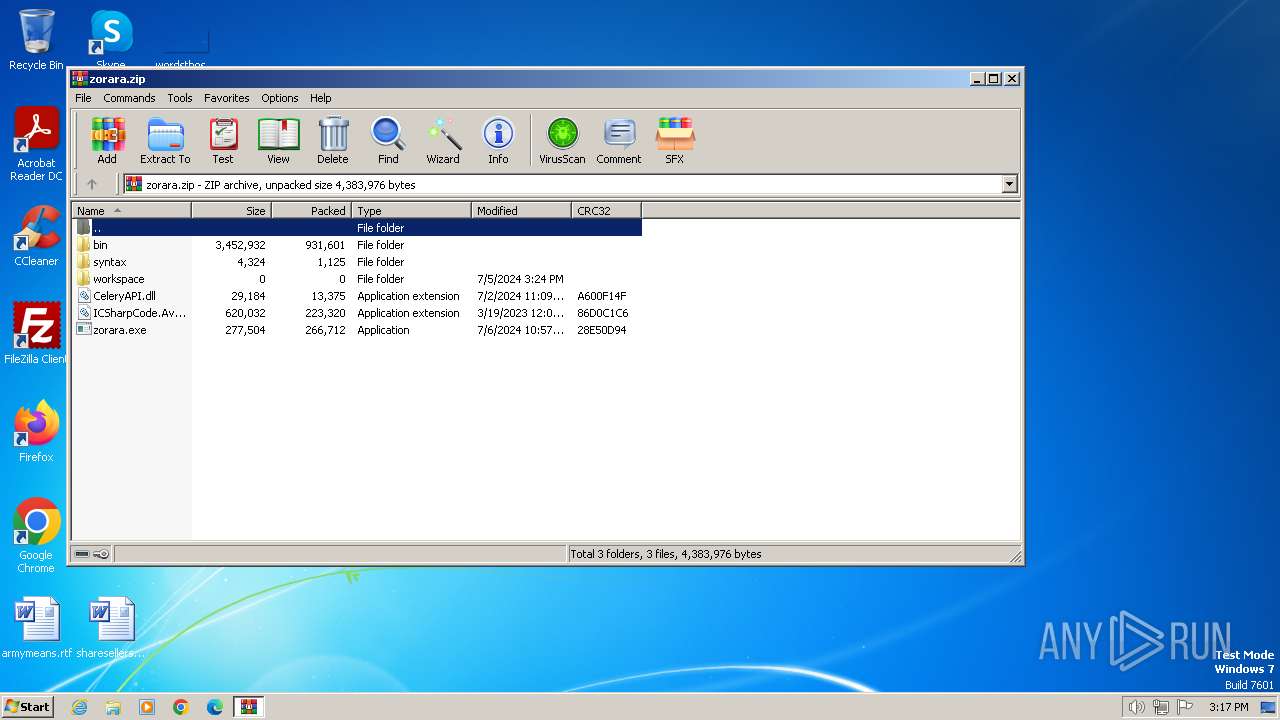
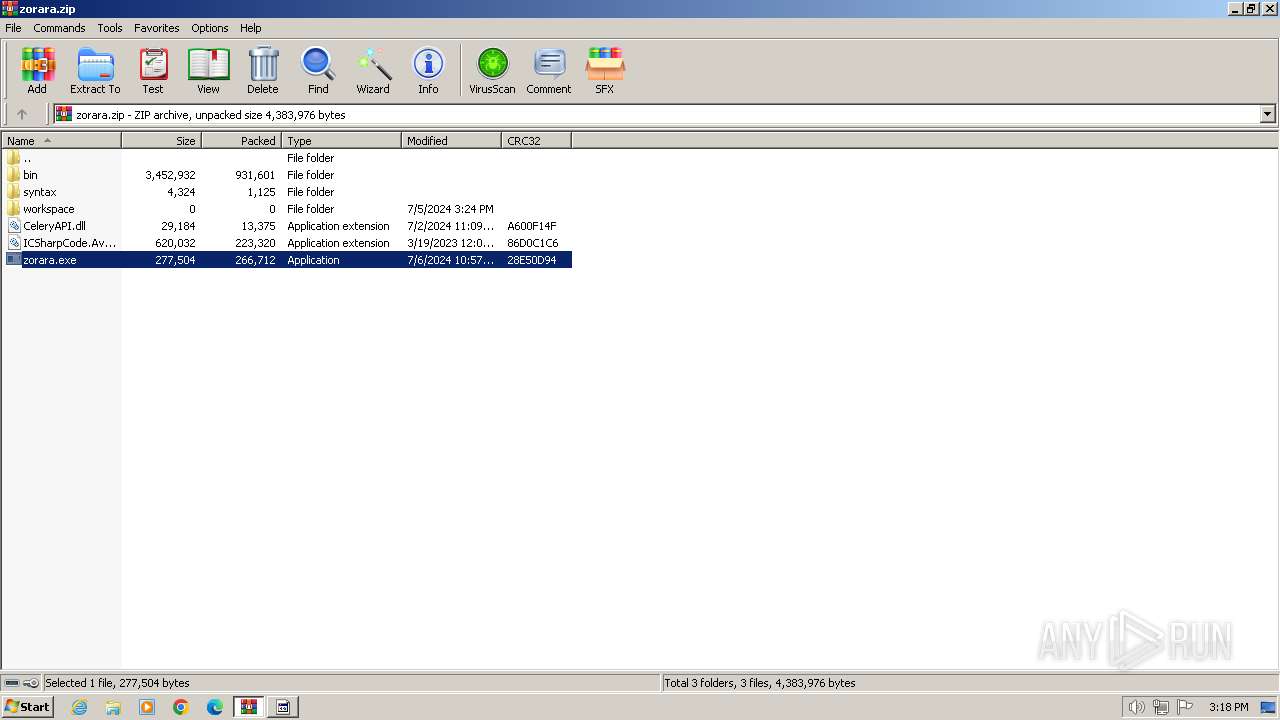
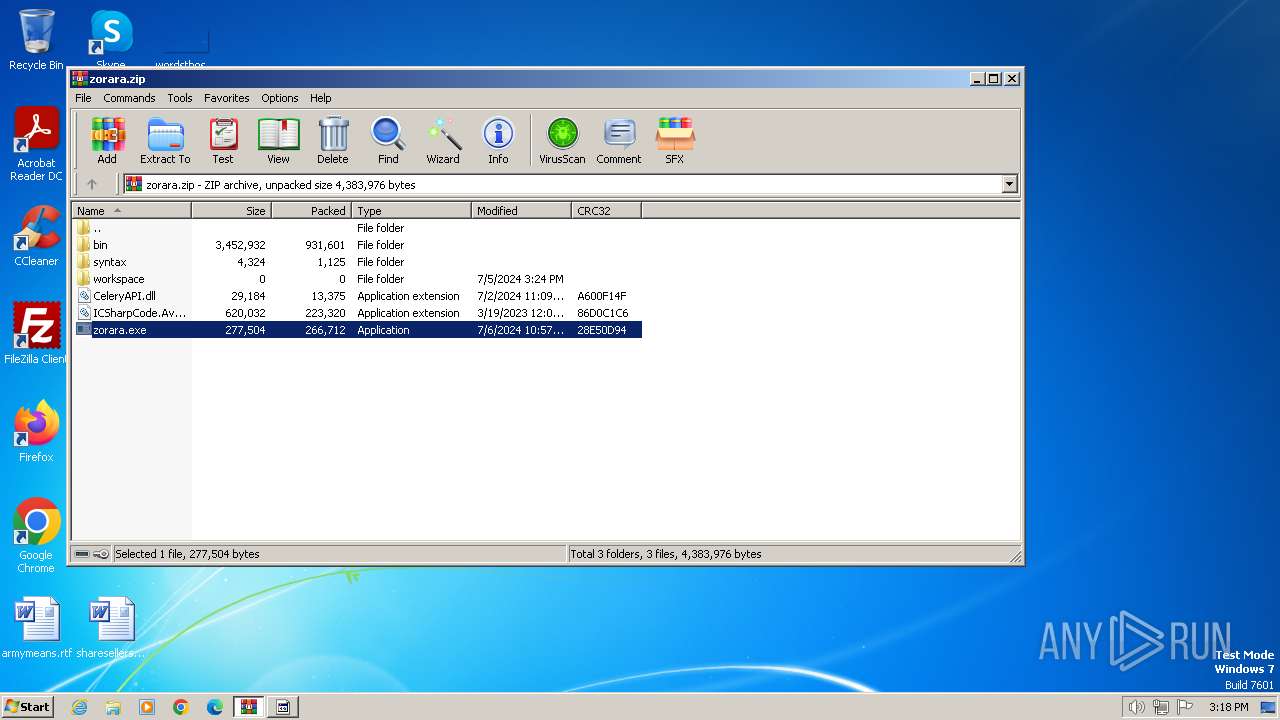
| File name: | zorara.zip |
| Full analysis: | https://app.any.run/tasks/c82ecb9c-5f20-45ff-a398-d52f15eda30d |
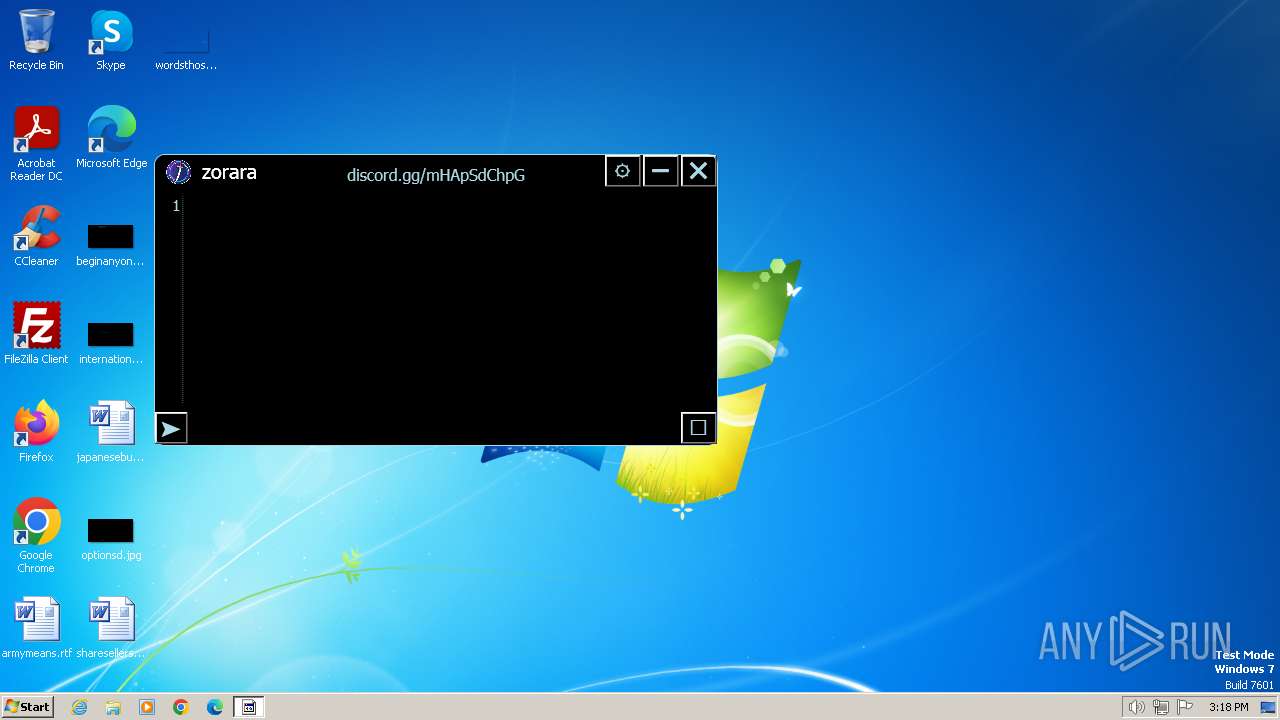
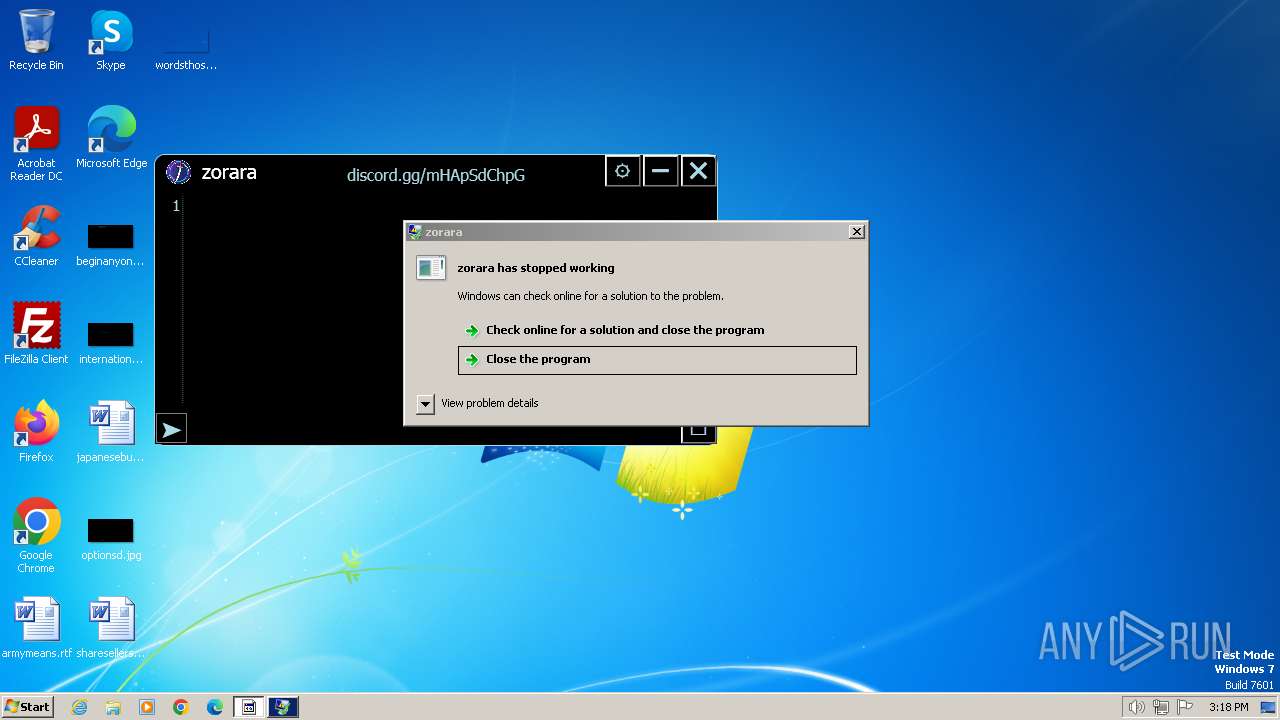
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2024, 14:17:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1B87E0FDFD6E57897FD9DBC1AF3443D4 |
| SHA1: | 8DA23DA2B63227C313761BE06772AD3CCFBB5B3D |
| SHA256: | 46AF44289F2C83C5ACB7A2BD97FC55967922EEA3066162A5D6A7D560C82B906F |
| SSDEEP: | 49152:6Q5lfID6gLffzHeaIHwuSV390btSx/l3r+AfuBuqtEfP91FwP3r5dXrefNl0hQ06:l5lWLffz+Xd9tUl+AfuAq21safvgQyl+ |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3384)
