| File name: | Fotos fiesta 7 millones de clientes .jpg.exe |
| Full analysis: | https://app.any.run/tasks/6d3ee945-527b-41b9-a3bb-3d0d5fd1871a |
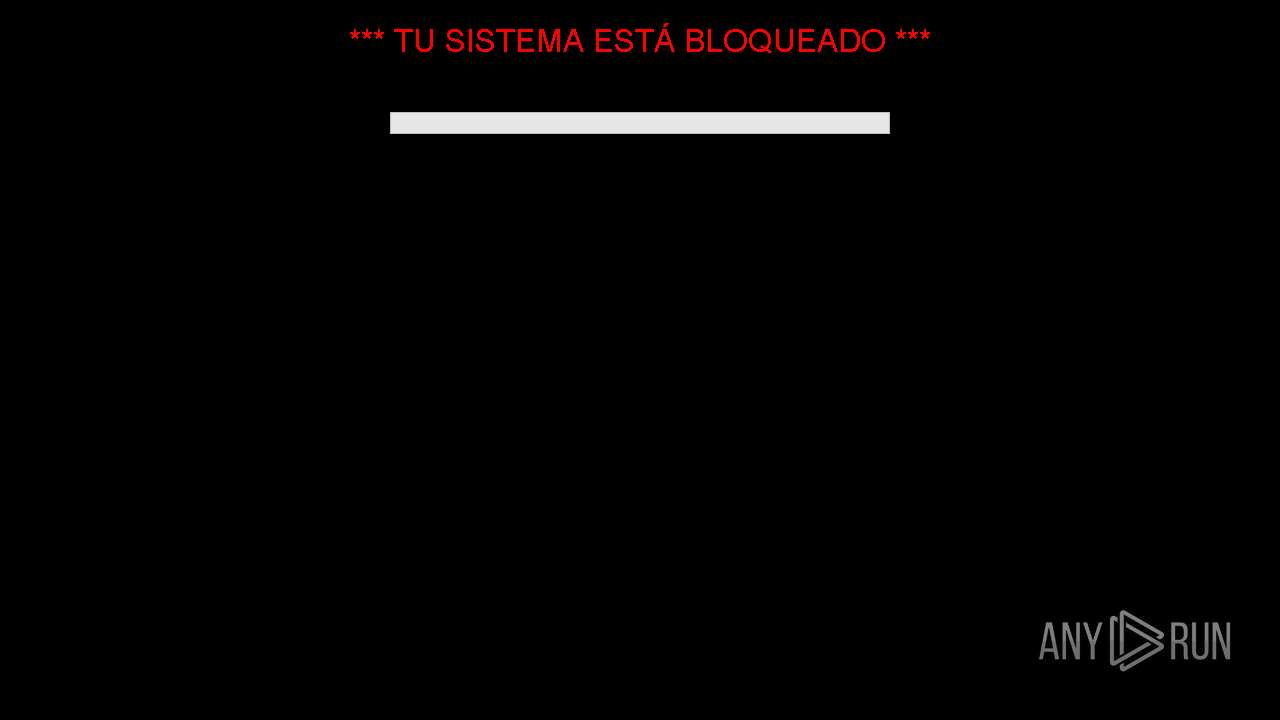
| Verdict: | Malicious activity |
| Analysis date: | October 16, 2024, 17:14:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 7A578E3738AFA30A63E0BEDE2B80B83A |
| SHA1: | B1C36FF3AE2E3468575F116780876B17F796E113 |
| SHA256: | 46ABEFCD1C15CD58B797BA58D15D7B0CE6F71F7FF35ED8299874CE46F3B3F85A |
| SSDEEP: | 196608:1NcP9YaqYITyYNwnGX4Be0plRWooJKIDSIc:1N4LITynGIBeYWLr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
Process drops python dynamic module
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
The process drops C-runtime libraries
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
Process drops legitimate windows executable
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
Application launched itself
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
INFO
Reads the computer name
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
Checks supported languages
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
Create files in a temporary directory
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
PyInstaller has been detected (YARA)
- Fotos fiesta 7 millones de clientes .jpg.exe (PID: 6692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:10:13 23:51:30+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 172032 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcdb0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
123
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5068 | "C:\Users\admin\AppData\Local\Temp\Fotos fiesta 7 millones de clientes .jpg.exe" | C:\Users\admin\AppData\Local\Temp\Fotos fiesta 7 millones de clientes .jpg.exe | — | Fotos fiesta 7 millones de clientes .jpg.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6164 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6692 | "C:\Users\admin\AppData\Local\Temp\Fotos fiesta 7 millones de clientes .jpg.exe" | C:\Users\admin\AppData\Local\Temp\Fotos fiesta 7 millones de clientes .jpg.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7128 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
292
Read events
292
Write events
0
Delete events
0
Modification events
Executable files
70
Suspicious files
3
Text files
1 037
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\_ctypes.pyd | executable | |
MD5:A55E57D7594303C89B5F7A1D1D6F2B67 | SHA256:F63C6C7E71C342084D8F1A108786CA6975A52CEFEF8BE32CC2589E6E2FE060C8 | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\VCRUNTIME140_1.dll | executable | |
MD5:68156F41AE9A04D89BB6625A5CD222D4 | SHA256:82A2F9AE1E6146AE3CB0F4BC5A62B7227E0384209D9B1AEF86BBCC105912F7CD | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\PIL\_webp.cp313-win_amd64.pyd | executable | |
MD5:946CAAF6DB0893119C36A528256BDD3C | SHA256:EE90ED7EB3D53AB8A7895CD3993418FF1AAC294A7FFA769487E4EAA109A2E061 | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\_queue.pyd | executable | |
MD5:1C03CAA59B5E4A7FB9B998D8C1DA165A | SHA256:B9CF502DADCB124F693BF69ECD7077971E37174104DBDA563022D74961A67E1E | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\_bz2.pyd | executable | |
MD5:CB8C06C8FA9E61E4AC5F22EEBF7F1D00 | SHA256:FC3B481684B926350057E263622A2A5335B149A0498A8D65C4F37E39DD90B640 | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\_lzma.pyd | executable | |
MD5:1BA022D42024A655CF289544AE461FB8 | SHA256:D080EABD015A3569813A220FD4EA74DFF34ED2A8519A10473EB37E22B1118A06 | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\PIL\_imagingtk.cp313-win_amd64.pyd | executable | |
MD5:1042EC0CB4E0CB65D6AA82FDE0B9C5A4 | SHA256:4604AB53311C25130E8A52E2721CF6F5B3E76B750B00B446FF03A3C224648B4A | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\PIL\_imaging.cp313-win_amd64.pyd | executable | |
MD5:EF228C0B3BEC799DB695CA6F8BBED5D6 | SHA256:3970E5ACEC7E890D5279F14E29DD5982C9435262CBB36BCBFD5DB493FA7C192A | |||
| 6692 | Fotos fiesta 7 millones de clientes .jpg.exe | C:\Users\admin\AppData\Local\Temp\_MEI66922\PIL\_imagingmath.cp313-win_amd64.pyd | executable | |
MD5:759BEDF5DC3E9A040C539BBC5267EE14 | SHA256:415E6FF9F410A07734C908129A5D819E61AB0718E704F3FC1B2E33EE274185D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
52
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2000 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.23.209.183:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.177:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |