBKiKfPmkIYE%2fAz88zFUJjgD6G9ZTw%3d%3d | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1737475195&P2=404&P3=2&P4=VBwjmK7Jt3UIBcKPg%2fozowAIY4Ib%2bkxwGyG8y%2fIyDe2dgvONAdzfZIlCSBKiKfPmkIYE%2fAz88zFUJjgD6G9ZTw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3508 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
5064 | SearchApp.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4444 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
6544 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
google.com |
| unknown |
www.bing.com |
| unknown |
config.edge.skype.com |
| unknown |
i-060.wwentua.com |
| unknown |
_446._https.i-060.wwentua.com |
| unknown |
edge.microsoft.com |
| unknown |
edge-mobile-static.azureedge.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
8008 | SunloginClient.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ifconfig .me) |
8008 | SunloginClient.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
SunloginClient_15.8.0.18235_x64.exe | [6400] 2025-01-17 11:40:30.481 = Debug = [select_tracker] run ok
|
SunloginClient_15.8.0.18235_x64.exe | [6416] 2025-01-17 11:40:30.481 = Debug = [thread] set thread name Thread-6416 95e392a0 / 6416
|
SunloginClient_15.8.0.18235_x64.exe | [6232] 2025-01-17 11:40:30.481 = Debug = [thread] set thread name Thread-6232 a5bee7c0 / 6232
|
SunloginClient_15.8.0.18235_x64.exe | [6400] 2025-01-17 11:40:30.481 - Info - [dpi] DPIAwareness set 2 success.
|
SunloginClient_15.8.0.18235_x64.exe | [5992] 2025-01-17 11:40:31.434 - Info - [dpi] DPIAwareness set 2 success.
|
SunloginClient_15.8.0.18235_x64.exe | [5992] 2025-01-17 11:40:31.434 = Debug = [select_tracker] run ok
|
SunloginClient_15.8.0.18235_x64.exe | [5080] 2025-01-17 11:40:31.434 = Debug = [thread] set thread name Thread-5080 22bd9110 / 5080
|
SunloginClient_15.8.0.18235_x64.exe | [6012] 2025-01-17 11:40:31.434 = Debug = [thread] set thread name Thread-6012 a5bee7c0 / 6012
|
SunloginClient_15.8.0.18235_x64.exe | [4512] 2025-01-17 11:40:31.572 = Debug = [thread] set thread name Thread-4512 253051b0 / 4512
|
SunloginClient_15.8.0.18235_x64.exe | [5992] 2025-01-17 11:40:31.572 = Debug = [select_tracker] run ok
|