SUSPICIOUS
Reads security settings of Internet Explorer
- zorara.exe (PID: 3520)
- WinRAR.exe (PID: 3384)
Reads settings of System Certificates
- zorara.exe (PID: 3520)
Reads the Internet Settings
- zorara.exe (PID: 3520)
INFO
Reads the computer name
- zorara.exe (PID: 3520)
Checks supported languages
- zorara.exe (PID: 3520)
Reads the machine GUID from the registry
- zorara.exe (PID: 3520)
Disables trace logs
- zorara.exe (PID: 3520)
Create files in a temporary directory
- zorara.exe (PID: 3520)
Reads Environment values
- zorara.exe (PID: 3520)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3384)
Reads the software policy settings
- zorara.exe (PID: 3520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:06:29 19:57:14 |
| ZipCRC: | 0x9d8da223 |
| ZipCompressedSize: | 16812 |
| ZipUncompressedSize: | 45056 |
| ZipFileName: | bin/CeleryIn.bin |
Total processes
40
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\zorara.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3520 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\zorara.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\zorara.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: zorara Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
7 930
Read events
7 865
Write events
65
Delete events
0
Modification events
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zorara.zip | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
5
Suspicious files
1
Text files
2
Unknown types
0
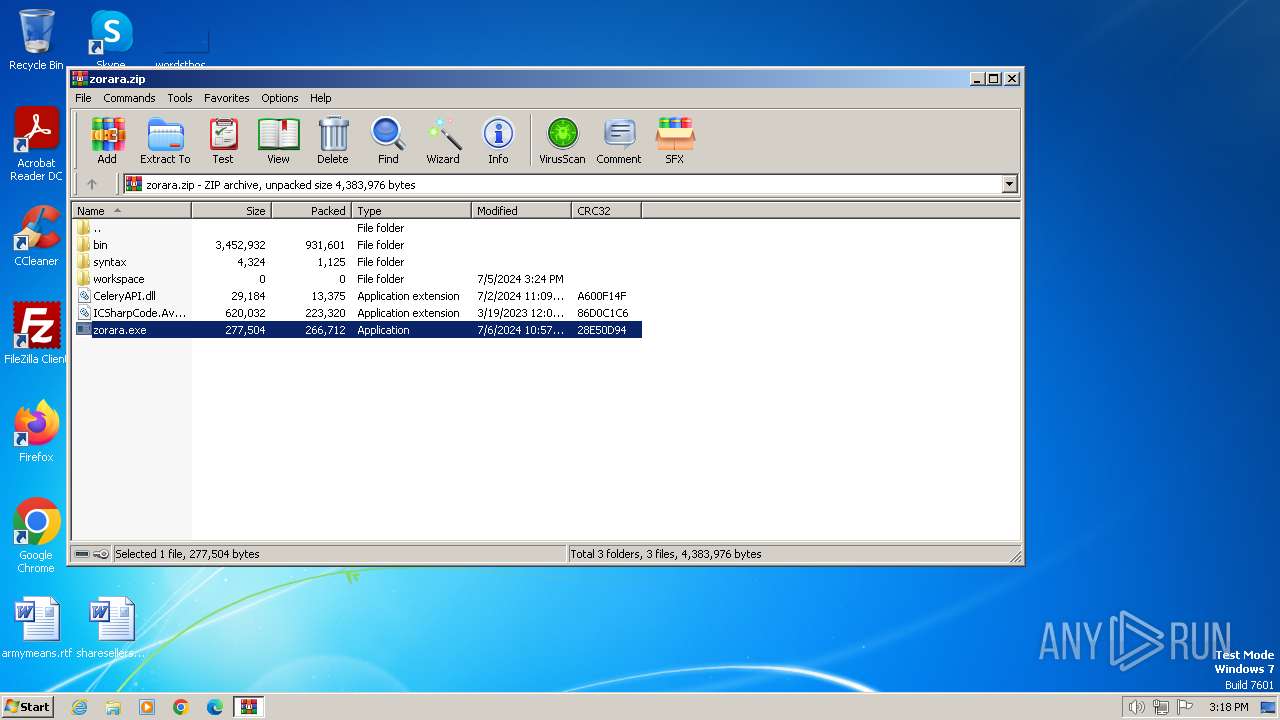
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\bin\CeleryIn.bin | executable | |
MD5:1345CBC437E118C1D7DFA6CB77C35E1E | SHA256:84B82453BBDA410B7F53521EB995DBF486B1CCE4706AB8504BC5CA35E93EB426 | |||
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\syntax\lua.xshd | xml | |
MD5:08713090C9CA001CA19735D0D23F93BB | SHA256:C1AF5D8D18E066F0C2D535B656174AE8CDBE5F0FFFE548E96D3FD2602FE7F9B3 | |||
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\bin\CeleryInjector.exe | executable | |
MD5:3B5F8A3991AA5E0079BBC52C7518C4D4 | SHA256:F5035DA7DE64C48F6B1EAF947A028F0E5FD3970F971C2A6C6075501C4AAD1AF8 | |||
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\ICSharpCode.AvalonEdit.dll | executable | |
MD5:D8F0E3940B5BBE9599EE0A84B541D50F | SHA256:202A4719E4B879DA67445AB50901D80A259F8680B5D16BC0F929E0A6F6FAD199 | |||
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\CeleryAPI.dll | executable | |
MD5:21FF21B6DCCA7549A20C1C942D1F7E86 | SHA256:238AFF8554764C1CE5927A1F15BD1BB6C4FE3D83DEB9B61913C81083FE15CB05 | |||
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\bin\ver.txt | text | |
MD5:25198DBBB5F787214992C13A596F5751 | SHA256:9D2BF356D838FABA1759EFD3E9DE32647BD68E9DA8C92878074B392872E9F04E | |||
| 3520 | zorara.exe | C:\Users\admin\AppData\Local\Temp\WPF\jekoyjyj.m4f | binary | |
MD5:AAADCE85E3A72CD5F6ED05B1EDF628E2 | SHA256:5828E602EDF3EED6FD143B403B853B481AB58F812B8F4AAF559983D2C5774027 | |||
| 3384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.29045\zorara.exe | executable | |
MD5:C3F736774723991E657505DE0DEBFB7E | SHA256:F5E1F8B288CCC8CEDC1165CFCE5A38EA520D73A77051A6321D667DB484B5C5FC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
9
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
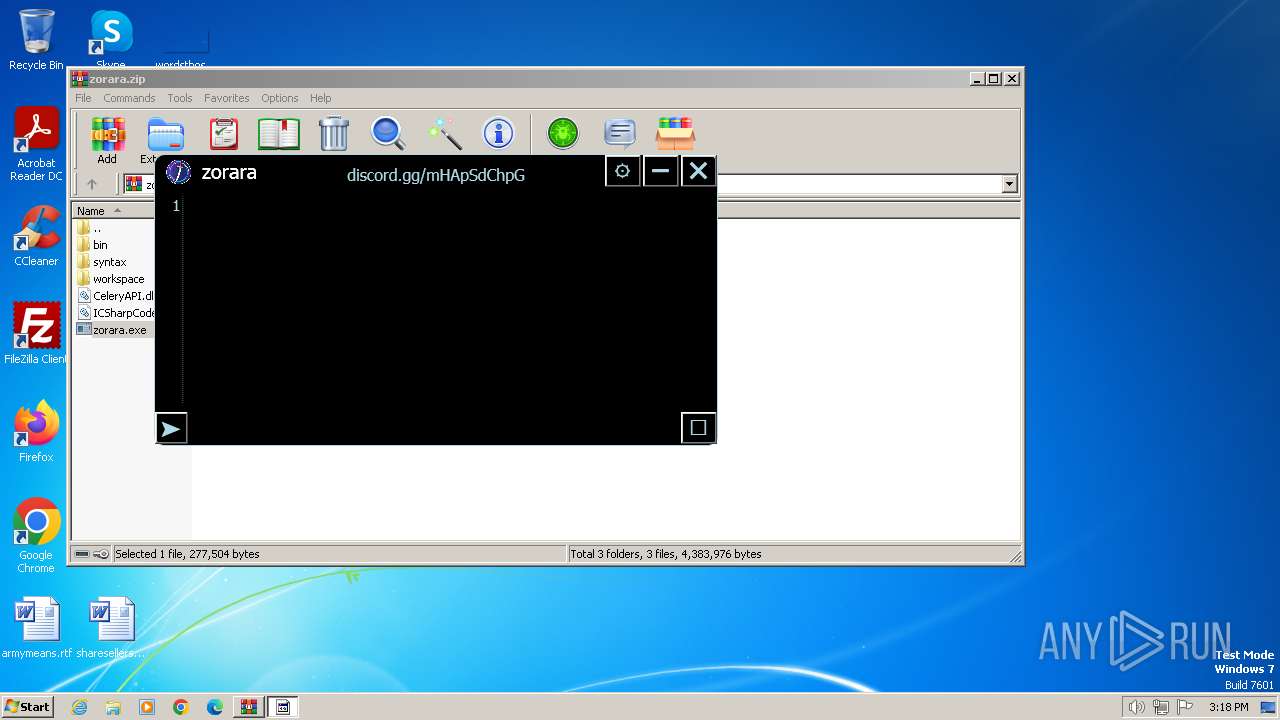
3520 | zorara.exe | 104.26.3.16:443 | rentry.co | CLOUDFLARENET | US | unknown |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1372 | svchost.exe | 23.50.131.216:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rentry.co |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
1060 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
3520 | zorara.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |